Cryptanalysis of Permutation–Diffusion-Based Lightweight Chaotic Image Encryption Scheme Using CPA
Abstract
:1. Introduction
- (1)
- We propose a feasible attack strategy that can completely break the original Permutation–Diffusion based image cryptosystem with high security and low computational overhead, which is especially applicable for secure image communication in the resource-constrained modern network environment.
- (2)
- Our cryptanalysis is also efficient with little computing, especially in the case of attack permutation phase where the equivalent rule for any complex scrambling method can be obtained. The proposed method is instructive for cryptanalysis researches of other image encryption schemes with a structure of permutation–diffusion.
- (3)
- The corresponding improvements are proposed by analyzing the complexity and security of the original encryption scheme [17], which will provide a useful reference for the development of image cryptosystem.
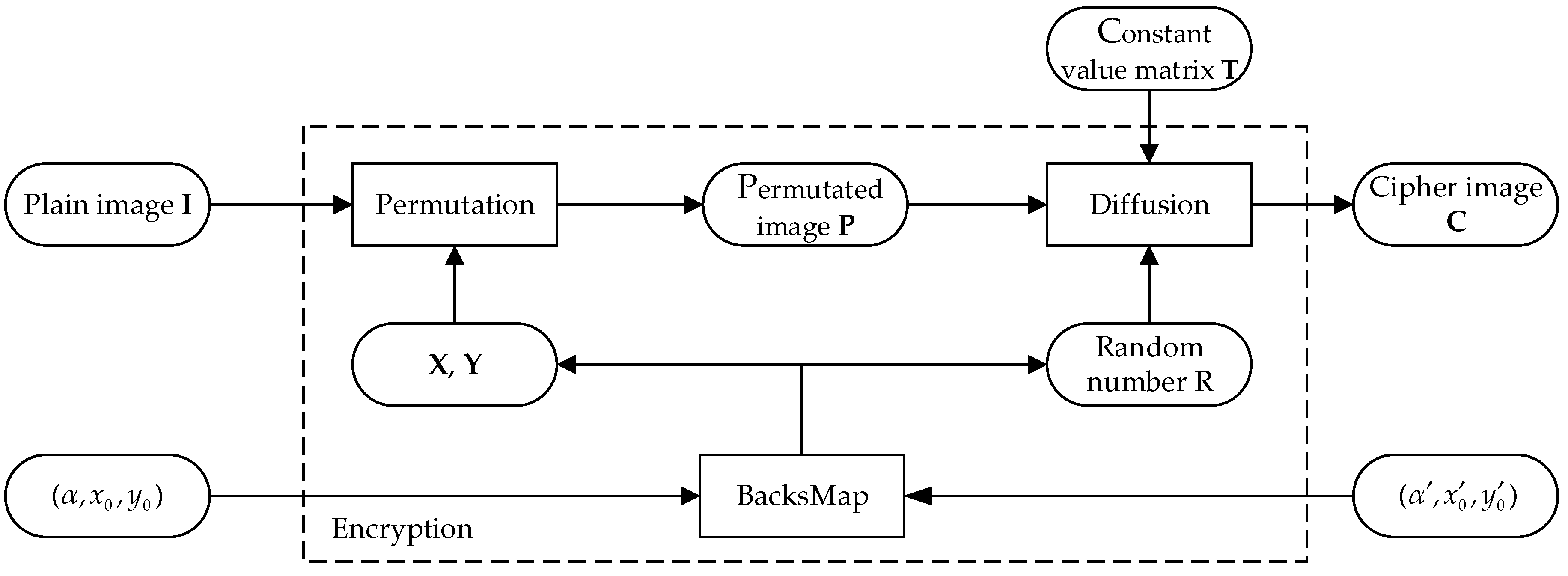
2. Review of the Original Scheme
3. Cryptanalysis of the Original Scheme
3.1. Obtain the Equivalent Secret Key
| Algorithm 1 Obtain the secret key R |
| Input: Full zero plain image I0 |
| Output: The secret key R |
| 1: procedure Key(I0) |
