Abstract
Blockchains are traditionally blind to the real world. This implies reliance on third parties called oracles when extrinsic data are needed for smart contracts. Oracle implementation, however, is still controversial and debated due to the reintroduction of trust and a single point of failure. The blindness to the real world also makes blockchains unable to communicate with each other, preventing any form of interoperability. This limitation prevents, for example, liquidity held in Bitcoin from flowing into DeFi applications. An early approach to the interoperability issue is constituted by “wrapped tokens”, representing blockchain native tokens issued on a non-native blockchain. Similar to how oracles reintroduce trust and a single point of failure, the issuance of wrapped tokens involves third parties whose characteristics need to be considered when evaluating the advantages of “crossing-chains”. This paper provides an overview of the available wrapped tokens and the main issuing procedures. Benefits, limitations, and implications for trust are listed and discussed.
1. Introduction
“Bitcoin can’t speak the language of Ethereum and vice versa……we can’t spend bitcoin on the Ethereum network, nor can we make use of Ethereum’s smart contracts on the Bitcoin network” [1]. There is no one-size-fits-all solution for blockchains, and each distinct ecosystem offers differences in scalability, security, programmability, and privacy [2]. The heterogeneity of users’ needs justifies the coexistence of different platforms [3]. However, from a financial perspective, their inability to communicate prevents DeFi applications from fully exploiting the capital held in the protocols [4,5]. Interoperability across chains was not integrated into the original idea of blockchain [6]; however, as technology grew, the need for cross-chain solutions arose [7,8]. Interoperability would grant users accessibility, speed, and a fee reduction [9]. Having BTC, the most touted crypto asset on the Ethereum network, for example, and including it in smart contracts was quite a fascinating idea, and it has been possible thanks to the introduction of wrapped tokens [10,11]. Wrapped tokens were proposed as a means to overcome the absence of communication between different blockchains [12]. According to the DeFi Pulse website, one of the most reliable resources for statistical analysis on DeFi, it emerges that more than 308,000 BTC (November 2021) are being used in DeFi as wrapped tokens [13]. The same website also shows that 80% of wrapped bitcoins are WBTC, while the remaining part is provided by other emerging companies/platforms. It is a considerable amount, taking into account how much Bitcoin is worth, but since the total circulation of bitcoin is over 18M, those used as wrapped tokens are still around 2%. Lately, the offer of wrapped tokens is increasing, and many companies, such as Tron, Binance, Huobi, Klever, Solana, and Tezos, are offering their cross-chain proposals [12,14,15]. Although most of these are based on the implementation of wrapped tokens, the bridging process slightly differs. With the technology available today, “bridging” an asset to another blockchain means locking the original asset on its blockchain and minting a copy on another chain that is not natively compatible [16].
Reviewing available material on the topic, this paper aims to explain the idea behind the creation of wrapped tokens, outlining their role, use, and drawbacks. Furthermore, comparing prominent and active projects in the field, the role of involved intermediaries is highlighted, examining their impacts on the trustless nature of the protocols.
In this paper, the first known examples, such as WETH, WBTC, and RenBTC, are discussed to understand the differences among the entities involved in their management [17,18,19]. Other approaches such as Synths are outlined, analyzing the architecture of a blockchain derivative platform solution. Finally, an overview of Layer2 (L2) solutions is provided, identifying the advantages and risks of this alternative approach [20,21]. The scope of this paper is to give a broad overview of the concept of wrapped tokens to facilitate further theoretical and empirical studies on this subject. While describing how technologies work, this study also focuses on how they will reintroduce the concept of trust in the blockchain [22]. Given the practical absence of academic material, the research will mostly rely on “gray literature”, which is a form of literature made of whitepapers, opinion posts, blogs, and official announcements [23,24]. Due to the rapid development of blockchain applications, the use of gray literature ensures the most up-to-date information. However, being non-peer-reviewed material, an explanation of how these data are retrieved and evaluated is also provided.
From the analyzed examples, it emerges that a real bridge between blockchains still does not exist, but wrapped tokens constitute an effective workaround until this feature is developed [16,25]. Discussing how they grant interoperability in a practical manner, insight on the most promising alternative is also provided in this work. The paper proceeds as follows. The following section outlines the materials and method, while the third section provides an overview of the history of wrapped tokens and their predecessors. Section 4 outlines some of the most promising solutions in the field, while Section 5 discusses their characteristics, analyzing strengths and weaknesses. Section 6 concludes the paper by providing suggestions for further research.
2. Materials and Methods
In order to gather relevant articles for this study, the initial approach was to query the most prestigious academic databases and review the retrieved materials. Therefore, on 2 September 2021, Scopus and Web-of-Science (WoS) databases were queried using the keywords “wrapped”, “token”, and “blockchain” using the “title-abs-key” and “Topic” sections. Unfortunately, the research returned no results either for Scopus or WoS. Therefore, it was necessary to enlarge the area of the research to retrieve the required data. Instead of selecting title-abs-key and Topic, the queries were run on “All Fields” for both databases. The research then returned 6 and 1 articles. The queries were also rerun on 11 November 2021 during the review process, returning the same entries. Inspecting the occurrences of the keywords with a word processor, it was immediately clear that most of the papers were inserted in the sample either for referring to other wrapping concepts (e.g., wrapped contracts or wrapped passwords) or for having articles concerning wrapped tokens in the references. Only two articles retrieved from Scopus discussed wrapped bitcoins and wrapped token mechanisms [26,27]. The only article found in WoS was discarded for being off topic. Although well written, the two retrieved papers were clearly not sufficient to undergo any analysis on wrapped bitcoin or wrapped tokens in general. Therefore, other resources were retrieved. When academic resources are insufficient or outdated, gray literature is also used in academic research [28,29,30]. With the term “gray literature”, we refer to publicly available material, such as blogs, newspaper articles, and opinion posts, that have not undergone a peer-review process. The use of gray literature can widely enlarge the available material, enabling more comprehensive and up-to-date information to be processed. On the other hand, introducing non-peer-reviewed material in academic research requires a rigorous selection of the retrieved articles to avoid misleading or false information being spread in the academic venues. Guided by the work of Garousi et al. [31], the gray literature sample consulted in this work is classified according to the degree of reliability and information extracted accordingly. The core concept discussed in the paper builds on the most reliable material, while data from other resources serve as complementary data.
The keywords used to find gray literature were the same as the academic research, but the platforms used were google.com and duckduckgo.com (03 Sep/2021). In line with the expectations, the query returned enough material so that only the Google research counted more than 18 million entries. Results were organized into ten per page, and titles were inspected in order to find relevant articles. Crawling was stopped at the 30th page due to the saturation of results. Initially, 67 articles were whitelisted, but after reading them, six were discarded for being published in untrusted blogs or for being extremely short. Furthermore, 11 more articles were retrieved for being cited in the selected ones. The reliability of articles was classified into A, B, C, and D, where A is the most reliable and D the least reliable, according to the following criteria:
- A.
- Within this group are whitepapers and official blogs written by the developers of the related platforms. Articles from renowned experts, such as Vitalik Buterin, also belong to this group. The reason for considering those resources as the most reliable is that details on technology are certain and accurate since they directly come from the developers. On the other hand, expert opinion is inserted, as it is thought to directly impact technology development.
- B.
- To this group belongs guides and study material, provided by famous blogs, such as Binance Academy, The Cryptonomist, or opinion posts written by academics/developers.
- C.
- This category includes opinion posts and blogs written by bloggers with a verifiable bio and a traceable history of blog activity. Therefore, bloggers’ first articles or articles without an identifiable source do not belong to this group.
- D.
- Finally, articles that are not on a reliable source and not written by an identifiable author are inserted in this group. They are not discarded as they provide information that is not available in other sources.
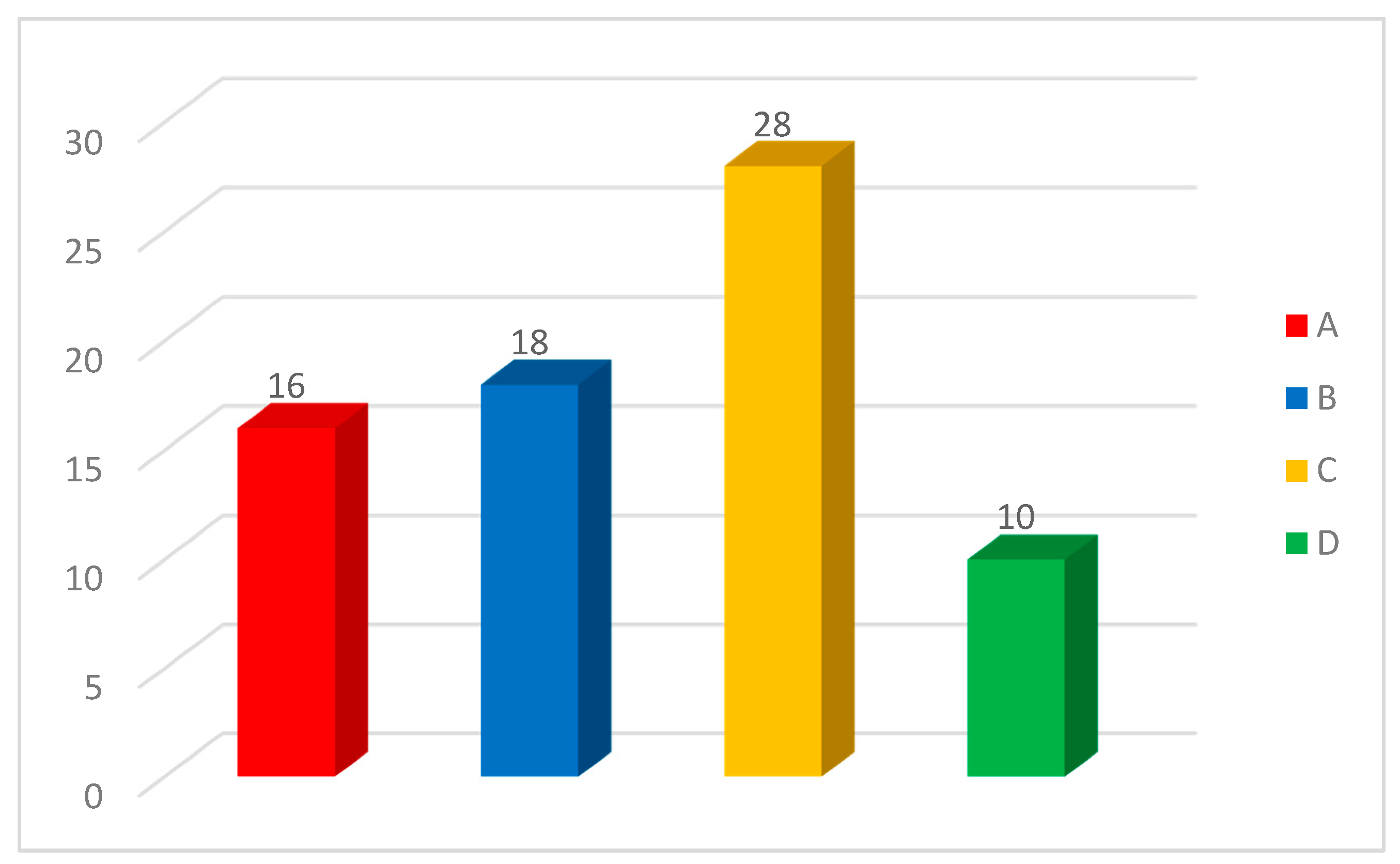
Figure 1 provides an overview of the retrieved material distinguished by the degree of reliability. The two academic papers are not included since their reliability is not questioned. Appendix A provides instead a sample of retrieved articles sorted according to the above-mentioned criteria.
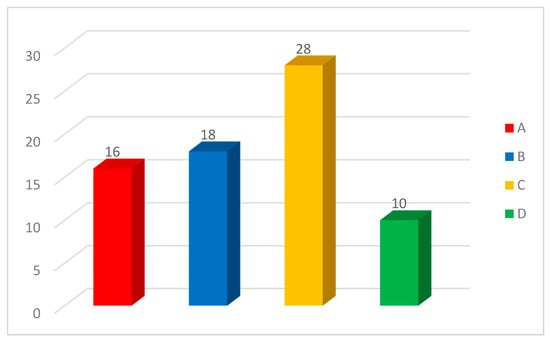
Figure 1.
Source Type/Entries.
Data Extraction
Concerning data extraction, it was necessary first to clarify the type of data to be retrieved. As a preliminary study on this particular topic, there was no predetermined framework to build upon. As most of the retrieved material was not academic, the usual data concerning metrics (title, date, author, institution, outlet, publisher, citations) were thought to be out of the scope. Therefore, data extraction mainly concerned the subject under analysis distinguished by specific topics. First, information on the underlying technology and precursor of wrapped tokens were extracted. Therefore, specific descriptions of what a wrapped token is and how it works were searched. Then, a list of alternatives or innovations to the original mechanism was searched.
