Decentralized Broadcast Encryption Schemes with Constant Size Ciphertext and Fast Decryption
Abstract
1. Introduction
- Level 1: At the setup phase, all users in the system collude to generate the secret key for each user as well as the public parameters of the system. After the setup phase, only the user knows his/her secret key, the collusion of all other users cannot derive his/her secret key. In addition, no more new users can be added to the system after the setup phase.
- Level 2: This is similar to Level 1 except that after the setup phase new users can still be added to the system. More precisely, each user colluding at the setup phase plays the role of an authority to generate a partial secret key for a new user. The full secret key of the new user is built from all of these partial secret keys. This level obviously deals well with the problem of trusting a single authority with the keys, but does not handle the bottleneck problem. The reason is that if anyone of the authorities is malfunctioning, the full secret key of a new user cannot be built. We note that the certificateless scheme [7,8,9] is in fact equivalent to Level 2 since it deals well with the users’ security aspect but does not handle the problem of bottleneck.
- Level 3: To deal with the problem of malfunctioning authority in Level 2, in this level, the system is able to revoke the right of generating partial secret keys for new users from a malfunctioning authority. This leads to the fact that a new user does not need to receive the partial secret key from this failing authority to build his/her full secret key. In other words, new users can still be added to the system despite the presence of malfunctioning authorities. New users could not be added to the system only if all authorities in the system are malfunctioning.
1.1. Related Work
1.2. Our Contributions
- constant-size ciphertext;
- constant-size secret key: in our first scheme, the secret key includes a maximum of two elements;
- fast decryption: to decrypt, the user only computes two Pairings in the prime order setting;
- decryption key size is linear in the maximum number of users in the system;
- The scheme is categorized as Level 2.
1.3. Paper Organization
2. Preliminaries
2.1. Decentralized Broadcast Encryption
- The first type is called key user. Key users take charge of generating partial secret keys for users in the system.
- The second type is called usual user who receives broadcast messages but does not participate in generating partial secret keys.
2.2. Security Model
2.3. Bilinear Maps
- ;
- if and then ;
- we can efficiently compute .
- if , it is in Type 1 Pairings
- if and there is an efficiently computable homomorphism , it is in Type 2 Pairings
- if and there are no efficiently computable homomorphism between and , it is in Type 3 Pairings
2.4. Linear Secret Sharing Matrix
3. First Scheme
3.1. Construction
3.2. Security
- First, chooses a usual user or a key user, then requests to know his/her secret key. To avoid the trivial attack, can only ask to know at most secret keys of key users, and obviously these key users are in the revoked set ;
- requests a part of the secret key of either usual user or key user who does not belong to the revoked set , that is . The reason why is able to make this query is that this part of the secret key is stored in the public server.
4. Second Scheme
- First, the system requires that user’s full secret key now includes partial secret keys, which are generated by key users from 1 to . This means when a new user is added to the system, this new user does not need to obtain the partial secret key from user n. In other words, even if user n is malfunctioning, we still can add a new user to the system.
