Obérisk: Cybersecurity Requirements Elicitation through Agile Remote or Face-to-Face Risk Management Brainstorming Sessions
Abstract
:1. Introduction
2. Literature Review
3. Method
- Overall, how would you rate the risk assessment brainstorming sessions?
- Did the set of workshops meet its objectives?
- What did you like about this event?
- What do you think should be improved?
- Do you feel you can now develop/maintain the analysis by yourself (as a team)?
- Do you think the approach would be applicable to other division system/product/equipment?
- Do you feel you could now run a new risk assessment by yourself on another system/product/equipment?
- The approach was developed to be specifically applicable at bid time, for an initial security analysis. Would you agree that this would be an adequate setting for this approach?
- How likely is it that you would recommend this approach to Thales colleagues?
- Any other comment?
4. Results
4.1. Workshop n°1: Framing and Security Baseline
4.1.1. Definition of the Study Objectives, System Missions, and Asset Owners
- The study objectives within pinkish sticky notes. By default, the datasheet allows room for three different objectives, but it is possible to have less.
- The missions of the system-under-study within blue sticky notes. Per default, the datasheet allows room for only two different objectives. This can be reduced to a single item if applicable. It is essential to keep the number of missions low; otherwise, some confusion might arise with the elicitation of the business assets (see below).
- Optionally, the analysis timeframe. The EBIOS Risk Manager method comprises two cycles: the strategic cycle and the operational cycle. The expected duration of those cycles can be documented here. Although they are seldom filled in, these fields are provided here to ensure compliance with the method. In practice, these durations are difficult to assess, especially when the strategic and operational cycles relate to different stakeholders, e.g., the customer versus the system’s end-user.
4.1.2. Illustration in a Naval Setting
4.1.3. Definition of Primary Assets
4.1.4. Illustration in a Naval Setting
4.1.5. Definition of the Existing Regulatory Security Controls
4.1.6. Illustration in a Naval Setting
4.1.7. Hindsight on the First Datasheet
4.1.8. Definition and Assessment of the Feared Events
4.1.9. Illustration in a Naval Setting
4.1.10. Hindsight on the Second Datasheet
4.1.11. System Architecture and Identification of Existing or Already Specified Security Measures
- At the top, the organizational assets, such as human resources and their structuring;
- In the middle, Information Technology (IT) or Operational Technology (OT) assets, covering hardware, software and networks;
- At the bottom are significant physical assets used but are not usually an integral part of the system-under-study; this includes premises where the system-under-study is located and large infrastructures used by the system-under-study, e.g., the World Wide Web.
4.1.12. Illustration in a Naval Setting
- The unavoidable security controls, i.e., the controls related to the premises where the cyber range is installed.
- The security controls that can be switched on or off at will on the cyber range. Colour coding is used to specify if the security controls were considered as always active (green), sometimes active (black) or deactivated (red) in the attack scenarios. Thus, the implementation status presented in Figure 7 is not representative of a real situation on board. It is intended to be editable at will, in order to allow for the development of attack scenarios, which is one of the platform’s key objectives.
- The security controls that may exist on certain ships but are not implemented in the scope of the cyber range.
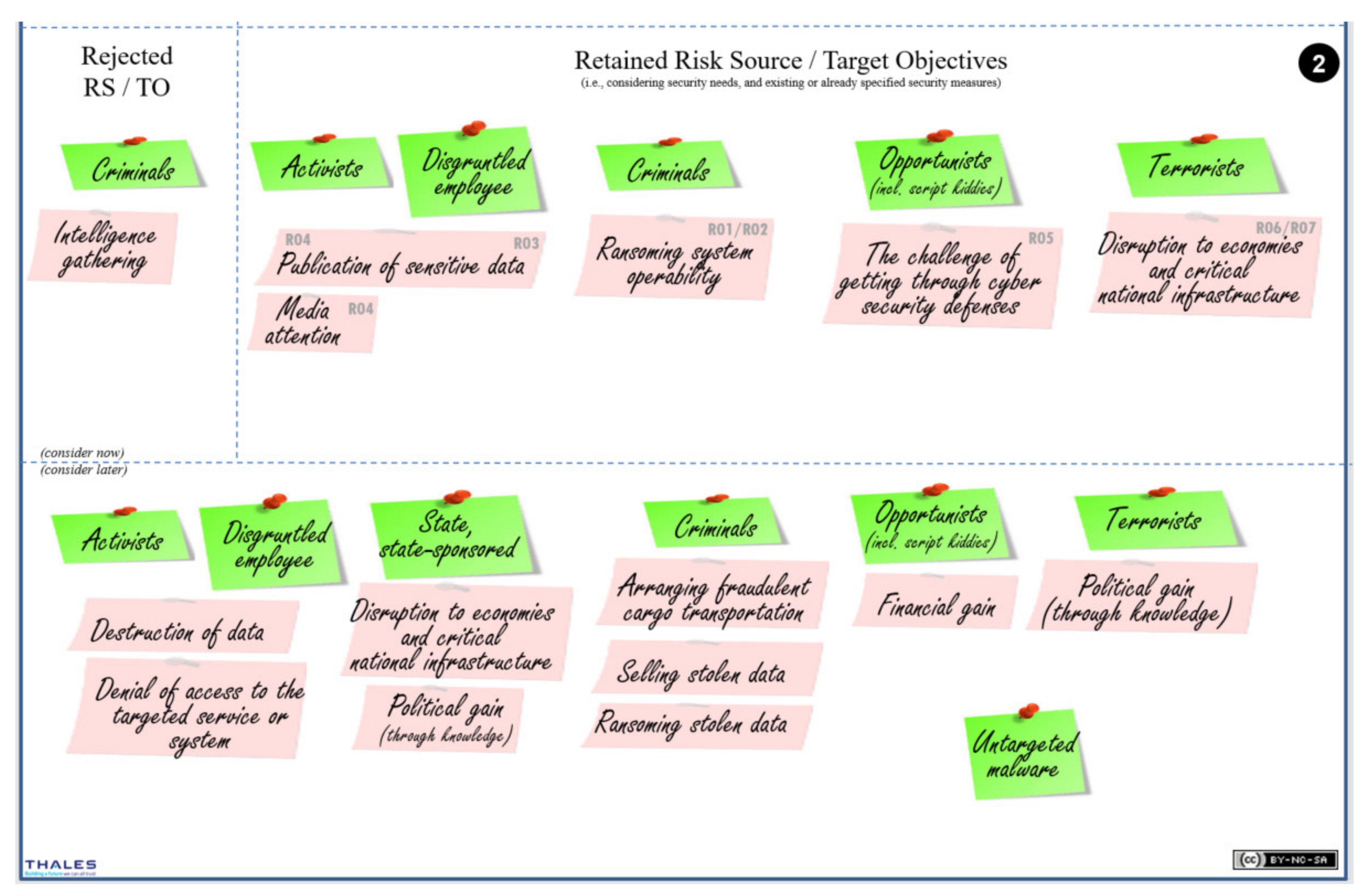
4.2. Workshop n°2: Risk Origins
4.2.1. Identification and Assessment of the Risk Origins
- Column n°1: human intentional (external) risk origins; here, external means not belonging to the organization of the sponsor of the risk analysis;
- Column n°2: human intentional (internal) risk origins; here, internal means belonging to the organization of the sponsor;
- Column n°3: accidental (natural or human) risk origins.