Once an overview of the theory of wrapped token was retrieved, research of advanced cases already operating was performed in order to better distinguish between the underlying technologies. The cases with complete and reliable sources were then presented and discussed. As blog articles may also be written for advertising purposes, all the minting, wrapping, and bridging steps were reproduced and commented on by the author to verify the veracity of retrieved information. When inconsistencies were found, where possible, the app developers were also contacted for clarifications.
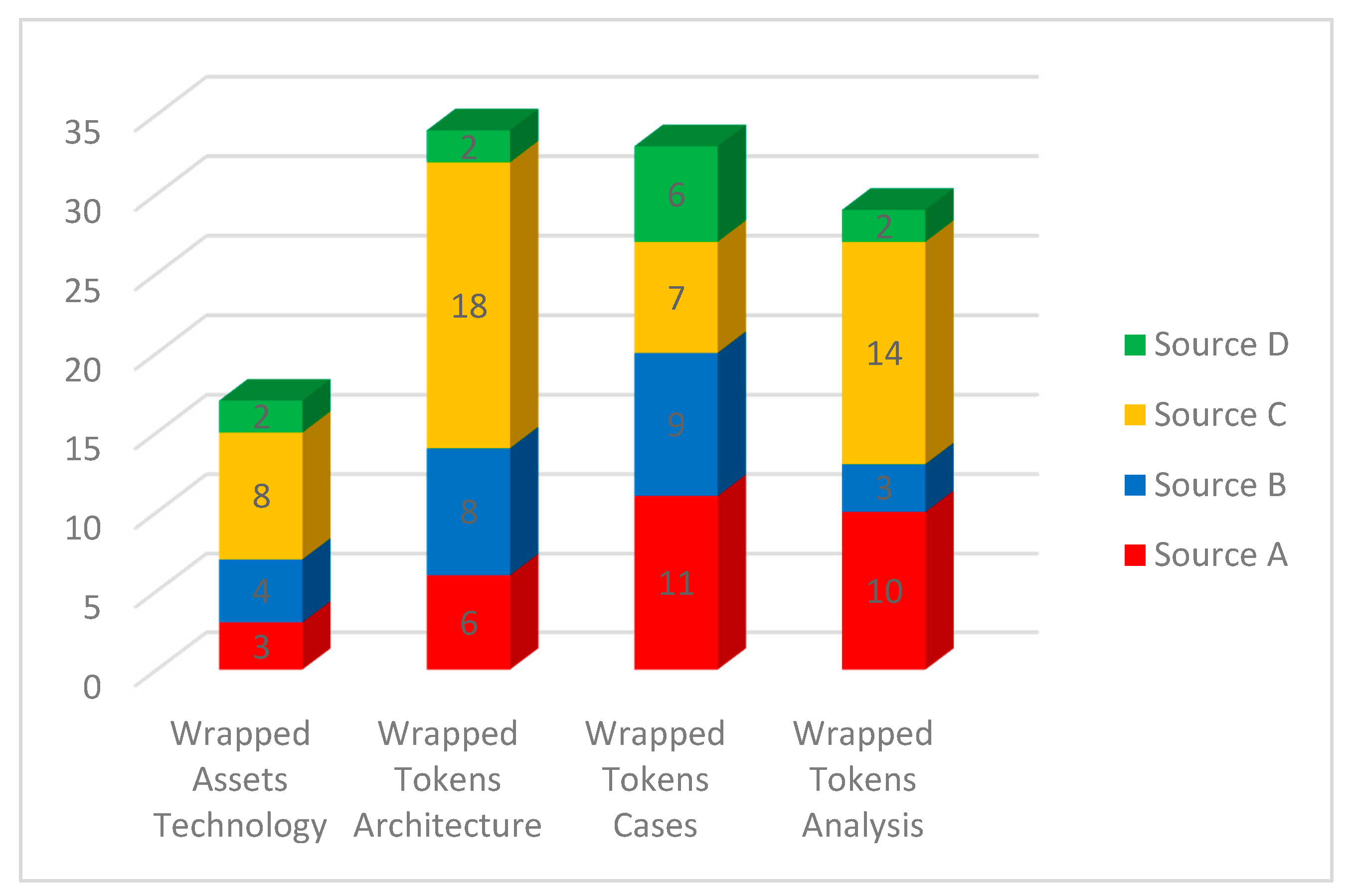
Lastly, articles offering a critical opinion or analysis on the topics were searched to better discuss the advantages, disadvantages, and risks of every technology/approach. As the coexistence of those technologies is possible but unlikely, the last groups of articles help identify the technologies with more chances to be adopted in the long run. Table 1 presents a description of extraction variables, and Figure 2 distinguishes them by source type. Since an article can provide data on multiple subjects, the number of papers in the figure is higher than the total sample.

Table 1.
Extraction variables.
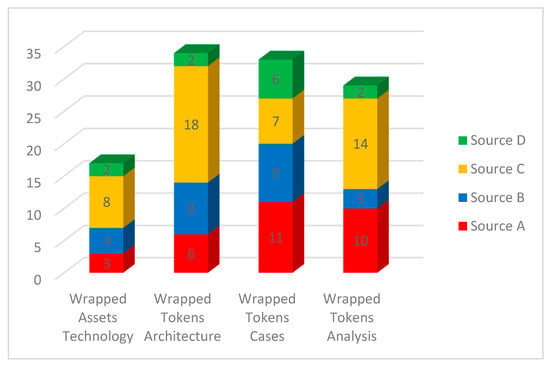
Figure 2.
Contributions by resource.
3. Why Wrapped Tokens?
3.1. Wrapped Assets and Stablecoins
To better understand the concept of wrapped tokens, it is helpful to first introduce the concept of a wrapped “asset”. The wrapped asset is a token that represents a real-world or crypto asset, and it is backed by the represented asset or assets of equal value [32]. The backing asset is put in a vault called a “wrapper” (hence, wrapped asset) [16]. Wrapped assets are issued on a blockchain and should keep the same value as the represented asset. Tokenizing an asset means converting its structure to a blockchain-compliant one so that smart contracts can manage it. The underlying idea of a wrapped asset is that since it is impossible to physically move an asset to the blockchain or make it blockchain-compliant, a token representing the asset is created instead. Of course, to avoid double-spending, the real-world asset should be locked until its “avatar” is used on the blockchain. Examples of wrapped assets are the so-called stablecoins [33,34]. The stablecoins are tokens that represent fiat currencies and are particularly useful in DeFi, given the usual volatility of cryptocurrencies [35]. In blockchain-based financial applications, fiat currencies were considered helpful to hedge against the risk of volatility. Unfortunately, they could not be directly imported into smart contracts for being in the real world and having no blockchain-compliant characteristics. Although digitized, fiat currencies cannot be directly imported on the blockchain. Therefore, in order to have those stable assets running on distributed ledgers, a representation of these had to be created with blockchain-compliant characteristics.
USD-T and USD-C are two stablecoins issued by the Tether Foundation and Centre, respectively [36,37]. The issuing organizations are in charge of guaranteeing the peg of those cryptocurrencies to the US dollar. In principle, in order to mint stablecoins, an equivalent amount of dollars or financial assets should have been “held” by trusted entities chosen by the issuing companies [38]. For that reason, the above-mentioned stablecoins are called “custodial” due to their dependency on a third-party centralized custodian service [29,33]. The centralization of control of those currencies and the absence of evident proof of assets makes some crypto communities reluctant to consider those as properly wrapped assets [39]. Although proof of funds is regularly provided through online reports on official websites, there exists not an on-chain publicly auditable source [40]. Therefore, a considerable level of trust must be granted to the service provider and auditing companies.
Other stablecoins (such as sUSD, DAI, USD-J) issued without third-party custodial services are called “non-custodial” and are instead widely recognized as wrapped assets [41,42]. The sUSD, for example, is a stablecoin issued by Synthetix when staking SNX native tokens. One-fourth of the staked SNX is issued as stablecoin, and the proof of the locked asset will always be available on-chain for auditing purposes. DAI and USD-J, instead, are decentralized projects issued by MakerDAO and JUST-GOV, respectively. They allow the issuance of stablecoins by collateralizing assets into a smart contract with at least a 150% ratio [43]. The main difference between the first group of stablecoins (USD-T, USD-C) and the second one (sUSD, DAI, USD-J) is that while the first involves a centralized authority and does not offer a transparent proof of asset, the second is fully managed by smart contracts, and the proof of asset is available on-chain. It is, however, crucial to state that although the second group does not rely on a third party for the proof of asset, they do rely on third-party oracles to retrieve the collateral exchange rate with USD [44]. The decentralization and reliability of those oracles then play a critical role in the trustworthiness of the protocol [35,45].
3.2. The Emergence of Wrapped Tokens
Wrapped tokens are a particular category of wrapped assets, not intended to create a crypto representation of real-world assets, such as gold, stock, or fiat currencies, but of other crypto assets instead (e.g., Bitcoin, BNB, Ether) [25,46]. The reason for their existence is because, as blockchains are entirely isolated from the external world, they are also isolated from each other [47]. Therefore, as there is no way to bring dollars to Ethereum blockchain and stablecoins are to be used instead, there is also no means to bring bitcoin to Ethereum, and wrapped tokens must be used instead [48]. Although hypothesized and desirable, the communication and interoperability between blockchains are impossible with the existing technologies [49], and cryptocurrencies cannot “jump” from one chain to another. The limitation of interoperability is addressed with the same solution as bringing real-world assets to the blockchain, therefore creating a “crypto-copy” of the required asset. Hence, the solution to using bitcoin on the Ethereum blockchain was creating an asset on Ethereum with the ERC-20 standard (Ethereum Request for Comments 20) [50] and “pretending” that it is bitcoin.
There are several reasons to aim and promote interoperability between the two chains and between blockchains, in general [26,51]. First, despite the interest of investors in Ethereum and altcoins, the highest portion of liquidity is still retained by bitcoin [52]. Therefore, while in centralized exchanges, almost all the trading pairs are with bitcoin, in decentralized exchanges, the trading pairs are with ETH, SOL, TRX, WAVES, and so on, reaching together a much lower volume of trade than bitcoin alone [53]. This creates a lack of liquidity for decentralized exchanges with respect to centralized exchanges. Second, blockchains, such as bitcoin, are characterized by low scalability and high transaction fees during congestion time. Therefore, they are not suitable for a constant large volume of transactions or microtransactions [54]. Lastly, crypto belonging to different ecosystems (e.g., Solana, Ethereum, Tron) does not adhere to the same standards [27]. Therefore, they are not suitable for management by the same smart contract. Furthermore, even in the same ecosystem, tokens may belong to different standards (e.g., ERC-20, ERC-223, TRC-10, TRC-20, BEP2), creating further interoperability issues.
Bridging separate blockchains and especially bridging bitcoin to other blockchains would solve the problem of liquidity that decentralized finance is experiencing. The capital hold in bitcoin could also be finally used to obtain an interest over its simple appreciation. Bridging blockchains would also decrease latency and the cost of transactions. The bitcoin network [55] has slow block time and high transaction fees (1/10 block/minute, and around 30 USD/transaction), while using bitcoin on the Tron network, for example, would mean moving them almost for free with a block time of roughly three seconds [56,57]. In the end, the bitcoin standard only allows basic scripts and not smart contracts [58], making it impossible to operate on the Bitcoin network the same kind of DeFi contracts available on Ethereum. In order to address the issues mentioned above, wrapped tokens issuance is necessary while an appropriate cross-chain solution is developed. However, due to their underlying mechanics, their use is still debated in dedicated forums [59].
3.3. Wrapped Tokens Issuing Mechanisms
Minting copies of bitcoin (or other crypto assets) on a non-native blockchain, such as Ethereum, is not a difficult task. The challenging part is to make those copies as accepted as the original token. First, the value of the wrapped token must be the same as the original token, and the peg must be maintained over time [12]. Second, the safety of the locked assets must be guaranteed, as well as the right to redeem the token at any time [60]. Third, the wrapping of a token must be convenient and its utility greater than holding the original token in its native chain [59]. At the moment, four means aim to provide these features.
Centralized: This method relies on one or more trusted organizations to maintain the wrapped token’s value. The third parties are in charge of providing the so-called proof of asset (PoA). The PoA proves that the locked assets are safely stored and not used in any other applications. The auditability of the locked assets must be kept over time without any access restriction, and the companies managing the protocol have to ensure that the wrapped assets can be redeemed for the corresponding assets at any time [7,16].
Trustless: Fully decentralized entities, such as decentralized autonomous organizations (DAOs), can manage the issuance of wrapped tokens. The custody of tokens is solely managed by smart contracts without any third-party intervention and any KYC requests. Being managed by on-chain smart contracts, a DAO should always ensure a transparent and censorship-resistant proof of assets [12,61].
Hybrid: This method uses both a centralized entity and smart contracts to issue wrapped tokens. A centralized entity is usually required to perform necessary tasks that smart contracts are still unable to do (e.g., KYC) or for a newly built protocol; it ensures that the smart contracts are correctly executed.
