Evaluating the Effectiveness of COVID-19 Bluetooth-Based Smartphone Contact Tracing Applications
Abstract
1. Introduction
2. Related Works
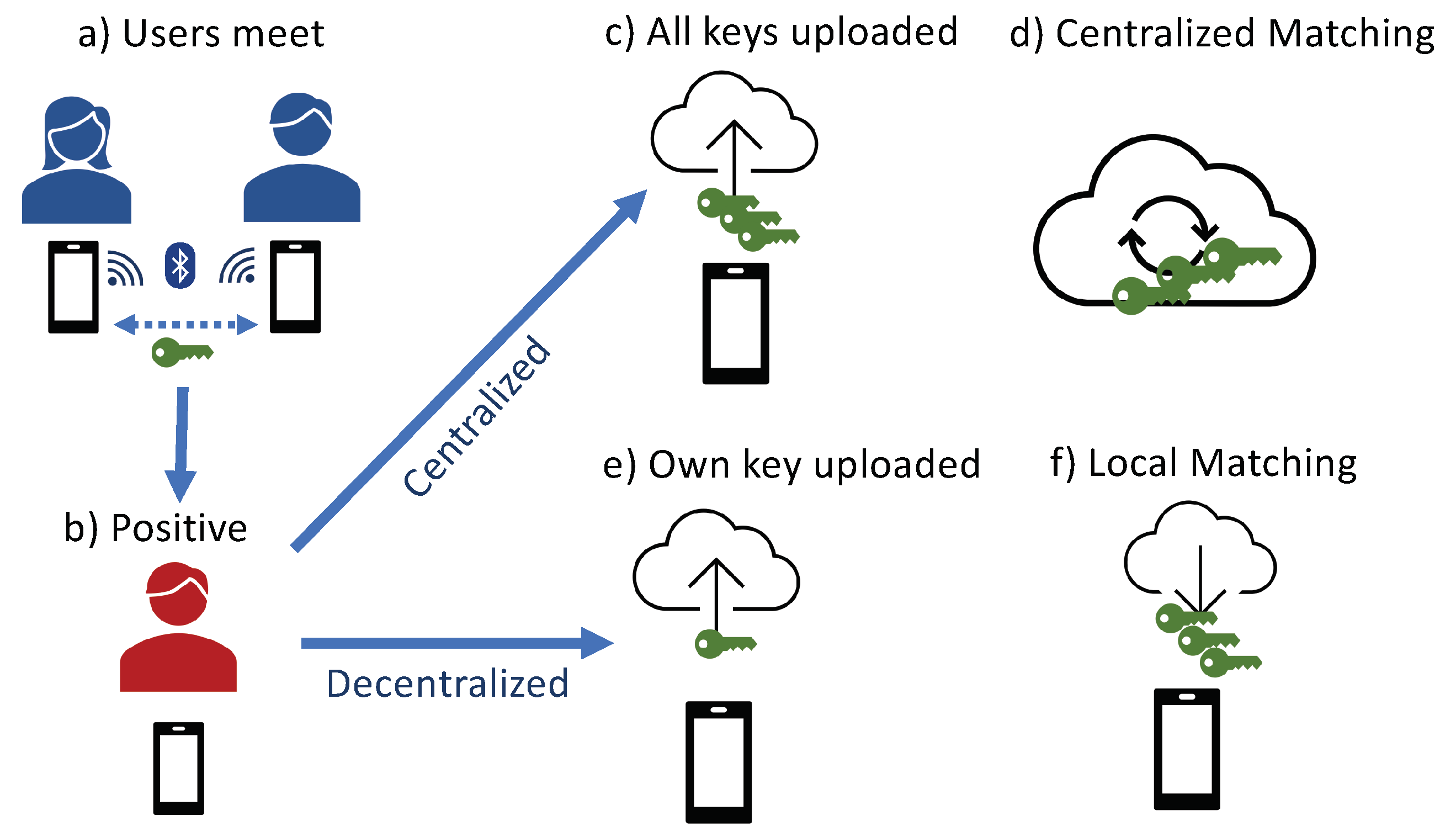
3. Smartphone-Based Contact Tracing
3.1. Contact Tracing Applications
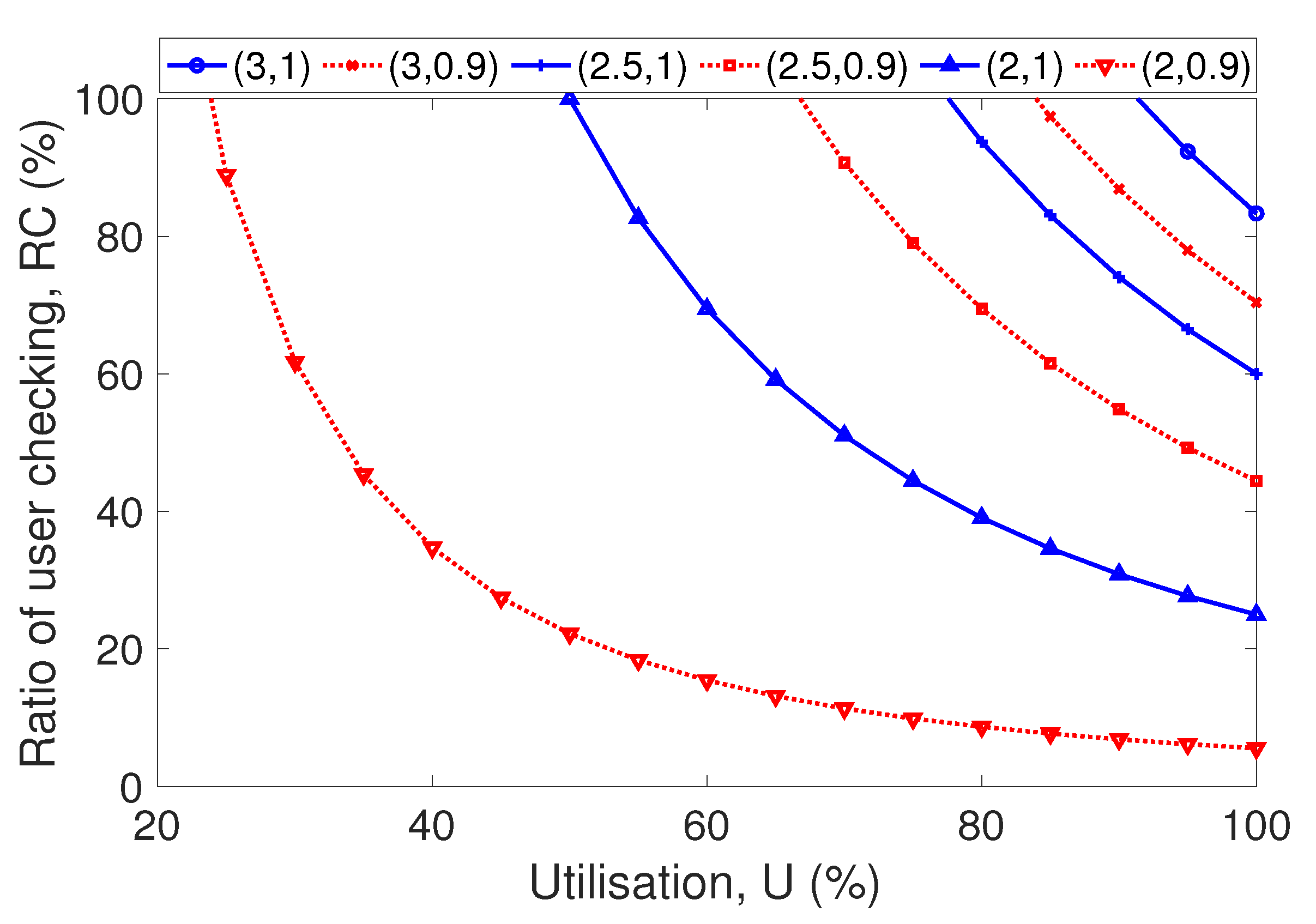
3.2. Characterizing Contact Tracing Effectiveness
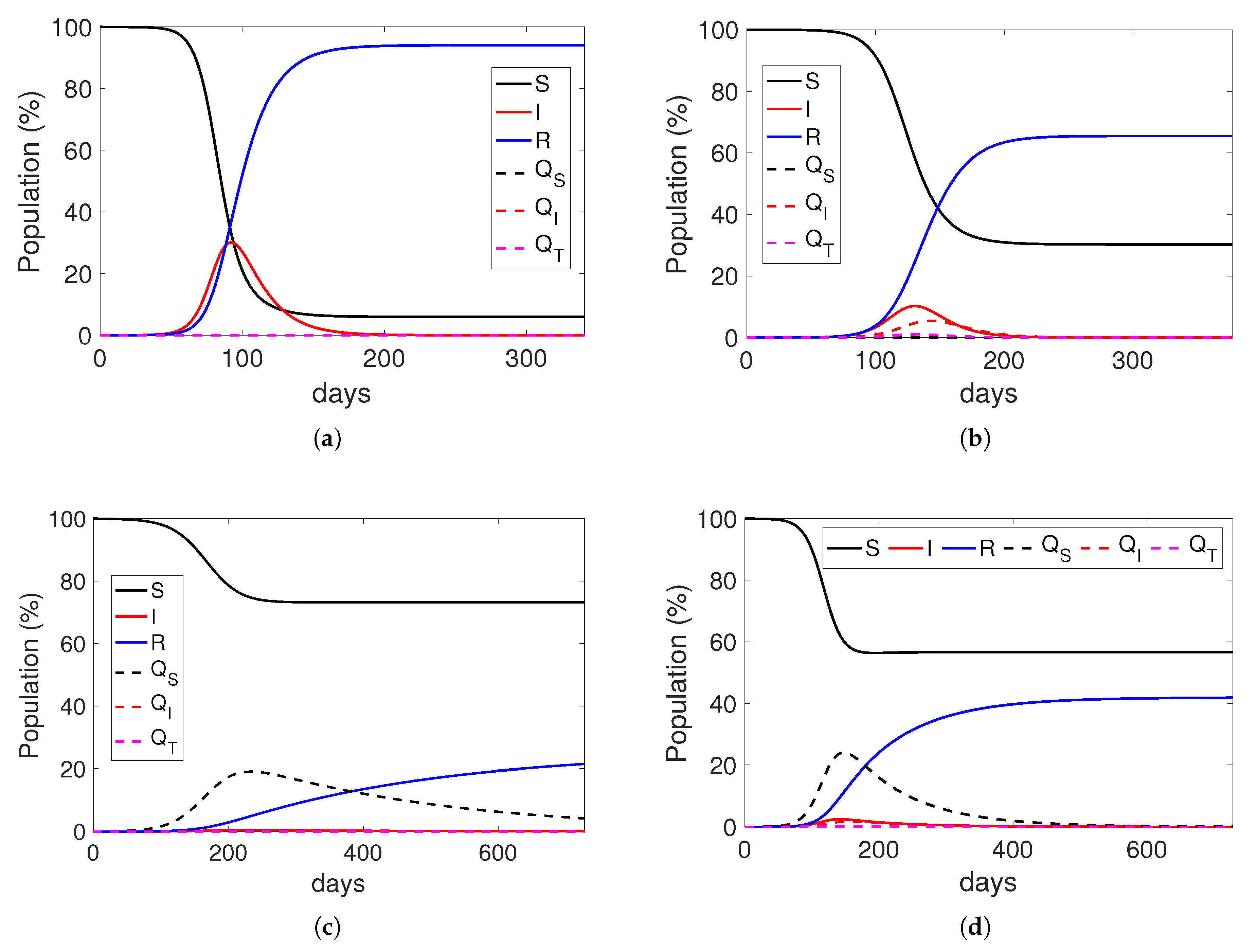
4. Epidemic Model
- : Infected individuals who are not traced and consequently, not quarantined. In general, the transmission rate, that is the rate in which the infection is transmitted from one infected individual to one susceptible individual, is formed from the product of the number of contacts per time unit k, and the probability to transmit the disease b; hence, newly infected individuals are generated with a whole rate . Note that this rate is for all infected individuals. Since in this transition we are only considering the infected ones that are not traced, the previous rate is multiplied by , that is the fraction of non-traced contacts, so that the transition rate is . The other fraction of infected individuals is considered in transition .