| 2: M, N ← size(I0) // Get the size of the plain image |
| 3: T ← zeros(M, N) |
| 4: for i from 1 to M |
| 5: for j from 1 to N |
| 6: T(i, j) ← mod(M/i + N/j, 256) // Obtain the constant matrix |
| 7: end |
| 8: end |
| 9: C ← encryption(I0) // Obtain the ciphertext image |
| 10: R ← bitxor(T, C) |
| 11: end procedure |
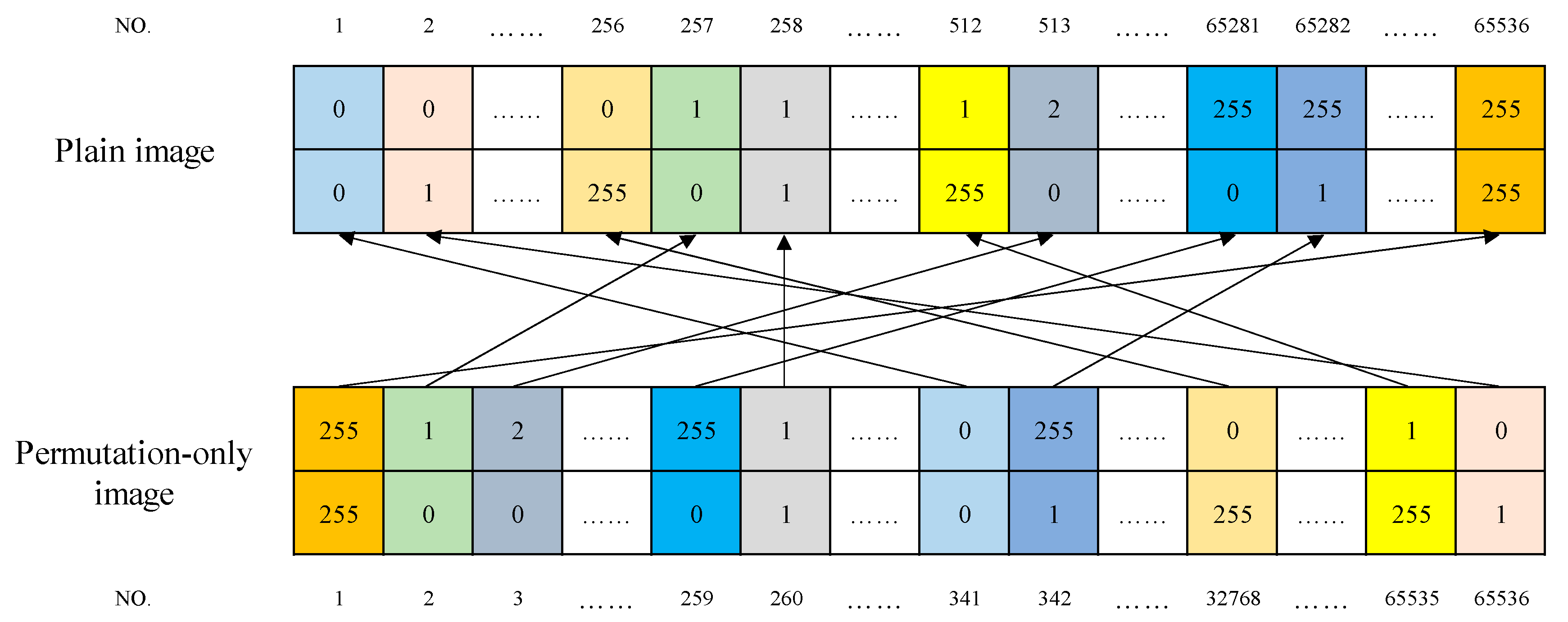
| Algorithm 2 Obtain the permutation rule lp |
| Input: N pairs of permutation-only images of chosen images |
| Output: Permutation rule lp and B |
| 1: procedure Rule(P1, P2, …, Pn) // Define a function to obtain the permutation rule |
| 2: M, N ← size(P1) // Get the size of the image |
| 3: B ← zeros(M, N) |
| 4: for i from 1 to M |
| 5: for j from 1 to N |
| 6: B(i, j) ← P1(i, j) * 256 + P2(i, j) |
| 7: end |
| 8: end |
| 9: lp ← reshape(B, 1, M * N) // Turn the matrix into a vector |
| 10: end procedure |
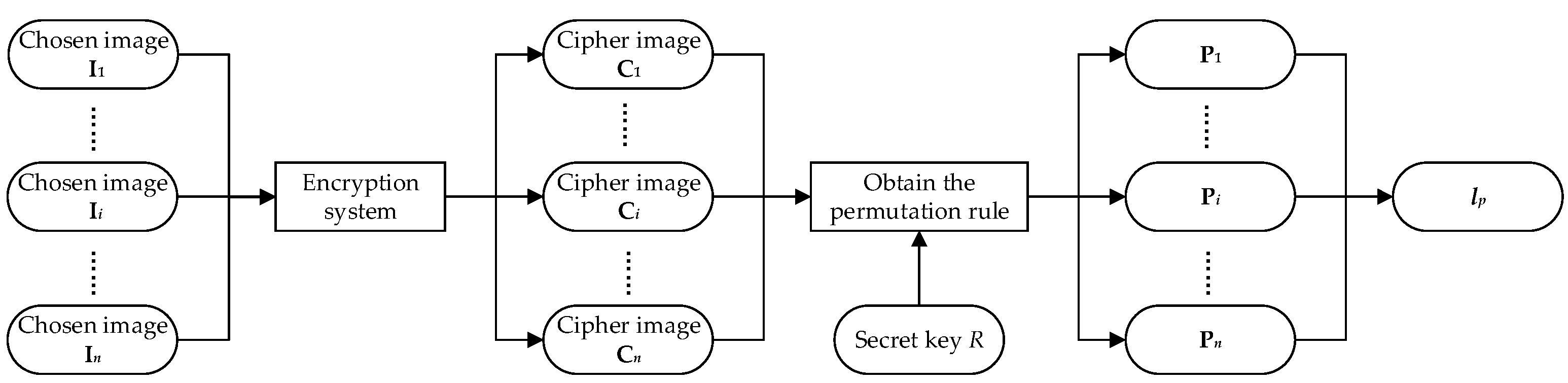
3.2. Obtain the Permutation Rule
| Algorithm 3 Proposed diffusion attack algorithm |
| Input: A known ciphertext image C, full zero plain image I0 |
| Output: The permutation-only image P of known ciphertext image C |
| 1: procedure De_ diffusion(C, I0) |
| 2: M, N ← size (C) // Get the size of the image |
