E-APTDetect: Early Advanced Persistent Threat Detection in Critical Infrastructures with Dynamic Attestation
Abstract
1. Introduction
- A new approach for the detection of APTs that leverages dynamic attestation;
- Reduced time for APT detection in the context of steady-state processes;
- Example computation of mass functions for the application of the Dempster-Shafer’s theory of evidence, and computation of the adversary’s advantage;
- Extensive experimental results that leverage the VAM process.
2. Related Work
3. Materials and Methods
3.1. Overview
3.2. Dynamic Attestation
3.2.1. System Dynamics and Sensitivity Analysis
3.2.2. Developed Dynamic Attestation
3.3. Two-Level Decision Fusion System
3.3.1. Dempster-Shaffer Theory of Evidence
3.3.2. Decision Fusion
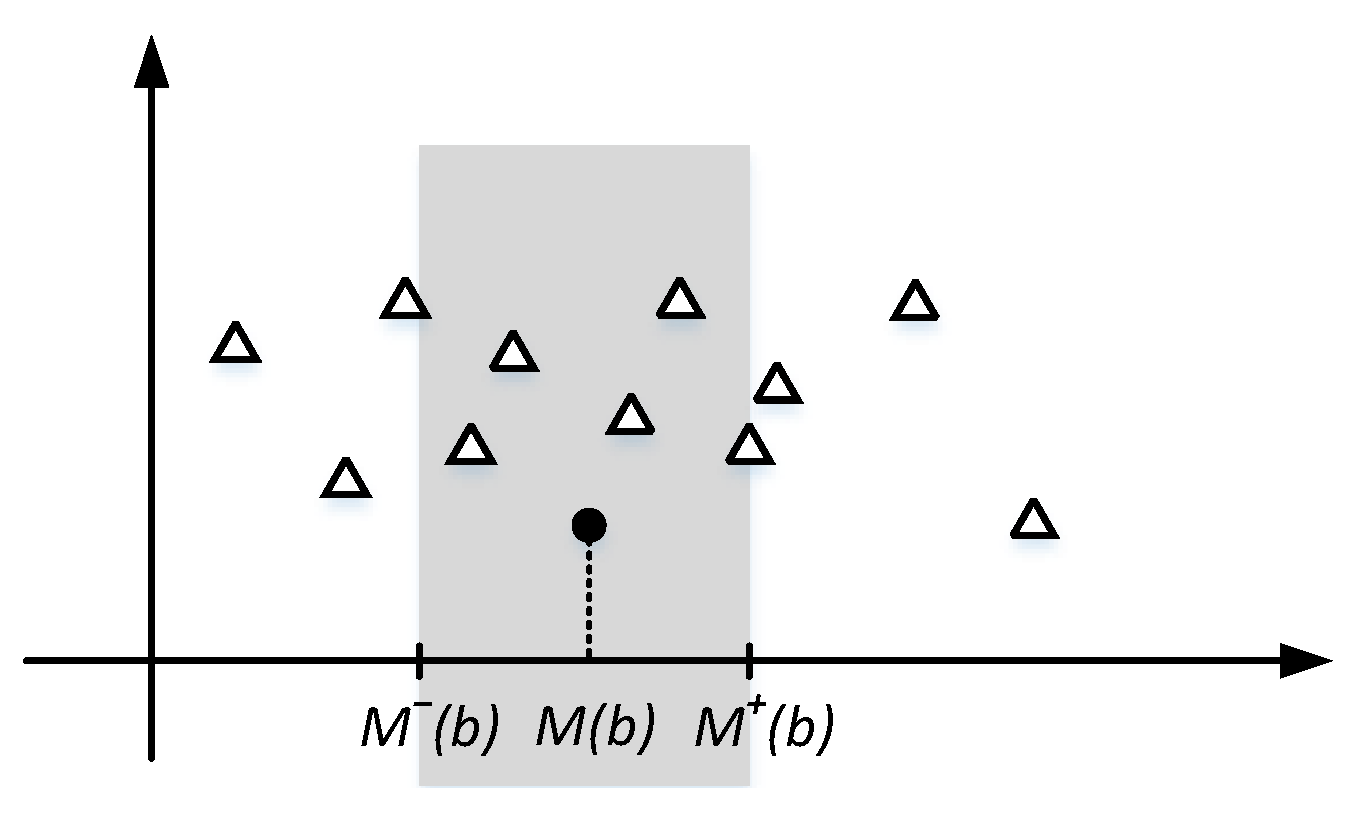
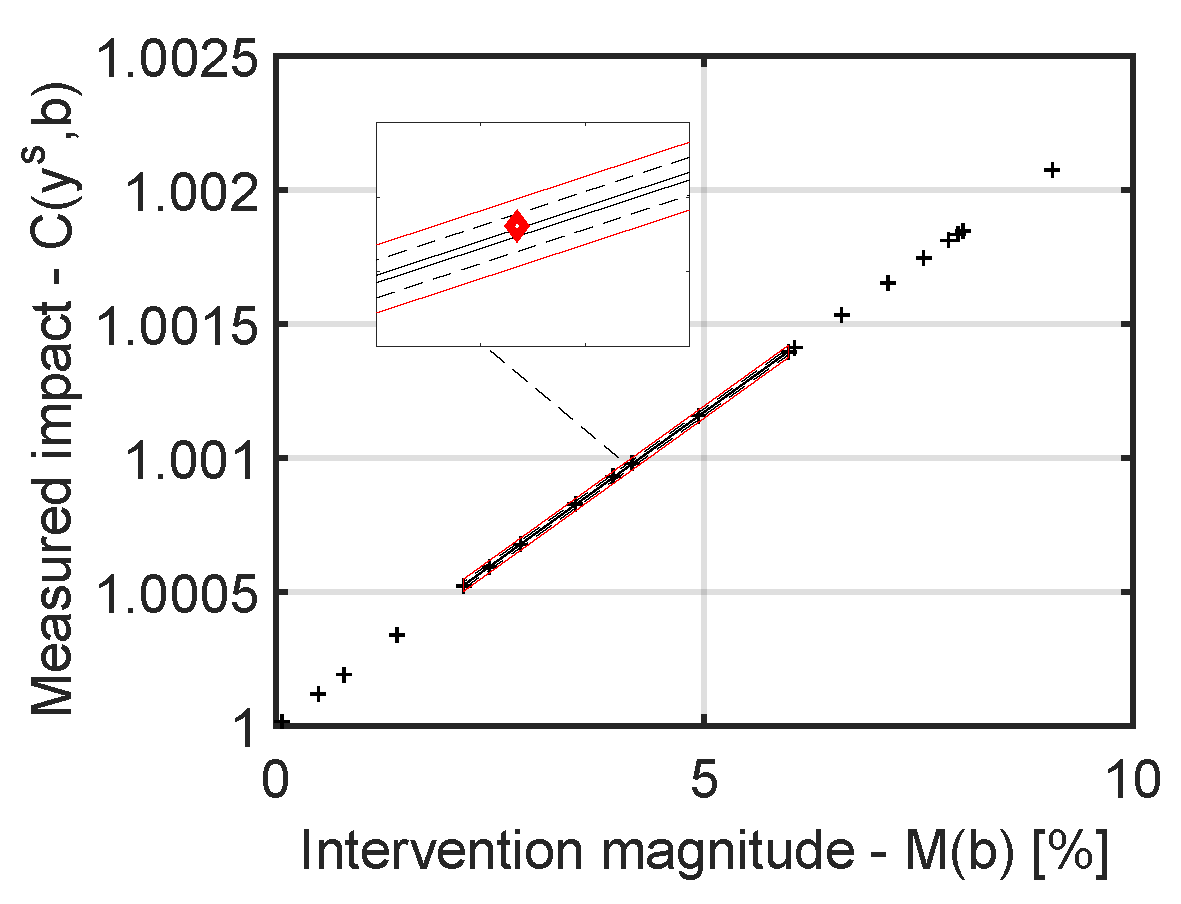
- Step 1. For a new behaviour that is to be attested, let denote the magnitude of the intervention, and the computed impact. The value of can be computed in various ways, a straightforward approach would be the sum of deviations of control variable values from their mean values. In other cases (e.g., where timing is relevant for instance), a combination of the timing of applying interventions on control variables, and their deviation, could also be used for this purpose. Next, to establish the value of k, we first assume that the magnitude of the attested intervention is comparable with apriorily learned neighbouring interventions. Accordingly, and, by leveraging expert knowledge on the attested infrastructure, the lower and upper bounds of () are determined (see Figure 2). Then, the set of relevant points, that is, the set of values to be used in the attestation of this new intervention, is determined according to Equation (8):According to the equation above, k equals the number of elements in .