- : Infected individuals who are being traced and go directly to the tracing state. When infected individuals are detected (that is, when they are in class ) their previous contacts that are in the susceptible class are traced, and some of them are quarantined. Therefore, this transition considers only the traced contacts, that is the fraction , so the rate is . It refers to the individuals that may have been infected during the day.
- : Non-infected individuals traced and quarantined. The transition rate is , considering that is the probability of not transmitting the disease. In this transition rate, the fraction considers the effect of false positives, which can increase the number of people unnecessarily quarantined.
- : Detection of infected individuals, triggering the tracing of their previous contacts using the application while being quarantined. In our model, infected individuals are detected, traced and quarantined with rate, staying in quarantine for an average time of days. Prior to going to the final quarantine class , these individuals stay during a short time in class , for tracing their previous contacts. This time is the tracing time () that models the necessary time to trace the contacts, allowing to compare the fast-tracing centralized approach versus the slower-tracing decentralized approach.
- : This transition supposes the end of the tracing. After the tracing time they move to the class, to finish their quarantine.
- : End of quarantine and infection. In this class, individuals continue their quarantine for the remaining quarantine time, which is obtained as = , and, finally, they are considered recovered and move to the R class afterward.
- : Non detected infected individuals recovered from the disease. This transition considers those infected individuals not detected, that is, asymptomatic ones which have not been tested. The rate is simply the recovery rate .
- : End of quarantine for susceptible individuals. After being quarantined, individuals in the class return to the susceptible class, after staying in quarantine for days.
