Intrusion Detection in IoT Networks Using Deep Learning Algorithm
Abstract
1. Introduction
2. Security and Deep-Learning Method
2.1. IoT Protection
2.2. IoT Threat
2.2.1. Cyber Threats
2.2.2. Threats to the Physical
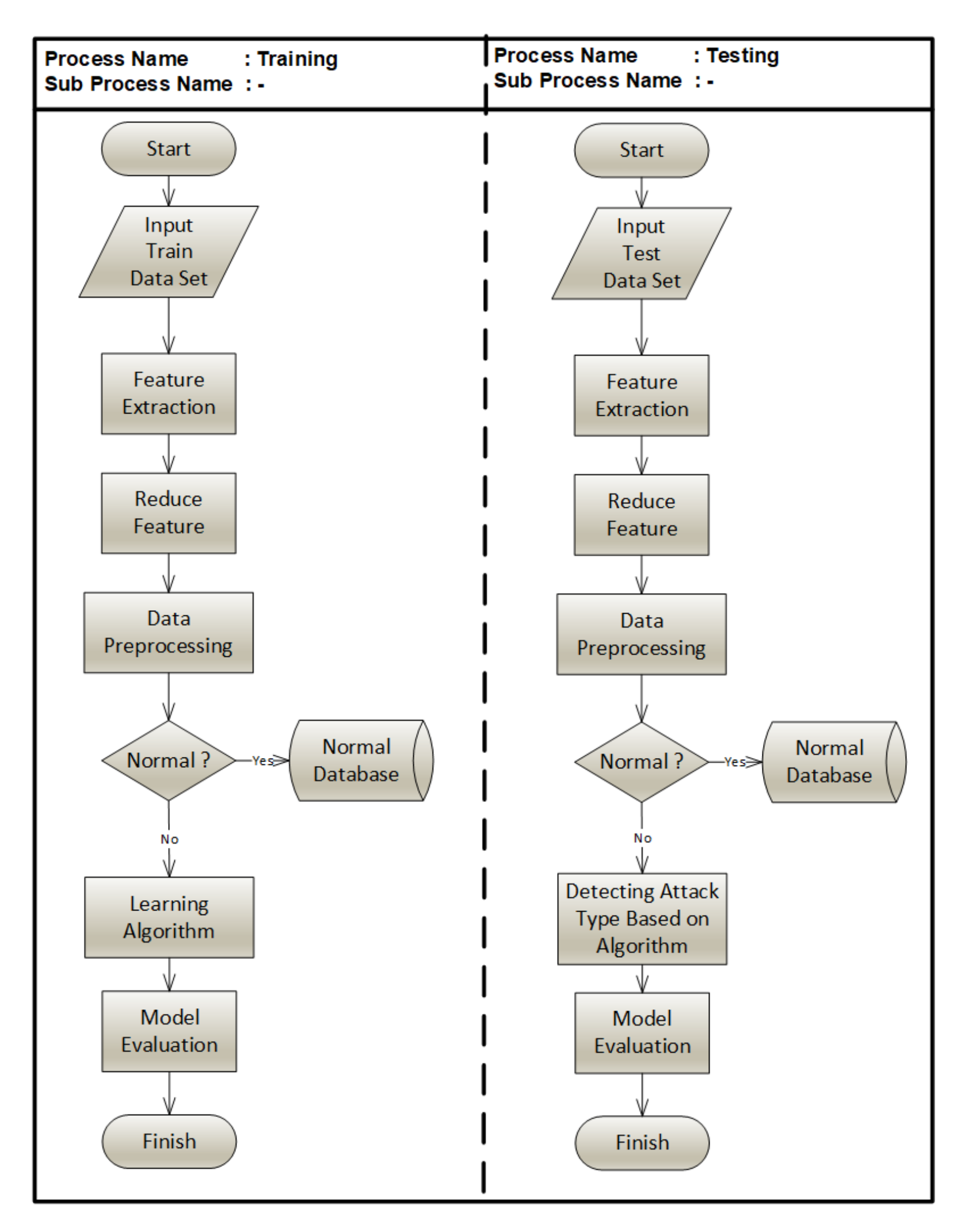
3. Method of Machine-Learning Application in IoT Security
3.1. Dataset Description
3.2. Machine-Learning and Deep-Learning Anomaly Detection
