CRC-Based Reliable WiFi Backscatter Communiation for Supply Chain Management
Abstract
1. Introduction
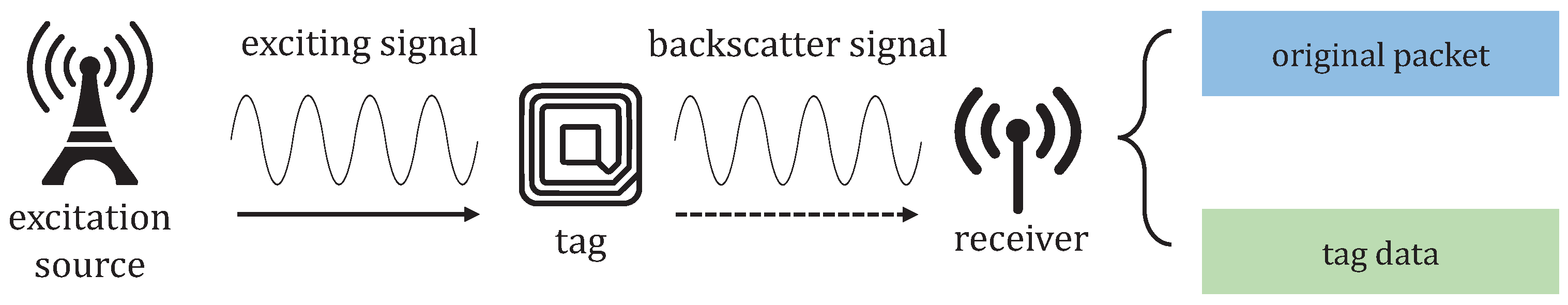
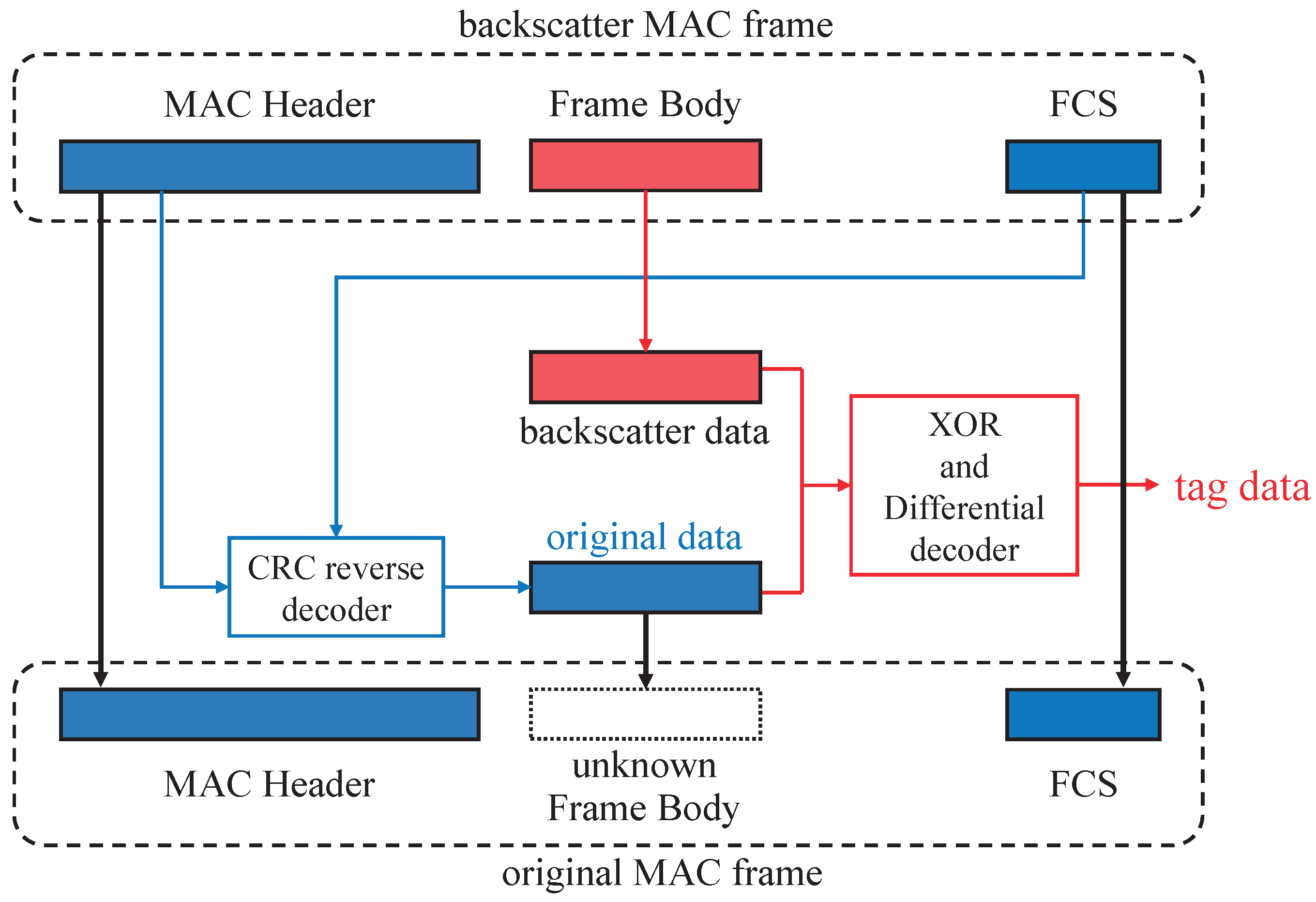
- The current study proposes a CRC reverse-algorithm-based single-AP backscatter system with ambient WiFi signals called CRCScatter. The system uses a CRC reverse decoder to solve the problem of decoding original excitation data from a backscatter packet.