5. Evaluation
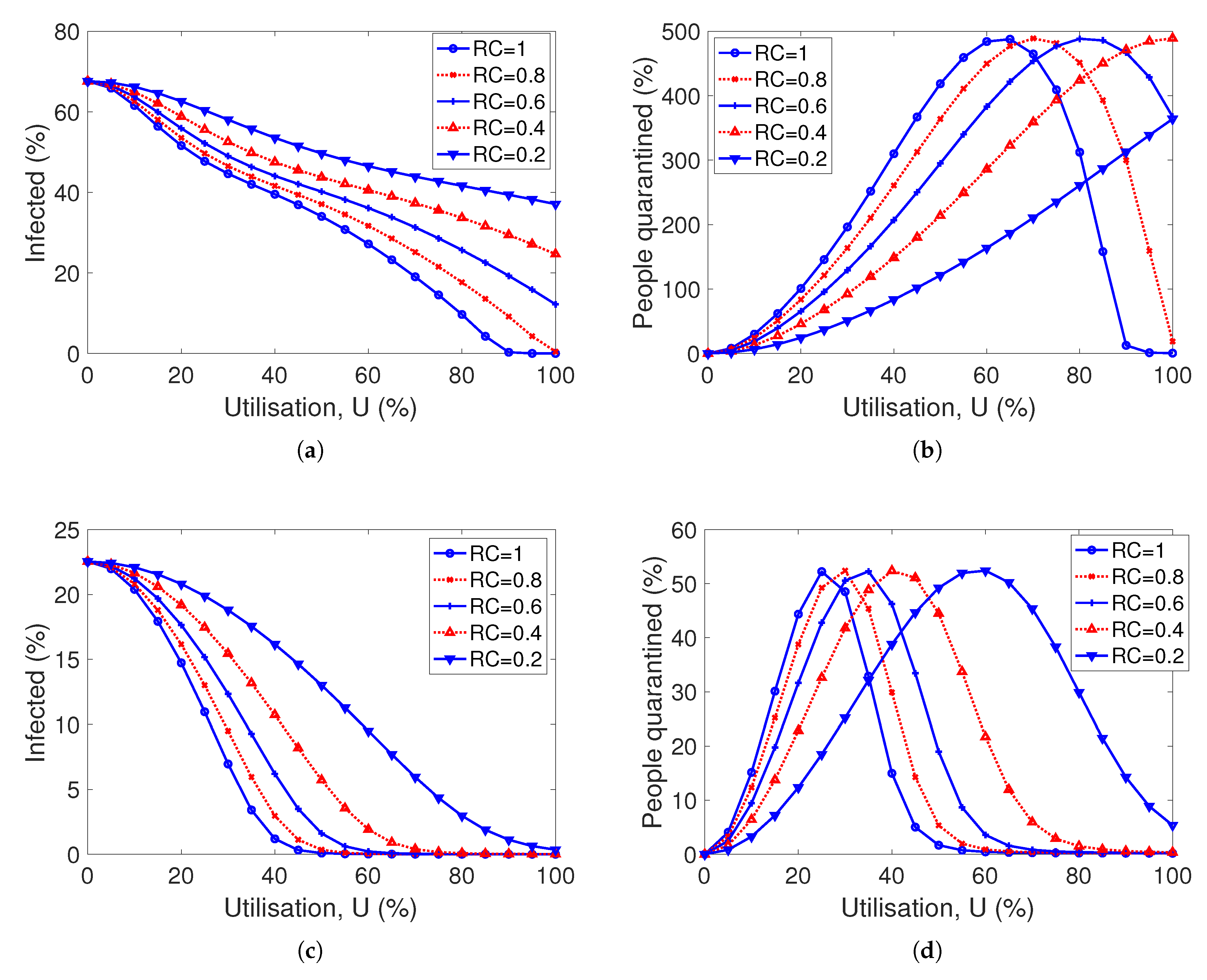
5.1. Impact of Utilization
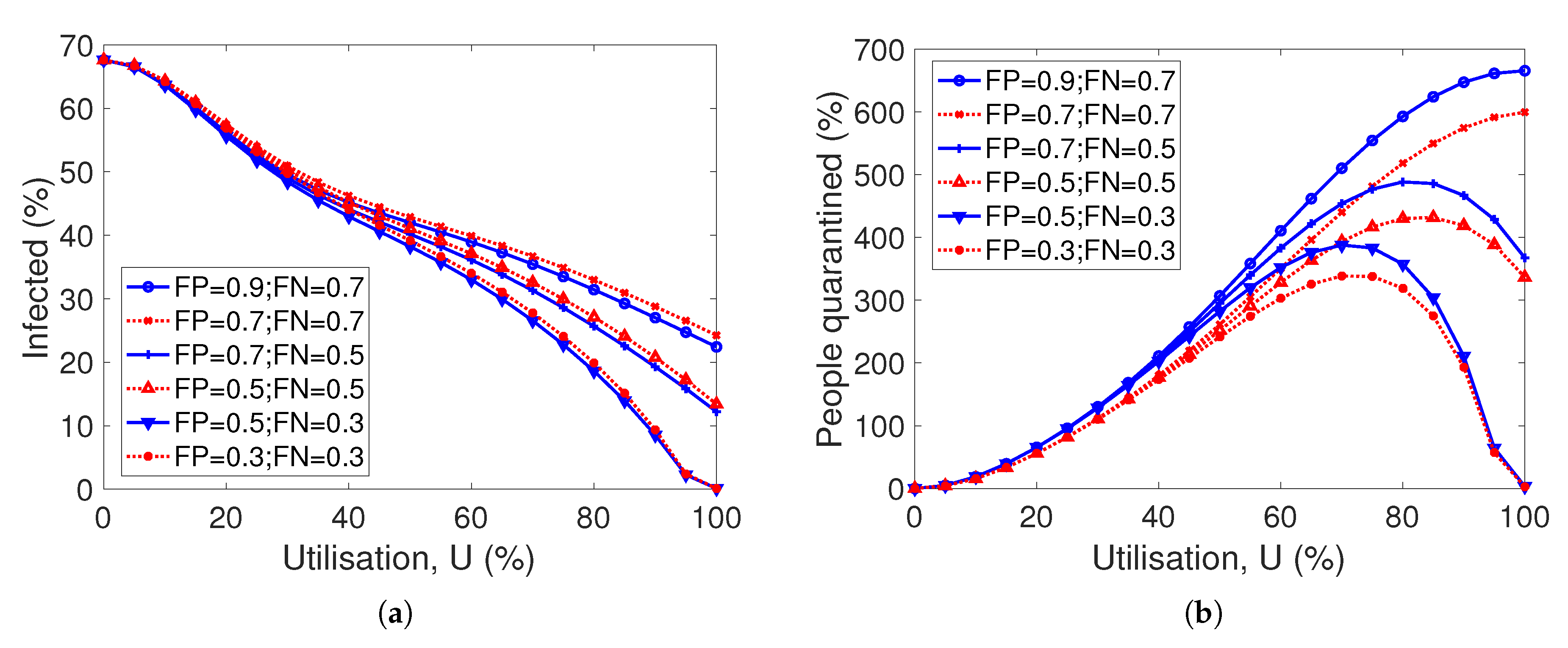
5.2. Impact of Accuracy
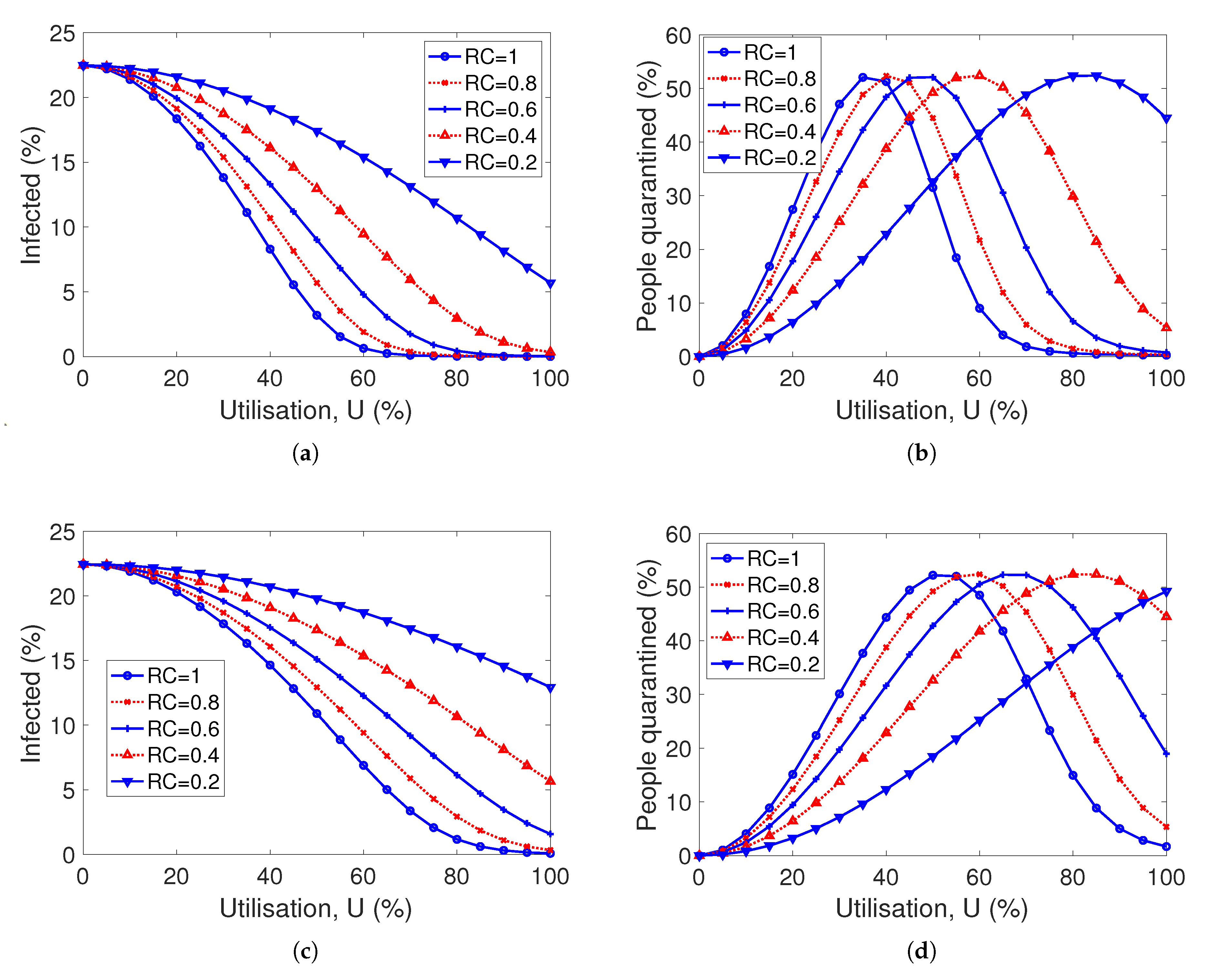
5.3. Centralized vs. Decentralized Solutions
6. Conclusions
Author Contributions
Funding
Conflicts of Interest
References
- Li, R.; Rivers, C.; Tan, Q.; Murray, M.B.; Toner, E.; Lipsitch, M. The demand for inpatient and ICU beds for COVID-19 in the US: Lessons from Chinese cities. medRxiv 2020. [Google Scholar] [CrossRef]
- COVID-19 National Emergency Response Center, Epidemiology and Case Management Team, Korea Centers for Disease Control and Prevention. Contact Transmission of COVID-19 in South Korea: Novel Investigation Techniques for Tracing Contacts. Osong Public Health Res Perspect 2020, 11, 60–63. [Google Scholar] [CrossRef]
- Eames, K.; Keeling, M. Contact Tracing and Disease Control. Proc. Biol. Sci. R. Soc. 2004, 270, 2565–2571. [Google Scholar] [CrossRef]
- Salathé, M. Digital epidemiology: What is it, and where is it going? Life Sci. Soc. Policy 2018, 14, 1. [Google Scholar] [CrossRef]
- Computer Laboratory-University of Cambridge. The FluPhone Study. 2010. Available online: https://www.fluphone.org (accessed on 24 May 2020).
- Singapore Government. Tracetogether. 2020. Available online: https://www.tracetogether.gov.sg (accessed on 15 April 2020).
- MIT. Safe Paths. 2020. Available online: http://safepaths.mit.edu (accessed on 22 April 2020).
- Raskar, R.; Schunemann, I.; Barbar, R.; Vilcans, K.; Gray, J.; Vepakomma, P.; Kapa, S.; Nuzzo, A.; Gupta, R.; Berke, A.; et al. Apps Gone Rogue: Maintaining Personal Privacy in an Epidemic. arXiv 2020, arXiv:2003.08567. [Google Scholar]
- PePP-PT e.V. i.Gr. Pan-European Privacy-Preserving Proximity Tracing (PEPP-PT). 2020. Available online: https://www.pepp-pt.org (accessed on 15 September 2020).
- Pelusi, L.; Passarella, A.; Conti, M. Opportunistic networking: Data forwarding in disconnected mobile ad hoc networks. Commun. Mag. IEEE 2006, 44, 134–141. [Google Scholar] [CrossRef]
- Zhang, X.; Neglia, G.; Kurose, J.; Towsley, D. Performance modeling of epidemic routing. Comput. Netw. 2007, 51, 2867–2891. [Google Scholar] [CrossRef]
