1. Introduction
The world is constantly developing information and communication technology and infrastructure, and cyberspace is recognized as the core basis for information administration services and the operation of major national infrastructure. With the recent surge in state-based cybercrime and terrorism, systematic cyberattacks are posing serious challenges to national security.
The Department of Defense (DoD) separates cyberspace from other spaces such as land, sea, air, and space, and has announced the DoD Strategy for Operating in Cyberspace, defining cyberspace as the fifth battlefield. Accordingly, the DoD is building a cyber warfare response system [
1]. In addition, JP 3-12 classifies cyberspace operations (CO) as cyber network operations (CNO), defensive cyberspace operations (DCO), and offensive cyberspace operations (OCO) [
2].
As the world has recognized the cyberspace domain as an operational and mission domain in earnest, we have been faced with the current trends in which we need to secure the ability to conduct COs from a macroscopic perspective in order to secure “cyberspace dominance.” The COs conducted by military forces require active and positive cyberspace actions, as well as cyberspace defense. To perform cyber intelligence, surveillance, and reconnaissance (ISR) in an enemy’s cyberspace during peacetime and identify and manage targets, active COs are essentially required. The identified potential targets are recommended through the target development and prioritization process, which is the second stage of the targeting process. In this second stage, basic and intermediate target development is performed, and a list of verified and approved targets is created as a cyber target list. Finally, target priorities must be given.
In this study, a target importance rank (TIR) algorithm based on the PageRank algorithm was used to explain the items to be considered when assigning priorities to the cyber target list and calculating the cyber target importance (CTI) scores for the items to be considered. The TIR algorithm was derived based on the PageRank algorithm to calculate the CTI score. This score is used to suggest a way to assign priorities.
2. Related Works
This section may be divided by subheadings. It should provide a concise and precise description of the experimental results, their interpretation, as well as the experimental conclusions that can be drawn.
2.1. Definition of Cyberspace Operations and Cyber Objects
COs are operations that use cyber-related capabilities to achieve military purposes in cyberspace. Cyber operations are largely divided into CNO, DCO, and OCO. JP 3-12 (2018) [
2] describes cyberspace where COs are performed as three largely interrelated layers, and FM 3-12 (2021) [
3] describes the cyberspace objects of each layer as follows:
The physical network layer consists of IT devices (PCs, servers, routers, etc.) in a physical domain that provide the storage, transmission, and processing of information within cyberspace, including connections between data stores and network components.
The logical network layer consists of logical programming (OS, apps, etc.) that runs network components and network elements related to each other in an abstract manner in a physical network.
A persona network layer is a cyberspace perspective created by using rules applied to the logical network layer to develop digital representations of an individual or an individual’s identity in cyberspace and extract data from the logical network layer. These persona network layers may be directly related to individuals or organizations (e-mails, IP addresses, web pages, phone numbers, SNS accounts, etc.) by integrating some personal or organizational data (e-mails, IP addresses, social media accounts, etc.).
2.2. Definition of Cyber Target and Cyber-Targeting Process
2.2.1. Definition of Cyber Target
The target refers to a specific area or complex of the enemy, such as facilities, units, equipment, and personnel who are judged to engage in military action, and the target value is determined by the degree to which the commander contributes to achieving the operational objectives [
4].
Target intelligence refers to a detailed and systematic analysis of nodes related to enemy personnel, units, locations, facility systems, missions, objectives, and capabilities as information, indicating vulnerability and importance by technology and identification of objects or groups [
4].
The definition of a cyber target is similar to that of a target in military operations according to the contents of cyber objects in JP 3-60 [
4] and 2.1. However, the targets of attacks include intangible as well as physical targets. That is, a cyber object existing in each layer of cyberspace may be a cyber target.
In this study [
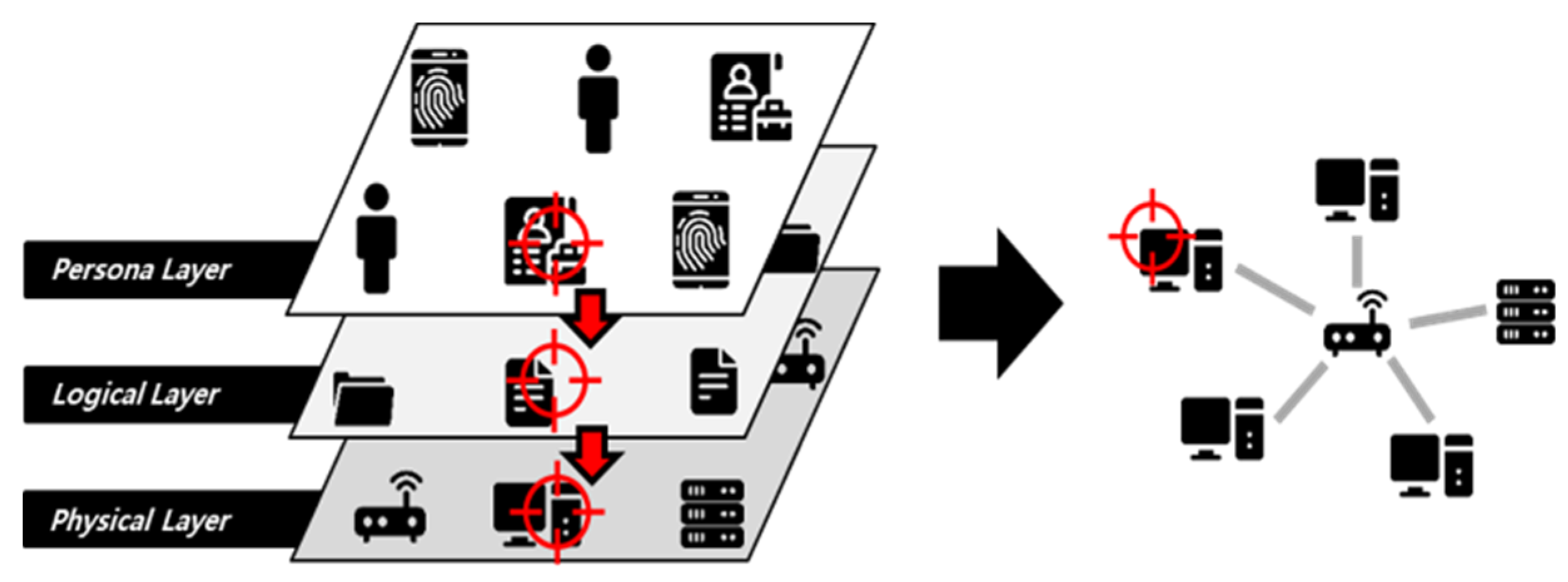
2], the dependence relationship of the cyberspace layer is interpreted as shown in
Figure 1, defining the persona network layer as belonging to the logical network layer and the logical network layer as belonging to the physical network layer.
In addition, the cyber target is defined as a host (server, client) belonging to the physical network layer.
