Botnet Defense System: Concept, Design, and Basic Strategy †
Abstract
1. Introduction
2. Related Work
2.1. Botnet and Mitigation Methods
2.2. White-Hat Worm
2.3. PN Model
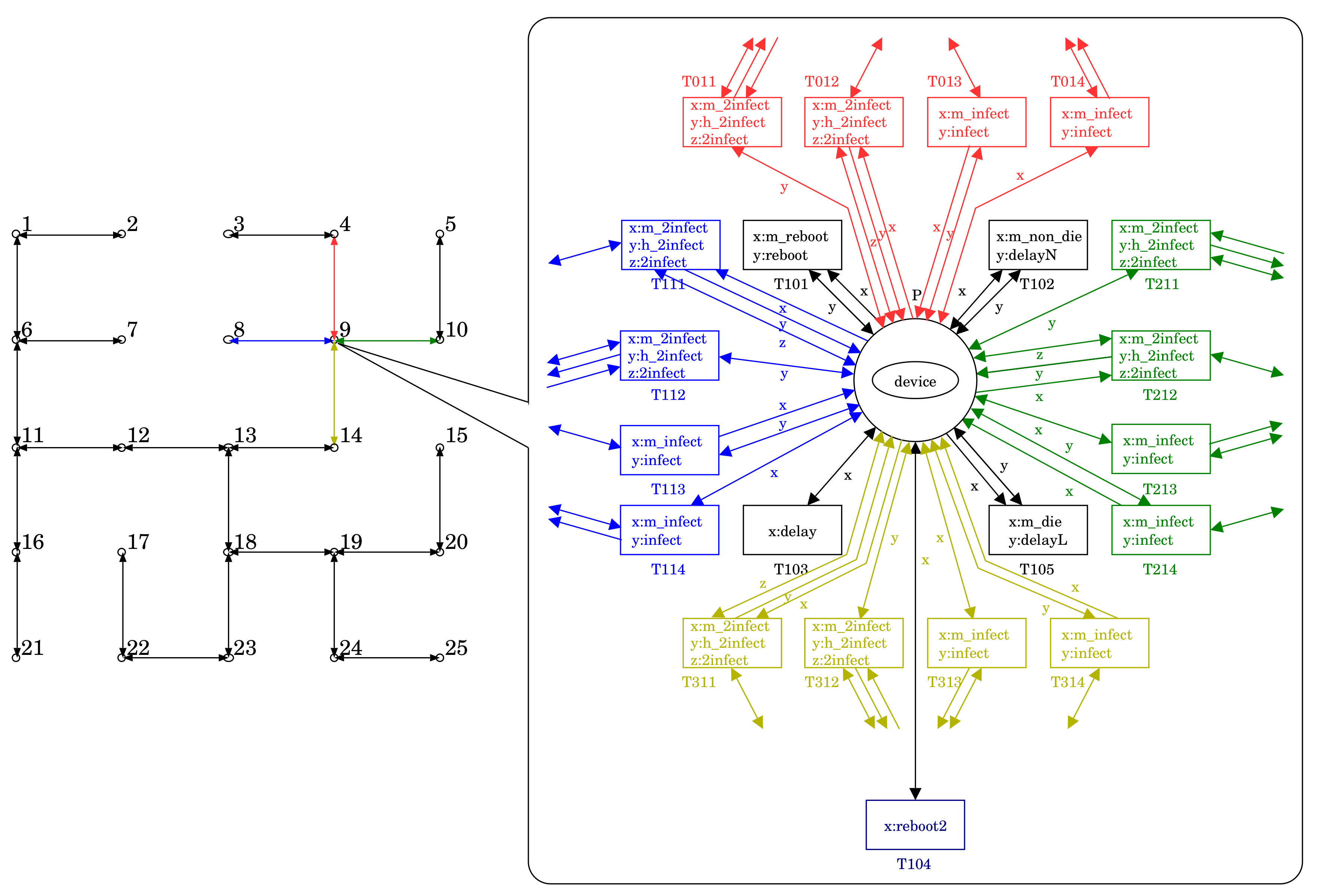
 represents an agent such as Mirai, the white-hat worm, and an IoT device, which corresponds to one of the agent nets. Each node has one device. Device device1 at place P1 is infected by Mirai. Device device2 at place P2 is normal. Device device3 at place P3 is infected by the white-hat worm. Each transition drawn as □ represents an action of one agent or an interaction among two or more agents. Whether an action can occur or not is decided based on the state of related agents. Red transitions of the environment net shown in Figure 1f show that they can occur. Let us induce the action represented by transition T214. This action means that the white-hat worm at P3 produces a copy of itself into P2, and the copy infects device2. Figure 2 shows the state after this action occurs. Please note that the action of transition T113 became disabled in order to occur. This means that the worm at P2 protects device2 from Mirai at P1.