- Step 2. In the next phase, the coordinates of the centroid C given by the values in are determined:
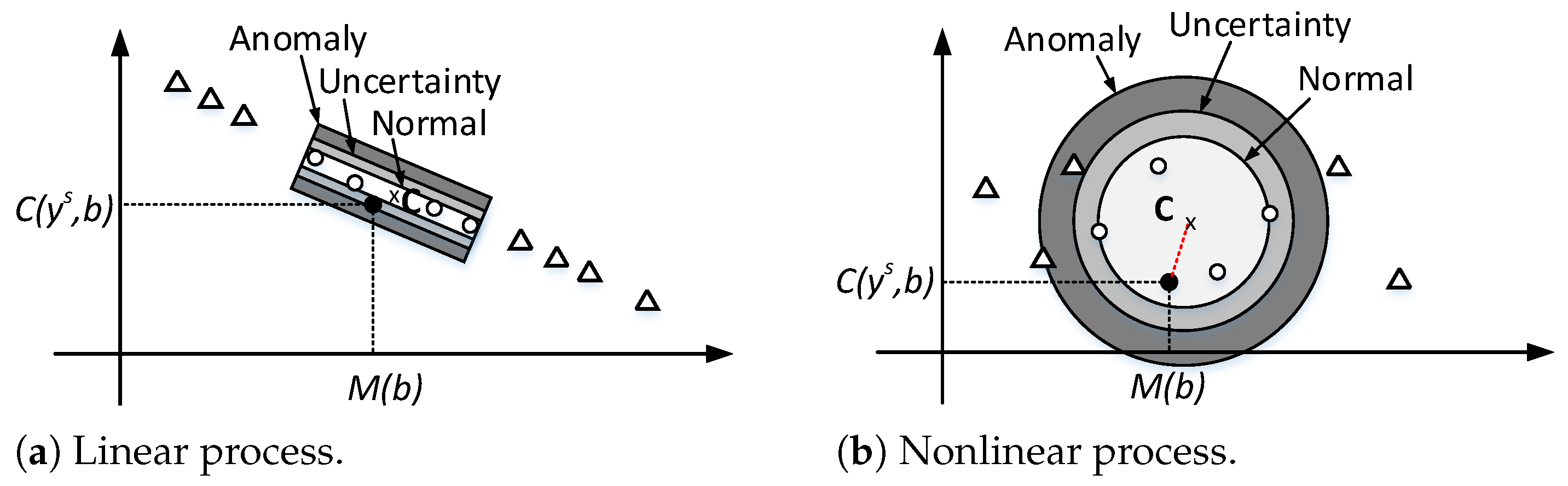
- Step 3. This last step determines the values for the mass functions for each hypothesis H. Unfortunately, various types of processes exhibit different behaviour. Some processes exhibit an approximately linear behaviour (considering possible measurement inaccuracies, and random noise), while others have a nonlinear behaviour. For each case, the estimate of the mass function should be particularly adapted.
3.4. Attestation Cost
3.5. APT Detection Time Reduction
3.6. Analysis on the APT’s Advantage