2.2.2. Definition of Cyber-Targeting Process
Targeting is used to systematically analyze and prioritize targets to achieve the commander’s objectives in consideration of operational requirements, capabilities, and evaluation results, and to apply appropriate killing and non-killing measures to targets. Target development refers to the process of identifying, evaluating, and documenting potential targets that contribute to the achievement of the commander’s objectives as part of the second phase of the target-processing cycle [
4].
In military operations, the targeting process is divided into a deliberate targeting process of reviewing and analyzing targets over a period that is sufficient to carry out a normal targeting process and a dynamic targeting process of quickly processing unexpected targets.
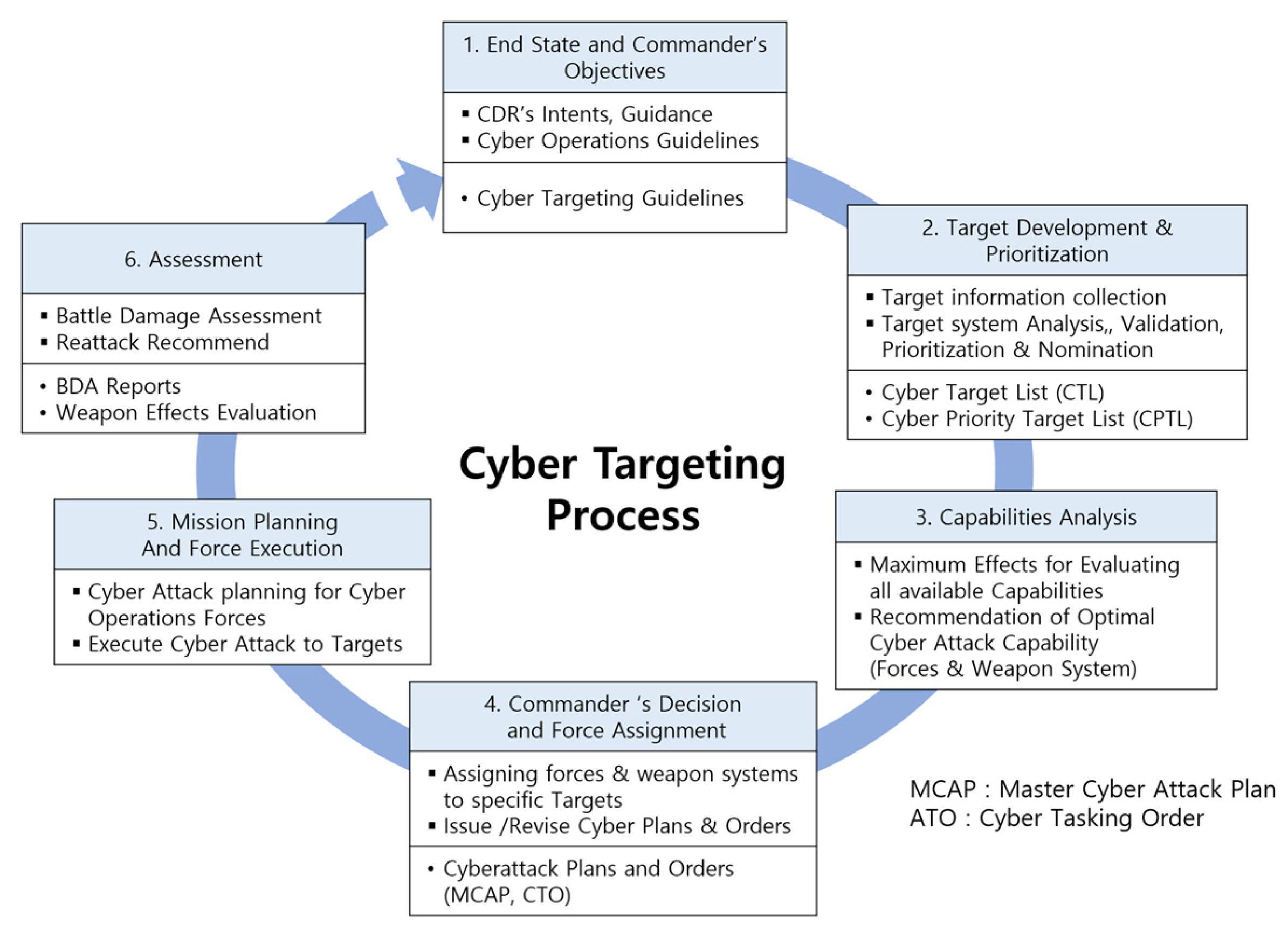
The deliberate targeting process is as follows. The target information maintains a close relationship with the operation and has continuity, as shown in
Figure 2, for each cycle [
4].
In this study, various studies and manuals are referenced to define the cyber-targeting process based on the deliberate targeting process in
Figure 2.
The US Chairman of the Joint Chiefs of Staff guidelines CJCSI 3370.01B (2016) [
5] describes more detailed content in the field of target development in JP 3-60 (2020) [
4]. In addition, it contains the procedures and contents of each stage of target development, the output, electronic target folders (ETF) used in the development stage, and the contents of the target DB. It also defines data on joint targets, information and intelligence relationships, target development roles and responsibilities, and targeting process cycles, as well as presenting data items and examples for basic, intermediate, and detailed target development in the target development stage. Franz [
6], the current head of operations at the U.S. Cyber Command, said that the integration of cyberspace operational effectiveness is essential in the joint forces’ operational planning and implementation in the cyber domain. It has also been suggested that the targeting process in a cyberspace operation be implemented in accordance with the targeting process of the joint unit commander. This also explains the application of the six-step procedure of the targeting process, major operational documents such as the United States CYber COMmand Joint Integrated Prioritized Target List (USCYCOM JIPTL) and Master Cyber Attack Plan (MCAP), and cooperation matters.
Combining these studies and manuals [
4,
5,
6], the cyber-targeting process applies the same steps as in
Figure 2. It is executed in conjunction with the targeting process of joint operations. In addition, the contents of each stage are adjusted and executed in accordance with CO. Accordingly, in this study, the CO targeting process and main activities are summarized as shown in
Figure 3.
2.3. Cyber Target Development and Cyber Target Prioritization Process
2.3.1. Cyber Target Development
In the second stage of the targeting process, “target development and prioritization,” target information collection, target analysis, target development and validation, and prioritization are performed. The cyber target development stage is applied in the same way as military operations [
2]. In target development, potential targets are analyzed first, followed by target development at the entity level. Target development at the entity level goes through the following process:
Basic Target Development;
Intermediate Target Development;
Detailed Target Development.
Each process is divided into the minimum essential data required according to the targeting process, such as the identification of basic information about the target, analysis of functional characteristics, and mission performance. The list of targets necessary for the execution of CO is also maintained and managed by applying the target list of military operations mutatis mutandis. In addition, the candidate target list (validation targets), CTL (target has been verified and there are no specific restrictions on engagement), cyber prioritization target list (CPTL) (prioritized based on CO commander’s objectives), etc., should be created and managed in various forms.