3.2.1. Random Forests
3.2.2. Support Vector Machine (SVM)
3.2.3. Multilayer Perceptron
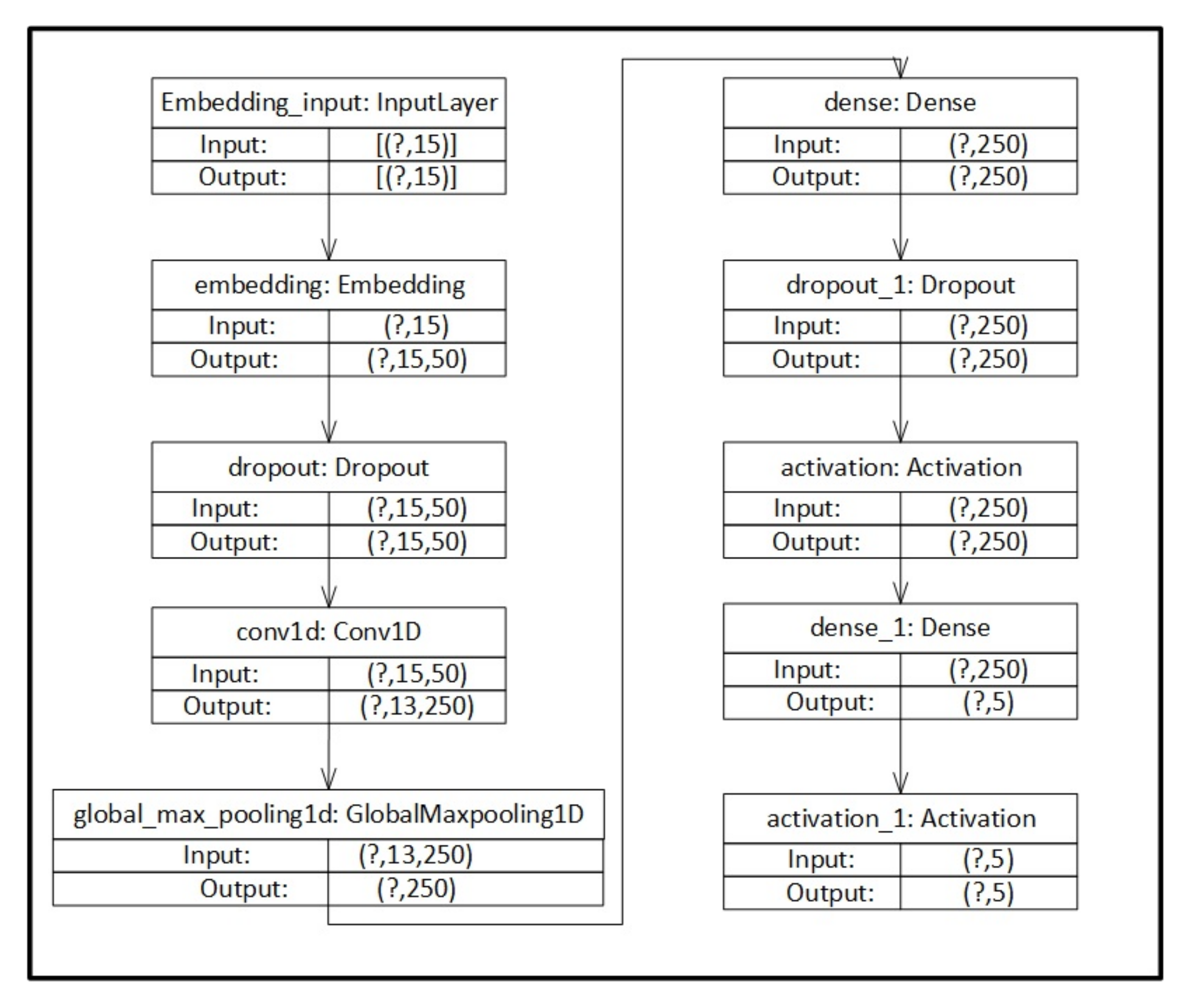
3.2.4. Convolutional Neural Network
3.3. Evaluation Criteria
- Embedding blocks, to apply context.
- Convolution and max-pooling blocks, for extracting dataset features.
- Dense and activation blocks, for learning and classification.
