In this section, we propose our STA on the two cases of NTRU implementation. For each case, we first describe the implementation and then suggest our STA. Lastly, we present the experimental results on our attack. The purpose of our attack is to recover the private key. Therefore, only the implementation of decryption is introduced in this paper.
3.1. NTRU Open Source
The integral parts of NTRU implementation are the way to store polynomials and a polynomial multiplication.
Representing Polynomials
To store a polynomial f of the private key, NTRU Open Source stores the degree of indeterminant x whose coefficient is or . Because the addition is computed according to the degree of and , it is possible to operate without the degree of . Thus, the private key array first stores all the degree whose coefficient is and then it stores all the degree where its coefficient is in an array. For example, if , then the array of f would be . The polynomial in general, is stored such that the coefficient of the xth degree is the xth element in an array. For example, the polynomial represent as .
Polynomial Multiplication
For efficiency, the private key is set as
and
F is divided into three trinary polynomials
. The advantage of splitting
F, is that it lowers the hamming weight of polynomials so that the multiplication could be speed up [
13,
30]. Consequently, the decryption of NTRU Open Source performs as in Equation (
7) considering the order of multiplication.
Computation of Equation (
7) is represented in Algorithm 1 and algorithm for polynomial multiplication is in Algorithm 2.
| Algorithm 1 Decryption in NTRU Open Source |
- Require:
The trinary polynomials with degree N ▷ is a private key polynomial satisfied - Ensure:
message
- 1:
▷ Algorithm 2 is polynomial multiplication - 2:
- 3:
- 4:
fordo - 5:
▷ add t and u - 6:
end for - 7:
fordo - 8:
▷∗ is a word multiplication - 9:
end for - 10:
returnm
|
The input b of Algorithm 2 is formed in a way such that the degree having coefficient is stored in ascending order and then degree having is stored. The polynomial multiplication starts with the smallest degree where its coefficient equals to and add cipher-text to the initialized array. Since the result must be reduced modulo , this implementation performs the addition from the beginning to and restarts for the th element in an array when the degree exceeds N. After the modular operation, the sign is reversed and the same steps are repeated on for the degree having coefficient . Lastly, the (mod operation is performed by AND(∧) since the q is set as power of .
| Algorithm 2 Polynomial Multiplication during NTRU Open Source Decryption |
- Require:
Polynomial with degree N and Private key array b ▷ let b be a information of private key F - Ensure:
- 1:
for++ do - 2:
- 3:
end for - 4:
for++ do ▷ private key has coefficients equal −1 - 5:
- 6:
for ++++ do - 7:
- 8:
end for - 9:
for ++++ do - 10:
- 11:
end for - 12:
end for - 13:
for++ do ▷ This step is because the above process is for −1 - 14:
- 15:
end for - 16:
for++ do ▷ private key has coefficients equal 1 - 17:
- 18:
for ++++ do - 19:
- 20:
end for - 21:
for ++++ do - 22:
- 23:
end for - 24:
end for - 25:
for++ do - 26:
▷ in the case of q is powering of 2, works for mod q - 27:
end for - 28:
returnH
|
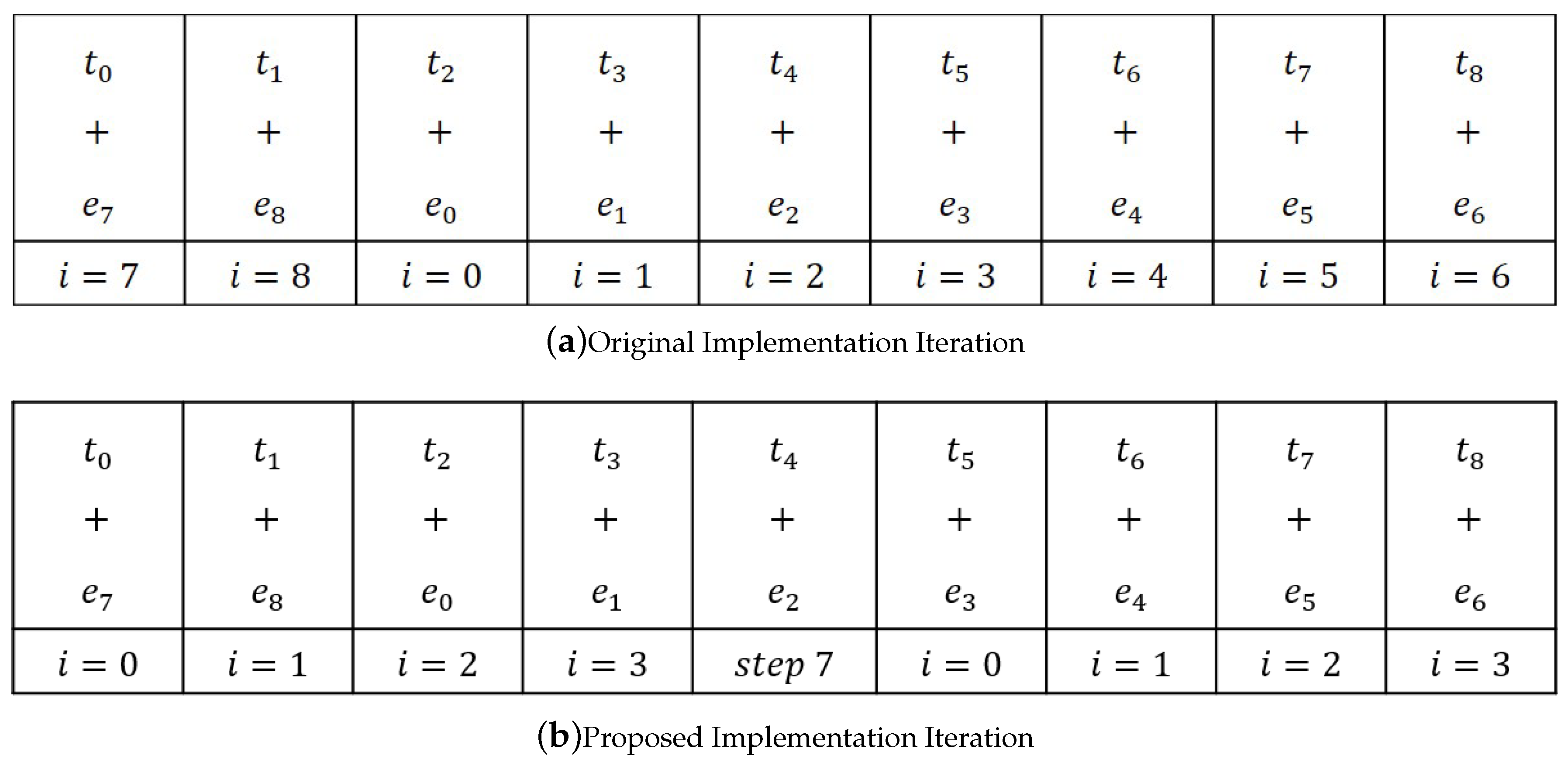
3.1.1. Proposed Method
The idea behind the attack is that the correlation between power consumption traces obtained when performing the same operations is higher than the power consumption trace obtained when performing different operations. Let the power trace obtained during the addition operation be taken as a reference trace
R. Let
O be the subtraces of the power consumption trace in Algorithm 2. When calculating the correlation between
R and
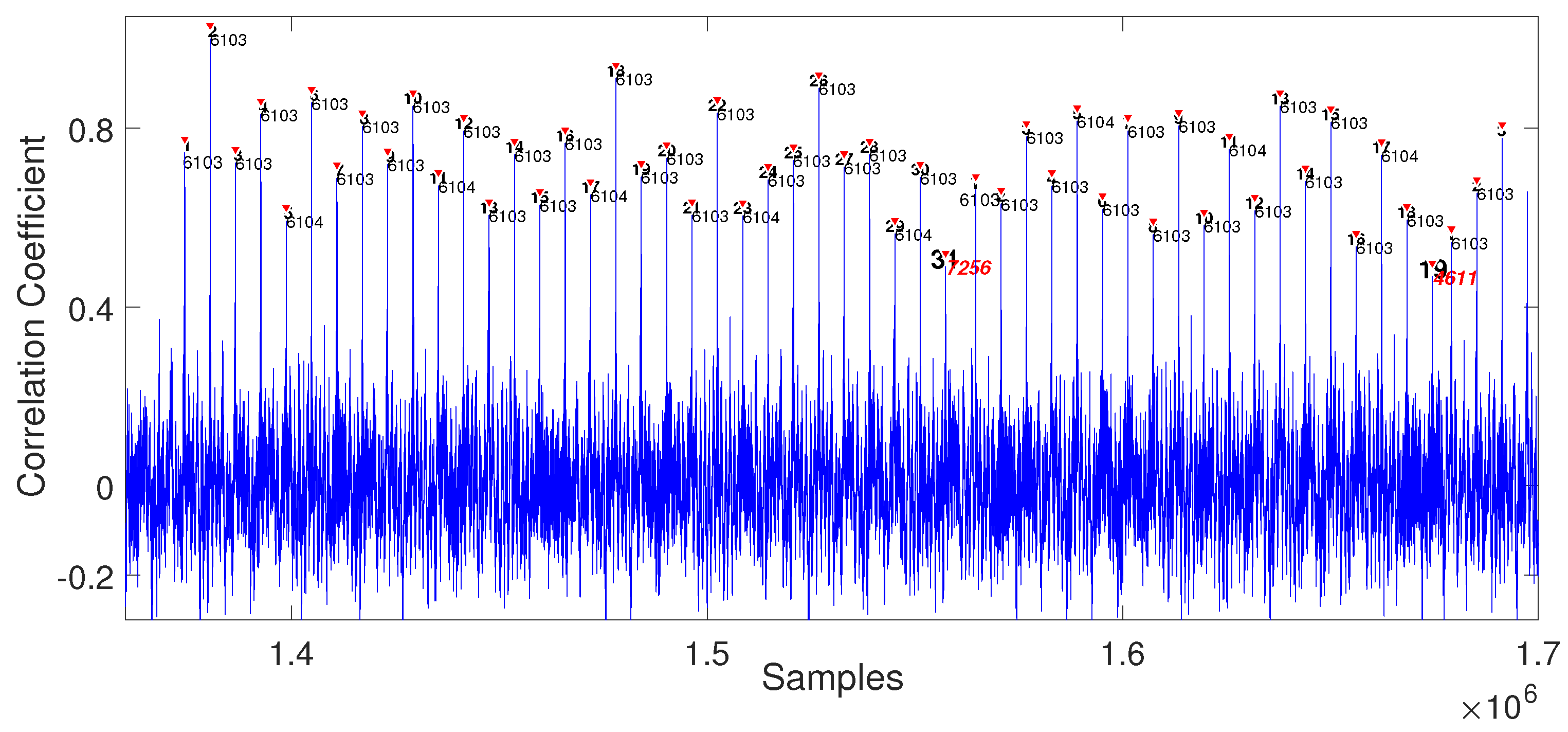
O, the correlation coefficient will be obtained when computing Algorithm 2. When plotting the gained coefficients values, then a graph appear like
Figure 1. There are peaks, called as high peak herein, which signify the affinity between
R and
O. Then, we recover the private key polynomial by calculating the distance between the high peaks.
As in Algorithm 2, the additions in steps 4 to 12 and steps 16 to 24 depend on the private value. For example, suppose and let be the smallest degree when its coefficient equals to . Then the steps 6 to 8 are repeated 6 times and steps 9 to 11 are repeated 5 times. Note that, there is a moment when the loop passes to the next loop, then the distance between high peaks is different at that moment. Thus, if the real value is x, so that the interval between th and th high peak is different from the others. Therefore, we can recover the whole value by applying the same steps for the coefficients and .
