Figure 1.
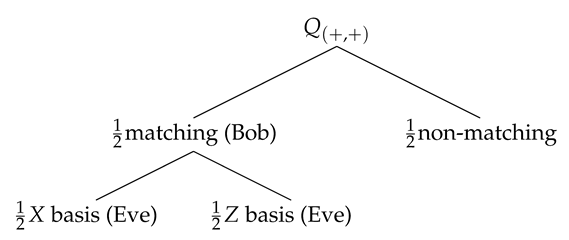
BB84 pulses represented in the Bloch sphere. The quantum states prepared by Alice (left) could be , , , and the measurement bases Bob could apply are X and Z (right).
Figure 1.
BB84 pulses represented in the Bloch sphere. The quantum states prepared by Alice (left) could be , , , and the measurement bases Bob could apply are X and Z (right).
Figure 2.
We represent pairs of quantum states: (a) orthogonal pairs (, ) and (, ), (b) non-orthogonal pairs (, ), (, ), (, ) and (, ) and (c) parallel pairs (, ), (, ),(, ) and (, ).
Figure 2.
We represent pairs of quantum states: (a) orthogonal pairs (, ) and (, ), (b) non-orthogonal pairs (, ), (, ), (, ) and (, ) and (c) parallel pairs (, ), (, ),(, ) and (, ).
Figure 3.
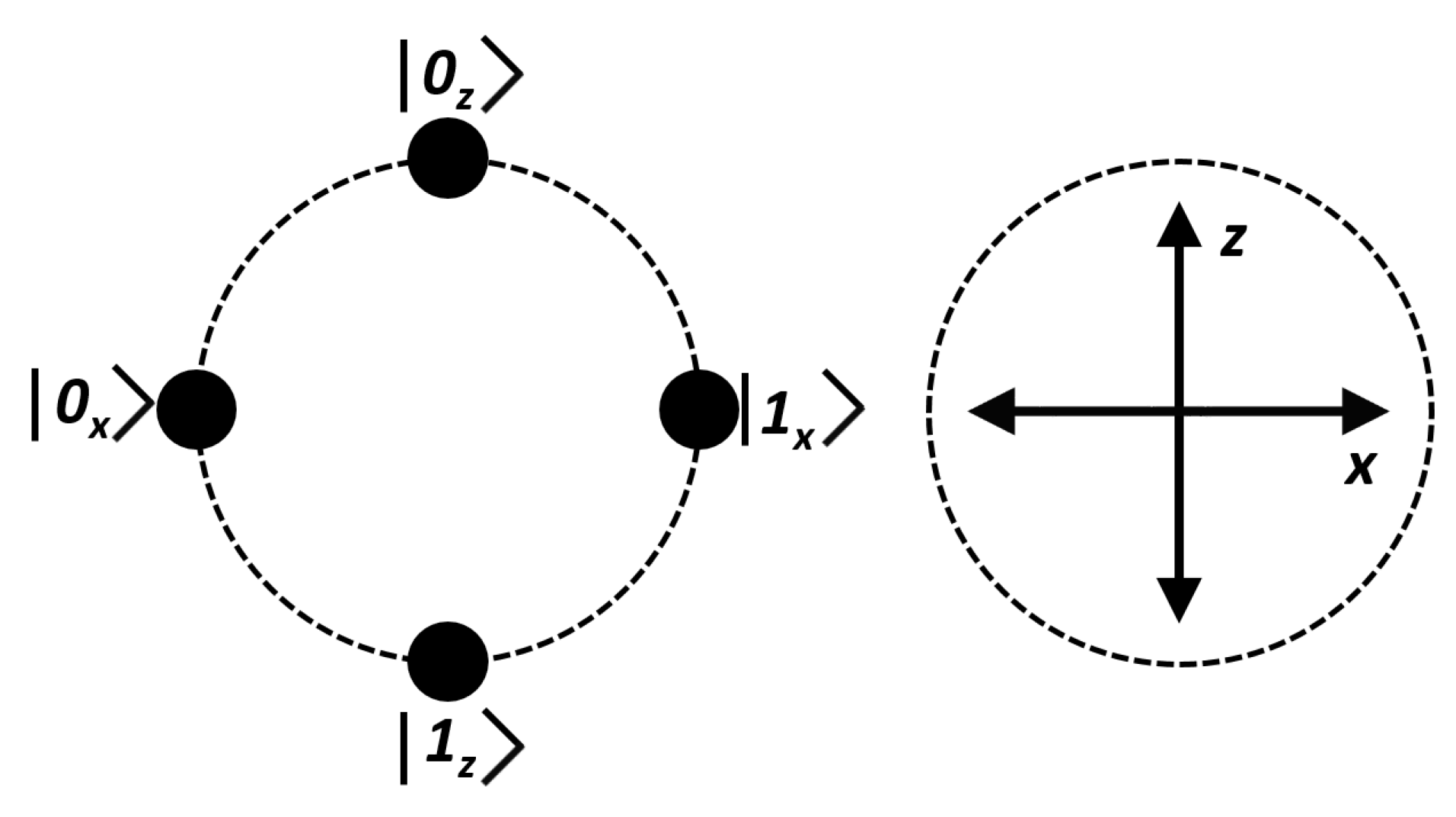
Alice sends the non-orthogonal pair to Bob. After a double matching detection event is produced at Bob’s optical system it could register or .
