How to Obtain Common Criteria Certification of Smart TV for Home IoT Security and Reliability
Abstract
:1. Introduction
1.1. Acronyms
1.2. Related Works
2. Our Certification Process
2.1. EAL2 Analysis and Requirements
2.2. Security Target
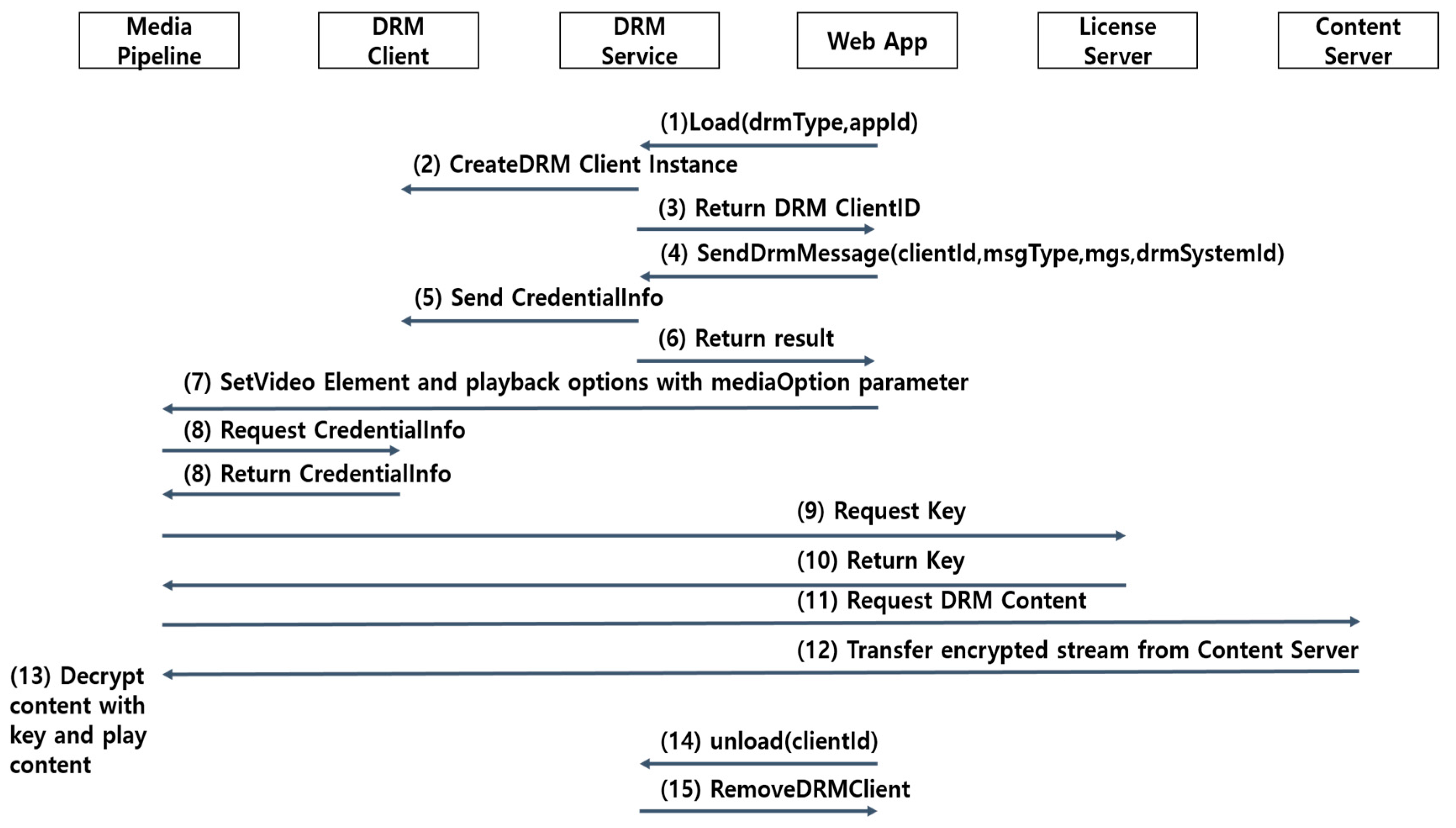
- (1)
- The Web App requests DRM Service to create DRM Client with load () method. The load () method requires DRM type and App ID.
- (2)
- The DRM Service creates DRM Client instance and returns its ID to Web App with a callback function.
- (3)
- The DRM Service sends to Return DRM Client ID to Web App.
