1. Introduction
Nowadays, life expectancy significantly differs from that of 25 years ago. Research of the World Health Organization [
1] indicates that over the last 25 years, life expectancy in Poland lengthened six years. Moreover, the research of Kontis et al. shows that with high probability, by the year 2030, life expectancy could lengthen for another three years [
2]. However, men’s and women’s life expectancy differs in most cases in favor of women, e.g., in Poland by eight years. Such a situation causes a significant part of the elderly population to live alone. In some cases, such people have mobility difficulties, symptoms of dementia or other health problems, but still would prefer to live in their homes and surroundings. Therefore, there is a need for information systems that could facilitate such a life without compromising people’s safety. This can be done by means of an autonomous system, which monitors people’s position and their vital signs and is able to distinguish different activities and situations, reacts accordingly to the degree of danger and alarms, e.g., appropriate services or caregivers.
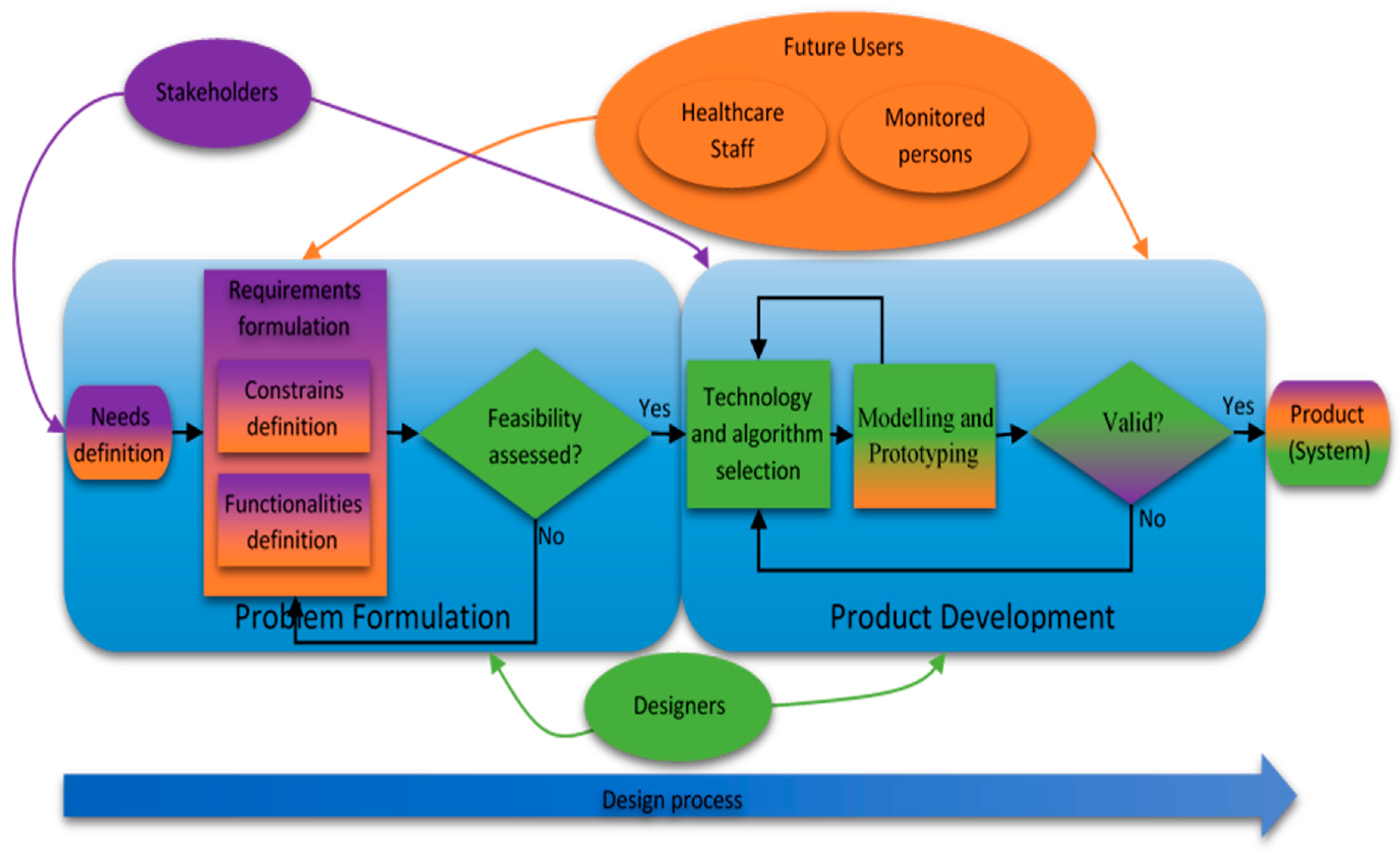
The aim of this paper is to propose an Internet of Things (IoT)-based healthcare information system intended for indoor and outdoor use where a methodological approach to the design process is in focus. A distinguishing feature of this approach is that the contracting authority’s and future users’ perspectives and needs are included in most stages of the design process. Moreover, in the proposed approach, the designer from the beginning has to think comprehensively to merge human and technical constraints and requirements. The proposed user-driven Design Methodology (DM) is used to solve the problems of the real-life scenario of supporting seniors living alone, especially those with limited abilities to manage their daily lives. The conducted design process results in a system proposal that meets the required assumptions.
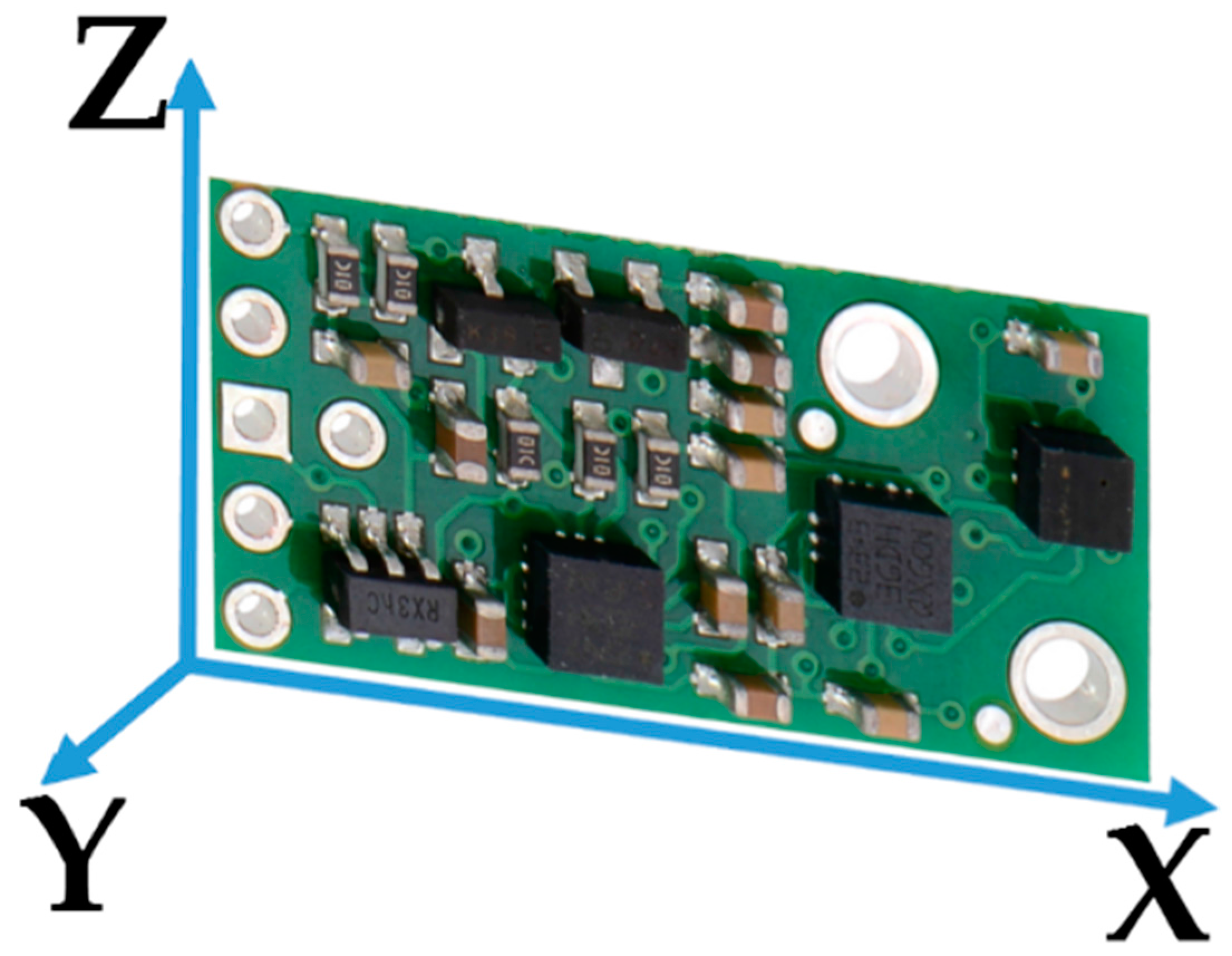
The conducted case studies verified that the designed system, consisting of the Inertial Measurement Unit (IMU) with a built-in three-axis accelerometer, gyroscope, magnetometer and altimeter, together with Wi-Fi and heart rate modules and applying thresholding, Pedestrian Dead Reckoning (PDR) and decision trees algorithms, works properly in the tested real environment. The achieved person’s localization accuracy within one meter fits the required four room-zone level localization accuracy in an apartment environment. The developed fall detection algorithm proved effectiveness of 98%, and other required activities were recognized with 95% compliance. Moreover, the proposed behavior classification algorithm is able to distinguish normal behaviors from suspicious and dangerous ones, working properly in almost 100% of cases.