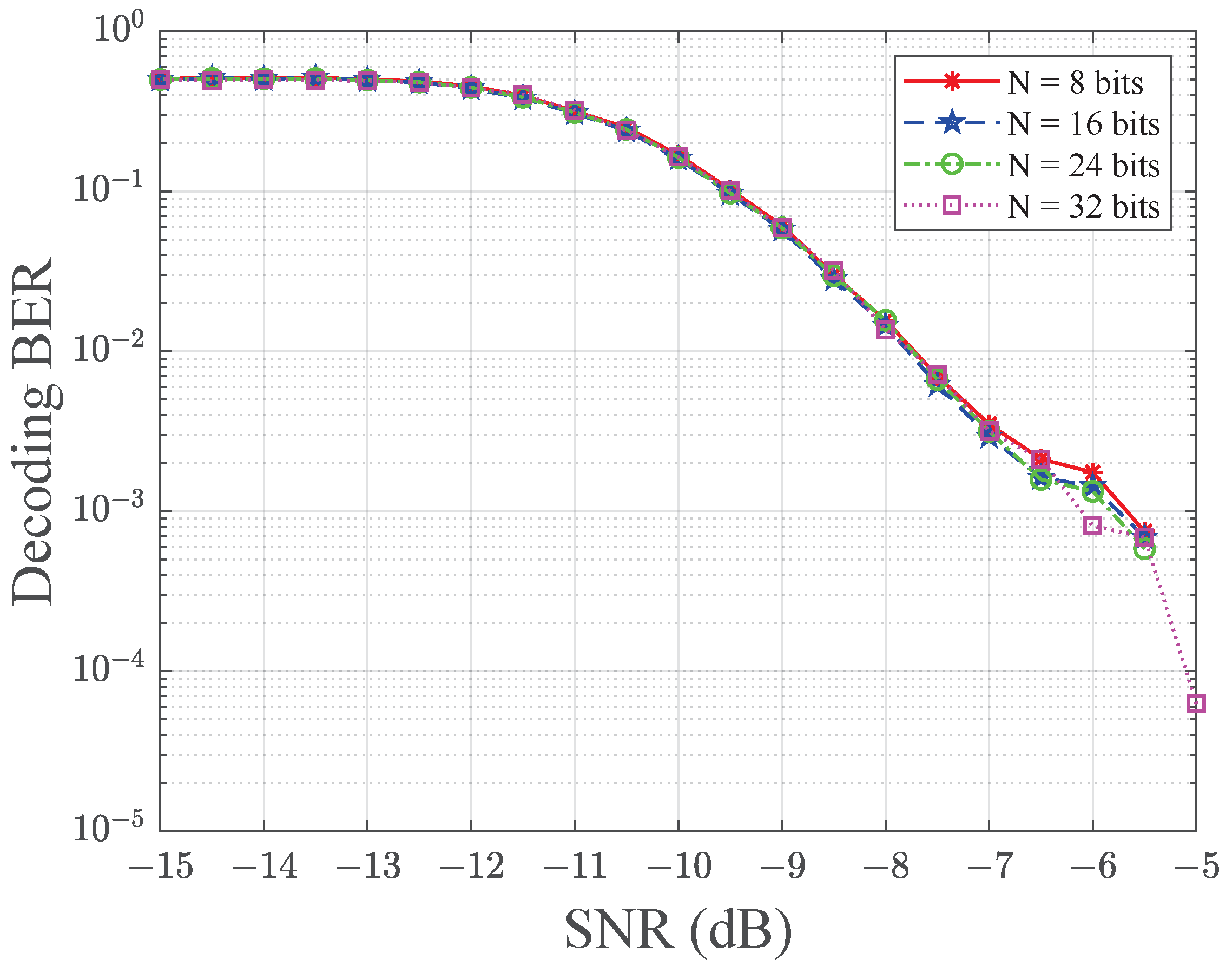
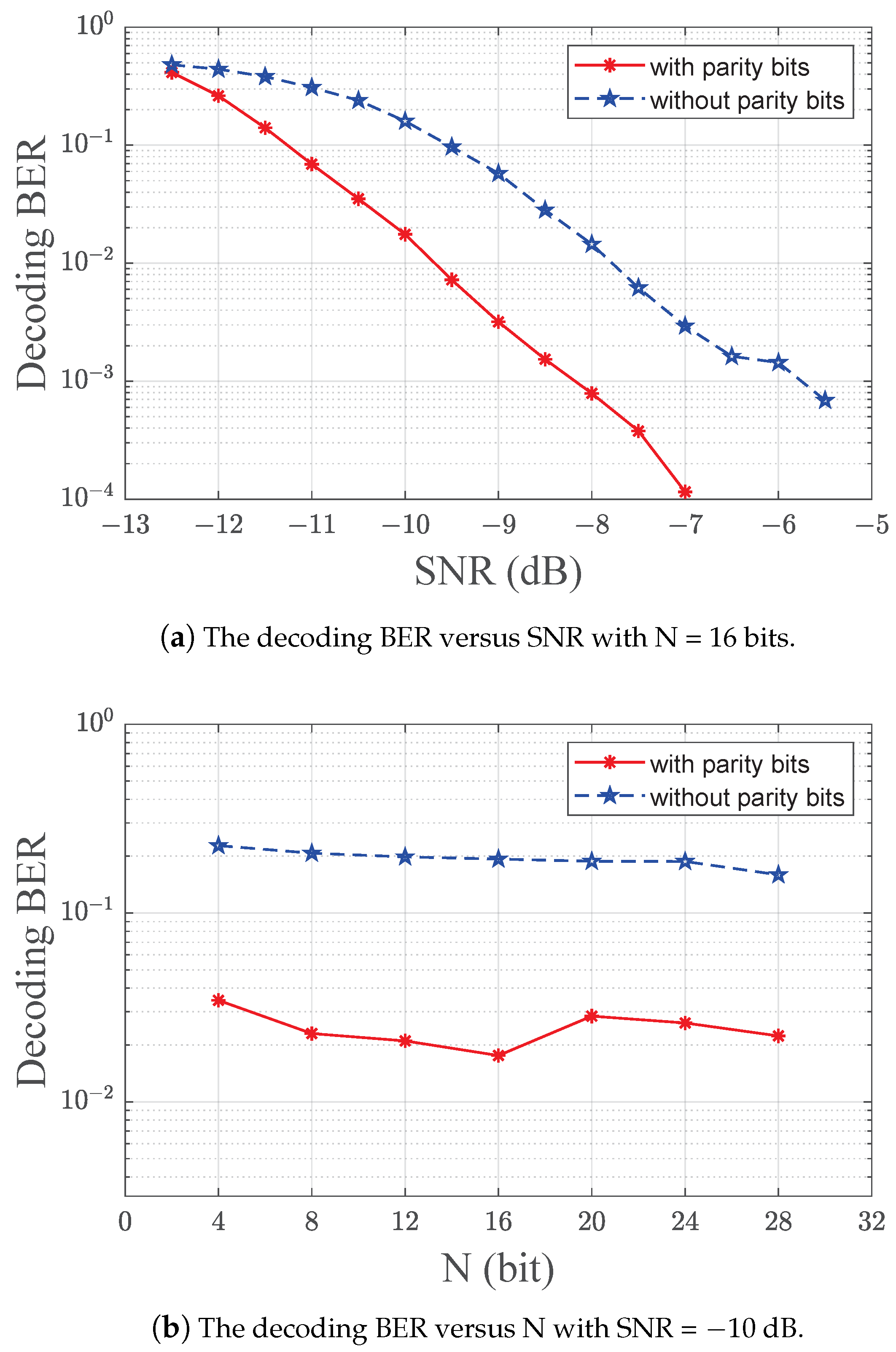
- The current research present simulation results to verify the effectiveness of CRCScatter and analyze the performance. The CRCScatter system achieves a decoding tag data bit error rate of at SNR = −7.5 dB.
- The simulation results verify that the CRC reverse algorithm is better than the brute-force search method in decoding efficiency and the average decoding time of CRCScatter is independent of the tag data length. An improved method for adding redundant bits to the tag data is proposed to improve the decoding accuracy in the presence of noise interference.