- (4)
- The Web App uses sendDrmMessage () method to give DRM message to a DRM client. DRM message holds credential information in DRM message format.
- (5)
- The DRM Service sends Credential Information to DRM Client.
- (6)
- The DRM Client verifies DRM message and returns the result to Web App with a callback function.
- (7)
- The Web App gives a content target, DRM Client ID, and playback options to Media Pipeline with video element and mediaOption Parameter.
- (8)
- The Media Pipeline gets the credential information from DRM Client.
- (9)
- The Media Pipeline sends Request Key to License Server.
- (10)
- The License Server sends Return Key to Media Pipeline.
- (11)
- The Media Pipeline gets the License Key from the License Server. Media Pipeline requests it with credential information.
- (12)
- The Content Server sends encrypted stream to Media Pipeline.
- (13)
- The Media Pipeline decrypts DRM content stream with License Key and plays decrypted content stream.
- (14)
- The DRM Client must be removed with unload () method before unloading the App.
- (15)
- The DRM Service removes DRM Client.
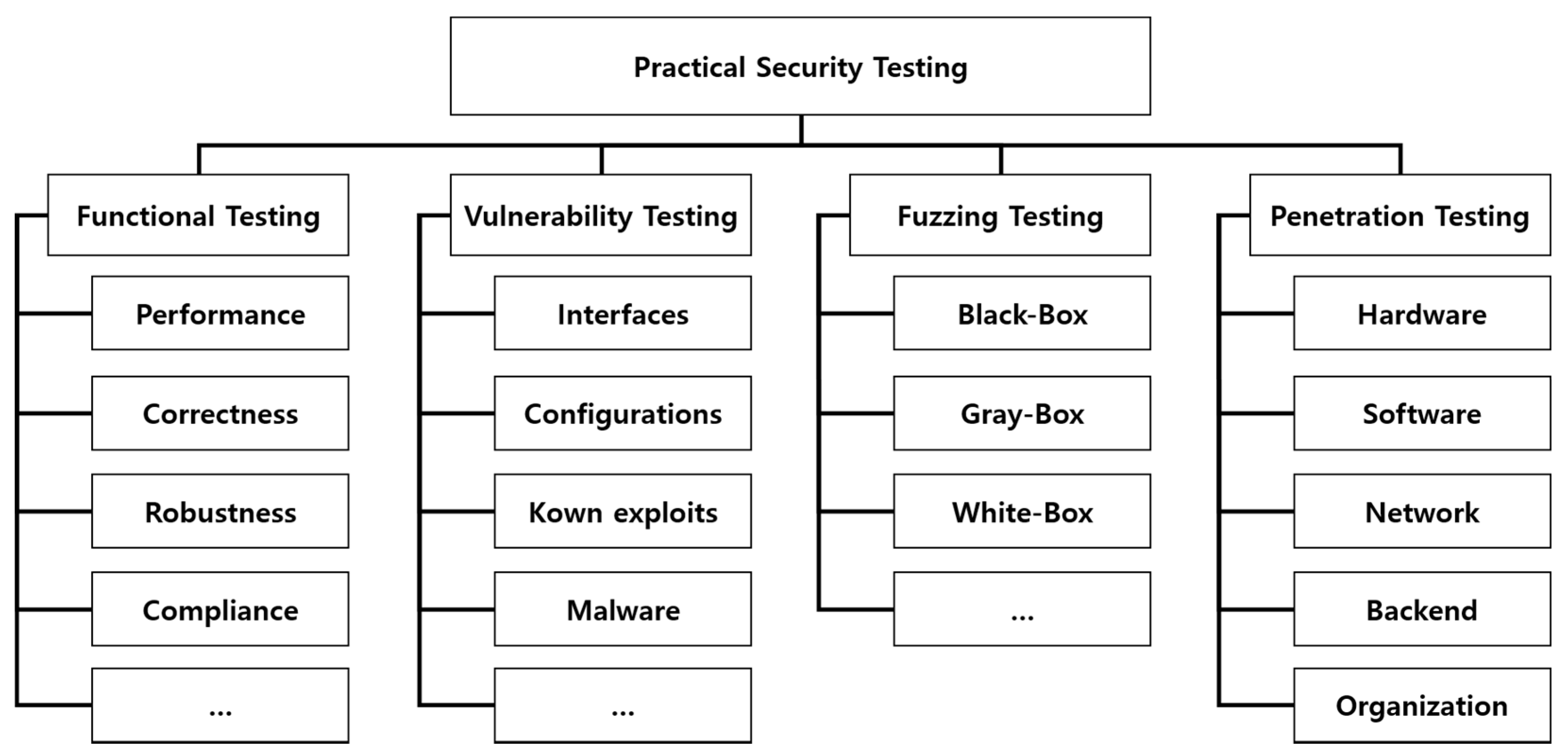
2.3. Test and Analysis
3. Lessons Learned
3.1. Lack of Previous Evaluations
3.2. Evaluation Assurance Level Decision
3.3. Simple design of security module
3.4. Life Cycle—Configuration management and Delivery
3.5. Certification Process Resources
4. Conclusions
Acknowledgments
Author Contributions
Conflicts of Interest
References
- Mustafa, A.; Jacob, J. Adapting the Cloud-COVER threat modelling tool to cover threats for the Internet of Things. In Proceedings of the Eighth York Doctoral Symposium on Computer Science and Electronics, York, UK, 28 October 2015. [Google Scholar]
- Ding, G.; Birgitta, L.; Gunnar, M.; Andler, S.F. Towards threat modeling for CPS-based critical infrastructure protection. In Proceedings of the 22nd International Emergency Management Society (TIEMS) Annual Conference, Rome, Italy, 30 September–2 October 2015; Volume 22. [Google Scholar]
- Wikileaks. Available online: https://wikileaks.org/ (accessed on 20 September 2017).
