1. Introduction
Nowadays, Cyber-Physical Systems (CPS) are bringing a new wave of innovation into our lives. This paradigm allows modern automotive systems to be more smart, intelligent and super-connected. They exploit various sensors, sophisticated control, powerful computation and seamless networking in order to improve convenience, efficiency, and safety [
1].
Various and large amounts of data required to control the vehicles are obtained from the equipped sensors in automotive CPS and are transmitted on vehicular networks. If any sensor is faulty temporarily during the operation due to environmental uncertainty, it may read wrong data [
2]. Besides, often there is a case where the wrong data are transmitted from a sensor to a controller. Sensor measurements might be lost if the communication errors occur when transmitting the data on Controller Area Network (CAN), FlexRay and Local Interconnect Network (LIN) [
3]. For any malicious purpose, an external attacker could steal, manipulate, and then inject data of the sensor [
4]. The data integrity is violated in the sense of delivery of inaccurate and distorted information in all three cases. In this paper, all three cases are referred to as sensor attacks.
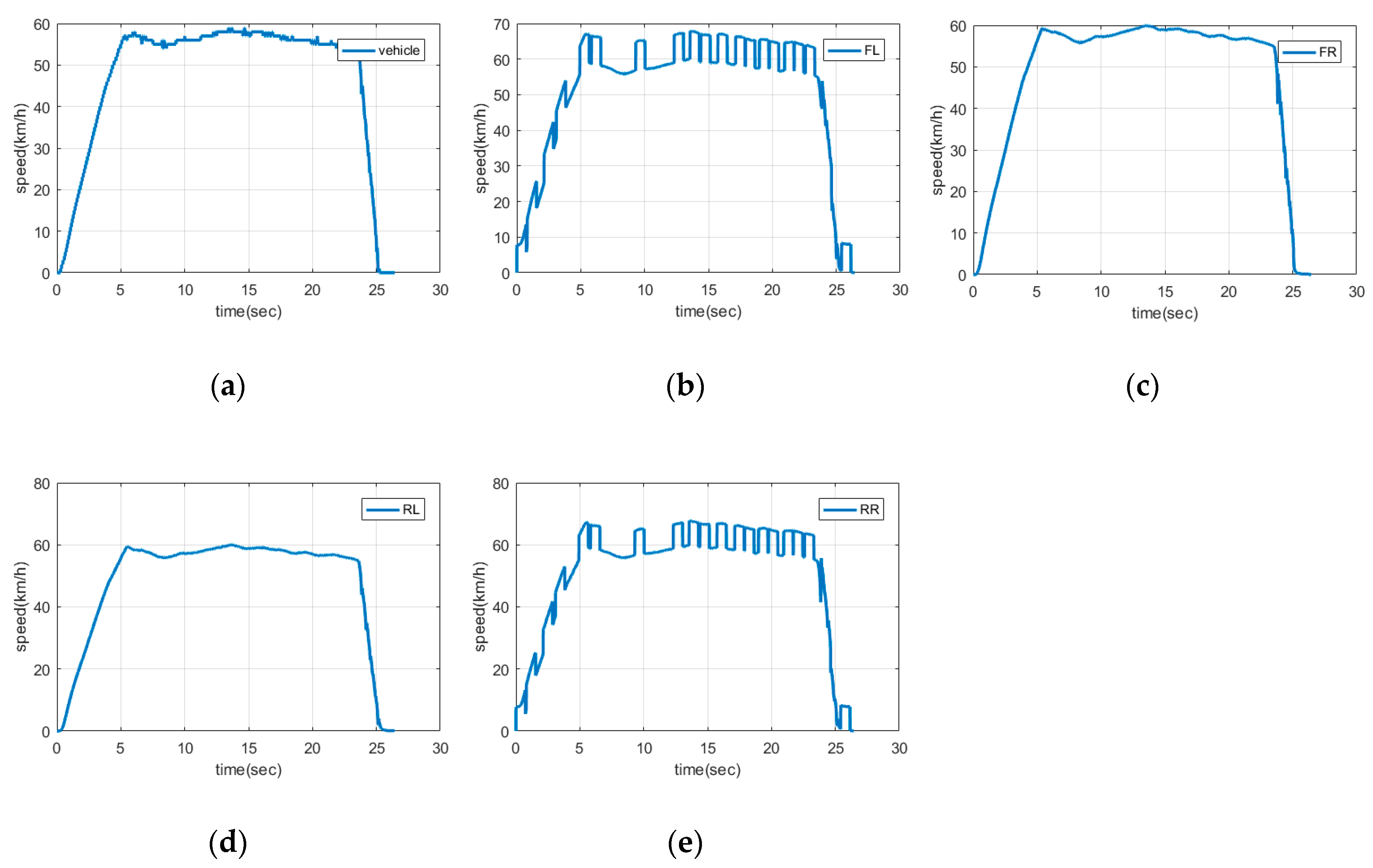