4. Results
5. Conclusions
Author Contributions
Funding
Acknowledgments
Conflicts of Interest
References
- Roopak, M.; Tian, G.Y.; Chambers, J. Deep Learning Models for Cyber Security in IoT Networks. In Proceedings of the 2019 IEEE 9th Annual Computing and Communication Workshop and Conference (CCWC), Las Vegas, NV, USA, 7–9 January 2019; pp. 452–457. [Google Scholar] [CrossRef]
- Yuan, X.; Li, C.; Li, X. DeepDefense: Identifying DDoS Attack via Deep Learning. In Proceedings of the 2017 IEEE International Conference on Smart Computing (SMARTCOMP), Hong Kong, China, 29–31 May 2017; pp. 1–8. [Google Scholar] [CrossRef]
- Evans, D. The Internet of Things: How the Next Evolution of the Internet Is Changing Everything; Cisco Internet Business Solutions Group (IBSG): San Jose, CA, USA, 2011. [Google Scholar]
- Kolias, C.; Kambourakis, G.; Stavrou, A.; Voas, J. DDoS in the IoT: Mirai and Other Botnets. Computer 2017, 50, 80–84. [Google Scholar] [CrossRef]
- Radanliev, P. Future developments in cyber risk assessment for the internet of things. Comput. Ind. 2018, 102, 14–22. [Google Scholar] [CrossRef]
- Bertino, E.; Islam, N. Botnets and Internet of Things Security. Computer 2017, 50, 76–79. [Google Scholar] [CrossRef]
- Al-Garadi, M.A.; Mohamed, A.; Al-Ali, A.; Du, X.; Guizani, M. A Survey of Machine and Deep Learning Methods for Internet of Things (IoT) Security. arXiv 2018, arXiv:1807.11023. Available online: https://ui.adsabs.harvard.edu/abs/2018arXiv180711023A (accessed on 2 January 2020).
- Okpe, O.A. Intrusion Detection in Internet of Things (Iot). Int. J. Adv. Res. Comput. Sci. 2018, 9, 504–509. [Google Scholar] [CrossRef]
- Meidan, Y. ProfilIoT. In Proceedings of the Symposium on Applied Computing—SAC ‘17, Marrakech, Morocco, 4–6 April 2017. [Google Scholar]
