1. Introduction
With the rapid development of indoor localization technologies [
1], location-based services (LBS) and applications have been a new research topic in recent years [
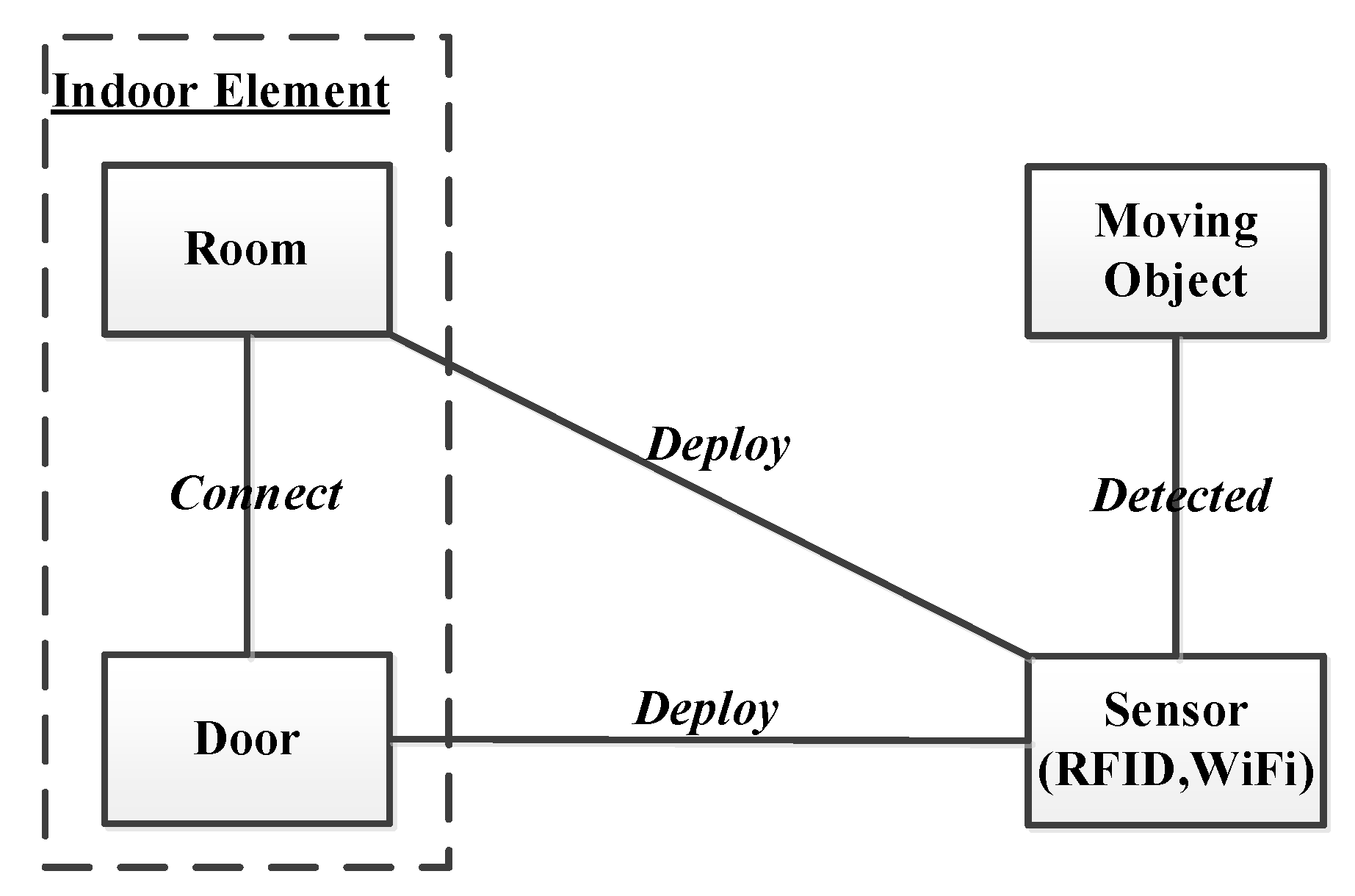
2]. Particularly, indoor localization devices make it possible to obtain people’s moving trajectories in indoor space. Such indoor moving trajectories are useful for mining decision-making knowledge in many applications. For example, a museum can find the hottest visiting places based on the historical moving trajectories of users. A shopping mall can detect the most welcoming shops according to the tracking records of its customers. All these findings are helpful for the museum and shopping mall to adjust their layout of arts/products or to recommend products, leading to the improvement of service quality.
In this study, we aim to identify highly influential positions from indoor moving trajectories inside certain indoor spaces, like shopping malls, office buildings, and airports. A typical example is to find the most influential shops in a shopping mall. We notice that the position-tracking historical data of persons in a shopping mall usually represents people’s interest in specific items, which is meant to detect highly influential positions, as, in many cases, people will not buy the same items (e.g., a refrigerator, or a wedding ring) again for a long time after they have bought one. Thus, it will be useful to tackle people’s indoor moving trajectories to know their potential buying interests. This is becoming a reality, due to the increasing deployment of indoor localization devices. For instance, most shopping malls now offer Wi-Fi services, which can be used to detect users’ position in indoor space.
However, it is not a trivial task to detect highly influential positions from indoor moving trajectories [
3]. The challenges are twofold. First, the positions in a specific indoor space are typically not visited by users equally. Taking a hotel as an example, the first floor usually has more visits than others, because all people have to visit the first floor when entering the hotel. In addition, some special positions, such as elevator rooms, are frequently visited. Thus, we cannot simply calculate the visiting number of indoor positions to detect influential positions. Second, the influence of an indoor position does not simply rely on the count of visits. The number of different users can reflect the covering range of users. Thus, it is necessary to consider both the visitor count and the number of users when detecting highly influential positions in indoor space.