represents an agent such as Mirai, the white-hat worm, and an IoT device, which corresponds to one of the agent nets. Each node has one device. Device device1 at place P1 is infected by Mirai. Device device2 at place P2 is normal. Device device3 at place P3 is infected by the white-hat worm. Each transition drawn as □ represents an action of one agent or an interaction among two or more agents. Whether an action can occur or not is decided based on the state of related agents. Red transitions of the environment net shown in Figure 1f show that they can occur. Let us induce the action represented by transition T214. This action means that the white-hat worm at P3 produces a copy of itself into P2, and the copy infects device2. Figure 2 shows the state after this action occurs. Please note that the action of transition T113 became disabled in order to occur. This means that the worm at P2 protects device2 from Mirai at P1.3. Botnet Defense System
3.1. Concept and Design
- 1°
- The monitor component watches over a specified IoT system. This activity itself may be done through white-hat worm. If detecting a malicious botnet, it investigates and reports the information such as the botnet type and its infection situation.
- 2°
- The strategy planner component makes a strategy against the malicious botnet based on the information reported by the monitor component.
- 3°
- The worm launcher component sends white-hat worms into the IoT system based on the strategy and constructs a white-hat botnet.
- 4°
- The C&C server component commands and controls the white-hat botnet to drive out the malicious botnet.
3.2. Strategies
3.2.1. All-Out Launch Strategy
3.2.2. Few-Elite Launch Strategy
3.2.3. Environment-Adaptive Strategy
4. Simulation Evaluation
4.1. Simulation
- or 12, i.e., or
- (or 19 if )
- The distribution of Mirai and white-hat bots at step 0 were decided at random
- The IoT system’s specification:
- –
- Network size
- –
- Network topology Grid or Tree, i.e., Network density or
- The white-hat worm’s capability:
- –
- Lifespan , or 5 steps, where the delay time until rebooting = 11 steps
- –
- Secondary infection possibility , or
- :
- :
| Secondary | Without BDS | With BDS | |||||||
|---|---|---|---|---|---|---|---|---|---|
| Infection | Launch Strategy | ||||||||
| Possibility | 1 | 3 | 5 | 7 | 13 | 19 | |||
| (a) with | |||||||||
| 0% | 97.0% | 97.0% | 96.9% | 97.0% | 96.5% | 96.9% | 96.9% | 96.9% | 96.9% |
| 25% | 96.9% | 96.9% | 96.7% | 96.5% | 95.5% | 94.7% | 94.7% | 94.7% | 94.7% |
| 50% | 94.0% | 88.9% | 82.9% | 77.2% | 66.5% | 48.1% | 48.1% | 48.1% | 48.1% |
| 75% | 70.0% | 61.5% | 53.9% | 49.5% | 41.8% | 27.7% | 27.7% | 27.7% | 27.7% |
| 100% | 37.4% | 26.1% | 21.9% | 17.6% | 13.8% | 8.6% | 8.6% | 8.6% | 8.6% |
| (b) with | |||||||||