4.2.2. Identification and Assessment of the Target Objectives
4.2.3. Illustration in a Naval Setting
4.3. Workshop n°3: Strategic Scenarios
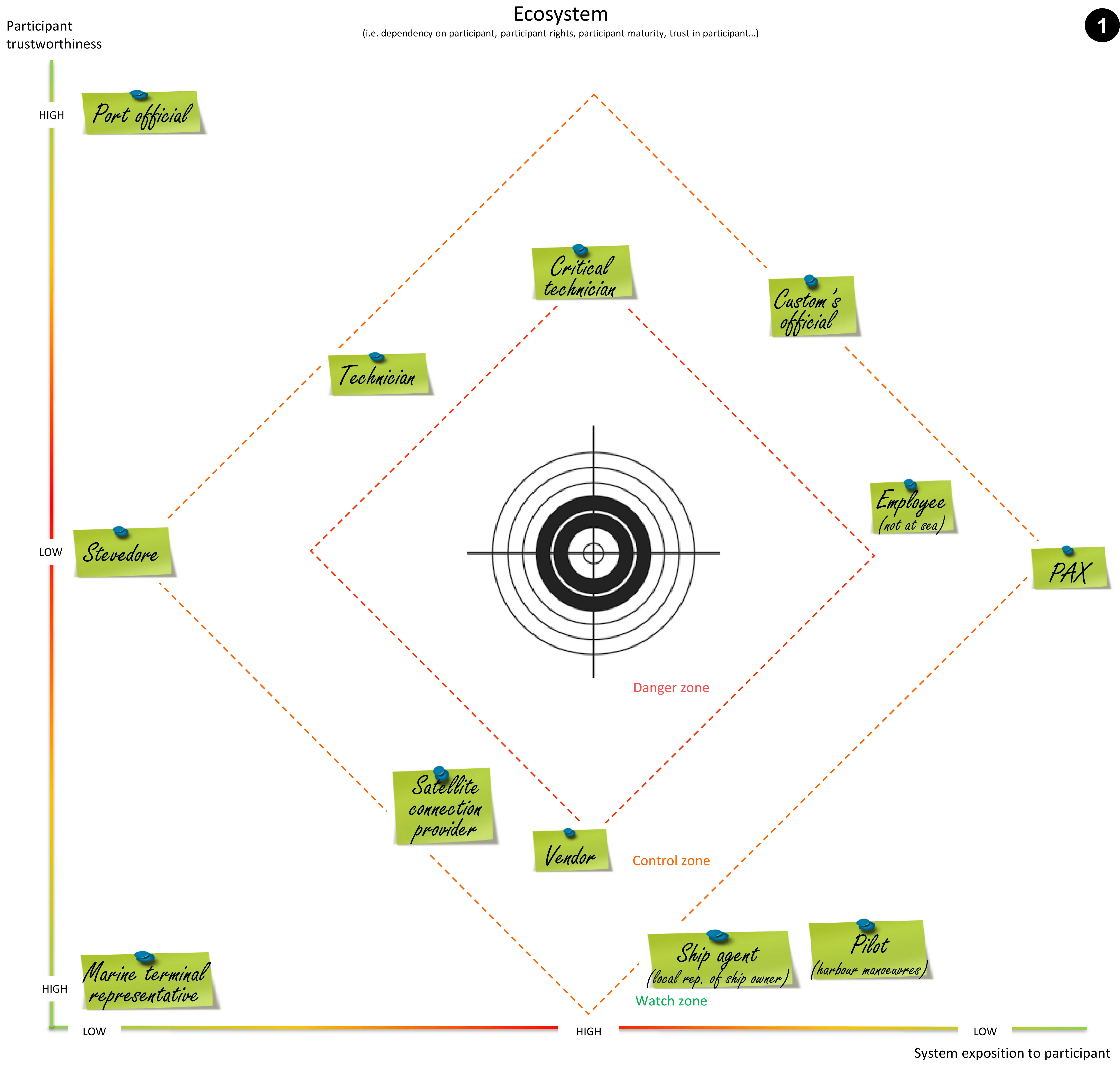
4.3.1. Identification and Assessment of the Ecosystem Participants
- The system’s exposure to the participant (see Equation (1));
- The cyber reliability of the participant (see Equation (2)).
- The horizontal axis relates to the system’s exposure to the participant, where exposure is defined as a combination of system dependency on the participant and the rights/privileges that the participant has over the system;
- The vertical axis relates to the participant’s cyber reliability, where cyber reliability is defined as a combination of cyber maturity (i.e., trustworthiness) and trust.
- When a participant is critically located at the centre of the diagram, they are also at the centre of attention; with normal axes, the critical participants would all be located in the upper right corner of the diagram;
- There is a lot of space on the sides of the diagram to group non-critical participants per type; for example, end-users can be located on the left, while maintenance operators can be located on the right, and internal staff can be located on the top, while external actors can be located at the bottom part of the diagram.
4.3.2. Illustration in a Naval Setting
4.3.3. Textual Definitions of Strategic Scenarios
- Risks by severity (cf. Figure 11): the study of these risks will continue in the following workshops.
- Postponed risks: These risks are considered less important; the study of these risks is postponed until a future iteration of the risk assessment; since the next iteration may be run months later, these risks are register here in order to ensure they will not be forgotten.
- Rejected risks: These risks are considered irrelevant in the scope of this study and are wilfully rejected; usually a justification is required here. The rejection justification can be captured in the slide notes. These risks are not to be confused with accepted risks. Risk acceptance is part of risk treatment, and will be handled during workshop n°5 (cf. Section 4.5). As previously mentioned, it is always important to capture elements that were considered and wilfully rejected, by contrast to elements that were just forgotten during the analysis.
4.3.4. Illustration in a Naval Setting
4.3.5. Alternative Approach to Strategic Scenario Modelling
- The direct attack of a business asset located within the system-under-study. This type of route is noted R0y.
