2. Related Works
Regarding UAV-assisted VANETs, a model was introduced in [
18] to estimate the probability of line-of-sight propagation in air-to-ground wireless communication across different urban environments. This model integrates building distribution, terrain, and other environmental parameters while accounting for signal attenuation, scattering, and multipath propagation. In [
19], the authors put forward an aerial-to-ground path loss model based on the probability model of LOS using UAVs. They further provided a methodology for determining the optimal height and angle of the UAV based on this model. Moreover, Ref. [
20] introduced the integration of UAV assistance to enhance the connectivity and support services in urban vehicle VANETs. By leveraging UAVs as mobile base stations, communication among vehicles can be enhanced, thereby facilitating the provision of additional services. In [
21], the authors introduced a routing approach that leverages UAVs for connectivity and traffic density perception. By employing UAVs as relay nodes, the Connected and Reliable UAV-assisted Vehicular (CRUV) network can dynamically select the most suitable routing path, thereby improving the efficiency and reliability of data transmission within vehicular self-organizing networks. Ref. [
22] introduces a methodology that leverages UAVs to provide services for highway VANETs and distributed antenna systems. Through the deployment of UAVs, the communication quality between vehicles can be enhanced, resulting in wider network coverage and stronger signal gain. Ref. [
23] introduces a traffic service solution aimed at minimizing latency in multi-tier UAV networks. By taking into account the hierarchical structure, connectivity, and data transmission demands of the UAV network, this scheme optimizes traffic routing and scheduling strategies to effectively reduce latency and ensure the provision of reliable traffic services.
There are currently two methods available to tackle the congestion traffic control problem in BSM transmission. The first approach involves regulating the BSM generation frequency. In [
24], the LIMERIC algorithm is proposed, which actively monitors the real-time congestion status of the network and dynamically adjusts the message rate according to the prevailing network conditions. This algorithm demonstrates notable improvements in system throughput and latency reduction, thereby better satisfying the communication demands of the Dedicated Short-Range Communications (DSRC) system. Ref. [
25] presents a congestion control technique that utilizes power or rate adaptation. By dynamically adjusting the transmission power or transfer rate of vehicle nodes in response to the prevailing network congestion level, this approach endeavors to optimize the utilization of network resources and mitigate congestion. In [
26], the authors propose a distributed algorithm design approach called DRCV, which leverages collaboration and information exchange among vehicle nodes to achieve efficient utilization of network resources and congestion control. The second approach to tackle congestion traffic control issues in BSM transmission involves power control, which regulates the transmission power of BSM. However, due to the influence of interference and path loss among vehicle nodes, distributed power control algorithms may experience anomalies during practical implementations [
27]. To overcome these challenges, the authors proposed an enhanced algorithm that leverages signal strength measurement and collaboration among vehicle nodes. By dynamically adjusting the transmission power of nodes, this algorithm endeavors to improve system performance and mitigate interference. Ref. [
28] presents a novel approach that involves real-time monitoring and analysis of vehicle status and the communication environment. This method enables the dynamic adjustment of communication parameters and route selection to optimize the overall communication performance. By continuously adapting to changing conditions, this approach aims to enhance the efficiency and effectiveness of communication in vehicular networks.
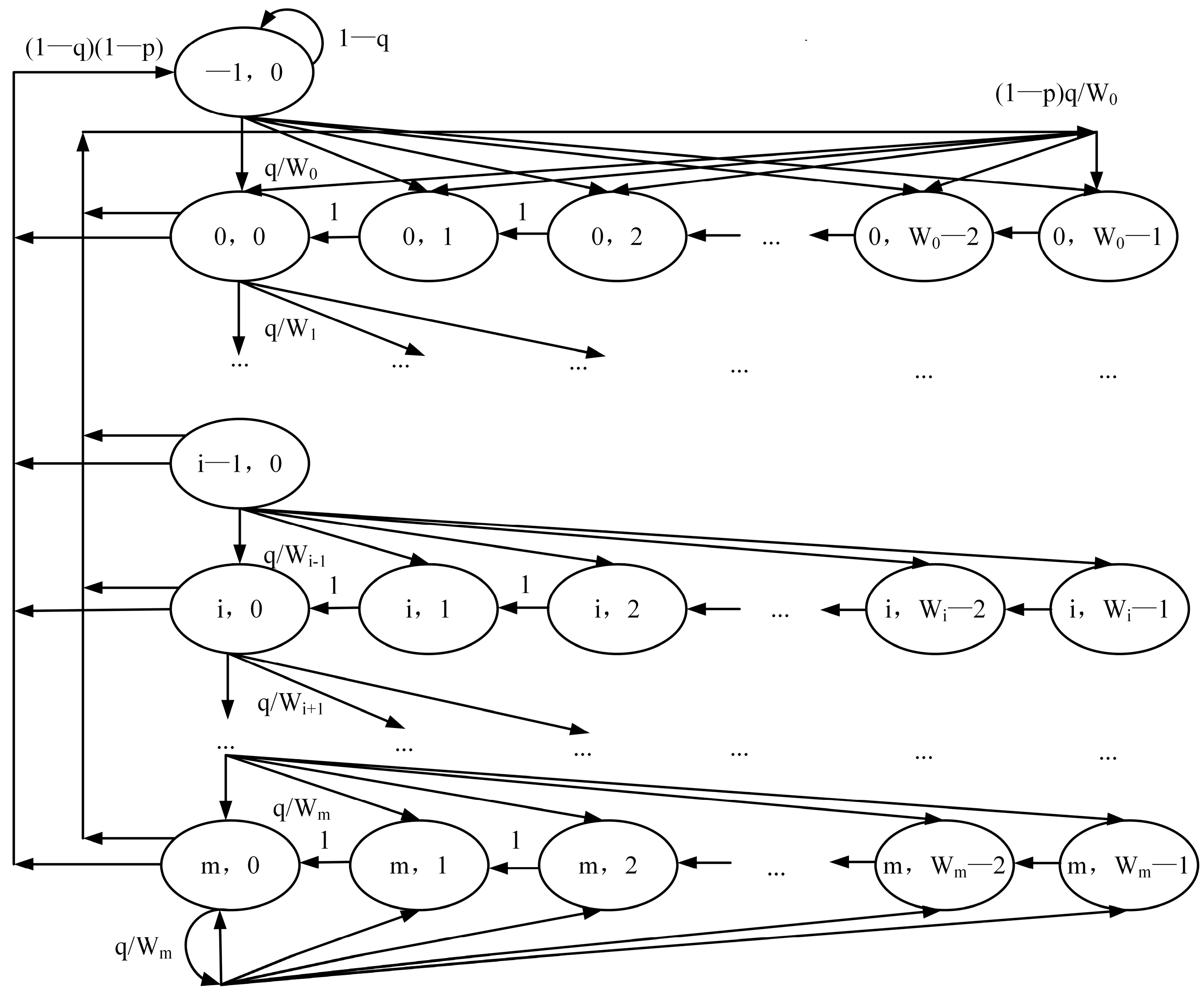
Significant progress has been made in the performance analysis of 802.11P, and Bianchi [
29] proposed the well-known Markov chain model for 802.11 DCF under saturated conditions. Using the Markov chain model, extensive research has been conducted on the performance of 802.11 DCF under saturated conditions [
30]. Shao et al. [
31] proposed an improved MAC protocol to address communication issues in VANETs. This protocol supports data transmission with multiple priorities and employs p-persistent techniques to manage media access, thereby enhancing network efficiency and performance. In [
32], the authors developed a throughput analysis model for the modified protocol and discussed how to optimize network performance through access control. By analyzing throughput and access control, this paper provides valuable insights for understanding and optimizing the performance of IEEE 802.11a networks. The application of queuing theory as a mathematical foundation for this protocol is also of great research significance. In [
33], the signal transfer function of the generalized state transition graph was derived to describe the probability distribution of the MAC layer service time, and the M/G/1/K and M/M/1/K models were used to characterize the 802.11 MAC layer. Through these improvements, the protocol’s throughput can be enhanced, latency can be reduced, and network stability and reliability can be improved. The FPMDC-MAC [
34] protocol algorithm is a notable contribution in the field of VANETs, specifically focusing on the MAC layer. This algorithm introduces a fuzzy logic-based priority assignment mechanism to ensure the efficient transmission of important information. Additionally, it incorporates a cooperative MAC protocol to facilitate communication coordination among vehicles, thereby improving data transmission efficiency. By modifying the 802.11p protocol and incorporating a priority scheme, FPMDC-MAC demonstrates significant enhancements over the existing protocol. In a related study by Wang [