Synthetic: Minting synthetic tokens slightly differs from the previous ones, as it does not require the lock of the original asset in a trusted vault or a smart contract. In order to mint a synthetic token, the user needs to lock a number of assets of the equivalent value (or more) of the represented asset (e.g., lock USD 200 worth of SNX to mint sBTC of equivalent value). Intuitively, when the user wishes to burn the wrapped token, they will not receive the represented token back, but the provided assets instead [11]. The platforms are usually fully decentralized (e.g., KYC), and the transactions happen on the same network. Proof of assets deposited as collateral is therefore available on-chain.
These are the known methods for issuing wrapped tokens on a non-native layer one (L1) ecosystem while ensuring the peg to the original asset. Lately, however, another approach to interoperability exploits both wrapped tokens and layer two (L2) network technologies [62]. Layer two networks are ecosystems built on top of layer one (e.g., Bitcoin, Ethereum, Tron) to increase the volume of transactions and reduce transaction fees. However, L2 networks may also be built on top of multiple L1 ecosystems, allowing for indirect asset interoperability [63,64]. While the original assets are locked on their native L1 chain, their avatars can interact with each other on the common L2 network.
Every interoperability method has its advantages, as well as drawbacks, that should not be underestimated. Risks and disadvantages do not only concern the chance of technology malfunction but also threats to the decentralization concept itself. Similarly, as to how oracles reintroduce the concept of trust and centralization in decentralized ecosystems [65], the issuance of tokens managed by centralized and trusted entities also undermines ecosystem decentralization [66]. Although pegged to the same value, the chance of having an untrusted copy of a trustless token should be considered when evaluating the advantages of interoperability obtained through wrapped tokens [67].
If the reason for acquiring bitcoin is its censorship resistance, it will not be a coherent choice to acquire a censorable version of Bitcoin, even if it is interoperable. Allowing centralized entities to issue wrapped tokens means that users are entirely dependent on the intermediary to keep custody of their assets. The safe custody of the assets must be ensured for the entire time the crypto copy is used on the non-native blockchain. They should always trust the system to behave correctly. Therefore, a considerable degree of trust is constantly required to rely on those institutions and contracts.
If the system is managed by a DAO, therefore only by smart contracts, there will not be a third party to trust, but the reliability of the system is always to be verified. As already happened in the past for other smart contracts (e.g., the DAO), they can be bugged or experience malfunction [68]. In that case, although not determined by a central authority, the loss of funds is definitely possible. Hybrid solutions reduce but do not prevent both drawbacks. The presence of a central authority can ensure assistance in case of contract malfunction, and on the other hand, the automation of contracts can ensure a higher level of operational transparency. Again, the problem of centralization or bugs remains [69].
To better understand the risks and drawbacks of existing solutions, in this paper, examples of wrapped tokens issuance from the retrieved sample are analyzed. However, only active projects with reliable, complete, and trusted sources are described. All the mentioned wrapping processes are also conducted by the author and discussed. Reproducing and describing minting steps is also considered necessary to better outline the phases into which intermediaries or smart contract risks intervene.
4. Active, Wrapped Tokens Projects
4.1. Wrapped Ether (WETH)
Although counterintuitive, existing on the Ethereum network is a wrapped version of Ethereum itself called WETH. It is the first wrapped token ever created, and it became live in January 2018. Since decentralized platforms running on Ethereum use smart contracts to facilitate trades, every asset should conform to the same standardized format. This format is recognized as ERC-20. Since ether was issued before the ERC-20 format, it is not suitable for DeFi smart contracts, and for this reason, a tokenized version of ETH (WETH) was perceived as necessary [17]. In fact, ether could be used in smart contracts, but its standard does not allow easy computations with tokens of different standards. Ideally, it is like performing operations with materials of which one (ether) is liquid and unsorted, and others (ERC-20 tokens) are solid and sorted. This modification allows ether to be easily countable, traceable, and storable by smart contracts.
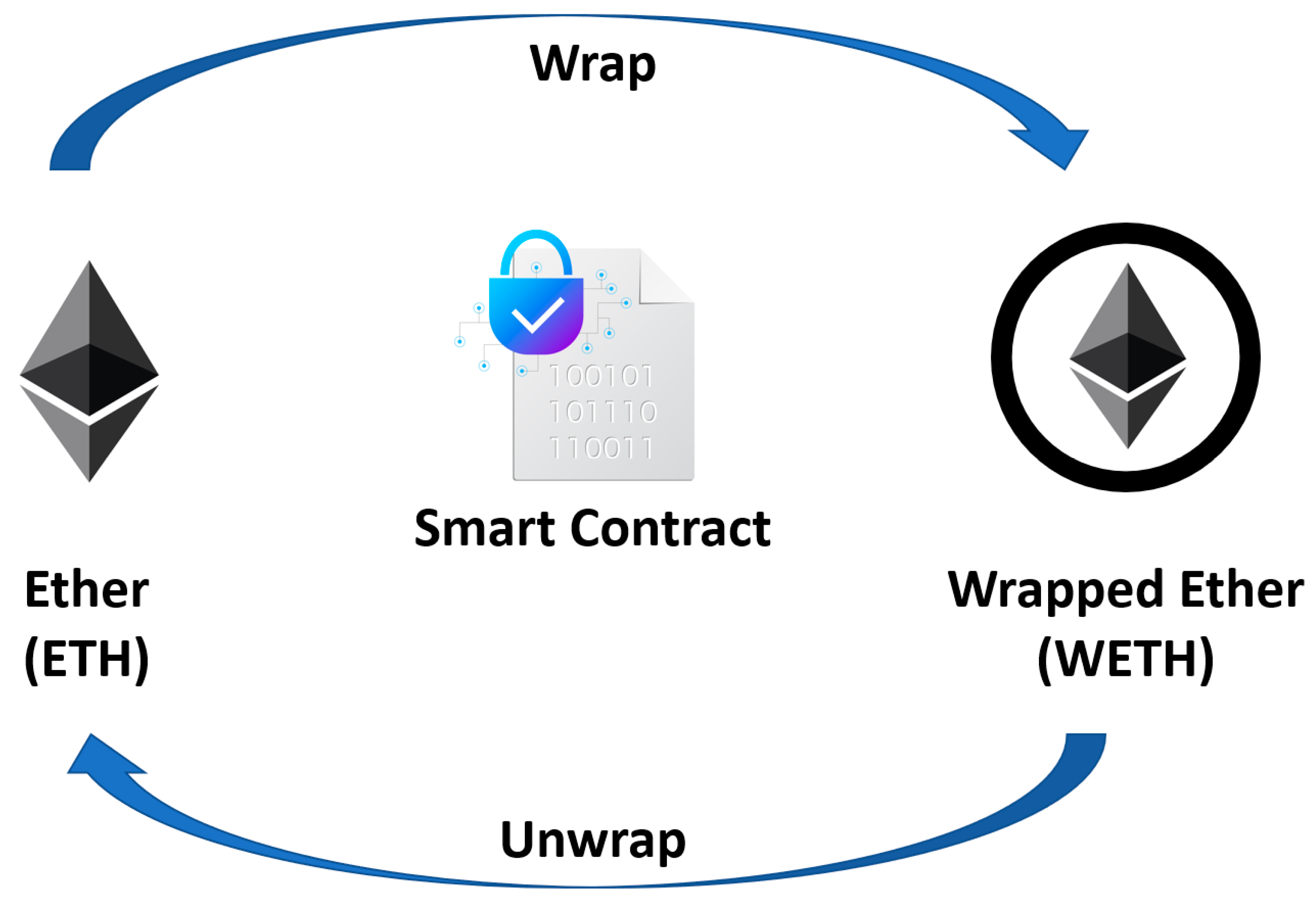
Wrapping ether in WETH is an easier procedure compared to other wrapping processes because the two cryptocurrencies belong to the same ecosystem. Therefore, no cross-chain transaction is needed. As shown in Figure 3, the process is as simple as an atomic swap [70] between Ether and WETH, which is made at 1:1 plus gas fees paid in ETH.
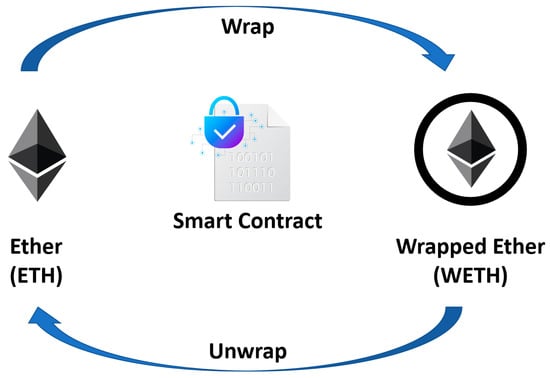
Figure 3.
WETH Minting.
Interestingly, WETH as an ERC-20 token can no longer be used to pay gas fees. When ether is wrapped into WETH, it acquires properties of ERC-20 tokens and can be used in smart contracts. At the same time, however, it loses ether properties and cannot be used as gas for transaction fees anymore. The swapped ether is then held in the smart contract, which is publicly auditable [71]. The process is completely decentralized and, unlike other wrappings, does not involve third-party trusted custodial services. Although WETH is widely used, as stated on the WETH website, “Hopefully, there is no future for WETH” [17]. There is the intention to make ether compatible with ERC-20 standards.
It is important to point out that today the acronym WETH does not refer only to the ERC-20 version of ETH. WETH also refers to wrapped ether issued on non-native blockchains; therefore, not all WETHs conform to the ERC-20 standards.
The steps to obtain WETH (ERC-20) are straightforward. Since the process is fully decentralized, no KYC is required; therefore, it is sufficient to have some ether in a non-custodial wallet (e.g., Metamask, MEW) and connect to a protocol that supports the WETH issuance smart contract (e.g., Uniswap, Sushiswap). For the purpose of this study, Metamask and both Uniswap and Sushiswap were used. The fees were negligible for both providers—in total, almost three times lower than an ERC-20 token swap but 50% higher than a simple ether transfer. Therefore, it appears to be a convenient transaction type even during network congestion. The transaction is generally executed in a few seconds (fees and congestion apart), and WETH tokens are retrievable in the non-custodial wallet when the token contract is added. The above-mentioned steps are summarized in Table 2.

Table 2.
WETH minting steps.
4.2. Wrapped Bitcoin (WBTC)
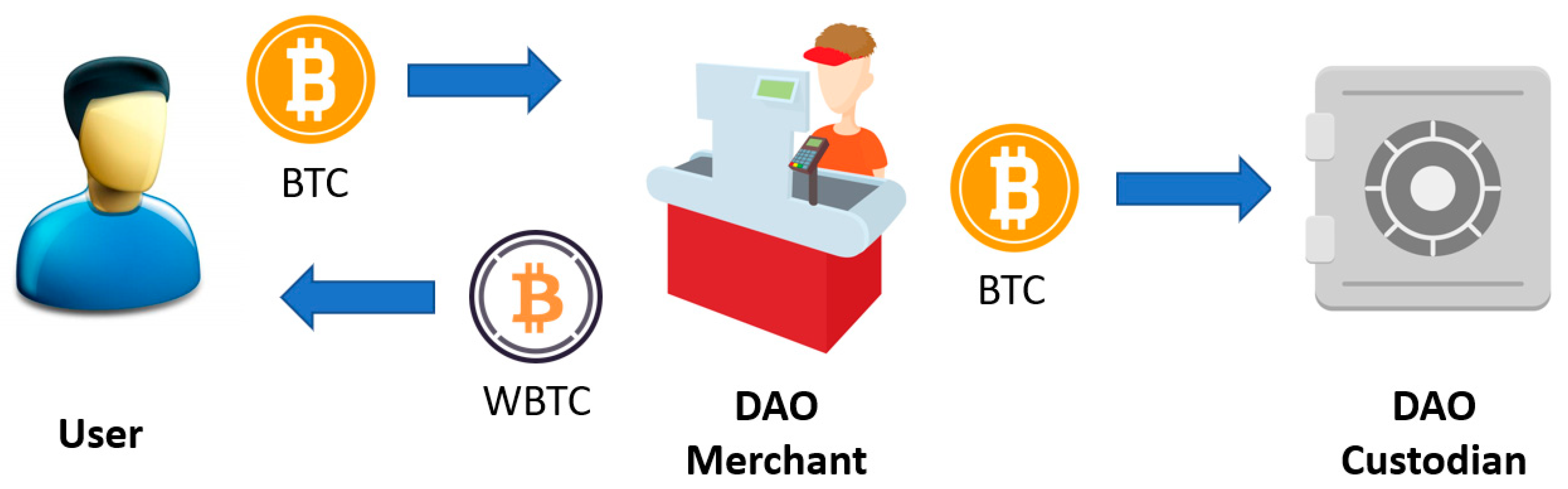
Although WETH was the first wrapped token by chronological order, the concept of wrapped tokens is associated with the announcement in late 2018 of a partnership between Kyber Network, BitGo, and Republic Protocol [72] to launch a wrapped version of bitcoin. Kyber Network is a decentralized liquidity aggregator proposing the best exchange rates from the supported DEXs, just like Skyscanner suggests the best prices for flights scanning all the supported flight companies [73]. BitGo, on the other hand, is a company specialized in custodial services for cryptocurrencies and enables institutional investments in the crypto space [74]. The Republic Protocol is a company specializing in the transaction and swap between bitcoin and tokens of the Ethereum network. It focuses on handling a large quantity of capital, also offering OTC services [60]. The three companies finally launched the WBTC project in January 2019, when the DeFi sector was still immature. However, they managed to attract USD 1 billion of collateralized assets at its launch and even USD 7 billion by May 2021 [56]. The idea promoted by those companies was to create a stablecoin pegged 1:1 at the value of a crypto asset (bitcoin in this case) that could be utilized on a non-native blockchain (Ethereum). The proposed ecosystem to handle WBTC, described in Figure 4, was composed of the following entities:

Figure 4.