- Common Criteria Recognition Arrangement, Common Criteria for Information Technology Security Evaluation; Version 3.1; Revision 4; Centre for Cellular & Molecular Biology (CCMB): Telangana, India, 2012.
- All Things Apple. Available online: https://technology.ihs.com/ (accessed on 20 September 2017).
- Seigneur, J.M.; Jensen, C.D.; Farrell, S.; Gray, E.; Chen, Y. Towards security auto-configuration for smart appliances. In Proceedings of the Smart Objects Conference, Grenoble, France, 15–17 May 2003; Volume 2003. [Google Scholar]
- Bachy, Y.; Frédéric, B.; Vincent, N.; Eric, A.; Mohamed, K.; Jean-Christophe, C.; Pierre, L. Smart-TV security analysis: Practical experiments. In Proceedings of the 45th Annual IEEE/IFIP International Conference on Dependable Systems and Networks (DSN), Rio de Janeiro, Brazil, 22–25 June 2015. [Google Scholar]
- Benjamin, M.; Karpow, A. Watch and be watched: compromising all Smart TV generations. In Proceedings of the IEEE 11th Consumer Communications and Networking Conference (CCNC), Las Vegas, NV, USA, 10–13 January 2014. [Google Scholar]
- Lee, S.; Seungjoo, K. Hacking, surveilling and deceiving victims on Smart TV. In Blackhat; Legendary Entertainment: Burbank, CA, USA, 2013. [Google Scholar]
- Shankar, K.S.D.; Helmut, K. Certifying open source-the Linux experience. IEEE Secur. priv. 2004, 2, 28–33. [Google Scholar] [CrossRef]
- Raimund, G. How hackers are outsmarting Smart TV’s and why it matters to you. In Proceedings of the Rsa Conference Europe, Amsterdam, The Netherlands, 29–31 October 2013. [Google Scholar]
- Al Falayleh, M. A review of Smart TV forensics: Present state & future challenges. In Proceedings of the International Conference on Digital Information Processing, E-Business and Cloud Computing (DIPECC), Dubai, UAE, 9–11 April 2013. [Google Scholar]
- Sutherland, I.; Huw, R.; Konstantinos, X. Forensic analysis of Smart TV: A current issue and call to arms. Digit. Investig. 2014, 11, 175–178. [Google Scholar] [CrossRef]
- Sutherland, I.; Xynos, K.; Read, H.; Jones, A.; Drange, T. A forensic overview of the LG Smart TV. In Proceedings of the 12th Australian Digital Forensics Conference, Perth, Australia, 1–3 December 2014. [Google Scholar]
- Heesoo, K.; Minsu, P.; Seungjoo, K. (The First Experimental) Study on Smart TV forensics. Korea Inst. Inf. Secur. Cryptol. 2014, 24, 851–860. [Google Scholar]
- Minsu, P.; Heesoo, K.; Jaeki, K.; Seungjin, L.; Seungjoo, K. Developing a protection profile for Smart TV. In Proceedings of the 14th International Common Criteria Conference, New Delhi, India, 9–11 September 2014. [Google Scholar]
- Samsung Smart TV Security Solution V1.0 Security Target V1.5; Version 1.5; International Transplant Skin Cancer Collaborative (ITSCC): Milwaukee, WI, USA, 2016.