- The indirect attack of a business asset located within the system-under-study; here, the risk origin uses a participant as an attack vector. This type of route is noted R0z.
- The indirect attack of a business asset located within a participant’s organization or information system (original asset or a copy of the asset). This type of route is noted R0x.
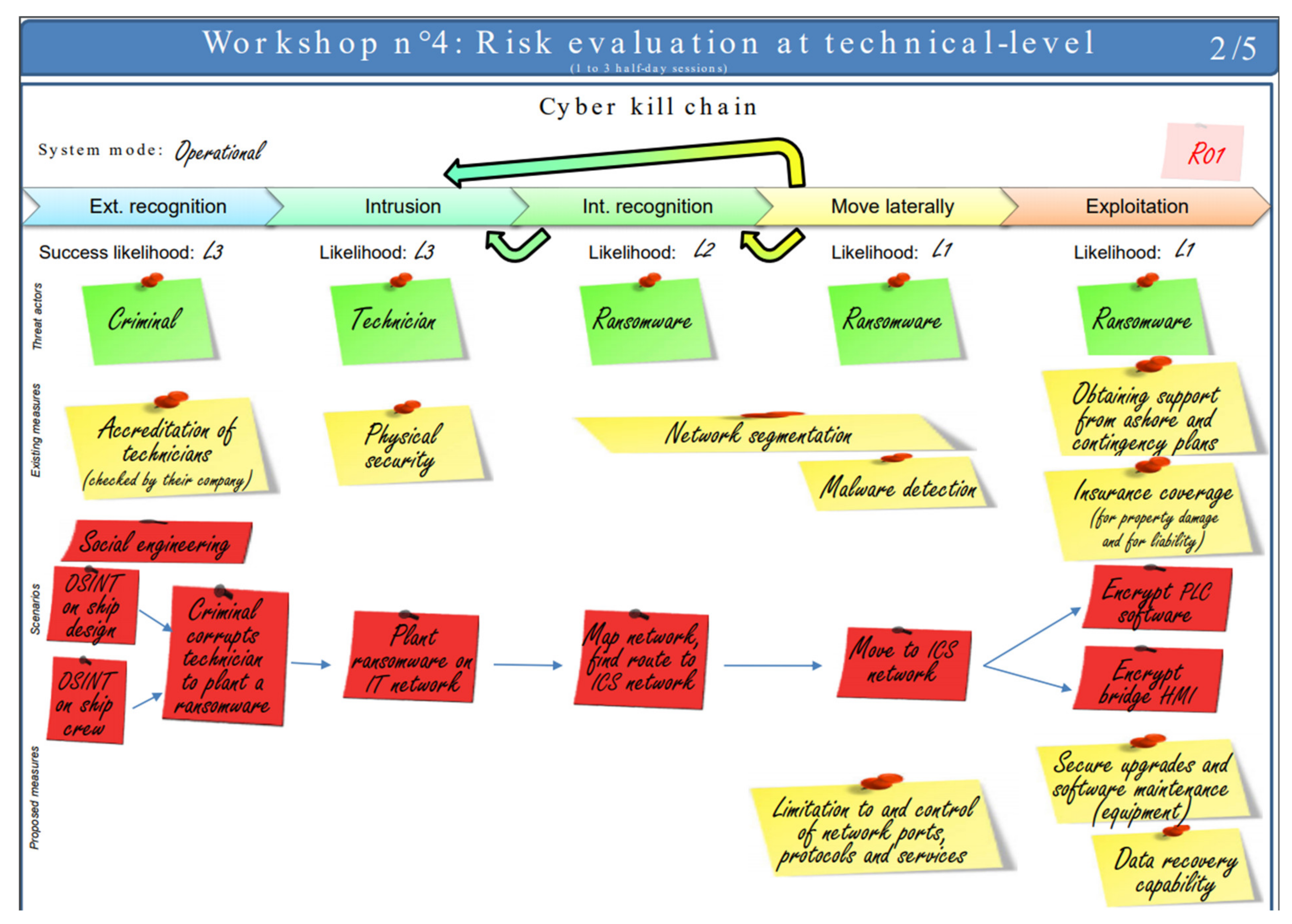
4.4. Workshop n°4: Operational Scenarios
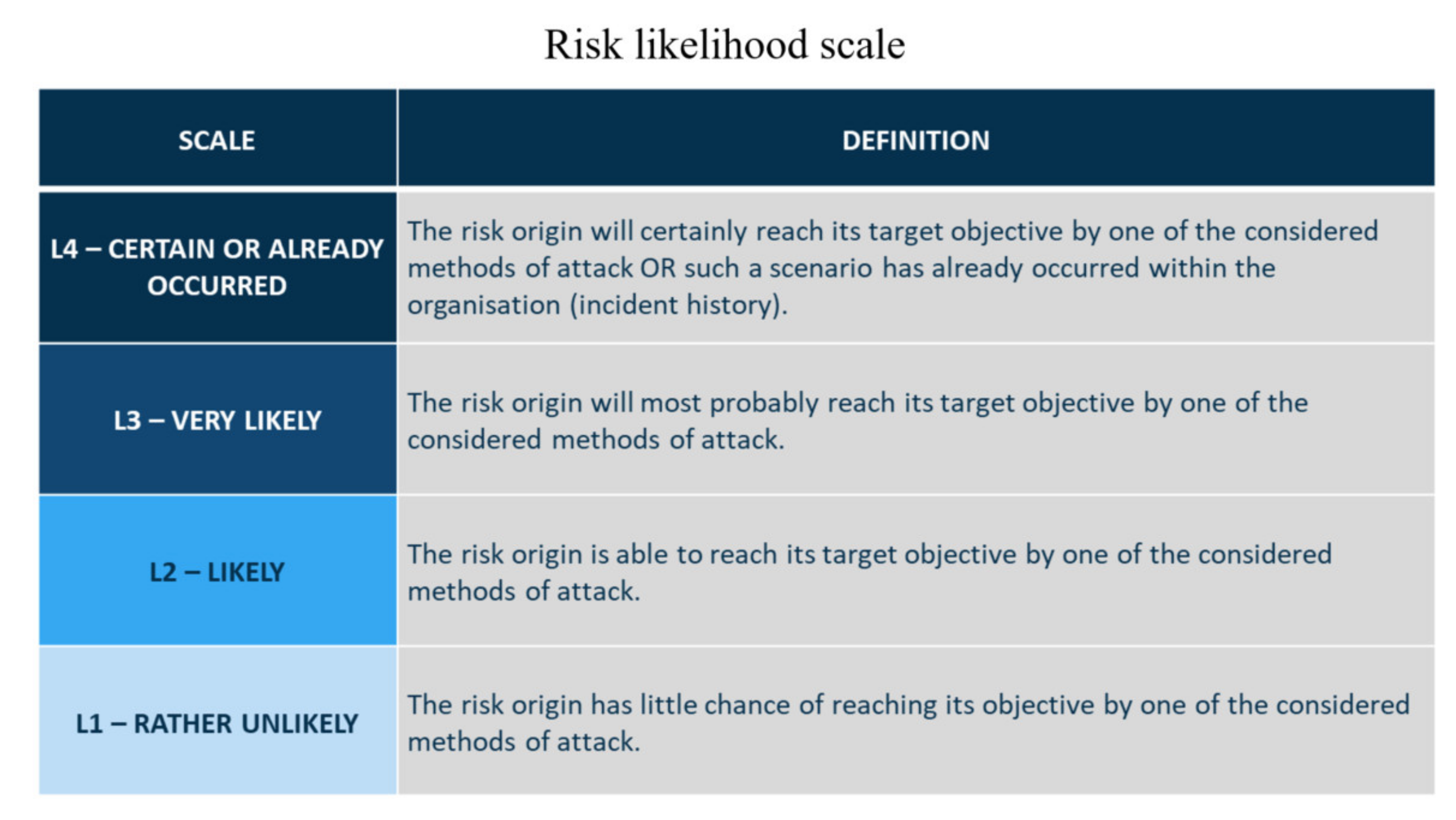
4.4.1. Cyber Kill Chain Definitions
- Success likelihood for each phase of the Cyber Kill Chain;
- Threat actors, using a green sticky note, such as in workshop n°2;
- Existing security measures, using yellow sticky notes, such as in workshops n°1 and 3;
- Elementary attack actions, using red sticky notes;
- Newly proposed security measures, again using yellow sticky notes.