WBTC issuing procedure.
Custodian. Has the task of holding and monitoring the token delivered as collateral. It is a specialized company meant to offer the highest security standards and provide all the necessary transparency to perform auditing procedures on collateralized assets [75]. The custodians perform the “wrapping and unwrapping” part of the whole process [56]. It can either be a centralized company or also a smart contract, such as in the case of WETH [46]. In the case of WBTC, the custodian role is performed by BitGo.
Merchant. It is the intermediary between the custodian and the user. For WBTC, this role was initially managed by Kyber and Republic Protocol. It receives the request from the user and delivers the collateral to the custodian. When the minting process is completed, it also delivers the wrapped token to the users. The merchant is also involved in the reverse process when receiving the burning request from the user. In that case, it handles the wrapped token to the custodian, returning the unwrapped token to the user [48]. In the case of WBTC, the merchant is also the entity in charge of executing KYC procedures.
User. It is the entity that initiates the process. It can be a private user or an institution. Given the characteristics of wrapped tokens, the scope of conversion is seen as mainly speculative. Therefore, the identification of the user by the merchant is necessary. The user then initiates the request to the merchant, which in turn involves the custodian. Essentially, to receive the wrapped token, the user must entrust his/her tokens to the merchant and pay the fees to both merchant and custodian. In case the user wishes to receive his/her token back, they must initiate the burning request and pay the fees again.
Governance. In the specific case of WBTC, the governance of the contract is managed by an “M of N” multi-signature wallet whose key owners are members of the so-called “WBTC DAO”. The governance is in charge of handling the contract and the addition and removal of custodians and merchants. All custodians and merchants are DAO members, but other institutions can also be included without a custodian or merchant role [76]. In “M of N” wallets, M is the required number of signatures to execute a transaction, and N is the total number of signatures. The values of M and N are mutually decided between WBTC DAO members, balancing security and the ease of adding/removing members [57].
Although WBTC can be acquired on centralized and decentralized exchanges, the minting process instead is not as easy as the WETH one. On the official WBTC web page, a list of providers, through which it is possible to mint WBTC, can be retrieved. Although retrieved articles claim that the issuance of WBTC is centralized [7,56], it appears that BadgerDAO (via RenVM) allows for a hybrid minting with no KYC requirements but with higher fees [60].
For the purpose of this study, Coinlist.co was randomly chosen to mint WBTC. Upon registration, KYC is required through ID and verification, which was completed in less than 24 h. It is necessary to buy or deposit BTC before minting WBTC, and then it is possible to execute the operation. The minting process is almost feeless (0.25% of total value); however, the withdrawal process from the service provider to an Ethereum non-custodial address may be expensive and slow during ETH congestion time. The minting steps are described in Table 3.

Table 3.
WBTC centralized minting.
4.3. Ren Project
The Republic Protocol (one of the WBTC DAO members) has launched the Ren Project and the RenVM to promote cross-chain interoperability [77]. While the Republic Protocol is also involved in the minting process of WBTC, the bitcoin created within the RenVM application is called RenBTC. The difference between the minting process of WBTC and RenBTC is that the latter is entirely automated, and users can directly bridge their crypto to a different blockchain (e.g., Ethereum, BinanceSmartChain) without performing KYC procedures. Furthermore, at the time of writing this study, WBTC is only available on the Ethereum network, while RenBTC is available on multiple networks. Assets are sent to the custodian’s address, and the smart contract handles all the processes, as well as the fees. The minted wrapped assets are then delivered to the user address corresponding to the destination ecosystem. The RenVM smart contract automates the role of the merchant and the custodian. While an automated user interface automates the merchant role, the custodian role is performed by “darknodes”, a network of stakers who also perform required computations in exchange for rewards [78,79]. It is important to note that although WBTC and RenBTC are representations of the same token (BTC), which is fungible in principle, the difference in the name with respect to WBTC plays a crucial role. By the time the user has his/her assets wrapped on the designed network, he/she acquires the right to invest them and to trade them for other tokens. However, selling a WBTC does not have the same meaning as selling a BTC. What a holder of WBTC transfers by selling the token is the right to redeem the locked token for the same amount of owned wrapped tokens. We recall that the ability to redeem the locked asset is the reason why the wrapped token maintains the value of the represented asset. Therefore, since the locked token may be in the “custody” of a different entity, it is vital to distinguish those by naming them differently to ensure their non-fungibility. WBTC, for example, cannot be redeemed through the RenVM (except for those minted on BadgerDAO), since they do not have the corresponding tokens in their custody.
Minting RenBTC was slightly different than WBTC. As a fully decentralized process, it requires connecting a non-custodial wallet to the RenVM, selecting the amount of BTC to convert and the destination network. Then the amount has to be sent to the “unique” gateway address generated by the RenVM and pay the fees. The fees for minting Ren Tokens are shared between RenVM dev, Darknodes, provenance chain miners, and destination chain miners.
The process, however, resulted in being expensive due to the high Ethereum gas fees. Selecting another network, such as BSC, would have drastically reduced the total cost. At the time of operating (17/11/2021 17:55 GMT+1), the total cost was USD 6 for BSC and USD 88 for Ethereum. Furthermore, due to the BTC network block time, the delivery of RenBTC to the wallet took a bit more than one hour. Since it mainly depends on the BTC network block-time, the delivery time is almost the same for every destination network selected. Bridging another asset, such as DigiBite, resulted in a delivery time of roughly 15 min. The RenBTC minting steps are summarized in Table 4.

Table 4.
RenBTC minting.
Following the ren Project, other companies such as Binance [80] launched their bridge to facilitate blockchain interoperability (however, it was terminated on 25 November 2021). The Binance bridge, for example, works very similarly to RenVM, pointing, however, to different ecosystems (BinanceSmartChain, Ethereum, Tron) [39]. Above using a decentralized bridge, users can also acquire wrapped tokens directly from exchanges (e.g., Binance), withdrawing them to a non-native platform supported by the exchange. There are, however, two consequences to consider when using this feature from a centralized exchange. Being KYC mandatory on centralized exchanges, wrapped tokens will not be acquired privately. Second, if wrapped tokens are obtained from an exchange, the existence of a corresponding locked asset should be guaranteed from a publicly auditable address showing proof-of-assets [81,82].
4.4. Synthetic Tokens and sBTC
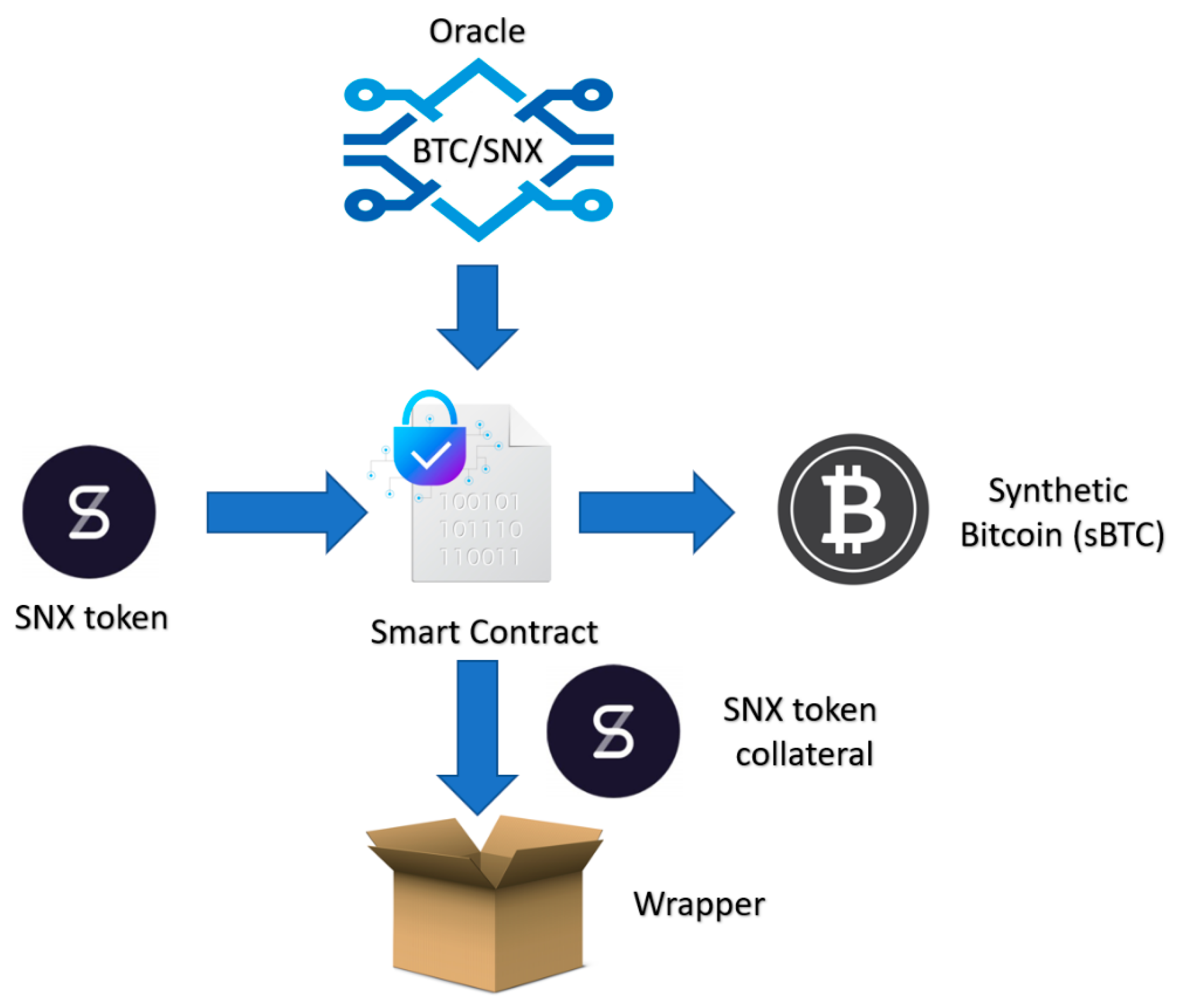
A synthetic token is conceptually different from a wrapped token, although it may have the same standard (ERC-20) and generally the same price. The synthetic Bitcoin is, for example, a derivative of the original token; therefore, its only function is to speculate on its price. We recall that a derivative is an asset that derives its value from an underlying asset or index [83]. Unlike the wrapped token, a synthetic token cannot be redeemed for the original token since no original token was locked to mint the synthetic version. However, the mechanism to issue a synthetic token, such as sBTC, is similar to wrapped tokens’ issuance, in particular to the DAI/USD-J Stablecoin. For example, on the Synthetix platform (before the 2019 Vega update), to mint sBTC, 800% of the minted asset had to be deposited in SNX token as collateral (Figure 5) [10,84]. An oracle service is queried to obtain the BTC/SNX exchange rate, which, in the case of Synthetix, is Chainlink [85]. The collateral is then returned when the user returns the sBTC, which is consequently burnt. It is also possible to acquire a short position on sBTC depositing collateral in sUSD. In that case, however, the fluctuation in the sBTC price will affect the deposited collateral. Therefore, the quantity of sUSD redeemed will differ from the provided amount (-fees).
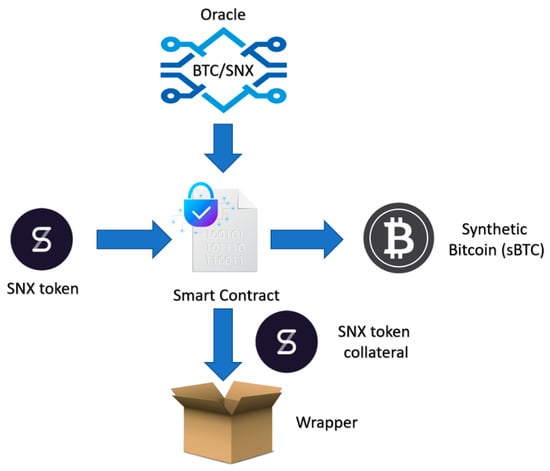
Figure 5.
Synthetic BTC minting.