2. Survey of Related Work
The Design Methodology (DM) of a product or system has been of interest to many researchers. Already in 1991, A. McKnight proposed a definition of DM as “… a sequence of activities required to get from one stage of the design process to another” [
3].
R. Prasad and H. Kobayashi, in order to improve hardware description language design productivity, propose the nine-step multi-methodology design process model consisting of system specification, system partitioning, modeling or adaptation, component simulation, system binding, system simulation, pre-synthesis modification, logic synthesis and logic simulation [
4]. Their solution enables the diminution of the time required for modeling and simulation-related activities by 31% and 16%, respectively, compared to the classical hardware description language-based design.
The design methodology proposed by S. A. Mengel et al. contains the three stages: requirements, specification and implementation [
5]. At the requirements stage, the designers should focus on the key concept of the problem and propose a graph with the structure of the system. At the specification stage, they refine the proposed graph into the content flowchart, which should be easily implementable into the considered system in the last design stage. Moreover, after each DM stage, the validation and verification should be carried out to ensure that the key concepts would have been met.
To improve the productivity of the complex electronics system design, H. Eskelinen proposes to apply two questionnaires to the traditional four-stage electronics system design, which are: system design, electronics design, mechanical design and design for manufacturing [
6]. Those questionnaires are used to form requirements lists of electronic system components.
F. Wang and M. J. Hannafin state that the design-based research should be “pragmatic, grounded, interactive, iterative, flexible, integrative, and contextual” [
7]. Based on this assumption they form nine principles of the design-based research: support design with research from the outset; set practical goals for theory development and develop an initial plan; conduct the research in representative real-world settings; collaborate closely with participants; implement research methods systematically and purposefully; analyze data immediately, continuously and retrospectively; refine designs continually; document contextual influences with design principles; and validate the generalizability of the design.
A. Saini and P. Yammiyavar chose the user as the focal point of the design of m-health system [
8]. They use the object-oriented system design methodology, typical for software development, and then study interactions and relationships between the system requirements and the components of the user’s needs and goals. User-driven design becomes especially useful in health applications, where the stakeholders and different kinds of users may express different requirements and constraints.
The suggested DM approach of M. Ahmad considers five design aspects: the target field failure rate, expected use environment, expected environment use conditions, expected enclosure use conditions and expected product internal conditions [
9]. The method is applicable to estimate the target’s lifetime in the Internet of Things (IoT). It uses the probabilistic approach for estimating hardware reliability with given uncertain use conditions while considering overall system reliability.
Emerging technologies create new opportunities, and the robust monitoring of persons or things, alike, in indoor and outdoor environments, becomes of interest to many scientific and industrial applications, where one of the most important is the healthcare domain. However, the conducted survey reveals that design methodologies, despite their efficacy, have not yet been of great interest to designers in the field of healthcare information systems in IoT. The emerging healthcare applications are possible due to the development in Micro-Electro-Mechanical Systems (MEMS), which enable the integration of various devices like actuators, sensor nodes or mobiles [
10,
11].
It is preferable that the devices used for monitoring purposes operate wirelessly [
12], forming Wireless Sensor Networks (WSNs), which constitute the substantial part of IoT [
13]. WSNs are widely used in healthcare applications due to their advantages and diversity. In [
14], C. Rotariu and V. Manta propose WSN for monitoring patients’ heart rate and oxygen saturation. W. Y. Chung, S. C. Lee and S. H. Toh embed Electrocardiography (ECG) and blood pressure sensors into a cellular phone [
15]. The wireless body area network is an example of a suitable approach to the IoT healthcare paradigm. S. -L. Tan, J. Garcia-Guzman and F. Villa-Lopez use Wi-Fi technology to transmit data about the blood pressure, heart rate, body temperature and oxygen saturation to the base station [
16]. J. Wannenburg and R. Malekianc apply Bluetooth technology and a smartphone for monitoring the patient’s health parameters [
17].
In IoT healthcare applications, one of the most frequently-monitored issues is the localization of patient or equipment. For this purpose, depending on the application, various methods and technologies are used. Numerous approaches are based on Received Signal Strength (RSS) [
18]. M. Shchekotov uses RSS measurements from several known Wi-Fi access points assuring the localization accuracy at a four room-zone level on a single floor of a building. In order to localize an asset in the healthcare environment, the authors of [
19] use the existing infrastructure of the Wireless Local Area Network (WLAN), extended just with six access point beacons. Based on Wi-Fi RSS measurements and small Wi-Fi tags, they are able to localize the assets like wheelchairs, beds, etc., with an accuracy of about 2 m in the hospital clinic environment of 63 m × 46 m size. W. H. Chen et al. use RFID RSS measurements of the reference and monitored tags to estimate the cost function consisting of the disparity and similarity of RSS between monitored and reference tags [
20]. In this way, the three optimal reference tags are found, and the position of the monitored tag is determined as the center of mass of the triangle, which they form. The average localization error of a patient or asset in a 5 m × 10 m healthcare environment is about 0.74 m. F. Palumbo et al. propose the stigmergy approach combined with RSS measurements of Bluetooth Low Energy (BLE) [
21]. Their approach results in a localization error of less than 1.8 m in 75% cases in a 6 m × 6 m furnished office. J. Wyffels et al. propose a healthcare dedicated indoor localization algorithm based on BLE RSS measurements and least squares-support vector machine, resulting at the four room-zone level localization accuracy [
22]. The authors of [
23] focus on patients’ localization, tracking and monitoring in the nursing institute environment. They use RSS measurements of the ZigBee standard and a particle filter. As a result, they achieved an average localization error of less than 2 m in 80% of cases.
Different algorithms and methods can be used to improve the localization accuracy. In [
24], the authors use the Radio Frequency Identification (RFID) fingerprints method and the artificial neural network, which enables a 3D localization accuracy of about 70 cm within a room-sized environment. A different approach to the indoor localization problem is shown in [
25] where the authors used fingerprints of Wi-Fi and barometric pressure to localize a target with the floor accuracy of a six-floor building. Their Barometer-aided Wi-Fi (BarFi) floor localization approach detects the target’s floor correctly in 96.3% of cases.
An interesting solution of the Pedestrian Dead Reckoning (PDR) algorithm is presented by Kang and Han in [
26]. They use data from off-the-shelf three-axis gyroscope, magnetometer and accelerometer smartphone sensors in an in-building environment. The proposed method ensures the mean localization accuracy of 1.35 m with the maximum localization error of 1.62 m. The authors of [
27] use data from the accelerometer, magnetometer and gyroscope to recognize a person’s posture and to detect the tumbling of the person [
28].
Information about the position of a monitored person or equipment is valuable not only for localization, but also it could be used for patient’s behavior recognition. This is especially useful while monitoring the elderly living alone or a person at the first stages of dementia. For this purpose, L. Wang et al. apply coin-sized RFID readers on both hands of a patient and one accelerometer on the patient’s waist [
29]. Using this set, along with a passive RFID tag, they are able to recognize 25 different activities of the supervised person. H. Martin et al. are able to recognize a person’s activities and body position by means of Google Nexus S embedded sensors like the magnetometer, gyroscope, accelerometer, light and proximity sensors and a fuzzy classifier [
30].
Most of the mentioned monitoring solutions have the common drawback of being dedicated just to indoor environment applications. In the case of an outdoor healthcare monitoring purpose, most of the enable solutions apply the Global Positioning System (GPS) [
31], which in the in-city environment provides localization accuracy of about 6 m. Ch. Wu et al. combine GPS data with gyroscope and accelerometer data using the dead reckoning algorithm, which results in an improvement of the in-city localization accuracy up to 4 m [
32]. For outdoor behavior recognition, L. Sun et al. apply the mobile embedded accelerometer and Support Vector Machine (SVM)-based classifier, to recognize activities like bicycling, running and walking [
33].