Aiming to effectively detect highly influential positions from indoor moving trajectories, in this paper, we first formulate the problem and analyze three baseline solutions. Then, we propose a new algorithm, called H-Count. Furthermore, we present an improved version of H-Count, named H-Count*, which is demonstrated to be more effective than H-Count. Briefly, we make the following contributions in this paper:
- (1)
We formulate the problem of detecting highly influential positions from indoor moving trajectories and present three baseline solutions.
- (2)
Motivated by the H-index in the evaluation of authors/journals, we propose a new algorithm called H-Count for detecting highly influential indoor positions. H-Count adopts a similar idea to H-index and develops a mechanism to evaluate the influence of indoor positions. The greatest advantage of H-Count is that it does not only consider the visitor count but also considers the different visitors.
- (3)
We further present an improvement for H-Count, denoted H-Count*, by taking a filtering step to remove unqualified trajectories. This is based on the observation that a lot of visits to a location such as a gate are meaningless for the detection of influential indoor positions.
- (4)
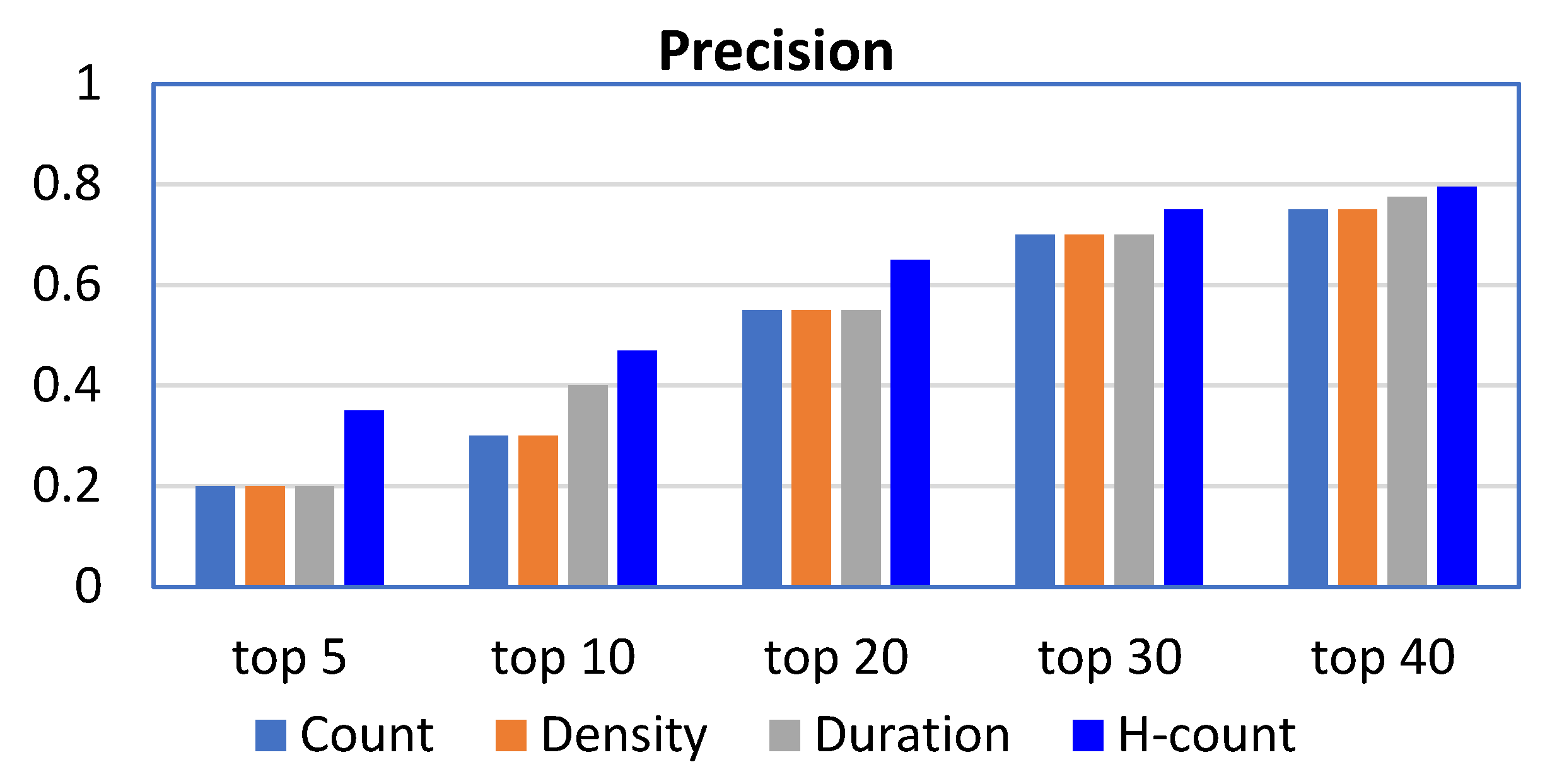
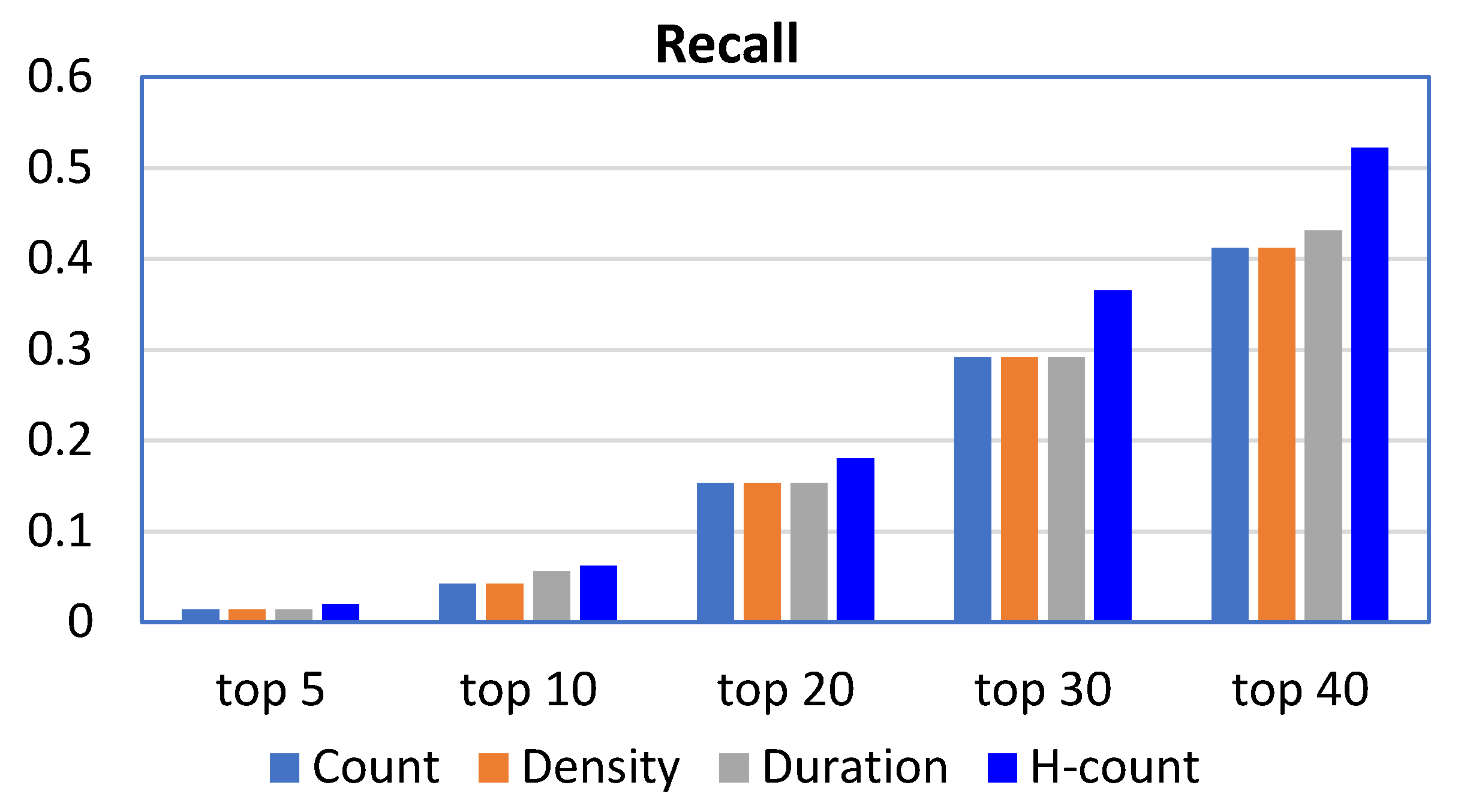