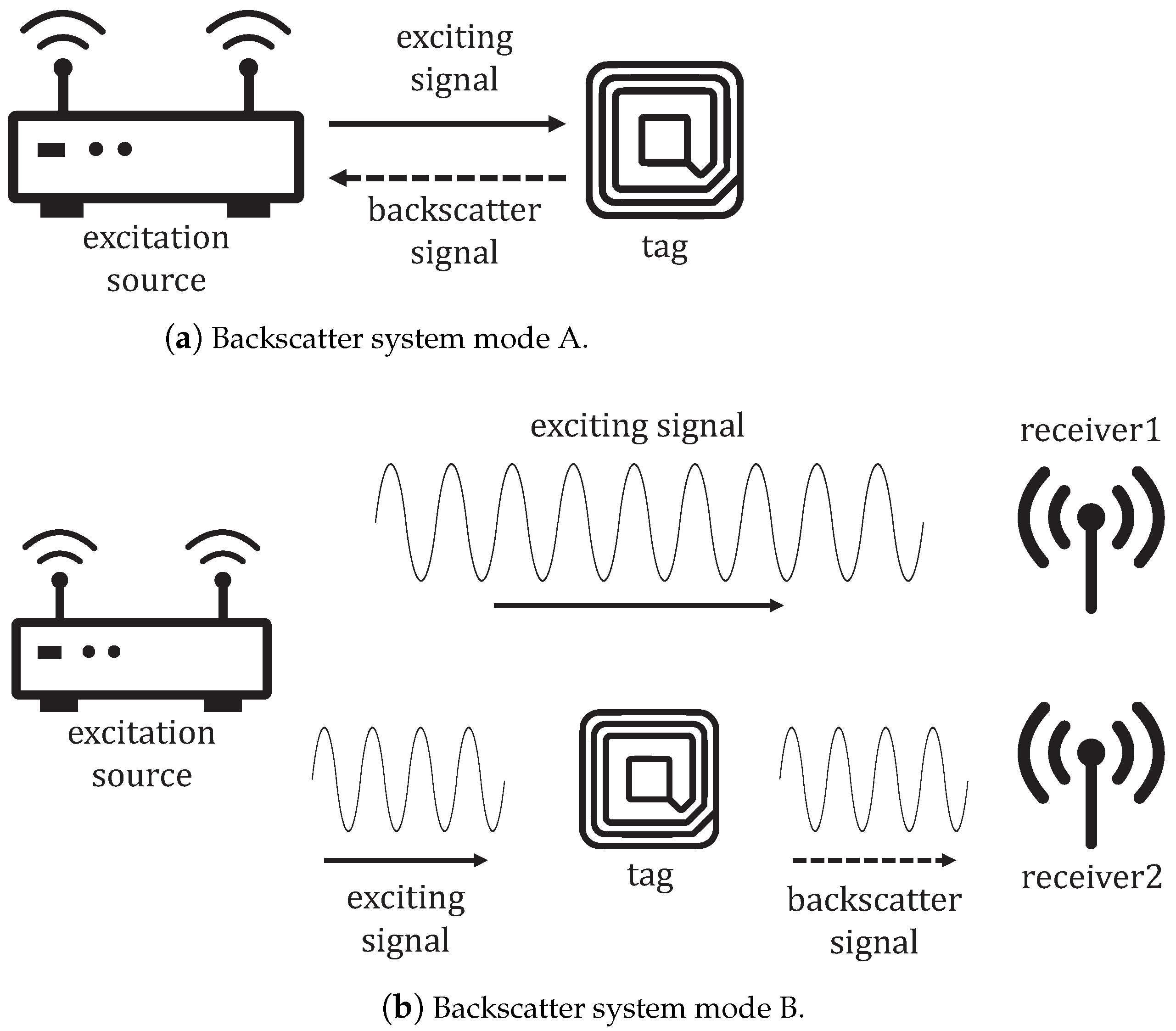
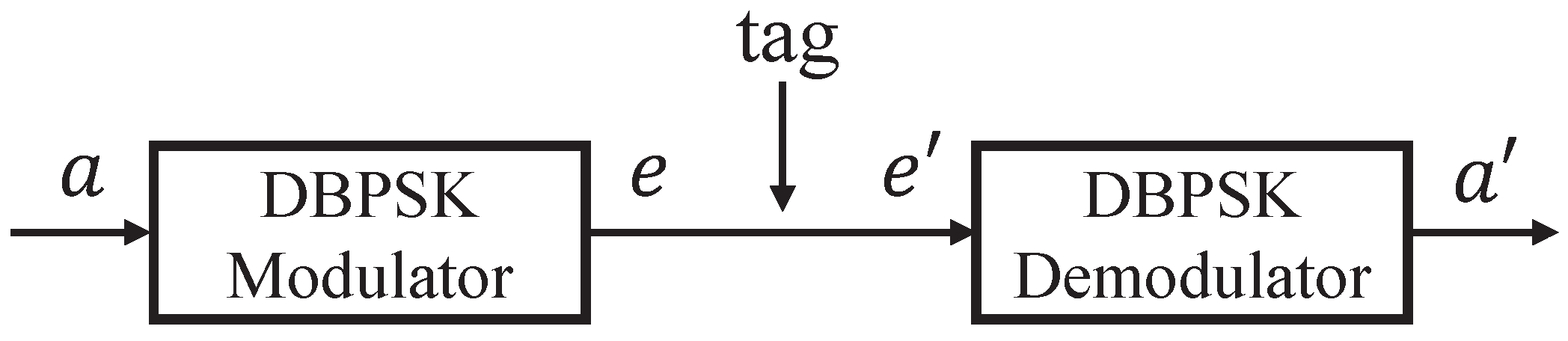
2. System Model
2.1. 802.11b Packet Structure
2.2. Codeword Translation
3. CRCScatter Decoder Design
3.1. CRCScatter Decoder Overview
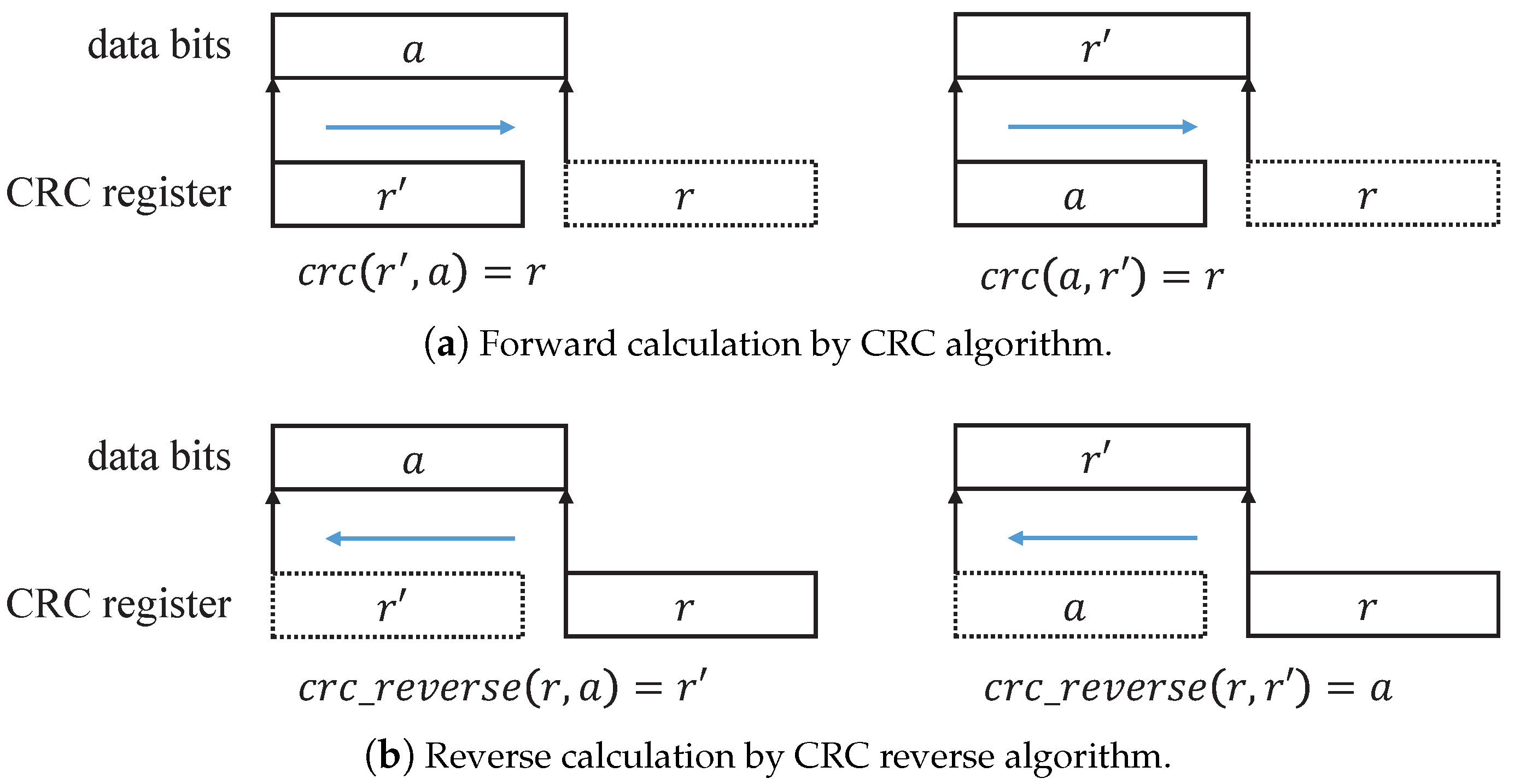
3.2. CRC Reverse Decoder
3.2.1. The Algorithms of CRC in the CRC Reverse Decoder
| Algorithm 1 Calculation of the CRC |
|
| Algorithm 2 CRC32 reverse algorithm |
|
3.2.2. How to Reverse the Unknown Data from CRC32 Value?
3.2.3. How to Reverse the Original Data?
| Algorithm 3 Calculation in CRC reverse decoder |
|
3.3. XOR and Differential Decoder
| Algorithm 4 Calculation in XOR and differential decoder |
|
4. Simulation Results
5. Discussions and Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
References
- Menanno, M.; Savino, M.M.; Accorsi, R. Digitalization of Fresh Chestnut Fruit Supply Chain through RFID: Evidence, Benefits and Managerial Implications. Appl. Sci. 2023, 13, 5086. [Google Scholar] [CrossRef]
- Lolli, F.; Coruzzolo, A.M.; Peron, M.; Sgarbossa, F. Age-based preventive maintenance with multiple printing options. Int. J. Prod. Econ. 2022, 243, 108339. [Google Scholar] [CrossRef]
- Feng, D.; Jiang, C.; Lim, G.; Cimini, L.J.; Feng, G.; Li, G.Y. A survey of energy-efficient wireless communications. IEEE Commun. Surv. Tutor. 2013, 15, 167–178. [Google Scholar] [CrossRef]
- Maselli, G.; Piva, M.; Stankovic, J.A. Adaptive Communication for Battery-Free Devices in Smart Homes. IEEE Internet Things J. 2019, 6, 6977–6988. [Google Scholar] [CrossRef]
- Huang, Y.; Yuan, L.; Gong, W. Research on IEEE 802.11 OFDM Packet Detection Algorithms for Household Wireless Sensor Communication. Appl. Sci. 2022, 12, 7232. [Google Scholar] [CrossRef]
- Yao, C.; Liu, Y.; Wei, X.; Wang, G.; Gao, F. Backscatter technologies and the future of internet of things: Challenges and opportunities. Intell. Converg. Netw. 2020, 1, 170–180. [Google Scholar] [CrossRef]
- Maselli, G.; Pietrogiacomi, M.; Piva, M.; Stankovic, J.A. Battery-Free Smart Objects Based on RFID Backscattering. IEEE Internet Things Mag. 2019, 2, 32–36. [Google Scholar] [CrossRef]
- Wu, W.; Hawbani, A.; Gong, W. Ortho-CodeA: Orthogonal Codes Assisted Backscatter Multiple Access. In Proceedings of the 2023 IEEE International Conference on Pervasive Computing and Communications (PerCom), Atlanta, GA, USA, 13–17 March 2023. [Google Scholar]