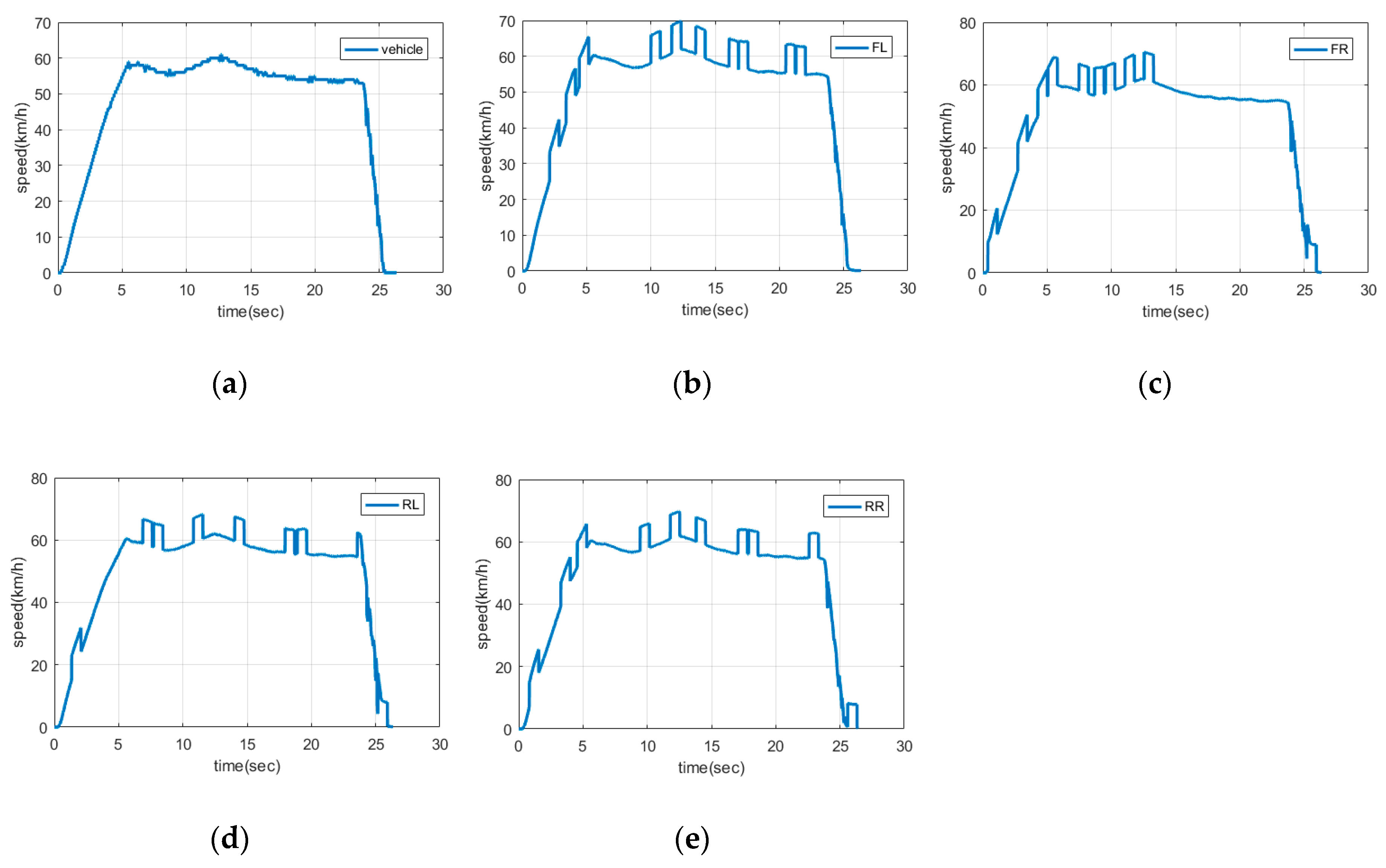
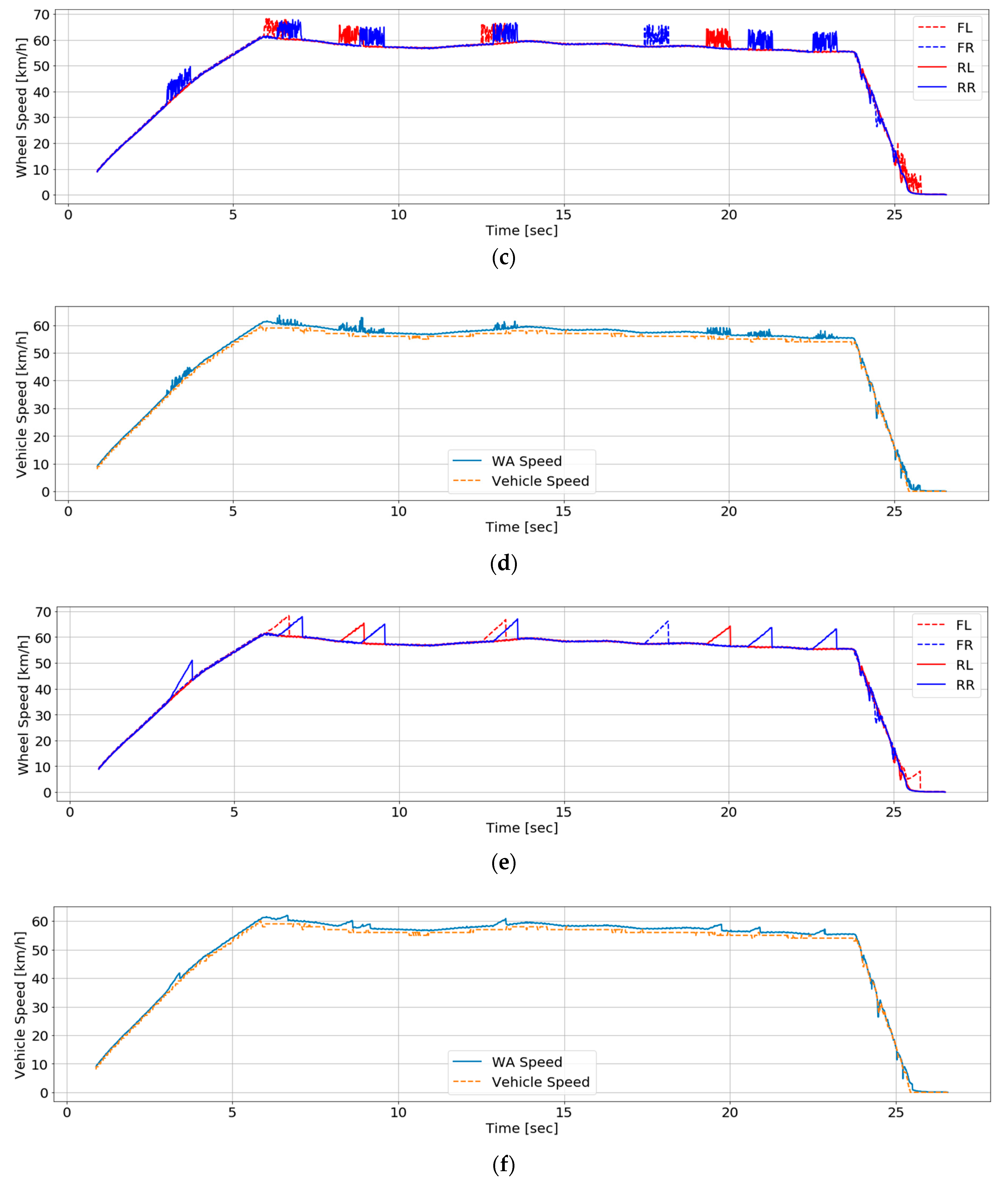
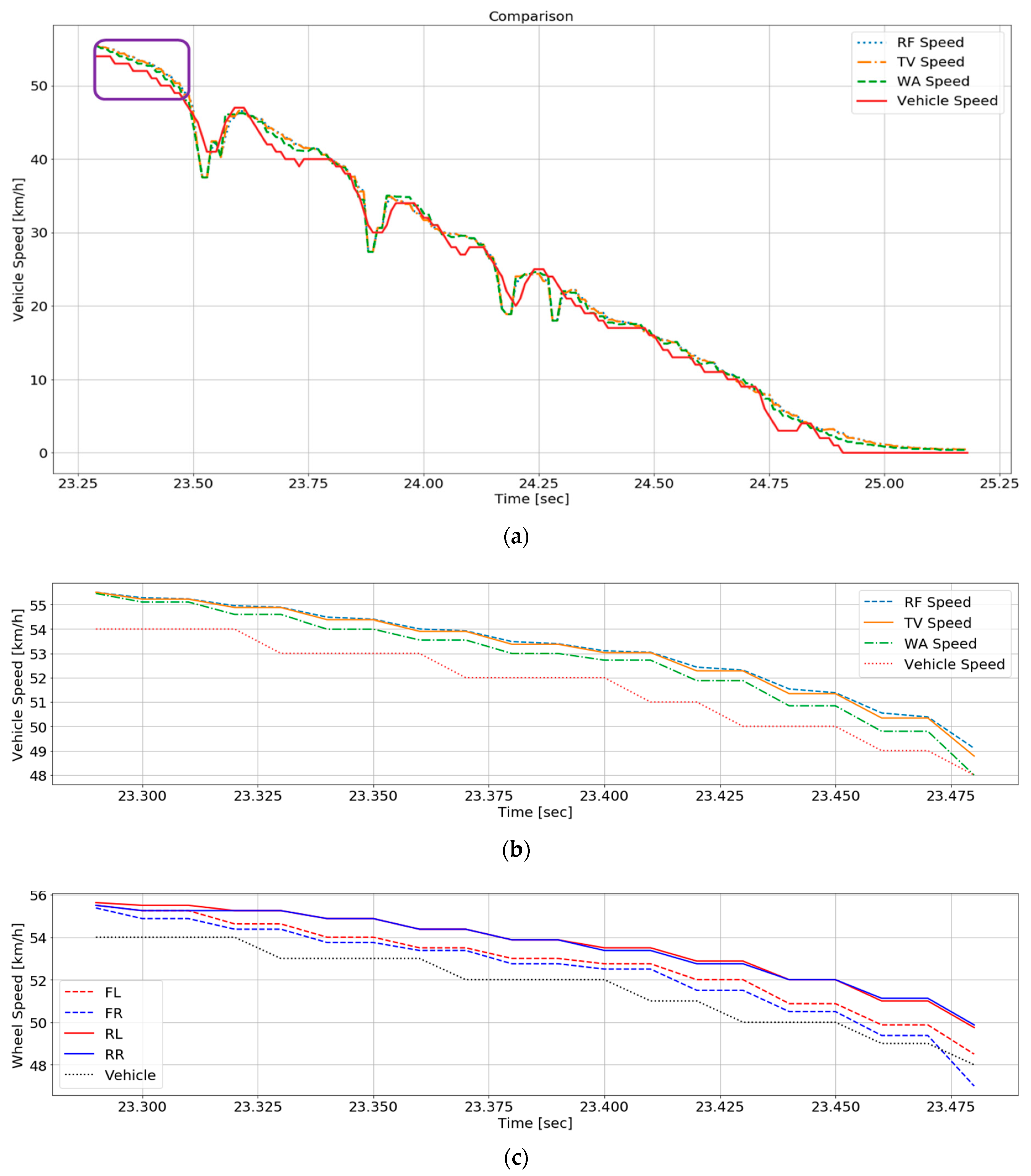
In the automotive CPS, if the data integrity of the sensor is not ensured, it is dangerous to the safety of drivers and pedestrians. Especially, the drivers and pedestrians would experience a catastrophic accident if an attack happens on a sensor used to implement a safety critical application such as Smart Cruise Control (SCC), airbag system, and Anti-lock Braking System (ABS). Data integrity is important on ABS. A vehicle speed is calculated based on four wheel speeds. When attacks occur on wheel speed sensors, the vehicle speed is miscalculated, and then the wrong speed information is sent to Brake Control Unit (BCU). The BCU decides whether to tighten wheels or not based on the wheel speeds and vehicle speed. Finally, the vehicle could spin or crash because clamping does not work at an appropriate time. Therefore, sensor attacks should be detected to ensure data integrity of the automotive CPS. In this regard, through handling the measurements of the sensor precisely, it is necessary to identify on which sensor an attack happens and then elaborately estimate the required value for safe control.