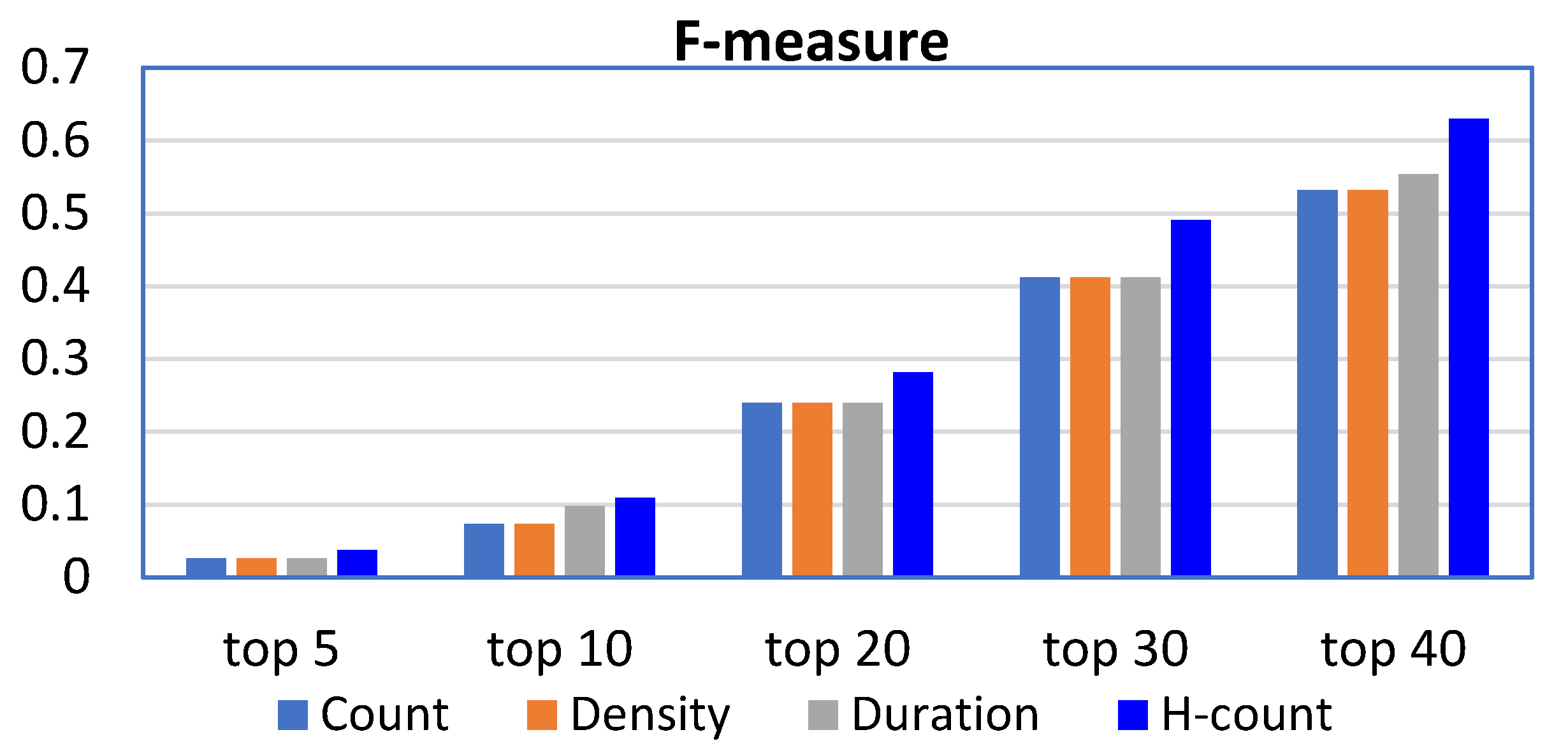
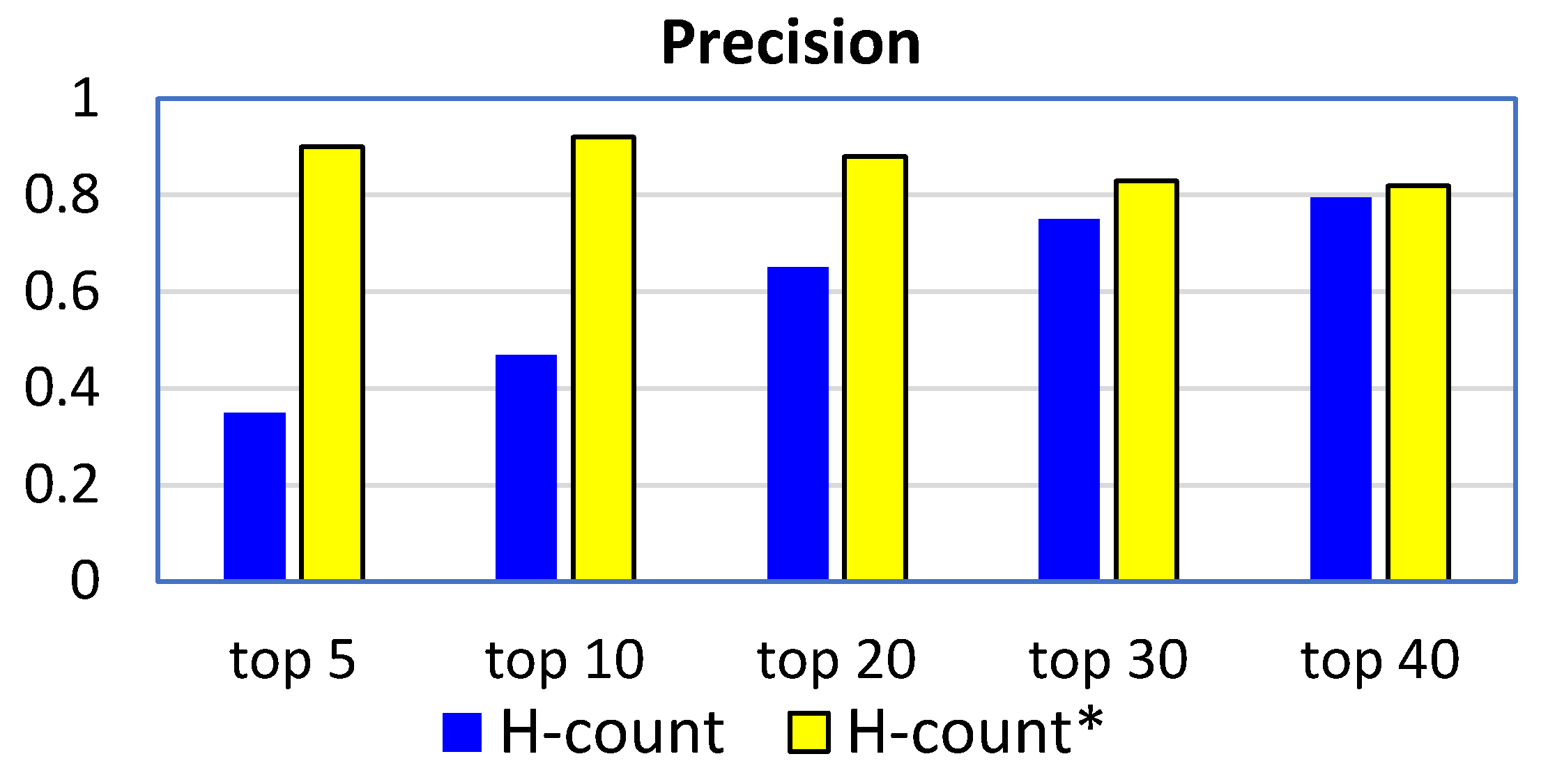
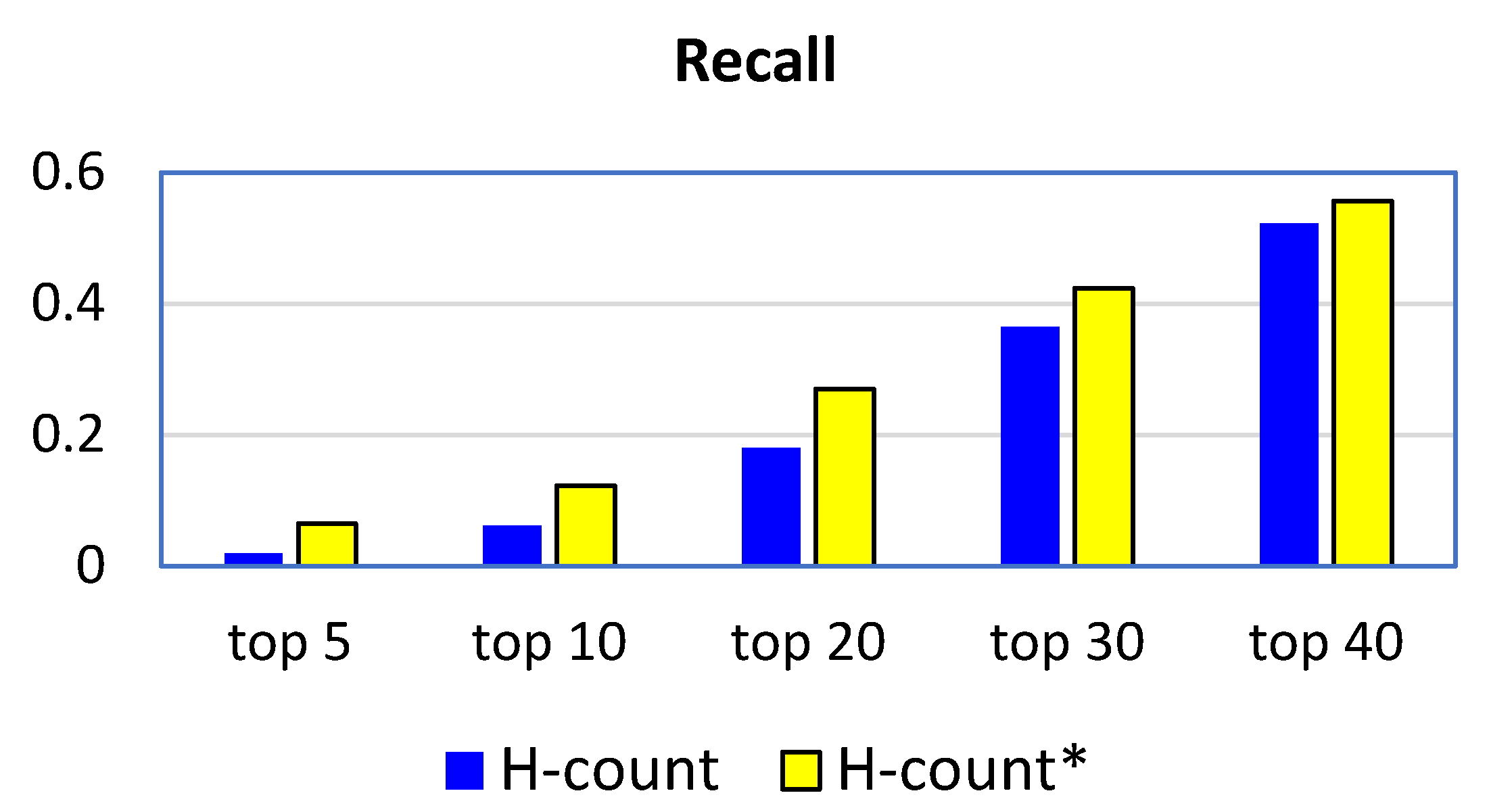
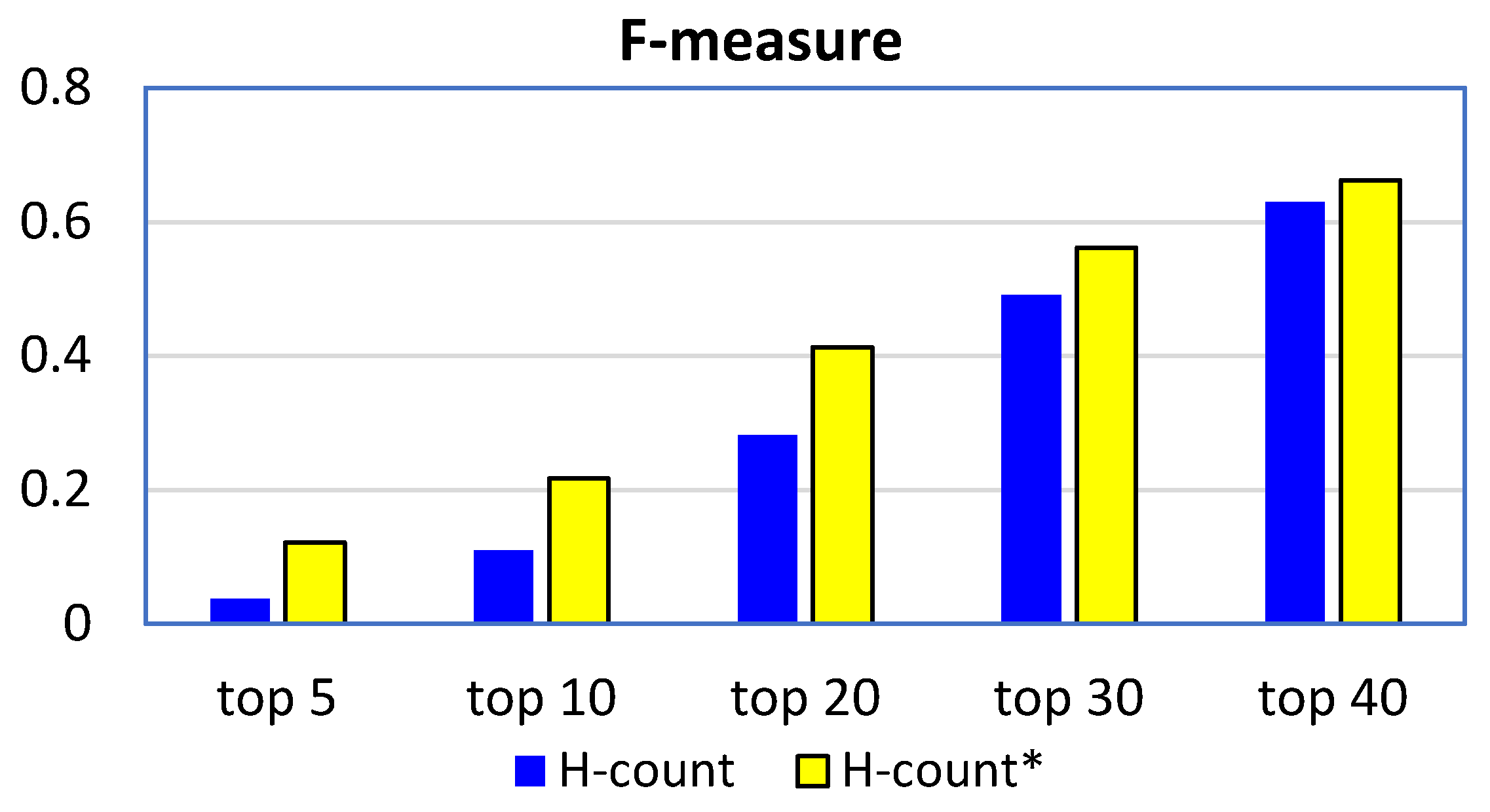
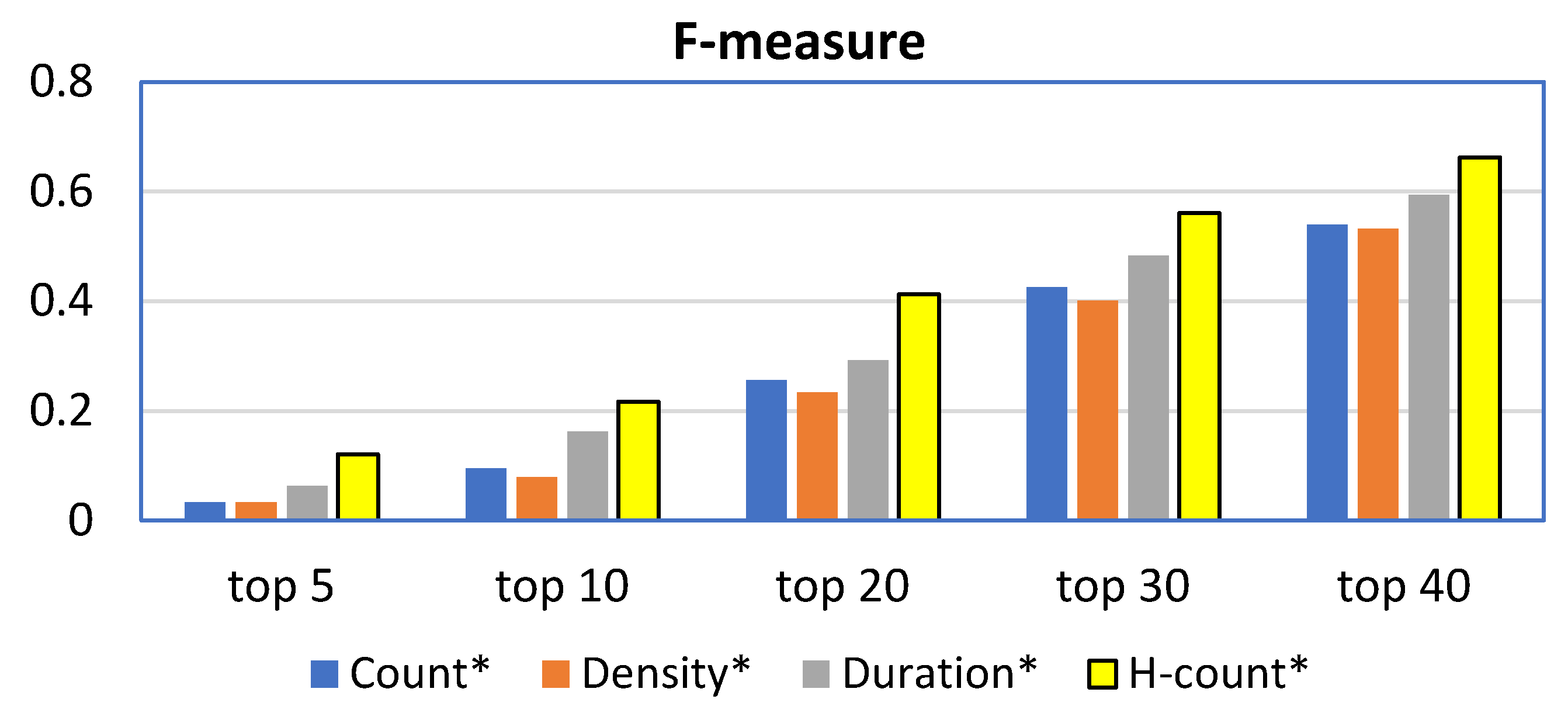
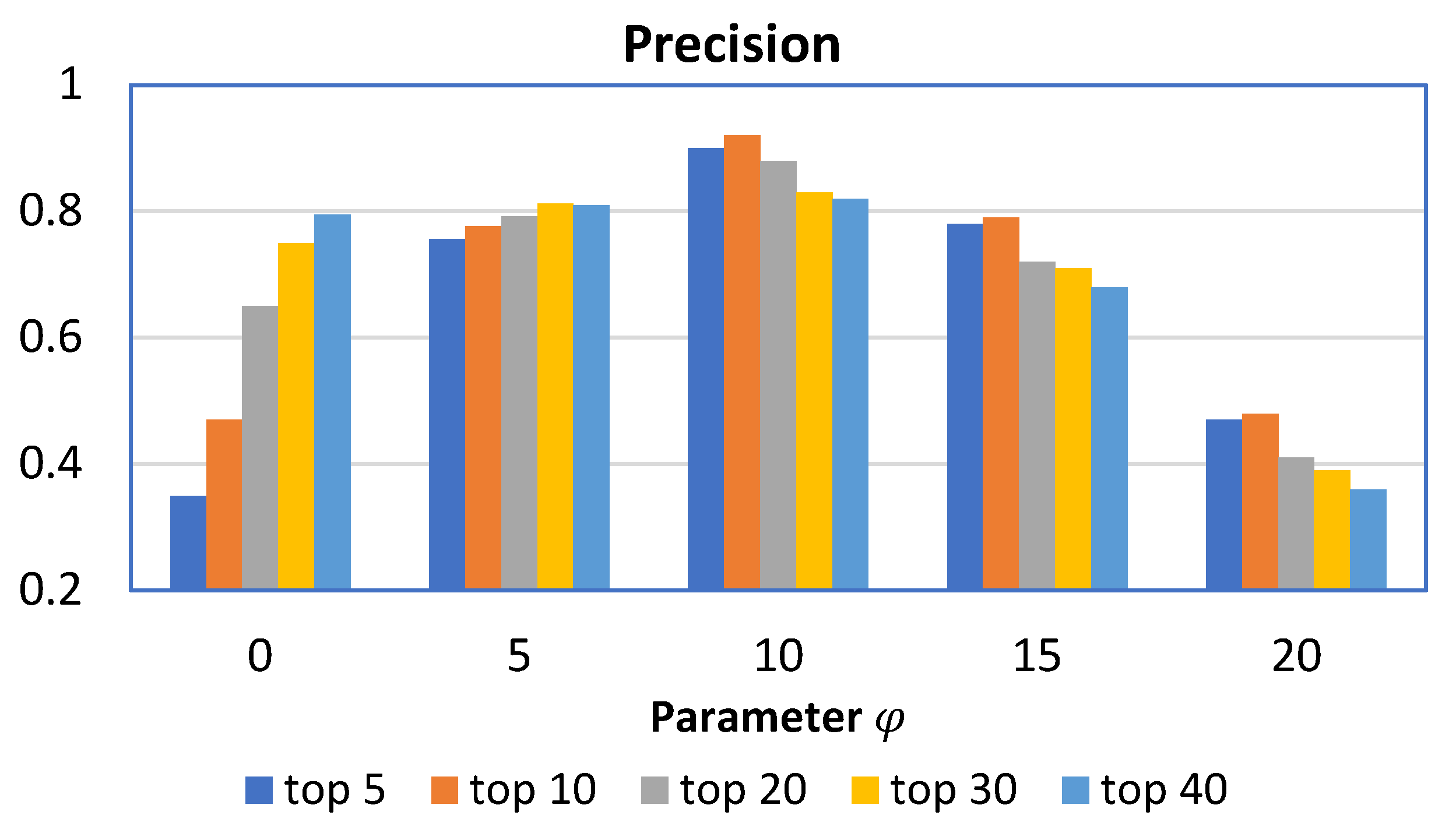
We conducted experiments on trajectory data in a simulated indoor space with RFID readers and compared our H-Count and H-Count* with three baseline algorithms. The results in terms of precision, recall, and F-measure show that H-Count outperforms all baselines and H-Count* can further improve the performance of H-Count by 113% on average.
The remainder of the paper is structured as follows. In
Section 2, we briefly describe the preliminaries and related work of this study. In
Section 3, we analyze the baseline algorithms. In
Section 4, we present the H-Count algorithm.
Section 5 details the H-Count* algorithm.
Section 6 reports the experimental results, and, finally, in
Section 7, we conclude the paper.
Author Contributions
Y.J., conceptualization, data curation, methodology, validation, writing—original draft preparation; L.C., funding acquisition, project administration, supervision, and writing—review and editing. All authors have read and agreed to the published version of the manuscript.
Funding