35], an improvement approach for enhancing the performance of the IEEE 802.11p/bd MAC protocol is presented. This approach utilizes a 2-D Markov chain model and queuing theory to construct the model, which shares similar methodologies with our research. However, it does not incorporate priority-related schemes, which constitutes a distinct advantage of our work. In [
36], Yang proposed a hybrid MAC protocol based on priority, which combines slot allocation with a carrier sense multiple access (CSMA) mechanism. By incorporating priority assignment and dynamic slot allocation strategies, this protocol achieves fair sharing and efficient utilization of network resources among vehicles with different priorities. The paper also provided detailed deployment schemes for unmanned aerial vehicles, demonstrating that the protocol effectively improves network throughput, latency, and reliability while ensuring fair sharing and balanced resource utilization among vehicles with different priorities. In [
37], the author Linn aimed to design a conflict-free cooperative MAC protocol to address the issue of heterogeneous collisions in VANETs caused by differences in vehicle speeds, communication ranges, and data transmission requirements. The protocol utilizes a cooperation mechanism among vehicles by dividing neighboring vehicles into multiple groups, where only one vehicle in each group is allowed to transmit data, while others act as relay nodes for data forwarding. This approach enables vehicles with different speeds and communication ranges to share network resources, reducing the probabilities of heterogeneous collisions and packet loss, thus improving network performance and stability. Ref. [
38] introduced a repetition-based cooperative broadcasting scheme to enhance the reliability and efficiency of message delivery in VANETs and mitigate the adverse effects of fading on message transmission. In this scheme, vehicles within the communication range form a cooperative group and collaborate to forward broadcast messages. Cooperation is achieved through the utilization of repetition techniques, where each vehicle retransmits the received message multiple times to increase the likelihood of successful message reception by other vehicles.
In [
39], a priority-based communication scheme for V2V communication is presented, which is realized in VANETS utilizing the IEEE 802.11p standard. This scheme focuses on enhancing the QoS mechanism and incorporates priority scheduling techniques to optimize communication efficiency and minimize latency. By assigning different priorities to various types of data and vehicles, the proposed scheme aims to prioritize critical information and improve the overall performance of vehicular communication systems. Ref. [
40] presented a novel priority-based approach for emergency data dissemination in urban environments. This method is specifically designed to facilitate the swift propagation of critical information during emergency situations. By leveraging prioritization techniques, the proposed method enhances the speed and reliability of data delivery, ensuring that emergency data reach relevant entities promptly. This approach holds great potential for improving emergency response systems and enhancing the overall efficiency of urban communication networks. In [
41], the authors propose a V2V emergency data transmission scheme based on TCP protocol and priority queue technology in VANETs. This scheme utilizes stable connections and priority queue techniques to achieve fast transmission of emergency data. Moreover, it incorporates mechanisms such as traffic control and congestion control to ensure the stability and reliability of the transmission. Ref. [
42] presents a novel dynamic resource allocation algorithm for optimizing the utilization of limited UAV and spectrum resources. The proposed algorithm takes into account both the communication demands of vehicles and the current network conditions. By considering factors such as vehicle-specific communication requirements and energy constraints, the algorithm intelligently allocates UAV resources to ensure efficient resource utilization. This approach holds significant potential for enhancing the overall performance and effectiveness of UAV-assisted communication systems in scenarios with limited resources.
Our work is based on the computational model of drone-assisted vehicular networks proposed in papers [
18,
19]. Furthermore, Refs. [
20,
21,
22,
23] provide strong evidence that supports the superiority and effectiveness of drones as relay nodes in vehicular networks. Currently, there are two main approaches to address the BSM traffic congestion control problem we are interested in: one is by adjusting the generation frequency, as discussed in Refs. [
24,
25,
26] and the other is power control, as explored in Refs. [
27,
28]. Our proposed solution focuses on designing a MAC layer protocol that minimizes latency through preemptive priority and queuing theory and subsequently adjusts the generation frequency. The limitations of Refs. [
24,
25] lie in their focus on real-time congestion monitoring and optimizing network utilization efficiency without modifying the MAC layer or providing system-wide optimization. While real-time congestion monitoring is an effective method, it does not solve the fundamental problem. On the other hand, Ref. [
26] mainly emphasizes vehicle-to-vehicle communication, overlooking the auxiliary role of drones or road test units. Our research centers around designing a MAC layer protocol to adjust the 802.11P protocol in vehicular networks, incorporating key aspects such as Markov chain modeling, queuing theory, and priority design. Unlike Refs. [
29,
30,
31,
32,
33,
34,
35,
36,
37,
38,
39,
40,
41], our work comprehensively considers these three aspects, which we believe will lead to better results.
To present a comprehensive comparison, we summarize the related work, its shortcomings, and our proposed solution in
Table 1. This table will allow readers to gain a clear understanding of the existing research landscape and how our approach stands out in addressing the identified limitations.