In the existing literature in relation to attack detection and identification, hardware redundancy has actively applied to detect an attacked sensor. Hardware redundancy uses multiple sensors to measure the same variables. Park et al. have solved an attack detection problem by using data of other normal sensors although an attack happens on one sensor [
5]. This approach provides the system with the exact information of the sensors but has disadvantages of cost, weight, space, and power. Model-based methods have been exploited to overcome the disadvantages of hardware redundancy in much literature. Model-based methods detect an attacked sensor and estimates data of the sensor by modeling vehicle dynamics. However, since vehicles are affected by a variety of factors due to rapid environmental changes, it is difficult to model perfectly the vehicles including all the factors. Samy et al. detected an attack by applying Extended Kalman Filter (EKF), but there are discrepancies between a real environment and a mathematical model because of linearization of the model [
6]. Amin et al. have studied an attack detection method to use an observer, but their system needs accurate flow dynamics [
7].
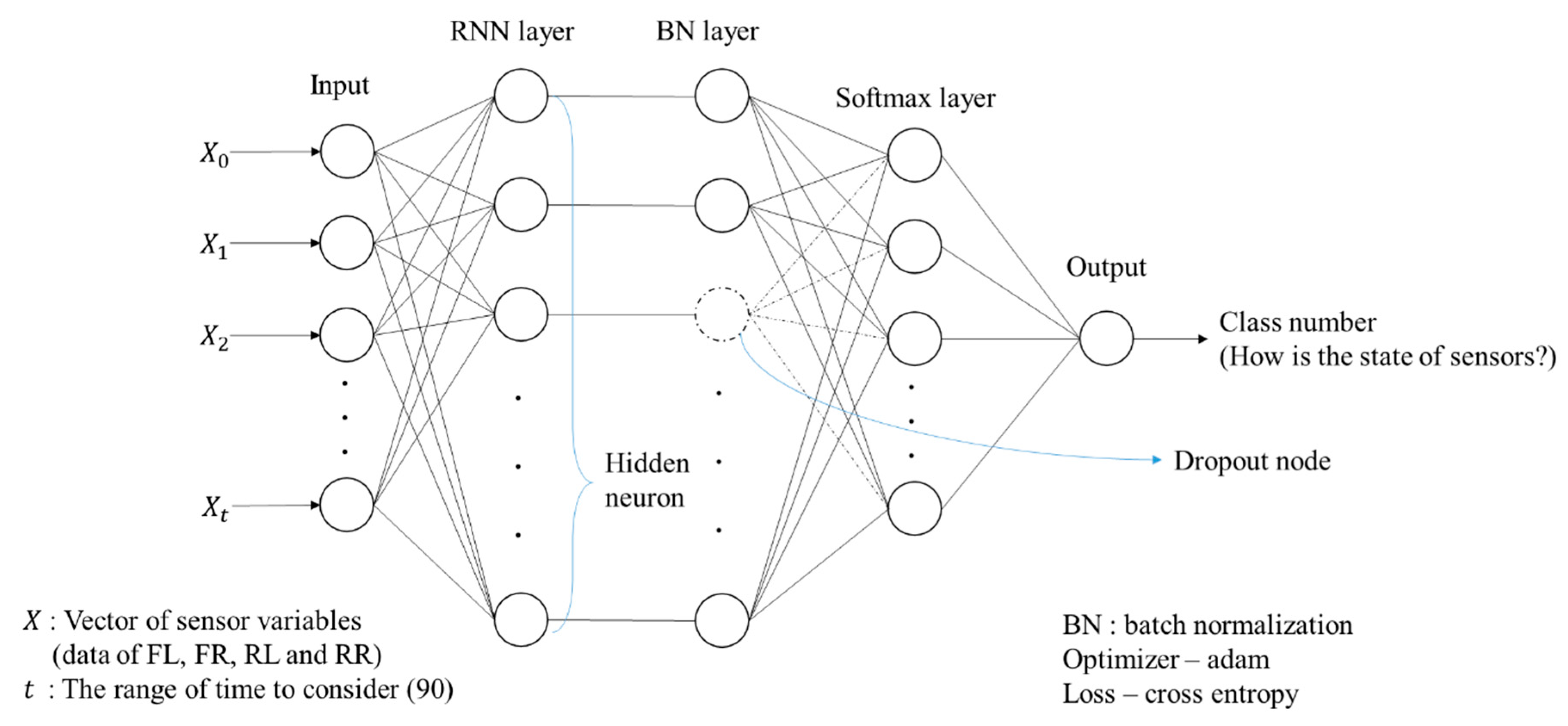
In recent years, data-based methods have been employed. Data-based methods represent the relationship between input and output by using data without modeling a system. Especially, machine learning technology, one of data-based methods, is emerging as an attack detection method. In machine learning, important features are processed manually and there is a limitation to learn a relatively complex system. Deep Neural Networks (DNNs) are capable of finding important features automatically and representing the relationship between input and output in a complex system. Meanwhile, automotive CPS may momentarily misrecognize normal data as data of the attacked sensor if stones or pits appear on the rough road because the driving environment is constantly changing. Recurrent Neural Network (RNN) among DNNs handles this problem by exploiting the previous information as a current input sequence [
8]. Despite sudden changes in the road environment while the vehicle is running, it is less influenced by the environment in predicting the present results because it knows the past information. Therefore, even if a sensor read the strange value at that moment, the detection result is output by referring to the past and current information overall.