- Second, the system updates the as
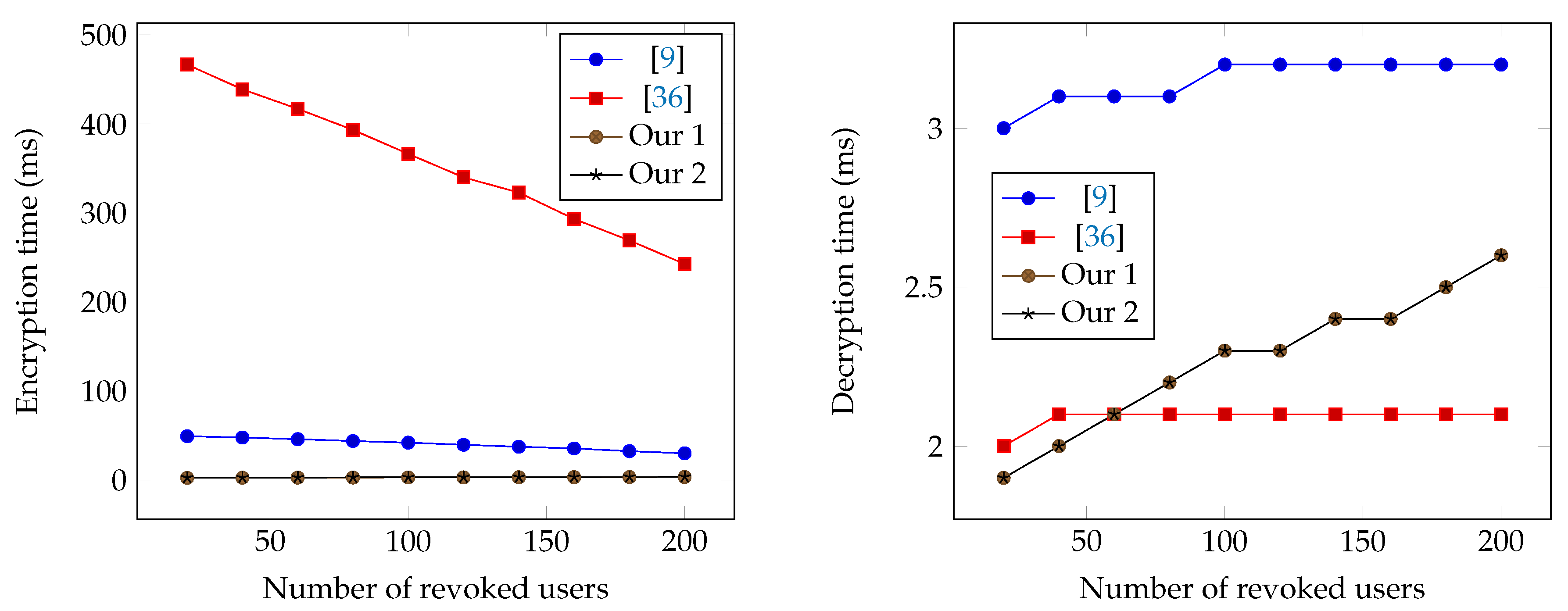
5. Performance Analysis
- the public parameters may not need to be stored permanently on the client and can be accessed on demand from a non-weak server with large computational resources. Moreover, keys are typically much more smaller than the data and/or its ciphertext in real-life scenarios. For example, consider using Broadcast encryption scheme for sharing files in a cloud storage system that encrypts files. The number of users N sharing access to a particular repository is typically limited. Therefore, the files ciphertexts are typically much larger than the public (which is for the proposed algorithms) or the constant-size secret key.
- although selective security is more limited than adaptive security, researchers nowadays agree that selective security is also acceptable for practical applications. In fact, many proposed schemes today only achieve this level of security for both broadcast encryption schemes [2,21,26,37] and attribute-based encryption schemes [20,38,39], to name a few. Particularly, the BGW scheme [2] now is used widely in Pay-TV systems. Finally, if we would like to achieve adaptive security, we may make use of some existing tools such as [40] to generically transform a selective security scheme to an adaptive security scheme with a cost to pay in efficiency. Note that Functional encryption () [6] is a generalization of , so this technique is directly applied to our proposed schemes. Note that in this paper we focus on the efficiency, so we omit this transformation.
6. Conclusions
- constant-size ciphertext;
- constant-size secret key: the secret key includes a maximum of two elements;
- fast decryption: to decrypt, the user only computes two Pairings in the prime order setting;
- decryption key size is linear in the maximum number of users in the system;
- supporting for level 2 decentralization, where new users can be added to the system dynamically.