The mentioned monitoring solutions are dedicated exclusively to just one, an indoor or outdoor, environment. A multi-environment localization solution was proposed by Millner et al. in [
34]. The authors, using the Symeo local positioning radar, are able to localize animals with an accuracy of 0.5 m in 75% of cases in both indoor and outdoor environments; however, the major constraint of the system is its applicability in an environment with low multipath distortions. J. Gonzalez et al. combine Ultra-Wide Band (UWB) and GPS technologies and a particle filter to localize a robot in the indoor and outdoor environments with a localization accuracy of about 2 m [
35].
However, these multi-environmental solutions, in turn, are difficult to implement in healthcare applications inter alia due to the size of the devices used. A localization system relatively easily implemented in healthcare, both indoor and outdoor environments, is presented in [
36]. It is based on RSS measurements in a ZigBee network [
37]. The major drawback of this solution is a significant number of needed reference nodes with known positions and the maximum distance from the reference node of 15 m, which considerably reduces the applicability of the system from the large outdoor environment.
A promising approach to the multi-environmental patient monitoring system is proposed by R. Tabish et al. [
38]. They propose a monitoring system of the patient’s temperature and ECG based on 3G/Wi-Fi IPv6 over Low Power Wireless Personal Area Networks (6LoWPAN). While the monitored person occurs in an indoor environment, the system uses local Wi-Fi for sensors’ data transfer, and in the case of the outdoor environment, the 3G/4G technology is applied. The drawback of this solution is a limited number of monitored vital parameters.
3. Problem Statement and Main Contributions
The number of related publications is enormous, and this review provides only examples of solutions, which in the authors’ opinion give a map of the development fields. However, the review of related works indicates that although a variety of solutions is used in the IoT healthcare-monitoring domain for indoor and outdoor environments, a methodological approach to the design process is still missing; where design is understood as “scientific principles, technical information and imagination in the definition of a structure, machine or system to perform pre-specified functions with the maximum economy and efficiency” [
39]. Furthermore, using a multi-environmental information system for behavior recognition and classification requires improvement and development.
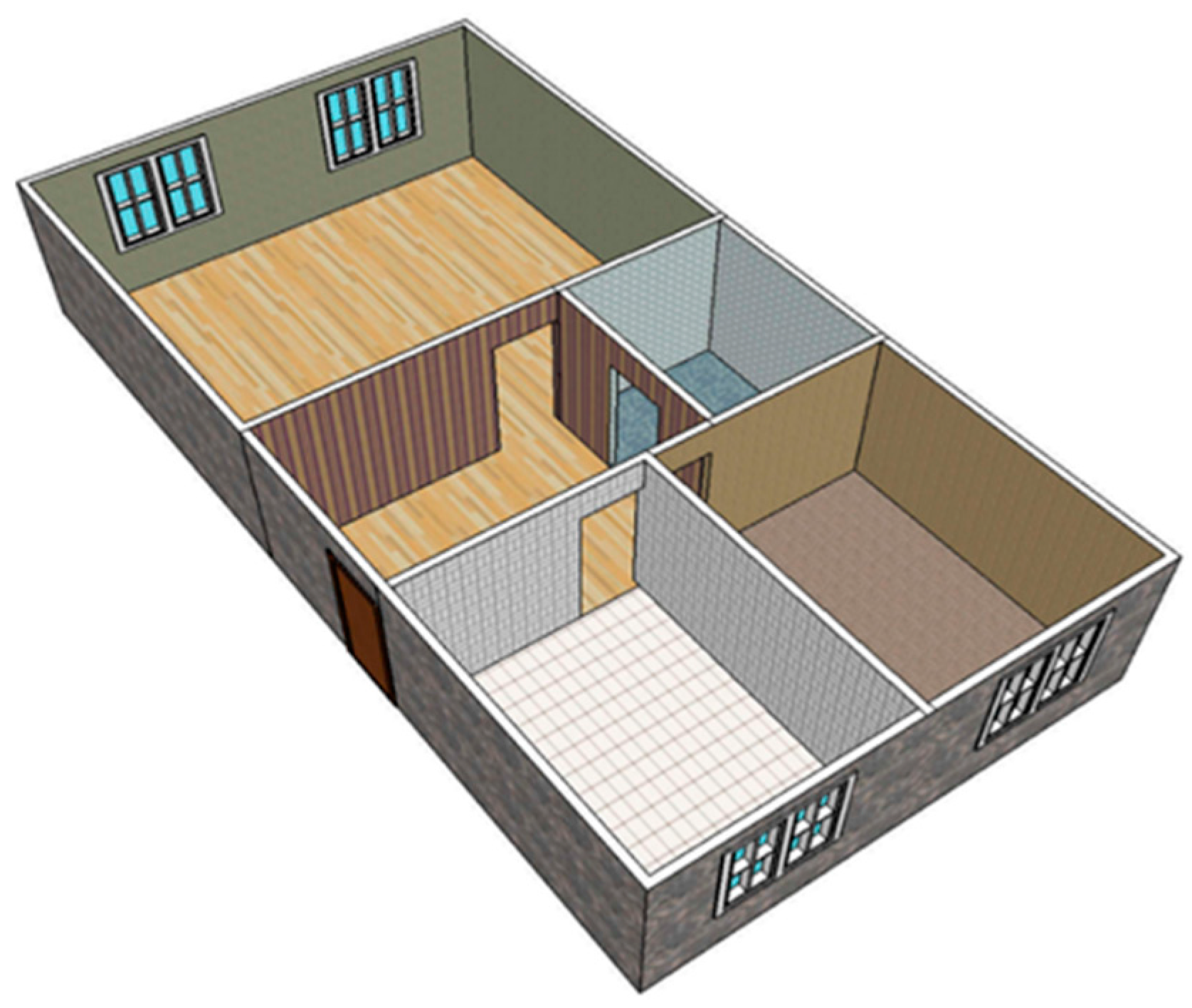
To fill the gap in the methodological approach to the design of a comprehensive information system for healthcare applications, the objective of this paper is to propose a systematic design procedure, which can enhance the development of healthcare appliances. Apart from technical requirements, the procedure considers multifarious constraints, including the lifetime, energy efficiency, usage comfort and even the price. The case study of the design process is an IoT-based system for monitoring people and things multi-environmentally capable inter alia of behavior recognition and diagnosis. The system is dedicated to support and localize elderly people in their multi-room apartments along with a multi-story building, but even outdoors in the building’s surroundings. The system’s functionalities consist of monitoring vital signs, posture recognition, suspicious behavior detection and classification.
The development procedure approaches the design target from the perspective of the stakeholders, the authority in charge and the potential users, as the view of the system developers. The proposed design methodology is modelled and then implemented and validated on the case study of the system for multi-environmental monitoring of elderly people living alone. The system has been implemented and validated in real scenarios.
5. Case Study: Problem Formulation
The proposed design methodology is implemented and validated on the case study of a healthcare system for multi-environmental monitoring of elderly people living alone in the Silesia region in Poland. The designed system can be used not only to support and localize the elderly people in their multi-room apartments located in multi-story buildings, but even outdoors in the buildings’ neighborhood.
5.1. Needs Definition
The growing number of elderly people is a global problem, and many local authorities, also of the Polish region Silesia, acknowledge its importance and are working on it. The general needs and targets introduced by the stakeholders and future users represented by elderly people and their families have considered possibilities to support elderly people, especially those of limited mobility, living alone or patients with the first symptoms of dementia. The support can be yielded by means of an autonomous system monitoring the target’s position, their vital signs and able to recognize different activities and even classify human behavior.
5.2. Requirements Formulation
The functionalities, desired by the stakeholders and future users, consist of the localization of the monitored person in his or her apartment with up to four room-zone level accuracy, but also within a multi-story building, where the apartment is located, with a floor level accuracy. Furthermore, the person’s positioning in the building’s outdoor neighborhood with an accuracy of at least 10 m is desired. Moreover, the system, in all of these surroundings, should be able to monitor the target’s vital signs and even detect the person’s fall.
To recognize the required behavioral changes of the monitored person, in addition to the localization and fall detection, there is a need to distinguish the person’s postures, like sitting, standing, walking or lying. It is even requested that the system should classify if a current behavior is normal, suspicious or dangerous for the monitored person and, in the case of unusual occurrences, notify the people responsible for care. In the instance of conduct that is classified as suspicious or dangerous, a subsidiary part should provide supplementary information about some vital signs.
According to a division of constraints into the two categories of general and particular, the reliability, size and comfort of device-wearing and even a maximum price of 200 EUR for the complete system are classified as the general constraints of the system. Moreover, the demands that the system should be easy to install, operate and maintain and even assure the subject’s privacy are also the general constraints of the system. The operational time of at least one week, necessary for many reasons, can be categorized as particular. The localization accuracy in the considered environments along with the reliabilities of activities and fall recognition are particular constraints. Furthermore, real-time secure non-invasive measurements are crucial particular constraints of the vital signs’ monitoring. The high validity of the behavior classification is also considered as a particular constraint. Both general and itemized functionalities, along with the particular requirements, are summarized in
Table 1. The table consists of possible technologies and algorithms, and these, which fulfill the stated requirements, are bolded.
