Side-Channel Vulnerabilities of Unified Point Addition on Binary Huff Curve and Its Countermeasure
Abstract
:1. Introduction
2. Preliminaries
2.1. Binary Huff Curve and Unified Point Addition
2.2. ROSETTA and HCCA
- ROSETTA. Clavier’s attack needs a single power consumption trace to recover secret information. For each field multiplication, ROSETTA detects whether the operation is (squaring) or (multiplication). Let and . A w-bit multiplication can be identified from the specific pattern in side-channel power consumption. ROSETTA considers the observation and extracted from the multiplication for all :s.t ⇒ Prob() for alls.t ⇒ Prob() for allFrom the observations and , collisions between and for all can be used to identify squarings from multiplications. To identify these collisions of field multiplication trace, ROSETTA exploits a triangle trace analysis which uses a Euclidean distance distinguisher relying on a collision correlation technique.
- HCCA. Bauer et al. introduced this method to extract keys using the collision of field multiplications in a single power consumption trace. The core idea of this attack is that collision occurs during two field multiplication computations when the same operands are used, which can be detected by HCCA. When performed in a horizontal setting, the observations and are extracted from the two field multiplications.and s.t and ⇒ Prob() for alland s.t and ⇒ Prob() ≈ 0 for allThe correlation between the two observations is then estimated by Pearson’s coefficient in order to determine whether the two operands of the field multiplications are the same or different.
