1. Introduction
The increasing logistics demand of the world maritime industry has led to higher energy consumption and carbon emissions [
1]. To reduce carbon emissions, the proportion of clean energy of the maritime industry is increasing. As an important part of the maritime industry, the seaport microgrid undertakes the task of shaping the green and low-carbon maritime transportation. A seaport microgrid has a higher proportion of renewable energy compared with a conventional microgrid [
2], which easily causes voltage and frequency deviations due to a strong randomness. Therefore, it is essential to investigate the distributed secondary control problem for a seaport microgrid to maintain its stability [
3].
A seaport microgrid is actually a multiagent system (MAS) [
4]. The distributed secondary control of the seaport microgrid relies on the communication network between the DGs. However, the traditional single-IP carrier communication network cannot support various types of data packets exchange between the heterogeneous DGs from different manufacturers. A polymorphic network [
5] can support the coexistence and collaboration of multiple communication modes by programmable hardware, which can break the restraint of an IP network for information exchange between the heterogeneous DGs. Therefore, how to construct a seaport microgrid under a polymorphic environment is crucial to the distributed secondary control for the heterogeneous DGs. As a crucial node in the port’s Internet of things (IoT) [
6,
7,
8], the seaport microgrid attracts potential adversaries because of its public network. When the attacks are launched into the communication network, the consensus performance of the DGs is destroyed. The seaport microgrid faces the risk of a power outage [
9,
10]. Once a power outage occurs, the electric-driven devices (such as cranes, handing machines and belt-conveying machines) are not able to maintain normal operation, causing huge economic losses. Therefore, how to defend against potential attacks on the seaport microgrid has been widely focused on.
The false data injection (FDI) attack [
11] on the microgrid is noteworthy; it destroys the consensus performance of the DGs by tampering with the neighboring information. The existing methods to defend against FDI attacks include two categories, one is to use detection and isolation algorithms to check whether the communication channels are attacked, and the other one is to use resilient control strategies to suppress attacks. The detection algorithms [
12,
13,
14] generally need enough time to check each node in the communication network due to limited computing resources. That is, these detection methods cannot guarantee the stability of seaport microgrids during the detection process. As a result, researchers have developed resilient control strategies by using the virtual layer to suppress attacks [
15,
16,
17,
18,
19]. Ref. [
15] used a virtual network to interconnect with the original one to defend against linear dynamics FDI attacks. Ref. [
16] proposed a resilient strategy in the case of directed graphs. For the microgrid, a resilient strategy makes the number of DGs under FDI attacks unlimited [
17,
18,
19]. Ref. [
17] designed the resilient strategy to defend against time-dependent and state-dependent FDI attacks on the multiple communication components. Ref. [
18] indicated a resilient strategy could resist not only FDI attacks, but also DoS attacks by using the virtual layer. Ref. [
19] proposed a resilient distributed method against unbounded time-dependent attacks for MASs. The above-mentioned attack types are time-dependent and state-dependent. For a seaport microgrid, the state estimator is applied to improve the measurement accuracy in complex weather environment [
20]. The potential adversaries can choose to steal the state estimator parameters to design estimation-dependent attacks rather than time-dependent and state-dependent attacks [
21]. It is noteworthy that compared with other FDI attacks, estimation-dependent attacks can change with the estimation results dynamically rather than with a fixed growth trajectory. The estimation-dependent attacks can destroy the state estimator function for making control decisions, causing a large-scale power outage of the seaport microgrid.
In conclusion, to defend against an estimation-dependent attack, this paper proposes a resilient distributed secondary control strategy for a polymorphic seaport microgrid. The contributions of this paper are as follows:
(1) The polymorphic seaport microgrid is constructed including a power layer, a data layer, a control layer and a service layer. The heterogeneous DGs can exchange information through the data layer. Furthermore, software-defined functions can be achieved by the control layer.
(2) A unbounded estimation-dependent attack from the perspective of attackers is designed. It can be generated by stolen estimator parameters of the seaport microgrid to cause a large-scale power outage due to the error estimation results. Furthermore, the characteristics of the estimation-dependent attack is analyzed to model the attack launched on the seaport microgrid.
(3) A resilient distributed secondary control strategy is proposed to defend against the estimation-dependent attack for the seaport microgrid. The virtual layer is used to interconnect with the control layer to generate an attack compensation vector, which can suppress the attack injected into the control layer.
The rest of this paper is organized as follows.
Section 2 establishes a polymorphic seaport microgrid.