- Protection Profile for General Purpose Operating Systems; Version 4.1; Significant Revision; National Information Assurance Partnership (NIAP): Columbia, SC, USA, 2016.
- Protection Profile for Mobile Device Fundamentals; Version 2.0; National Information Assurance Partnership (NIAP): Columbia, SC, USA, 2014.
- Application Software Protection Profile (ASPP); Version 1.0; National Information Assurance Partnership (NIAP): Columbia, SC, USA, 2014.
- Protection Profile for Application Software; Version 1.2; National Information Assurance Partnership (NIAP): Columbia, SC, USA, 2016.
- Application Security Solution V1.0 for LG webOS TV Security Target V1.5; Version 1.5; National Information Assurance Partnership (NIAP): Columbia, SC, USA, 2017.
- Amini, A.; Jamil, N.; Ahmad, A.R.; Zaba, M.R. Threat modeling approaches for securing cloud computing. J. Appl. Sci. 2015, 15, 953–967. [Google Scholar]
- Di, J.; Scott, S. A hardware threat modeling concept for trustable integrated circuits. In Proceedings of the 2007 IEEE Region 5 Technical Conference, Fayetteville, AR, USA, 20–22 April 2007. [Google Scholar]
- Kornecki, A.J.; Janusz, Z. Threat Modeling for Aviation Computer Security. Available online: http://m.crosstalkonline.org/issues/22/200/ (accessed on 20 September 2017).
- Löhr, H.; Reza Sadeghi, A.; Stüble, C.; Weber, M.; Winandy, M. Modeling trusted computing support in a protection profile for high assurance security kernels. In Proceedings of the 2nd International Conference on Trusted Computing, Oxford, UK, 6–8 April 2009. [Google Scholar]
- ETAS K.K. Security Crash Test—Practical Security Evaluations of Automotive Onboard IT Components. Available online: https://www.semanticscholar.org/paper/Security-Crash-Test-Practical-Security-Evaluations-Bayer-Enderle/7e564242772ad55f3151f331024638e0c94675b1 (accessed on 20 September 2017).
- Michéle, B. Security & Privacy Implications. In Smart TV Security; Springer Briefs in Computer Science: Zürich, Switzerland, 2015; pp. 81–92. [Google Scholar]
| Acronyms | Description |
|---|---|
| ADV | Assurance DeVelopment Class |
| AGD | Assurance Guidance Documents Class |
| ALC | Assurance Life-Cycle Support Class |
| ARC | Security ARChitecture |
| ASE | Assurance Security Target Class |
| ATE | Assurance Teste Class |
| AVA | Assurance Vulnerability Analysis Class |
| CC | Common Criteria |
| CCDB | Common Criteria Development Board |
| cPP | Collaborative Protection Profiles |
| CCRA | Common Criteria Recognition Arrangement |
| CMC | Configuration Management Capabilities Component |
| CMS | Configuration Management Scope Component |
| DEL | Delivery Component |
| EAL | Evaluation Assurance Level |
| FAU | Security AUdit Function Component |
| FCS | Cryptographic Support Function Component |
| FDP | User Data Protection Function Component |
| FMT | Security ManagemenT Function Component |
| FPT | Protection of the TSF Function Component |
| FTP | Trusted Path/channels Function Component |
| FSP | Functional SPecification Component |
| iTC | International Technical Community |
| OPE | OPErational User Guidance Component |
| OR | Observation Report |
| PRE | PREparative Procedures Component |
| SAR | Security Assurance Requirement |
| SD | Supporting Document |
| SFR | Security Function Requirement |
| ST | Security Target |
| TDS | TOE DeSign |
| TOE | Target Of Evaluation |
| TSFI | TOE Security Function Interfaces |
| PP | Protection Profile |
| Class | Component | Description | Submissions |
|---|---|---|---|
| ADV | ADV_ARC.1 | Security architecture description | Security architecture submission |
| ADV_FSP.2 | Security-enforcing functional Specification | Functional specification submission | |
| ADV_TDS.1 | Basic design | TOE design submission | |
| AGD | AGD_OPE.1 | Operational user guidance | Manual submission |