| 3: R ← Key (I0) // Invoke algorithm 1 to obtain the key R |
| 4: r ← 0 |
| 5: for i from 1 to M |
| 6: for j from 1 to N |
| 7: r ← mod(C(i−1, j−1) + R, 256) |
| 8: P(i, j) ← bitxor(r, C(i, j)) |
| 9: T(i, j) ← mod(M/i + N/j, 256) // Obtain the constant matrix |
| 10: end |
| 11: end |
| 12: P ← bitxor(P, T) // Return the permutation-only image |
| 13: end procedure |
| Algorithm 4 Proposed confusion attack algorithm |
| Input: The permutation-only image P, and n pairs of permutation-only images of chosen images |
| Output: The deciphering image I |
| 1: procedure De_ confusion(P, P1, P2, …, Pn) |
| 2: M, N ← size(P) // Get the size of the image |
| 3: I ← zeros(M, N) |
| 4: lp, B ← Rule(P1, P2, …, Pn) // Invoke algorithm 2 to obtain the permutation rule |
| 5: x, y ← 0 |
| 6: for i from 1 to M |
| 7: for j from 1 to N |
| 8: x ← floor(B(i, j) / M) + 1 // Obtain the original row number |
| 9: y ← mod(B(i, j), M) // Obtain the original column number |
| 10: I(x, y) ← P(i, j) // Return the permutation-only image |
| 11: end |
| 12: end |
| 13: end procedure |
3.3. Summary of the Attack Strategy
- Step 1: According to Algorithm 1, obtain the secret key or equivalent key via a known full zero image (Attack 1) as stated in Section 3.1.