Figure 3.
Alice sends the non-orthogonal pair to Bob. After a double matching detection event is produced at Bob’s optical system it could register or .
Figure 4.
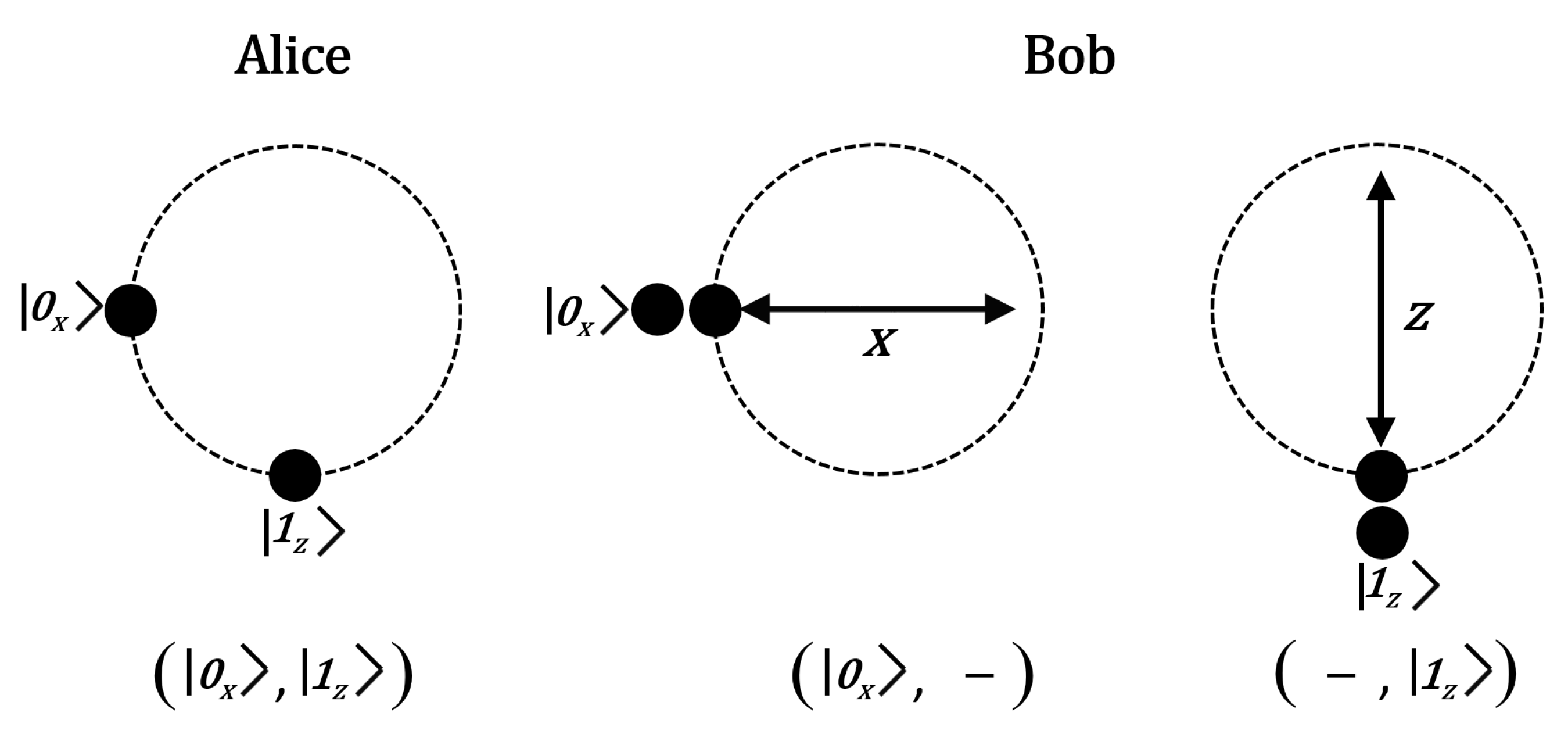
Quantum states inside a non-orthogonal pair are separated temporally to avoid losses due to consecutive detection events. The order between two non-orthogonal states is not relevant for the present discussion.
Figure 4.
Quantum states inside a non-orthogonal pair are separated temporally to avoid losses due to consecutive detection events. The order between two non-orthogonal states is not relevant for the present discussion.