3.7. Summary of the Attestation Algorithm
| Algorithm 1: Attestation procedure including Level 1 and Level 2 fusion |
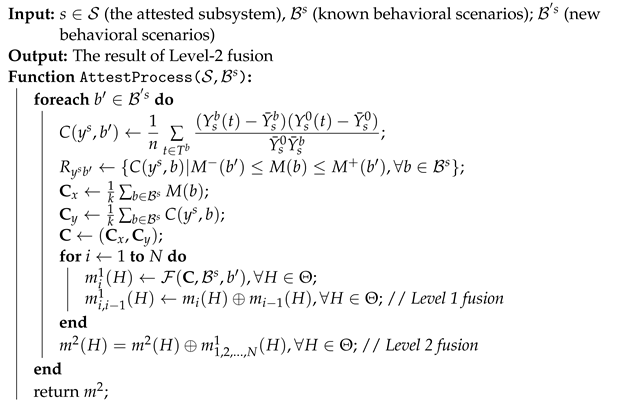 |
4. Results
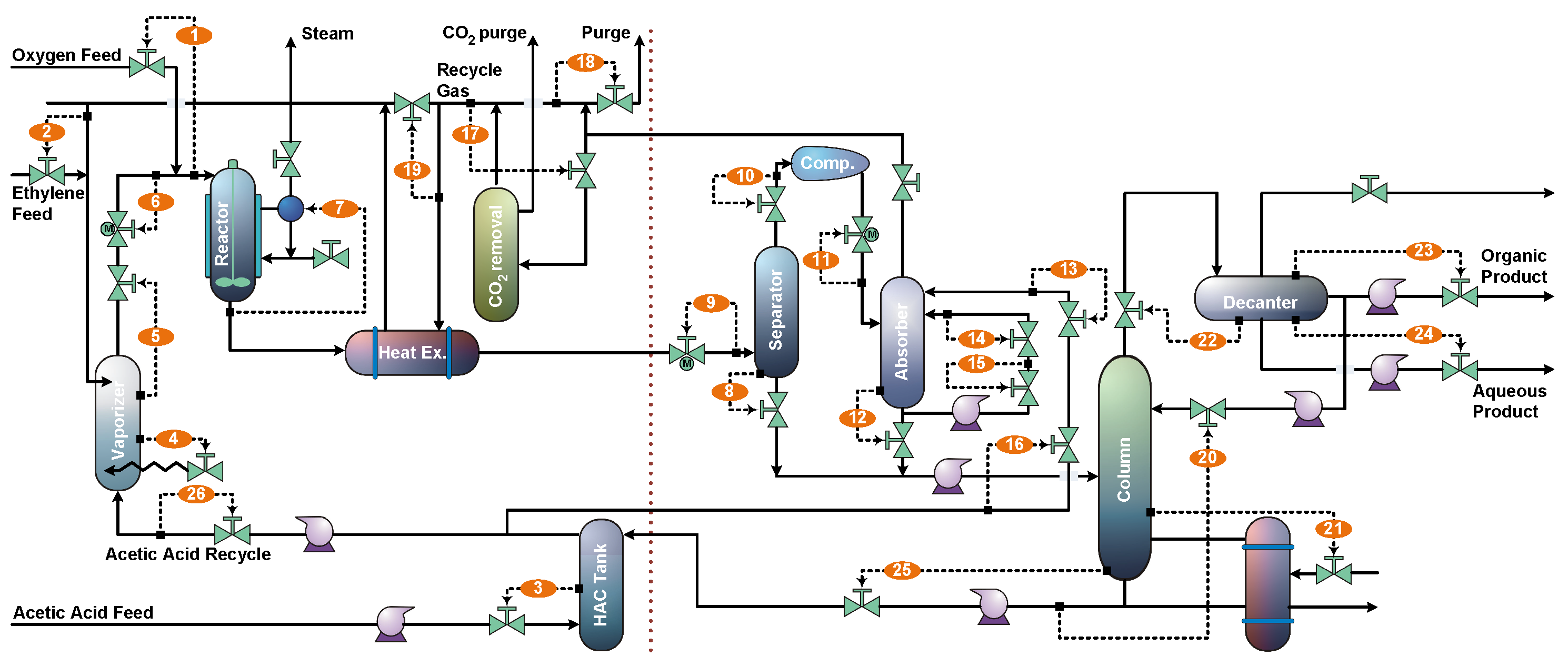
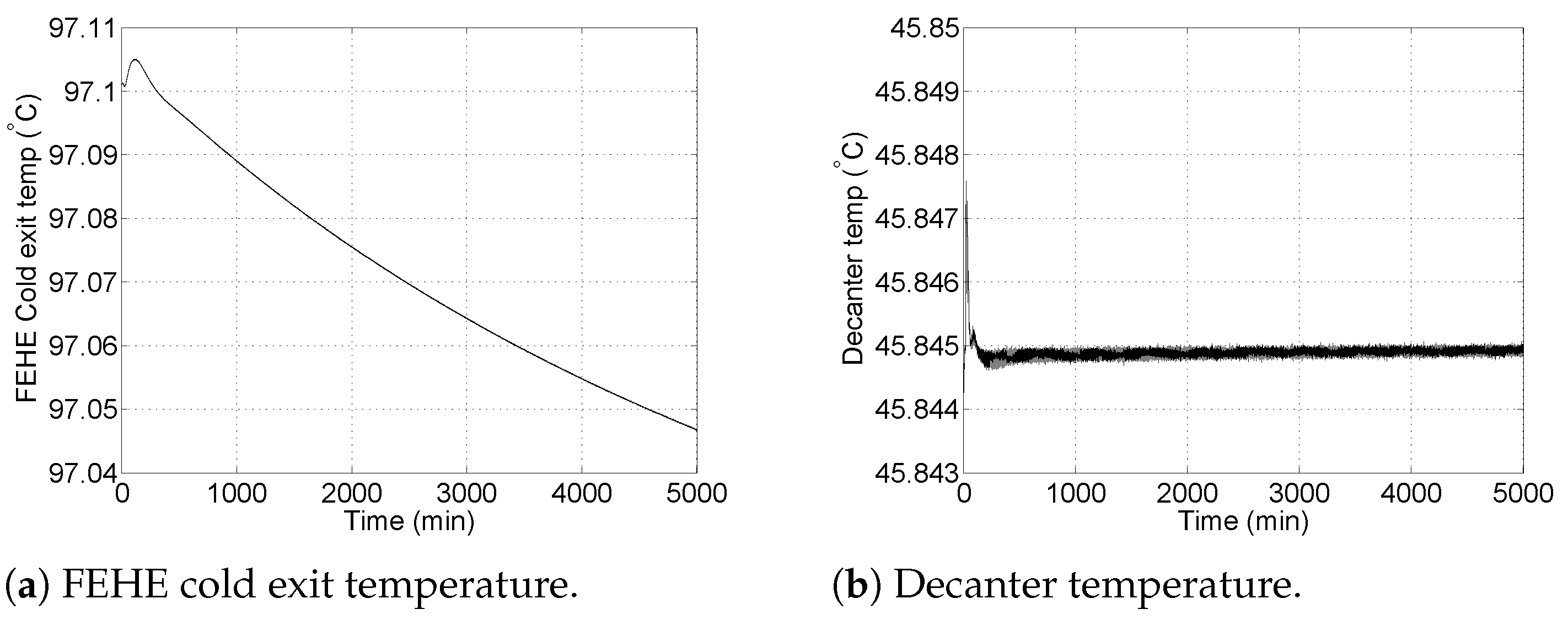
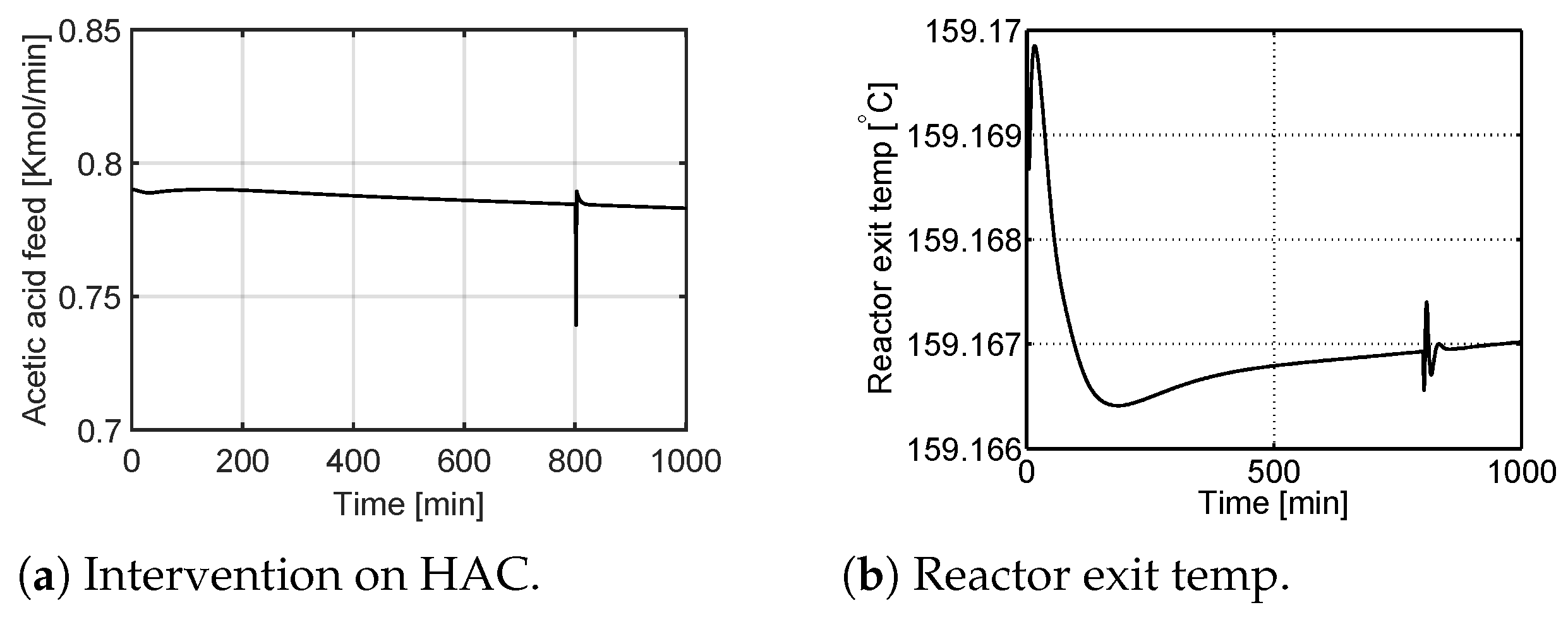
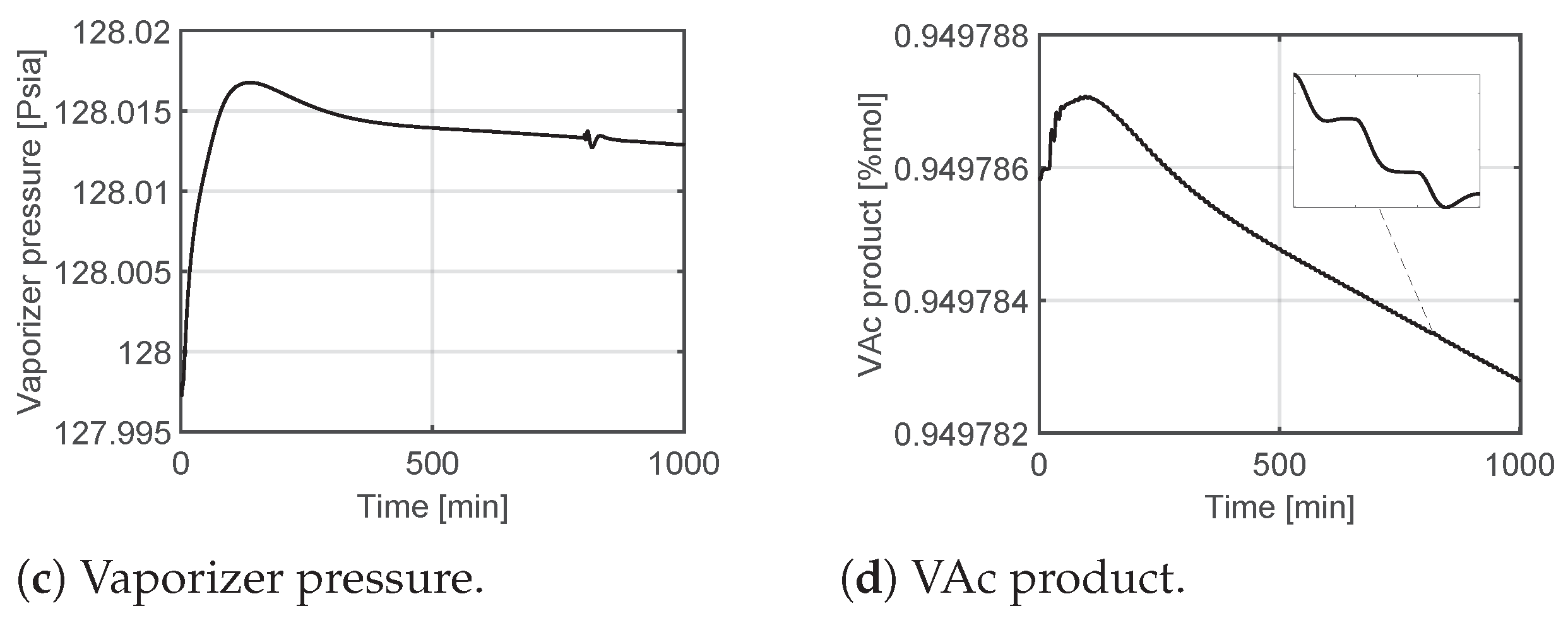
4.1. Process Description
- The oxygen composition must not exceed 8 mol% in the gas recycle loop. This is needed so that the process remains outside the explosivity envelope of ethylene;
- The pressure in the gas recycle loop and distillation column cannot exceed 140 psia because of the mechanical construction limit of the process vessels.