3. Vulnerabilities of Unified Point Addition
3.1. Vulnerabilities of Unified Point Addition
- Type 1. (Vulnerability by ROSETTA): The unified point addition operation can compute the point doubling and point addition with the same formula. However, depending on the input points of unified point addition, field multiplications can be performed as squaring or multiplication. For example, let and be the two input points of the unified point addition formula. Note that there exists the operation in unified point addition. If , then this operation computes to . If , then this operation computes to . Then, this operation becomes a vulnerability that is exploitable by ROSETTA.
- Type 2. (Vulnerability by HCCA): Considering two field multiplications, if they have at least one common operand, they can be distinguished by HCCA. In unified point addition, the two different multiplications can be identically computed according to the inputs. For example, the operations and exist in unified point addition. If , then will be computed twice. If , then and will be computed. Then, these operations become a vulnerability that is exploitable by HCCA.
3.2. Vulnerabilities of Binary Huff Curve
- Type 1 vulnerability: Let us consider the computation of . In this formula, it is computed as for , whereas it is computed as for . Similarly, for , for , and , these are computed as , , , and , respectively. Thus, an adversary can distinguish between and .
- Type 2 vulnerability: In Table 1, let us consider the computations of , , and for , , and , respectively. If , then . Since the value of is zero in , then for . Also, for . Thus, the operands of , , and for , , and are the same for but different for . Similarly, consider and for and . Since , and have the same inputs for but different inputs for . Therefore, they can be distinguished between and .