- Helgason, Ó.; Kouyoumdjieva, S.T.; Karlsson, G. Opportunistic Communication and Human Mobility. IEEE Trans. Mob. Comput. 2014, 13, 1597–1610. [Google Scholar] [CrossRef]
- Chancay-García, L.; Hernández-Orallo, E.; Manzoni, P.; Calafate, C.T.; Cano, J. Evaluating and Enhancing Information Dissemination in Urban Areas of Interest Using Opportunistic Networks. IEEE Access 2018, 6, 32514–32531. [Google Scholar] [CrossRef]
- Dede, J.; Förster, A.; Hernández-Orallo, E.; Herrera-Tapia, J.; Kuladinithi, K.; Kuppusamy, V.; Manzoni, P.; bin Muslim, A.; Udugama, A.; Vatandas, Z. Simulating Opportunistic Networks: Survey and Future Directions. IEEE Commun. Surv. Tutor. 2018, 20, 1547–1573. [Google Scholar] [CrossRef]
- Hernández-Orallo, E.; Murillo-Arcila, M.; Calafate, C.T.; Cano, J.C.; Conejero, J.A.; Manzoni, P. Analytical evaluation of the performance of contact-Based messaging applications. Comput. Netw. 2016, 111, 45–54. [Google Scholar] [CrossRef][Green Version]
- Hernandez-Orallo, E.; Serrat Olmos, M.; Cano, J.C.; Calafate, C.; Manzoni, P. CoCoWa: A Collaborative Contact-Based Watchdog for Detecting Selfish Nodes. IEEE Trans. Mob. Comput. 2015, 14, 1162–1175. [Google Scholar] [CrossRef]
- Hernández-Orallo, E.; Manzoni, P.; Calafate, C.T.; Cano, J. Evaluating How Smartphone Contact Tracing Technology Can Reduce the Spread of Infectious Diseases: The Case of COVID-19. IEEE Access 2020, 8, 99083–99097. [Google Scholar] [CrossRef]
- Christaki, E. New technologies in predicting, preventing and controlling emerging infectious diseases. Virulence 2015, 6, 558–565. [Google Scholar] [CrossRef] [PubMed]
- Cecilia, J.M.; Cano, J.C.; Hernández-Orallo, E.; Calafate, C.T. Mobile crowdsensing approaches to address the COVID-19 pandemic in Spain. IET Smart Cities 2020, 2, 58–63. [Google Scholar] [CrossRef]
- Hernández-Orallo, E.; Borrego, C.; Manzoni, P.; Marquez-Barja, J.M.; Cano, J.C.; Calafate, C.T. Optimising data diffusion while reducing local resources consumption in Opportunistic Mobile Crowdsensing. Pervasive Mob. Comput. 2020, 67, 101201. [Google Scholar] [CrossRef]
- Doran, D.; Severin, K.; Gokhale, S.; Dagnino, A. Social media enabled human sensing for smart cities. AI Commun. 2016, 29, 57–75. [Google Scholar] [CrossRef]