- Anthi, E.; Williams, L.; Slowinska, M.; Theodorakopoulos, G.; Burnap, P. A Supervised Intrusion Detection System for Smart Home IoT Devices. IEEE Internet Things J. 2019, 6, 9042–9053. [Google Scholar] [CrossRef]
- Azmoodeh, A.; Dehghantanha, A.; Choo, K.-K.R. Robust Malware Detection for Internet of (Battlefield) Things Devices Using Deep Eigenspace Learning. IEEE Trans. Sustain. Comput. 2019, 4, 88–95. [Google Scholar] [CrossRef]
- Hajiheidari, S.; Wakil, K.; Badri, M.; Navimipour, N.J. Intrusion detection systems in the Internet of things: A comprehensive investigation. Comput. Netw. 2019, 160, 165–191. [Google Scholar] [CrossRef]
- Radanliev, P. Future developments in standardisation of cyber risk in the Internet of Things (IoT). SN Appl. Sci. 2020, 2. [Google Scholar] [CrossRef]
- Nicolescu, R.; Huth, M.; Radanliev, P.; de Roure, D. Mapping the Values of IoT. J. Inf. Technol. 2019, 33, 345–360. [Google Scholar] [CrossRef]
- Elrawy, M.F.; Awad, A.I.; Hamed, H.F.A. Intrusion detection systems for IoT-based smart environments: A survey. J. Cloud Comput. 2018, 7. [Google Scholar] [CrossRef]
- Jan, S.U.; Ahmed, S.; Shakhov, V.; Koo, I. Toward a Lightweight Intrusion Detection System for the Internet of Things. IEEE Access 2019, 7, 42450–42471. [Google Scholar] [CrossRef]
- Abomhara, M.; Koien, G.M. Cyber Security and the Internet of Things: Vulnerabilities, Threats, Intruders and Attacks. J. Cyber Secur. Mobil. 2015, 4, 65–88. [Google Scholar] [CrossRef]
- Alaba, F.A.; Othman, M.; Hashem, I.A.T.; Alotaibi, F. Internet of Things security: A survey. J. Netw. Comput. Appl. 2017, 88, 10–28. [Google Scholar] [CrossRef]
- Diro, A.A.; Chilamkurti, N. Distributed attack detection scheme using deep learning approach for Internet of Things. Future Gener. Comput. Syst. 2018, 82, 761–768. [Google Scholar] [CrossRef]
- Ge, M.; Fu, X.; Syed, N.; Baig, Z.; Teo, G.; Robles-Kelly, A. Deep Learning-Based Intrusion Detection for IoT Networks. In Proceedings of the 2019 IEEE 24th Pacific Rim International Symposium on Dependable Computing (PRDC), Kyoto, Japan, 1–3 December 2019. [Google Scholar]