2.3.2. Cyber Target Prioritization Process
The priorities of military targets are selected by integrating the target nomination list (TNL) recommended by the component forces according to the goals of the joint force commander and reviewing them in relation to the commander’s objectives and operational point of view. Prioritization of the CTL is also normally applied according to the “Cyber Force Operation Guidelines” according to the commander’s objectives.
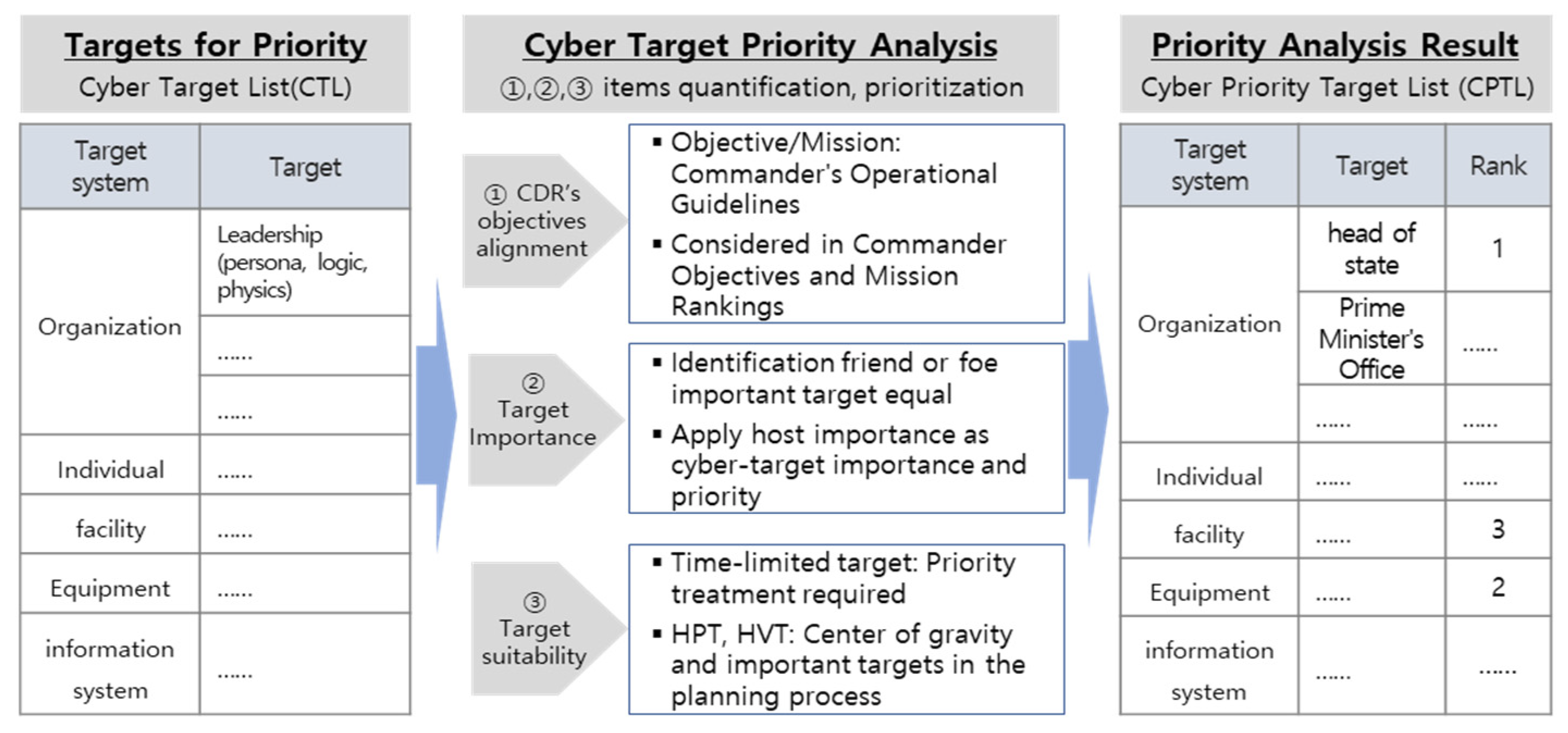
When examining the priority selection items for the component military target recommendations of the military operations, as shown in
Table 1, the target recommendation priority criteria can be divided into three items.
The US JP 3-60 [
4] presents special considerations for prioritizing military operations targets. To summarize, it is organized into three types, as shown in
Table 2. The following items are considered when calculating a target’s priority:
Adequacy for the achievement of the commander’s objectives (compliance with commander’s objectives and operating guidelines: Criteria Item 1, Special Consideration Item 1);
The importance of targets (relative importance between targets in cyberspace: Criteria Item 2);
Target suitability (Special Consideration Items 2, 3).
Based on the above, the cyber target prioritization process was designed as shown in
Figure 4. The priority analysis items are selected based on the commander’s objectives, importance of the target, and suitability of the target, and can be added or excluded, if necessary, by the commander. A cyber target prioritization item is applied in consideration of the characteristics of the CO, and by quantifying and aggregating them, cyber targets can be prioritized. The cyber priority target list becomes a CPTL, which is utilized in the third stage of targeting (capability analysis) and operational planning.
To give priority to the CTL, this study proposes a method for calculating and prioritizing the importance score for each target to quantify its importance among the cyber target priority analysis items.
2.3.3. Definition of Cyber Target Importance
The importance of targets in military operations can be summarized as seen in
Table 3 by referring to [
2,
6]. In summary, important targets (regions, facilities, bases, etc.) of enemy defense operations can be selected as sub targets. It is possible to calculate the importance of each target and give it a relative priority. Considering
Table 3 and the manual [
3,
4], the definition of target importance in CO CTI is the relative importance between cyber targets in cyberspace. This is a value representing how much damage can be inflicted on the enemy if a specific target is attacked while CO are being carried out. Therefore, it is necessary to select a cyber target from among the enemy cyber assets and evaluate the importance of the target by first considering the host as defined in 2.2.1 in terms of the value of the target.
2.4. Case Study on Quantifying Importance of Cyber Assets
In 2.2.1, a cyber target is defined as a host (server, client) belonging to the physical network layer, and research cases deducing the importance of the host among cyber assets were investigated.
2.4.1. PageRank Algorithm
Page and Brin et al., [
7,
8] proposed the PageRank algorithm. The PageRank algorithm assigns a numerical weight to each element of a hyperlinked document set such as the World Wide Web (WWW) and performs power iteration to quantitatively calculate the relative importance within the set.
The PageRank algorithm outputs a probability distribution that is used to represent the likelihood that a person who randomly clicks on a link will arrive at a particular page. It is assumed that the distribution of all the pages it can collect when the computer process starts is evenly divided. That probability is expressed as a numeric value between 0 and 1. For example, a probability of 0.3 is usually expressed as a “30% probability” that something will happen. In other words, a page with a PageRank of 0.3 means that there is a 30% chance that a person who clicks on any link will be directed to the corresponding document.