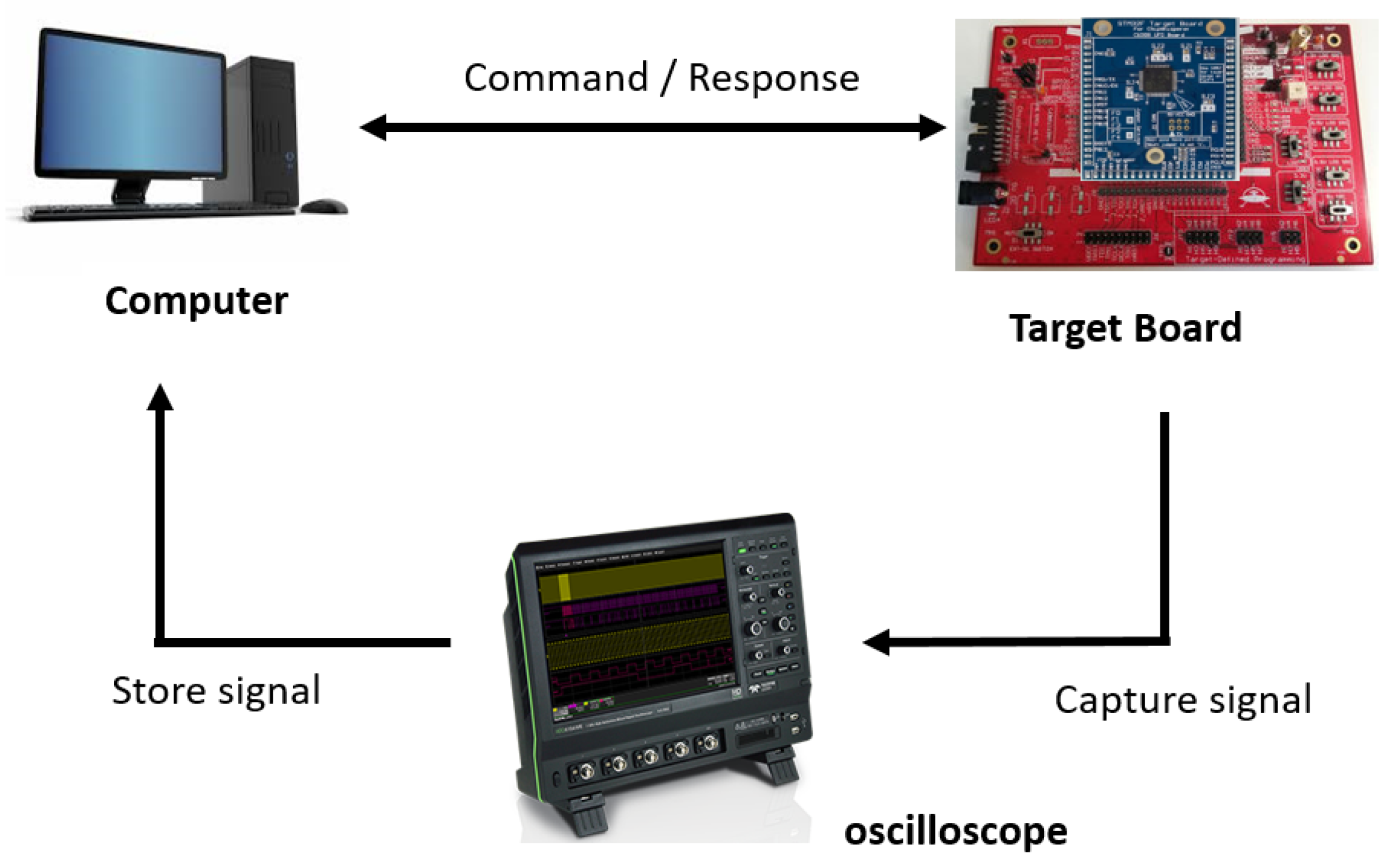
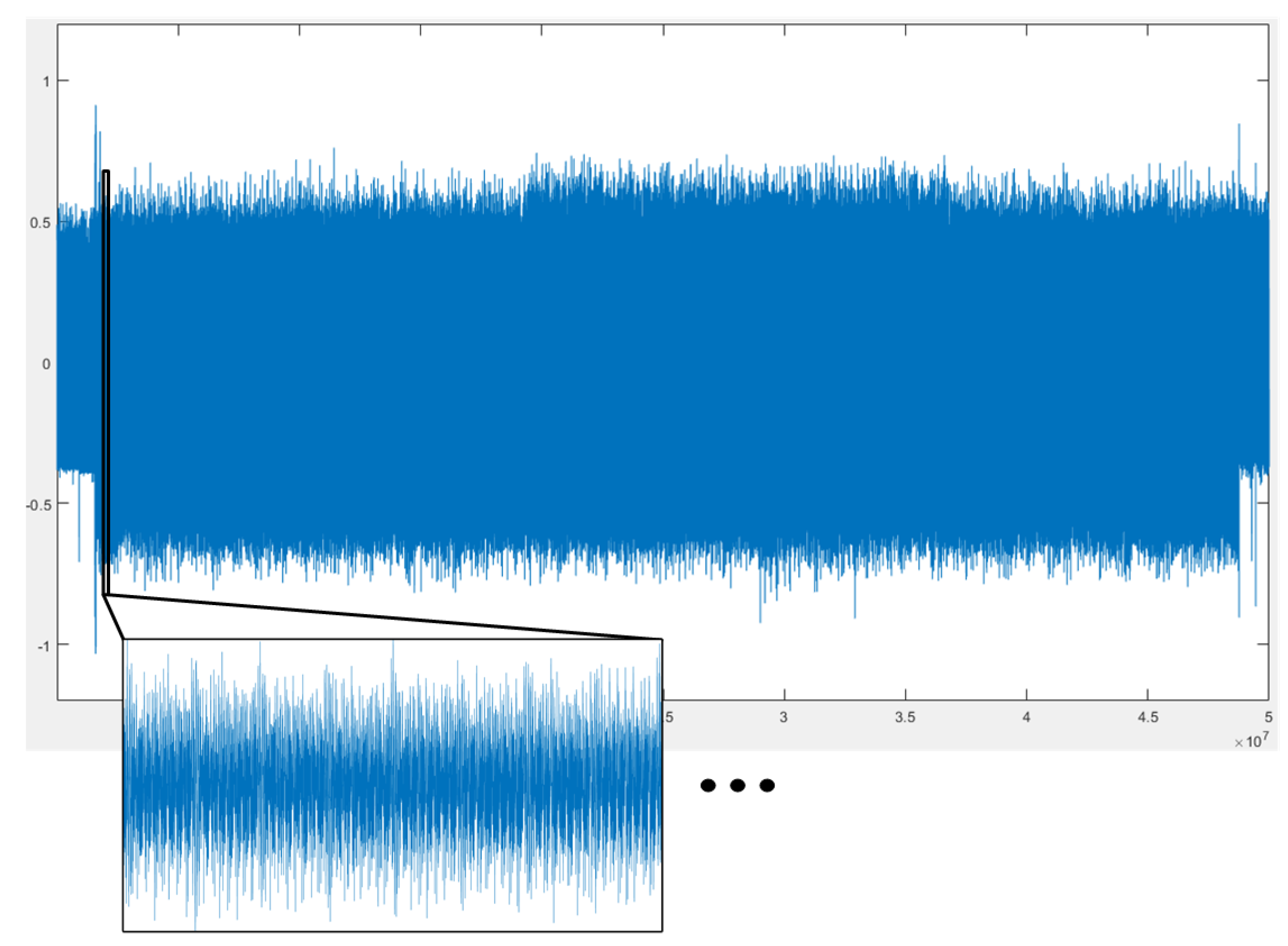
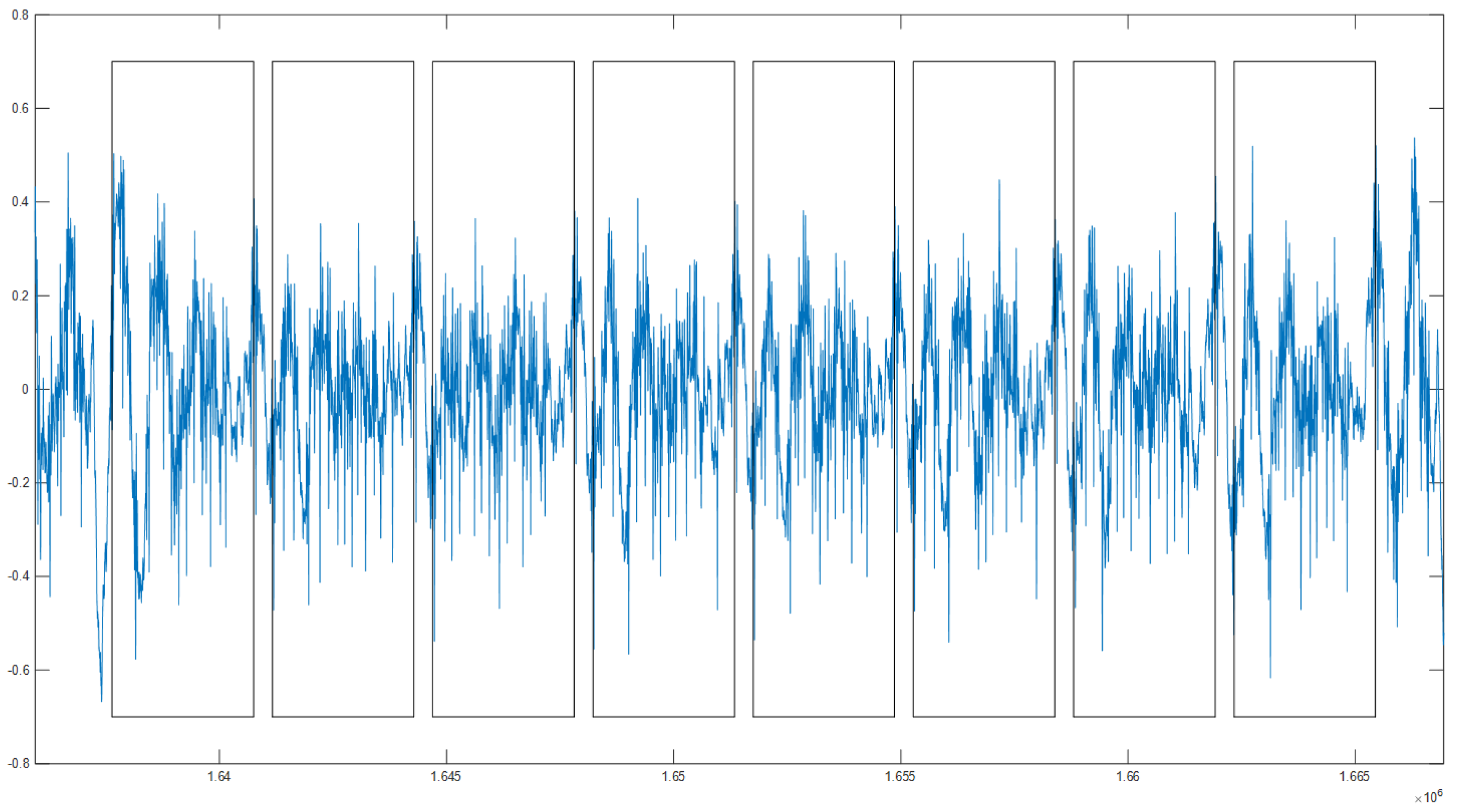
4. Experiments
5. Countermeasures
5.1. Countermeasures
| Algorithm 1: A w-bit random projective coordinate for the binary Huff curve (wRPC) |
| Require: Ensure:
|
| Algorithm 2: Side-channel atomic algorithm using wRPC |
| Require: , Ensure:
|
5.2. Security Analysis of the Proposed Method
- Type 1 vulnerability: As shown in Table 2, if , then the output of the proposed unified point addition operation is , where is the output of Table 1. Since , then . In addition, if , then , and can be computed as follows:For , although , the operands and are different. Similarly, the operands of the field multiplications for , and are different. Also, there is no other field multiplication vulnerable to Type 1. Thus, the proposed algorithm is secure against the Type 1 vulnerability for the binary Huff curve.
- Type 2 vulnerability: Although wRPC is applied to the proposed unified point addition operation, and when . Thus, . Similarly, . Thus, if we compute , , and as the previous unified point addition operation, their operands are the same when . On the other hand, they are different when . Likewise, the operands of and are the same when . They become targets to a Type 2 vulnerability. The reason for this vulnerability is that the same intermediate results occur in the previous unified point addition operation. They