Section 3 proposes a resilient distributed secondary strategy to suppress the estimation-dependent attack and completes a stability analysis.
Section 4 gives simulation cases to validate the effectiveness of the proposed strategy. Finally,
Section 5 summarizes this paper.
2. Framework of the Polymorphic Seaport Microgrid
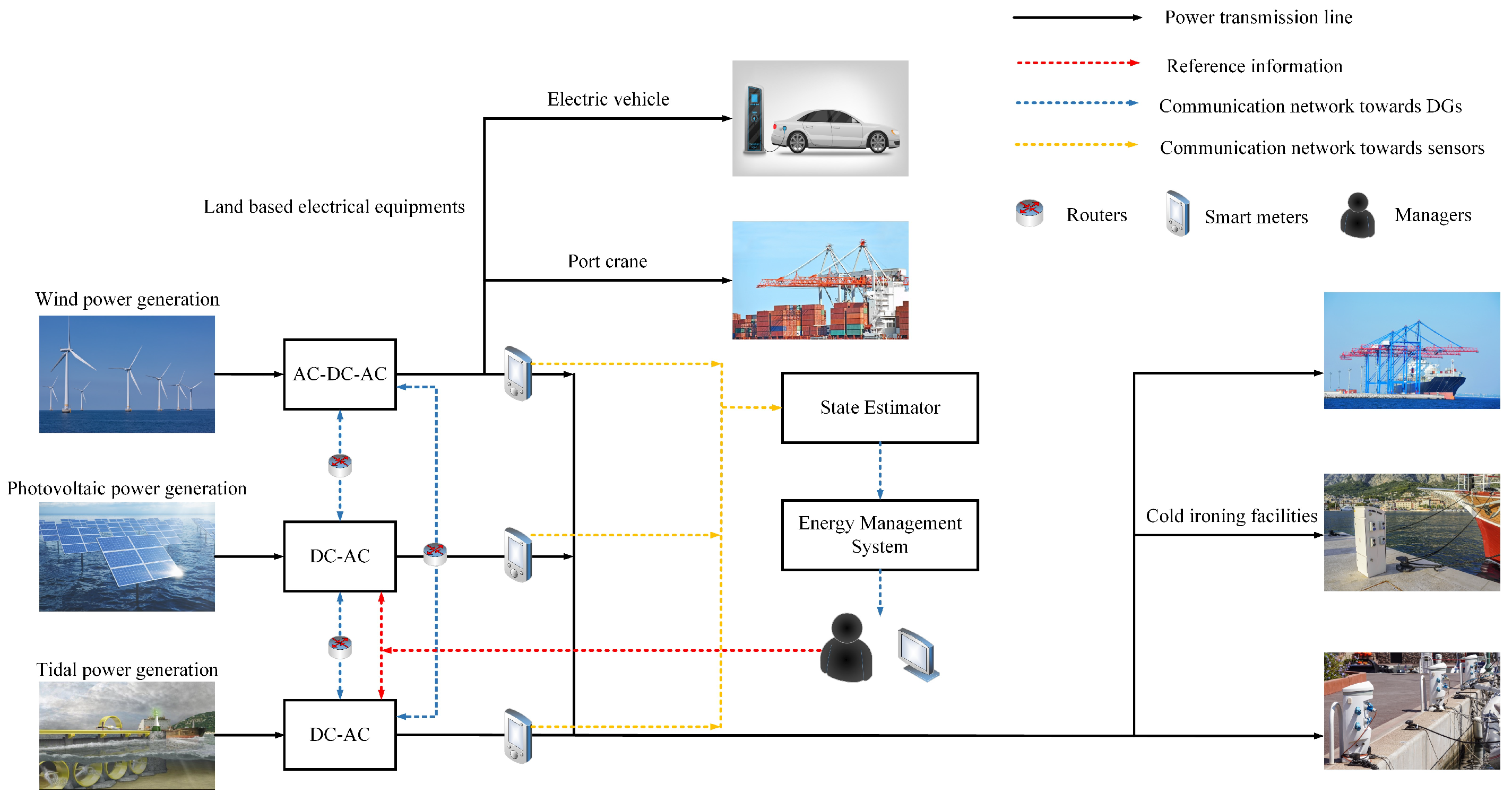
The structure [
22,
23,
24] of a seaport microgrid consists of DGs, power loads and control systems, as shown in
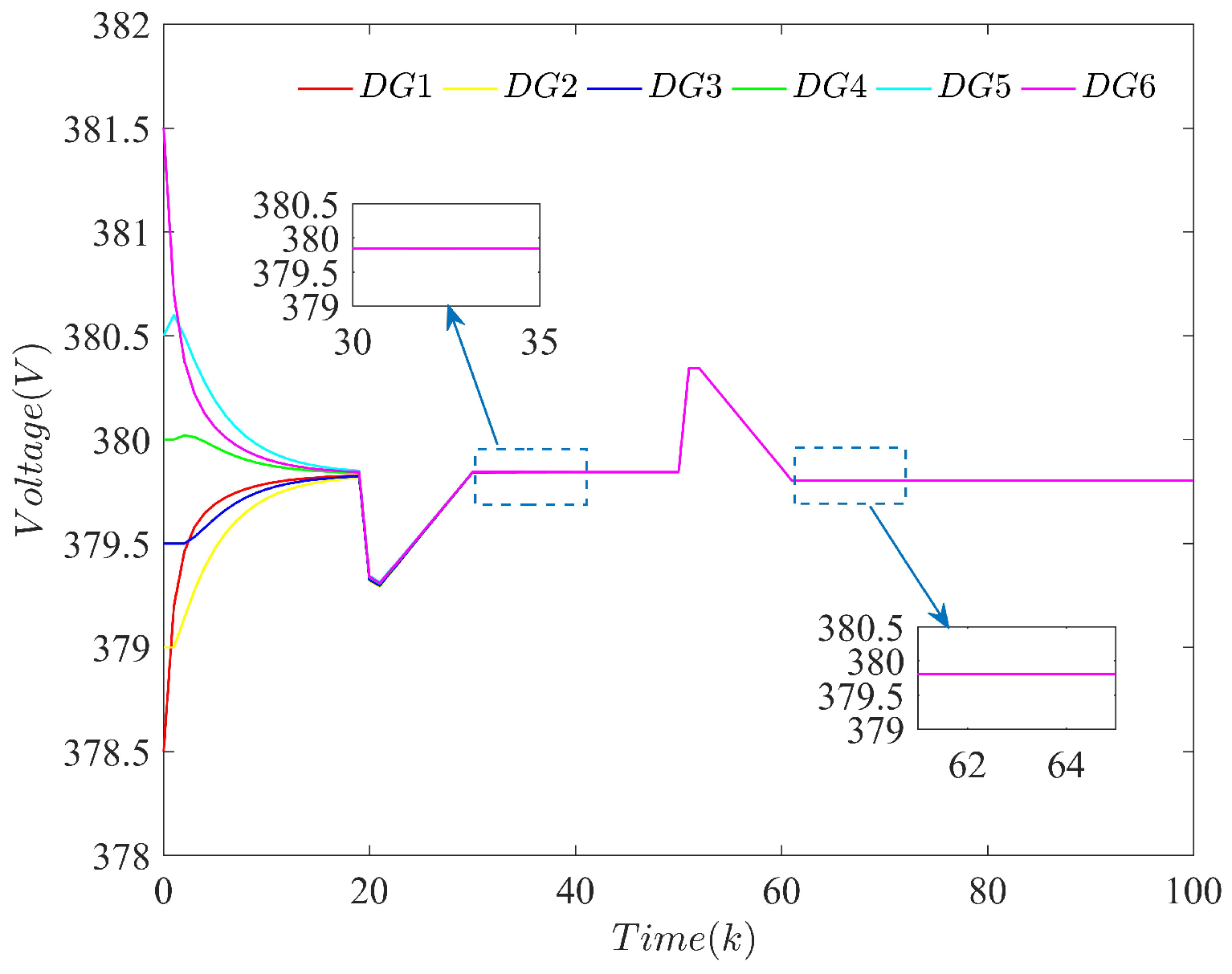
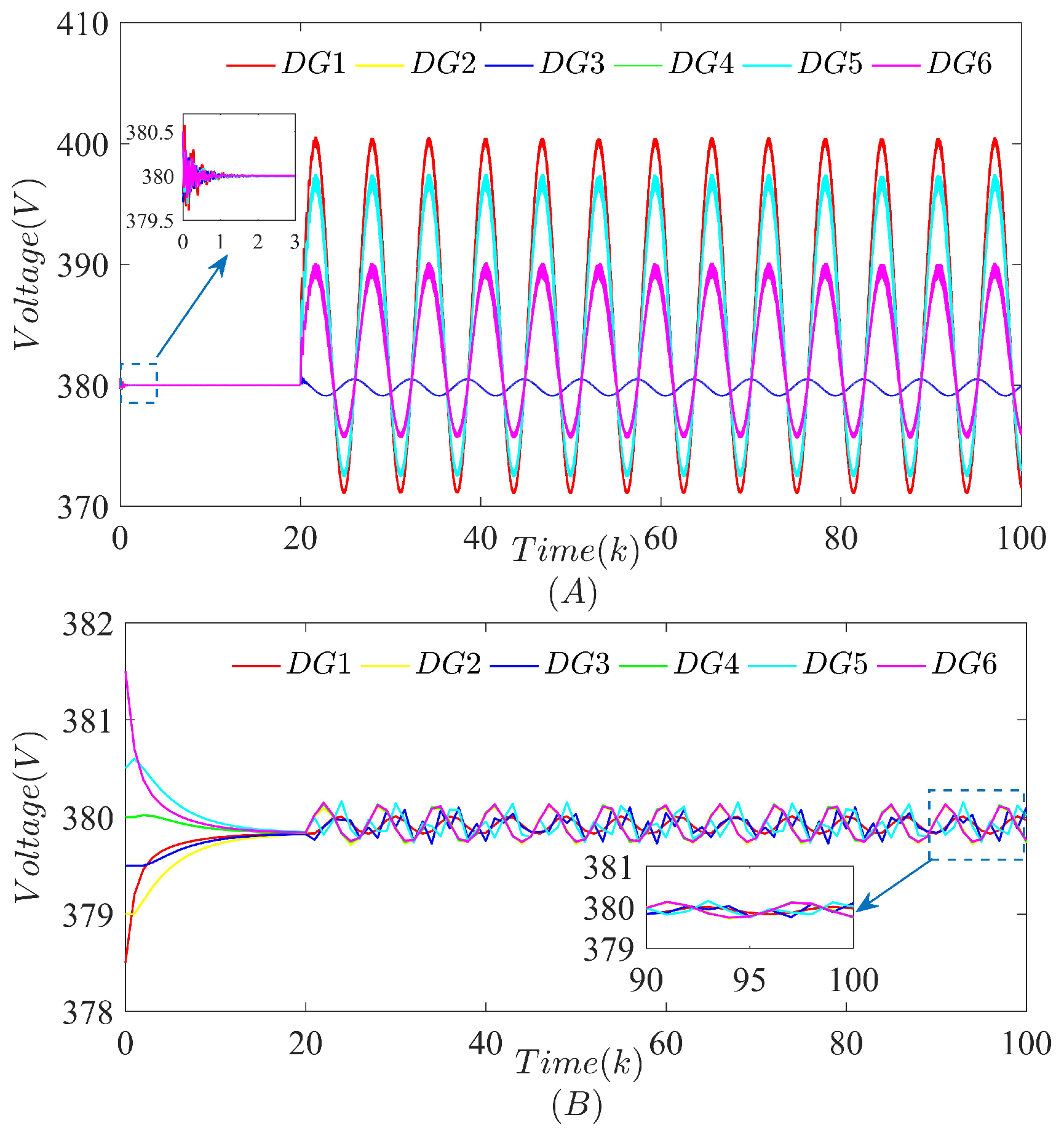
Figure 1. To reduce carbon emissions, various renewable energy devices (such as wind turbines, photovoltaic panels, etc.) are integrated into the seaport microgrid. Since the seaport is an important link between the sea and the land, the power loads generally contain land-based electrical equipment (electric vehicles, port cranes, etc.) and cold ironing facilities providing power to the ships. In addition, the seaport microgrid is equipped with control systems to analyze data and make decisions. The SCADA system is responsible for collecting the measurement results uploaded by sensors in the channels between the DGs. The state estimator using the measurement results provides estimation results to the EMS.
To break the restraint of traditional IP carrier network, a polymorphic seaport microgrid is established to exchange information between the heterogeneous DGs from different manufacturers in
Figure 2. The manager-oriented service layer contains the state estimator and the EMS. That is, the control systems of the seaport microgrid shown in
Figure 1 are included into the service layer. The control layer ensures the software-defined functions are compatible with various control strategies. Furthermore, the data layer configures the polymorphic identification table to exchange various types of data packets between the neighboring DGs through different transmission channels (such as FPGA, etc.). The power layer contains the whole DGs and loads, from which all the measurements are obtained. Thus, the polymorphic seaport microgrid can not only exchange information between the heterogeneous DGs, but also design and implement a resilient strategy using the virtual layer against estimation-dependent attacks.