- Daskalakis, S.N.; Goussetis, G.; Assimonis, S.D.; Tentzeris, M.M.; Georgiadis, A. A uW Backscatter-Morse-Leaf Sensor for Low-Power Agricultural Wireless Sensor Networks. IEEE Sens. J. 2018, 18, 7889–7898. [Google Scholar] [CrossRef]
- Fieuzal, R.; Baup, F. Estimation of Multi-Frequency, Multi-Incidence and Multi-Polarization Backscattering Coefficients over Bare Agricultural Soil Using Statistical Algorithms. Appl. Sci. 2023, 13, 4893. [Google Scholar] [CrossRef]
- Daskalakis, S.N.; Kimionis, J.; Collado, A.; Tentzeris, M.M.; Georgiadis, A. Ambient FM backscattering for smart agricultural monitoring. In Proceedings of the 2017 IEEE MTT-S International Microwave Symposium (IMS), Honololu, HI, USA, 4–9 June 2017. [Google Scholar]
- Daskalakis, S.N.; Assimonis, S.D.; Goussetis, G.; Tentzeris, M.M.; Georgiadis, A. The Future of Backscatter in Precision Agriculture. In Proceedings of the 2019 IEEE International Symposium on Antennas and Propagation and USNC-URSI Radio Science Meeting, Atlanta, GA, USA, 7–12 July 2019. [Google Scholar]
- Lin, K.; López, O.L.A.; Alves, H.; Chapman, D.; Metje, N.; Zhao, G.; Hao, T. Throughput optimization in backscatter-assisted wireless-powered underground sensor networks for smart agriculture. Internet Things 2022, 20, 100637. [Google Scholar] [CrossRef]
- Gong, W.; Chen, S.; Liu, J.; Wang, Z. MobiRate: Mobility-Aware Rate Adaptation Using PHY Information for Backscatter Networks. In Proceedings of the IEEE INFOCOM 2018-IEEE Conference on Computer Communications, Honolulu, HI, USA, 16–19 April 2018. [Google Scholar]
- Gong, W.; Yuan, L.; Wang, Q.; Zhao, J. Multiprotocol backscatter for personal IoT sensors. In Proceedings of the 16th International Conference on emerging Networking EXperiments and Technologies, Barcelona, Spain, 1–4 December 2020. [Google Scholar]
- Zhao, J.; Gong, W.; Liu, J. Towards scalable backscatter sensor mesh with decodable relay and distributed excitation. In Proceedings of the 18th International Conference on Mobile Systems, Applications, and Services, Toronto, ON, Canada, 15–19 June 2020. [Google Scholar]
- Wang, A.; Iyer, V.; Talla, V.; Smith, J.R.; Gollakota, S. FM Backscatter: Enabling Connected Cities and Smart Fabrics. In Proceedings of the 14th USENIX Symposium on Networked Systems Design and Implementation (NSDI ’17), Boston, MA, USA, 27–29 March 2017. [Google Scholar]