| 0% | 97.0% | 96.9% | 96.9% | 97.0% | 96.5% | 96.8% | 96.8% | 96.8% | 96.8% |
| 25% | 84.1% | 78.1% | 75.6% | 74.1% | 71.4% | 68.0% | 68.0% | 68.0% | 68.0% |
| 50% | 32.6% | 29.7% | 27.2% | 25.2% | 24.0% | 15.7% | 15.7% | 15.7% | 15.7% |
| 75% | 7.5% | 6.6% | 6.2% | 5.9% | 6.7% | 4.0% | 4.0% | 6.2% | 6.2% |
| 100% | 1.3% | 0.6% | 0.4% | 0.4% | 0.1% | 0.2% | 0.2% | 0.4% | 0.4% |
| (c) with | |||||||||
| 0% | 96.8% | 96.5% | 96.0% | 95.8% | 94.6% | 93.4% | 93.4% | 93.4% | 93.4% |
| 25% | 22.0% | 11.4% | 10.1% | 9.7% | 7.9% | 8.9% | 8.9% | 10.1% | 10.1% |
| 50% | 1.5% | 0.9% | 1.0% | 1.0% | 0.8% | 0.7% | 0.7% | 1.0% | 1.0% |
| 75% | 0.2% | 0.1% | 0.2% | 0.2% | 0.1% | 0.1% | 0.1% | 0.2% | 0.2% |
| 100% | 0.0% | 0.0% | 0.0% | 0.0% | 0.0% | 0.0% | 0.0% | 0.0% | 0.0% |
| Secondary | Without BDS | With BDS | ||||||
|---|---|---|---|---|---|---|---|---|
| Infection | Launch Strategy | |||||||
| Possibility | 1 | 3 | 5 | 7 | 13 | |||
| (a) with | ||||||||
| 0% | 96.9% | 97.0% | 97.0% | 97.0% | 97.0% | 97.0% | 97.0% | 97.0% |
| 25% | 96.9% | 96.9% | 96.9% | 96.8% | 96.8% | 96.8% | 96.8% | 96.8% |
| 50% | 95.0% | 92.4% | 90.3% | 87.0% | 76.9% | 76.9% | 76.9% | 76.9% |
| 75% | 72.8% | 67.1% | 63.6% | 59.8% | 49.4% | 49.4% | 49.4% | 49.4% |
| 100% | 38.8% | 29.5% | 25.8% | 23.0% | 16.3% | 16.3% | 16.3% | 16.3% |
| (b) with | ||||||||
| 0% | 97.0% | 97.0% | 97.0% | 96.9% | 96.9% | 96.9% | 96.9% | 96.9% |
| 25% | 86.4% | 79.9% | 79.6% | 78.4% | 77.4% | 77.4% | 77.4% | 77.4% |
| 50% | 35.0% | 32.1% | 32.3% | 31.0% | 27.0% | 27.0% | 27.0% | 27.0% |
| 75% | 7.9% | 8.1% | 8.4% | 8.1% | 7.4% | 7.4% | 8.4% | 8.4% |
| 100% | 1.1% | 0.7% | 0.6% | 0.7% | 0.5% | 0.5% | 0.6% | 0.6% |
| (c) with | ||||||||
| 0% | 96.9% | 96.8% | 96.7% | 96.5% | 96.2% | 96.2% | 96.2% | 96.2% |
| 25% | 26.8% | 12.2% | 10.5% | 10.0% | 10.0% | 10.0% | 10.5% | 10.5% |
| 50% | 1.8% | 0.9% | 1.1% | 1.1% | 1.3% | 1.3% | 1.1% | 1.1% |
| 75% | 0.0% | 0.3% | 0.2% | 0.2% | 0.2% | 0.2% | 0.2% | 0.2% |
| 100% | 0.0% | 0.0% | 0.0% | 0.0% | 0.0% | 0.0% | 0.0% | 0.0% |
| Secondary | Without BDS | With BDS | |||||||
|---|---|---|---|---|---|---|---|---|---|
| Infection | Launch Strategy | ||||||||
| Possibility | 1 | 3 | 5 | 7 | 13 | 19 | |||
| (a) with | |||||||||
| 0% | 94.5% | 94.4% | 94.6% | 94.4% | 94.4% | 93.9% | 93.9% | 93.9% | 93.9% |
| 25% | 94.4% | 94.5% | 94.4% | 94.3% | 94.0% | 92.4% | 92.4% | 92.4% | 92.4% |
| 50% | 94.5% | 94.1% | 92.9% | 91.1% | 81.2% | 67.9% | 67.9% | 67.9% | 67.9% |
| 75% | 94.4% | 92.5% | 89.0% | 85.4% | 70.6% | 57.2% | 57.2% | 57.2% | 57.2% |
| 100% | 93.1% | 87.9% | 80.2% | 72.8% | 52.8% | 38.1% | 38.1% | 38.1% | 38.1% |
| (b) with | |||||||||
| 0% | 94.5% | 94.5% | 94.5% | 94.4% | 94.3% | 93.9% | 93.9% | 93.9% | 93.9% |
| 25% | 94.3% | 94.0% | 93.2% | 92.3% | 87.8% | 82.9% | 82.9% | 82.9% | 82.9% |