5.3. Feasibility Assessment
The needs, functionalities and constraints presented by both stakeholders and future users need to be scrutinized by the designer. After the comprehensive analysis, the general needs of a system supporting elderly people living alone with limited mobility or with the first signs of dementia are assessed as technically accomplishable and feasible. Furthermore, the performed research proved that the related functionalities and constraints concerning the working environments, activity recognition, vital signs’ monitoring and behavior classification are also technically feasible at a moderate level of technical and algorithmic complexity. Nevertheless, the trade-off between the desired low price and the system’s reliability and the further constraints has been acknowledged as challenging.
7. Results Discussion
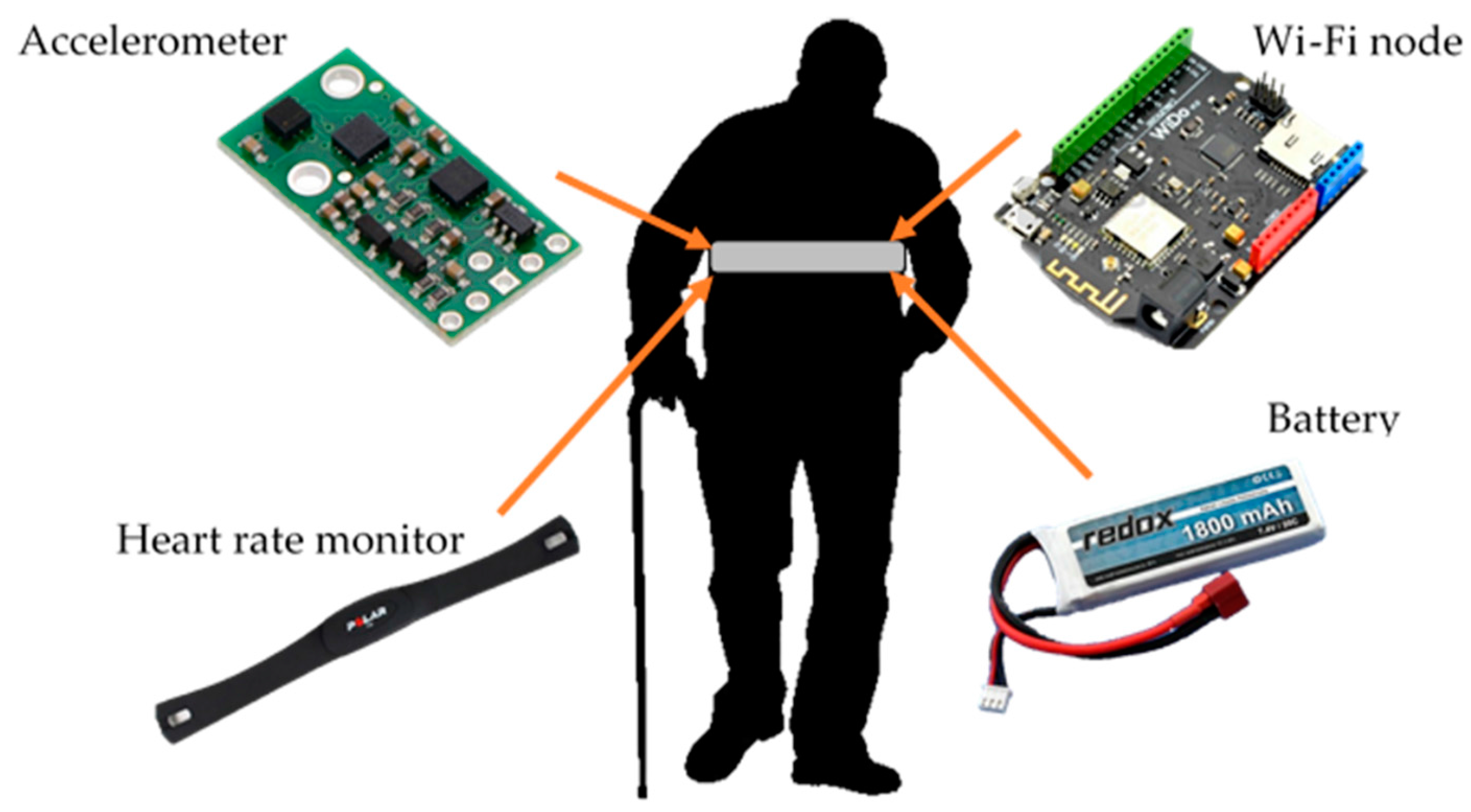
The system design process was conducted using the proposed DM, and based on validation results, the stakeholders and future users approved the solution and continued the project towards implementation and commercialization. The applied DM resulted in the system consisting of hardware and software components, shown in
Table 1, suitable to realize required functionalities and fulfilling general constraints.
The presented system validation concerned the crucial requirements of stakeholders and future users such as a four room-zones level localization accuracy, fall detection, activity recognition and classification of normal, suspicious and dangerous situations.
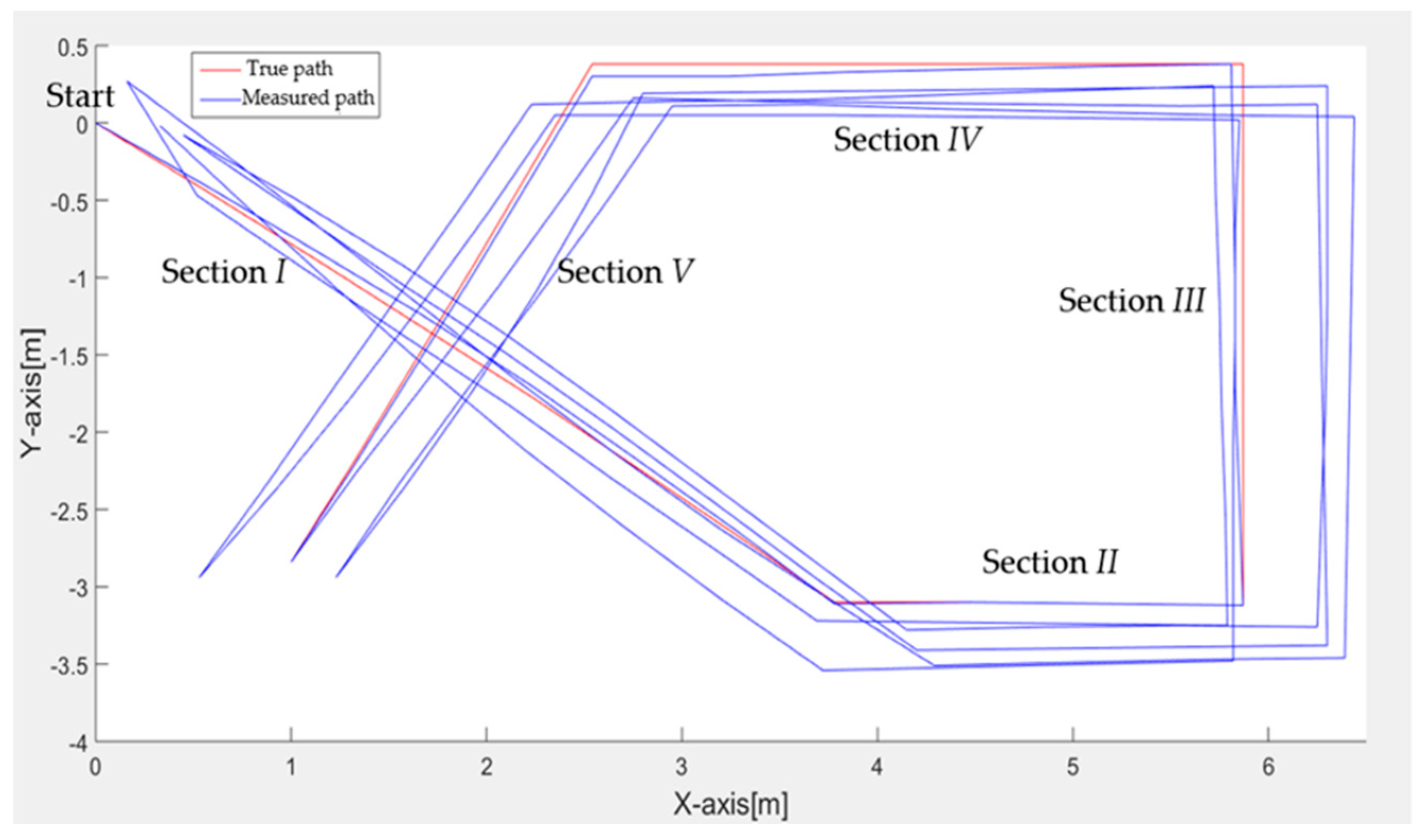
The 1500-step test proved that the proposed step detection method, based on data gathered with the three-axial accelerometer and magnetometer, together with the signal magnitude vector and the pedestrian dead reckoning algorithm, shows a high robustness of 98%. The direction estimation test gave 1.33° of the mean uncertainty of the angular walking direction with a standard deviation of 1.15° and maximal error of 3°. Such high accuracy and sensitivity confirm the usefulness of the method for indoor location monitoring.