A straightforward approach to estimate a vehicle speed accurately is to add sensors in the manner of hardware redundancy. Song et al. have estimated vehicle speeds by adding an accelerometer [
9]. Cumulative errors of the accelerometer’s measurements used for their speed calculation cause the inaccurate estimation of vehicle speeds. Bevly et al. have exploited Global Positioning System (GPS) in order to estimate vehicle speeds based on the wheel slip [
10]. When their system is deployed in skyscrapers or tunnels, it becomes difficult to get the accurate GPS measurements due to the interference of the magnetic field. In terms of cost-effectiveness, using heterogeneous sensors such as the accelerometer, GPS, or other sensors is not cheap. Thus, homogeneous sensors (i.e., wheel speed sensors) are employed in this work. Fusion process for same physical variables is needed. Conventional data fusion methods of homogeneous sensors are described in [
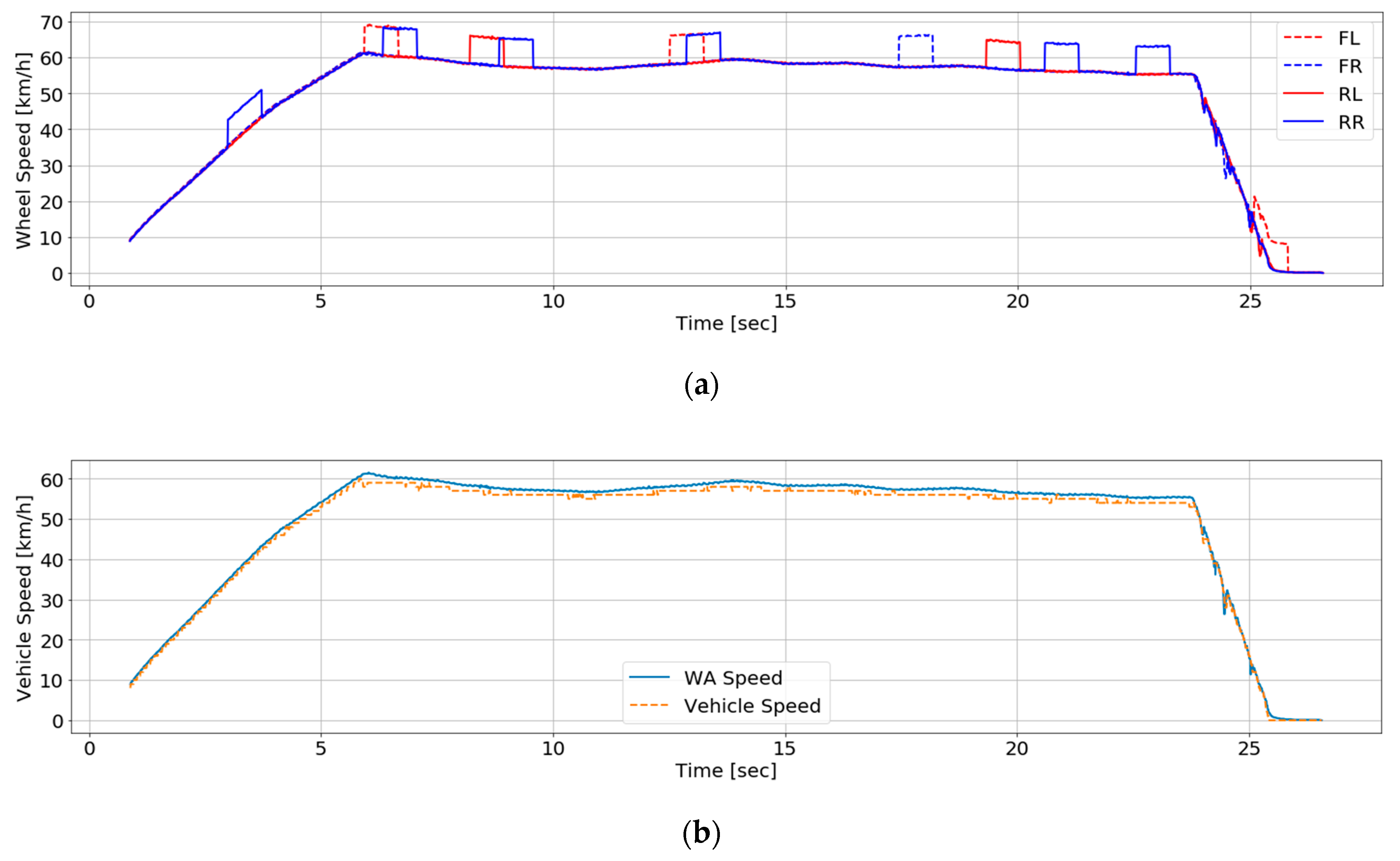
11]. It is possible for Weighted Average (WA) to change weighted values. This makes an estimation system flexible in some environments. WA is selected because it is capable of changing weighted values depending on driving environments to estimate vehicle speeds based on homogeneous wheel speed sensors.