- Step 2: Obtain permutation rule using the following substeps.
- Determine the number of chosen images (Attack 2) according to (9).
- According to Algorithm 2, obtain the permutation-only images of chosen images with the diffusion key .
- According to Algorithm 3, obtain the permutation rule with the permutation-only images.
- Step 3: Invoke Algorithm 3 to obtain the permutation-only image of the final ciphertext image.
- Step 4: Invoke Algorithm 4 to obtain the deciphering image of the final ciphertext image.
3.4. Computational Complexity Analysis
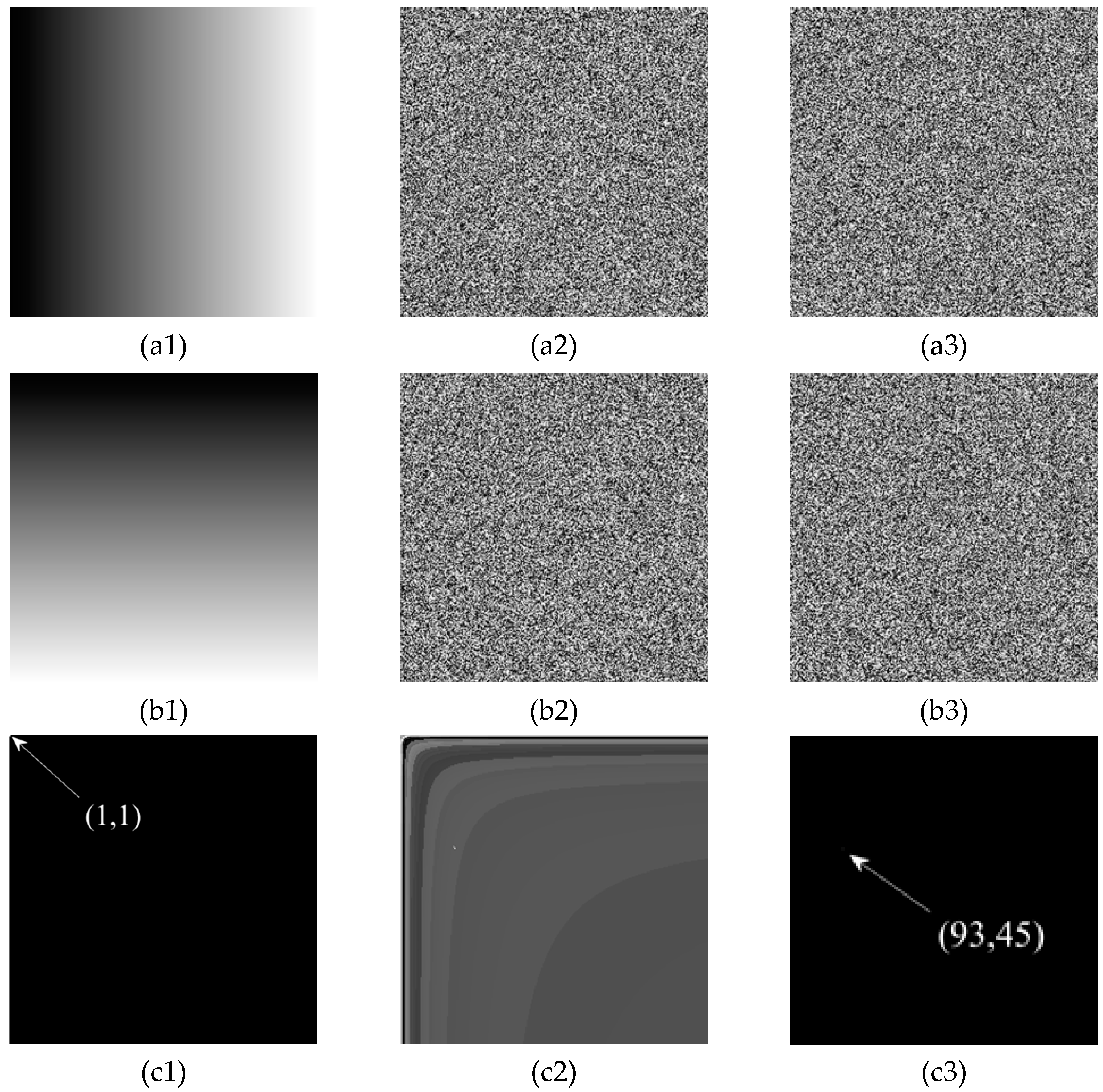
4. Conclusions
Author Contributions
Funding
Conflicts of Interest
References
- Li, X.W.; Lee, I.K. Robust copyright protection using multiple ownership watermarks. Opt. Express 2015, 23, 3035–3046. [Google Scholar]
- Fan, H.; Li, M.; Liu, D.; An, K. Cryptanalysis of a plaintext-related chaotic RGB image encryption scheme using total plain image characteristics. Multimed. Tools Appl. 2018, 77, 20103–20127. [Google Scholar]
- Wang, X.; Wang, Q.; Zhang, Y. A fast image algorithm based on rows and columns switch. Nonlinear Dyn. 2015, 79, 1141–1149. [Google Scholar]
- Li, M.; Ren, H.; Zhang, E.; Wang, W.; Sun, L.; Xiao, D. A VQ-Based Joint Fingerprinting and Decryption Scheme for Secure and Efficient Image Distribution. Secur. Commun. Netw. 2018, 2018, 4313769. [Google Scholar]
- Cambareri, V.; Mangia, M.; Pareschi, F.; Rovatti, R.; Setti, G. Low-Complexity Multiclass Encryption by Compressed Sensing. IEEE Trans. Signal Process. 2015, 63, 1. [Google Scholar]
- Zhang, L.Y.; Liu, Y.; Pareschi, F.; Zhang, Y.; Wong, K.-W.; Rovatti, R.; Setti, G. On the security of a class of diffusion mechanisms for image encryption. IEEE Trans. Cybern. 2018, 48, 1163–1175. [Google Scholar]
- Zheng, P.; Huang, J. Efficient Encrypted Images Filtering and Transform Coding with Walsh-Hadamard Transform and Parallelization. IEEE Trans. Image Process. 2018, 27, 2541–2556. [Google Scholar]