3.1.2. Experiment
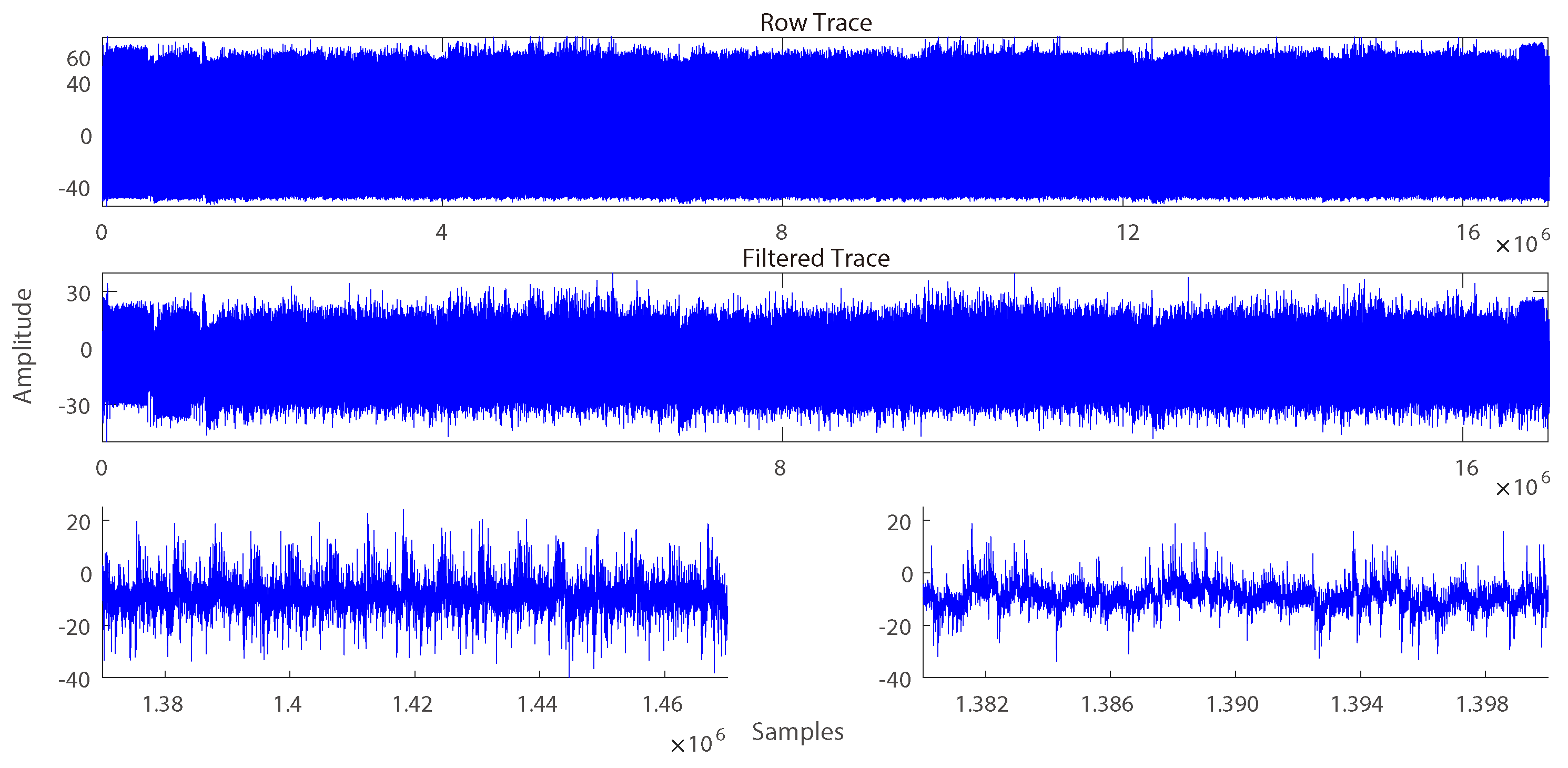
Figure 2 is a full trace of the NTRU Open Source porting on an KLA-SCARF AVR, captured in Lecroy HDO6104A oscilloscope with 250 M sampling rate [
12,
31]. The parameters for the experiment are
N =
,
=
,
=
,
=
and the private key is as follows.
We choose these values as we considered them to be suitable in the experimental environment. The first 16 entries of b represent , the next 16 values represent and the rest of the values represent .