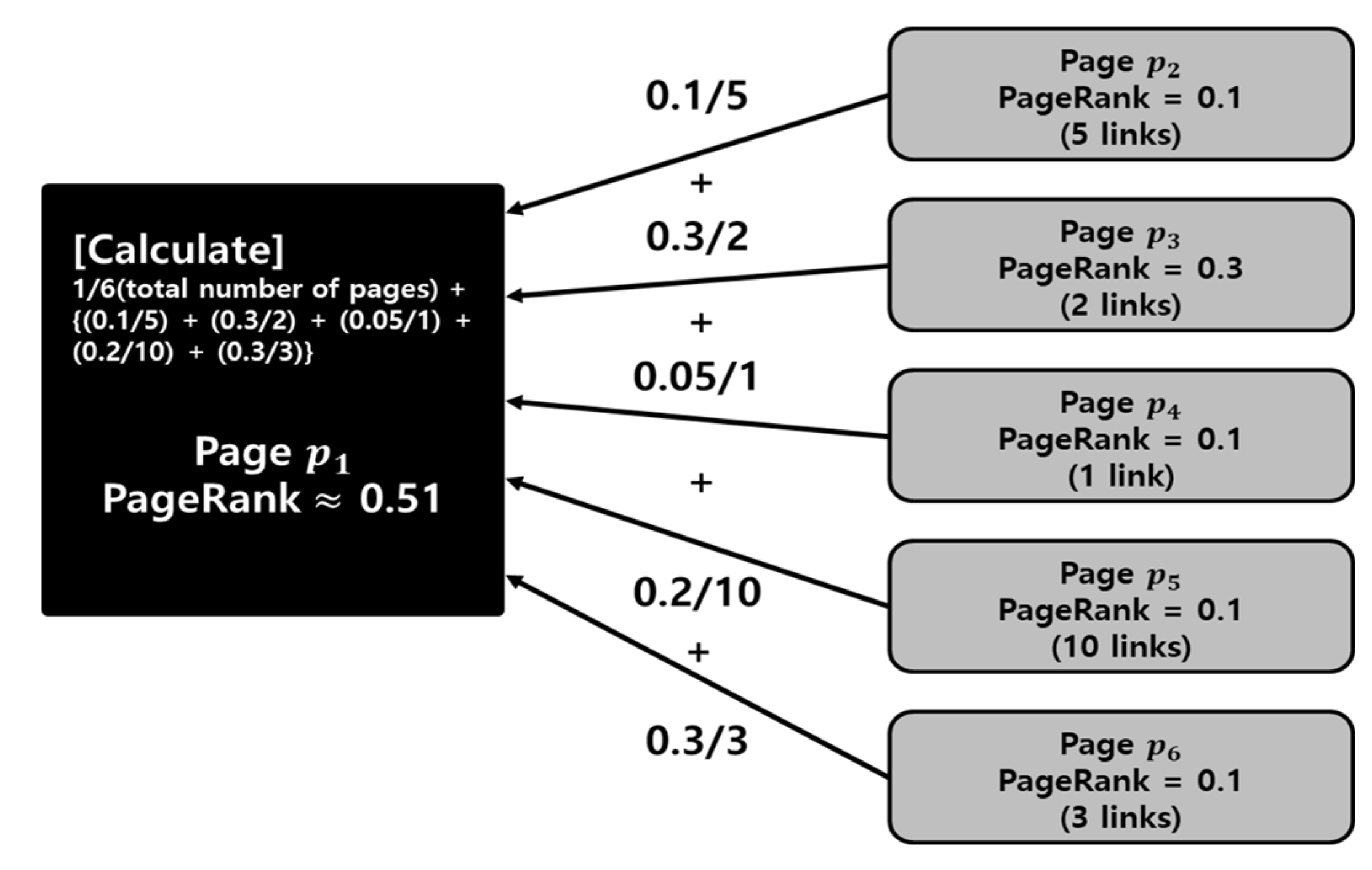
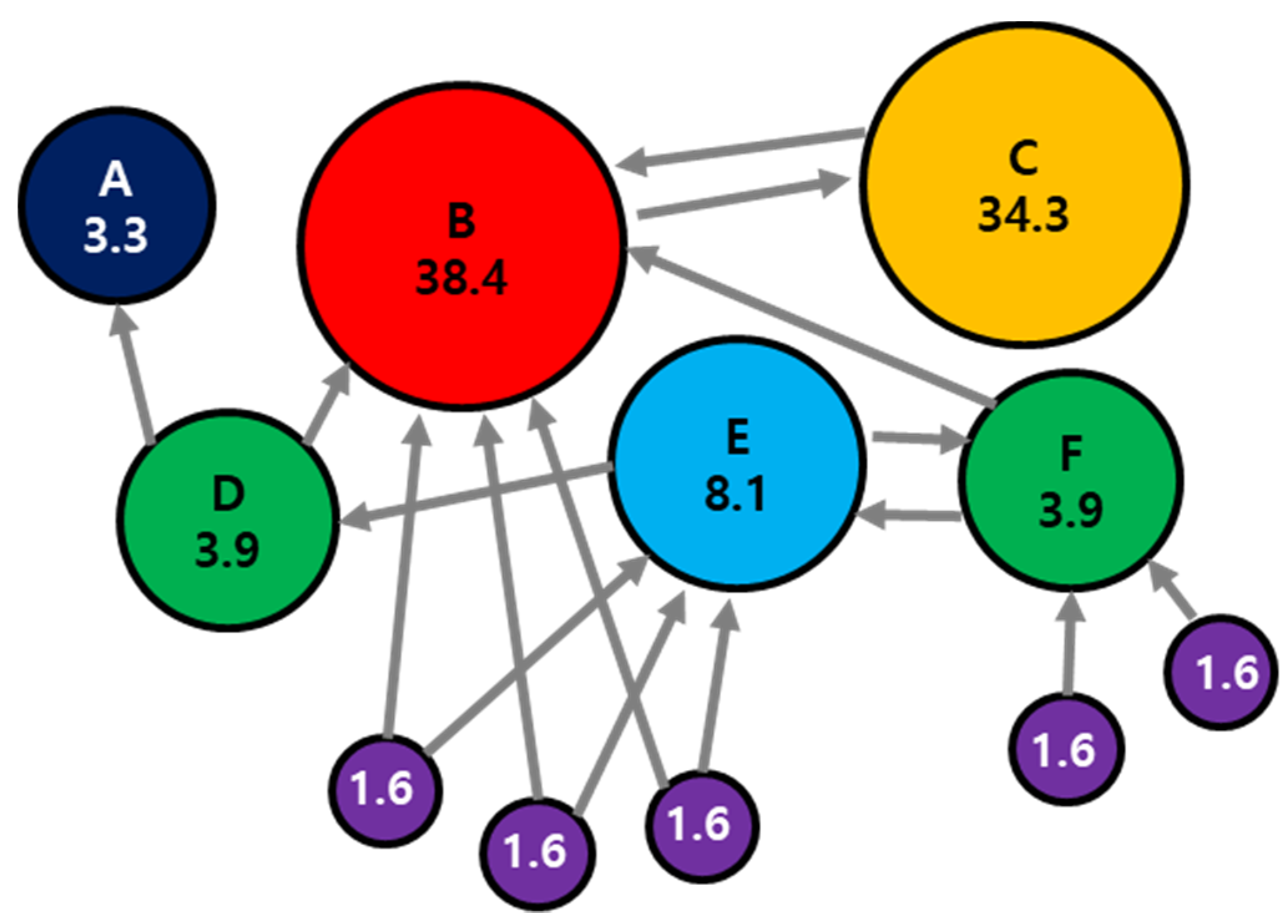
The PageRank calculation formula is shown in Equation (1), and the definitions of the parameters used in the formula are listed in
Table 4. Analyzing Equation (1), all the pages and hyperlinks in the WWW can be expressed as vertices and arcs. As a calculation example of the PageRank algorithm, we want to derive the value of page
out of 6 pages. At this time, when the value of
is 1 and the link and PageRank values of each page are as shown in
Figure 5, the PageRank value of
is 1/6 (total number of pages) + {(0.1/5) + (0.3/2) + (0.05/1) + (0.2/10) + (0.3/3)} = 0.51.