However, the further investigation indicated that small natural motions of the body during walking caused up to a 1-m error in the position estimation. Therefore, the 6° threshold filter was applied, which resulted in the reduction of uncertainty in position estimation by up to 40 cm.
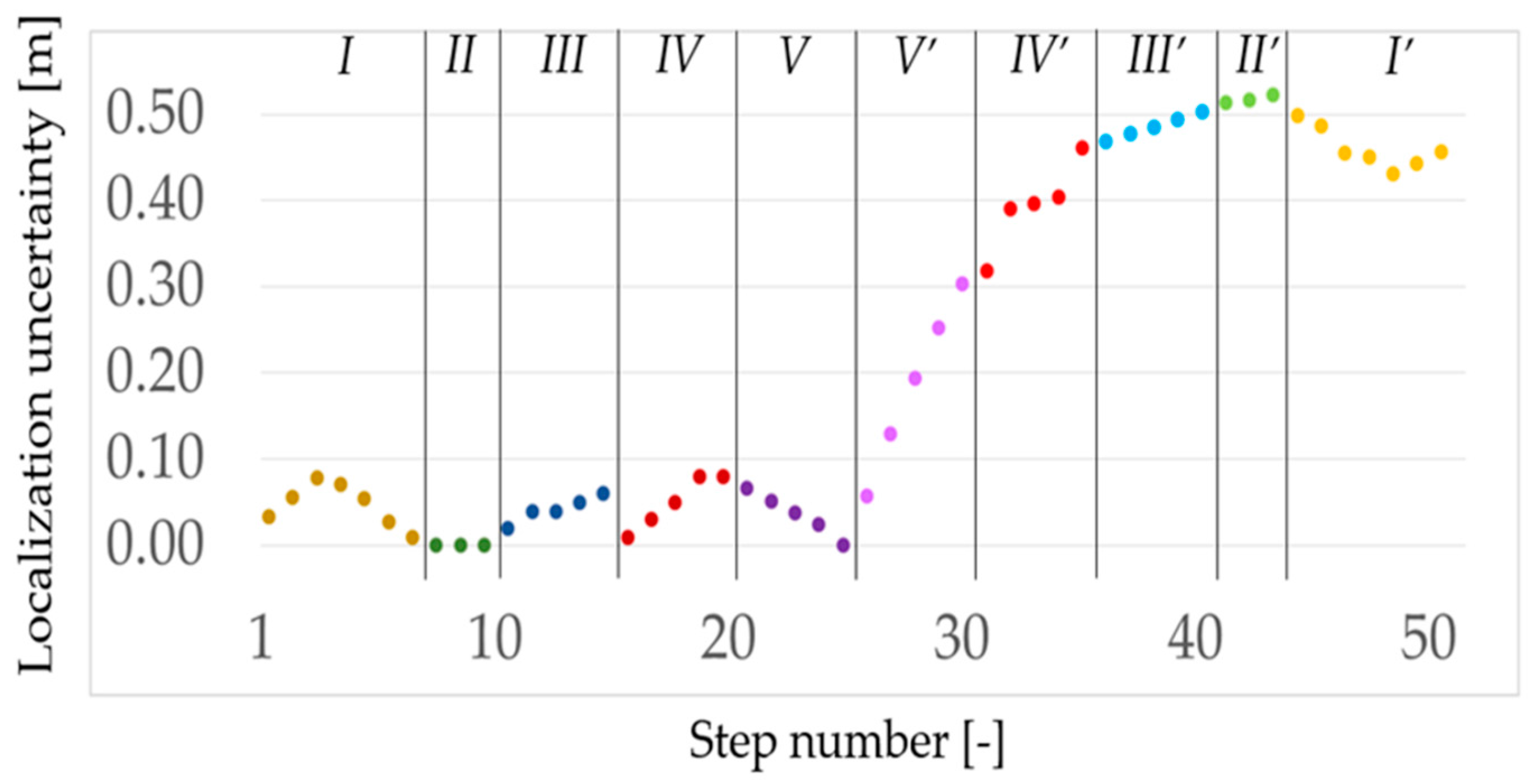
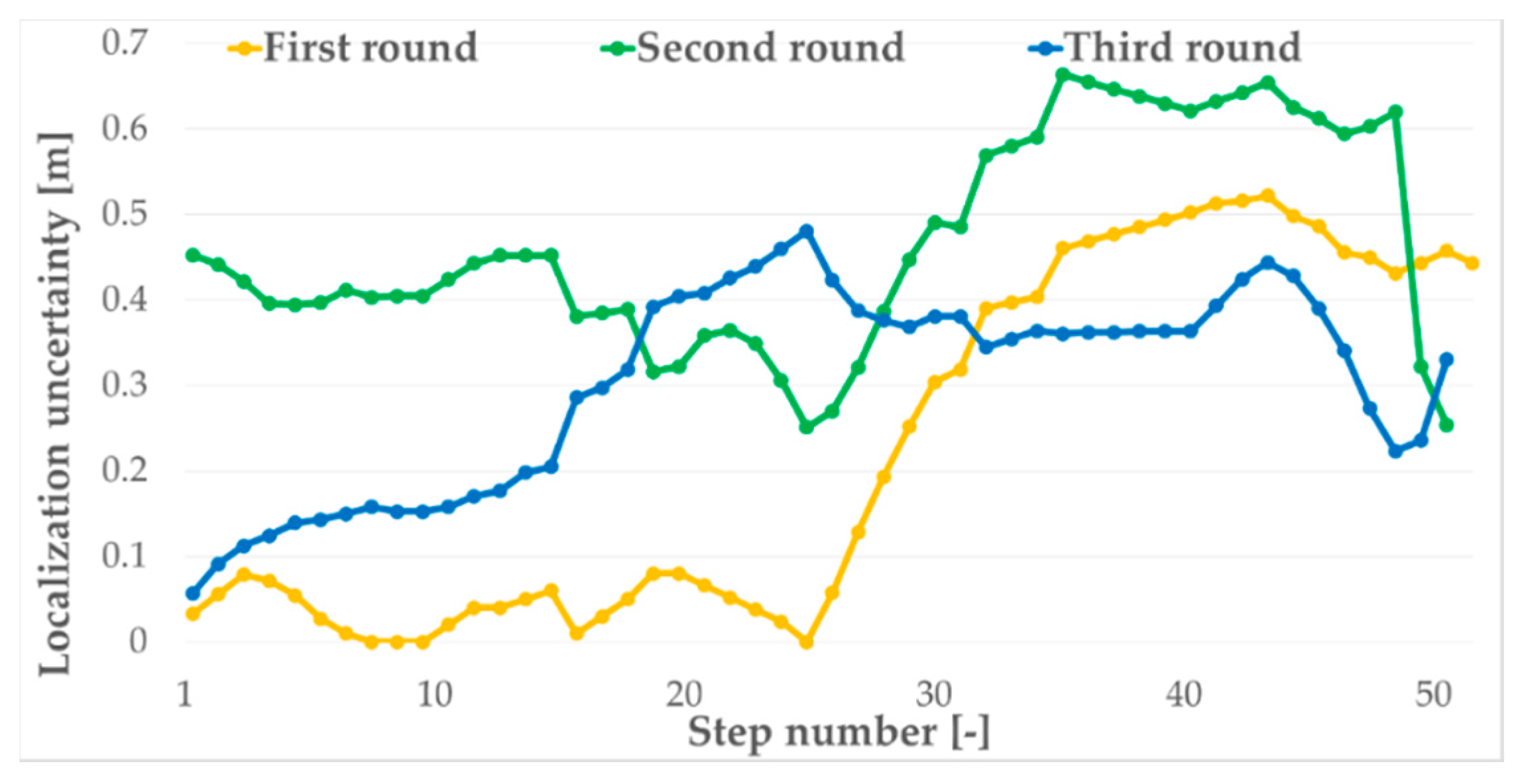
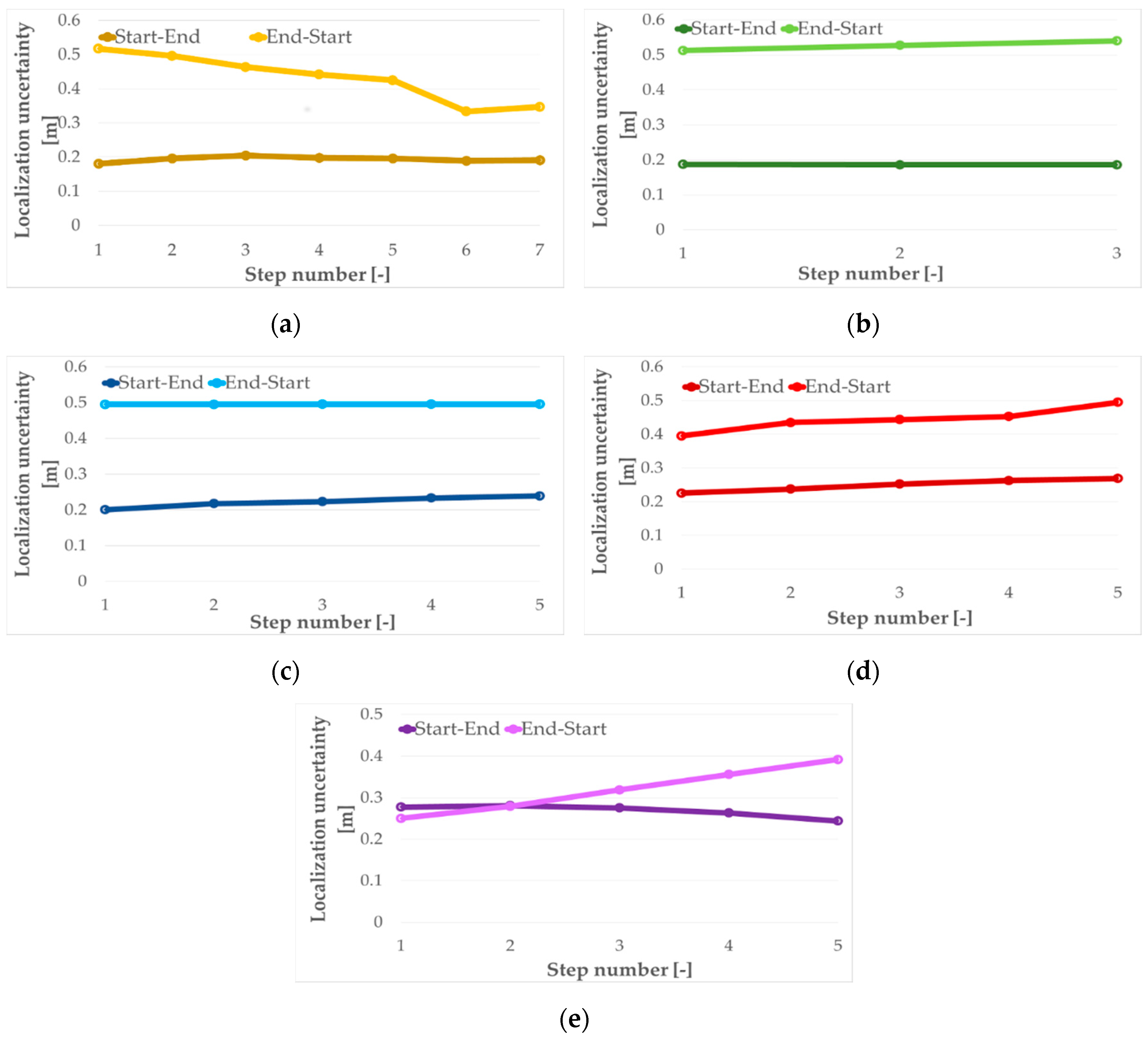
For the walk test path consisting of five sections performed back and forth and repeated three times, the mean localization uncertainty was 33 cm with a standard deviation of 18 cm where the maximal localization error was 66 cm. The same test’s results indicated that for one round of the walk from the start to end points, the mean localization uncertainty was just 4 cm with a