- Salathé, M.; Kazandjieva, M.; Lee, J.W.; Levis, P.; Feldman, M.W.; Jones, J.H. A high-resolution human contact network for infectious disease transmission. Proc. Natl. Acad. Sci. USA 2010, 107, 22020–22025. [Google Scholar] [CrossRef]
- Fraser, C.; Riley, S.; Anderson, R.; Ferguson, N. Factors that make an infectious disease outbreak controllable. Proc. Natl. Acad. Sci. USA 2004, 101, 6146–6151. [Google Scholar] [CrossRef]
- Klinkenberg, D.; Fraser, C.; Heesterbeek, H. The Effectiveness of Contact Tracing in Emerging Epidemics. PLoS ONE 2006, 1, e12. [Google Scholar] [CrossRef]
- Kwok, K.O.; Tang, A.; Wei, V.W.; Park, W.H.; Yeoh, E.K.; Riley, S. Epidemic Models of Contact Tracing: Systematic Review of Transmission Studies of Severe Acute Respiratory Syndrome and Middle East Respiratory Syndrome. Comput. Struct. Biotechnol. J. 2019, 17, 186–194. [Google Scholar] [CrossRef] [PubMed]
- Müller, J.; Kretzschmar, M.; Dietz, K. Contact tracing in stochastic and deterministic epidemic models. Math. Biosci. 2000, 164, 39–64. [Google Scholar] [CrossRef]
- Huerta, R.; Tsimring, L.S. Contact tracing and epidemics control in social networks. Phys. Rev. E Stat. Nonlin. Soft Matter Phys. 2002, 66, 056115. [Google Scholar] [CrossRef] [PubMed]
- Lipsitch, M.; Cohen, T.; Cooper, B.; Robins, J.M.; Ma, S.; James, L.; Gopalakrishna, G.; Chew, S.K.; Tan, C.C.; Samore, M.H.; et al. Transmission dynamics and control of severe acute respiratory syndrome. Science 2003, 300, 1966–1970. [Google Scholar] [CrossRef] [PubMed]
- Hellewell, J.; Abbott, S.; Gimma, A.; Bosse, N.I.; Jarvis, C.I.; Russell, T.W.; Munday, J.D.; Kucharski, A.J.; Edmunds, W.J.; Sun, F.; et al. Feasibility of controlling COVID-19 outbreaks by isolation of cases and contacts. Lancet Glob. Health 2020, 8, e488–e496. [Google Scholar] [CrossRef]
- Farrahi, K.; Emonet, R.; Cebrian, M. Epidemic contact tracing via communication traces. PLoS ONE 2014, 9, e95133. [Google Scholar] [CrossRef] [PubMed]
- Yang, H.X.; Wang, W.X.; Lai, Y.C.; Wang, B.H. Traffic-driven epidemic spreading on networks of mobile agents. EPL (Europhys. Lett.) 2012, 98, 68003. [Google Scholar] [CrossRef]