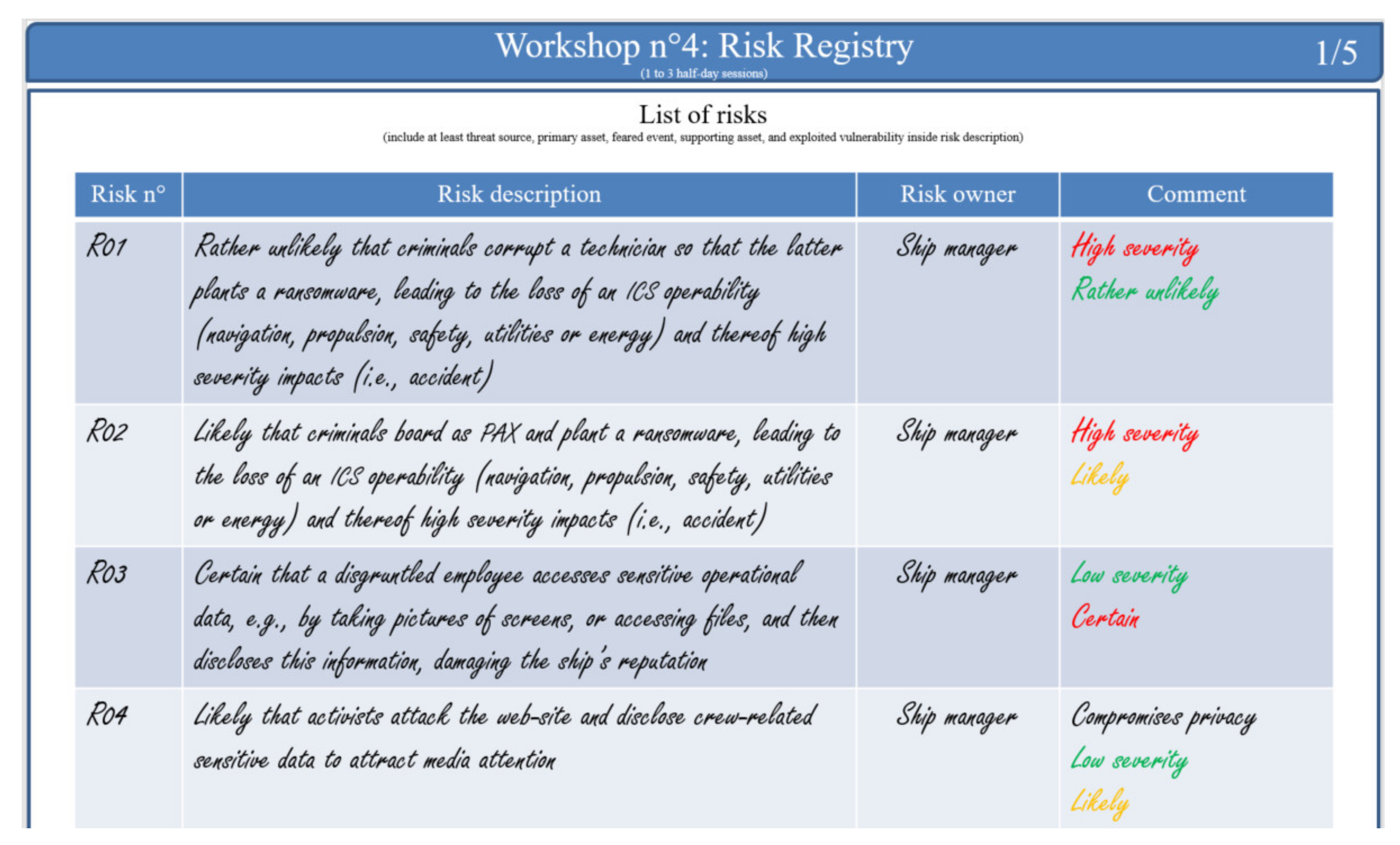
4.4.2. Risk Registry
4.4.3. Illustration in a Naval Setting
- The feasibility of steps one and two was very likely (L3), mainly due to the human factor, which is very difficult to control;
- The cumulative feasibility of step three drops to likely (L2), because it concerns our system network exclusively, and we have a certain degree of control over it;
- The cumulative feasibility of step four drops again to rather unlikely (L1) given the security measures already implemented to prevent lateral movement.
- Seven operational scenarios were described in this fashion for our naval use case.