are used as inputs to more than one multiplication without modification for . Thus, we used the proposed method to mask the operands of vulnerable multiplications. Considering and in Table 1, since the operand is identically used in two multiplications, they do not affect the vulnerability. Thus, we only have to mask the other operand (or ). Specifically, we computed as so that an adversary cannot distinguish between and using a Type 2 vulnerability. However, we additional cost is incurred for . To reduce this additional cost, we computed as to use the advantage of zero computational cost for squaring in a binary field, which is almost free. Similarly, we applied masking to as . In addition, for and , we modified the computation of as and without performing . Based on the proposed algorithm, Type 1 and Type 2 vulnerabilities no longer exist (Table 2).
6. Comparisons
7. Conclusions
Author Contributions
Funding
Conflicts of Interest
Appendix A
| Curve | Type 1 | Type 2 | Countermeasures |
|---|---|---|---|
| Weierstraß | insecure | insecure | wRPC The modified unified point addition |
| Hessian | insecure | insecure | wRPC |
| Edwards | insecure | secure | wRPC |
| Jacobi intersections | secure | insecure | wRPC |
| Jacobi quartic | insecure | insecure | wRPC |
| binary Edwards | insecure | insecure | wRPC The modified unified point addition |
Appendix A.1. Weierstraß Elliptic Curve
- Type 1 vulnerability: Let us consider the computation . In this formula, it is computed as for , whereas it is computed as for . Similarly, for in R, this is computed as for . Thus, we can distinguish between and using ROSETTA.