- Leith, D.J.; Farrell, S. Coronavirus Contact Tracing: Evaluating the Potential of Using Bluetooth Received Signal Strength For Proximity Detection; Technical Report; School of Computer Science and Statistics, Trinity College: Dublin, Ireland, 2020. [Google Scholar]
- Kindt, P.H.; Chakraborty, T.; Chakraborty, S. How Reliable is Smartphone-based Electronic Contact Tracing for COVID-19? arXiv 2020, arXiv:2005.05625. [Google Scholar]
- Anglemyer, A.; Moore, T.; Parker, L.; Chambers, T.; Grady, A.; Chiu, K.; Parry, M.; Wilczynska, M.; Flemyng, E.; Bero, L. Digital contact tracing technologies in epidemics: A rapid review. Cochrane Database Syst. Rev. 2020. [Google Scholar] [CrossRef]
- Braithwaite, I.; Callender, T.; Bullock, M.; Aldridge, R.W. Automated and partly automated contact tracing: A systematic review to inform the control of COVID-19. Lancet Digit. Health 2020, 9, 5. [Google Scholar] [CrossRef]
- Ferretti, L.; Wymant, C.; Kendall, M.; Zhao, L.; Nurtay, A.; Abeler-Dorner, L.; Parker, M.; Bonsall, D.; Fraser, C. Quantifying SARS-CoV-2 transmission suggests epidemic control with digital contact tracing. Science 2020, 368, 6491. [Google Scholar] [CrossRef] [PubMed]
- Cencetti, G.; Santin, G.; Longa, A.; Pigani, E.; Barrat, A.; Cattuto, C.; Lehmann, S.; Lepri, B. Using real-world contact networks to quantify the effectiveness of digital contact tracing and isolation strategies for Covid-19 pandemic. medRxiv 2020. [Google Scholar] [CrossRef]
- Kretzschmar, M.E.; Rozhnova, G.; Bootsma, M.; van Boven, M.E.; van de Wijgert, J.; Bonten, M. Time is of the essence: Impact of delays on effectiveness of contact tracing for COVID-19. medRxiv 2020. [Google Scholar] [CrossRef]
- Lambert, A. A mathematical assessment of the efficiency of quarantining and contact tracing in curbing the COVID-19 epidemic. medRxiv 2020. [Google Scholar] [CrossRef]
- Sattler, F.; Ma, J.; Wagner, P.; Neumann, D.; Wenzel, M.; Schäfer, R.; Wiegand, T. Risk estimation of SARS-CoV-2 transmission from bluetooth low energy measurements. NPJ Digit. Med. 2020, 3, 1. [Google Scholar] [CrossRef]
- Pueyo, T. Coronavirus: How to Do Testing and Contact Tracing. Medium. 2020. Available online: https://medium.com/@tomaspueyo (accessed on 11 June 2020).