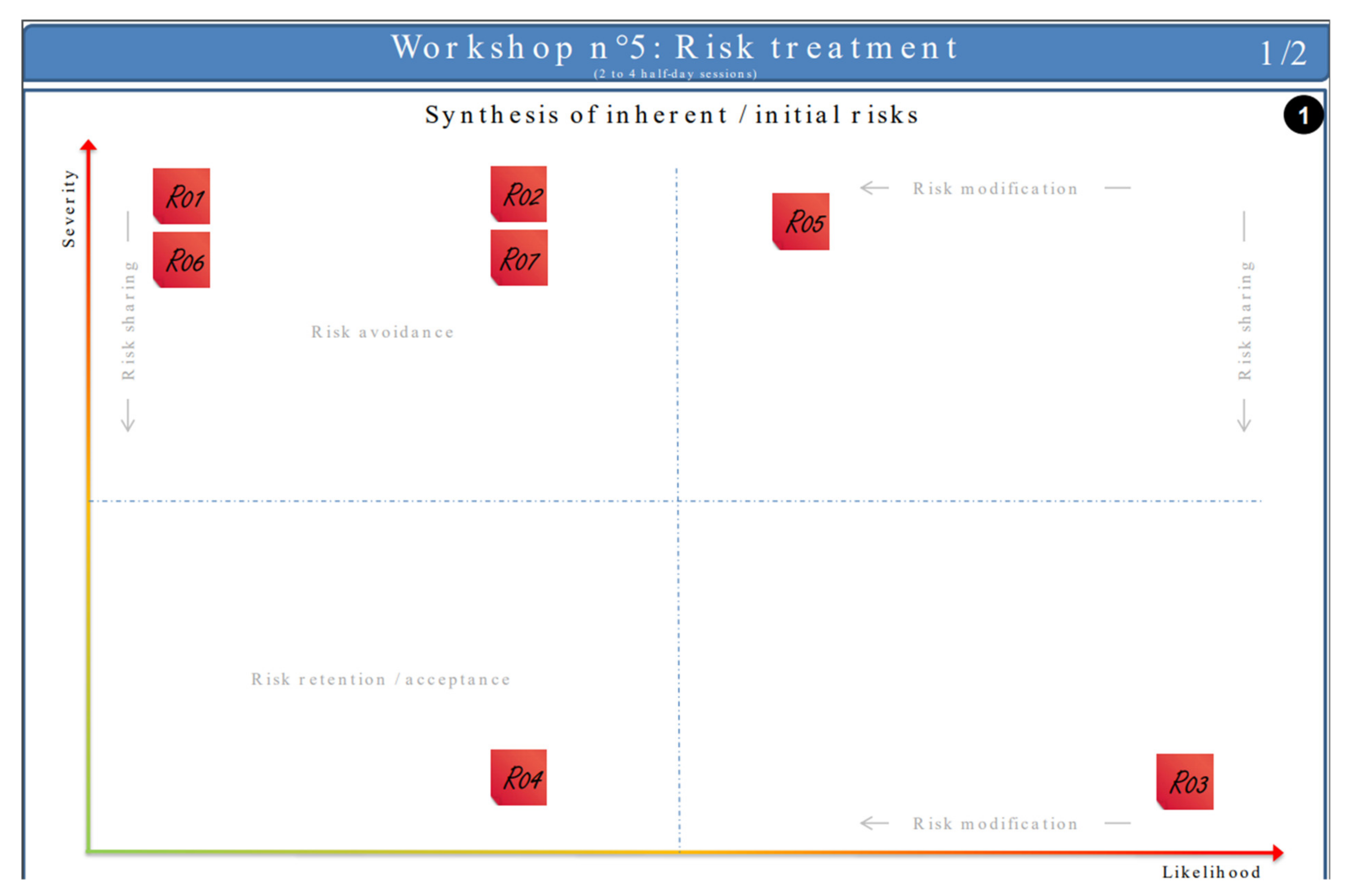
4.5. Workshop n°5: Risk Treatment
4.5.1. Risk Syntheses
4.5.2. Illustration in a Naval Setting
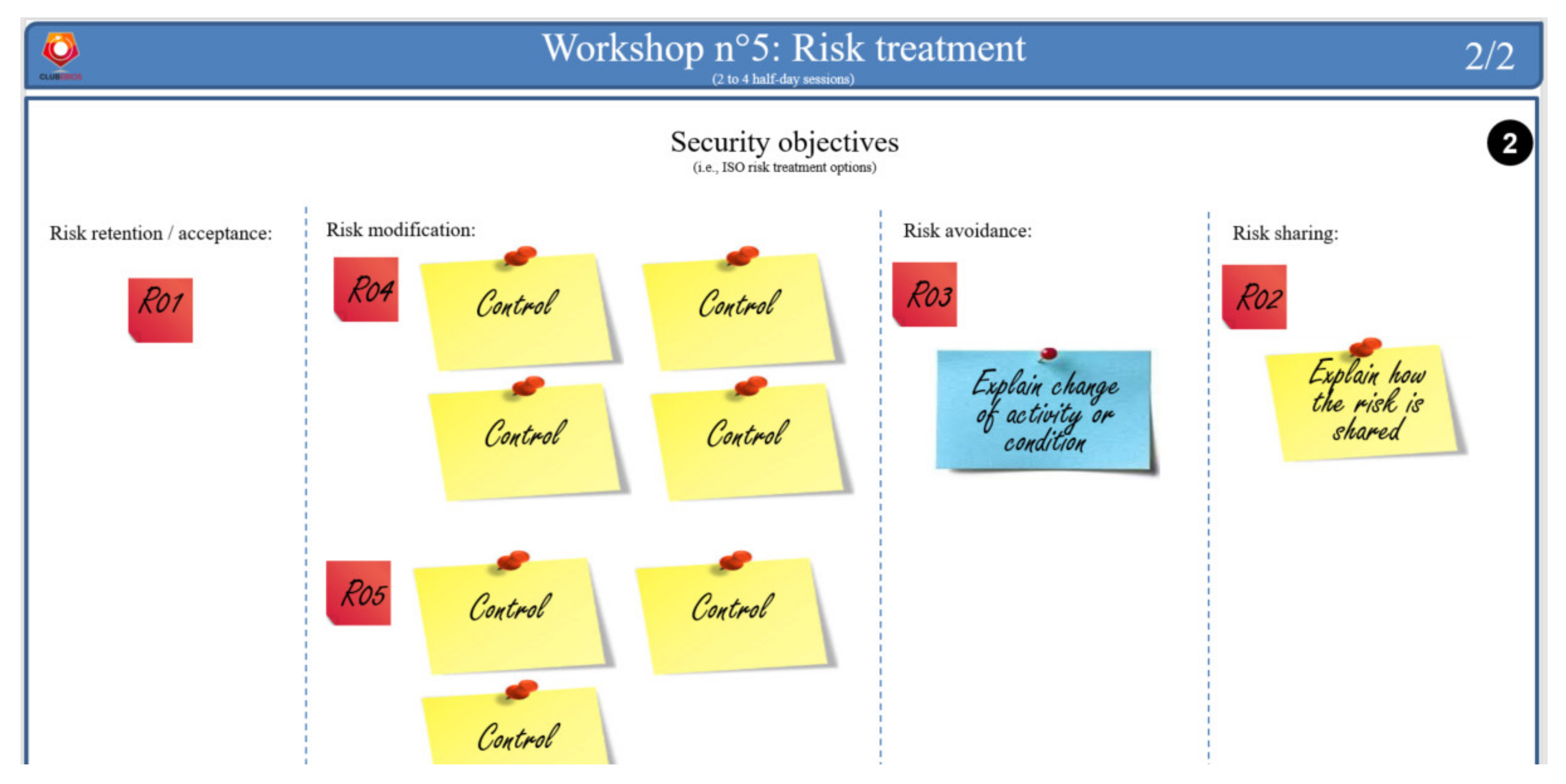
4.5.3. Risk Treatment
4.5.4. Study Conclusions
5. Discussion
5.1. The Naval Use Case End-User Viewpoint
5.2. Further Work
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Acknowledgments
Conflicts of Interest
Appendix A. Brief Overview of the EBIOS Risk Manager Method

- It explicitly targets populations beyond the classical cybersecurity experts, including company directorates, risk managers, Chief Information Security Officers (CISOs), Chief Information Officers (CIOs) and business/operational experts, such as Architects (ARCs), Product Line Architects (PLAs), Design Authorities (DAs) and System Engineering Managers (SEMs).