This research was funded by the National Science Foundation of China (grant number: 91846205).
Acknowledgments
We would like to thank the editors and anonymous reviewers for their suggestions and comments to improve the quality of the paper.
Conflicts of Interest
The authors declare no conflict of interest. The funders had no role in the design of the study; in the collection, analyses, or interpretation of data; in the writing of the manuscript; or in the decision to publish the results.
References
- Li, J.; Feng, G.; Wei, W.; Luo, C.; Cheng, L.; Wang, H.; Ming, Z. PSOTrack: A RFID-Based System for Random Moving Objects Tracking in Unconstrained Indoor Environment. IEEE Internet Things J. 2018, 5, 4632–4641. [Google Scholar] [CrossRef]
- Jin, P.; Zhang, L.; Zhao, J.; Zhao, L.; Yue, L. Semantics and Modeling of Indoor Moving Objects. Int. J. Multimed. Ubiquitous Eng. 2012, 7, 153–158. [Google Scholar]
- Zhang, X.; Jin, P.; Yue, L.; Wang, N.; Li, Q. Towards Mobile Information Systems for Indoor Space. Mobile Inf. Syst. 2016. [Google Scholar] [CrossRef]
- Jin, P.; Cui, T.; Wang, Q.; Jensen, C. Effective Similarity Search on Indoor Moving-Object Trajectories. In Proceedings of the 21st International Conference on Database Systems for Advanced Applications (DASFAA 2016), Dallas, TX, USA, 16–19 April 2016; pp. 181–197. [Google Scholar]