- Zhao, J.; Gong, W.; Liu, J. X-Tandem: Towards Multi-Hop Backscatter Using Commodity WiFi. In Proceedings of the 24th Annual International Conference on Mobile Computing and Networking, New Delhi, India, 29 October–2 November 2018. [Google Scholar]
- Zhao, R.; Zhu, F.; Feng, Y.; Peng, S.; Tian, X.; Yu, H.; Wang, X. OFDMA-enabled Wi-Fi backscatter. In Proceedings of the 25th Annual International Conference on Mobile Computing and Networking, Los Cabos, Mexico, 21–25 October 2019. [Google Scholar]
- Yang, Y.; Gong, W. Universal Space-Time Stream Backscatter with Ambient WiFi. In Proceedings of the 2022 IEEE International Conference on Pervasive Computing and Communications (PerCom), Pisa, Italy, 21–25 March 2022. [Google Scholar]
- Wang, Q.; Chen, S.; Zhao, J.; Gong, W. RapidRider: Efficient WiFi Backscatter with Uncontrolled Ambient Signals. In Proceedings of the IEEE INFOCOM 2021-IEEE Conference on Computer Communications, Online, 10–13 May 2021. [Google Scholar]
- Yuan, L.; Gong, W. SubScatter: Sub-symbol WiFi Backscatter for High Throughput. In Proceedings of the 2022 IEEE 30th International Conference on Network Protocols (ICNP), Lexington, KY, USA, 30 October–2 November 2022. [Google Scholar]
- Dunna, M.; Meng, M.; Wang, P.; Zhang, C.; Bharadia, D. SyncScatter: Enabling WiFi like synchronization and range for WiFi backscatter Communication. In Proceedings of the 18th USENIX Symposium on Networked Systems Design and Implementation, Boston, MA, USA, 12–14 April 2021. [Google Scholar]
- Jia, Z.; Gong, W.; Liu, J. Spatial stream backscatter using commodity wifi. In Proceedings of the 16th Annual International Conference on Mobile Systems, Applications, and Services, Munich, Germany, 10–15 June 2018. [Google Scholar]
- Zhang, P.; Rostami, M.; Hu, P.; Ganesan, D. Enabling Practical Backscatter Communication for On-body Sensors. In Proceedings of the 2016 ACM SIGCOMM Conference, Florianópolis, Brazil, 22–26 August 2016. [Google Scholar]
- Li, Y.; Chi, Z.; Liu, X.; Zhu, T. Passive-ZigBee: Enabling ZigBee Communication in IoT Networks with 1000X+ Less Power Consumption. In Proceedings of the 16th ACM Conference on Embedded Networked Sensor Systems, Shenzhen, China, 4–7 April 2018. [Google Scholar]