standard deviation of 2 cm. However, for a walk in reverse order, the mean value and standard deviation increased up to 40 cm and 12 cm, respectively. The detailed analysis of the test data resulted in the mean localization uncertainties for each round of 22 cm, 46 cm and 30 cm, with standard deviations of 20 cm, 12 cm and 11 cm for the first, second and third round, respectively. Moreover, average localization uncertainties for the forward direction are almost the same and equal about 21 cm, and the same uncertainty for the back direction is about double and equal to almost 40 cm. This means that the proposed localization algorithm has a small localization uncertainty, and the most distortive movements are turns. It seems that the turns are the cause of the increasing localization uncertainty. The test results verified that the designed method is sufficient for the four room-zone level accuracy requirement.
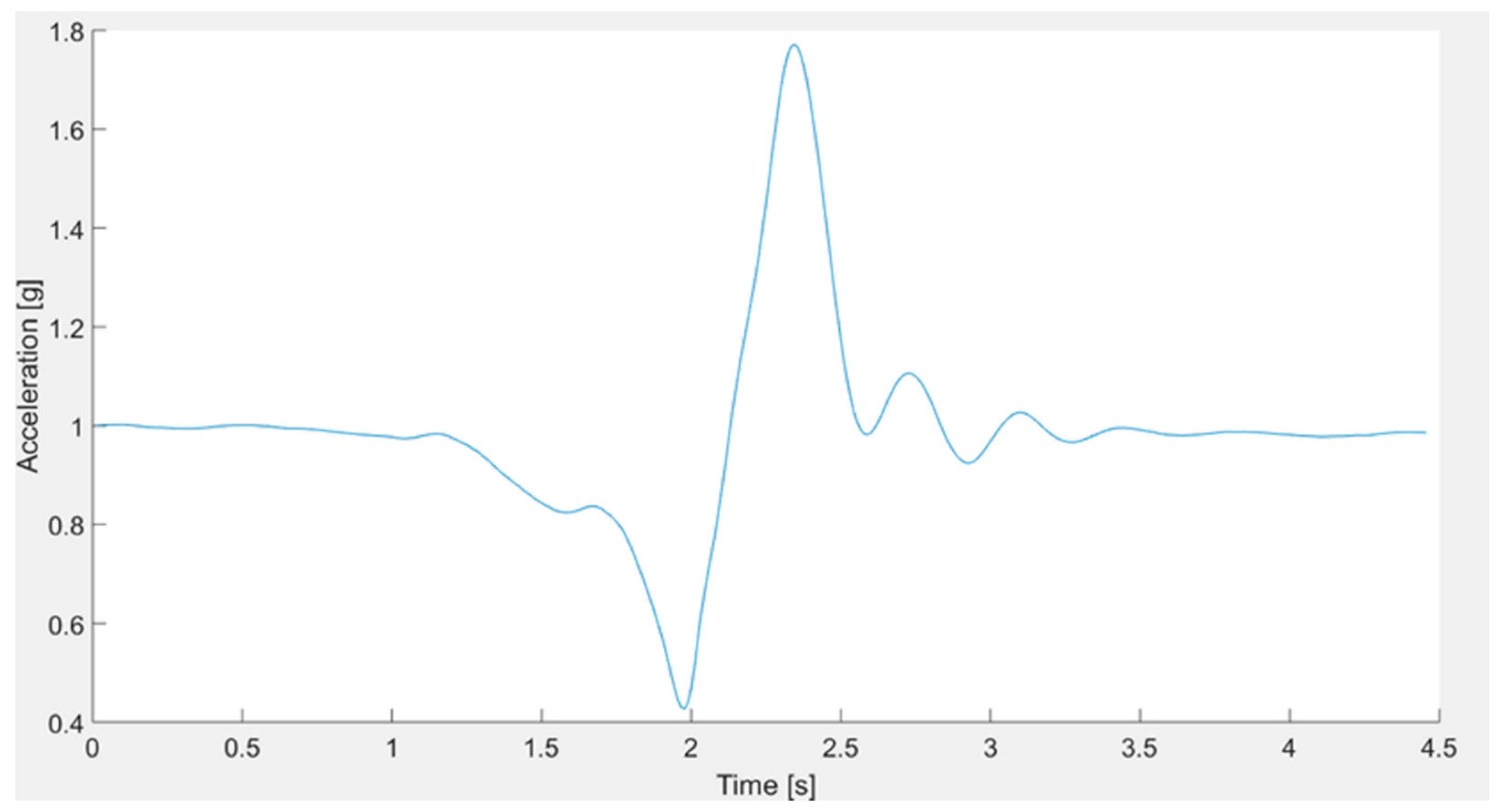
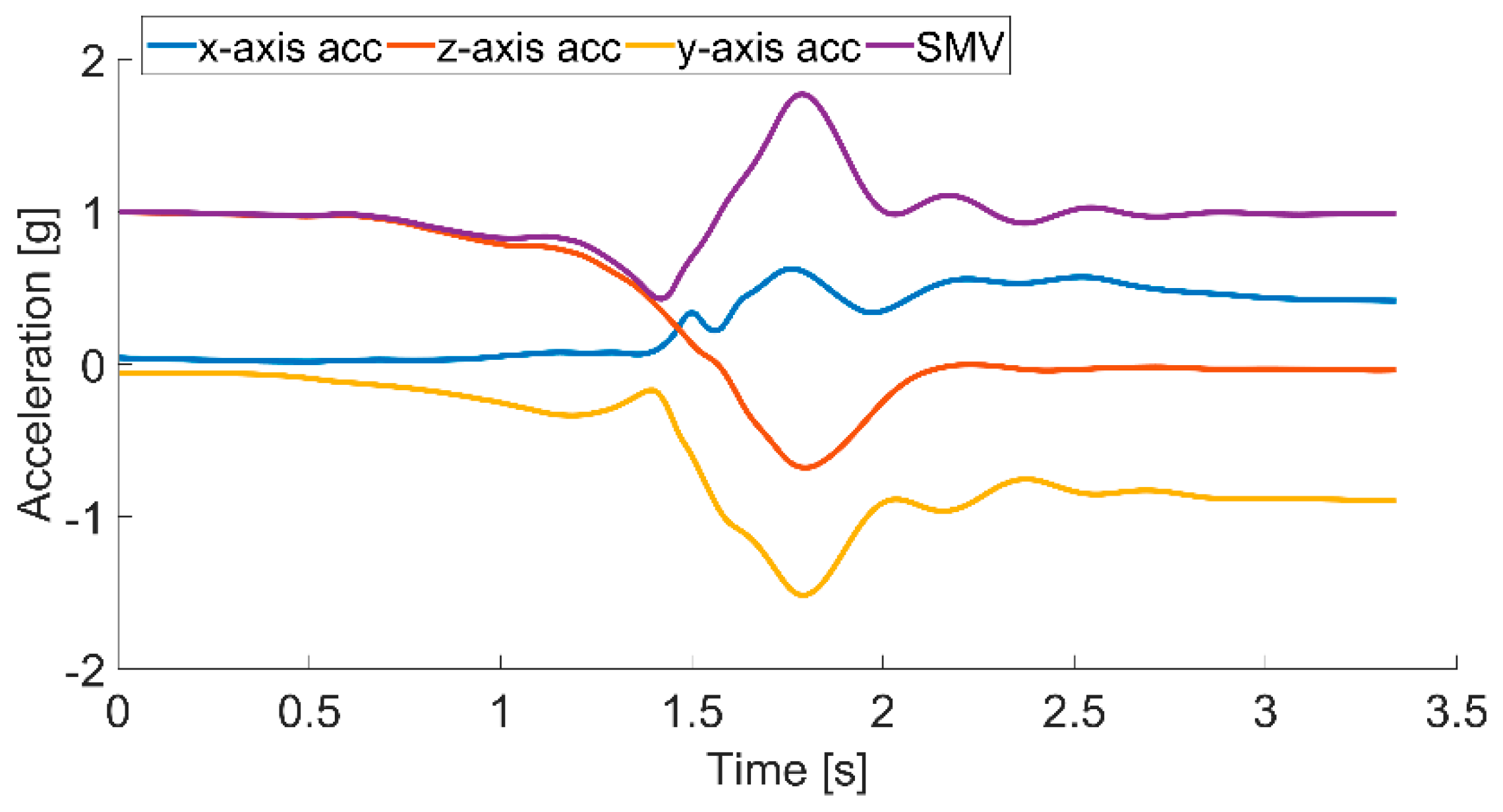
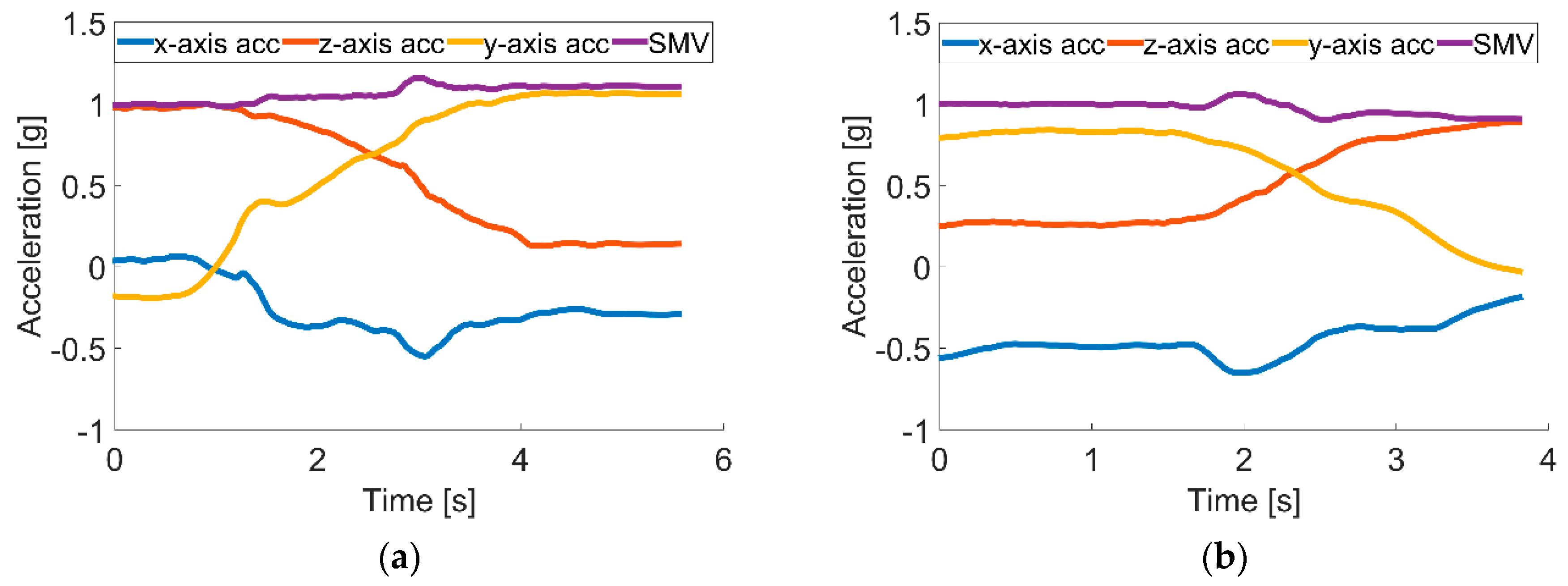
Analysis of test results of forward fall accelerations in the x-, y- and z-axes and SMV, showing the characteristic peaks concerning the beginning of the fall and the contact with the floor, was applied to define the signal thresholds used to recognize the fall. Moreover, the acceleration change in the z-axis, which the gravity force influences the most, indicating the lying position of the monitored person, is used for the fall confirmation. The performed tests proved that the designed method of fall detection is valid in 98% of cases.