Author Contributions
Funding
Conflicts of Interest
Appendix A. Summary of Used Symbols
| Term | Description | Term | Description |
|---|---|---|---|
| N | Total number of users in the system | Secret key for user i | |
| S | Target set of valid key users | K | Symmetric session key |
| Set of revoked users | Session key space | ||
| r | Number of revoked users | Public parameters | |
| ℓ | Size of the access policy | Adversary | |
| n | Number of key users (or attribute authorities) | Challenger | |
| Security parameter | Simulator | ||
| ABE | Attribute based encryption | BE | Broadcast encryption |
| LSS | Linear secret sharing | FE | Functional encryption |
| SM | Standard model | ROM | Random oracle model |
| DDH | Decision Diffie-Hellman | CBDH | Computational bilinear Diffie-Hellman |
| BDHE | Bilinear Diffie-Hellman exponent | MBDHE | Modified BDHE |
References
- Fiat, A.; Naor, M. Broadcast encryption. In Lecture Notes in Computer Science, Proceedings of the Annual International Cryptology Conference, Santa Barbara, CA, USA, 22–26 August 1994; Stinson, D.R., Ed.; Springer: Berlin/Heidelberg, Germany, 1994; Volume 773, pp. 480–491. [Google Scholar]
- Boneh, D.; Gentry, C.; Waters, B. Collusion Resistant Broadcast Encryption with Short Ciphertexts and Private Keys. In Lecture Notes in Computer Science, Proceedings of the Annual International Cryptology Conference, Barbara, CA, USA, 14–18 August 2005; Shoup, V., Ed.; Springer: Berlin/Heidelberg, Germany, 2005; Volume 3621, pp. 258–275. [Google Scholar]
- Naor, D.; Naor, M.; Lotspiech, J. Revocation and tracing schemes for stateless receivers. In Lecture Notes in Computer Science, Proceedings of the Annual International Cryptology Conference, Santa Barbara, CA, USA, 19–23 August 2001; Kilian, J., Ed.; Springer: Berlin/Heidelberg, Germany, 2001; Volume 2139, pp. 41–62. [Google Scholar]
- Shamir, A. Identity-based cryptosystems and signature schemes. In Lecture Notes in Computer Science, Proceedings of the Advances in Cryptology—CRYPTO’84, Santa Barbara, CA, USA, 19–22 August 1984; Blakley, G.R., Chaum, D., Eds.; Springer: Berlin/Heidelberg, Germany, 1984; Volume 196. [Google Scholar]
- Sahai, A.; Waters, B. Fuzzy identity-based encryption. In Lecture Notes in Computer Science, Proceedings of the Advances in Cryptology—EUROCRYPT 2005, Aarhus, Denmark, 22–26 May 2005; Cramer, R., Ed.; Springer: Berlin/Heidelberg, Germany, 2005; Volume 3494, pp. 457–473. [Google Scholar]
- Boneh, D.; Sahai, A.; Waters, B. Functional encryption: Definitions and challenges. In Lecture Notes in Computer Science, Proceedings of the TCC 2011, Providence, RI, USA, 28–30 March 2011; Springer: Berlin/Heidelberg, Germany, 2011; pp. 253–273. [Google Scholar]
- Al-Riyami, S.S.; Paterson, K.G. Certificateless public key cryptography. In Lecture Notes in Computer Science, Proceedings of the Advances in Cryptology—ASIACRYPT 2003, Taipei, Taiwan, 30 November–4 December 2003; Laih, C.-S., Ed.; Springer: Berlin/Heidelberg, Germany, 2003; Volume 2894, pp. 452–473. [Google Scholar]
- Gentry, C. Certificate-based encryption and the certificate revocation problem. In Lecture Notes in Computer Science, Proceedings of the Advances in Cryptology—EUROCRYPT 2003, Warsaw, Poland, 4–8 May 2003; Biham, E., Ed.; Springer: Berlin/Heidelberg, Germany, 2003; Volume 2656, pp. 272–293. [Google Scholar]
- Li, J.; Chen, L.; Lu, Y.; Zhang, Y. Anonymous certificate-based broadcast encryption with constant decryption cost. Inf. Sci. 2018, 454–455, 110–127. [Google Scholar] [CrossRef]