4.2. Scenario Attestation
4.2.1. Scenario Description
4.2.2. Intervention Example
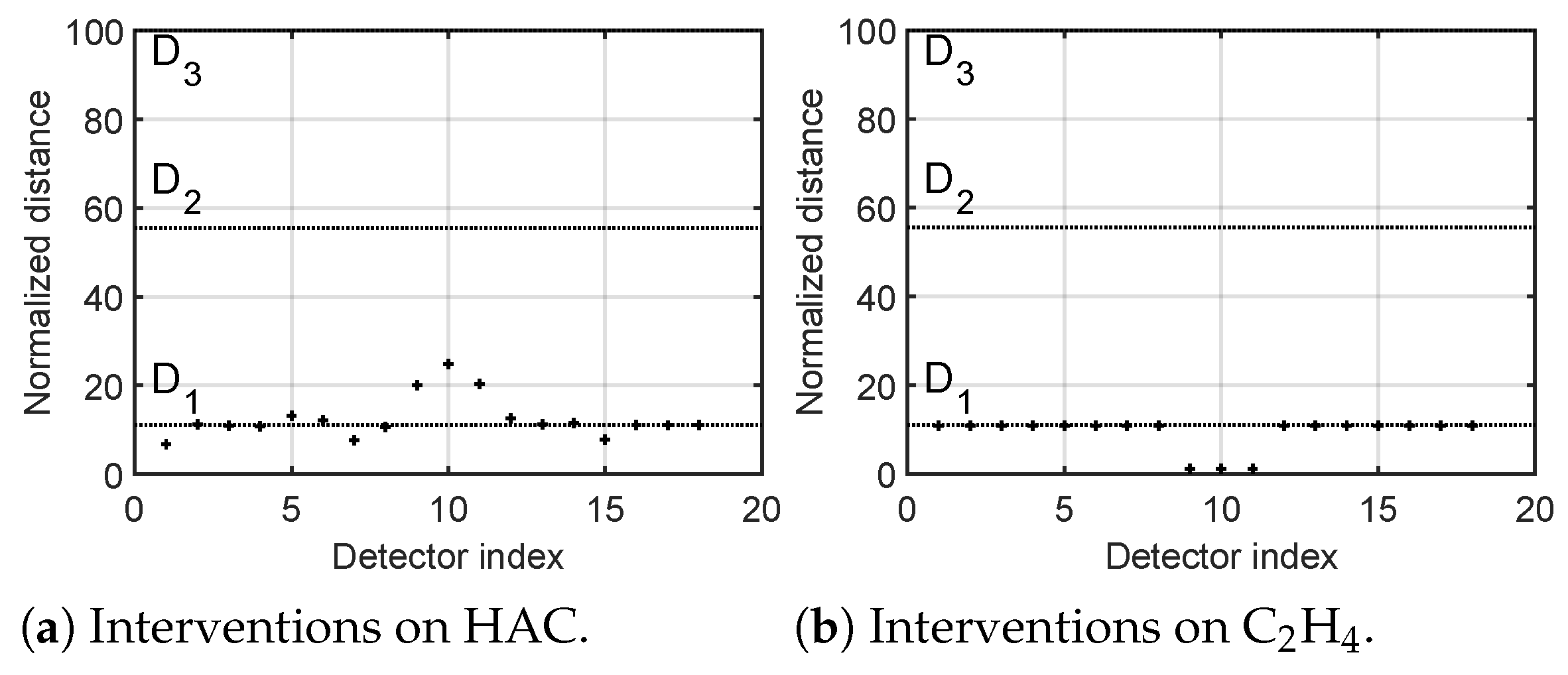
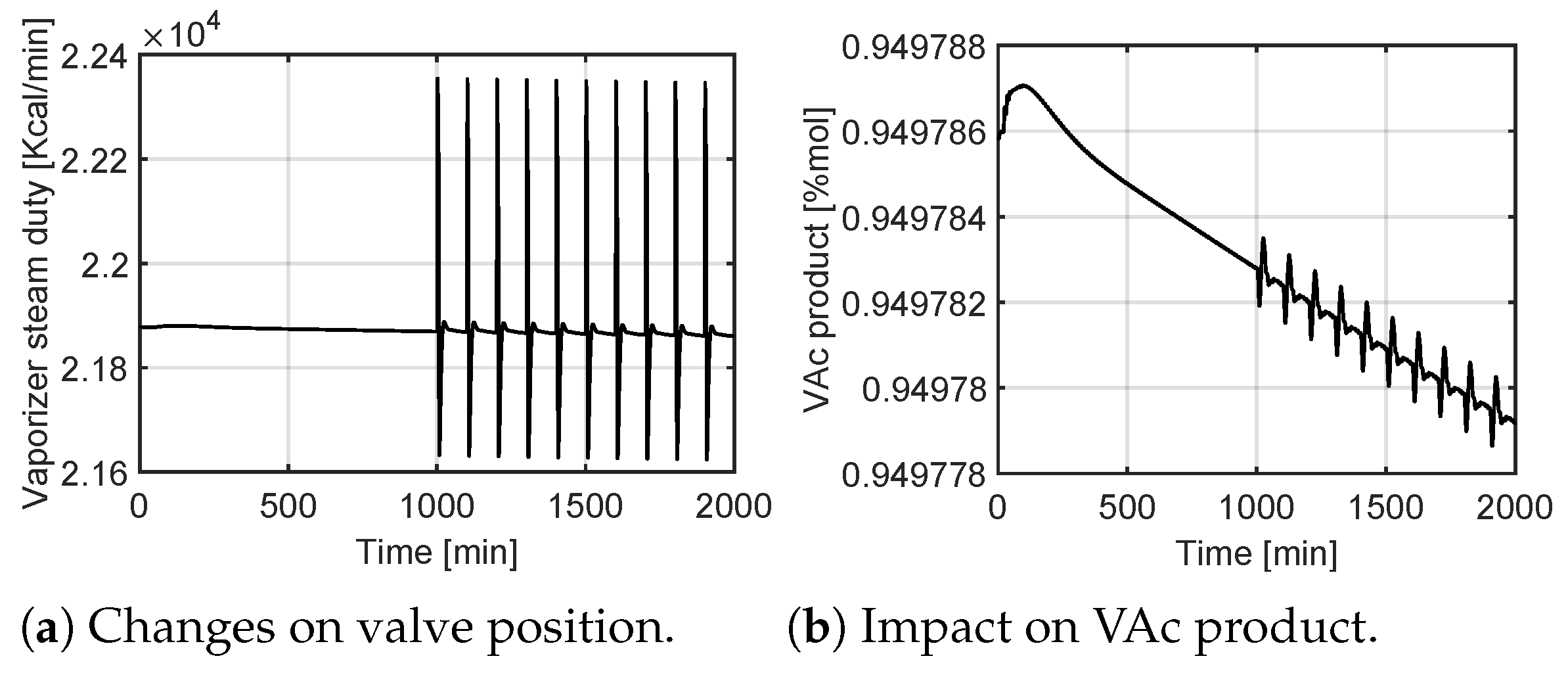
4.2.3. Random Interventions
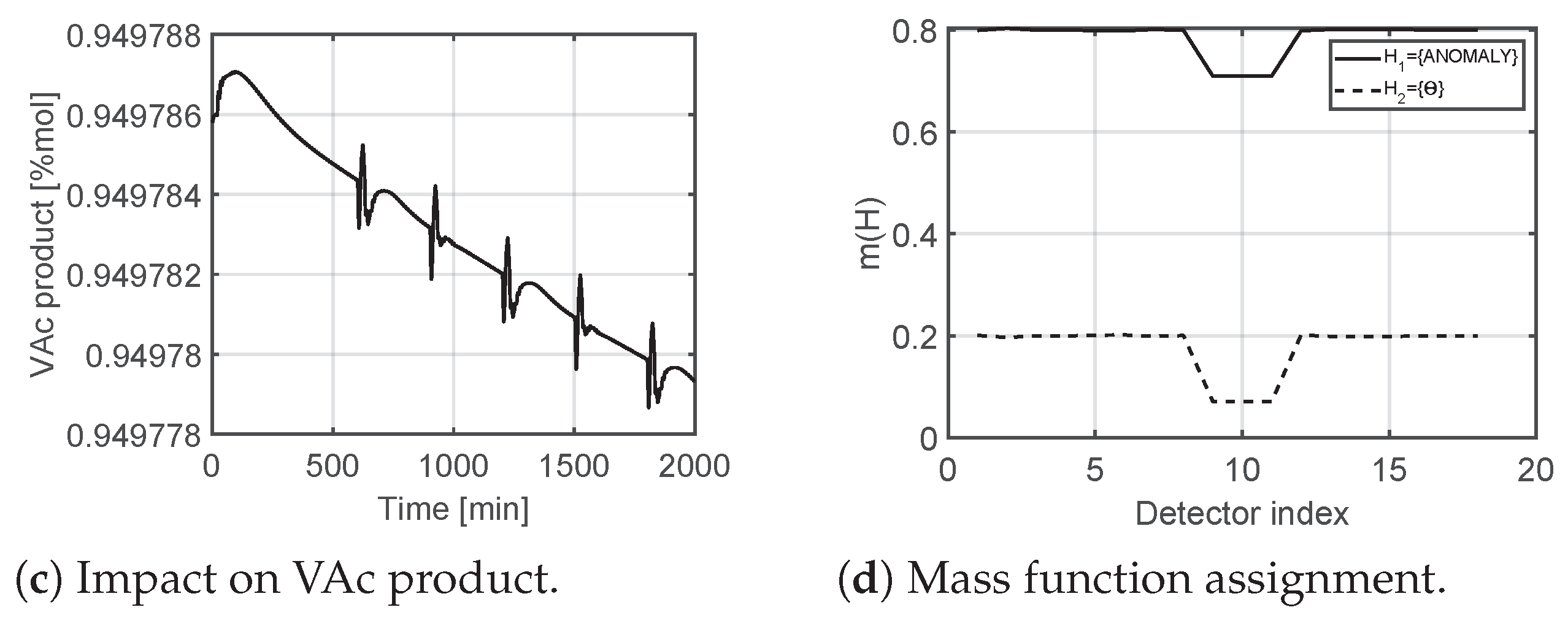
4.2.4. Constructing the Mass Functions
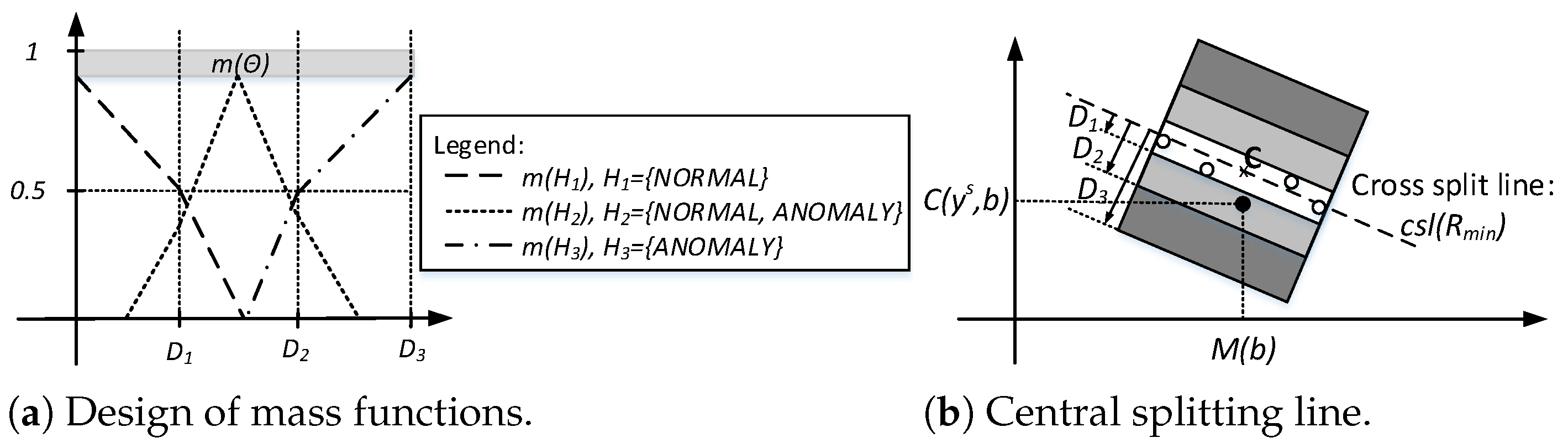
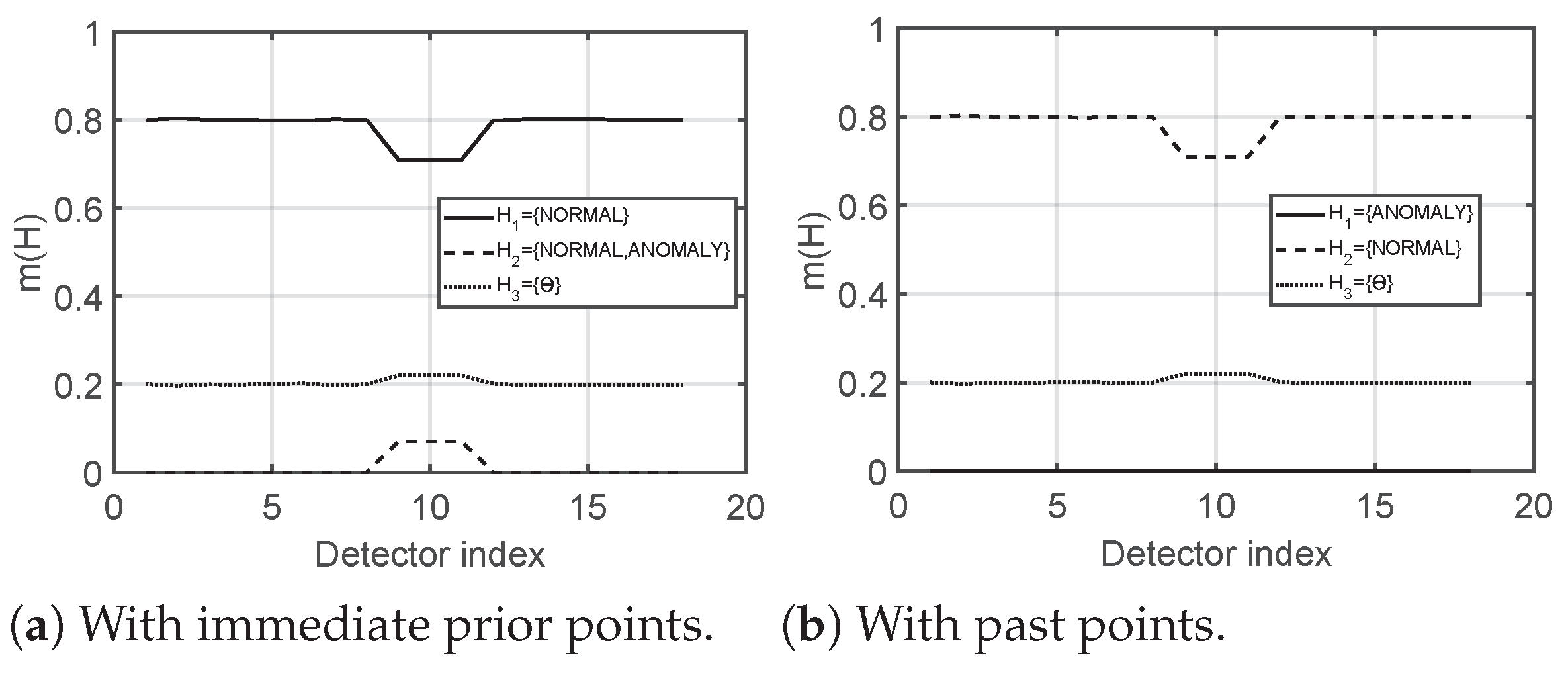
- Case 1. . Two hypothesis are active: = {NORMAL}, and = {NORMAL, ANOMALY}. The rationale for this is that as we move away from the center of the level of confidence in a normal state decreases, and, at the same time, we experience an increase in the level of uncertainty. In this case, the uncertainty is that the detector cannot distinguish between a normal and anomalous state.