- It mandates securing by conformity, prior to securing by scenario. Securing by conformity means that a Minimal Set of Security Controls (MSSC), based on best practices, is selected prior to risk identification. Then, risks are identified taking into account existing controls. ANSSI’s hypothesis is that accidental events should normally be covered by the MSSCs, so that the analysis can focus solely on malevolence. In other words, only a few incident scenarios should be necessary, either to prove that the solution is secure, or to highlight some rare holes in the system. This is very important in terms of scaling. If the study becomes big, you have something wrong!
- It is run as a set of short workshops (i.e., brainstorming sessions), with two to four participants per session.
- It is an agile approach, providing quick results for decision makers. Typically, it is possible to start outputting grosgrain risks after only three workshops. To go in depth, it is possible to iterate on the workshops. It is also recommended to iterate through operational and/or strategical cycles, to keep the system in secure conditions throughout its lifecycle. The operational cycle deals with fast changing facts, e.g., security measures, vulnerabilities. The strategic cycle deals with slower-changing facts, e.g., system missions, risk sources.
- It is configurable. More explicitly, it is not required to run all five workshops in sequence. The choice to run a workshop depends on the study objectives.
- Its scope is extended to include the ecosystem, also known as actors who interact with the system. ANSSI’s assumption here is that many attacks do not directly target the system, but first target an actor in the ecosystem (e.g., a sub-contractor), then move laterally.
Appendix B. Obérisk Framework
| EBIOS-RM Workshop | Main Obérisk Datasheets | Alternative Obérisk Datasheets |
|---|---|---|
| 1 | Framing and security baseline (1/3) Business impact assessment (2/3) Framing and security baseline (3/3) | Framing (n°1) Framing and security baseline Framing (n°2) Security baseline |
| 2 | Identification of adverse objectives | |
| 3 | Risk evaluation at ecosystem-level Strategic scenarios (textual) | Strategic scenarios (graphical) |
| 4 | Risk evaluation at technical-level (2 scenarios per page) Risk registry | Risk evaluation at technical-level (1 scenario per page) Risk registry (with risk likelihood scale) |
| 5 | Risk syntheses Risk treatment | |
| Conclusions |
References
- Shimel, A.; Miller, M. A Brief History of DevSecOps and Where We Go from Here. In Proceedings of the RSA Conference, Webcasts, 30 July 2019. [Google Scholar]
- Allspaw, J.; Hammond, P. 10+ deploys per day: Dev & ops cooperation at Flickr. In Proceedings of the Velocity, Web Performance and Operations Conference, San Jose, CA, USA, 22–24 June 2009. [Google Scholar]
- Delio, M. Gates Finally Discovers Security, WIRED. 17 January 2002. Available online: https://www.wired.com/2002/01/gates-finally-discovers-security/ (accessed on 3 February 2021).
- Red Hat. What is DevSecOps? Red Hat, Inc. 2021. Available online: https://www.redhat.com/en/topics/devops/what-is-devsecops (accessed on 2 February 2021).
- Cohen, S. Automation: One of the Keys to DevSecOps. Synopsys. 12 October 2018. Available online: https://www.synopsys.com/blogs/software-security/automation-in-devsecops/ (accessed on 2 February 2021).
- IBM. DevSecOps. IBM. 30 July 2020. Available online: https://www.ibm.com/cloud/learn/devsecops (accessed on 2 February 2021).
- Lietz, S. What is DevSecOps? DevSecOps. 1 June 2015. Available online: https://www.devsecops.org/blog/2015/2/15/what-is-devsecops (accessed on 2 February 2021).
- Paul, S.; Varela, P. Poster Support for an Obeya-like Risk Management Approach. In Proceedings of the 6th International Workshop on Graphical Models for Security (GraMSec), Hoboken, NJ, USA, 24 June 2019. [Google Scholar]
- Agence Nationale de la Sécurité des Systèmes d’Information (ANSSI). EBIOS Risk Manager; ANSSI: Paris, France, 2019; p. 49.
- KPMG. KPMG 2021 CEO Outlook Pulse Survey—Preparing for a New Reality. KPMG International Limited. 1 April 2021. Available online: https://home.kpmg/xx/en/home/insights/2021/03/ceo-outlook-pulse.html (accessed on 1 April 2021).
- Chapman, C.; Ward, S. Project Risk Management: Processes, Techniques and Insights; John Wiley: Chichester, UK, 1996; p. 344. [Google Scholar]
- Chevalier, A.; Hirsch, G. Risk Management: For Better Control of Business Risks; FeniXX: Paris, France, 1982; p. 190. [Google Scholar]
- Cleland, D.I. Leadership and the project-management body of knowledge. Int. J. Proj. Manag. 1995, 13, 83–88. [Google Scholar] [CrossRef]
- Beihoff, B.; Oster, C.; Friedenthal, S.; Paredis, C.; Kemp, D.; Stoewer, H.; Nichols, D.; Wade, J. A World in Motion–Systems Engineering Vision 2025—INCOSE-SE Leading Indicators Guide. 2014. Available online: https://www.incose.org/docs/default-source/aboutse/se-vision-2025.pdf (accessed on 2 August 2021).