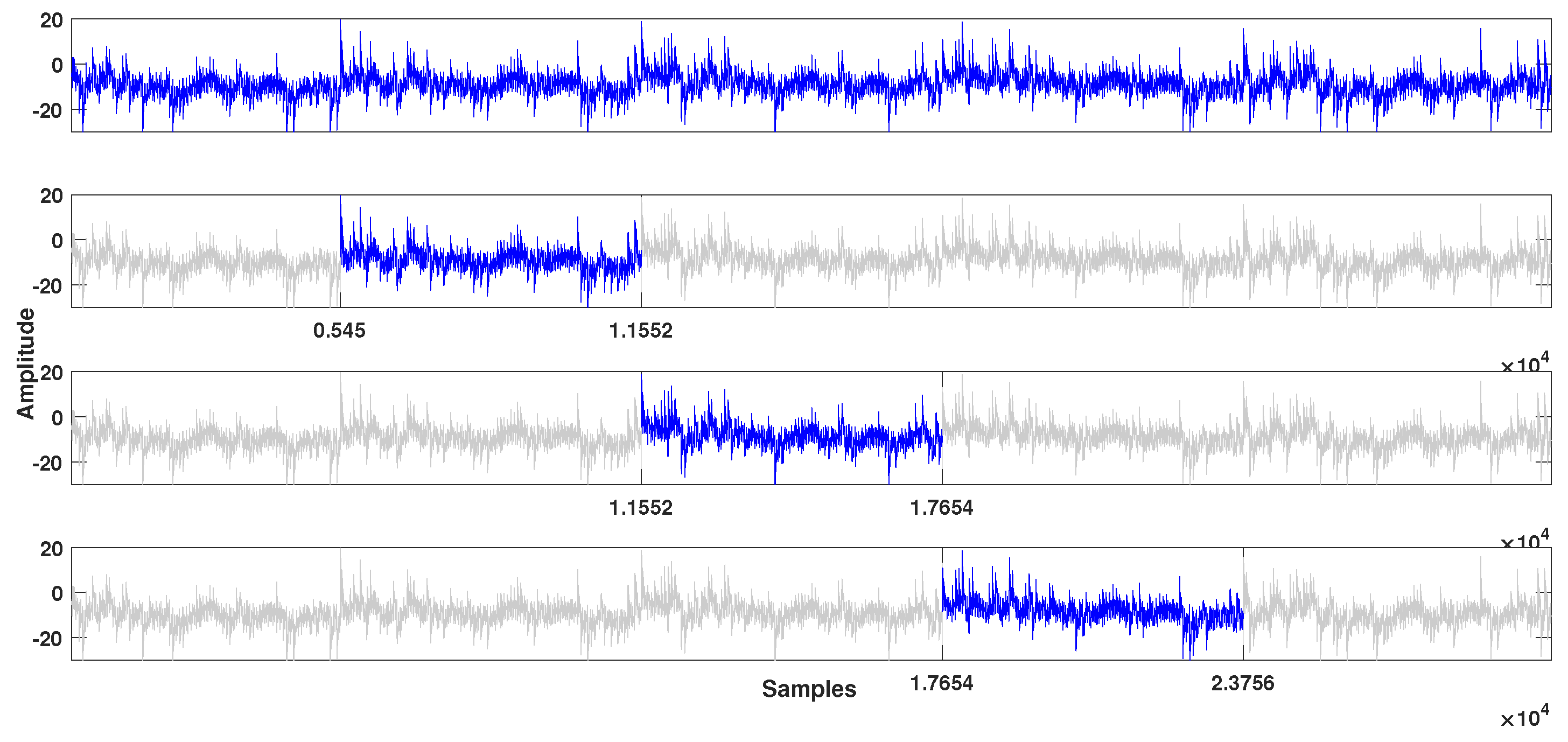
The first step for analysis is discovering a reference trace
R by SPA (
Figure 3). The length of
R is calculated by dividing the full trace length by the total number of operations. After that, the correlation coefficient can be calculated from the trace using the reference.
Figure 1 is a part of the result containing the high peaks and the following intervals. There are two indices tagged on each peak, one represents an order of the high peak and the other is a distance between the previous high peak. The
th peak has different distance than others, so the first degree where coefficient is
is
. With this process, we can recover
and the private key.
3.2. NTRUEncrypt
Representing Polynomials
In the NTRUEncrypt, the polynomial is represented as the coefficients in order. For example, stored as F = . Before the polynomial multiplication of cipher-text and private key, there are steps to compute .
Polynomial Multiplication
The the Equation (
3) operates using the grade school multiplication. Unlike NTRU Open Source, the polynomial multiplication operates separately. These steps are described in Algorithm 3.
| Algorithm 3 Decryption in NTRUEncrypt |
- Require:
Trinary polynomial , cipher-text - Ensure:
message
- 1:
fordo - 2:
- 3:
end for - 4:
- 5:
fordo - 6:
- 7:
end for - 8:
fordo - 9:
- 10:
for do - 11:
- 12:
end for - 13:
end for - 14:
- 15:
fordo - 16:
- 17:
end for - 18:
returnm
|
3.2.1. Proposed Method
The proposed method exploits the power consumption of steps 1 to 3 and steps 5 to 13 in Algorithm 3 to recover the trinary polynomial F. When F get recovered, the private key polynomial f is computed by , where p is a public value. The relative order of coefficients is discovered by analyzing the steps 1 to 3 operation. Because F is a trinary polynomial, a constant value p is multiplied by three values . Since most of the processor apply 2’s complement method to express negative value, a hamming weight of is bigger than others. Thus we can observe the high peaks in the power consumption trace when the is operated. Note that, the proposed analysis depends on the operation of the processor. Thus, if the processor uses another method to represent negative value, the proposed analysis should consider such circumstances.