The main objective of our research is to address the congestion traffic control problem in BSM transmission. Unlike existing research, we focus on the specific needs of vehicles for BSM transmission. Specifically, we adjust the frequency of BSM generation so that faster-moving vehicles can transmit safety information at shorter intervals, thereby meeting their higher safety standards. In addition, we improve the 802.11P-based DCF protocol by combining it with a preemptive priority M/G/1 queue mathematical model. According to this protocol as the MAC layer protocol of the link, we perform uplink data transmission and allocate resources based on delay as the primary performance indicator in resource-constrained scenarios. This approach ensures that vehicles with higher priorities receive a greater share of resources to meet their shorter transmission interval requirements and better meet the needs of safe driving. Through extensive experimental validation, we demonstrate the effectiveness of our proposed method in controlling congested traffic and improving overall system performance.
3. System Model
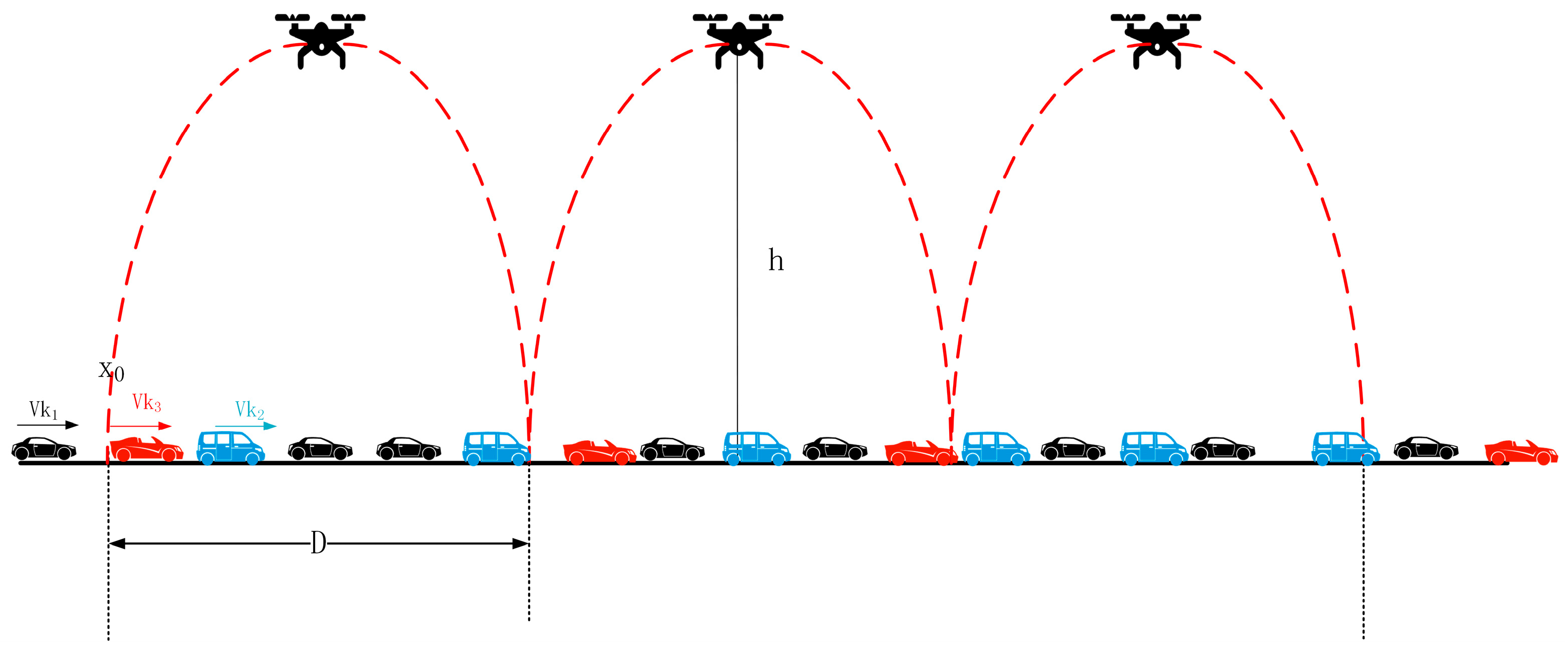
In our analysis, we consider a single-directional highway segment
based on UAVs with a length of D. We need to consider the following situation: As shown in
Figure 1,
represents the reference point where vehicles arrive. The network consists of N vehicles (index
) and M UAVs (index
). The UAVs have a communication range that covers the entire road segment, with the distribution parameter
following a uniform distribution. Given the limited availability of communication resources in UAV and VANET communications, ensuring real-time monitoring of vehicle safety conditions and road conditions becomes a critical challenge. It is essential to transmit BSM information at the shortest possible intervals to meet these requirements. However, this can result in resource constraints and insufficient timeliness, leading to potential safety hazards caused by an overwhelming number of BSMs. Consequently, there is a need to prioritize vehicles and their transmitted data packets. This paper will focus on prioritizing vehicles based on speed ranges and give particular attention to BSM information.
The process can be divided into two steps: (1) classifying vehicles and their transmitted information based on their speed and designing a MAC layer protocol to schedule and queue the transmitted information; (2) using the 802.11p protocol, vehicles transmit the required messages through the MAC layer scheduling process and send them to the UAVs via the uplink. The following provides a detailed explanation.
For convenience, the significant notations and variables used in the analysis procedure are summarized in
Table 2.
3.1. Ground-Bound Vehicular Traffic Model
This paper assumes that the considered segment D represents a low- to moderate-density free-flow ground transportation system. Such a transportation system has been widely applied in the literature. The macroscopic free-flow traffic model used in this study is based on Ref. [
43].
Because the communication range of UAVs under the V2I scenario in a highway depends on multiple factors, including the frequency, power, antenna gain of its communication system, as well as environmental conditions, the communication range can vary from several hundred meters to several kilometers based on different UAV communication systems and specific configurations. Additionally, assuming a constant velocity can help study the worst-case scenario in V2I. Therefore, we assume that after each vehicle k reaches position , its velocity remains unchanged at the speed at position until it exits the communication range of the UAV, .
We assume that the number of vehicles follows a Poisson distribution, and the vehicle density is . The premise of our study is that the vehicle density is not high, as in the case of high vehicle density, and it is highly likely to find multiple vehicle-UAV paths for connection, which does not align with our design approach. We focus on the worst-case scenario, aiming to minimize the number of paths. In this scenario, each time a vehicle enters the communication range of a UAV, it needs to be processed individually.
Additionally, we assume that the VANET includes a location service, such as Hierarchical Location Service (HLS) or Geographic Location Service (GLS), and the information related to the location service is included in the header of the transmitted data packets.
We divide a time window
into several equal intervals
. Since the traffic flow follows a Poisson random process with the parameter
, the arrival time of vehicles is also a random variable denoted as
and follows an exponential distribution with the parameter
. Assuming that there is one vehicle arriving at the entrance point
in each time interval
, the average value and probability density function (pdf) [
44] of the vehicle arrival time can be written as follows:
The speed
at point
is a continuous random variable, represented by
for the mean value and
for the standard deviation. The probability density function (pdf) of
follows a truncated normal distribution [
45].