- Thamilarasu, G.; Chawla, S. Towards Deep-Learning-Driven Intrusion Detection for the Internet of Things. Sensors 2019, 19, 1977. [Google Scholar] [CrossRef]
- Yin, C.; Zhu, Y.; Fei, J.; He, X. A Deep Learning Approach for Intrusion Detection Using Recurrent Neural Networks. IEEE Access 2017, 5, 21954–21961. [Google Scholar] [CrossRef]
- Rhode, M.; Burnap, P.; Jones, K. Early-stage malware prediction using recurrent neural networks. Comput. Secur. 2018, 77, 578–594. [Google Scholar] [CrossRef]
- Kaur, S.; Singh, M. Hybrid intrusion detection and signature generation using Deep Recurrent Neural Networks. Neural Comput. Appl. 2019. [Google Scholar] [CrossRef]
- Vishwakarma, R.; Jain, A.K. A survey of DDoS attacking techniques and defence mechanisms in the IoT network. Telecommun. Syst. 2019, 73, 3–25. [Google Scholar] [CrossRef]
- Xia, S.; Guo, S.; Bai, W.; Qiu, J.; Wei, H.; Pan, Z. A New Smart Router-Throttling Method to Mitigate DDoS Attacks. IEEE Access 2019, 7, 107952–107963. [Google Scholar] [CrossRef]
- Cvitić, I.; Peraković, D.; Periša, M.; Botica, M. Novel approach for detection of IoT generated DDoS traffic. Wirel. Netw. 2019. [Google Scholar] [CrossRef]
- Siboni, S. Security Testbed for Internet-of-Things Devices. IEEE Trans. Reliab. 2019, 68, 23–44. [Google Scholar] [CrossRef]
- Restuccia, F.; D’Oro, S.; Melodia, T. Securing the Internet of Things in the Age of Machine Learning and Software-Defined Networking. IEEE Internet Things J. 2018, 5, 4829–4842. [Google Scholar] [CrossRef]
- Doshi, R.; Apthorpe, N.; Feamster, N. Machine Learning DDoS Detection for Consumer Internet of Things Devices. In Proceedings of the 2018 IEEE Security and Privacy Workshops (SPW), San Francisco, CA, USA, 24 May 2018. [Google Scholar]