- Type 2 vulnerability: Let us consider the computations and . If , then is computed twice. Namely, the operands of and for and are the same for but different for . Similarly, considering and , the multiplications for and have the same operands for but different operands for . Therefore, we can distinguish between and using HCCA.
| Out | ||
|---|---|---|
| Z | ||
| ⋮ | ⋮ | ⋮ |
Appendix A.2. Hessian Elliptic Curve
- Type 1 vulnerability: Let us consider the computation . In this formula, it is computed as for , whereas it is computed as for . Similarly, in and , these are computed as and for , respectively. Thus, we can distinguish between and using ROSETTA.
- Type 2 vulnerability: Let us consider the computations and . If , then and are computed. Thus, they have the same operand when but not when . Similarly, considering and , the multiplications for C and E have the same operand for and different operands for . Also, the multiplications for A and E have the same operand for . Therefore, we can distinguish between and using HCCA.
| Out | ||
|---|---|---|
| A | ||
| B | ||
| C | ||
| D | ||
| E | ||
| F | ||
| ⋮ | ⋮ | ⋮ |
Appendix A.3. Edwards Elliptic Curve
- Type 1 vulnerability: Let us consider the computation . In this formula, it is computed as for , whereas it is computed as for . Similarly, in , and , and these are computed as , , and for , respectively. Thus, we can distinguish between and using ROSETTA.
- Type 2 vulnerability: The vulnerability of Type 2 does not exist.
| Out | ||
|---|---|---|
| A | ||
| B | ||
| C | ||
| D | ||
| ⋮ | ⋮ | ⋮ |
Appendix A.4. Jacobi Intersections Elliptic Curve
- Type 1 vulnerability: The vulnerability of Type 1 does not exist.
- Type 2 vulnerability: Let us consider the computations of and . If , then are computed twice. Namely, the operands of and for A and B are the same for and different for . Similarly, consider multiplications for B and D, E and G, F and H, and J and K. These multiplication pairs have the same operands for and different operands for . Also, consider multiplication of and . If , then and are computed. Thus, they have the same operand when but not when . Similarly, the multiplication pairs A and H, B and E, B and F, C and E, C and F, D and G, and D and H have the same operand , , , , , , and for , respectively. Therefore, we can distinguish between and using HCCA.
| Out | ||
|---|---|---|
| A | ||
| B | ||
| C | ||
| D | ||
| E | ||
| F | ||
| G | ||
| H | ||
| ⋮ | ⋮ | ⋮ |
Appendix A.5. Jacobi Quartic Elliptic Curve
- Type 1 vulnerability: Let us consider the computation . In this formula, it is computed as for , whereas it is computed as for . Similarly, in and , these are computed as and for , respectively. Thus, we can distinguish between and using ROSETTA.
- Type 2 vulnerability: Let us consider the computations and . If ; then, and are computed. Thus, they have the same operand when but not when . Similarly, considering and , the multiplications for C and E have the same operand for and different operands for . Also, the multiplications for A and E have the same operand for . Therefore, we can distinguish between and using HCCA.
| Out | ||
|---|---|---|
| A | ||
| B | ||
| C | ||
| D | ||
| E | ||
| F | ||
| ⋮ | ⋮ | ⋮ |
Appendix A.6. Binary Edwards Elliptic Curve
- Type 1 vulnerability: Let us consider the computation . In this formula, it is computed as for , whereas it is computed as for . Similarly, for , , , , and , these are computed as , , , , and for . Also, if , I and J compute as follows:andThus, if , An adversary can distinguish between and using ROSETTA.