- Peng, Y.; Shangguan, L.; Hu, Y.; Qian, Y.; Lin, X.; Chen, X.; Fang, D.; Jamieson, K. PLoRa: A passive long-range data network from ambient LoRa transmissions. In Proceedings of the 2018 Conference of the ACM Special Interest Group on Data Communication, Budapest, Hungary, 20–25 August 2018. [Google Scholar]
- Iyer, V.; Talla, V.; Kellogg, B.; Gollakota, S.; Smith, J. Inter-Technology Backscatter: Towards Internet Connectivity for Implanted Devices. In Proceedings of the 2016 ACM SIGCOMM Conference, Florianópolis, Brazil, 22–26 August 2016. [Google Scholar]
- Zhang, M.; Zhao, J.; Chen, S.; Gong, W. Reliable Backscatter with Commodity BLE. In Proceedings of the IEEE INFOCOM 2020-IEEE Conference on Computer Communications, Online, 6–9 July 2020. [Google Scholar]
- Kim, T.; Lee, W. AnyScatter: Eliminating Technology Dependency in Ambient Backscatter Systems. In Proceedings of the IEEE INFOCOM 2020-IEEE Conference on Computer Communications, Online, 6–9 July 2020. [Google Scholar]
- Huang, Z.; Gong, W. EAScatter: Excitor-Aware Bluetooth Backscatter. In Proceedings of the 2022 IEEE/ACM 30th International Symposium on Quality of Service (IWQoS), Oslo, Norway, 10–12 June 2022. [Google Scholar]
- Kellogg, B.; Parks, A.; Gollakota, S.; Smith, J.R.; Wetherall, D. Wi-fi backscatter: Internet connectivity for RF-powered devices. In Proceedings of the 2014 ACM Conference on SIGCOMM, Chicago, IL, USA, 17–22 August 2014. [Google Scholar]
- Bharadia, D.; Joshi, K.R.; Kotaru, M.; Katti, S. BackFi: High Throughput WiFi Backscatter. In Proceedings of the ACM SIGCOMM 2015 Conference, London, UK, 17–21 August 2015. [Google Scholar]
- Kellogg, B.; Talla, V.; Smith, J.R.; Gollakot, S. PASSIVE WI-FI: Bringing Low Power to Wi-Fi Transmissions. In Proceedings of the 13th USENIX Symposium on Networked Systems Design and Implementation (NSDI ’16), Santa Clara, CA, USA, 16–18 March 2016. [Google Scholar]
- Zhang, P.; Bharadia, D.; Joshi, K.; Katti, S. Hitchhike: Practical backscatter using commodity WiFi. In Proceedings of the 14th ACM Conference on Embedded Network Sensor Systems CD-ROM, Stanford, CA, USA, 14–16 November 2016. [Google Scholar]
- Zhang, P.; Josephson, C.; Bharadia, D.; Katti, S. Freerider: Backscatter communication using commodity radios. In Proceedings of the 13th International Conference on emerging Networking EXperiments and Technologies, Seoul/Incheon, Republic of Korea, 12–15 December 2017. [Google Scholar]