- Moh, M.; Raju, R. Machine Learning Techniques for Security of Internet of Things (IoT) and Fog Computing Systems. In Proceedings of the 2018 International Conference on High Performance Computing & Simulation (HPCS), Orleans, France, 16–20 July 2018. [Google Scholar]
- Li, C. Detection and defense of DDoS attack-based on deep learning in OpenFlow-based SDN. Int. J. Commun. Syst. 2018, 31. [Google Scholar] [CrossRef]
- Jia, B.; Huang, X.; Liu, R.; Ma, Y. A DDoS Attack Detection Method Based on Hybrid Heterogeneous Multiclassifier Ensemble Learning. J. Electr. Comput. Eng. 2017, 2017, 1–9. [Google Scholar] [CrossRef]
- Nawir, M.; Amir, A.; Yaakob, N.; Lynn, O.B. Internet of Things (IoT): Taxonomy of security attacks. In Proceedings of the 2016 3rd International Conference on Electronic Design (ICED), Phuket, Thailand, 11–12 August 2016; pp. 321–326. [Google Scholar] [CrossRef]
- Koroniotis, N.; Moustafa, N.; Sitnikova, E.; Turnbull, B. Towards the development of realistic botnet dataset in the Internet of Things for network forensic analytics: Bot-IoT dataset. Future Gener. Comput. Syst. 2019, 100, 779–796. [Google Scholar] [CrossRef]
- Berman, D.; Buczak, A.; Chavis, J.; Corbett, C. A Survey of Deep Learning Methods for Cyber Security. Information 2019, 10, 122. [Google Scholar] [CrossRef]
- Baig, Z.A.; Sanguanpong, S.; Firdous, S.N.; Vo, V.N.; Nguyen, T.G.; So-In, C. Averaged dependence estimators for DoS attack detection in IoT networks. Future Gener. Comput. Syst. 2020, 102, 198–209. [Google Scholar] [CrossRef]
- Hasan, M.; Islam, M.M.; Zarif, M.I.I.; Hashem, M.M.A. Attack and anomaly detection in IoT sensors in IoT sites using machine learning approaches. Internet Things 2019, 7. [Google Scholar] [CrossRef]
- Buczak, A.L.; Guven, E. A Survey of Data Mining and Machine Learning Methods for Cyber Security Intrusion Detection. IEEE Commun. Surv. Tutor. 2016, 18, 1153–1176. [Google Scholar] [CrossRef]