In addition,
, and the time for a vehicle to pass through
is denoted as
.
3.2. UAV-Assisted Vehicular Channel Model
The task of utilizing UAVs as intermediate relay bridges to facilitate the construction of VANET networks for enabling communication between two vehicles that are not within direct range of each other has been extensively studied in previous research papers. However, this specific scenario is not the focus of this paper. Instead, this paper primarily focuses on studying the connections formed within the communication range of a UAV. Each UAV categorizes and prioritizes all vehicles within its coverage area based on their speeds. By calculating the total delay, performing comparisons, and making optimal allocations, this paper aims to provide a detailed explanation. The relationship between drones and vehicles’ positions is as shown in
Figure 2.
The speed
of each vehicle is gathered at location
and remains constant until it exits the communication range of the UAV. At any given time, a vehicle establishes an uplink connection with the UAV. To ensure that the UAV can receive signals from each vehicle and obtain signal strength, this model is considered to be composed of both LoS and NLoS links [
22]. Depending on the UAV’s position and flight altitude, these links will have different probabilities. The vehicle K’s position is defined as
, while the UAV’s position is
, and
must be optimized to satisfy QoS constraints. As shown in
Figure 2, according to the Euclidean distance, the distance d between vehicle k and UAV u can be written as:
Assuming
negligible values are ignored and considered as 0, the probabilities of LoS and NLoS links corresponding to the UAV are as follows:
where
and
are constants determined by the environment and carrier frequency,
is the elevation angle, and
=
. Thus, the path loss expressions for LoS and NLoS links can be derived as follows:
where,
represents the path loss exponent, and
and
are determined by the environment and represent the average additional loss for free space propagation in LoS and NLoS connections, respectively.
denotes the speed of light, and
represents the carrier frequency. Therefore, we can obtain the average path loss and the average channel gain as follows:
Thus, we can derive the SNR received by the UAV u from the vehicle at its current position as follows:
where
is the transmission power of vehicle k,
represents co-channel interference,
denotes Gaussian white noise, and W is the bandwidth. According to the model, to achieve effective data transmission between the UAV and the vehicles, it is necessary to maximize the end-to-end rate while minimizing latency and power consumption.
3.3. The MAC Layer Communication Protocol
In densely populated traffic areas, such as congested urban roads or highways, vehicles often accumulate a substantial volume of safety information. As per the J2735 standard established by the Society of Automotive Engineers (SAE) in the United States [
9], the increased number of vehicles leads to a significant rise in the frequency of BSMs received by UAVs per second. Consequently, important safety information may be discarded due to large transmission intervals, resulting in delayed or inadequate updates that compromise timeliness. This situation poses significant safety hazards. To mitigate such concerns, we have implemented a prioritization scheme for vehicles and their messages, enabling the prioritized validation and transmission of critical safety information. The subsequent section outlines the design of our MAC layer protocol.
In this study, due to vehicles entering the UAV communication range as a Poisson process and each vehicle transmitting fixed-sized data packets of
bits at any given time, we adopt an M/G/1 queue model. Taking into account the priority categories, we assume there are r priority levels. Vehicles and their transmitted data packets of priority level i arrive according to a Poisson process with arrival rate
, with specific values obtained from
Section 3.1. It is worth noting that the adopted priority mechanism in this study is Preemptive-Resume Priority [
46], meaning that high-priority customers interrupt the service of low-priority customers. Upon interruption, a checkpoint is set, and the interrupted data enter the Shunts for storage. The service time of the lower-priority customer resumes at the checkpoint. For a customer of priority level i, due to the preemption rule, there are no lower-priority customers appearing ahead of them in their queue, i.e.,
. The following provides a detailed explanation of the priority setting.
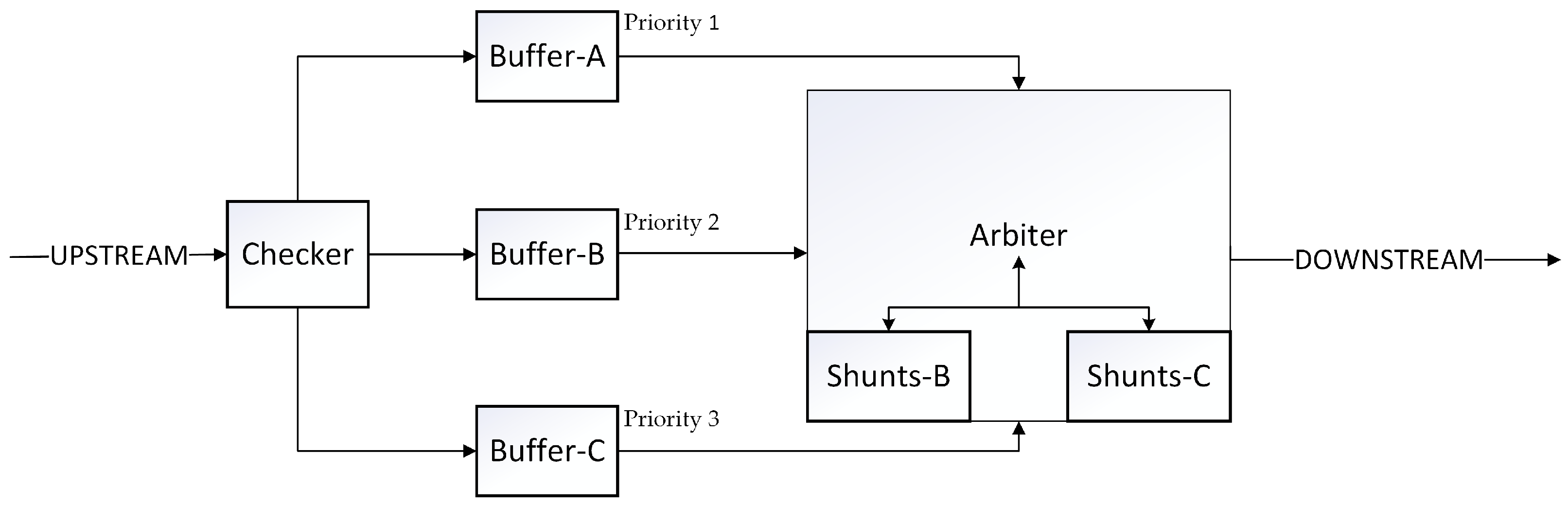
As shown in
Figure 3, all devices are located inside the UAV for operation. The frame-header Checker (referred to as Checker in the diagram) is responsible for checking the header of the message packets received from the vehicles on the uplink, determining whether to accept them and dividing them into segments based on the vehicle’s speed (included in the packet header). Buffer-A, Buffer-B, and Buffer-C represent three buffers that receive data packets from different priority levels and wait for instructions from the Arbiter. The Arbiter is responsible for scheduling the transmission order on the output link and accessing the outgoing packets. It has Shunts B and Shunts C buffers that store the remaining data packets of interrupted low and medium priority levels due to the Preemptive-Resume Priority rule.