3. Resilient Distributed Secondary Control Strategy for the Seaport Microgrid
In this section, the impact of an estimation-dependent attack on the seaport microgrid is analyzed, and a resilient distributed secondary control strategy is proposed to defend against the estimation-dependent attack.
3.1. Graph Theory
The communication topology of the seaport microgrid considered is a directed graph containing a leader and N followers. The weighted adjacency matrix of can be described as , where is the weight between nodes. If , the agent i can receive neighboring information from agent j, otherwise, . The in-degree matrix of can be described as , and . The Laplace matrix of can be described as . In addition, is the matrix of gains from the leader to the ith follower. For a better expression, the notations involved in this paper are shown in Notations.
3.2. Problem Formulation
The droop mechanisms of the
ith DG in the seaport microgrid can be shown as
where
is the angular frequency of the
ith DG,
is the output voltage of the
ith DG,
and
are the set points for the droop mechanisms,
and
are droop coefficients chosen according to the power rating of the
ith DG and
and
are the active and reactive output power of the
ith DG, respectively.
To maintain the consensus performance of the DGs,
and
are exchanged between the neighboring DGs. Differentiating (1) and (2) yields
where
and
are auxiliary control inputs.
Based on the leader–follower information,
and
at each DG can be shown as
where
and
are the frequency and voltage reference information, respectively. Then, (5) and (6) can be reformulated as
where
,
and the power sharing mechanisms
and
are included in the distributed secondary control laws (7) and (8).
The frequency and the voltage of each DG can converge steadily due to the relationship between the active power/reactive power of each DG and its angular frequency/output voltage [
25]. That is, to synchronize
and
/
and
, we can directly synchronize
/
. For convenience,
/
is used to denote
/
. We consider the local form of discrete-time distributed secondary control laws as
The compact form combining (9) and (10) is shown as
where
is the voltage and frequency of the
ith DG and
is the reference voltage and frequency of each DG.
T is the sample time of the seaport microgrid. Then, the global form of (11) can be shown as
where
,
, and
. In addition, to improve the measurement accuracy of the seaport microgrid, the state estimator is proposed as
where
is the estimation result at time
,
is the measurement vector,
C is a
-dimensional identity observation matrix. Define
as the estimation residual, which aims to measure whether FDI attacks can be detected by the
detector.
K is the Kalman gain, which can reach the steady state at an exponential speed from any original state [
26]. Therefore,
K can be solved by (14) and (15)
where
Q and
R are both
-dimensional positive definite matrices. They represent the covariance of the noise in the seaport microgrid, which can also be used for designing a control strategy without considering noise factors [
27].
The strategy shown in (12) can keep the stability of the seaport microgrid. However, considering potential attacks, the strategy changes from (12) to (16):
where
is the voltage and frequency of DGs under FDI attacks.
is the FDI attack vector. Accordingly, the dynamic expression of the state estimator (13) under FDI attacks is shown as
where
is the estimation result under FDI attacks,
is the measurement vector under FDI attacks and
is the estimation residual under FDI attacks. From (17), the estimation results will deviate from the ones under normal operation under attacks. In order to reflect the deviation more clearly, we define
and
as the estimation difference and the residual difference, respectively. Combining with (12), (13), (16) and (17), the expression of (17) can be given as
where
reflects the impact on the voltage and frequency of DGs caused by FDI attacks.
3.3. The Estimation-Dependent FDI Attack on the Seaport Microgrid
In existing works, potential FDI attacks on the microgrid are usually modeled as time-dependent sinusoidal and proportional functions, such as . f and b are both constants, and c is a positive integer. Obviously, there exists a arbitrary constant which can achieve . Specially, if the FDI attack is modeled as , it becomes an unbounded attack. Such time-dependent attack modeling methods are indeed reasonable. However, potential adversaries can choose to steal the state estimator parameters to design estimation-dependent attacks. To illustrate the impact of estimation-dependent attack, this subsection designs an algorithm to generate an estimation-dependent FDI attack from the perspective of adversaries, as shown in Algorithm 1. It should be noted that Algorithm 1 needs to satisfy the following assumptions.
| Algorithm 1 The estimation-dependent attack for the seaport microgrid |
| Initialization parameters: |
| Define .
|
| Choose an arbitrary and a detection threshold . |
| while do |
| Set , ; |
| Calculate ; |
| Calculate |
| ; |
| ; |
| ; |
| end while |
Assumption 1. Attackers have perfect knowledge of the communication topology inside the seaport microgrid.