- Ping, P.; Wu, J.; Mao, Y.; Xu, F.; Fan, J. Design of image cipher using life-like cellular automata and chaotic map. Signal Process. 2018, 150, 233–247. [Google Scholar]
- Pak, C.; Huang, L. A new color image encryption using combination of the 1D chaotic map. Signal Process. 2017, 138, 129–137. [Google Scholar]
- Li, M.; Xiao, D.; Liu, H.; Bai, S. A recoverable chaos-based fragile watermarking with high PSNR preservation. Secur. Commun. Netw. 2016, 9, 2371–2386. [Google Scholar]
- Hua, Z.; Jin, F.; Xu, B.; Huang, H. 2D Logistic-Sine-Coupling Map for Image Encryption. Signal Process. 2018, 149, 148–161. [Google Scholar]
- Li, M.; Liu, S.; Niu, L.; Liu, H. Cryptanalyzing a chaotic encryption algorithm for highly auto correlated data. Opt. Laser Technol. 2016, 86, 33–38. [Google Scholar]
- Dhall, S.; Pal, S.K.; Sharma, K. Cryptanalysis of image encryption scheme based on a new 1D chaotic system. Signal Process. 2018, 146, 22–32. [Google Scholar]
- Sun, Y.; Luo, H.; Das, S.K. A trust-based framework for fault-tolerant data aggregation in wireless multimedia sensor networks. IEEE Trans. Dependable Secur. Comput. 2012, 9, 785–797. [Google Scholar]
- Luo, H.; Luo, J.; Liu, Y.; Das, S. Adaptive data fusion for energy efficient routing in wireless sensor networks. IEEE Trans. Comput. 2006, 55, 1286–1299. [Google Scholar]
- Zhao, D.; Li, X.Y.; Ma, H. How to crowdsource tasks truthfully without sacrificing utility: Online incentive mechanisms with budget constraint. In Proceedings of the IEEE INFOCOM 2014-IEEE Conference on Computer Communications, Toronto, ON, Canada, 27 April–2 May 2014. [Google Scholar]
- Mondal, B.; Kumar, P.; Singh, S. A chaotic permutation and diffusion based image encryption algorithm for secure communications. Multimed. Tools Appl. 2018, 77, 31177–31198. [Google Scholar]
- Jolfaei, A.; Wu, X.W.; Muthukkumarasamy, V. On the Security of Permutation-Only Image Encryption Schemes. IEEE Trans. Inf. Forensics Secur. 2015, 11, 235–246. [Google Scholar]
- Kerckhoffs, A. La cryptographie militaire. J. Des Sci. Mil. 1883, 4, 161–191. [Google Scholar]