There exist the following issues to be addressed in detecting a sensor attack and estimating a specific value on automotive CPS.
It is hard to detect all the attacked sensors even when the majority of the sensors are attacked. For attack detection and estimation, a voting method is mainly applied or the relation between sensor measurements is exploited. These methods suffer from identifying the attacked sensors in the situation where the majority of the sensors are attacked.
Another challenge is that variances between estimated vehicle speeds are large when different datasets are input. This means that the estimation method does not make sure to have high performance whenever it calculates vehicle speed.
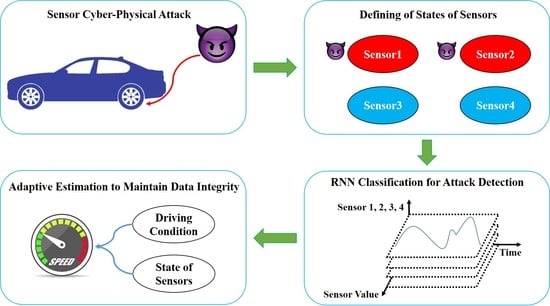
We propose a novel attack detection, identification and estimation method using only wheel speed sensors already installed in the automotive CPS. RNN is applied to sensor attack detection. To estimate the speed after attack detection and identification, we leverage and modify WA which gives different weights to each sensor in order to adapt to the dynamic environment by checking little difference between the actual measurements and the estimated values in our experiments.
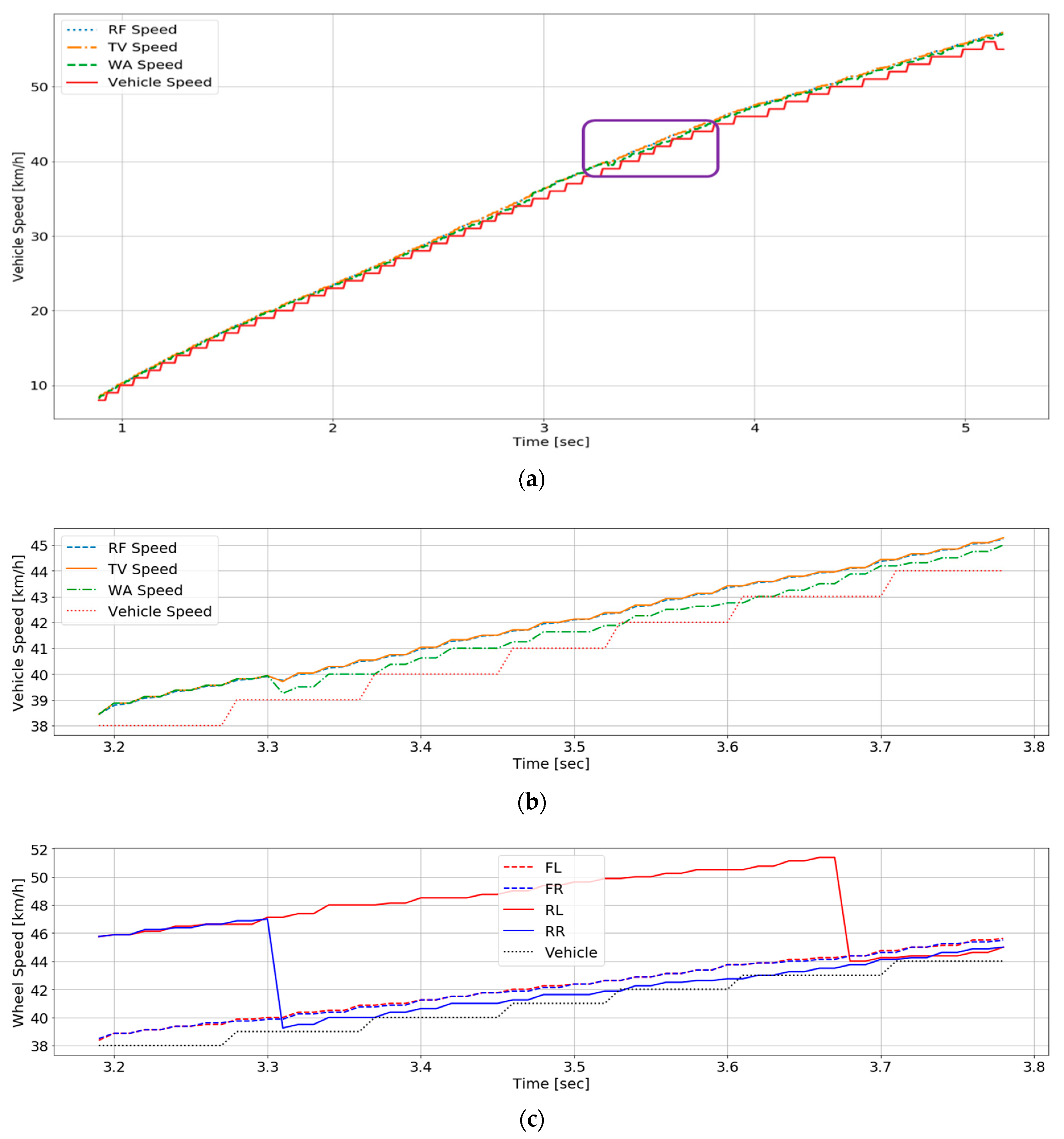
To address the above issues, we define classes of the states and design a specialized architecture to detect attacked sensors and classify states of all the sensors in RNN. This approach lets our system distinguish normal sensors from the majority of attacked sensors. For the speed estimation, parameters of WA is set after understanding characteristics of driving. The performance of the WA method depends on setting the weight required for it. In other words, if the weights are not fixed well, the performance of WA has big differences between results of different input datasets. For this reason, we have trouble in fixing a weight of WA.
Hence, we tune the weight of the WA through driving condition analysis to adapt to the dynamic conditions including the center of gravity and inertia. The driving condition is divided into tracking and braking. Between them, data of the braking has different patterns from the data seen during tracking because wheel slip happens frequently during braking. If we ignore the characteristics of data with different patterns representing these conditions and a single static weight with a constant value is applied