2.4.2. Event Prioritization Framework
Kim et al. (2014) [
9] proposed an event prioritization framework (EPF) that determines priorities according to the influence of events on the host. This framework quantitatively calculates the network’s host exposure, asset criticality, and events to hosts (sum of comprehensive event effectiveness, event clustering, etc.). Then, using the calculated value, the priority is determined according to the effect of the event on the host.
Host exposure (HE) is a potential attack risk value that synthesizes various vulnerabilities of a host. The calculation formula is as shown in Equation (2), and the definitions of the parameters used in the Equation are listed in
Table 5. Asset criticality (AC) is quantified by considering app, network, data, command, and operation system (OS) importance values using the TOPSIS [
10] algorithm proposed by Yoon et al. (1995).
2.4.3. Host Severity Assessment Cases
As part of the cyber command and control real-time decision support technology project conducted by the Korea Defense Science Research Institute, the impact on mission performance was evaluated when the network infrastructure was subjected to a cyber-attack. To evaluate the impact, we mapped and managed the dependency on assets and missions, and used the indicators listed in
Table 6 to evaluate the criticality of the host asset based on confidentiality, integrity, and availability (CIA).
3. Design of Target Importance Rank Algorithm
In this section, the cyber target development and cyber target importance of 2.3 are synthesized to derive target importance criteria for CO. In addition, the TIR algorithm is designed to quantify the score of each criterion by synthesizing the 2.4 cyber asset importance quantification research cases. Finally, scenarios (network topology, experimental data) to verify this algorithm are designed based on the STUXNET case.
3.1. Identification of Cyber Target Materiality Criteria and Utilization Parameters
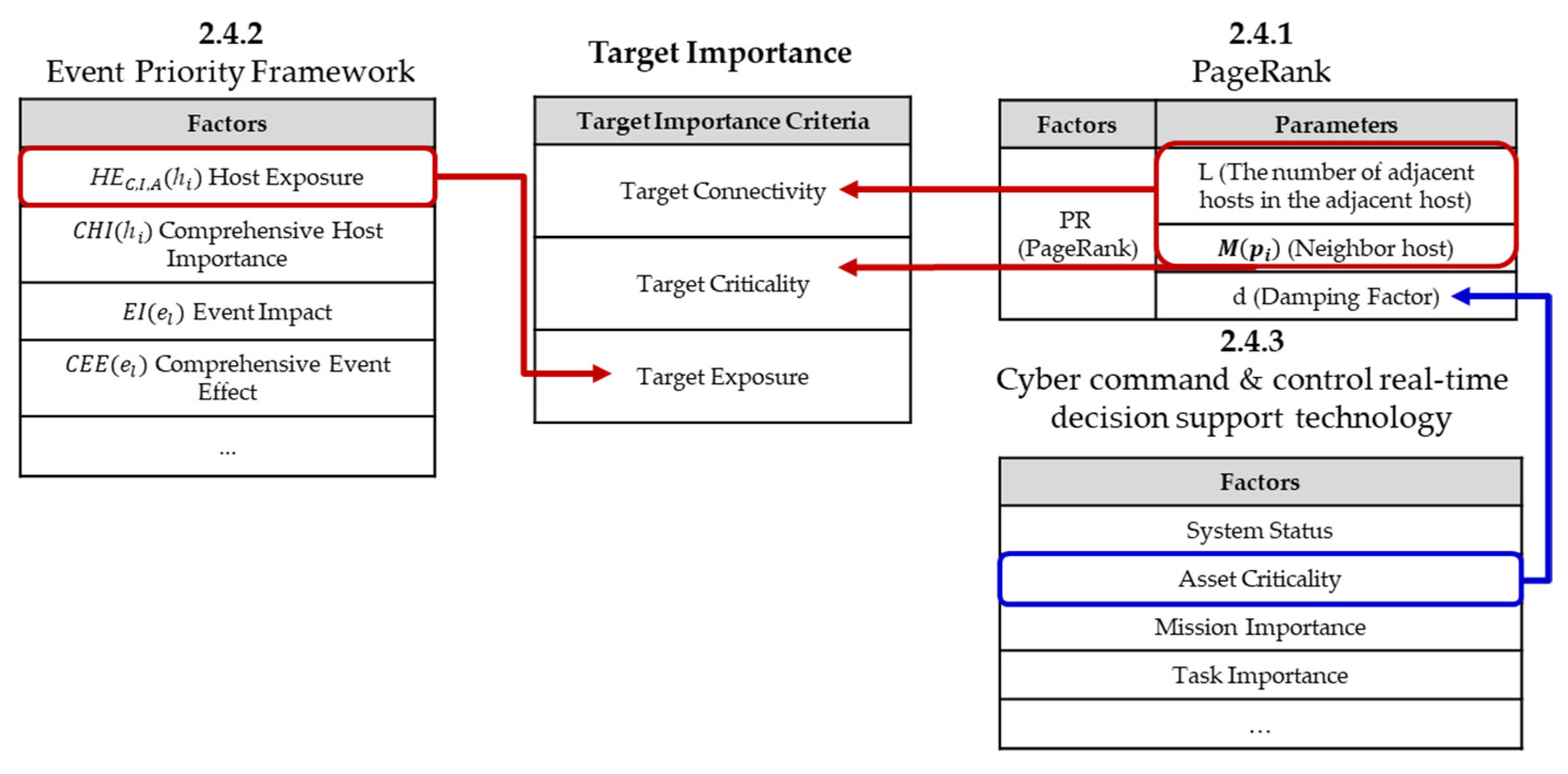
The cyber target importance quantification method defined in
Section 2.3.3 was derived by synthesizing the research cases in 2.4.