- Luo, W.; Jin, P.; Yue, L. Time-Constrained Sequenced Route Query in Indoor Spaces. In Proceedings of the 18th Asia-Pacific Web conference (APWeb 2016), Suzhou, China, 23–25 September 2016; pp. 129–140. [Google Scholar]
- Jeong, S.; Jo, H.; Kang, S. Self-Organizing Distributed Architecture Supporting Dynamic Space Expanding and Reducing in Indoor LBS Environment. Sensors 2015, 15, 12156–12179. [Google Scholar] [CrossRef] [PubMed]
- Lu, H.; Cheema, M. Indoor data management. In Proceedings of the ICDE 2016: International Conference on Data Engineering, Helsinki, Finland, 16–20 May 2016; pp. 1414–1417. [Google Scholar]
- Sakai, K.; Sun, M.; Ku, W.; Lu, H.; Lai, T. Data Verification in Integrated RFID Systems. IEEE Syst. J. 2019, 13, 1969–1980. [Google Scholar] [CrossRef]
- Ma, Q.; Li, X.; Li, G.; Ning, B.; Bai, M.; Wang, X. MRLIHT: Mobile RFID-Based Localization for Indoor Human Tracking. Sensors 2020, 20, 1711. [Google Scholar] [CrossRef] [PubMed]
- Jensen, C.; Lu, H.; Yang, B. Indoor—A New Data Management Frontier. IEEE Data Eng. Bull. 2010, 33, 12–17. [Google Scholar]
- Alvares, L.; Bogorny, V.; Kuijpers, B.; de Macedo, J.A.F.; Moelans, B.; Vaisman, A. A Model for Enriching Trajectories with Semantic Geographical Information. In Proceedings of the 15th ACM International Symposium on Advances in Geographic Information Systems, Seattle, WA, USA, 7–9 November 2007; pp. 21–22. [Google Scholar]