- Abdalla, M.; Benhamouda, F.; Kohlweiss, M.; Waldner, H. Decentralizing Inner-Product Functional Encryption. In Lecture Notes in Computer Science, Proceedings of the Public-Key Cryptography (PKC 2019), Beijing, China, 14–17 April 2019; Lin, D., Sako, K., Eds.; Springer: Cham, Switzerland, 2019; Volume 11443, pp. 128–157. [Google Scholar]
- Chotard, J.; Sans, E.D.; Gay, R.; Phan, D.H.; Pointcheval, D. Decentralized Multi-Client Functional Encryption for Inner Product. In Lecture Notes in Computer Science, Proceedings of the Advances in Cryptology—ASIACRYPT 2018, Brisbane, QLD, Australia, 2–6 December 2018; Springer: Berlin/Heidelberg, Germany, 2018; Volume 11273, pp. 703–732. [Google Scholar]
- Chase, M. Multi-authority attribute based encryption. In Proceedings of the Theory of Cryptography: 4th Theory of Cryptography Conference (TCC 2007), Amsterdam, The Netherlands, 21–24 February 2007; Springer: Berlin/Heidelberg, Germany, 2007; pp. 515–534. [Google Scholar]
- Chase, M.; Chow, S.S.M. Improving privacy and security in multi-authority attribute-based encryption. In Proceedings of the 16th ACM Conference on Computer and Communications Security (CCS ’09), Hyatt Regency, Chicago, Chicago, IL, USA, 9–13 November 2009; ACM: New York, NY, USA, 2009; pp. 121–130. [Google Scholar]
- Ma, C.; Ge, A.; Zhang, J. Fully Secure Decentralized Ciphertext-Policy Attribute-Based Encryption in Standard Model. In Proceedings of the Information Security and Cryptology: Inscrypt, Nanjing, China, 6–8 December 2019; Springer: Berlin/Heidelberg, Germany, 2019. [Google Scholar] [CrossRef]
- Lewko, A.; Waters, B. Decentralizing attribute-based encryption. In Lecture Notes in Computer Science, Proceedings of the Advances in Cryptology—EUROCRYPT 2011, Tallinn, Estonia, 15–19 May 2011; Paterson, K.G., Ed.; Springer: Berlin/Heidelberg, Germany, 2011; pp. 568–588. [Google Scholar]
- Lin, H.; Cao, Z.; Liang, X.; Shao, J. Secure threshold multi authority attribute based encryption without a central authority. In Proceedings of the Cryptology—INDOCRYPT 2008: 9th International Conference on Cryptology in India, Kharagpur, India, 14–17 December 2008; Springer: Berlin/Heidelberg, Germany, 2008; pp. 426–436. [Google Scholar]
- Liu, Z.; Cao, Z.; Huang, Q.; Wong, D.S.; Yuen, T.H. Fully secure multi-authority ciphertext-policy attribute-based encryption without random oracles. In Proceedings of the Computer Security ESORICS 2011: 16th European Symposium on Research in Computer Security, Leuven, Belgium, 12–14 September 2011; Springer: Berlin/Heidelberg, Germany, 2011; pp. 278–297. [Google Scholar]
- Müller, S.; Katzenbeisser, S.; Eckert, C. Distributed attribute-based encryption. In Proceedings of the Information Security and Cryptology ICISC 2008: 11th International Conference, Seoul, Korea, 3–5 December 2008; Springer: Berlin/Heidelberg, Germany, 2009. [Google Scholar]
- Phan, D.-H.; Pointcheval, D.; Strefler, M. Decentralized Dynamic Broadcast Encryption. In Lecture Notes in Computer Science, Proceedings of the SCN 2012: International Conference on Security and Cryptography for Networks, Amalfi, Italy, 5–7 September 2012; Lopez, J., Tsudik, G., Eds.; Springer: Berlin/Heidelberg, Germany, 2012; Volume 7485, pp. 166–183. [Google Scholar]
- Rouselakis, Y.; Waters, B. Efficient statically-secure large-universe multi-authority attribute-based encryption. In Lecture Notes in Computer Science, Proceedings of the FC 2015: 19th International Conference on Financial Cryptography and Data Security, San Juan, PR, USA, 26–30 January 2015; Springer: Berlin/Heidelberg, Germany, 2015; pp. 315–332. [Google Scholar]