Equation (1) calculates the connectivity of each page through parameters such as and outputs the probability distribution using parameter . Therefore, we change the definition of the connectivity between pages to the connectivity between hosts. We then compute as the “asset criticality” value and assign a cyber target importance using the PageRank algorithm.
As the cyber target is defined as the host in
Section 2.2.1, the host exposure in Equation (2) can be assumed to be the target exposure, and the exposure degree, which is the vulnerability of the target, can be quantitatively calculated using EPF.
Finally, using the indicators in
Table 6, the target criticality, which is the degree of influence when attacking the host, can be quantitatively calculated.
Based on these research results, three criteria for the importance of cyber targets were defined as listed in
Table 7. When deriving the scores for each standard item quantitatively, factors that can be utilized were identified with
Table 8.
Analyzing
Table 8, Equation (1) has two target importance criteria. It is a suitable algorithm for synthesizing the elements of the research cases of this paper. In addition, if Equation (2), which can quantify the target exposure, is properly fused with Equation (1), the importance of the target can be calculated quantitatively.
In the next section, Equations (1) and (2), and
Table 6, are used to design the TIR algorithm to be used to achieve the purpose of this study.
3.2. TIR Algorithm Design and Prioritization Method
In this section, we propose a method for calculating the score for each surrender using the identified parameters and criteria listed in
Table 7 and
Table 8. By synthesizing the calculated scores, the cyber target score is then calculated, and a plan is proposed that can be used to select priorities.
3.2.1. Cyber Target Connectivity Score Calculation Method
According to
Section 2.2.1 which defines cyber targets as hosts, the definition of ’d’ in
Table 4 is changed to ’the probability of moving to another network if the network is not important from an attacker’s point of view’, and the page(p) in Equation (1) is changed to host(h) as shown in Equation (3).
3.2.2. Cyber Target Criticality Score Calculation Method
An arbitrary value between 0 and 1 is substituted for
(damping factor) in
Table 4. This is calculated by dividing the value derived using the indicators in
Table 6,
Table 7,
Table 8,
Table 9 and
Table 10 so that it conforms to the target importance calculation method. In
Section 2.4.1, because the value of
is applied globally, the average of the
values of hosts belonging to one network cluster is calculated, and the score of
in
Table 9 is calculated, as shown in
Figure 6.
3.2.3. Cyber Target Exposure Score Calculation Method
Previously, the target connectivity and target criticality were derived among the target importance criteria, and finally the target exposure was derived from Equation (2) for the HE value in
Section 2.4.2. First, the definition of HE is changed to the “potential attack risk value that synthesizes various vulnerabilities on the target.” The derived HE value is integrated into the PageRank-based target importance assignment formula derived as shown in Equation (3) and defined as TIR. Accordingly, PR is changed to TIR, as shown in
Figure 7.
3.2.4. TIR Scoring and Prioritization
The score elements for each cyber target importance criterion from
Section 3.2.1,
Section 3.2.2 and
Section 3.2.3 are summarized, as shown in
Figure 8. Accordingly, Equation (4) for synthesizing the target importance score is derived. Equation (4) is an algorithm for deriving the target importance score using the PageRank algorithm proposed in this study. The parameters to be used comply with the contents of
Table 9, but the added parameters and changed definitions are provided in
Table 10.
The network topology is transformed into a logical structure, as shown in
Figure 9, to derive the target importance priority. Then, using the TIR algorithm, the results listed in