- Case 2. . Three hypothesis are active: = {NORMAL}, = {NORMAL, ANOMALY}, and = {ANOMALY}. The rationale behind this decision is that, as we move further from , we experience a decrease in the confidence of normality, while experiencing an increased confidence in uncertainty. Subsequently, starting from the middle of this interval the confidence in uncertainty begins to decrease as we proceed toward the limit. At the same time, the confidence assigned to an anomalous state begins to increase as we approach .
- Case 3. . Two hypothesis are active: = {NORMAL, ANOMALY}, and = {ANOMALY}. Similarly to the previous two cases, the rationale is that we experience a continuous decrease in the confidence in uncertainty, and, as we proceed towards the level of confidence increases for an anomalous state.
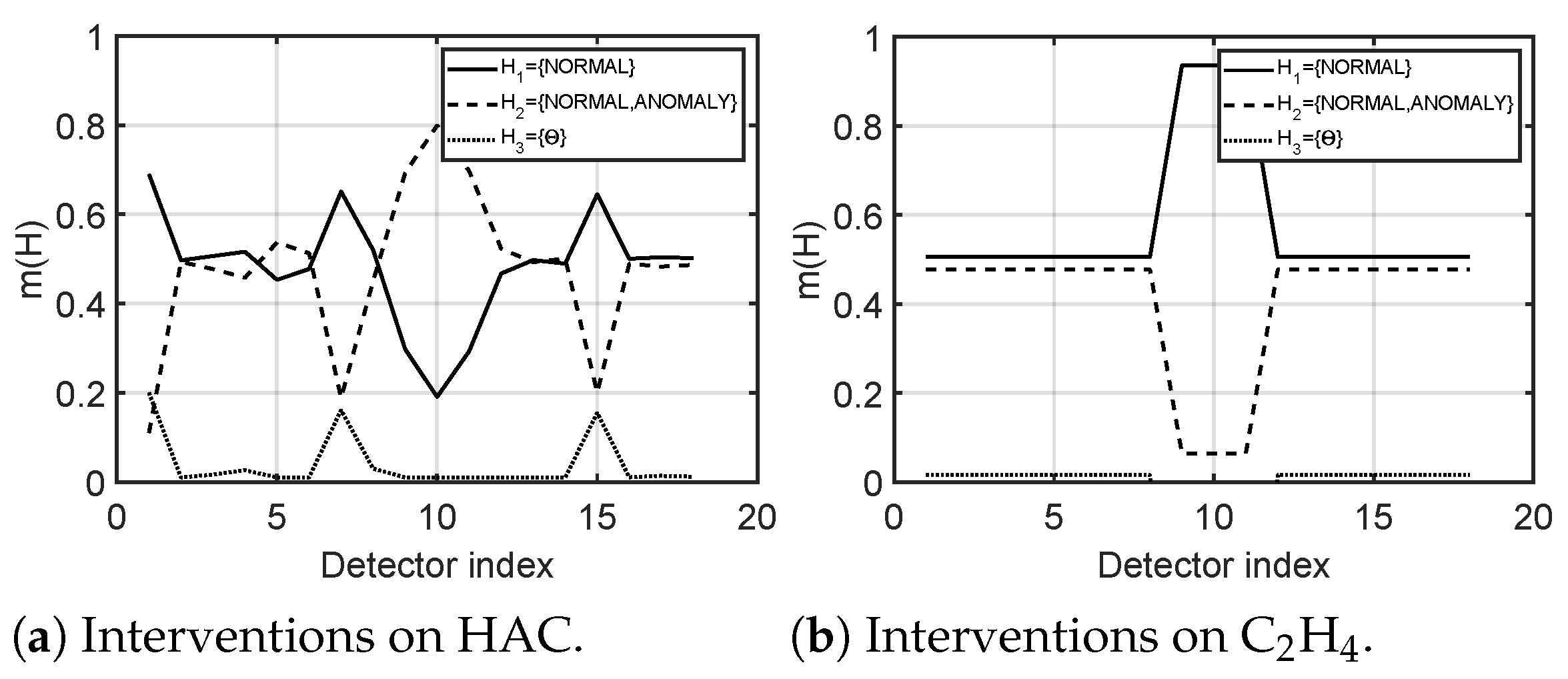
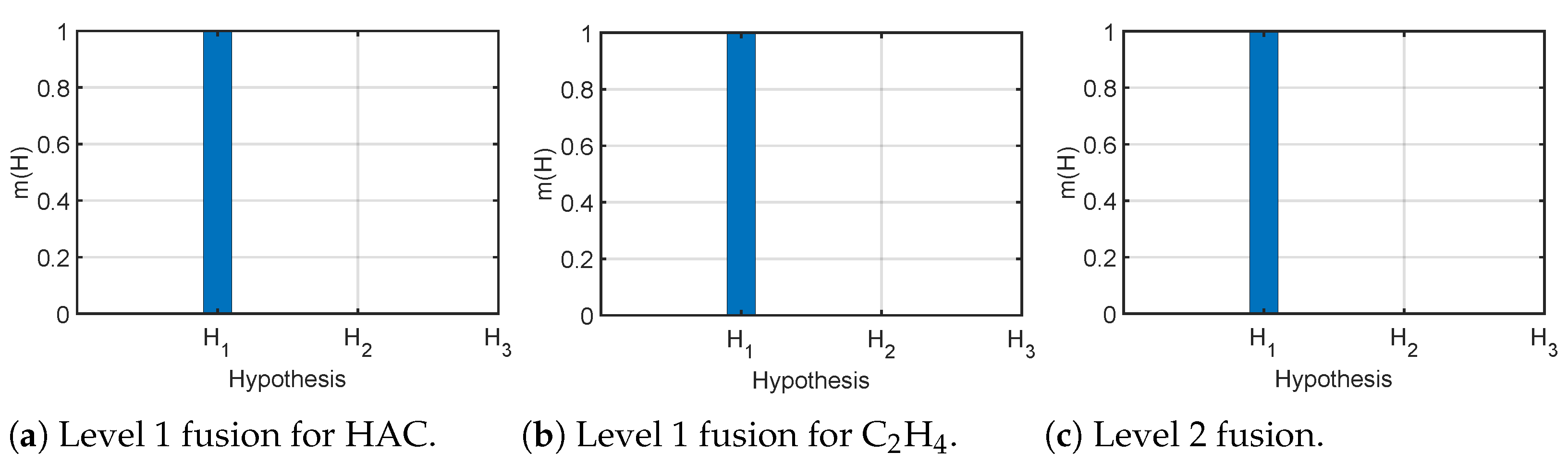
4.2.5. Level 1 and Level 2 Fusion
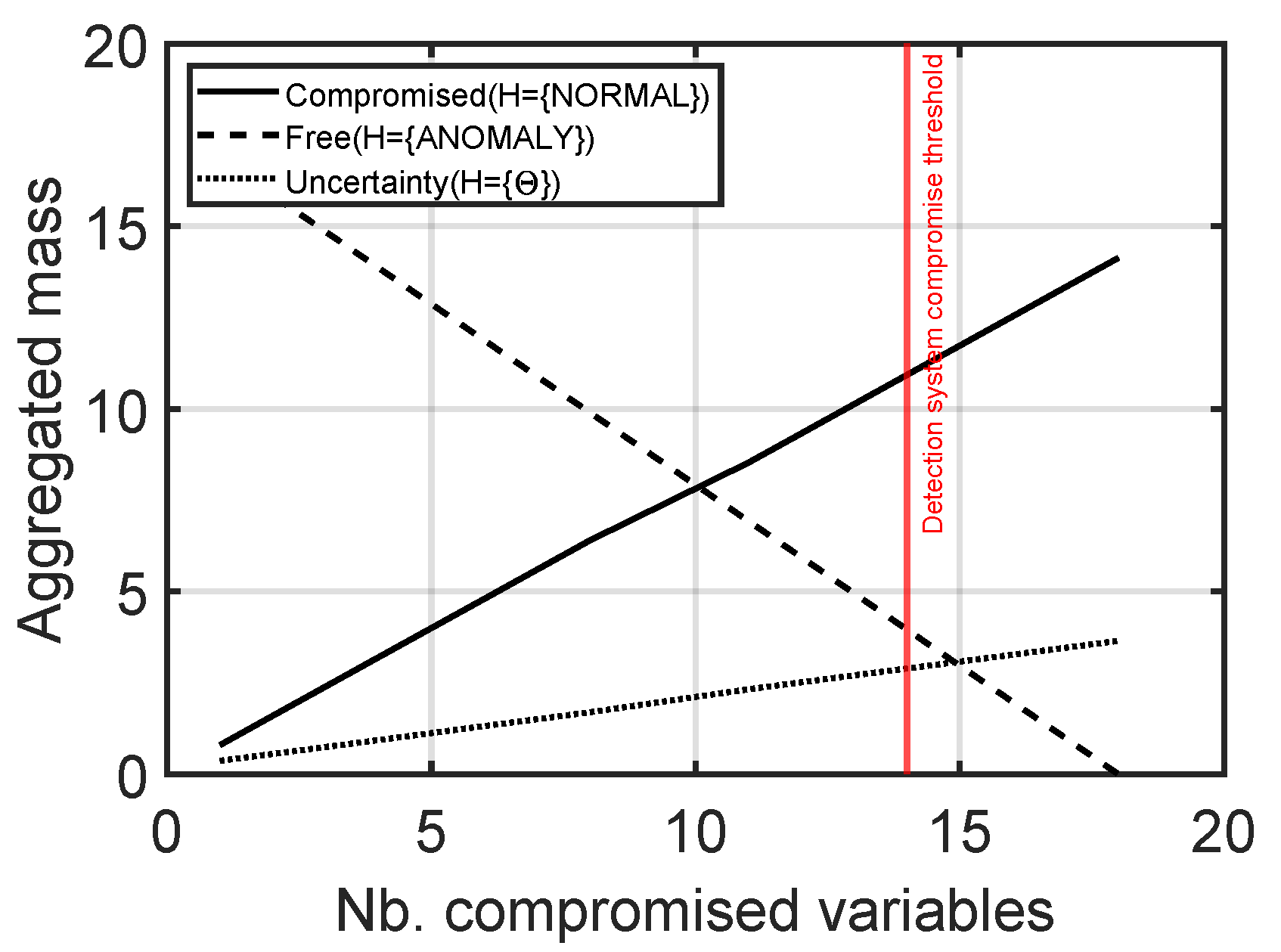
4.3. APT Detection
4.4. Discussion
5. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Data Availability Statement
Conflicts of Interest
References
- Hagerott, M. Stuxnet and the vital role of critical infrastructure operators and engineers. Int. J. Crit. Infrastruct. Prot. 2014, 7, 244–246. [Google Scholar] [CrossRef]
- Turton, W.; Mehrotra, K. Hackers Breached Colonial Pipeline Using Compromised Password. 2021. Available online: https://www.bloomberg.com/news/articles/2021-06-04/hackers-breached-colonial-pipeline-using-compromised-password (accessed on 5 March 2023).
- MacKenzie, H. How Dragonfly Hackers and RAT Malware Threaten ICS Security. 2014. Available online: https://www.belden.com/blogs/industrial-security/how-dragonfly-hackers-and-rat-malware-threaten-ics-security (accessed on 5 March 2023).
- Genge, B.; Graur, F.; Haller, P. Experimental assessment of network design approaches for protecting industrial control systems. Int. J. Crit. Infrastruct. Prot. 2015, 11, 24–38. [Google Scholar] [CrossRef]
- Alshamrani, A.; Myneni, S.; Chowdhary, A.; Huang, D. A Survey on Advanced Persistent Threats: Techniques, Solutions, Challenges, and Research Opportunities. IEEE Commun. Surv. Tutor. 2019, 21, 1851–1877. [Google Scholar] [CrossRef]
- Bolboacă, R. Adaptive Ensemble Methods for Tampering Detection in Automotive Aftertreatment Systems. IEEE Access 2022, 10, 105497–105517. [Google Scholar] [CrossRef]
- Huang, L.; Zhu, Q. A dynamic games approach to proactive defense strategies against Advanced Persistent Threats in cyber-physical systems. Comput. Secur. 2020, 89, 101660. [Google Scholar] [CrossRef]
- Rubio, J.E.; Roman, R.; Alcaraz, C.; Zhang, Y. Tracking Advanced Persistent Threats in Critical Infrastructures Through Opinion Dynamics. In Proceedings of the European Symposium on Research in Computer Security, ESORICS 2018, Barcelona, Spain, 3–7 September 2018; Lopez, J., Zhou, J., Soriano, M., Eds.; Springer International Publishing: Cham, Switzerland, 2018; pp. 555–574. [Google Scholar] [CrossRef]
- Rubio, J.E.; Roman, R.; Lopez, J. Integration of a Threat Traceability Solution in the Industrial Internet of Things. IEEE Trans. Ind. Inform. 2020, 16, 6575–6583. [Google Scholar] [CrossRef]
- Neuschmied, H.; Winter, M.; Stojanović, B.; Hofer-Schmitz, K.; Božić, J.; Kleb, U. APT-Attack Detection Based on Multi-Stage Autoencoders. Appl. Sci. 2022, 12, 6816. [Google Scholar] [CrossRef]
- Sathya, M.; Jeyaselvi, M.; Krishnasamy, L.; Hazzazi, M.M.; Shukla, P.K.; Shukla, P.K.; Nuagah, S.J. A novel, efficient, and secure anomaly detection technique using DWU-ODBN for IoT-enabled multimedia communication systems. Wirel. Commun. Mob. Comput. 2021, 2021, 4989410. [Google Scholar] [CrossRef]
- Forrester, J.W. Counterintuitive behavior of social systems. Theory Decis. 1971, 2, 109–140. [Google Scholar] [CrossRef]
- Genge, B.; Kiss, I.; Haller, P. A system dynamics approach for assessing the impact of cyber attacks on critical infrastructures. Int. J. Crit. Infrastruct. Prot. 2015, 10, 3–17. [Google Scholar] [CrossRef]