| 50% | 92.6% | 87.4% | 80.9% | 74.4% | 59.4% | 45.8% | 45.8% | 45.8% | 45.8% |
| 75% | 81.2% | 66.0% | 54.8% | 48.0% | 33.6% | 24.1% | 24.1% | 54.8% | 24.1% |
| 100% | 58.9% | 40.3% | 31.1% | 24.7% | 13.7% | 7.7% | 7.7% | 31.1% | 7.7% |
| (c) with | |||||||||
| 0% | 94.2% | 93.8% | 93.6% | 93.4% | 92.3% | 91.6% | 91.6% | 91.6% | 91.6% |
| 25% | 85.7% | 76.9% | 69.4% | 64.6% | 54.3% | 47.2% | 47.2% | 69.4% | 47.2% |
| 50% | 57.7% | 40.2% | 31.7% | 26.9% | 19.1% | 14.4% | 14.4% | 31.7% | 14.4% |
| 75% | 27.4% | 13.9% | 10.3% | 8.1% | 5.9% | 3.9% | 3.9% | 10.3% | 3.9% |
| 100% | 9.5% | 4.6% | 2.9% | 2.5% | 1.2% | 0.6% | 0.6% | 2.9% | 0.6% |
| Secondary | Without BDS | With BDS | ||||||
|---|---|---|---|---|---|---|---|---|
| Infection | Launch Strategy | |||||||
| Possibility | 1 | 3 | 5 | 7 | 13 | |||
| (a) with | ||||||||
| 0% | 94.4% | 94.3% | 94.5% | 94.4% | 94.5% | 94.5% | 94.5% | 94.5% |
| 25% | 94.4% | 94.5% | 94.4% | 94.5% | 94.5% | 94.5% | 94.5% | 94.5% |
| 50% | 94.4% | 94.4% | 94.3% | 93.9% | 90.0% | 90.0% | 90.0% | 90.0% |
| 75% | 94.3% | 93.7% | 92.6% | 91.3% | 83.9% | 83.9% | 83.9% | 83.9% |
| 100% | 93.6% | 91.1% | 87.3% | 82.8% | 66.8% | 66.8% | 66.8% | 66.8% |
| (b) with | ||||||||
| 0% | 94.4% | 94.4% | 94.5% | 94.4% | 94.5% | 94.5% | 94.5% | 94.5% |
| 25% | 94.3% | 94.2% | 94.2% | 93.8% | 92.0% | 92.0% | 92.0% | 92.0% |
| 50% | 93.1% | 90.4% | 87.5% | 83.7% | 72.5% | 72.5% | 72.5% | 72.5% |
| 75% | 82.5% | 71.2% | 64.0% | 59.4% | 45.7% | 45.7% | 64.0% | 45.7% |
| 100% | 61.8% | 45.7% | 38.8% | 33.4% | 20.2% | 20.2% | 38.8% | 20.2% |
| (c) with | ||||||||
| 0% | 94.4% | 94.3% | 94.1% | 94.1% | 93.8% | 93.8% | 93.8% | 93.8% |
| 25% | 87.5% | 79.2% | 74.2% | 70.4% | 62.5% | 62.5% | 74.2% | 62.5% |
| 50% | 60.6% | 43.5% | 36.7% | 32.7% | 23.9% | 23.9% | 36.7% | 23.9% |
| 75% | 28.1% | 15.8% | 13.0% | 10.4% | 8.0% | 8.0% | 13.0% | 8.0% |
| 100% | 9.8% | 5.2% | 4.3% | 3.6% | 1.9% | 1.9% | 4.3% | 1.9% |
4.2. Discussion
5. Conclusions
Funding
Conflicts of Interest
References
- Antonakakis, M.; April, T.; Bailey, M.; Bernhard, M.; Bursztein, E.; Cochran, J.; Durumeric, J.; Halderman, J.A.; Invernizzi, L.; Kallitsis, M.; et al. Understanding the Mirai Botnet. In Proceedings of the 26th USENIX Security Symposium (SEC’17), Vancouver, BC, Canada, 16–18 August 2017; pp. 1093–1110. [Google Scholar]
- Kolias, C.; Kambourakis, G.; Stavrou, A.; Voas, J. DDoS in the IoT: Mirai and other botnets. IEEE Comput. 2017, 50, 80–84. [Google Scholar] [CrossRef]
- Remillano, A., II; Urbanec, J. New Mirai Variant Uses Multiple Exploits to Target Routers and Other Devices. Available online: https://blog.trendmicro.com/trendlabs-security-intelligence/new-mirai-variant-uses-multiple-exploits-to-target-routers-and-other-devices/ (accessed on 10 April 2020).