| AGD_PRE.1 | Preparative procedures | ||
| ALC | ALC_CMC.2 | Use of a CM system | Configuration management submission |
| ALC_CMS.2 | Parts of the TOE CM coverage | ||
| ALC_DEL.1 | Delivery procedures | Delivery submission | |
| ASE | ASE_CCL.1 | Conformance claims | Security Target |
| ASE_ECD.1 | Extended components definition | ||
| ASE_INT.1 | ST introduction | ||
| ASE_OBJ.2 | Security objectives | ||
| ASE_REQ.2 | Derived security requirements | ||
| ASE_SPD.1 | Security problem definition | ||
| ASE_TSS.1 | TOE summary specification | ||
| ATE | ATE_COV.1 | Evidence of coverage | Test submission |
| ATE_FUN.1 | Functional testing | ||
| ATE_IND.2 | Independent testing—sample | ||
| AVA | AVA_VAN.2 | Vulnerability analysis | Vulnerability analysis submission |
| PP Name | Protection Profile for General Purpose Operating Systems [18] | Protection Profile for Mobile Device Fundamentals [19] | Application Software Protection Profile (ASPP) [20] | Protection Profile for Application Software [21] | Smart TV Security Target [22] |
|---|---|---|---|---|---|
| Date | 9 March 2016 | 17 September 2014 | 10 November 2014 | 22 April 2016 | 19 April 2017 |
| EAL | EAL1 | EAL1 | EAL1 | EAL1 | EAL2 |
| Function | Kernel | Mobile Device | DRM | Application | Smart TV |
| Threat | T.NETWORK_ATTACK | T.NETWORK Network Attack | T.PLAINTEXT_DATA_SPOOFING | T.NETWORK_ATTACK | T.Modifying App Package File |
| T.NETWORK_EAVESDROP | T.EAVESDROP Network Eavesdropping | T.PLAINTEXT_DATA_SPOOFING | T.NETWORK_EAVESDROP | T.Modifying App Package File | |
| T.LOCAL_ATTACK | ㅡ | T.KEYING_MATERIAL_COMPROMISE T.KEYSPACE_EXHAUST T.PLAINTEXT_COMPROMISE T.TSF_FAILURE T.UNSAFE_AUTHFACTOR_VERIFICATION | T.LOCAL_ATTACK | T.Unauthorized Access To Other App’s Execution Domain | |
| T.LIMITED_PHYSICAL_ACCESS | T.PHYSICAL Physical Access | T.UNAUTHORIZED_DATA_ACCESS | T.PHYSICAL_ACCESS | T.Unauthorized Access To Smart TV Assets | |
| — | T.FLAWAPP Malicious or Flawed Application | — | — | T.Unauthorized App Installation T.Modifying App Package File | |
| — | T.PERSISTENT Persistent Presence | — | — | T.Unauthorized Access To Smart TV Assets | |
| — | — | — | — | T.App Copyright Infringement | |
| Security Objectives | O.ACCOUNTABILITY | O.AUTH Authorization and Authenticatio | O.AUTHORIZATION, O.DATA_AUTHENTICATION | — | O.App Package File Verification O.App Contents Protection |
| O.INTEGRITY | O.INTEGRITY Mobile Device Integrit | — | O.INTEGRITY | O.App Contents Protection | |
| O.MANAGEMENT | O.CONFIG Mobile Device Configuration | O.WIPE_MEMORY O.SAFE_AUTHFACTOR_VERIFICATION | O.MANAGEMENT | O.App Access Control | |
| O.PROTECTED_STORAGE | O.STORAGE Protected Storage | O.KEY_MATERIAL_PROTECTION O.FEK_SECURITY O.PROTECT_DATA | O.PROTECTED_STORAGE | P.Secure Key Operation Management | |
| O.PROTECTED_COMMS | O.COMMS Protected Communication | — | O.PROTECTED_COMMS | O.App Contents Protection O.App Access Control P.Secure Smart TV Update | |
| — | — | — | O.QUALITY | P.Secure Key Operation Management P.Secure Smart TV Update |
© 2017 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Kang, S.; Kim, S. How to Obtain Common Criteria Certification of Smart TV for Home IoT Security and Reliability. Symmetry 2017, 9, 233. https://doi.org/10.3390/sym9100233
Kang S, Kim S. How to Obtain Common Criteria Certification of Smart TV for Home IoT Security and Reliability. Symmetry. 2017; 9(10):233. https://doi.org/10.3390/sym9100233
Chicago/Turabian StyleKang, Sooyoung, and Seungjoo Kim. 2017. "How to Obtain Common Criteria Certification of Smart TV for Home IoT Security and Reliability" Symmetry 9, no. 10: 233. https://doi.org/10.3390/sym9100233
APA StyleKang, S., & Kim, S. (2017). How to Obtain Common Criteria Certification of Smart TV for Home IoT Security and Reliability. Symmetry, 9(10), 233. https://doi.org/10.3390/sym9100233