The advantage of acquiring and utilizing synthetic tokens is that the process is entirely trustless and automated. Unlike the minting process for WBTC and RenBTC, the issuance of sBTC does not involve a custodian that locks the crypto on a different chain. The process is automated by the smart contract and involves already interoperable assets. In this sense, the issuance of sBTC is more similar to the issuance of WETH.
Obtaining sBTC is, however, not as intuitive as WBTC and RenBTC. It requires familiarity with derivative platforms, such as Synthetix/Mintr, and considerable capital to lock as collateral. Unfortunately, private users cannot mint synths, other than sUSD, and trade them outside the Synthetix network after the Vega update. Therefore, at the time of writing the paper, all the passages to mint sBTC could not be repeated. Synths’ minting functionality was removed since it was not possible to prevent frontrunners from exploiting oracle price updates [84]. Essentially, frontrunner bots detecting a not-yet-updated price change could mint synths and immediately burn them after the oracle price update. Since an effective method to prevent this kind of oracle manipulation still does not exist [29], the minting functionality was removed. Furthermore, the fact that the original token was not locked to mint the synthetic assets made those kinds of tokens not as accepted as the wrapped versions [20]. Therefore, although the synthetic token was not different from the wrapped token in its functionalities and standards, their acceptance was minimal. At the time of writing this paper, it is only possible to interact with sBTC on dedicated platforms where only buy, sell, and short functions are enabled. Table 5 summarizes the former steps to obtain sBTC. Due to the complexity of the contract, the minting of synths compared to other wrapped tokens is also quite costly.

Table 5.
Minting sBTC process (before VEGA update) *.
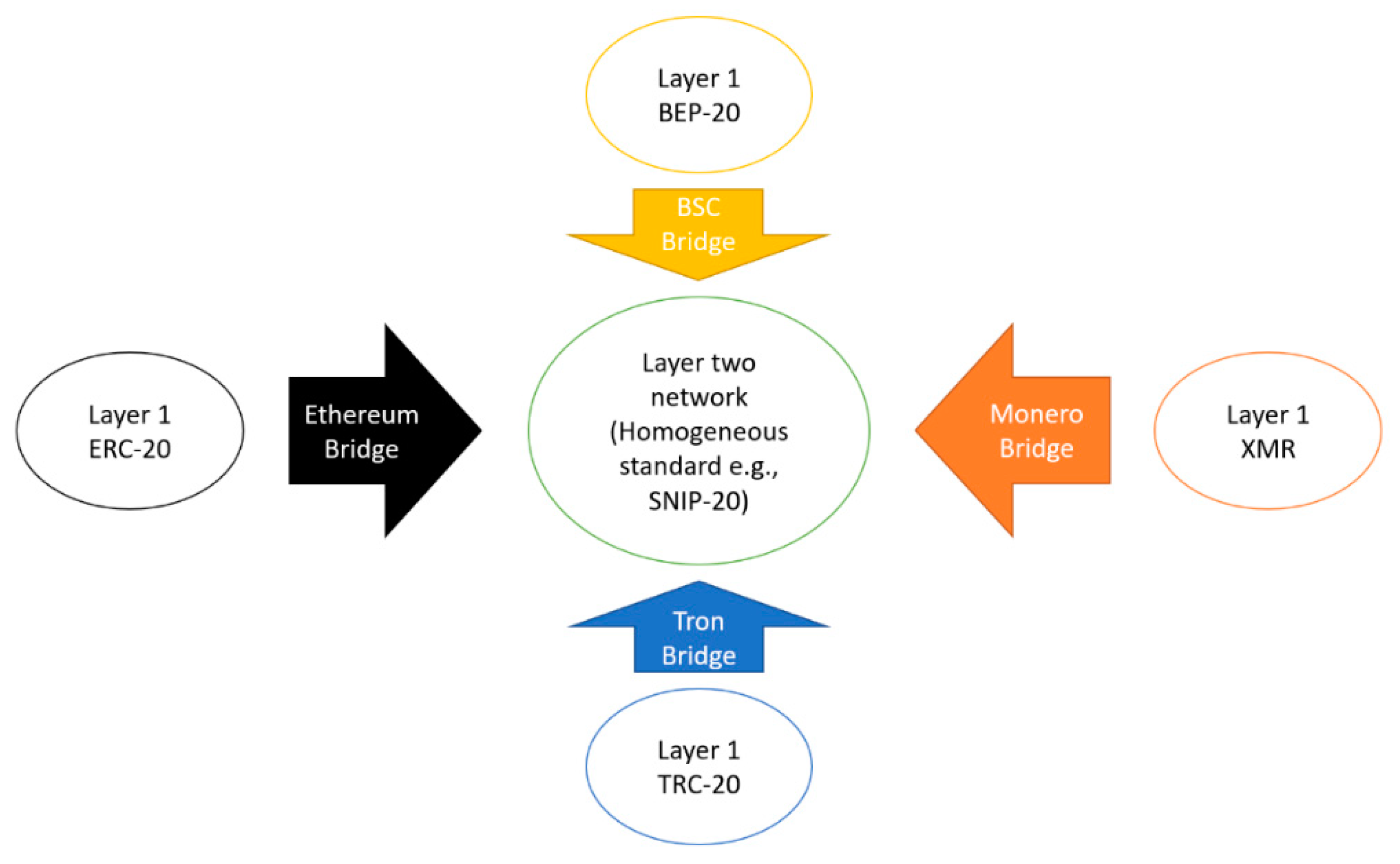
4.5. Secret Network
Since the creation of Bitcoin, the cryptocurrency world has had the task of balancing privacy and transparency. As blockchains are mostly public, we are witnessing the rise of firms specializing in auditing blockchain transactions. They aim to discover the owner of addresses and the motives of transactions. Due to that increasing lack of privacy, in 2014, the Enigma project was founded to provide privacy to smart contracts on Ethereum. In 2020, Enigma launched its main-net with the name Secret Network [86]. The Secret Network is based on Cosmos SDK, so it has the same consensus mechanism (delegated proof of stake) and the same block-time (6–7 s). Similar to the Binance chain, it consists of two parallel ecosystems, of which one is public and one is private. The public ecosystem is mainly used to transfer and stake SCRT native tokens. The private ecosystem is used for privacy-preserving applications developed on their protocol and to transact secret tokens (tokens with SNIP standards). An interesting feature of the Secret Network is the implementation of a bridge very similar to the RenVM to enable interoperability between different ecosystems [87]. Instead of just wrapping tokens to be usable in another ecosystem, the Secret Network empowers dedicated two-layer ecosystems where all wrapped tokens can interact (Figure 6).
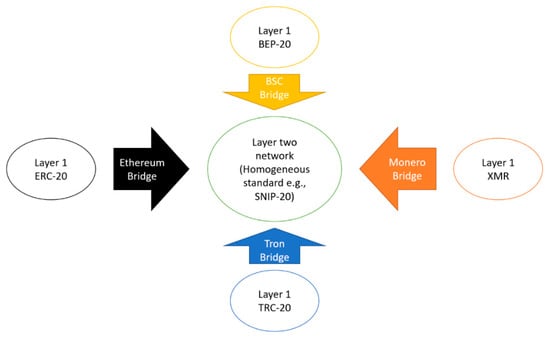
Figure 6.
Interoperable two-layer networks (e.g., Secret Network, BitTorrentChain).
Unlike RenVM, the secret bridge directly connects wallets supporting separate ecosystems (e.g., Ethereum and Secret). The users select the token to bridge, and once the process is complete, a snip-20 version of the locked token is minted on the Secret Network. The original token is locked in a smart contract on its native platform, and the bridge should ensure its safety and auditability. Although tokens coming from different bridges can interact together and be inserted in liquidity pools, those such as sETH and sETH(BSC) are non-fungible. This means that although both representations of the same token (ether), with the same standard and on the same platform, since they are coming from Ethereum and BSC, they cannot be merged in the same escrow. As already explained for WBTC and RenBTC, this feature is crucial to prevent a token native of the Ethereum chain, for example, from being unwrapped in another chain by mistake [21].
Migrating tokens to Secret Network layer two was very intuitive. However, instead of requiring one non-custodial wallet, it requires two. The first, usually Metamask, needs to be synchronized to the provenance network of the tokens to be bridged. The second, usually Keplr, should instead be set to the “secret” destination network. Currently, it does not support the BTC network; therefore, WBTC or RenBTC should be acquired prior to using BTC on the Secret Network. Bridge fees are comparable to an ERC-20 transfer, but since a direct BTC bridge is not supported, the cost of acquiring WBTC or RenBTC must be taken into account. Table 6 summarizes the Secret Network wrapping steps.

Table 6.
Minting sWBTC (Snip-20) on the Secret Network.
5. Discussion
The following discussion is based both on the reviewed material and on the experience made exploring the protocols while repeating the described minting steps. To facilitate the analysis, a comparison between different wrapped versions of BTC is provided. As a fully decentralized alternative of BTC is still not available, WETH is discussed instead. Again, mentioning specific active protocols is solely due to the availability of material and to provide more practical examples of different wrapping techniques. First, a discussion on minting, complexity, and cost is given, also providing an overview of the overall acceptance of the wrapped token. Then, an analysis of the risks and consequences of wrapping tokens is provided, also discussing their impact on decentralization. Finally, a discussion on the interoperability obtained with these wrapping techniques is provided, listing the advantages and disadvantages of each method.
5.1. Ease of Use, Costs, and Acceptance
As mentioned above, there are many available methods for minting wrapped tokens. Apart from synthetic ones, removed in 2019, there are still centralized, decentralized, and hybrid solutions [61]. Since synthetic token minting (except for sUSD) was removed due to oracle manipulation and scarce acceptance [84], it is arguable that those may be reintroduced at a later time if an effective solution to frontrunning is found. Furthermore, as they are still available in dedicated platforms, such as Kwenta or Curve, their acceptance may also increase [83]. Concerning costs, at least on Ethereum, synthetic minting is still too expensive when compared to centralized, decentralized, and hybrid minting. Furthermore, the need for a considerable collateralization ratio (400–800%) makes synthetic solutions further unfeasible. The over-collateralization and inability to redeem the original assets also make their trading and acceptance outside derivative platforms very unlikely [59]. Even if the sale of the synth were convenient, the issue of recovering locked collateral would still constitute a deterrent. Moreover, the lending and borrowing features are mostly unavailable due to the scarce acceptance [10]. Finally, as described in the related section, the minting process requires specific knowledge of derivative platforms and functioning.
On the other hand, centralized solutions, such as WBTC or hBTC, appear to be the most used and accepted alternative of a wrapped token [13]. Although WBTC issuance has always been centralized, there is lately a hybrid alternative, thanks to which it is possible to avoid KYC in exchange for higher minting costs. Unlike synthetic BTC, WBTC sale, lending, and borrowing are accepted in almost all of the most prominent exchanges and Ethereum DeFi applications (Aave, Compound, Maker, Uniswap, Sushiswap, and so on.) [56,88].
Hybrid alternatives, such as RenBTC, instead have the advantage of being interoperable upon multiple chains (BSC, Polygon, Solana, Avalanche). However, unlike WBTC, it is less accepted in DeFi protocols, at least on Ethereum [89]. Main DeFi projects such as Aave, Maker, and Compound do not support tokens wrapped on RenVM. Although they are used for swap and liquidity pools, they are probably not yet trusted enough for being lent or held as collateral. However, its minting cost is very low and mostly depends on the destination network. Compared to WBTC, however, it requires a bit more familiarity with decentralized applications and gateway notions.
Layer two solutions have many advantages but also drawbacks. Minting tokens on an L2 network is a bit more difficult than using a hybrid solution, but it has lower costs. However, requiring familiarity with non-custodial wallets and bridge applications, it can be more complex and expensive than centralized solutions. It must be said that the overall acceptance of L2 solutions is minimal, and it is limited to the L2 ecosystem itself. Therefore, if no applications are built on the dedicated ecosystem, there is no means of exploiting the wrapped tokens [90]. The acceptance and value of L2 solutions strictly depend on the network’s magnitude (in terms of users).
Finally, WETH (erc-20) appears to be the only fully decentralized wrapped token with low minting costs and complexity. It is always accepted for token swaps on Ethereum but is not available outside its network [17]. For example, the token called wETH on the polygon network is not the same decentralized token as WETH (ERC-20). It is issued on a separate platform with a hybrid mechanism, reflecting the hybrid wrapped tokens’ properties. Table 7 summarizes the main technical differences for wrapped token types. Due to the volatility of gas prices, costs are expressed in order of magnitude according to the Etherscan Gas Tracker table [91]. Furthermore, only Ethereum gas costs are considered since other minting fees are almost always negligible. Appendix B provides instead an overview of minting costs expressed in terms of Ether and Gwei.

Table 7.
Ease of use, acceptance, and cost of wrapping alternatives.