- Luyben, M.L.; Tyreus, B.D. An industrial design/control study for the vinyl acetate monomer process. Comput. Chem. Eng. 1998, 22, 867–877. [Google Scholar] [CrossRef]
- Filippini, R.; Silva, A. A modeling framework for the resilience analysis of networked systems-of-systems based on functional dependencies. Reliab. Eng. Syst. Saf. 2014, 125, 82–91. [Google Scholar] [CrossRef]
- Giani, A.; Bent, R.; Pan, F. Phasor measurement unit selection for unobservable electric power data integrity attack detection. Int. J. Crit. Infrastruct. Prot. 2014, 7, 155–164. [Google Scholar] [CrossRef]
- Rubio, J.E.; Alcaraz, C.; Roman, R.; Lopez, J. Analysis of Intrusion Detection Systems in Industrial Ecosystems. In Proceedings of the 14th International Joint Conference on e-Business and Telecommunications (ICETE 2017)—Volume 4: SECRYPT, Madrid, Spain, 24–26 July 2017; pp. 116–128. [Google Scholar] [CrossRef]
- Cárdenas, A.; Amin, S.; Lin, Z.; Huang, Y.; Huang, C.; Sastry, S. Attacks against process control systems: Risk assessment, detection, and response. In Proceedings of the 6th ACM Symposium on Information, Computer and Communications Security, ASIACCS 2011, Hong Kong, China, 22–24 March 2011; pp. 355–366. [Google Scholar] [CrossRef]
- Giraldo, J.; Cardenas, A.; Quijano, N. Integrity Attacks on Real-Time Pricing in Smart Grids: Impact and Countermeasures. IEEE Trans. Smart Grid 2017, 8, 2249–2257. [Google Scholar] [CrossRef]
- Carcano, A.; Coletta, A.; Guglielmi, M.; Masera, M.; Fovino, I.N.; Trombetta, A. A Multidimensional Critical State Analysis for Detecting Intrusions in SCADA Systems. IEEE Trans. Ind. Inform. 2011, 7, 179–186. [Google Scholar] [CrossRef]
- Fovino, I.N.; Coletta, A.; Carcano, A.; Masera, M. Critical State-Based Filtering System for Securing SCADA Network Protocols. IEEE Trans. Ind. Electron. 2012, 59, 3943–3950. [Google Scholar] [CrossRef]
- Kiss, I.; Genge, B.; Haller, P.; Sebestyén, G. Data clustering-based anomaly detection in industrial control systems. In Proceedings of the 2014 IEEE 10th International Conference on Intelligent Computer Communication and Processing (ICCP), Cluj-Napoca, Romania, 4–6 September 2014; pp. 275–281. [Google Scholar] [CrossRef]
- Wang, B.; Mao, Z. One-class classifiers ensemble based anomaly detection scheme for process control systems. Trans. Inst. Meas. Control 2018, 40, 3466–3476. [Google Scholar] [CrossRef]
- Ha, D.; Ahmed, U.; Pyun, H.; Lee, C.J.; Baek, K.H.; Han, C. Multi-mode operation of principal component analysis with k-nearest neighbor algorithm to monitor compressors for liquefied natural gas mixed refrigerant processes. Comput. Chem. Eng. 2017, 106, 96–105. [Google Scholar] [CrossRef]
- Portnoy, I.; Melendez, K.; Pinzon, H.; Sanjuan, M. An improved weighted recursive PCA algorithm for adaptive fault detection. Control Eng. Pract. 2016, 50, 69–83. [Google Scholar] [CrossRef]
- Chen, B.; Ho, D.W.C.; Zhang, W.A.; Yu, L. Distributed Dimensionality Reduction Fusion Estimation for Cyber-Physical Systems Under DoS Attacks. IEEE Trans. Syst. Man Cybern. Syst. 2017, 49, 455–468. [Google Scholar] [CrossRef]
- Genge, B.; Haller, P.; Enăchescu, C. Anomaly Detection in Aging Industrial Internet of Things. IEEE Access 2019, 7, 74217–74230. [Google Scholar] [CrossRef]
- Enăchescu, C.; Sándor, H.; Genge, B. A Multi-Model-based Approach to Detect Cyber Stealth Attacks in Industrial Internet of Things. In Proceedings of the 2019 International Conference on Software, Telecommunications and Computer Networks (SoftCOM), Split, Croatia, 19–21 September 2019; pp. 1–6. [Google Scholar] [CrossRef]
- Zhao, J.; Zhang, G.; Jabr, R.A. Robust Detection of Cyber Attacks on State Estimators Using Phasor Measurements. IEEE Trans. Power Syst. 2017, 32, 2468–2470. [Google Scholar] [CrossRef]
- Shoukry, Y.; Nuzzo, P.; Puggelli, A.; Sangiovanni-Vincentelli, A.L.; Seshia, S.A.; Tabuada, P. Secure State Estimation for Cyber-Physical Systems under Sensor Attacks: A Satisfiability Modulo Theory Approach. IEEE Trans. Autom. Control 2017, 62, 4917–4932. [Google Scholar] [CrossRef]