- Li, R.; Pei, S.; Chen, B.; Song, Y.; Zhang, T.; Yang, W.; Shaman, J. Substantial undocumented infection facilitates the rapid dissemination of novel coronavirus (SARS-CoV2). Science 2020, 368, 489–493. [Google Scholar] [CrossRef]
| Symbol | Definition |
|---|---|
| N | Population |
| Susceptible, Infected and Recovered classes | |
| Class of susceptible individuals in quarantine by contact tracing | |
| Class of infected individuals detected and quarantined. | |
| Class of infected individuals detected, quarantined and being traced. | |
| People quarantined by contact tracing. | |
| Basic/effective reproductive number () | |
| k | Average contacts per individual and time unit (days). |
| b | Probability to transmit the disease. |
| Detection rate of infected individuals | |
| Transmission rate | |
| Recovery rate (that is, = days to recover) | |
| Average duration of the quarantine | |
| Average duration of the remaining quarantine (that is, ) | |
| Average tracing time (also ) | |
| False negative ratio | |
| False positive ratio | |
| U | Ratio of user using the application |
| Ratio of users checking for exposure | |
| , | Estimated fraction of traced contacts (normalized) |
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Hernández-Orallo, E.; Calafate, C.T.; Cano, J.-C.; Manzoni, P. Evaluating the Effectiveness of COVID-19 Bluetooth-Based Smartphone Contact Tracing Applications. Appl. Sci. 2020, 10, 7113. https://doi.org/10.3390/app10207113
Hernández-Orallo E, Calafate CT, Cano J-C, Manzoni P. Evaluating the Effectiveness of COVID-19 Bluetooth-Based Smartphone Contact Tracing Applications. Applied Sciences. 2020; 10(20):7113. https://doi.org/10.3390/app10207113
Chicago/Turabian StyleHernández-Orallo, Enrique, Carlos T. Calafate, Juan-Carlos Cano, and Pietro Manzoni. 2020. "Evaluating the Effectiveness of COVID-19 Bluetooth-Based Smartphone Contact Tracing Applications" Applied Sciences 10, no. 20: 7113. https://doi.org/10.3390/app10207113
APA StyleHernández-Orallo, E., Calafate, C. T., Cano, J.-C., & Manzoni, P. (2020). Evaluating the Effectiveness of COVID-19 Bluetooth-Based Smartphone Contact Tracing Applications. Applied Sciences, 10(20), 7113. https://doi.org/10.3390/app10207113