- Acharya, K.; Dutta, R. Recipient revocable broadcast encryption schemes without random oracles. In Lecture Notes in Computer Science, Proceedings of the ICISC 2017: 20th International Conference on Information Security and Cryptology, Seoul, Korea, 29 November–1 December 2017; Springer: Cham, Switzerland, 2018; Volume 10779, ISBN 978-3-319-78555-4. [Google Scholar]
- Acharya, K.; Dutta, R. Adaptively secure broadcast encryption with dealership. In Lecture Notes in Computer Science, Proceedings of the ICISC 2016: 19th International Conference on Information Security and Cryptology, Seoul, Korea, 30 November–2 December 2016; Springer: Berlin/Heidelberg, Germany, 2017; pp. 161–177. [Google Scholar]
- Agrawal, S.; Bhattacherjee, S.; Phan, D.H.; Stehlé, D.; Yamada, S. Efficient public trace and revoke from standard assumptions: Extended abstract. In Proceedings of the 2017 ACM SIGSAC Conference on Computer and Communications Security, CCS 2017, Dallas, TX, USA, 30 October–3 November 2017; ACM: New York, NY, USA, 2017. ISBN 978-1-4503-4946-8. [Google Scholar]
- Boneh, D.; Sahai, A.; Waters, B. Fully collusion resistant traitor tracing with short ciphertexts and private keys. In Lecture Notes in Computer Science, Proceedings of the Advances in Cryptology—EUROCRYPT 2006, St. Petersburg, Russia, 28 May–1 June 2006; Vaudenay, S., Ed.; Springer: Berlin/Heidelberg, Germany, 2006; Volume 4004, pp. 573–592. [Google Scholar]
- Boneh, D.; Waters, B.; Zhandry, M. Low overhead broadcast encryption from multilinear maps. In Lecture Notes in Computer Science, Proceedings of the Advances in Cryptology—CRYPTO 2014, Part I, Santa Barbara, CA, USA, 17–21 August 2014; Garay, J.A., Gennaro, R., Eds.; Springer: Berlin/Heidelberg, Germany, 2014; Volume 8616, pp. 206–223. [Google Scholar]
- Delerablée, C. Identity-based broadcast encryption with constant size ciphertexts and private keys. In Lecture Notes in Computer Science, Proceedings of the Advances in Cryptology – ASIACRYPT 2007, Kuching, Malaysia, 2–6 December 2007; Kurosawa, K., Ed.; Springer: Berlin/Heidelberg, Germany, 2007; Volume 4833, pp. 200–215. [Google Scholar]
- Dodis, Y.; Fazio, N. Public key trace and revoke scheme secure against adaptive chosen ciphertext attack. In Lecture Notes in Computer Science, Proceedings of the PKC 2003: 6th International Workshop on Theory and Practice in Public Key Cryptography, Miami, FL, USA, 6–8 January 2003; Desmedt, Y., Ed.; Springer: Berlin/Heidelberg, Germany, 2003; Volume 2567, pp. 100–115. [Google Scholar]
- Gentry, C.; Waters, B. Adaptive security in broadcast encryption systems (with short ciphertexts). In Lecture Notes in Computer Science, Proceedings of the Advances in Cryptology—EUROCRYPT 2009, Cologne, Germany, 26–30 April 2009; Joux, A., Ed.; Springer: Berlin/Heidelberg, Germany, 2009; Volume 5479, pp. 171–188. [Google Scholar]
- Lewko, A.B.; Sahai, A.; Waters, B. Revocation systems with very small private keys. In Proceedings of the 2010 IEEE Symposium on Security and Privacy, Oakland, CA, USA, 16–19 May 2010; IEEE Computer Society Press: Washington, DC, USA, 2010; pp. 273–285. [Google Scholar]