The information enters the frame-header Checker from vehicles on the Up Stream and the message priority is determined. The information transmitted by vehicles in the high-speed section enters Buffer-A as high-priority, while that transmitted by vehicles in the medium-speed section enters Buffer-B as medium-priority and that transmitted by vehicles in the low-speed section enters buffer Buffer-C as low-priority. The Arbiter is responsible for scheduling the transmission order on the output link and accessing the outgoing packets. If a medium-priority packet is interrupted by a high-priority packet, a breakpoint is set, and the remaining packets are transferred to Shunts B. If a low-priority packet is interrupted by a high- or medium-priority packet, a breakpoint is set and the remaining packets are transferred to Shunts C. We assume that the time it takes for packets to be transmitted to the buffer is negligible [
47].
The protocol defines the mechanism for bandwidth allocation and packet scheduling. Assuming that the number of packets is negligible and that each buffer has an infinite capacity, the Arbiter can simply schedule the packets based on the following priority order (from highest to lowest). The packet scheduling is based on considerations of timeliness since the unmanned vehicle has a limited capacity to process messages within a given time period. Therefore, the protocol prioritizes the processing of data packets from vehicles in the high-speed section. Here is the specific priority order:
Packets from Buffer-A
Packets from Buffer-B
Packets from Buffer-C
In this order, the Arbiter will allocate resources and schedule packet transmission accordingly.
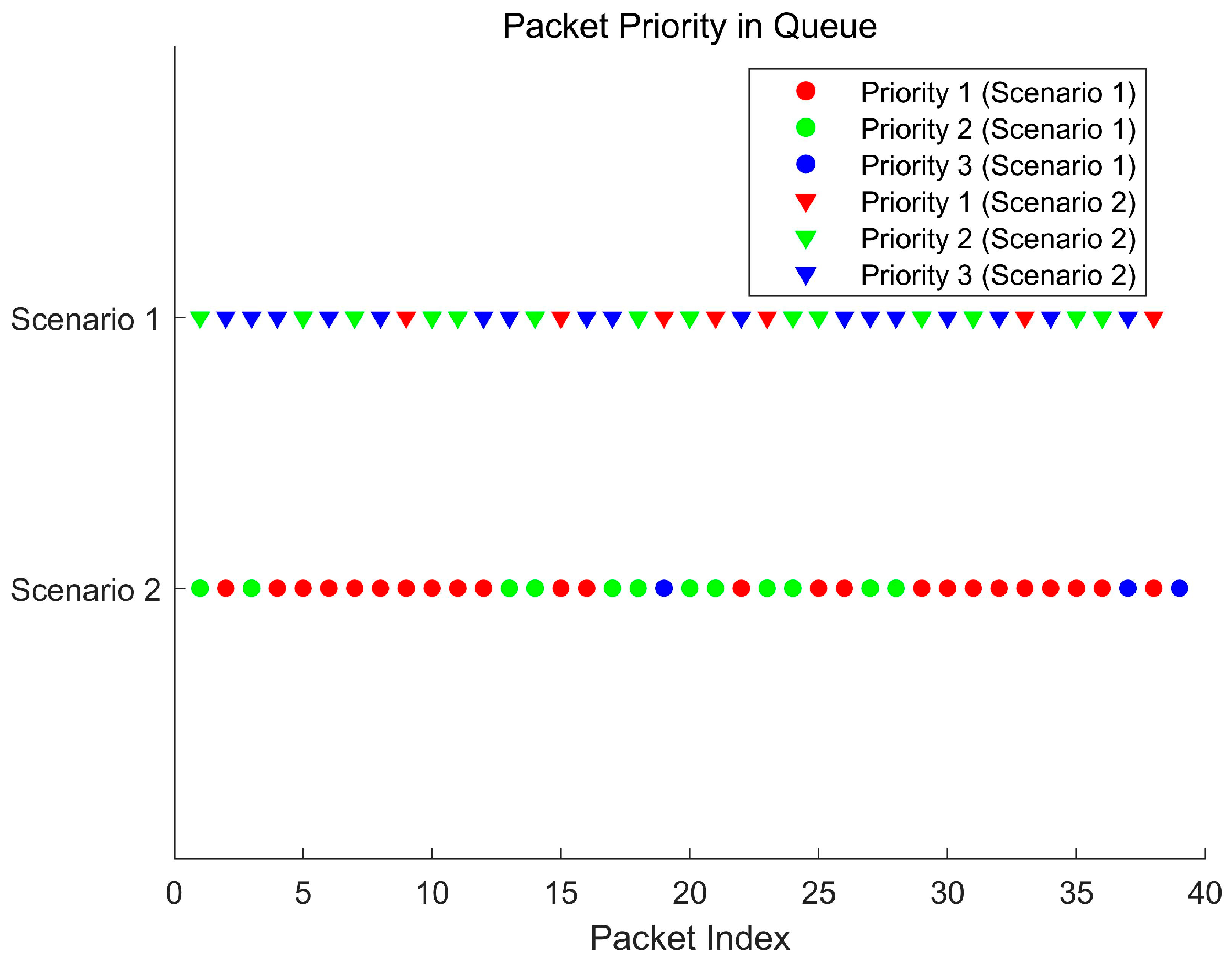
As shown in
Figure 4, the queue currently contains one data packet with priority 2 and two data packets with priority 3. At this moment, when a data packet with priority 1 arrives, it interrupts the queue and is prioritized for processing.
The following is a description of the protocol steps for the Preemptive-Resume Priority 802.11 CSMA/CA [
48] with an arbiter in this article; the flowchart is shown in
Figure 5.
Step 1: Initialization
Each node determines its own priority and sets reasonable initial contention window sizes, maximum backoff times, and an arbiter node to coordinate the priority transmission order between nodes and the preemptive interruption (including the buffer).
Step 2: Contention Stage
When a node is ready to send data, it first sends requests to the Arbiter and carries its priority information.
The Arbiter sets different listening times for different priorities brought by each node (shorter for higher priority, and so on, defined as High Distributed inter-frame space (HDIFS), Middle Distributed inter-frame space (MDIFS), and Low Distributed inter-frame space (LDIFS)). If the channel is idle during the listening time, the contention channel stage is entered; otherwise, the backoff mechanism is triggered.