- Valdés, F.; Güting, R. A Framework for Efficient Multi-Attribute Movement Data Analysis. VLDB J. 2019, 28, 427–449. [Google Scholar] [CrossRef]
- Bermingham, L.; Lee, I. Mining Place-Matching Patterns from Spatio-Temporal Trajectories using Complex Real-World Places. Expert Syst. Appl. 2019, 122, 334–350. [Google Scholar] [CrossRef]
- Hussein, S.; Lu, H.; Pedersen, T. Reasoning about RFID-Tracked Moving Objects in Symbolic Indoor Spaces. In Proceedings of the SSDBM, 2013: Conference on Scientific and Statistical Database Management, Baltimore, MD, USA, 1–12 July 2013. [Google Scholar]
- Ahmed, T.; Pedersen, T.; Lu, H. Finding Dense Locations in Symbolic Indoor Tracking Data: Modeling, Indexing, and Processing. GeoInformatica 2017, 21, 119–150. [Google Scholar] [CrossRef]
- Ahmed, T.; Pedersen, T.; Lu, H. Finding Dense Locations in Indoor Tracking Data. In Proceedings of the IEEE 15th International Conference on Mobile Data Management, MDM 2014, Brisbane, Australia, 14–18 July 2014; pp. 189–194. [Google Scholar]
- Li, H.; Lu, H.; Shou, L.; Chen, G.; Chen, K. In Search of Indoor Dense Regions: An Approach Using Indoor Positioning Data. In Proceedings of the 35th IEEE International Conference on Data Engineering, Macao, China, 8–11 April 2019; pp. 2127–2128. [Google Scholar]