- Huang, L.; Zhu, Q. Adaptive Strategic Cyber Defense for Advanced Persistent Threats in Critical Infrastructure Networks. ACM SIGMETRICS Perform. Eval. Rev. 2019, 46, 52–56. [Google Scholar] [CrossRef]
- Hassannataj Joloudari, J.; Haderbadi, M.; Mashmool, A.; Ghasemigol, M.; Band, S.S.; Mosavi, A. Early Detection of the Advanced Persistent Threat Attack Using Performance Analysis of Deep Learning. IEEE Access 2020, 8, 186125–186137. [Google Scholar] [CrossRef]
- Javed, S.H.; Ahmad, M.B.; Asif, M.; Almotiri, S.H.; Masood, K.; Ghamdi, M.A.A. An Intelligent System to Detect Advanced Persistent Threats in Industrial Internet of Things (I-IoT). Electronics 2022, 11, 742. [Google Scholar] [CrossRef]
- Ghafir, I.; Hammoudeh, M.; Prenosil, V.; Han, L.; Hegarty, R.; Rabie, K.; Aparicio-Navarro, F.J. Detection of advanced persistent threat using machine-learning correlation analysis. Future Gener. Comput. Syst. 2018, 89, 349–359. [Google Scholar] [CrossRef]
- Zimba, A.; Chen, H.; Wang, Z.; Chishimba, M. Modeling and detection of the multi-stages of Advanced Persistent Threats attacks based on semi-supervised learning and complex networks characteristics. Future Gener. Comput. Syst. 2020, 106, 501–517. [Google Scholar] [CrossRef]
- Bell, R.; Åström, K. Dynamic Models for Boiler–Turbine Alternator Units: Data Logs and Parameter Estimation for a 160 MW Unit; Report TFRT–3192; Lundt Institute of Technology: Skåne, Sweden, 1987. [Google Scholar]
- Huang, J.; Howley, E.; Duggan, J. The Ford Method: A Sensitivity Analysis Approach. In Proceedings of the Twenty-Seventh International Conference of the System Dynamics Society, Albuquerque, NM, USA, 26–30 July 2009; pp. 355–366. [Google Scholar]
- Shafer, G. A Mathematical Theory of Evidence; Princeton University Press: Princeton, NJ, USA, 1976. [Google Scholar]
- Chen, R.; Dave, K.; McAvoy, T.J. A Nonlinear Dynamic Model of a Vinyl Acetate Process. Ind. Eng. Chem. Res. 2003, 42, 4478–4487. [Google Scholar] [CrossRef]
- Krotofil, M.; Larsen, J.W. Rocking the pocket book: Hacking chemical plants for competition and extortion. In Proceedings of the BlackHat; 2015. Available online: https://www.blackhat.com/us-15/briefings.html#marina-krotofil (accessed on 5 March 2023).
- Haller, P.; Genge, B.; Forloni, F.; Baldini, G.; Carriero, M.; Fontaras, G. VetaDetect: Vehicle tampering detection with closed-loop model ensemble. Int. J. Crit. Infrastruct. Prot. 2022, 37, 100525. [Google Scholar] [CrossRef]
- Oruc, A.; Gkioulos, V.; Katsikas, S. Towards a Cyber-Physical Range for the Integrated Navigation System (INS). J. Mar. Sci. Eng. 2022, 10, 107. [Google Scholar] [CrossRef]
- Smadi, A.A.; Ajao, B.T.; Johnson, B.K.; Lei, H.; Chakhchoukh, Y.; Abu Al-Haija, Q. A Comprehensive Survey on Cyber-Physical Smart Grid Testbed Architectures: Requirements and Challenges. Electronics 2021, 10, 1043. [Google Scholar] [CrossRef]
- Siaterlis, C.; Genge, B.; Hohenadel, M. EPIC: A Testbed for Scientifically Rigorous Cyber-Physical Security Experimentation. IEEE Trans. Emerg. Top. Comput. 2013, 1, 319–330. [Google Scholar] [CrossRef]




Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2023 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Genge, B.; Haller, P.; Roman, A.-S. E-APTDetect: Early Advanced Persistent Threat Detection in Critical Infrastructures with Dynamic Attestation. Appl. Sci. 2023, 13, 3409. https://doi.org/10.3390/app13063409
Genge B, Haller P, Roman A-S. E-APTDetect: Early Advanced Persistent Threat Detection in Critical Infrastructures with Dynamic Attestation. Applied Sciences. 2023; 13(6):3409. https://doi.org/10.3390/app13063409
Chicago/Turabian StyleGenge, Béla, Piroska Haller, and Adrian-Silviu Roman. 2023. "E-APTDetect: Early Advanced Persistent Threat Detection in Critical Infrastructures with Dynamic Attestation" Applied Sciences 13, no. 6: 3409. https://doi.org/10.3390/app13063409
APA StyleGenge, B., Haller, P., & Roman, A.-S. (2023). E-APTDetect: Early Advanced Persistent Threat Detection in Critical Infrastructures with Dynamic Attestation. Applied Sciences, 13(6), 3409. https://doi.org/10.3390/app13063409