Table 11 are obtained. Finally, if the TIR scores are sorted in descending order, the important targets are listed from the top.
4. Design of Experimental Scenario and Experiment Results
4.1. Design of Experimental Scenario
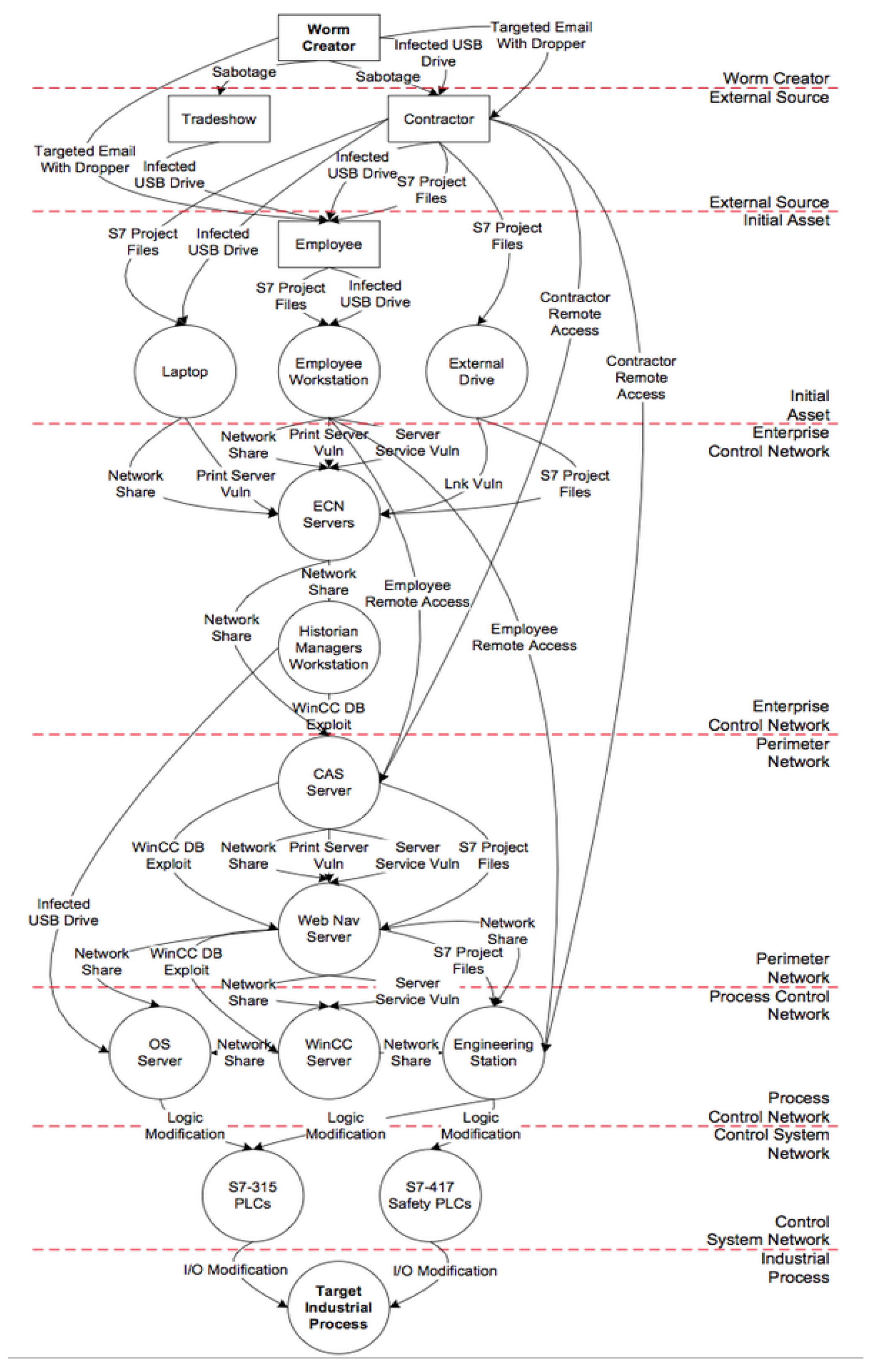
4.1.1. Analysis of STUXNET Case
The STUXNET attack, which destroyed and incapacitated the SCADA system of an Iranian nuclear power plant, was an incident in which a centrifuge in the Iranian Natanz nuclear facility was damaged as a result of a series of cyberattacks between 2007 and 2012 [
11]. The Iran nuclear facility target system consists of the Natanz nuclear facility and Arack; the centrifuge, power supply system, and SCADA system can be viewed as target components. The identified cyber targets were the PLC H/W, PLC logic control S/W, etc., considering the three layers of cyberspace [
11]. The SCADA system is a major piece of equipment that collects and controls data in real time. It is mainly installed in computer-controlled core infrastructure such as power plants, oil and gas pipelines, refineries, and water supply facilities, and programmable logic controllers (PLCs) H/W. The PLCs at the Natanz nuclear facility that STUXNET attacked were Simatic Step 7 controllers from Siemens, Germany. STUXNET infected this system to tamper with the PLC code blocks, hide the tampered code, and execute the hidden tampered code block when Step 7 was called. The final targets of STUXNET’s attack were two central processing units, S7-315 and S7-417. In this case, certificates from trusted companies were used to prevent exposure by automatic detection systems. In order to break into the computers in the facility (Air-Gap), we used vulnerabilities that existed between computers or between computers and USB. An analysis of the above text shows that the Natanz nuclear facility is a production and enrichment facility among Iranian nuclear facilities, and can be classified as a component of a target system. As a target, it can be classified as a centrifuge, a power supply system, and a SCADA system. For the selection of the target, the experiment was performed by selecting the SCADA system and PLCs as dual components and selecting the access path to connect the internal worker PC via USB.
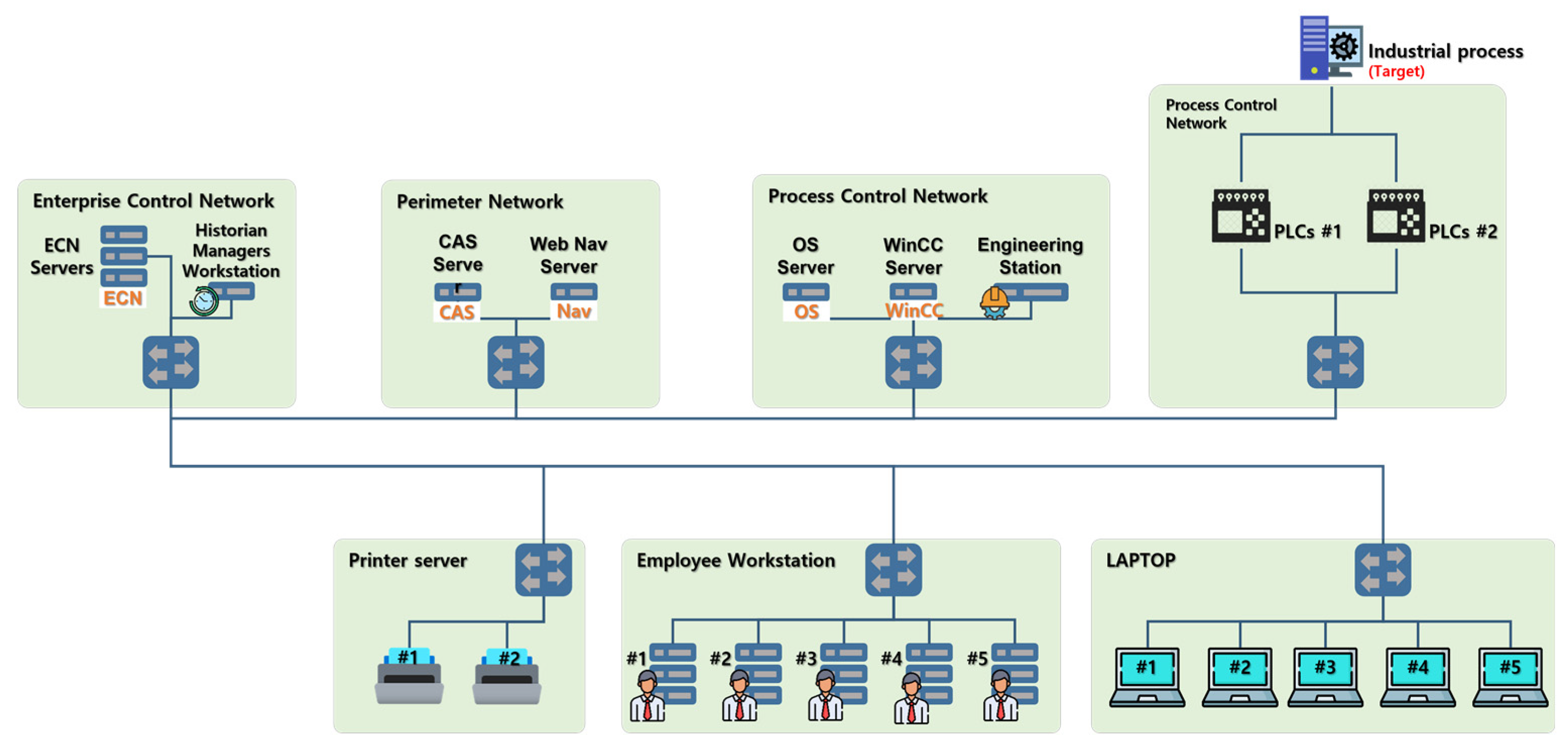
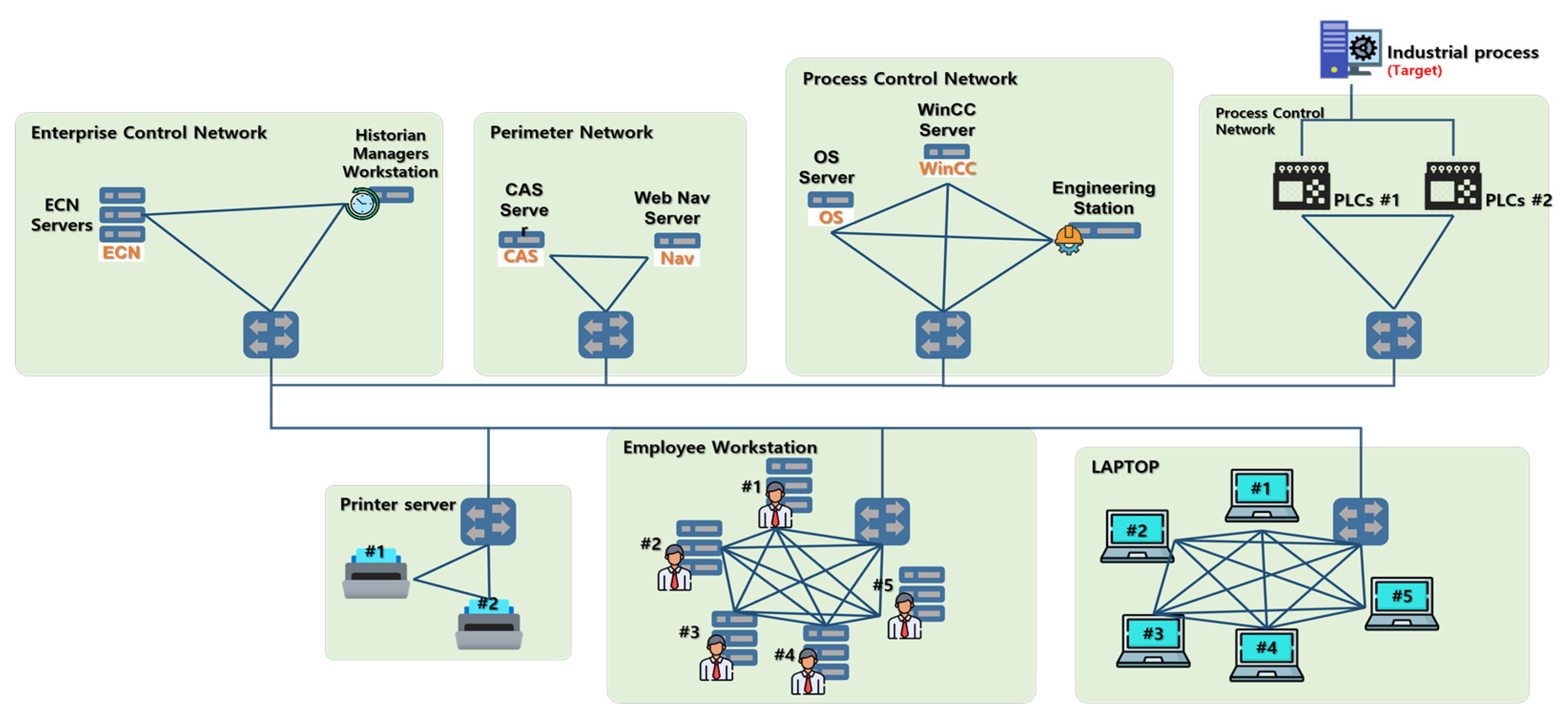
4.1.2. STUXNET Case-Based Network Topology and Scenario Data Configuration
A scenario was constructed using the attack graph designed based on the STUXNET case, as shown in
Figure 10, out of the cases [
11,
12] introduced in
Section 4.1.1. The goal of the operation and the commander’s goal were to neutralize the target industrial process at the bottom of
Figure 10, and it was assumed that the operation was performed in cyberspace. After that, it was assumed that the targets analyzed according to the cyber target processing procedure in
Figure 3 were composed of the network topology structure shown in
Figure 11.
Each vertex in
Figure 10 is defined as one node in
Figure 11, which shows the network structure. In addition, assuming that there can be multiple nodes such as a printer server, employee workstation, and laptop, 2–5 nodes were placed. The cluster consisted of each tier in
Figure 10, except for the initial asset layer and the print server. Each cluster was also assumed to be connected to one switch, and the switches were assumed to be connected to each other in one direction.
To perform the TIR proposed in this study, it needed to be converted into a logical network topology as shown in
Figure 9. It could be converted as shown in
Figure 12 through the following process:
It is assumed that nodes clustered based on the switch (clotted with a green background) may communicate internally with each other because of the switch;
Connect the nodes in one cluster to each other.
Among the nodes in
Figure 12, the common vulnerabilities and exposures (CVE) of the hosts were selected by combining the contents of case [