- Talla, V.; Hessar, M.; Kellogg, B.; Najafi, A.; Smith, J.R.; Gollakota, S. LoRa Backscatter: Enabling The Vision of Ubiquitous Connectivity. In Proceedings of the ACM on Interactive, Mobile, Wearable and Ubiquitous Technologies, Maui, HI, USA, 11–15 September 2017. [Google Scholar]
- Li, D. Two Birds With One Stone: Exploiting Decode-and-Forward Relaying for Opportunistic Ambient Backscattering. IEEE Trans. Commun. 2020, 68, 1405–1416. [Google Scholar] [CrossRef]
- Li, D. Hybrid Active and Passive Antenna Selection for Backscatter-Assisted MISO Systems. IEEE Trans. Commun. 2020, 68, 7258–7269. [Google Scholar] [CrossRef]
- Liu, V.; Parks, A.; Talla, V.; Gollakota, S.; Wetherall, D.; Smith, J.R. Ambient backscatter: Wireless communication out of thin air. In Proceedings of the ACM SIGCOMM 2013 Conference, Hong Kong, China, 12–16 August 2013. [Google Scholar]
- Stigge, M.; Plötz, H.; Müller, W.; Redlich, J. Reversing CRC—Theory and Practice; Humboldt University Berlin: Berlin, Germany, 2006. [Google Scholar]

| Tag Bit | Phase Offset |
|---|---|
| 0 | 0 |
| 1 | 180° |
| Tag Data Length N (Bit) | Brute-Force Search (s) | CRC Reverse Algorithm (s) |
|---|---|---|
| 4 | 0.0026 | 0.0104 |
| 6 | 0.0049 | 0.0095 |
| 8 | 0.0194 | 0.0103 |
| 10 | 0.0586 | 0.0110 |
| 12 | 0.224 | 0.0118 |
| 14 | 0.896 | 0.0099 |
| 16 | 3.529 | 0.0111 |
| 18 | 38.707 | 0.0097 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2023 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Liu, Y.-H.; Liu, T.; Huang, Y.; Ding, H.; Xi, W.; Gong, W. CRC-Based Reliable WiFi Backscatter Communiation for Supply Chain Management. Appl. Sci. 2023, 13, 5471. https://doi.org/10.3390/app13095471
Liu Y-H, Liu T, Huang Y, Ding H, Xi W, Gong W. CRC-Based Reliable WiFi Backscatter Communiation for Supply Chain Management. Applied Sciences. 2023; 13(9):5471. https://doi.org/10.3390/app13095471
Chicago/Turabian StyleLiu, Yun-Hao, Tao Liu, Yimeng Huang, Han Ding, Wei Xi, and Wei Gong. 2023. "CRC-Based Reliable WiFi Backscatter Communiation for Supply Chain Management" Applied Sciences 13, no. 9: 5471. https://doi.org/10.3390/app13095471
APA StyleLiu, Y.-H., Liu, T., Huang, Y., Ding, H., Xi, W., & Gong, W. (2023). CRC-Based Reliable WiFi Backscatter Communiation for Supply Chain Management. Applied Sciences, 13(9), 5471. https://doi.org/10.3390/app13095471