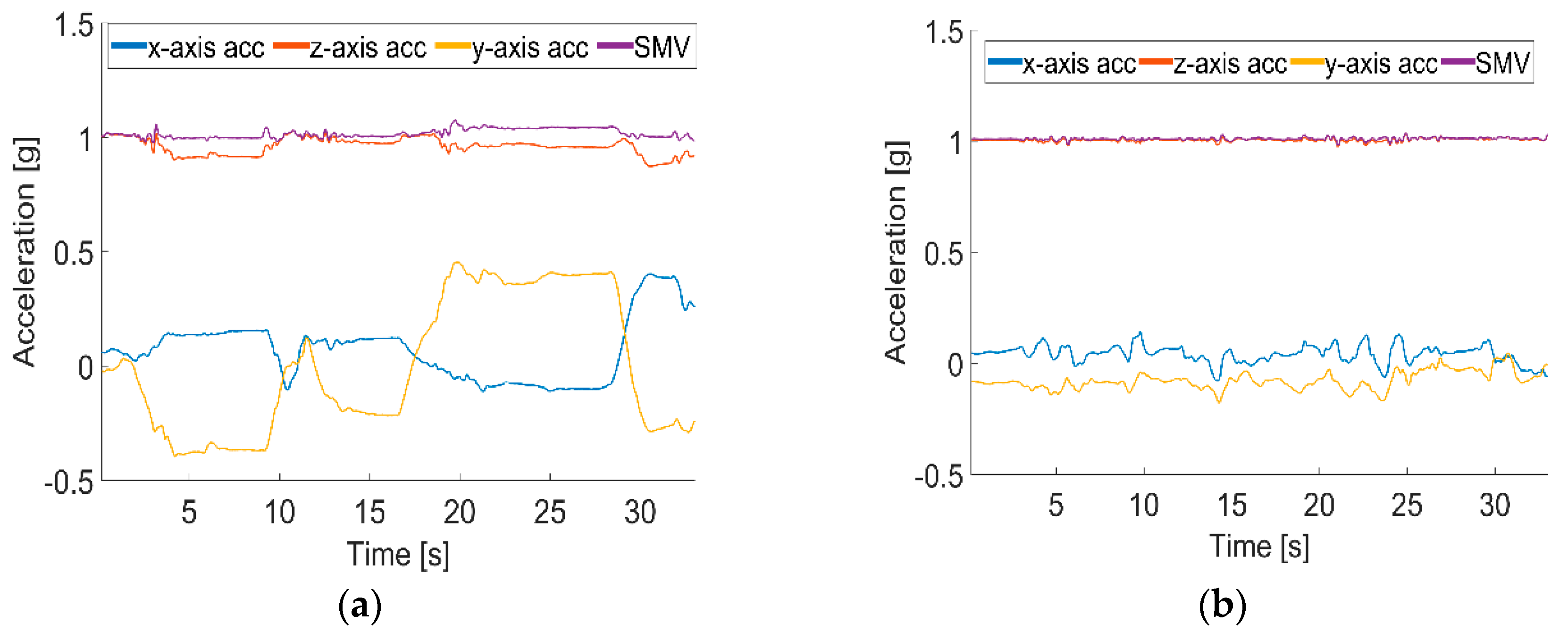
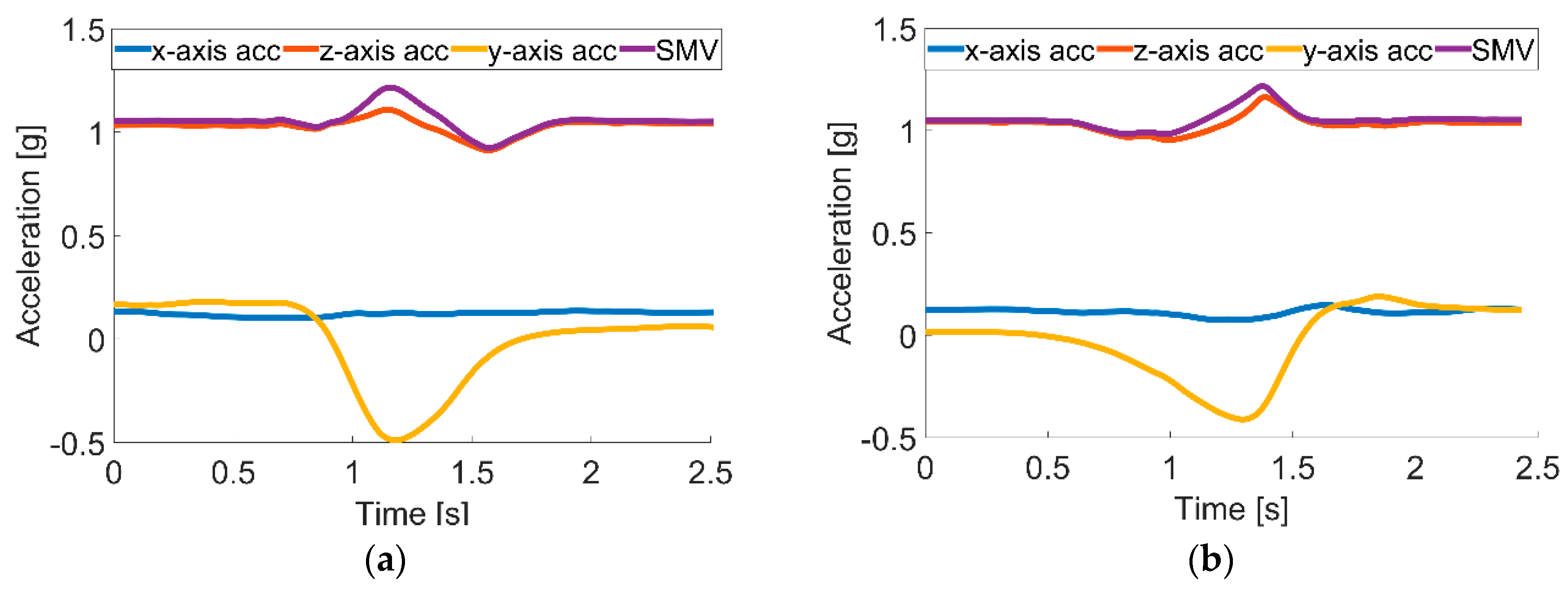
The data gathered during standing and sitting activities indicated that the observed differences in accelerations in the
x-,
y- and
z-axes and SMV are not sufficient to distinguish between these two activities. However, possible identification of getting up and sitting down activities can be used to recognize standing and sitting activities. The beginning of the getting up activity causes the acceleration in the
z-axis; hence, SMV changes quickly, and at the end of the activity both acceleration in the
z-axis and SMV gently stabilize. In turn, the start of the sitting down activity causes the mild change in acceleration in the
z-axis, and at the end of the activity, both acceleration in the
z-axis and SMV change quickly. Based on appropriate thresholds, the identification for both of these changes allows one to distinguish between those two activities. Similar analysis can be used to distinguish between lying down and rising activities. When lying down, due to an orientation change of the accelerometer causing a shift of the axis that the gravity force influences the most, the acceleration in the
y-axis rapidly decreases, and acceleration of the
z-axis sharply increases; while when rising, the acceleration curves of the
y- and
z-axes behave conversely; the
y-axis rapidly increases; and acceleration of the
z-axis sharply decreases. These phenomena are used to distinguish these two activities. The proposed activity recognition method was validated based on tests consisting of 350 falls, 200 lying down, 200 standing up, 400 sitting down and 200 walks, and the results are summarized in
Table 3. The overall validity of the system activity recognition was 95.5%, where 2.5% of activities were recognized incorrectly and 2.0% not detected at all.
The activity categorization in class of behavior as normal, suspicious or dangerous is based on the analysis of five components: time of day, section of apartment, zone of activity, form of activity and duration of activity. The classification procedure is grounded on the comparison of current measures with the existing behavior database. The behavior database was created from regular three-day observation of three volunteers’ activities. From six evaluated machine learning techniques, the decision trees II, KNN I and KNN II showed the highest classification validity of 94.8%, 96.0% and 95.8%, respectively. The conducted optimization of the three best methods indicated that only the tuned decision trees II increased classification accuracy up to 99.1%. The confusion matrix for the tuned decision tree indicates that only 0.2% of the tested dangerous behaviors were classified as normal, which can be treated as a critical mistake, and 0.3% of them were classified as suspicious, which is less critical since the suspicious behavior should be verified anyway. The chosen behavior classification technique of highest validity was verified with a set of 25 normal, 7 suspicious and 18 dangerous behaviors of random timeframes, and as a result, 100% of them were classified correctly.
8. Conclusions and Future Work
Due to the lengthening of life expectancy, society is aging, and more and more people live to an older age. Therefore, it is highly important to assure life quality and safety. Existing and emerging technologies can provide tools that can support elderly people in their everyday life, making it easy and safe. This paper concerns the design methodology of such tools especially for indoor and outdoor localization, health monitoring, fall detection and behavior recognition and classification.
The authors propose the design methodology for the IoT-based home care information system intended for indoor and outdoor environment use. The presented DM approaches the home care problem not only from the designer’s perspective, but also considering the contracting authority’s and potential users’ requirements, which means that apart from the technical requirements, the design procedure considers the multifarious constraints, including the lifetime, energy issue, usage comfort and even the price.
The proposed DM was verified with a case study of real-life scenarios where there is a need for supporting elderly people, especially those of limited mobility living alone. The desire stated by the stakeholders and future users required the system for identifying people’s position and their vital signs, but also to be able to recognize basic activities, especially falls, and to classify them as normal, suspicious or dangerous.
The outcome of the conducted design procedure is the system based on IMU, with a built-in three-axis accelerometer, gyroscope, magnetometer and altimeter. It is also equipped with Wi-Fi, GPS and heart rate modules. For an in-apartment localization with four room-zone level resolution, the IMU with PDR algorithm is used. For in-building localization with floor level accuracy, the BarFi algorithm based on pressure and Wi-Fi fingerprints is proposed. For an outdoor localization with an accuracy of at least ten meters, the GPS module and PDR algorithm are applied. In order to detect activities of falling, lying, standing, sitting and walking, the IMU and thresholding algorithms are used. As a method for classifying activities as normal, suspicious or dangerous, the authors developed the six-element behavior vector and used it together with a decision tree algorithm.
The validation procedure performed for the most crucial requirements of the four room-zone level in apartment localization, fall detection, activity recognition and its classification as normal, suspicious and dangerous situations proves that the system works according to the required functionalities and constraints.
The future works concern the verification step, conducted together with the stakeholders and future users, of designed modules and algorithms for a multi-story building environment and nearby outdoor environments. Another future improvement of this system could be further recognition of specific activities like teeth brushing, cooking, watching TV or taking medication. Such information would be informative for caregivers whether the monitored person skipped a meal or forgot to take a medication. Moreover, it could be also included in the behavior vector and inform caregivers about behavior changes within a given period. The other improvement of the system may concern the usefulness of additional sensors for monitoring vital signs. The lifetime extension of the device by means of energy-saving algorithms and methods is another direction for future work.