Step 3: Backoff Mechanism
This article employs the backoff mechanism of IEEE 802.11 standard DCF, which uses a binary exponential backoff method with a backoff time range of (0, ). represents the current backoff stage, and represents the corresponding contention window size. is equal to 2 to the power of J, where m is the maximum backoff stage specified in the 802.11 standard, and W is the initial contention window size (as set in step 1). The backoff counter takes a value of and decreases by one for every time slot when the channel is idle; otherwise, it remains unchanged. If a collision occurs (i.e., multiple nodes have the same priority or the Arbiter indicates preemption is allowed, causing these nodes to potentially send data simultaneously), the contention window of the colliding nodes doubles to reduce the collision probability. The node enters the contention phase when the backoff counter countdown ends; otherwise, it continues to wait and updates the counter.
Step 4: Contention Channel
After the backoff counter of a node reaches zero, the node sends another request to the Arbiter. The Arbiter evaluates the priority of the node and considers other ongoing transmissions to determine the next node for data transmission. If the current node has the highest priority or the Arbiter indicates that the node can preempt, the node immediately sends the data. Otherwise, the node continues to wait.
Step 5: Data Transmission
Nodes that obtain permission from the Arbiter start transmitting data. Other nodes temporarily stop sending data and continue to monitor the channel state upon detecting channel occupancy.
Step 6: Channel Release
Upon completion of data transmission, the node releases the channel and notifies the Arbiter that the channel is idle, allowing other nodes to contend for the channel.
In summary, in this scenario, we need to consider the following aspects:
Reasonable selection of UAV altitude and communication range.
Considering the transmission time from vehicles to UAVs, calculate the MAC layer service time. The queuing time is calculated using the designed UAV MAC layer protocol. Calculate the expressions for latency and rate, and based on this, calculate the BSM transmission interval.
Based on the parameter definition of the objective function, obtain a solution that is in line with practical considerations and simulate its implementation.
5. Numerical Results
In this paper, we idealize the definition of a message to contain only one packet, which can be adjusted in size as bits. Multiple packets contained within a message can be treated as one large packet. In this paper, the packet size is set to 10,240 bits.
To evaluate the effectiveness of the above expression, we conducted simulation experiments on MATLAB. In the simulation, the set parameters are shown in the following table, where the G2A link delay is based on
Table 3 and referenced from the literature [
19].
The MAC layer and queuing delay are based on
Table 4, referenced from the literature [
48].
Furthermore, this paper defines the number of priority levels r as 3. The control frame rate is . The DIFS for each priority level is defined as . The vehicle speed range is defined as ; .
Analysis of Delay and Processed Packet Volume under Different Arrival Rates
For scenario 1, we selected and defined the collision probability P based on the number of vehicles or messages, where a higher number of messages corresponds to a higher probability of packet collisions, .
For scenario 2, we selected and defined the collision probability P based on the number of vehicles or messages, considering the case where higher priority packets need to take into account the presence of low priority packets in effective collisions, .
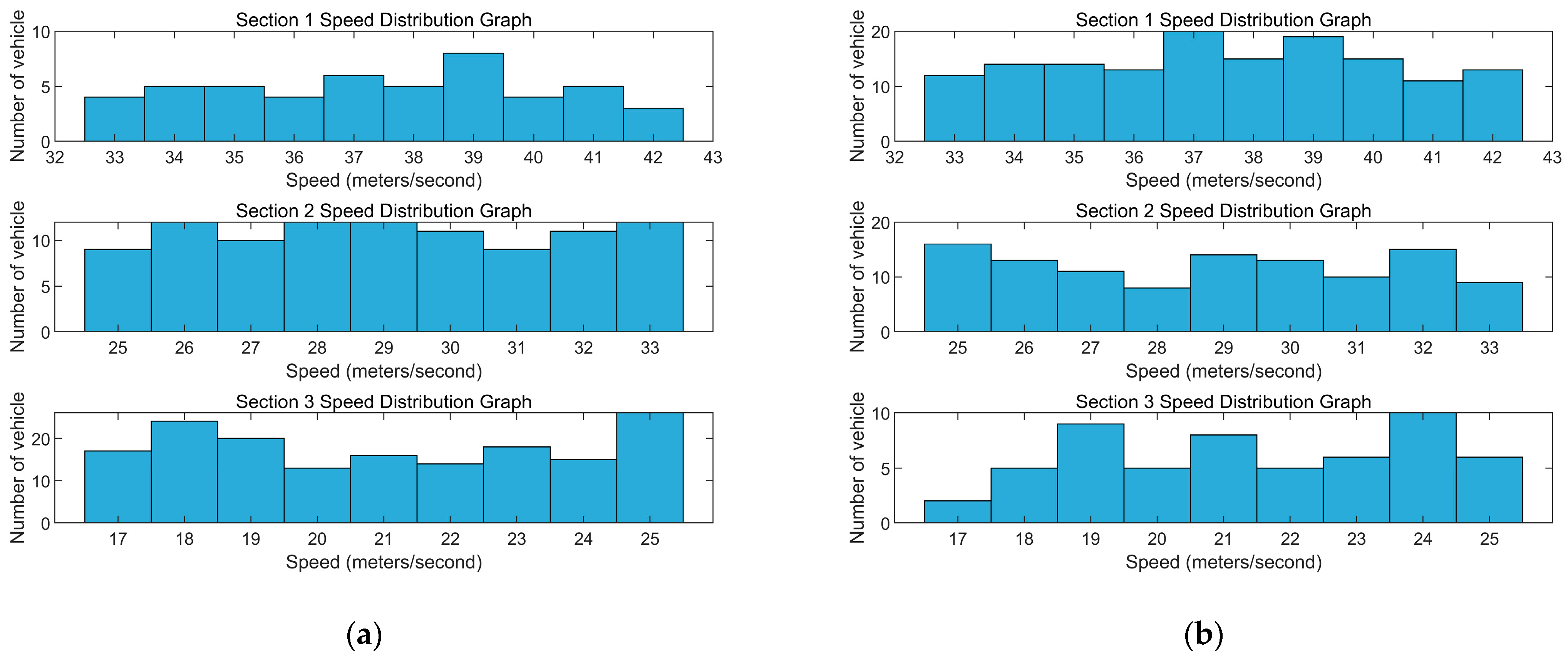
According to
Figure 8a, the model follows a Poisson distribution, and it shows the number of vehicles in different speed ranges under the condition of
.
According to
Figure 8b, the model follows a Poisson distribution, and it shows the number of vehicles in different speed ranges under the condition of
.
According to the simulation and
Figure 9a, the average speed in different speed ranges is
. The average passage time in different speed ranges is
.
According to
Figure 9b, it can be observed that the difference between scenarios 1 and 2 lies in the varying arrival rates, which in turn lead to different numbers of vehicles. However, there is not much impact on the average values of different vehicle speeds or the average passage times. the average speed in different speed ranges is
. The average passage time in different speed ranges is
.