- Jin, P.; Du, J.; Huang, C.; Wan, S.; Yue, L. Detecting Hotspots from Trajectory Data in Indoor Spaces. In Proceedings of the 20th International Conference on. Database Systems for Advanced Applications (DASFAA 2015), Hanoi, Vietnam, 20–23 April 2015; pp. 209–225. [Google Scholar]
- Hirsch, J. An Index to Quantify an Individuals Scientific Research Output. PNAS 2005, 102, 16569–16572. [Google Scholar] [CrossRef]
- Huang, C.; Jin, P.; Wang, H.; Wang, N.; Wan, S.; Yue, L. IndoorSTG: A Flexible Tool to Generate Trajectory Data for Indoor Moving Objects. In Proceedings of the 14th International Conference on Mobile Data Management, Milan, Italy, 3–6 June 2013; pp. 341–343. [Google Scholar]
- Manning, C.; Raghavanm, P.; Schütze, H. An Introduction to Information Retrieval; Cambridge University Press: Cambridge, UK, 2008. [Google Scholar]
- Liu, F.; Liu, J.; Yin, Y.; Wang, W.; Hu, D.; Chen, P.; Niu, Q. Survey on WiFi-Based Indoor Positioning Techniques. IET Commun. 2020, 14, 1372–1383. [Google Scholar] [CrossRef]
- Zhong, Y.; Wang, T.; Gan, C.; Luo, X. The Location Privacy Preserving Scheme Based on Hilbert Curve for Indoor LBS. In Proceedings of the 10th International Conference on Systematic Innovation (ICSI) & Global Competition on Systematic Innovation (GCSI), Liverpool, UK, 8–11 July 2019; pp. 387–399. [Google Scholar]