- Type 2 vulnerability: Let us consider the computations , in V and in . If , since , both operations have at least one same operand. Therefore, they can be distinguished using HCCA.
| Out | ||
|---|---|---|
| A | ||
| B | ||
| C | ||
| G | ||
| H | ||
| K | ||
| ⋮ | ⋮ | ⋮ |
References
- Kocher, P.; Jaffe, J.; Jun, B. Differential power analysis. In Proceedings of the Annual International Cryptology Conference, Santa Barbara, CA, USA, 15–19 August 1999; Springer: Berlin/Heidelberg, Germany, 1999; pp. 388–397. [Google Scholar]
- Coron, J.S. Resistance against differential power analysis for elliptic curve cryptosystems. In Proceedings of the International Workshop on Cryptographic Hardware and Embedded Systems, Worcester, MA, USA, 12–13 August 1999; Springer: Berlin/Heidelberg, Germany, 1999; pp. 292–302. [Google Scholar]
- Izu, T.; Takagi, T. A fast parallel elliptic curve multiplication resistant against side channel attacks. In Proceedings of the International Workshop on Public Key Cryptography, Paris, France, 12–14 February 2002; Springer: Berlin/Heidelberg, Germany, 2002; pp. 280–296. [Google Scholar]
- Chevallier-Mames, B.; Ciet, M.; Joye, M. Low-cost solutions for preventing simple side-channel analysis: Side-channel atomicity. IEEE Trans. Comput. 2004, 53, 760–768. [Google Scholar] [CrossRef]
- Brier, E.; Joye, M. Weierstraß elliptic curves and side-channel attacks. In Proceedings of the International Workshop on Public Key Cryptography, Paris, France, 12–14 February 2002; Springer: Berlin/Heidelberg, Germany, 2002; pp. 335–345. [Google Scholar]
- Bauer, A.; Jaulmes, E.; Prouff, E.; Reinhard, J.R.; Wild, J. Horizontal collision correlation attack on elliptic curves. Cryptogr. Commun. 2015, 7, 91–119. [Google Scholar] [CrossRef]
- Clavier, C.; Feix, B.; Gagnerot, G.; Giraud, C.; Roussellet, M.; Verneuil, V. ROSETTA for single trace analysis. In Proceedings of the International Conference on Cryptology in India, Kolkata, India, 9–12 December 2012; Springer: Berlin/Heidelberg, Germany, 2012; pp. 140–155. [Google Scholar]
- Devigne, J.; Joye, M. Binary huff curves. In Proceedings of the Cryptographers’ Track at the RSA Conference, San Francisco, CA, USA, 14–18 February 2011; Springer: Berlin/Heidelberg, Germany, 2011; pp. 340–355. [Google Scholar]
- Ghosh, S.; Kumar, A.; Das, A.; Verbauwhede, I. On the implementation of unified arithmetic on binary huff curves. In Proceedings of the International Workshop on Cryptographic Hardware and Embedded Systems, Santa Barbara, CA, USA, 20–23 August 2013; Springer: Berlin/Heidelberg, Germany, 2013; pp. 349–364. [Google Scholar]
- Clavier, C.; Feix, B.; Gagnerot, G.; Roussellet, M.; Verneuil, V. Horizontal correlation analysis on exponentiation. In Proceedings of the International Conference on Information and Communications Security, Barcelona, Spain, 15–17 December 2010; Springer: Berlin/Heidelberg, Germany, 2010; pp. 46–61. [Google Scholar]
- Joye, M.; Tibouchi, M.; Vergnaud, D. Huff’s model for elliptic curves. In Proceedings of the International Algorithmic Number Theory Symposium, Nancy, France, 19–23 July 2010; Springer: Berlin/Heidelberg, Germany, 2010; pp. 234–250. [Google Scholar]
- O’Flynn, C.; Chen, Z.D. Chipwhisperer: An open-source platform for hardware embedded security research. In Proceedings of the International Workshop on Constructive Side-Channel Analysis and Secure Design, Paris, France, 13–15 April 2014; Springer: Berlin/Heidelberg, Germany, 2014; pp. 243–260. [Google Scholar]
- Gierlichs, B.; Lemke-Rust, K.; Paar, C. Templates vs. stochastic methods. In Proceedings of the International Workshop on Cryptographic Hardware and Embedded Systems, Yokohama, Japan, 10–13 October 2006; Springer: Berlin/Heidelberg, Germany, 2006; pp. 15–29. [Google Scholar]