- Phan, D.H.; Pointcheval, D.; Shahandashti, S.F.; Strefler, M. Adaptive CCA broadcast encryption with constant-size secret keys and ciphertexts. In Proceedings of the ACISP 12: 17th Australasian Conference on Information Security and Privacy, Wollongong, NSW, Australia, 9–11 July 2012; Susilo, W., Mu, Y., Seberry, J., Eds.; Springer: Berlin/Heidelberg, Germany, 2012; Volume 7372, pp. 308–321. [Google Scholar]
- Phan, D.H.; Pointcheval, D.; Strefler, M. Security notions for broadcast encryption. In Lecture Notes in Computer Science, Proceedings of the ACNS 11: 9th International Conference on Applied Cryptography and Network Security, Nerja, Spain, 7–10 June 2011; Lopez, J., Tsudik, G., Eds.; Springer: Berlin/Heidelberg, Germany, 2011; Volume 6715, pp. 377–394. [Google Scholar]
- Susilo, W.; Chen, R.; Guo, F.; Yang, G.; Mu, Y.; Chow, Y.-W. Recipient revocable identity-based broadcast encryption: How to revoke some recipients in IBBE without knowledge of the plaintext. In Proceedings of the ASIACCS 16: 11th ACM Symposium on Information, Computer and Communications Security, Xi’an, China, 30 May–3 June 2016; ACM Press: New York, NY, USA, 2016; pp. 201–210. [Google Scholar]
- Qiao, H.; Ba, H.; Zhou, H.; Wang, Z.; Ren, J.; Hu, Y. Practical, Provably Secure, and Black-Box Traceable CP-ABE for Cryptographic Cloud Storage. Symmetry 2018, 10, 482. [Google Scholar] [CrossRef]
- Canard, S.; Phan, D.H.; Trinh, V.C. An Attribute-based Broadcast Encryption Scheme For Lightweight Devices. IET Inf. Secur. 2018, 12, 52–59. [Google Scholar] [CrossRef]
- Xu, Q.; Tan, C.; Fan, Z.; Zhu, W.; Xiao, Y.; Cheng, F. Secure Data Access Control for Fog Computing Based on Multi-Authority Attribute-Based Signcryption with Computation Outsourcing and Attribute Revocation. Sensors 2018, 18, 1609. [Google Scholar] [CrossRef] [PubMed]
- Malluhi, Q.; Shikfa, A.; Tran, V.; Trinh, V.C. Decentralized ciphertext-policy attribute-based encryption schemes for lightweight devices. Comput. Commun. 2019, 145, 113–125. [Google Scholar] [CrossRef]
- Acharya, K.; Dutta, R. Constructions of Secure Multi-Channel Broadcast Encryption Schemes in Public Key Framework. In Lecture Notes in Computer Science, Proceedings of the CANS 2018: International Conference on Cryptology and Network Security, Naples, Italy, 30 September–3 October 2018; Springer: Berlin/Heidelberg, Germany, 2018; Volume 11124, ISBN 978-3-030-00434-7. [Google Scholar]
- Hohenberger, S.; Waters, B. Attribute-based encryption with fast decryption. In Lecture Notes in Computer Science, Proceedings of the PKC 2013: 16th International Workshop on Theory and Practice in Public Key Cryptography, Nara, Japan, 26 February–1 March 2013; Kurosawa, K., Hanaoka, G., Eds.; Springer: Berlin/Heidelberg, Germany, 2013; Volume 7778, pp. 162–179. [Google Scholar]
- Rouselakis, Y.; Waters, B. Practical constructions and new proof methods for large universe attribute-based encryption. In Proceedings of the ACM CCS 13: 20th Conference on Computer and Communications Security, Berlin, Germany, 4–8 November 2013; Sadeghi, A.R., Gligor, V.D., Yung, M., Eds.; ACM Press: New York, NY, USA, 2013; pp. 463–474. [Google Scholar]
- Ananth, P.; Brakerski, Z.; Segev, G.; Vaikuntanathan, V. From Selective to Adaptive Security in Functional Encryption. In Lecture Notes in Computer Science, Proceedings of the Advances in Cryptology—CRYPTO 2015, Santa Barbara, CA, USA, 16–20 August 2015; Gennaro, R., Robshaw, M., Eds.; Springer: Berlin/Heidelberg, Germany, 2015; Volume 9216, p. 9216. [Google Scholar]
- Lynn, B. The Stanford Pairing Based Crypto Library. Available online: http://crypto.stanford.edu/pbc (accessed on 5 June 2020).