The next step, the relative orders of the coefficient are known from 5 to 13 steps which are the polynomial multiplication of cipher-text e and private key f. The power consumption when calculating the coefficient of the cipher-text and 0 will be lower than other calculation processes. This portion where the power consumption is low is referred to as low peak. Therefore, after finding the relative position from to , and combining this result with the information of s then F is completed recovered. Finally, we can get f by computing .
3.2.2. Experiment
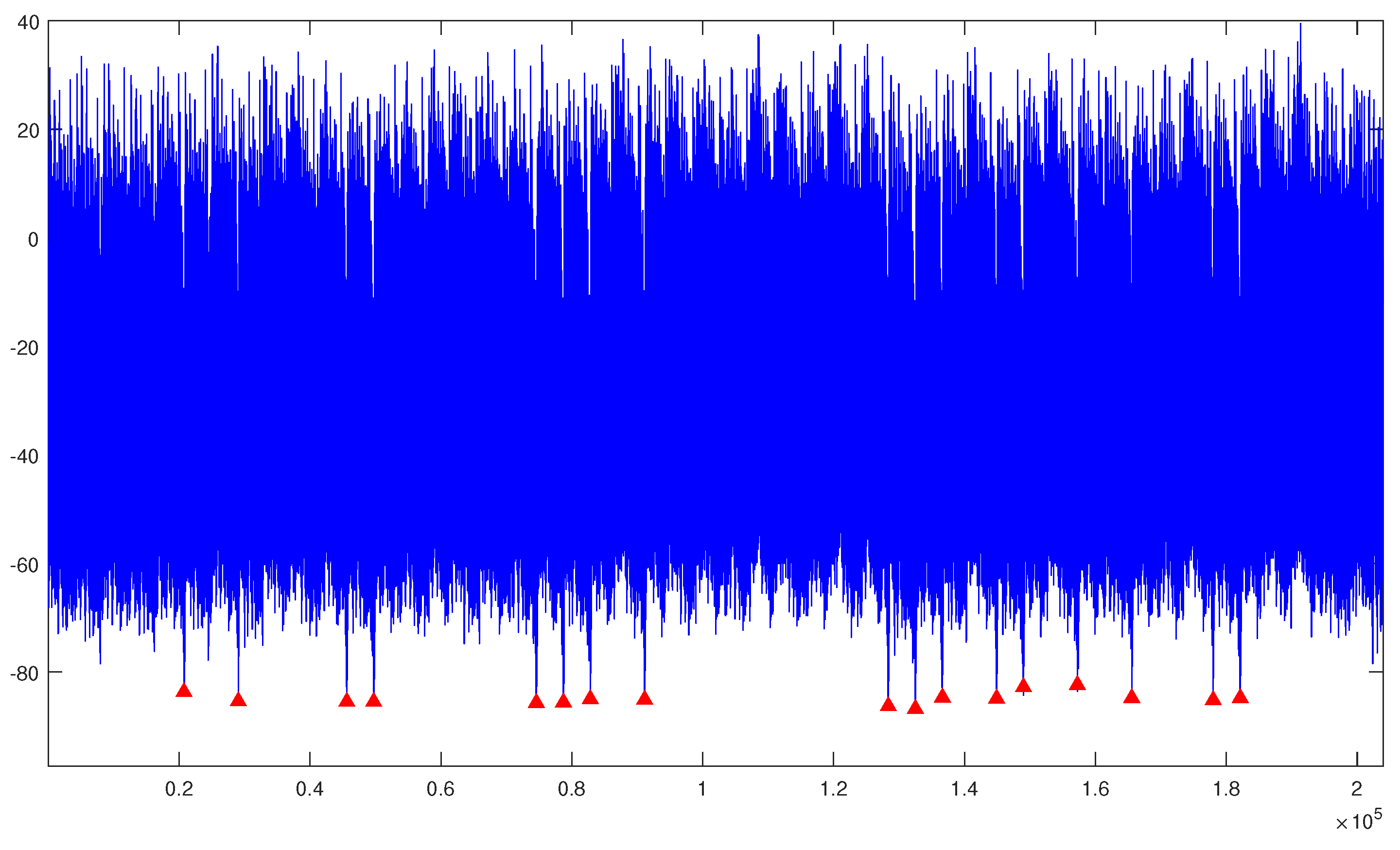
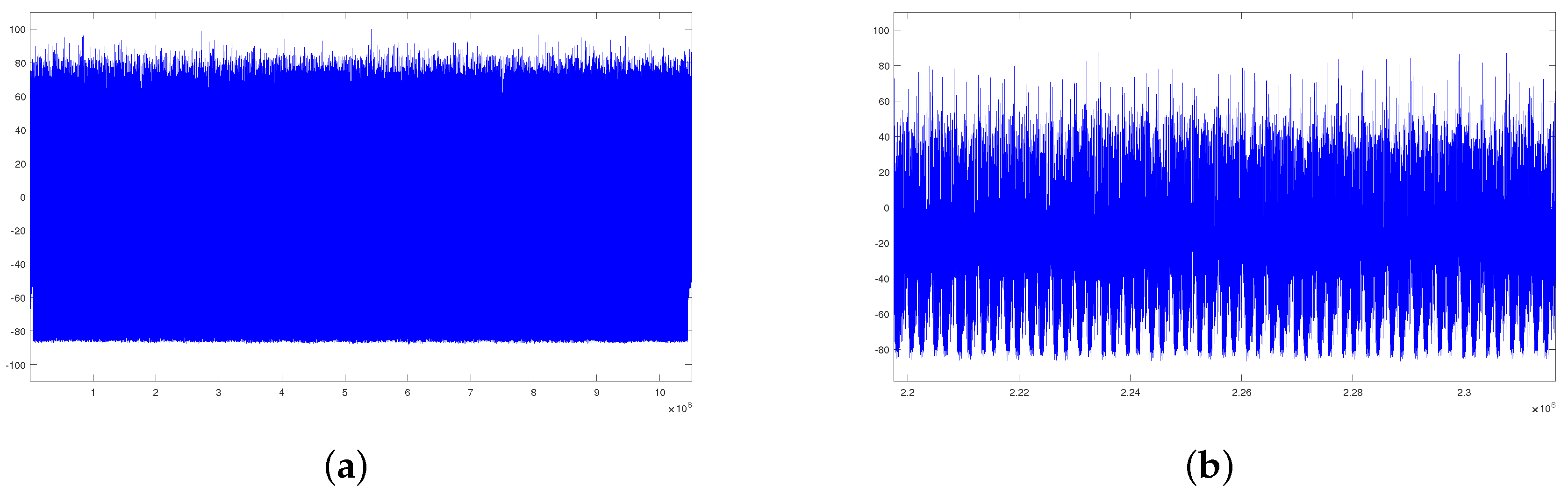
Figure 4a is a full trace of the NTRUEncrypt porting on the KLA-SCARF AVR and is captured with a Lecroy HDO6104A oscilloscope at a 250 M sampling rate [
12,
31]. The parameters for the experiment are
N =
,
p =
,
q =
, and a private key is as follows.
The p and q follow the proposed parameter but N is smaller than the standard because of the experimental environment.
Figure 4c depicts the power consumption of steps 1 to 3 in Algorithm 3. As mentioned above, the high peaks represent the moment when
p is multiplied by
. Also, in the
Figure 4c, there are the low peaks related to the coefficient
and
. Thus the relative orders of
and others can be recovered by analyzing
Figure 4c.
The following process is to recover the coefficients
. For each coefficient of the cipher-text, there are
N multiplications with the private key. During the
N operations, the operation of the private key
appears in the same order, so the low peaks appear regularly on the whole power trace (
Figure 4a). To recover the degree, we should classify a set of multiplications by SPA among the trace. The multiplication between cipher-text and private key occurs after computing
, and the total recovered number of multiplications is
. To reduce the noise, one can average multiple power consumption trace.
Figure 5 illustrates the average of 10 traces.
Figure 4b is an enlarged plot of four low peaks to deduce that peaks are identified. Lastly, with the three coefficients recovered from the analysis, the private key
f is obtained.