5.2. Risks and Concerns of Wrapping Tokens
The need for wrapped tokens is justified by the inability of blockchains to directly communicate with each other; wrapped tokens overcome the lack of interoperability [1]. As described, the mean of minting wrapped tokens is very similar to that of minting stablecoins. Unlike custodial stablecoins, however, minting is initiated by the users and not by institutions. On the other hand, they cannot be considered similar to non-custodial stablecoins due to the centralized nature of custodians [33]. The utilization of custodians is a very debated concept in crypto space. As a matter of fact, the whole idea of decentralization and DeFi should involve the ability of users to have complete control of their assets without involving trusted third parties and without KYC requirements [22]. Due to AML reasons, custodians of crypto assets are obliged (through merchants) to request KYC from users depositing collateral. Therefore, the process of minting some of the wrapped tokens cannot be initiated without a KYC. As centralized entities, custodial activity is subject to regulation and may also be ceased or censored [16,57,92]. Acquiring WBTC means giving up to the pseudonymity of BTC and its uncensorship features while operating under different security standards. If a bitcoin belonging to a black-listed user is frozen or censored by the custodian service upon request of the authority, its corresponding avatar would probably lose its value.
Users also have the choice of acquiring wrapped tokens privately on a decentralized exchange without submitting KYC procedures. However, as explained, the intrinsic value of the wrapped token lies in the right to redeem the corresponding locked asset. Therefore, although the token may have been acquired privately, KYC procedures cannot be avoided at the moment of token redemption. If, in order to redeem WBTC, the user has to undertake the KYC procedure, the benefits of privacy given by the blockchain technology are forfeited. Projects such as Binance Bridge and RenVM do not require KYC when redeeming tokens [39]. However, as RenVM terms and conditions state, regulations may always change procedures or even delete some [92]. This condition means that although the contract is trustless and decentralized, the company managing the protocol may be ceased or be obliged to change some function at any time due to regulatory hurdles. Furthermore, although RenVM claims to be trustless and decentralized, online resources label it as a hybrid solution [13,78]. Since a restricted number of DarkNodes manages the protocol, and the contract is not open source and not “fully-audited”, its trustless and decentralized nature is still debated [78]. According to DefiPulse, the only decentralized wrapped token mechanism is the one implemented by tBTC. However, since relying on a third-party oracle for the collateral price and being still at the “alpha” stage, its reliability and acceptance, in the long run, are yet to be proven. Among those discussed in the present article, the only wrapped tokens with a trustless minting service appear to be WETH (erc-20), synthetic tokens, and layer two solutions, such as Secret Network [20,87].
As already explained, the issuance of synthetic tokens is very similar to wrapped tokens. However, they are often not considered as such. Wrapped tokens ensure that the circulation of a specific token remains the same regardless of the chain on which it is operating. This means that if a WBTC is being lent on Ethereum, a BTC is contextually being frozen on the Bitcoin blockchain. This mechanism ensures that the total supply of BTC remains the same and the price of both assets is safeguarded. For synthetic assets, however, this condition does not hold. As an example, synthetic bitcoin operating on Ethereum does not have a counterparty locked on the Bitcoin network, de facto altering the total supply of BTC. This may be a reason why synthetic tokens may never operate outside their dedicated network. Another important aspect to consider, which is rarely discussed, is the smart contract reliance on external oracle services [93]. Since the locked token is not the same as the synthetic token, an oracle service must be queried to obtain the token’s exchange rates. As discussed in many papers, those oracle services are often centralized entities prone to malfunction and manipulation [29,85]. Therefore, even if the synthetic contract is trustless and automated, the reliance on a third-party service constitutes a single point of failure.
Layer two networks are an interesting approach to interoperability, but, as also stated in the Secret Network F.A.Q., using a layer two network is not free of risks. Being smaller networks compared to Ethereum or Bitcoin, they are more subject to attacks or the unavailability of nodes [94]. In the case of network failures, there is a chance of losing all tokens locked in the bridge [95]. Above the smart contract risk, there is also the chance that the bridge operators collude to move the funds locked to create the wrapped tokens. In a hybrid solution, such as RenVM, although smart contracts automate the merchant role, the custodian role is entrusted to an oligopoly of trusted operators. As broadly explained in dedicated papers and books, as the locked assets’ value increases, the higher the incentive to collude [96]. Therefore, the importance of trust in the operators may increase proportionally to the total value locked.
WETH (erc-20) comprises assets that present fewer issues related to trust, privacy, and smart contract risks. Its utility, however, only lies in its standard; therefore, it may completely lose its usefulness in the near future. Table 8 summarizes the trust and smart contract concerns, as well as possible workarounds for the discussed wrapping solutions.

Table 8.
Wrapping concerns, outcomes, and possible solutions.
In the end, it is arguable that unlike bitcoin or dash, which can be considered decentralized currencies, a wrapped token is mainly issued and managed by organizations that “guarantee” their value and reconvertibility to the former token. The trust to put in the token issuer and the token itself is then strictly related to the specific mechanism undertaken to mint the token, which varies according to the issuing company/authority [97,98]. Therefore, if a considerable number of assets are stored by centralized, custodial entities, the entire nature of the protocol would change. If Bitcoin is decentralized, but centralized custodians hold the majority of tokens, it cannot be considered a decentralized network anymore [99]. In this regard, even Vitalik Buterin showed his concerns in a recent tweet, writing, “I’m worried about the trust models of some of these tokens. It would be sad if there ends up being $5b of BTC on Ethereum and the keys are held by a single institution” [100]. Moreover, since miners/stakers are rewarded for processing transactions on the layer one network, and this incentive mechanism is what makes networks secure, having a considerable amount of tokens wrapped may constitute a threat for the network itself. If a bitcoin is wrapped and its avatar is spent on a secondary network, the transaction fees are spent only in the secondary network. Then, being a decentralized network maintained only by the fees and rewards, a drastic reduction in fees may eventually cause the network to collapse.
5.3. Evaluation of Interoperability Features
Although wrapped tokens are a solution to interoperability issues, it is important to discuss if this purpose is effectively fulfilled (Table 9). In this regard, it must be said that although synths can represent assets of any type and from any network, they are not interoperable with each other. Synths are tokens that live in their ecosystems. They cannot be minted by users (due to the Vega update) and cannot perform any particular operation above what is allowed by the protocol (buy, sell, short) [84]. Therefore, at present, they do not seem to cover any interoperability purposes. ERC-20 WETH, although being the cheapest, trusted, and most risk-free wrapped token, cannot be considered an interoperability solution. As its only purpose is to make ether ERC-20 compliant, it is more like a temporary workaround for the Ethereum heterogenous standard issue [101]. Since it is unable to perform cross-chain transfers, its technology will probably soon become obsolete [17].

Table 9.
Interoperability approach/expectation.
The approach implemented by the Secret Network is lately being seen in other ecosystems, such as Tron, with the launch of BitTorrentChain [14]. Their idea is essentially to create a layer two environment in which all tokens have the same standard and can interact together. If this approach, on the one hand, enables interoperability, it has considerable limitations on the other. First, as a stand-alone environment, it is not compatible with all the most prominent applications in the DeFi space based on Ethereum. The company and partners are developing their own applications, which at the moment constitute less than 0.07% of the total capital invested in DeFi [13]. Convincing investors to switch from their trusted platform to a newly built one may not be an easy task. Second, the availability of wrapped assets is subject to the development of bridges. A direct bridge with the Bitcoin network, for example, is still not available (although under development); therefore, it is not possible to directly interact with bitcoin on the Secret Network. A direct bridge is, in fact, only available between networks and tokens that are smart contract-friendly; therefore, Bitcoin (at the moment) is not compatible with any available solution of this type (e.g., BitTorrentChain) [14]. However, it is possible to bridge WBTC and RenBTC from the Ethereum network. This option would mean wrapping the original token (bitcoin) twice (e.g., sWBTC). Therefore, the bridging of BTC on L2 would not be possible if other wrapping techniques were not available. As one of the main purposes of interoperability is to bring bitcoin liquidity to DeFi smart contracts, layer two approaches cannot be considered a complete solution. Lastly, as the application’s utility is strictly dependent on its user base—the interoperability is only a result of its network effect. With this approach, layer one networks remain de facto disconnected [90].
WBTC, as the first and most widespread solution to bring bitcoin to the Ethereum network, given the market cap [13], is probably also considered the most effective. Once deployed, WBTC is practically equal to an ERC-20 token; however, it is limited to interacting with tokens with the same standard. Therefore, its interoperability starts and ends within the Ethereum network boundaries. Since its launch, changes in the Ethereum network have made its minting and operating costs inconvenient. Moreover, with the rise in solid layer one alternative to Ethereum, such as BSC, Solana, Avalanche, and Polygon, WBTC could soon end up being an obsolete technology [7,19].
Given the KYC requirements necessary for a centralized provider, wrapping/unwrapping cost, and transaction time, hypothesizing a stable flow of assets between the two chains is also very unlikely with this solution.
Lastly, the RenVM hybrid approach to interoperability needs to be discussed. It supports few assets, but unlike the solutions mentioned above, it enables transfers to multiple layer one ecosystems [77]. Since it directly connects two separate chains, it does not require dedicated two-layer networks with ad-hoc applications and standards. As long as protocols support Ren tokens, those are fully interoperable with native ones. Being decentralized, no KYC is required, and the token transfer is then private, quick, and automated. However, the existing problem is that the transfer of tokens between two non-native ecosystems must be performed manually. For example, if BTC is converted in RenBTC on Ethereum and those need to be transferred to Solana, the user cannot directly operate the transfer. It is necessary first to unwrap RenBTC to BTC and then to rewrap those to the requested network, resulting in high fees and a slow transaction time. Ren developers, however, have recently announced the launch of RenJS v3 and the so-called Host-to-Host (h2h) technology [102]. With the h2h, tokens would be quickly, directly, and cheaply transferred between non-native chains, de facto “jumping” the unwrapping/rewrapping passage. This improvement may constitute a revolution in cross-chain interoperability. However, as it is still not an active feature, it is hard to predict if it will operate as intended. Moreover, requiring substantial changes to the protocol, a new evaluation of its security and reliability will be required.
6. Conclusions
The scope of this paper was to undertake a study on wrapped tokens to highlight the advantages and drawbacks of the available alternatives. Wrapped tokens are a practical solution for cross-chain communication and interoperability [89]. They also enable faster and more accessible options for transactions when a particular blockchain is experiencing delays or high fees. Allowing the use of tokens over a non-native blockchain can constitute an effective solution to bring liquidity to the developing DeFi space [10]. Reducing transaction costs and speed can enable the microtransactions that were initially doable at the birth of blockchain and soon became unmanageable due to congestions and transaction fees. However, there are drawbacks to consider when interacting with these tokens that mainly concern the entities involved in their creation. Custodians, whose role is essential to keep the tokens locked, are centralized entities subject to audits and regulations. If, on the one hand, this guarantees their trustworthiness, on the other hand, the pressure of regulation may alter the proposed service or even censor transactions. Other wrapped tokens may work without a centralized custodian or merchant. Their role is de facto replaced by a smart contract or virtual machine. Although decentralized, their use is not risk-free since smart contracts are not exempt from errors and bugs [103].
Although the promise of wrapped tokens is to reduce fees, the truth is that this is not guaranteed. Wrapping bitcoin to Ethereum would result first in high minting costs, and then transactions would be subject to Ethereum fees that are not always lower than the bitcoin ones [16]. Therefore, switching chains regularly to reduce transaction costs does not seem to be a convenient option. Nevertheless, a wrapped version of a coin is not that coin—it is another cryptocurrency entirely. Therefore, most of their native functionalities are forfeited. For example, some passive income platforms do not accept wrapped tokens, and neither do some exchanges and wallets. As explained, although counterintuitive, it is not possible to pay gas fees with WETH on the Ethereum network even if it is a wrapped version of ether [89].
As for the currently available technology, wrapped tokens cannot be used for true cross-chain transactions [61,104]. The examples discussed in this paper show that the offered proposals constitute a mere workaround to the problem and not a definitive solution. In every case, there are some features to give up in exchange for interoperability. While WBTC needs trust over custodians, RenBTC as a hybrid system is eventually subject to smart contract risks and regulatory pressures. Synthetic solutions are often debated for their price peg and their impact on the market. On the other hand, layer two solutions, such as the Secret Network, require trust in a different network with different security standards and applications. An interesting approach to layer one interoperability with wrapped tokens seems to be the host-to-host feature developed by Ren, which, however, is still not available [102].
With respect to other studies on interoperability, this one takes a user perspective and aims to shed light on the actual usefulness of wrapped tokens alternatives. Therefore, it is intended to contribute to academic literature but also be exploitable by practitioners to obtain a broad overview of different wrapping procedure advantages and drawbacks. However, limitations arose from that choice since the availability of resources undertaking a similar approach was extremely limited. Furthermore, as a single author study, the overall analysis and resource selection criteria may have been biased by the author’s personal background.
The shared opinion is that the use of the wrapped token is temporary, and it will probably be abandoned when a proper cross-chain solution is discovered [49]. Since it is uncertain when and if full interoperability between blockchains will be reached, further studies comparing emerging cross-chain protocols with the already operating ones could be helpful to better understand their development and potential.