| Ciphertext | Decryption Key | Secret Key | System Public Storage | Dec Time | |
|---|---|---|---|---|---|
| [19] | |||||
| [9] | 1 | ||||
| [18] | |||||
| [15] | |||||
| [17] | |||||
| [20] | |||||
| [14] | |||||
| [36] | 1 | ||||
| Ours 1 | 2 | 1 | |||
| Ours 2 | 2 | n |
| Security Model | Pairings | Decentralizing Tech | Assumption | |
|---|---|---|---|---|
| [19] | Adaptive+SM | no | Level 2 | DDH |
| [9] | Adaptive+ROM | Type 1 | Level 2 | CBDH |
| [18] | Generic group | Type 1 | ABE | Generic group |
| [15] | Adaptive+ROM | Composite | ABE | Subgroup decision |
| [17] | Adaptive+SM | Composite | ABE | Subgroup decision |
| [20] | Selective+ROM | Type 1 | ABE | q-DPBDHE2 |
| [14] | Adaptive+SM | Composite | ABE | Subgroup decision |
| [36] | Selective+SM | Type 1 | ABE | Modified-BDHE |
| Ours 1 | Selective+SM | Type 3 | Level 2 | MBDHE |
| Ours 2 | Weak Selective+SM | Type 3 | Level 3 | MBDHE |
| Target Users | [9] | [36] | Ours 1 | Ours 2 | |||||
|---|---|---|---|---|---|---|---|---|---|
| Enc Time | Dec Time | Enc Time | Dec Time | Enc Time | Dec Time | Enc Time | Dec Time | ||
| 3 | |||||||||
| 3 | |||||||||
| 2 | 2 | ||||||||
| 24 | 3 | ||||||||
| 3 | 2 | 2 | |||||||
| 3 | |||||||||
| 3 | |||||||||
| 3 | 3 | ||||||||
| 3 | 326 | ||||||||
| 841 | |||||||||
| 45 | 3 | ||||||||
| Target Users | Ciphertext | Secret Key | User Public Storage | |||||||
|---|---|---|---|---|---|---|---|---|---|---|
| [9,36] | Ours 1, 2 | [9,36] | Ours 1 | Ours 2 | [9] | [36] | Ours 1 | Ours 2 | ||
| 5915 | 130 | 65 | 65 | 650 | 6695 | 6825 | ||||
| 5265 | ||||||||||
| 4615 | ||||||||||
| 130 | 65 | 65 | 650 | |||||||
| 9165 | ||||||||||
| 130 | 65 | 65 | 650 | |||||||
| 130 | 65 | 65 | 650 | |||||||
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Malluhi, Q.; Tran, V.D.; Trinh, V.C. Decentralized Broadcast Encryption Schemes with Constant Size Ciphertext and Fast Decryption. Symmetry 2020, 12, 969. https://doi.org/10.3390/sym12060969
Malluhi Q, Tran VD, Trinh VC. Decentralized Broadcast Encryption Schemes with Constant Size Ciphertext and Fast Decryption. Symmetry. 2020; 12(6):969. https://doi.org/10.3390/sym12060969
Chicago/Turabian StyleMalluhi, Qutaibah, Vinh Duc Tran, and Viet Cuong Trinh. 2020. "Decentralized Broadcast Encryption Schemes with Constant Size Ciphertext and Fast Decryption" Symmetry 12, no. 6: 969. https://doi.org/10.3390/sym12060969
APA StyleMalluhi, Q., Tran, V. D., & Trinh, V. C. (2020). Decentralized Broadcast Encryption Schemes with Constant Size Ciphertext and Fast Decryption. Symmetry, 12(6), 969. https://doi.org/10.3390/sym12060969