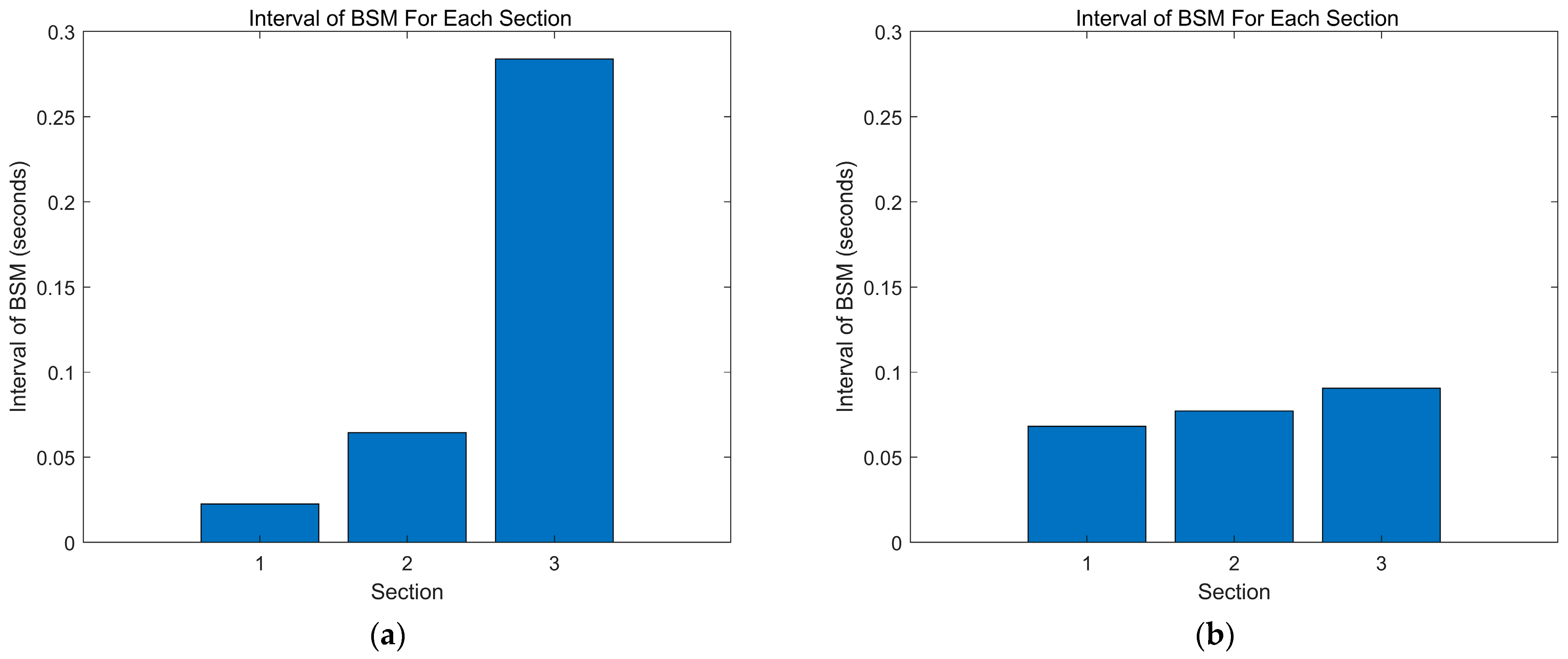
The specific data in
Figure 10a are as follows:
,
.
Figure 10a shows that due to the low number of vehicles in the higher priority segment (Priority 1) and the smaller collision probability P at the stations, the vehicles in the higher speed range can send data packets with little waiting time and have shorter processing times compared to other speed ranges. This finding aligns with the real-world scenario. On the other hand, for the medium and lower speed ranges corresponding to Priority 2 and 3, the delay increases. Vehicles in the lower speed range need to wait for some time before sending data packets. This matches the initial design intention of this study.
The specific data in
Figure 10b are as follows:
. Comparing scenario 1, it can be observed that due to the increased arrival rate in the higher speed range, there is an increase in the number of vehicles and thus, an increase in the number of sent data packets. As a result, the average service time, average waiting time, and total delay for Priority 1 also increase compared to scenario 1. Additionally, the medium and lower speed ranges also experience an increase in delay due to the need to avoid the data packets from the higher speed range. This observation aligns with the requirements of this study.
The specific data in
Figure 11a are as follows:
. The vehicles in speed range 3, which represents the slowest speed, have a longer travel time within the UAV coverage area. However, due to their longer transmission or queuing time, the time interval between sending BSMs for these vehicles is longer compared to other speed ranges, and it shows an increasing trend.
The specific data in
Figure 11b are as follows:
. Compared with scenario 1, it can be observed that due to the increased number of vehicles and thus, an increase in the number of high-priority data packets in the higher speed range, the time interval between sending BSMs increases in scenario 2. This is reasonable since more vehicles result in more data packets, which increases collision probability and thus, increases service and waiting times in the queue, leading to longer time intervals between packet transmissions.
However, as shown in
Figure 11a,b, for the medium and lower speed ranges, the delay time in the queue does not decrease but increases when the arrival rate and the number of vehicles and data packets decrease compared to scenario 1. Additionally, due to the reduced number of vehicles, there are fewer BSM data packets, resulting in similar time intervals between packet transmissions for Priority 2 compared to scenario 1 (as the arrival rate for Priority 2 remains unchanged), and shorter time intervals for Priority 3 but still higher than those for Priorities 1 and 2.