- Fiore, U.; Palmieri, F.; Castiglione, A.; de Santis, A. Network anomaly detection with the restricted Boltzmann machine. Neurocomputing 2013, 122, 13–23. [Google Scholar] [CrossRef]
- Chen, Y.; Zhang, Y.; Maharjan, S.; Alam, M.; Wu, T. Deep Learning for Secure Mobile Edge Computing in Cyber-Physical Transportation Systems. IEEE Netw. 2019, 33, 36–41. [Google Scholar] [CrossRef]
- Hiromoto, R.E.; Haney, M.; Vakanski, A. A secure architecture for IoT with supply chain risk management. In Proceedings of the 2017 9th IEEE International Conference on Intelligent Data Acquisition and Advanced Computing Systems: Technology and Applications (IDAACS), Bucharest, Romania, 21–23 September 2017; Volume 1, pp. 431–435. [Google Scholar] [CrossRef]
- Vinayakumar, R.; Alazab, M.; Soman, K.P.; Poornachandran, P.; Al-Nemrat, A.; Venkatraman, S. Deep Learning Approach for Intelligent Intrusion Detection System. IEEE Access 2019, 7, 41525–41550. [Google Scholar] [CrossRef]
| Categorized | Attack | Port | Tools | Number |
|---|---|---|---|---|
| Information gathering | Service scanning | Nmap, hping3 | 1,463,364 | |
| OS Finger Printing | Nmap, xprobe2 | 358,275 | ||
| Denial of service | DDoS | TCP | hping3 | 19,547,603 |
| UDP | hping3 | 18,965,106 | ||
| HTTP | golden-eye | 19,771 | ||
| DoS | TCP | hping3 | 12,315,997 | |
| UDP | hping3 | 20,659,491 | ||
| HTTP | golden-eye | 29,706 | ||
| Information theft | Keylogging | Metasploit | 1469 | |
| Data theft | Metasploit | 118 | ||
| Total | 73,360,900 |
| Algorithm | Batch Size | Activation Function | Optimizer | Epochs |
|---|---|---|---|---|
| Convolutional Neural Network (CNN) | 32, 64, 128 | ReLU and softmax | Adam | 10, 30, 50 |
| Multilayer Perceptron (MLP) | 32, 64, 128 | ReLU and softmax | Adam | 10, 30, 50 |
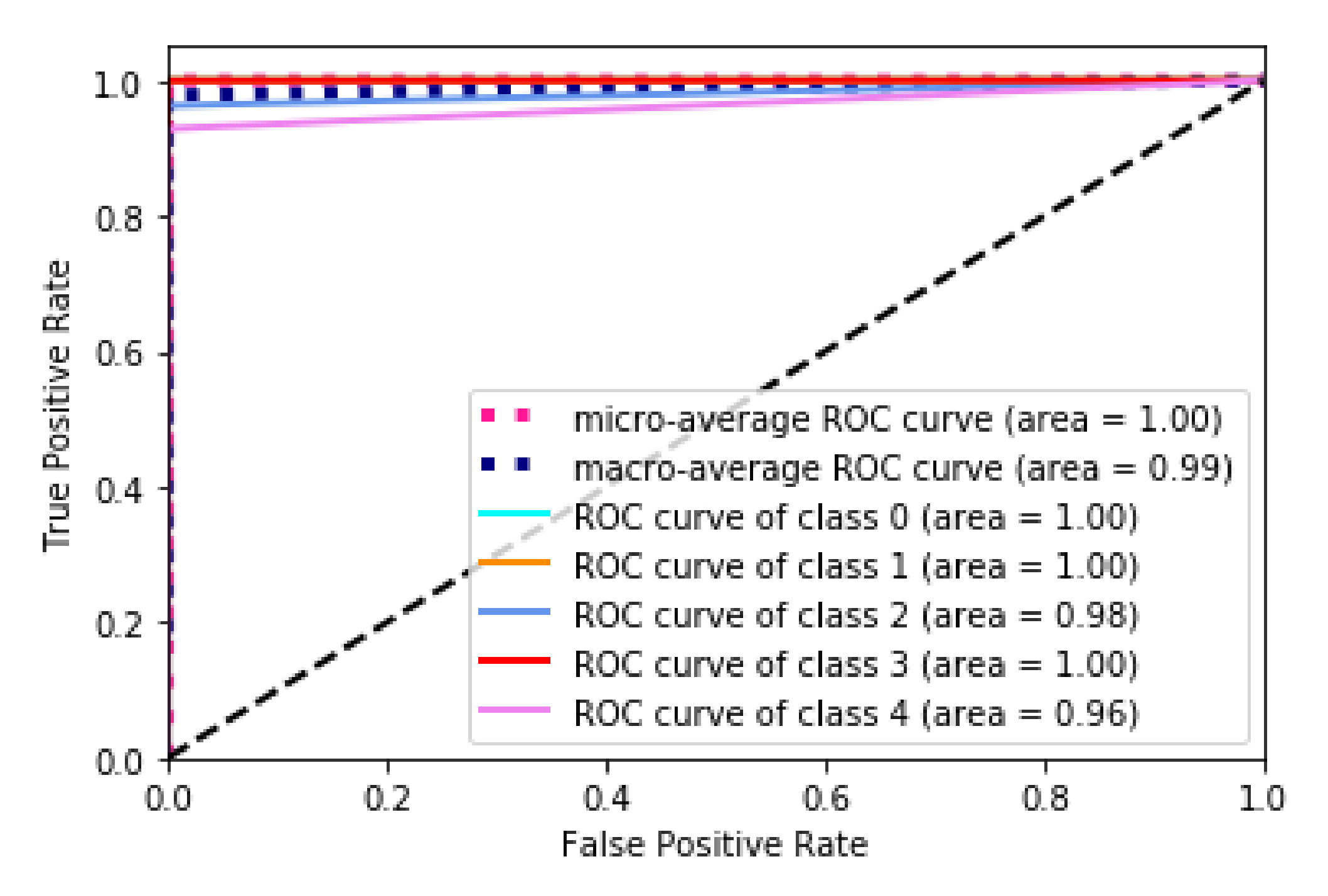
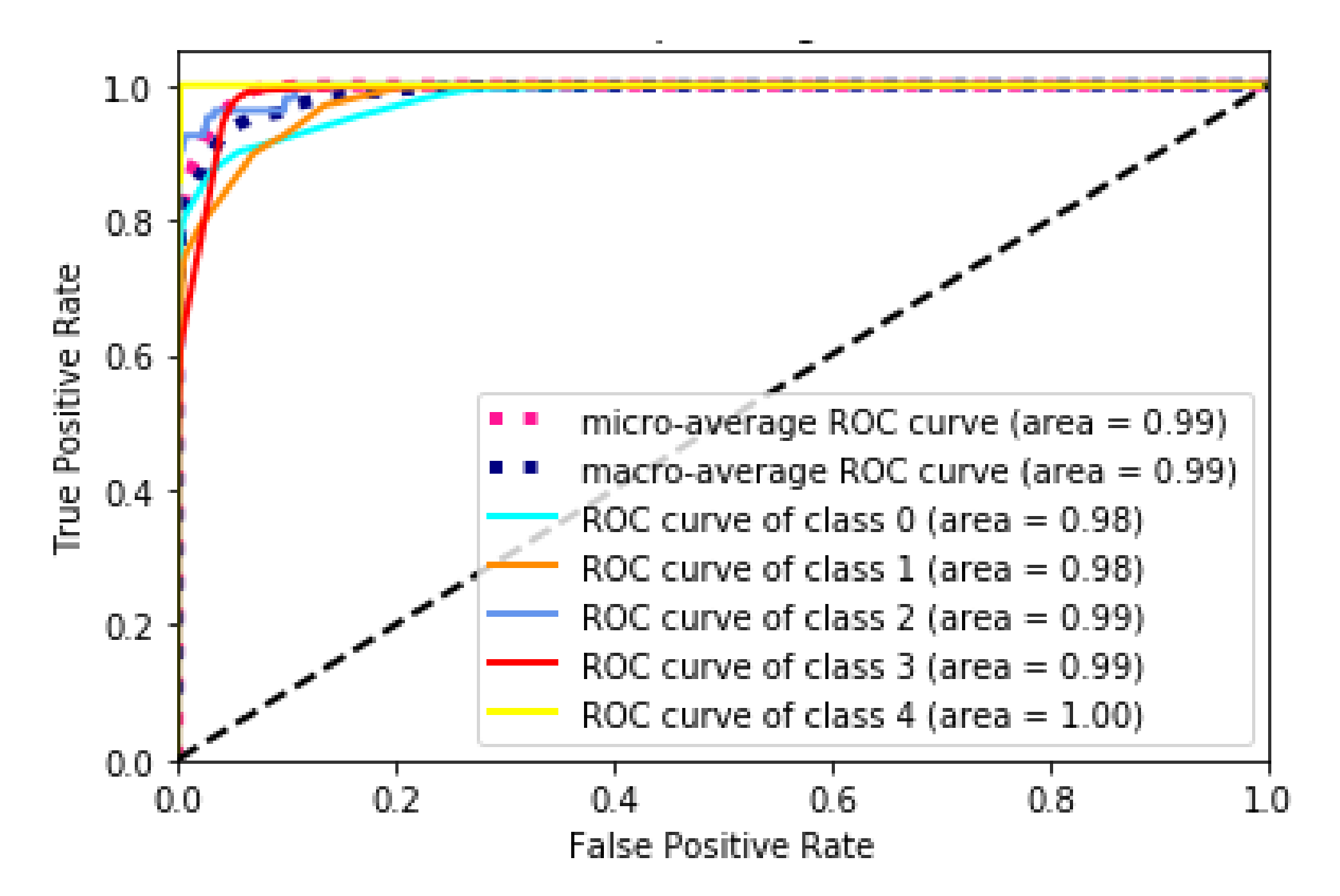