- Naghizade, E.; Kulik, L.; Tanin, E.; Bailey, J. Privacy- and Context-Aware Release of Trajectory Data. ACM Trans. Spat. Algorithms Syst. 2020, 6, 25. [Google Scholar] [CrossRef]
- Sun, G.; Song, L.; Liao, D.; Yu, H.; Chang, V. Towards Privacy Preservation for “Check-In” Services in Location-Based Social Networks. Inf. Sci. 2019, 481, 616–634. [Google Scholar] [CrossRef]
- Wang, W.; Gong, Z.; Zhang, J.; Lu, H.; Ku, W. On Location Privacy in Fingerprinting-based Indoor Positioning System: An Encryption Approach. In Proceedings of the ACM SIGSPATIAL International Conference on Advances in Geographic Information Systems 2019 (ACM SIGSPATIAL 2019), Chicago, IL, USA, 5–8 November 2019; pp. 289–298. [Google Scholar]
- Eshun, S.; Palmieri, P. A Privacy-Preserving Protocol for Indoor Wi-Fi Localization. In Proceedings of the ACM International Conference on Computing Frontiers—Malicious Software and Hardware in Internet of Things (MAL-IoT 2019), Alghero, Italy, 30 April–2 May 2019; pp. 380–385. [Google Scholar]
- Li, G.; Gomez, R.; Nakamura, K.; He, B. Human-Centered Reinforcement Learning: A Survey. IEEE Trans. Human-Mach. Syst. 2019, 49, 337–349. [Google Scholar] [CrossRef]
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).