11] and
Figure 10. In the case of an engineering station, as shown in
Figure 10, there was only network share in the call related to the vulnerability. After that, the Windows shell LNK (CVE-2010-2568)—a network share vulnerability introduced in the cases in [
11]—was selected as a vulnerability, and common vulnerability scoring system (CVSS) v2 [
13] parameter scores were inserted. There were a total of two neighboring hosts (other hosts in the same cluster), and this operation was repeated to generate data to be used in the experiment, as listed in
Table 12.
4.2. Experiment Result
By substituting the scenario data listed in
Table 12 into the TIR algorithm (Equation (4)) written in 3.2 and the priority selection method, the target priority was derived as listed in
Table 13.
For target connectivity, according to the
Section 2.2.1 cyber target definition, the number of edges between hosts (excluding switches among the parts grouped in the green box in
Figure 12) was used. The target criticality was quantified according to
Table 6 and replaced with qualitative items, and weights were selected as MI: 1, MV: 0.5, and ACA: 1 when calculating the target exposure. When calculating up to the process in
Figure 6, the target connectivity and target criticality scores were synthesized by selecting the initial PR value as 0.1 and performing power iteration four times to make the vector values similar. Finally, the TIR score was calculated by multiplying the target exposure value and sorted in descending order to finally derive the results listed in
Table 13. As a result, the S7-315 PLCs were selected as the most important targets. This will allow commanders to easily understand target priorities and issue correct operational guidelines.
5. Conclusions
In this study, a method for assigning cyber target importance to calculate cyber target priorities was developed. To conduct the research, the importance of the target was defined by first examining domestic and foreign manuals. To calculate the importance score of the defined target, PageRank, an event prioritization framework, and host criticality evaluation cases were investigated.
The TIR algorithm was designed by deriving target importance criteria based on the investigated cases and synthesizing the formulas and indicators of the research cases. To prove this, the STUXNET case was analyzed, experimental data were created, and an experiment was conducted.
As a result, the S7-315 PLCs, which were physically and logically the closest to the objectives of the operation, were selected as the most important targets.
When designing cyber operations, the TIR algorithm can be used to determine which of the cyber targets located on the network are the most important. In addition, it could be a good reference for flexibly designing the operation by checking the connectivity, criticality, and exposure scores of the target, respectively.
In the private sector, if the TIR algorithm is used when designing operations belonging to the red team during cyber defense training, the operation success rate can be further increased. Cybersecurity teams can use the TIR algorithm to identify the riskiest network nodes and establish security measures for them.
Overall, our experiments with the TIR algorithm derive the importance of assets in cyberspace. This suggests that it is very useful in terms of cybersecurity.
In future research, after collecting BGP-Archive-Data and processing it into geographic information, the network status map will be visualized on the battlefield map. From this visualized network information, we will collect information (PC, Server, IP, SNS ID/PW, E-Mail, etc.) on friendly network areas, hostile network areas and private network areas and identify target groups. Thereafter, there are plans to further develop procedures and techniques for cyberattacks, such as prioritizing each target within the identified target group and selecting a policy to attack the target.