- Welch, B.L. The generalization ofstudent’s’ problem when several different population variances are involved. Biometrika 1947, 34, 28–35. [Google Scholar] [PubMed]
- Hospodar, G.; Gierlichs, B.; De Mulder, E.; Verbauwhede, I.; Vandewalle, J. Machine learning in side-channel analysis: a first study. J. Cryptogr. Eng. 2011, 1, 293. [Google Scholar] [CrossRef]
- Choudary, O.; Kuhn, M.G. Efficient template attacks. In Proceedings of the International Conference on Smart Card Research and Advanced Applications, Berlin, Germany, 27–29 November 2013; Springer: Berlin/Heidelberg, Germany, 2013; pp. 253–270. [Google Scholar]
- Durvaux, F.; Standaert, F.X. From improved leakage detection to the detection of points of interests in leakage traces. In Proceedings of the Annual International Conference on the Theory and Applications of Cryptographic Techniques, Vienna, Austria, 8–12 May 2016; Springer: Berlin/Heidelberg, Germany, 2016; pp. 240–262. [Google Scholar]
- Hankerson, D.; Menezes, A.J.; Vanstone, S. Guide to Elliptic Curve Cryptography; Springer Science & Business Media: Berlin/Heidelberg, Germany, 2006. [Google Scholar]
- Fan, J.; Guo, X.; De Mulder, E.; Schaumont, P.; Preneel, B.; Verbauwhede, I. State-of-the-art of secure ECC implementations: a survey on known side-channel attacks and countermeasures. In Proceedings of the 2010 IEEE International Symposium on Hardware-Oriented Security and Trust (HOST), Anaheim, CA, USA, 13–14 June 2010; pp. 76–87. [Google Scholar]
- Locke, G.; Gallagher, P. Fips pub 186-3: Digital signature standard (dss). Fed. Inf. Process. Stand. Publ. 2009, 3, 186-3. [Google Scholar]
- Bernstein, D.J. Explicit-Formulas Database. Available online: http://www. hyperelliptic. org/EFD (accessed on 22 October 2018).


| Out | ||
|---|---|---|
| Out | ||
|---|---|---|
| Algorithm | SPA | ROSETTA | HCCA |
|---|---|---|---|
| [8] | insecure | insecure | insecure |
| [9] | secure | insecure | insecure |
| [8] using [10] | secure | secure | secure |
| [9] using [10] | secure | secure | secure |
| proposed method | secure | secure | secure |
| n | Algorithm | M | Additional Cost | Total Cost | Ratio |
|---|---|---|---|---|---|
| 233 | [8,9] | 64 | - | 1088 | 1.000 |
| [8,9] using [10] | 81 | - | 1377 | 1.266 | |
| proposed method | 64 | 48 | 1136 | 1.044 | |
| 283 | [8,9] | 81 | - | 1377 | 1.000 |
| [8,9] using [10] | 100 | - | 1700 | 1.235 | |
| proposed method | 81 | 54 | 1431 | 1.039 | |
| 409 | [8,9] | 169 | - | 2873 | 1.000 |
| [8,9] using [10] | 196 | - | 3332 | 1.160 | |
| proposed | 169 | 78 | 2951 | 1.027 | |
| 571 | [8,9] | 324 | - | 5508 | 1.000 |
| [8,9] using [10] | 361 | - | 6137 | 1.114 | |
| proposed method | 324 | 108 | 5616 | 1.020 |
© 2018 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Cho, S.M.; Jin, S.; Kim, H. Side-Channel Vulnerabilities of Unified Point Addition on Binary Huff Curve and Its Countermeasure. Appl. Sci. 2018, 8, 2002. https://doi.org/10.3390/app8102002
Cho SM, Jin S, Kim H. Side-Channel Vulnerabilities of Unified Point Addition on Binary Huff Curve and Its Countermeasure. Applied Sciences. 2018; 8(10):2002. https://doi.org/10.3390/app8102002
Chicago/Turabian StyleCho, Sung Min, Sunghyun Jin, and HeeSeok Kim. 2018. "Side-Channel Vulnerabilities of Unified Point Addition on Binary Huff Curve and Its Countermeasure" Applied Sciences 8, no. 10: 2002. https://doi.org/10.3390/app8102002
APA StyleCho, S. M., Jin, S., & Kim, H. (2018). Side-Channel Vulnerabilities of Unified Point Addition on Binary Huff Curve and Its Countermeasure. Applied Sciences, 8(10), 2002. https://doi.org/10.3390/app8102002