- Boehm, B.; Turner, R. Management challenges to implementing agile processes in traditional development organizations. IEEE Softw. 2005, 22, 30–39. [Google Scholar] [CrossRef]
- Arif, M.Y.M.; Shahar, S.M.; Yusof, M.F.H.; Satar, N.S.M. The Challenges of Implementing Agile Scrum in Information System’s Project. J. Adv. Res. Dyn. Control Syst. JARDCS 2018, 10, 2357–2363. [Google Scholar]
- Hayata, T.; Han, J. A hybrid model for IT project with Scrum. In Proceedings of the IEEE International Conference on Service Operations, Logistics and Informatics, Beijing, China, 10–12 July 2011. [Google Scholar]
- Paasivaara, M.; Durasiewicz, S.; Lassenius, C. Distributed Agile Development: Using Scrum in a Large Project. In Proceedings of the IEEE International Conference on Global Software Engineering, Bangalore, India, 17–20 August 2008. [Google Scholar]
- Gritzalis, D.; Iseppi, G.; Mylonas, A.; Stavrou, V. Exiting the risk assessment maze: A meta-survey. ACM Comput. Surv. (CSUR) 2018, 51, 1–30. [Google Scholar] [CrossRef]
- Shameli-Sendi, A.; Aghababaei-Barzegar, R.; Cheriet, M. Taxonomy of information security risk assessment (ISRA). Comput. Secur. 2016, 57, 14–30. [Google Scholar] [CrossRef]
- Wangen, G.; Hallstensen, C.; Snekkenes, E. A framework for estimating information security risk assessment method completeness. Int. J. Inf. Secur. 2018, 17, 681–699. [Google Scholar] [CrossRef] [Green Version]
- Fenz, S.; Heurix, J.; Neubauer, T.; Pechstein, F. Current challenges in information security risk management. Inf. Manag. Comput. Secur. 2014, 22, 410–430. [Google Scholar] [CrossRef]
- ISO/IEC 27005. Information Technology—Security Techniques—Information Security Risk Management; International Organization for Standardization/International Electrotechnical Commission: Geneva, Switzerland, 2018. [Google Scholar]
- IEC 62443-32. Security for Industrial Automation and Control Systems—Part 3-2: Security Risk Assessment for System Design; International Electrotechnical Commission: Geneva, Switzerland, 2020. [Google Scholar]
- NIST SP800-30. Guide for Conducting Risk Assessments; National Institute of Standards and Technology: Gaithersburg, MD, USA, 2012. [Google Scholar]
- BSI-Standard 200-3. Risk Analysis Based on IT-Grundschutz; Federal Office for Information Security (BSI): Bonn, Germany, 2017. [Google Scholar]
- Amutio, M.A.; Candau, J.; Mañas, J.A. MAGERIT—Methodology for Information Systems Risk Analysis and Management; Ministry of Finance and Public Administration: Madrid, Spain, 2014. [Google Scholar]
- Tucker, B.A. Advancing Risk Management Capability Using the OCTAVE FORTE Process; Carnegie Mellon University (CMU): Pittsburgh, PA, USA, 2020; p. 106. [Google Scholar]
- Mozilla. Rapid Risk Assessment. Mozilla. 2017. Available online: https://infosec.mozilla.org/guidelines/risk/rapid_risk_assessment (accessed on 17 April 2021).
- CLUSIF. Fondamentals of the MEHARI Method (in French Only). French Information Security Club (CLUSIF). Available online: https://clusif.fr/services/management-des-risques/les-fondamentaux-de-mehari/ (accessed on 3 February 2021).
- ISO 31000. Risk Management—Guidelines; International Organization for Standardization: Geneva, Switzerland, 2018. [Google Scholar]
- ALL4TEC. Agile Risk Manager Tools Up Your EBIOS RM Analysis. ALL4TEC. 2020. Available online: https://www.all4tec.com/en/agile-risk-manager-your-ebios-risk-manager-certified-solution/ (accessed on 8 December 2020).
- Egérie. Egérie Risk Manager. Available online: https://egerie-software.com/en/egerie-risk-manager/ (accessed on 26 June 2021).
- Risk’n Tic. Risk’n Tic—Simple Risk Management Solutions. 2018. Available online: https://riskntic.com/en/ (accessed on 26 June 2021).
- Nespoli, P.; Papamartzivanos, D.; Mármol, F.G.; Kambourakis, G. Optimal countermeasures selection against cyber attacks: A comprehensive survey on reaction frameworks. IEEE Commun. Surv. Tutor. 2017, 20, 1361–1396. [Google Scholar] [CrossRef]
- Thamhain, H. Managing Risks in Complex Projects. Proj. Manag. J. 2013, 44, 20–35. [Google Scholar] [CrossRef]
- Bakker, K.d.; Boonstra, A.; Wortmann, H. Risk managements’ communicative effects influencing IT project success. Int. J. Proj. Manag. 2012, 30, 444–457. [Google Scholar] [CrossRef]
- McShane, M.; Eling, M.; Nguyen, T. Cyber risk management: History and future research directions. Risk Manag. Insur. Rev. 2021, 24, 93–125. [Google Scholar] [CrossRef]
- Böhme, R.; Laube, S.; Riek, M. A fundamental approach to cyber risk analysis. Variance 2019, 12, 161–185. [Google Scholar]
- Crawford, L.; Morris, P.; Thomas, J.; Winter, M. Practitioner development: From trained technicians to reflective practitioners. Int. J. Proj. Manag. 2006, 24, 722–733. [Google Scholar] [CrossRef]
- De Carvalho, M.M.; Junior, R.R. Impact of risk management on project performance: The importance of soft skills. Int. J. Prod. Res. 2014, 53, 321–340. [Google Scholar] [CrossRef]
- Söderlund, J.; Maylor, H. Project management scholarship: Relevance, impact and five integrative challenges for business and management schools. Int. J. Proj. Manag. 2012, 30, 686–696. [Google Scholar] [CrossRef]
- Raz, T.; Shenhar, A.J.; Dvir, D. Risk management, project success, and technological uncertainty. R D Manag. 2002, 32, 101–109. [Google Scholar] [CrossRef]
- Agence Nationale de la Sécurité des Systèmes d’Information (ANSSI). Digital Agility & Security: Method and Tools for Use by Project Teams (in French: Agilité & Sécurité Numériques: Méthode et Outils à l’usage des Equipes Projet); Direction Interministérielle du Numérique et du Système d’Information et de Communication de l’État (DINSIC): Paris, France, 2018.
- iObeya. Unleash the Power of Visual Management. 2020. Available online: https://www.iobeya.com/ (accessed on 29 March 2021).
- MURAL. Put Imagination to Work. Tactivos, Inc. dba MURAL. 2020. Available online: https://www.mural.co/ (accessed on 29 March 2021).
- ESME Sudria. International Graduate Program in Cybersecurity. Available online: https://www.esme.fr/en/studies-engineering-school/international-program-cybersecurity (accessed on 1 April 2021).