Funding
This research was funded by the Emma Gianesini Fund, managed by the UniCredit Foundation.
Data Availability Statement
Data is contained within the article or supplementary material.
Conflicts of Interest
The author declares no conflict of interest.
Appendix A
The following table provides a sample of the retrieved gray literature articles sorted according to the reliability criteria described in Section 2.

Table A1.
Source/reliability.
Table A1.
Source/reliability.
| Reliability | Source Name | Author/s | Title | Reference |
|---|---|---|---|---|
| A | wbtc.network | Kyber Network BitGo Inc. Republic Protocol | Wrapped Tokens A multi-institutional framework for tokenizing any asset | [57] |
| A | Weth.io | Radar Relay Inc. 2021 | WTF IS WETH? | [17] |
| A | Renproject.io | Zhang, T. Wang, L. | Republic Protocol A decentralized dark pool exchange providing atomic swaps for Ethereum-based assets and Bitcoin | [77] |
| A | U.Today | Dovbnya, A | Vitalik Buterin Worried About ‘Trust Models’ of Some Bitcoin-Backed Ethereum Tokens | [100] |
| B | Bitrates | Banov, M. | Wrapped Tokens, Crypto-Derivatives and Candidate Ethereum Standards (ERCs). | [101] |
| B | The Cryptonomist | Cavicchioli, M. | What are the so-called wrapped bitcoin? | [98] |
| B | Cointelegraph.com | Kuznetsov, N. | Wrapped Crypto Tokens, Explained | [76] |
| B | Shrimpy Academy | The Shrimpy Team | What Are Wrapped Tokens? | [72] |
| C | NiceHash | Tarman, M. | What is Wrapped Bitcoin? | [67] |
| C | BSC NEWS | Wilfred, V. | cryptonomics-wrapped-tokens-explained | [12] |
| C | The Chain Bulletin | Andreychev, A. | Binance Introduces Wrapped Tokens For Ethereum | [80] |
| C | CoinsCapture | Ghag, S. | Wrapped Tokens-Explained | [69] |
| D | Publish0x | Gongo | Wrapped Tokens Explained | [75] |
| D | Phemex | Tang, N. | Wrapped Tokens: Wrap Your Head Around These New Crypto Tokens | [34] |
| D | The Motley Fool | Sun, Z. | What Are Wrapped Tokens? | [88] |
| D | Cryptopedia | Cryptopedia Staff | wBTC: What Can You Do with Wrapped Bitcoin? | [43] |
Appendix B
The following table provides an overview of Ethereum gas costs (expressed in Ether and Gwei) required to mint wrapped tokens. Other minting fees are omitted for being irrelevant or proportional to the wrapped amount.

| Wrapped Token | Gas Price * (Gwei) | Total Cost (Ether) | Transaction Description | Platform |
|---|---|---|---|---|
| WETH (ERC-20) | 96 | 0.004 | Wrapping Ether into WETH | SushiSwap |
| sWBTC | 89 | 0.005 | Bridge WBTC to secret network | Secret Bridge |
| WBTC | 75 | 0.01 | Bridge BTC to Ethereum (centralized) | Coinlist.co |
| WBTC | 107 | 0.076 | Bridge BTC to Ethereum (Hybrid) | BadgerDao |
| RenBTC | 89 | 0.019 | Mint RenBTC (erc-20) once received by RenVM | Renproject Bridge |
| sUSD ** | 90 | 0.05 | Mint sUSD, depositing SNX as collateral | Synthetix |
* Gas price for a standard transaction at the time of data collection, with an Ether mean price of $4312.40. ** Arguably, the sUSD minting price should be the same as for sBTC (before Vega update).
References
- Larsen, A. A Primer on Blockchain Interoperability. Available online: https://medium.com/blockchain-capital-blog/a-primer-on-blockchain-interoperability-e132bab805b (accessed on 9 December 2019).
- Tasca, P.; Tessone, C.J. A Taxonomy of Blockchain Technologies: Principles of Identification and Classification. Ledger 2019, 4, 140. [Google Scholar] [CrossRef]
- Hardjono, T.; Lipton, A.; Pentland, A. Towards a Design Philosophy for Interoperable Blockchain Systems. arXiv 2018, arXiv:1805.05934. [Google Scholar]
- The European Union Blockchain Observatory and Forum. Central Bank Digital Currencies and a Euro for the Future; The European Union Blockchain Observatory and Forum: Brussels, Belgium, 2021. [Google Scholar]
- Pang, Y. A New Consensus Protocol for Blockchain Interoperability Architecture. IEEE Access 2020, 8, 153719–153730. [Google Scholar] [CrossRef]
- Hardjono, T.; Lipton, A.; Pentland, A. Toward an Interoperability Architecture for Blockchain Autonomous Systems. IEEE Trans. Eng. Manag. 2020, 67, 1298–1309. [Google Scholar] [CrossRef]
- Imsicoinexc. What Is a Wrapped Token? What Does WBTC Do? Available online: https://coinexc.com/2021/05/26/what-is-a-wrapped-token-what-does-wbtc-do/ (accessed on 21 August 2021).
- Borkowski, M.; Sigwart, M.; Frauenthaler, P.; Hukkinen, T.; Schulte, S. Dextt: Deterministic Cross-Blockchain Token Transfers. IEEE Access 2019, 7, 111030–111042. [Google Scholar] [CrossRef]
- Lafourcade, P.; Lombard-Platet, M. About blockchain interoperability. Inf. Process. Lett. 2020, 161, 105976. [Google Scholar] [CrossRef]
- Beck, J. How Wrapped Tokens Bring More Liquidity to DeFi. Available online: https://consensys.net/blog/codefi/put-your-bitcoin-to-work-on-ethereum/ (accessed on 12 August 2021).
- LEDU. What Is a Wrapped Token? Available online: https://ledu.education-ecosystem.com/what-is-a-wrapped-token/ (accessed on 31 August 2021).
- Wilfred, V. Wrapped Tokens Explained. Available online: https://www.bsc.news/post/cryptonomics-wrapped-tokens-explained (accessed on 30 August 2021).
- DefiPulse. Bitcoin At Work. Available online: https://defipulse.com/btc (accessed on 10 September 2021).
- Tron BitTorrent-Chain Whitepaper 1 Introduction. Available online: https://tron.network/static/doc/BitTorrent-ChainWhitepaper_EN.pdf (accessed on 13 September 2021).
- Behrens, A. Wrapped ETH Comes to Tezos as It Takes on Ethereum DeFi Market. Available online: https://decrypt.co/51860/wrapped-eth-comes-to-tezos-as-it-takes-on-ethereum-defi-market (accessed on 4 September 2021).
- Santiago, S. Wrapped Tokens: A Tool to Jump across Blockchains. Available online: https://thecrypto.app/blog/wrapped-tokens-blockchain-btc-wbtc/?cookie-state-change=1630431206305 (accessed on 31 August 2021).
- RADAR. WTF IS WETH? Available online: https://weth.io/ (accessed on 19 August 2021).
- Loong How RenVM Actually Works. Available online: https://medium.com/renproject/how-renvm-actually-works-c2f76a2630c4 (accessed on 12 August 2021).
- Carpenter, A. What is Wrapped Bitcoin (WBTC) and How Can DeFi Investors Use It? Available online: https://www.bitcoinmarketjournal.com/what-is-wrapped-bitcoin/ (accessed on 19 August 2021).
- Baker, P. Synthetic Bitcoin Product Launches on Ethereum. Available online: https://cryptobriefing.com/synthetic-bitcoin-synthetix/ (accessed on 7 September 2021).
- SecretNetwork. Introducing Secret Network. Available online: https://scrt.network/blog/introducing-secret-network (accessed on 19 August 2020).
- Frankenreiter, J. The Limits of Smart Contracts. J. Inst. Theor. Econ. JITE 2019, 175, 149–162. [Google Scholar] [CrossRef]
- Soldani, J. Grey Literature. ACM SIGSOFT Softw. Eng. Notes 2019, 44, 11–12. [Google Scholar] [CrossRef]
- Ogawa, R.T.; Malen, B. Towards Rigor in Reviews of Multivocal Literatures: Applying the Exploratory Case Study Method. Rev. Educ. Res. 2016, 61, 265–286. [Google Scholar] [CrossRef]
- Pupyshev, A.; Sapranidi, I.; Dzhafarov, E.; Khalilov, S.; Teterin, I. Graviton: Interchain swaps and wrapped tokens liquidity incentivisation solution. arXiv 2020, arXiv:2009.05540. [Google Scholar]
- Darisi, M.; Savla, J.; Shirole, M.; Bhirud, S. STEM: Secure Token Exchange Mechanisms. Commun. Comput. Inf. Sci. 2019, 1132, 206–219. [Google Scholar] [CrossRef]
- Moncada, R.; Ferro, E.; Favenza, A.; Freni, P. Next Generation Blockchain-Based Financial Services. In Euro-Par 2020: Parallel Processing Workshops; Springer: Cham, Switzerland, 2021; Volume 12480, pp. 30–41. [Google Scholar]
- Fedorova, E.P.; Skobleva, E.I. Application of blockchain technology in higher education. Eur. J. Contemp. Educ. 2020, 9, 552–571. [Google Scholar] [CrossRef]
- Caldarelli, G.; Ellul, J. The Blockchain Oracle Problem in Decentralized Finance—A Multivocal Approach. Appl. Sci. 2021, 11, 7572. [Google Scholar] [CrossRef]
- Pasdar, A.; Dong, Z.; Lee, Y.C. Blockchain Oracle Design Patterns. arXiv 2021, arXiv:2106.09349. [Google Scholar]
- Garousi, V.; Felderer, M.; Mäntylä, M.V. Guidelines for including grey literature and conducting multivocal literature reviews in software engineering. Inf. Softw. Technol. 2019, 106, 101–121. [Google Scholar] [CrossRef] [Green Version]
- EnergiDefi. What Is a Wrapped Asset? Available online: https://defi.support.energi.world/hc/en-us/articles/360055624532-What-is-a-wrapped-asset- (accessed on 10 September 2021).
- Klages-Mundt, A.; Harz, D.; Gudgeon, L.; Liu, J.-Y.; Minca, A. Stablecoins 2.0: Economic Foundations and Risk-based Models. SSRN Electron. J. 2020, 59–79. [Google Scholar] [CrossRef]
- Tang, N. Wrapped Tokens: Why Are Wrapped Tokens so Important?—Phemex Academy. Available online: https://phemex.com/academy/what-are-wrapped-tokens (accessed on 3 December 2021).
- Gu, W.C.; Raghuvanshi, A.; Boneh, D. Empirical Measurements on Pricing Oracles and Decentralized Governance for Stablecoins. Cryptoecon. Syst. 2021, 1. [Google Scholar] [CrossRef]
- Tether Holdings Limited Tether: Fiat currencies on the Bitcoin blockchain. Northwest. Univ. Law Rev. 2018, 113, i–viii.
- Centre USDC Centre Whitepaper. Self-Publ. White Pap. 2018. Available online: https://f.hubspotusercontent30.net/hubfs/9304636/PDF/centre-whitepaper.pdf (accessed on 10 September 2021).
- Werner, S.M.; Perez, D.; Gudgeon, L.; Klages-Mundt, A.; Harz, D.; Knottenbelt, W.J. SoK: Decentralized Finance (DeFi). SSRN Electron. J. 2021, 1–19. [Google Scholar] [CrossRef]
- DR, T. An Introduction to Binance Bridge. Available online: https://academy.binance.com/en/articles/an-introduction-to-binance-bridge (accessed on 6 September 2021).
- Moore, C. Independent Accountant’s Report. 2021. Available online: https://tether.to/wp-content/uploads/2021/08/tether_assuranceconsolidated_reserves_report_2021-06-30.pdf (accessed on 10 September 2021).
- Maker Team. The Dai Stablecoin System. Whitepaper 2017, 21. Available online: https://makerdao.com/whitepaper/White%20Paper%20-The%20Maker%20Protocol_%20MakerDAO%E2%80%99s%20Multi-Collateral%20Dai%20(MCD)%20System-FINAL-%20021720.pdf (accessed on 11 September 2021).
- Brooks, S.; Jurisevic, A.; Spain, M.; Warwick, K. Synthetix: A Decentralised Payment Network and Stablecoin v0.8. Available online: https://www.synthetix.io/uploads/synthetix_litepaper.pdf (accessed on 9 January 2021).
- Cryptopedia Staff. Wrapped Bitcoin: What Can You Do With A wBTC Token? | Gemini. Available online: https://www.gemini.com/cryptopedia/wrapped-bitcoin-what-can-you-do (accessed on 3 December 2021).
- Amler, H.; Eckey, L.; Faust, S.; Kaiser, M.; Sandner, P.; Schlosser, B. DeFi-ning DeFi: Challenges & Pathway. arXiv 2021, arXiv:2101.05589. [Google Scholar]
- Liu, B.; Szalachowski, P.; Zhou, J. A First Look into DeFi Oracles. In Proceedings of the 2021 IEEE International Conference on Decentralized Applications and Infrastructures (DAPPS), Oxford, UK, 23–26 August 2020. [Google Scholar]
- Udeji, C. What Are Wrapped Tokens?—Everything You Need To Know. Available online: https://www.nigeriabitcoincommunity.com/wrapped-tokens/ (accessed on 12 August 2021).