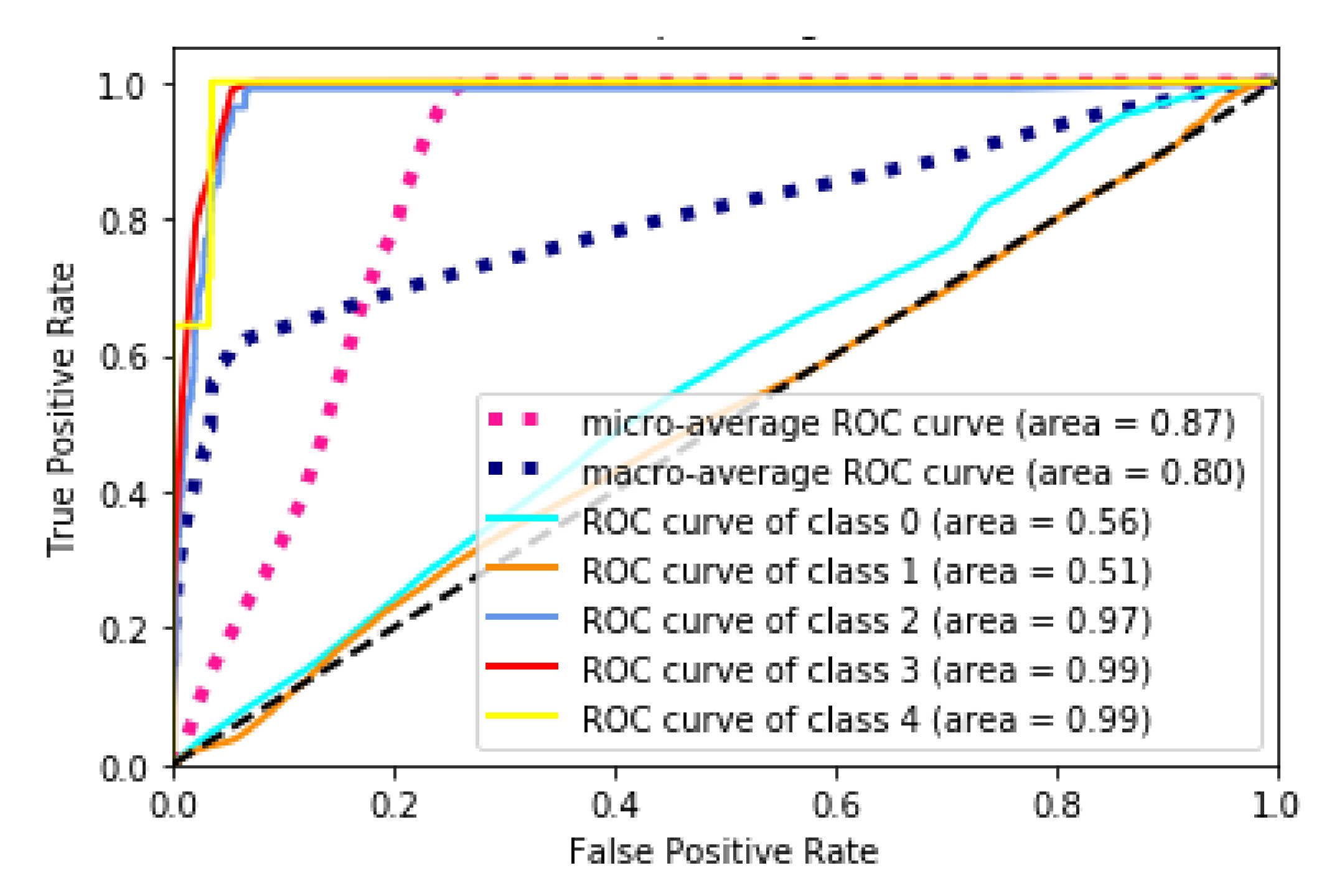
| Algorithm | Metrics | ||||
|---|---|---|---|---|---|
| AUC DDOS | AUC DOS | AUC Reconnaissance | AuC Normal | AUC Theft | |
| Random Forests (RF) | 1 | 1 | 0.98 | 1 | 0.96 |
| CNN | 0.98 | 0.98 | 0.99 | 0.99 | 1 |
| MLP | 0.56 | 0.51 | 0.97 | 0.99 | 0.99 |
| Algorithm | Epoch | Mean Accuracy | Elapsed Time |
|---|---|---|---|
| CNN | 10 | 90.85% | 59 min 38 s |
| MLP | 10 | 53.07% | 37 min 8 s |
| CNN | 30 | 89.82% | 155 min 29 s |
| MLP | 30 | 62.95% | 122 min 33 s |
| CNN | 50 | 88.30% | 227 min 21 s |
| MLP | 50 | 62% | 184 min 45 s |
| Algorithm | Epoch | Mean Accuracy | Elapsed Time |
|---|---|---|---|
| CNN | 10 | 91.15% | 20 min 57 s |
| MLP | 10 | 76.92% | 26 min 56 s |
| CNN | 30 | 91.02% | 64 min 18 s |
| MLP | 30 | 54.04% | 64 min 19 s |
| CNN | 50 | 90.64% | 112 min 55 s |
| MLP | 50 | 53.89% | 102 min 20 s |
| Algorithm | Epoch | Mean Accuracy | Elapsed Time |
|---|---|---|---|
| CNN | 10 | 90.87% | 11 min 33 s |
| MLP | 10 | 54.10% | 10 min 16 s |
| CNN | 30 | 90.76% | 45 min 44 s |
| MLP | 30 | 54.43% | 27 min 58 s |
| CNN | 50 | 91.27% | 54 min 27 s |
| MLP | 50 | 79.01% | 46 min 18 s |
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Susilo, B.; Sari, R.F. Intrusion Detection in IoT Networks Using Deep Learning Algorithm. Information 2020, 11, 279. https://doi.org/10.3390/info11050279
Susilo B, Sari RF. Intrusion Detection in IoT Networks Using Deep Learning Algorithm. Information. 2020; 11(5):279. https://doi.org/10.3390/info11050279
Chicago/Turabian StyleSusilo, Bambang, and Riri Fitri Sari. 2020. "Intrusion Detection in IoT Networks Using Deep Learning Algorithm" Information 11, no. 5: 279. https://doi.org/10.3390/info11050279
APA StyleSusilo, B., & Sari, R. F. (2020). Intrusion Detection in IoT Networks Using Deep Learning Algorithm. Information, 11(5), 279. https://doi.org/10.3390/info11050279