to the braking condition in order to estimate the speed, our speed estimation yield the unexpected and inaccurate results. Furthermore, the front wheels operate differently from the rear wheels during braking. In order to explore the characteristics of the front and rear wheels while braking and tracking, we compare each Mean Squared Error (MSE) value of the pairs when the weights with a certain value are given on individual pairs of the front wheels and the rear wheels, respectively. According to these MSE values, each weight is determined for the front wheels and the rear wheels during braking. The determined different weights by the defined classes and divided conditions are used to estimate vehicle speeds.
Although this paper concentrates on attacks on wheel speed sensors to enhance the safety of the automotive CPS, we aim to provide a diagnosis system and present direction of attack detection and data recovery methods in all of the industry so that a controller can receive exact information from sensors and control an actuator stably for safety and security.
The contributions of this paper by solving the two research issues above are as follows.
In order to detect and identify attacks that simultaneously happen on the majority of sensors, we present how RNN learns and predicts data obtained from a real vehicle. Each state of the sensors is defined as 15 classes and an architecture is designed by repeated experiments.
We propose a speed estimation method based on modified WA using data of only normal sensors. Each driving situation is analyzed to increase the performance of speed estimation. We divide the situations into traction and braking and provide how to assign different weights depending on the driving situations and classes in automotive CPS.
There are very few studies to address both attack detection and identification and vehicle speed estimation at the same time. In this work, the process of attack detection is connected to that of vehicle speed estimation to satisfy data recovery property.
The remainder of the paper is organized as follows. In
Section 2, we provide the information about sensor data and describe how sensor attack detection system is developed.
Section 3 puts forward how to estimate vehicle speeds by applying some algorithms. Our system is validated and the results are analyzed in
Section 4. Finally, we draw conclusions and discuss future works in
Section 5.