- Qasse, I.A.; Talib, M.A.; Nasir, Q. Inter blockchain communication: A survey. In Proceedings of the ArabWIC 6th Annual International Conference Research Track, Rabat, Morocco, 7–9 March 2019; pp. 1–6. [Google Scholar] [CrossRef]
- Frincu, I.A. Wrapped Tokens, Long-Story-Short. Available online: https://www.linkedin.com/pulse/wrapped-tokens-long-story-short-ioana-alexandra-frincu/ (accessed on 23 August 2021).
- Hancock, B. What Is a Wrapped Token? Available online: https://blog.uphold.com/what-is-a-wrapped-token (accessed on 6 September 2021).
- Antonopoulos, A.M.; Woods, G. Mastering Ethereum—Building Smart Contracts and DAPPS; O’Reilly: Newton, MA, USA, 2018. [Google Scholar]
- Schär, F. Decentralized Finance: On Blockchain- and Smart Contract-based Financial Markets. SSRN Electron. J. 2020, 1–24. [Google Scholar] [CrossRef]
- DefiPulse. DexGuru—Real-time Data, Analytics and Trading for AMMs in One Place. Available online: https://defipulse.com/blog/dexguru/ (accessed on 19 April 2021).
- CoinMarketCap. Today’s Cryptocurrency Prices by Market Cap. Available online: https://coinmarketcap.com/ (accessed on 13 September 2021).
- Easley, D.; O’Hara, M.; Basu, S. From mining to markets: The evolution of bitcoin transaction fees. J. Financ. Econ. 2019, 134, 91–109. [Google Scholar] [CrossRef]
- Nakamoto, S. Bitcoin: A Peer-to-Peer Electronic Cash System. Available online: https://bitcoin.org/bitcoin.pdf (accessed on 11 June 2019).
- Elena, R. A 3 Minute Guide to Wrapped Bitcoin—WBTC. Available online: https://coinpedia.org/information/guide-to-wrapped-bitcoin/ (accessed on 23 August 2021).
- Network, K.; Protocol, R. Wrapped Tokens—A Multi-Institutional Framework for Tokenizing Any Asset. Available online: https://wbtc.network/assets/wrapped-tokens-whitepaper.pdf (accessed on 1 September 2021).
- Antonopoulos, A.M. Mastering Bitcoin: Programming the Open Blockchain, 2nd ed.; O’Reilly: Newton, MA, USA, 2017. [Google Scholar]
- U/qqwe22 People Who Own Wrapped Btc and Similair Tokens, Why? Available online: https://www.reddit.com/r/CryptoCurrency/comments/ozrodk/people_who_own_wrapped_btc_and_similair_tokens_why/ (accessed on 26 August 2021).
- Zhang, T. Republic Protocol: An Introduction. Available online: https://medium.com/renproject/republic-protocol-an-introduction-3d04e74c8f04 (accessed on 4 September 2021).
- BinanceAcademy. What Are Wrapped Tokens? Available online: https://academy.binance.com/en/articles/what-are-wrapped-tokens?ref=JLI1VBLA&utm_source=BinanceTwitter&utm_medium=GlobalSocial&utm_campaign=GlobalSocial (accessed on 30 August 2021).
- Gudgeon, L.; Moreno-Sanchez, P.; Roos, S.; McCorry, P.; Gervais, A. SoK: Layer-Two Blockchain Protocols. In Financial Cryptography and Data Security, Proceedings of the 24th International Conference on Financial Cryptography and Data Security, Kota Kinabalu, Malaysia, 10–14 February 2020; Springer: Cham, Switzerland, 2020; Volume 12059, pp. 201–226. [Google Scholar] [CrossRef]
- Li, C.; Zhang, J.; Yang, X. Scalable blockchain storage mechanism based on two-layer structure and improved distributed consensus. J. Supercomput. 2021, 1–32. [Google Scholar] [CrossRef]
- Johnson, S.; Robinson, P.; Brainard, J. Sidechains and interoperability. arXiv 2019, arXiv:1903.04077. [Google Scholar]
- Egberts, A. The Oracle Problem—An Analysis of how Blockchain Oracles Undermine the Advantages of Decentralized Ledger Systems. SSRN Electron. J. 2017. [Google Scholar] [CrossRef]
- Madine, M.; Salah, K.; Jayaraman, R.; Al-Hammadi, Y.; Arshad, J.; Yaqoob, I. appXchain: Application-Level Interoperability for Blockchain Networks. IEEE Access 2021, 9, 87777–87791. [Google Scholar] [CrossRef]
- Tarman, M. What is Wrapped Bitcoin? | NiceHash. Available online: https://www.nicehash.com/blog/post/what-is-wrapped-bitcoin#! (accessed on 3 December 2021).
- Thomson, C. The DAO of ETHEREUM: Analyzing the DAO Hack, the Blockchain, Smart Contracts, and the Law. Available online: https://medium.com/blockchain-review/the-dao-of-ethereum-e228b93afc79 (accessed on 3 April 2020).
- Ghag, S. Wrapped Tokens—Explained | CoinsCapture. Available online: https://coinscapture.com/blog/wrapped-tokens-explained (accessed on 3 December 2021).
- Scheid, E.J.; Hegnauer, T.; Rodrigues, B.; Stiller, B. Bifröst: A Modular Blockchain Interoperability API. In Proceedings of the 2019 IEEE 44th Conference on Local Computer Networks (LCN), Osnabrueck, Germany, 14–17 October 2019; pp. 332–339. [Google Scholar] [CrossRef] [Green Version]
- Yos Smart Contract Extensibility with Wrapped Tokens. Available online: https://yos.io/2019/07/13/smart-contract-extensibility-wrapped-tokens/ (accessed on 21 August 2021).
- TheShrimpyTeam. What Are Wrapped Tokens? Available online: https://academy.shrimpy.io/lesson/what-are-wrapped-tokens (accessed on 24 August 2021).
- CryptopediaStaff. What Is Kyber Network and How Does It Work? Available online: https://www.gemini.com/cryptopedia/what-is-kyber-network (accessed on 28 August 2021).
- Rothrie, S. What Is BitGo? Enterprise Cryptocurrency Solutions. Available online: https://coincentral.com/what-is-bitgo/ (accessed on 28 August 2021).
- Gongo Wrapped Tokens Explained. Available online: https://www.publish0x.com/decentralization-why-is-it-important/wrapped-tokens-explained-xzwkzpn (accessed on 3 December 2021).
- Kuznetsov, N. Wrapped Crypto Tokens, Explained. Available online: https://cointelegraph.com/explained/wrapped-crypto-tokens-explained (accessed on 2 December 2021).
- Zhang, T.; Wang, L. Republic Protocol A Decentralized Dark Pool Exchange Providing Atomic Swaps for Ethereum-Based Assets and Bitcoin. Available online: https://renproject.io/whitepaper_1.0.0.pdf (accessed on 5 June 2021).
- We Are DigiByte. renDGB—It’s Here and Here’s What You Can Do with It. | By We Are DigiByte | Medium. Available online: https://wearedgb.medium.com/rendgb-its-here-and-here-s-what-you-can-do-with-it-a092f567a563 (accessed on 18 November 2021).
- Project, R. Ren Whitepaper. Available online: https://medium.com/renproject (accessed on 13 September 2021).
- Andreychev, A. Binance Introduces Wrapped Tokens For Ethereum—The Chain Bulletin. Available online: https://chainbulletin.com/binance-introduces-wrapped-tokens-for-ethereum/ (accessed on 2 December 2021).
- Sriram, S. Binance Launches BTokens—Wrapped Tokens on Ethereum. Available online: https://eng.ambcrypto.com/binance-btokens-ethereum/ (accessed on 30 August 2021).
- Binance.org. Proof of Assets. Available online: https://www.binance.org/en/assets-proof (accessed on 18 November 2021).
- TheShrympyTeam. What Are Crypto Synths? Synthetic Assets Explained. Available online: https://academy.shrimpy.io/post/what-are-crypto-synths-synthetic-assets-explained (accessed on 7 September 2021).
- The Synthetix Team. The Vega Release. Available online: https://blog.synthetix.io/the-vega-release/ (accessed on 15 November 2021).
- Al-Breiki, H.; Rehman, M.H.U.; Salah, K.; Svetinovic, D. Trustworthy Blockchain Oracles: Review, Comparison, and Open Research Challenges. IEEE Access 2020, 8, 85675–85685. [Google Scholar] [CrossRef]
- Krupka, D. Secret Network (SCRT) Review: Privacy Meets Compliance. Available online: https://www.coinbureau.com/review/secret-network-scrt/ (accessed on 8 September 2021).
- Hayward, A. What Is Secret Network (SCRT)? Available online: https://decrypt.co/resources/what-is-secret-network-scrt-formerly-enigma (accessed on 8 September 2021).
- Sun, Z. What Are Wrapped Tokens? | The Motley Fool. Available online: https://www.fool.com/investing/2021/10/05/what-are-wrapped-tokens/ (accessed on 3 December 2021).
- ByBitLearn. What are Wrapped Tokens—And How do They Work? Available online: https://learn.bybit.com/crypto/what-are-wrapped-tokens-and-how-do-they-work/ (accessed on 1 September 2021).
- Jin, H.; Dai, X.; Xiao, J. Towards a novel architecture for enabling interoperability amongst multiple blockchains. In Proceedings of the 2018 IEEE 38th International Conference on Distributed Computing Systems (ICDCS), Vienna, Austria, 2–6 July 2018; pp. 1203–1211. [Google Scholar] [CrossRef]
- Gas Tracker—Etherscan. Available online: https://docs.etherscan.io/api-endpoints/gas-tracker (accessed on 18 November 2021).
- Ren RenBridge Terms of Service. Available online: https://documentcloud.adobe.com/link/track?uri=urn:aaid:scds:US:33d77e75-ba96-4db3-85d1-5ffb6fd34a8f#pageNum=1 (accessed on 24 August 2021).
- Caldarelli, G. Understanding the Blockchain Oracle Problem: A Call for Action. Information 2020, 11, 509. [Google Scholar] [CrossRef]
- Monika; Bhatia, R. Interoperability solutions for blockchain. In Proceedings of the 2020 International Conference on Smart Technologies in Computing, Electrical and Electronics (ICSTCEE), Bengaluru, India, 9–10 October 2020; pp. 381–385. [Google Scholar] [CrossRef]
- SecretFinance. Secret Finance F.A.Q. Available online: https://bridge.scrt.network/faq (accessed on 14 September 2021).
- Sztorc, P. The Oracle Problem. Available online: https://www.infoq.com/presentations/blockchain-oracle-problems (accessed on 3 March 2020).
- Pillai, B.; Biswas, K.; Muthukkumarasamy, V. Cross-chain interoperability among blockchain-based systems using transactions. Knowl. Eng. Rev. 2020, 35, e23. [Google Scholar] [CrossRef]
- Cavicchioli, M. What Are the So-Called Wrapped Bitcoin?—The Cryptonomist. Available online: https://en.cryptonomist.ch/2020/09/19/what-are-wrapped-bitcoin/ (accessed on 3 December 2021).
- Reike, F. Advantages and Disadvantages of Wrapped Assets. Available online: https://medium.com/nakamo-to/advantages-and-disadvantages-of-wrapped-assets-ffe35fa2f566 (accessed on 17 August 2021).
- Dovbnya, A. Vitalik Buterin Worried About “Trust Models” of Some Bitcoin-Backed Ethereum Tokens. Available online: https://u.today/vitalik-buterin-worried-about-trust-models-of-some-bitcoin-backed-ethereum-tokens (accessed on 22 November 2021).
- Banov, M. Ethereum Instruments and Standard Specifications. Wrapped Tokens and ERCs. Available online: https://www.bitrates.com/news/p/wrapped-tokens-crypto-derivatives-and-candidate-ethereum-standards-ercs (accessed on 3 December 2021).
- Ren Community Ren, October Development Update. Available online: https://medium.com/renproject/october-development-update-3b68ea6d2dea (accessed on 19 November 2021).
- Arasa, D. What Are Wrapped Tokens? How Wrapped Tokens Bring the Gift of Blockchain in Many Ways. Available online: https://usa.inquirer.net/79580/what-are-wrapped-tokens (accessed on 30 August 2021).
- Liu, Z.; Xiang, Y.; Shi, J.; Gao, P.; Wang, H.; Xiao, X.; Wen, B.; Hu, Y.C. Hyperservice: Interoperability and programmability across heterogeneous blockchains. In Proceedings of the 2019 ACM SIGSAC Conference on Computer and Communications Security, London, UK, 11–15 November 2019; pp. 549–566. [Google Scholar] [CrossRef]
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2021 by the author. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).