It should be noted that attackers cannot change the attack abruptly during the generation process due to limited resources [
28]. In this case, it is reasonable to consider that
is energy-bounded. That is, the attack grows at a steady or decaying rate. In existing works, the attack is believed to be proportional to the time or the state of the system [
19,
21,
29]. Obviously, unbounded attacks [
19,
21,
29] satisfy the nonstrict convexity. Therefore, we propose Assumption 2 to describe the general characteristic of unbounded attacks.
Assumption 2. The estimation-dependent attack satisfies the nonstrictly convex function characteristic after several steps of initialization.
Algorithm 1 generates the estimation-dependent attack as
where
is the
sth column of a
-dimensional identity matrix. To be more precise, the selection principle of
s is given by [
21]. As Algorithm 1 shows, the estimation difference of voltage and frequency is set to zero at
. Since
,
will be a nonzero vector in the iterative process, which indicates
can affect the seaport microgrid all the time. When the stability of the seaport microgrid is destroyed,
has a nonzero value, which leads to the divergence of
. The diverging
will generate
at the next time
k, which leads to the divergence of
. Thus, both
and
will diverge to
∞ eventually.
In fact, when diverges to a certain degree, the seaport microgrid manager will make an outage decision to avoid causing great economic losses. Therefore, to defend against the estimation-dependent attack illustrated in Algorithm 1, a resilient strategy should be proposed.
3.4. Resilient Distributed Secondary Control Strategy Based on a Layered Network
This subsection introduces a virtual network , which interconnects with the original network to defend against an estimation-dependent attack. Since the virtual network has no physical meanings, it has a pretty high level of security. The attackers can achieve the goal of destabilizing the seaport microgrid only by injecting limited resources. Therefore, a resilient distributed secondary control strategy using a virtual network is proposed to defend against an estimation-dependent attack on .
As shown in
Figure 3, both networks have the same number of nodes, and these nodes can accept reference information. The resilient strategy (21)–(23) is proposed to suppress the estimation-dependent attack launched on the original network
.
where
is the state vector of
,
is the difference of the state vectors between
and
and
is the attack-compensation vector generated by (21) and (22). Define the error between
in
and the reference information
as
, and the error between
in
and the reference information
as
.
Assumption 3. If there is a path to each other node, the direct graph ς has a spanning tree.
Lemma 1 (see [
30]).
Suppose Assumption 3 holds, is a positive-definite and nonsingular matrix. Lemma 2 (see [
19]).
If is a Hurwitz matrix, then is also Hurwitz. Theorem 1. Suppose the estimation-dependent attack (20) satisfying Assumption 1 and Assumption 2, and Assumption 3 holds. The synchronization of DGs under the estimation-dependent attack (20) can be maintained by using the proposed resilient distributed secondary control strategy (21)–(23).
Proof of Theorem 1. For the resilient distributed secondary control strategy (21)–(23) against the estimation-dependent attack in Algorithm 1, the stability of the original control layer (21) should be proven. Since , we prove the stability of and in two steps and finally show the stability of the original control layer .
Step 1: From Assumption 1, the estimation-dependent attack can be generated by Algorithm 1. Define
, which is the difference between the estimation-dependent attack vector and the attack-compensation vector (23). Then, the expression of
can be obtained from (21) and (22) as
From (23), the differential relationship between
and
is
To be more convenient, integrate (26) and (27) into a compact matrix form as
Define
. The relationship between
and
is
, where
. A Lyapunov function is chosen as
From Assumption 2,
. A Lyapunov function is chosen as
where
is a symmetric matrix. The differential form of (30) is shown as
From Assumption 3 and Lemma 1, since
is positive-definite,
is Hurwitz. From Lemma 2,
is also Hurwitz. Thus, there exists a symmetric positive matrix
, which makes
for any symmetric positive matrix
. From Assumption 2,
. Therefore,
can be given after the initial time.
Step 2: To prove the stability of the virtual layer
(22), the differential form of
can be written as
. Let
, and the differential form is shown as
Since
is Hurwitz, the positive symmetric matrix
can achieve
. As a result,
. The stability of the virtual layer
can be proven.
Step 1 and Step 2 show that the original control layer (21) and the virtual layer (22) are both stable under the estimation-dependent attack. Thus, the resilient strategy (21)–(23) can defend against the estimation-dependent attack effectively. This completes the proof of Theorem 1. □