| Image Size | Image | Encrypted | Attack | ||||
|---|---|---|---|---|---|---|---|
| Permutation | Diffusion | Total | Permutation | Diffusion | Total | ||
| 256 × 256 | Lena | 0.0654 | 0.1445 | 0.2099 | 0.4619 | 2.4130 | 2.8749 |
| Peppers | 0.1285 | 0.1359 | 0.2644 | 0.3859 | 2.4044 | 2.7903 | |
| Chemical plant | 0.0691 | 0.1343 | 0.2034 | 0.4268 | 2.4500 | 2.8768 | |
| Average running time | 0.0877 | 0.1382 | 0.2259 | 0.4249 | 2.4225 | 2.8473 | |
| 512 × 512 | Lena | 0.3460 | 0.5924 | 0.9384 | 1.8203 | 8.2682 | 10.0885 |
| Peppers | 0.3620 | 0.5283 | 0.8903 | 1.6024 | 8.0715 | 9.6739 | |
| Chemical plant | 0.3739 | 0.6094 | 0.9833 | 1.4860 | 8.3940 | 9.8800 | |
| Average running time | 0.3606 | 0.5767 | 0.9373 | 1.6362 | 8.2446 | 9.8808 | |
| 1024 × 1024 | Lena | 1.3516 | 2.3106 | 3.6622 | 0.4619 | 32.7784 | 33.2403 |
| Peppers | 1.2991 | 2.2230 | 3.5221 | 6.6447 | 34.2910 | 40.9357 | |
| Chemical plant | 1.3232 | 2.3558 | 3.6790 | 6.0613 | 32.3943 | 38.4556 | |
| Average running time | 1.3246 | 2.2965 | 3.6211 | 4.3893 | 33.1546 | 37.5439 | |
© 2019 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Li, M.; Zhou, K.; Ren, H.; Fan, H. Cryptanalysis of Permutation–Diffusion-Based Lightweight Chaotic Image Encryption Scheme Using CPA. Appl. Sci. 2019, 9, 494. https://doi.org/10.3390/app9030494
Li M, Zhou K, Ren H, Fan H. Cryptanalysis of Permutation–Diffusion-Based Lightweight Chaotic Image Encryption Scheme Using CPA. Applied Sciences. 2019; 9(3):494. https://doi.org/10.3390/app9030494
Chicago/Turabian StyleLi, Ming, Kanglei Zhou, Hua Ren, and Haiju Fan. 2019. "Cryptanalysis of Permutation–Diffusion-Based Lightweight Chaotic Image Encryption Scheme Using CPA" Applied Sciences 9, no. 3: 494. https://doi.org/10.3390/app9030494
APA StyleLi, M., Zhou, K., Ren, H., & Fan, H. (2019). Cryptanalysis of Permutation–Diffusion-Based Lightweight Chaotic Image Encryption Scheme Using CPA. Applied Sciences, 9(3), 494. https://doi.org/10.3390/app9030494