- FORESIGHT Project. Advanced Cyber Security Simulation Platform for Preparedness Training in Aviation, Power Grid and Naval Environments. H2020 FORESIGHT Project. 2021. Available online: https://foresight-h2020.eu/ (accessed on 9 June 2021).
- Club EBIOS. The Risk Management Forum. Club EBIOS. Available online: https://club-ebios.org/site/en/welcome/ (accessed on 16 March 2021).
- Paul, S. Obérisk: A Tooled-Up Obeya-Like Approach to Risk Management. Club EBIOS, 01. 2021. Available online: https://club-ebios.org/site/en/obeya-like-risk-management-approach/ (accessed on 12 March 2021).
- Paul, S. Obérisk: A Poster Support for an Obeya-Like Risk Management Approach. Research Gate. Available online: https://www.researchgate.net/publication/336686823_Oberisk_a_poster_support_for_an_Obeya-like_risk_management_approach (accessed on 16 March 2021).
- Chair of the Naval Cyber-Defence. Cybersecurity at the Service of the Maritime World (in French: La cybersécurité au Service du Monde Maritime). Available online: https://www.chaire-cyber-navale.fr/ (accessed on 9 June 2021).
- Annex 3 of FORESIGHT D5.3. Models for Risk Analysis and Assessment (Naval Use-Case). 2021. Available online: https://club-ebios.org/site/wp-content/uploads/productions/ClubEBIOS-Oberisk-Exemple-2021-01-07.pdf (accessed on 9 June 2021).
- European Parliament and European Council. Regulation (EU) 2016/679 of the European Parliament and of the Council of 27 April 2016 on the Protection of Natural Persons with Regard to the Processing of Personal Data and on the Free Movement of Such Data (General Data Protection Regulation). EUR-Lex. 27 April 2016. Available online: https://eur-lex.europa.eu/legal-content/EN/TXT/?uri=CELEX%3A32016R0679 (accessed on 31 March 2021).
- Bruns, K. “Negation Symbol,” Wumbo. 2021. Available online: https://wumbo.net/symbol/negation/ (accessed on 31 March 2021).
- CESG IA BIL. Extract from HMG IA Standard No.1—Business Impact Level Tables. 2009. Available online: https://www.shreddingmachines.co.uk/business-impact-tables.pdf (accessed on 25 August 2021).
- Agence Nationale de la Sécurité des Systèmes d’Information (ANSSI). EBIOS Risk Manager—Going Further; ANSSI: Paris, France, 2021.
- Lockheed Martin. The Cyber Kill Chain. Available online: https://www.lockheedmartin.com/en-us/capabilities/cyber/cyber-kill-chain.html (accessed on 6 March 2019).
- Object Management Group (OMG). About the Software & Systems Process Engineering Metamodel Specification—Version 2.0. 2008. Available online: https://www.omg.org/spec/SPEM/About-SPEM/#docs-normative-supporting (accessed on 7 April 2021).
- CESG. HMG IA Standard Numbers 1 & 2, Information Risk Management; National Technical Authority for Information Assurance: Cheltenham, UK, 2012.
- PRAETORIAN. Protection of Critical Infrastructures from Advanced Combined Cyber and Physical Threats. European Commission. Available online: https://praetorian-h2020.eu/ (accessed on 28 July 2021).
- Agence Nationale de la Sécurité des Systèmes d’Information (ANSSI). Expression of Needs and Identification of Security Objectives (EBIOS)—Risk Management Method; ANSSI: Paris, France, 2010.
- FAIR Institute. What is FAIR? 2021. Available online: https://www.fairinstitute.org/what-is-fair (accessed on 28 July 2021).








| Exercise Type | Dates and Occurrences | Number of Participants | Profile of Participants |
|---|---|---|---|
| Thales internal cybersecurity training: engineering, risk management and architecting | Mid-2016 to end 2020 94 sessions | 16–20 per session, for a total of ≈ 1700 | System engineers; system architects; integration, verification and validation engineers |
| Risk management course at engineering school | 4 sessions, 2018–2021 | 24–28 per session, for a total of ≈ 100 | Master 2 students |
| Thales internal risk management training | 3 sessions, 2019–2020 | 7–30 per session, for a total of ≈ 50 | Cybersecurity specialists |
| Thales Low Altitude Air Traffic Management use case | Mid-2018 | 3 | Senior architects; domain experts |
| Thales Air Traffic Geofencing use case | End 2018 | 3 | Senior architects; domain experts |
| Thales IoT for SCADA use case | Early 2019 | 7 | System engineers and architects; domain experts; cybersecurity expert |
| Thales Railway Signalling use case | Mid-2019 | 12 | System engineers and architects; domain experts; developers; managers; cybersecurity expert |
| Thales Cloud-Computing use case | Mid-2019 | 2 | System engineers and architects; cybersecurity expert |
| Thales In-Flight Entertainment use case | End 2020 | 5 | System engineers and architects; cybersecurity experts |
| FORESIGHT H2020 naval use case | End 2020 to mid-2021 | 7 | PhD students; domain and cybersecurity expert |
| FORESIGHT H2020 airport landside use case | Early 2021 to mid-2021 | 3 | Manager; domain expert; cybersecurity experts |
| FORESIGHT H2020 power grid use case | Early 2021 to mid-2021 | 9 | System engineers and architects; domain experts; cybersecurity experts |
| College of Practitioners of the Club EBIOS | End 2020 to early 2021 | 5 | Senior risk management practitioners |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2021 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Paul, S.; Naouar, D.; Gureghian, E. Obérisk: Cybersecurity Requirements Elicitation through Agile Remote or Face-to-Face Risk Management Brainstorming Sessions. Information 2021, 12, 349. https://doi.org/10.3390/info12090349
Paul S, Naouar D, Gureghian E. Obérisk: Cybersecurity Requirements Elicitation through Agile Remote or Face-to-Face Risk Management Brainstorming Sessions. Information. 2021; 12(9):349. https://doi.org/10.3390/info12090349
Chicago/Turabian StylePaul, Stéphane, Douraid Naouar, and Emmanuel Gureghian. 2021. "Obérisk: Cybersecurity Requirements Elicitation through Agile Remote or Face-to-Face Risk Management Brainstorming Sessions" Information 12, no. 9: 349. https://doi.org/10.3390/info12090349
APA StylePaul, S., Naouar, D., & Gureghian, E. (2021). Obérisk: Cybersecurity Requirements Elicitation through Agile Remote or Face-to-Face Risk Management Brainstorming Sessions. Information, 12(9), 349. https://doi.org/10.3390/info12090349