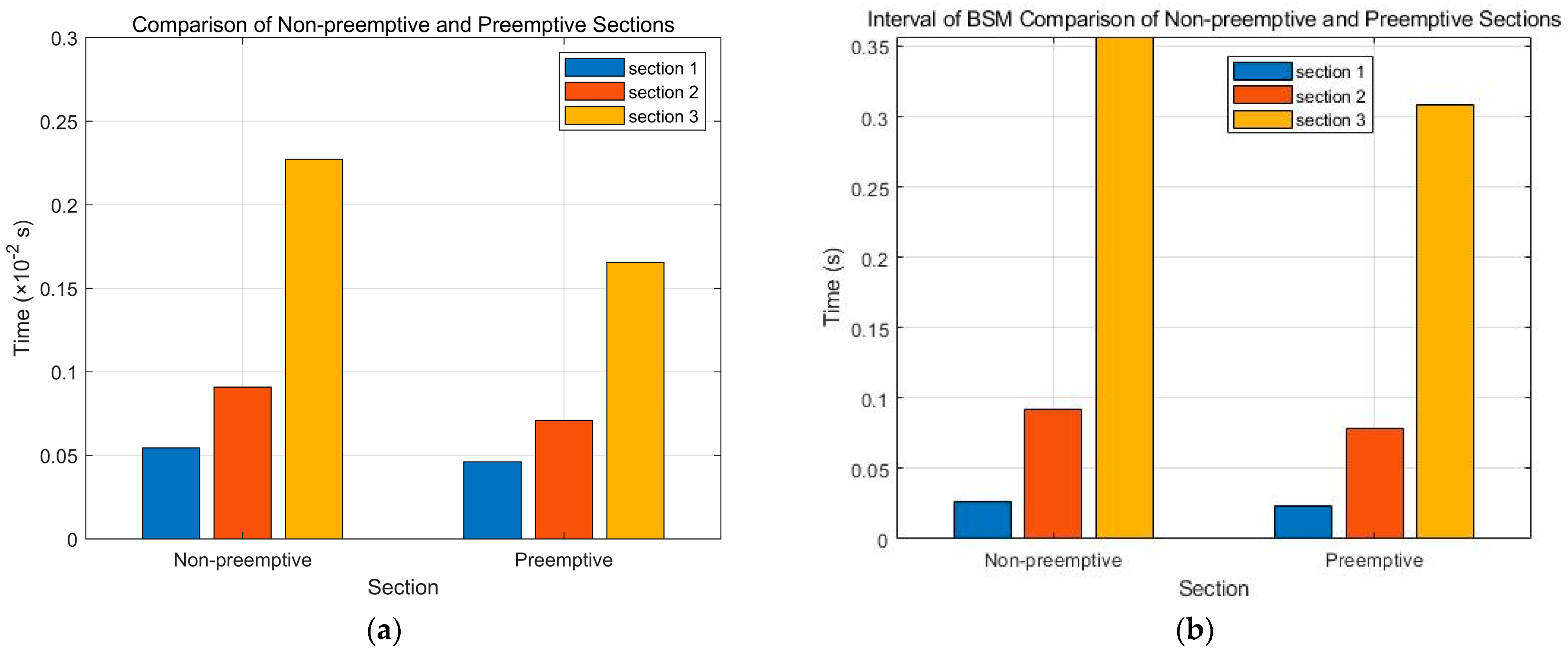
Figure 12a,b demonstrates the practicality of the preemptive priority assignment scheme and MAC layer protocol design adopted in this paper by comparing preemptive and commonly used non-preemptive priority assignment schemes. Compared to non-preemptive schemes, preemptive schemes are more effective in managing and scheduling tasks in highly competitive resource environments, improving system responsiveness and throughput. By assigning different priorities to tasks, preemptive schemes can ensure that high-priority tasks are executed in a timely manner, thereby meeting the requirements of applications with higher real-time performance demands. Additionally, it is worth noting that based on the data, the preemptive scheme reduces latency compared to the non-preemptive high-priority scheme by 8.17% and overall system by 24.92%. In terms of frequency, the preemptive scheme is 23.55% stronger than the non-preemptive scheme. Therefore, the preemptive priority assignment scheme and MAC layer protocol design adopted in this paper are very useful and can effectively improve system performance and network transmission quality, meeting the requirements of different application scenarios.
As shown in
Figure 13a, this study compares the preemptive priority allocation scheme employed in this paper with the priority-based MAC layer modification scheme proposed in reference [
34], demonstrating the practicality of the priority allocation scheme and MAC layer protocol design utilized in this work. Compared to reference [
34], our proposed scheme exhibits significant advantages in terms of overall system delay performance, achieving a 68.8% higher overall efficiency. This further validates the novelty and effectiveness of our approach. By introducing a priority allocation mechanism, our proposed scheme better meets the real-time and reliability requirements of different types of data in vehicular communication, thereby enhancing system performance and efficiency. This positions our paper as a valuable point of comparison and provides beneficial insights for research and practice in the field of vehicular networking.
As depicted in
Figure 13b, this study presents a comparison between our proposed scheme and a paper published in the Sensor journal under MDPI [
35]. Both studies focus on modifying the 802.11P protocol using queuing theory and 2D Markov models. However, our proposed scheme incorporates a priority allocation mechanism, which enhances the timeliness of high-priority vehicles and significantly improves the overall system performance. Additionally, our proposed scheme better caters to the communication requirements of different vehicles, optimizing system performance and efficiency. Comparative analysis reveals that our proposed scheme outperforms the approach presented in paper [
35], resulting in a 22.7% higher overall system efficiency. This further validates the novelty and practicality of our proposed scheme, offering valuable insights for research and applications within the vehicular networking domain.
This finding suggests that the priority classification in this study achieves the expected results of prioritizing higher priority vehicles, i.e., those in the higher speed range, to use limited resources, and allows for speed limiting measures to be taken for these vehicles to ensure normal UAV operation. The small change in numbers is mainly due to the limited number of data packets and vehicles and insufficient arrival rate parameters, which is in line with realistic scenarios [
49,
50].
Congestion: In situations with high vehicle arrival rates, the number of vehicles on the road may exceed the road capacity, leading to congestion. This can cause traffic jams and reduce vehicle speeds. When the arrival rate approaches or exceeds the road capacity, vehicle speeds often significantly decrease.
Traffic safety: On highways, vehicle speeds may be limited to maintain safe distances and prevent accidents. If the vehicle arrival rate increases but the road capacity cannot accommodate it, traffic management authorities may take measures to restrict vehicle speeds to ensure safety.
Road infrastructure and design: Road structures, signs, speed limits, and other factors can affect vehicle speeds. Even if the arrival rate increases, if the road design and facilities do not support high-speed travel, vehicle speeds may still be limited.
These aspects will be further explored and addressed in subsequent research.
6. Conclusions
In this paper, we proposed an algorithm based on UAV-assisted VANETs for prioritizing data transmission and interaction between vehicles and UAVs, considering the speed of the moving vehicles. This algorithm was used to allocate limited wireless communication resources and ensure priority for the transmission of safety-critical information, such as traffic information. To achieve this, we designed an improved 802.11 CSMA/CA MAC layer access protocol equipped with an arbitrator. Additionally, we established a preemptive M/G/1 queuing theory model based on this network and calculated the data delay. By prioritizing the transmission requirements of the highest-priority moving vehicles in safety-related information transmission, we addressed the problem of minimizing total delay. We further transformed the problem of minimizing total delay within the same UAV coverage area into a problem of minimizing BSM transmission intervals. Finally, through simulation experiments, we validated the effectiveness of the proposed method in this paper. The simulation results demonstrated that under different arrival rates, this mechanism could reduce the transmission intervals for high-speed vehicles, thereby improving the efficiency of information transmission for high-speed driving vehicles and meeting the network performance requirements of safety driving applications in intelligent transportation systems.
At the time of this research, certain limitations existed in our work. First, this paper only considered the uplink transmission from vehicles to the relay portion; the downlink transmission from the relay back to the user vehicles will be investigated in future studies. Second, our research focused primarily on the V2I communication mode, but future work is needed to incorporate V2V communication for further expansion. Additionally, it is important to note that our simulation results are numerical solutions, and therefore, future studies will involve utilizing other simulation software to conduct further research and validate the practical implications of our findings. In order to further enhance our research, we plan to address these limitations and conduct a more comprehensive exploration in future studies.