- US Computer Emergency Readiness Team. Heightened DDoS Threat Posed by Mirai and Other Botnets. alert TA16-288A. Available online: Https://www.us-cert.gov/ncas/alerts/TA16-288A (accessed on 29 October 2019).
- Moffitt, T. Source Code for Mirai IoT Malware Released. Available online: https://www.webroot.com/blog/2016/10/10/source-code-Mirai-iot-malware-released/ (accessed on 10 April 2020).
- Cisco Annual Internet Report (2018–2023) White Paper. Available online: https://www.cisco.com/c/en/us/solutions/collateral/executive-perspectives/annual-internet-report/white-paper-c11-741490.html (accessed on 19 July 2020).
- Yamaguchi, S. White-Hat Worm to Fight Malware and Its Evaluation by Agent-Oriented Petri Nets. Sensors 2020, 20, 556. [Google Scholar] [CrossRef] [PubMed]
- Hiraishi, K. A Petri-net-based model for the mathematical analysis of multi-agent systems. IEICE Trans. Fundam. 2001, 84, 2829–2837. [Google Scholar]
- Yamaguchi, S.; Bin Ahmadon, M.A.; Ge, Q.W. Introduction of Petri Nets: Its Applications and Security Challenges. In Handbook of Research on Modern Cryptographic Solutions for Computer and Cyber Security; Gupta, B.B., Agrawal, D.P., Yamaguchi, S., Eds.; IGI Publishing: Hershey, PA, USA, 2016; pp. 145–179. [Google Scholar]
- Ogu, E.C.; Ojesanmi, O.A.; Awodele, O.; Kuyoro, S. A Botnets Circumspection: The Current Threat Landscape, and What We Know So Far. Information 2019, 10, 337. [Google Scholar] [CrossRef]
- Bezerra, V.H.; da Costa, V.G.T.; Barbon, J.; Miani, R.S.; Zarpelão, B.B. IoTDS: A One-Class Classification Approach to Detect Botnets in Internet of Things Devices. Sensors 2019, 19, 3188. [Google Scholar] [CrossRef] [PubMed]
- Manso, P.; Moura, J.; Serrão, C. SDN-Based Intrusion Detection System for Early Detection and Mitigation of DDoS Attacks. Information 2019, 10, 106. [Google Scholar] [CrossRef]
- Edwards, S.; Profetis, I. Hajime: Analysis of a Decentralized Internet Worm for IoT Devices. Available online: Http://security.rapiditynetworks.com/publications/2016-10-16/Hajime.pdf (accessed on 29 October 2019).
- Molesky, M.J.; Cameron, E.A. Internet of Things: An Analysis and Proposal of White Worm Technology. In Proceedings of the 37th IEEE International Conference on Consumer Electronics (ICCE 2019), Las Vegas, NV, USA, 11–13 January 2019. [Google Scholar]
- Nakahori, K.; Yamaguchi, S. A support tool to design IoT services with NuSMV. In Proceedings of the 35th IEEE International Conference on Consumer Electronics (ICCE 2017), Las Vegas, NV, USA, 8–10 January 2017; pp. 84–87. [Google Scholar]






Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2020 by the author. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Yamaguchi, S. Botnet Defense System: Concept, Design, and Basic Strategy. Information 2020, 11, 516. https://doi.org/10.3390/info11110516
Yamaguchi S. Botnet Defense System: Concept, Design, and Basic Strategy. Information. 2020; 11(11):516. https://doi.org/10.3390/info11110516
Chicago/Turabian StyleYamaguchi, Shingo. 2020. "Botnet Defense System: Concept, Design, and Basic Strategy" Information 11, no. 11: 516. https://doi.org/10.3390/info11110516
APA StyleYamaguchi, S. (2020). Botnet Defense System: Concept, Design, and Basic Strategy. Information, 11(11), 516. https://doi.org/10.3390/info11110516