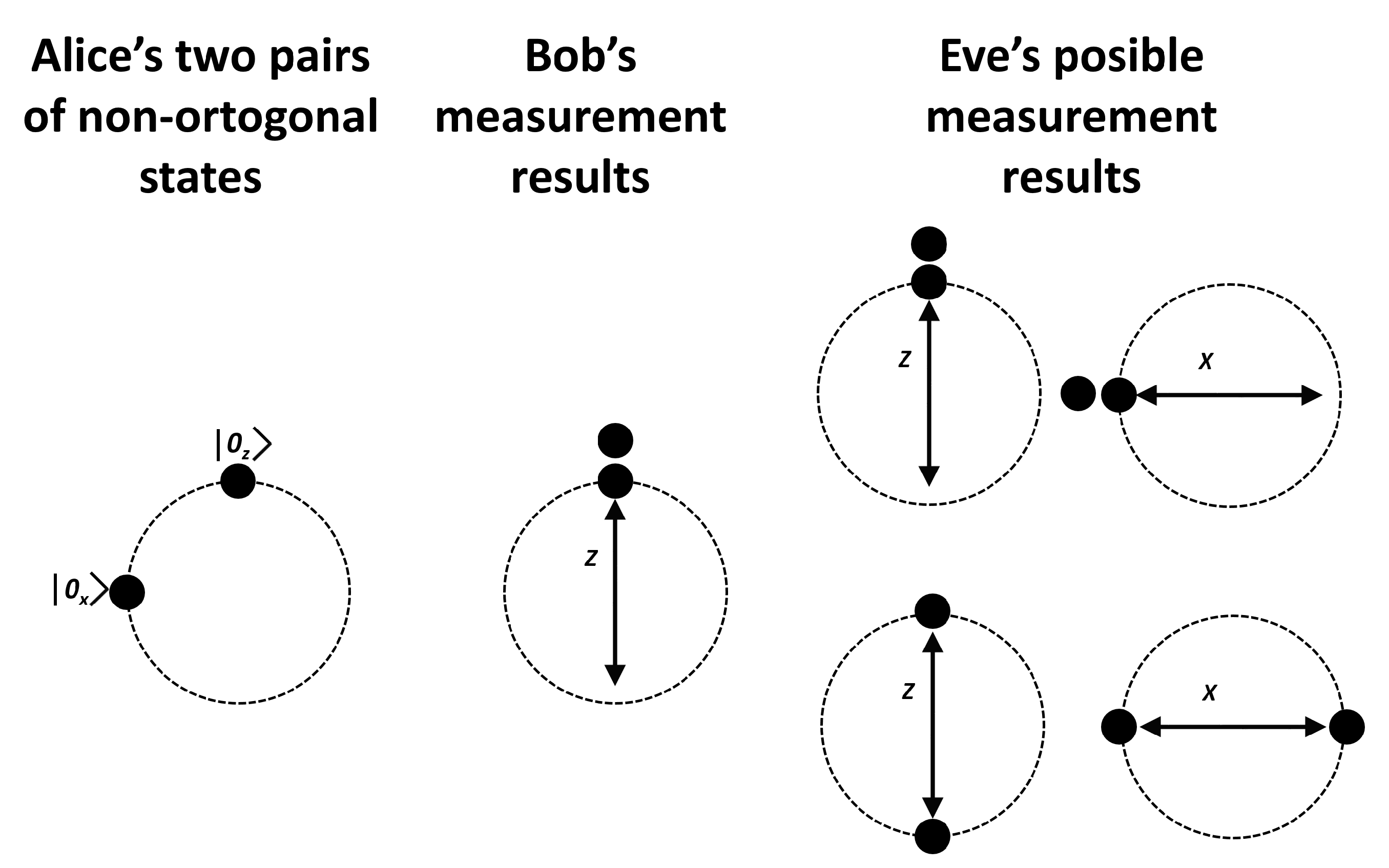
Figure 5.
We see (at left) the states prepared by Alice, two pairs of non-orthogonal states: and . After a double matching detection event is produced at Bob’s side (in this example two double detection events) the possible matching results are exhibited at the right.
Figure 5.
We see (at left) the states prepared by Alice, two pairs of non-orthogonal states: and . After a double matching detection event is produced at Bob’s side (in this example two double detection events) the possible matching results are exhibited at the right.
Figure 6.
The exchange of messages assuming an error free protocol. represents the pairs of non-orthogonal qubits, the sub-indices k denote the double matching detection events at Bob’s station, f represents the the required information to construct the frames and s denotes the sifting bits computed by Bob.
Figure 6.
The exchange of messages assuming an error free protocol. represents the pairs of non-orthogonal qubits, the sub-indices k denote the double matching detection events at Bob’s station, f represents the the required information to construct the frames and s denotes the sifting bits computed by Bob.
Figure 7.
From the experimental simulation in
Table 14 we show the frame contribution when QBER = 30%, 605,060 frames have been created and 237,762 correspond to auxiliary frames. For each frame
,
,
and
we show the number of frames created (left) and the frames after error correction (right).
Figure 7.
From the experimental simulation in
Table 14 we show the frame contribution when QBER = 30%, 605,060 frames have been created and 237,762 correspond to auxiliary frames. For each frame
,
,
and
we show the number of frames created (left) and the frames after error correction (right).
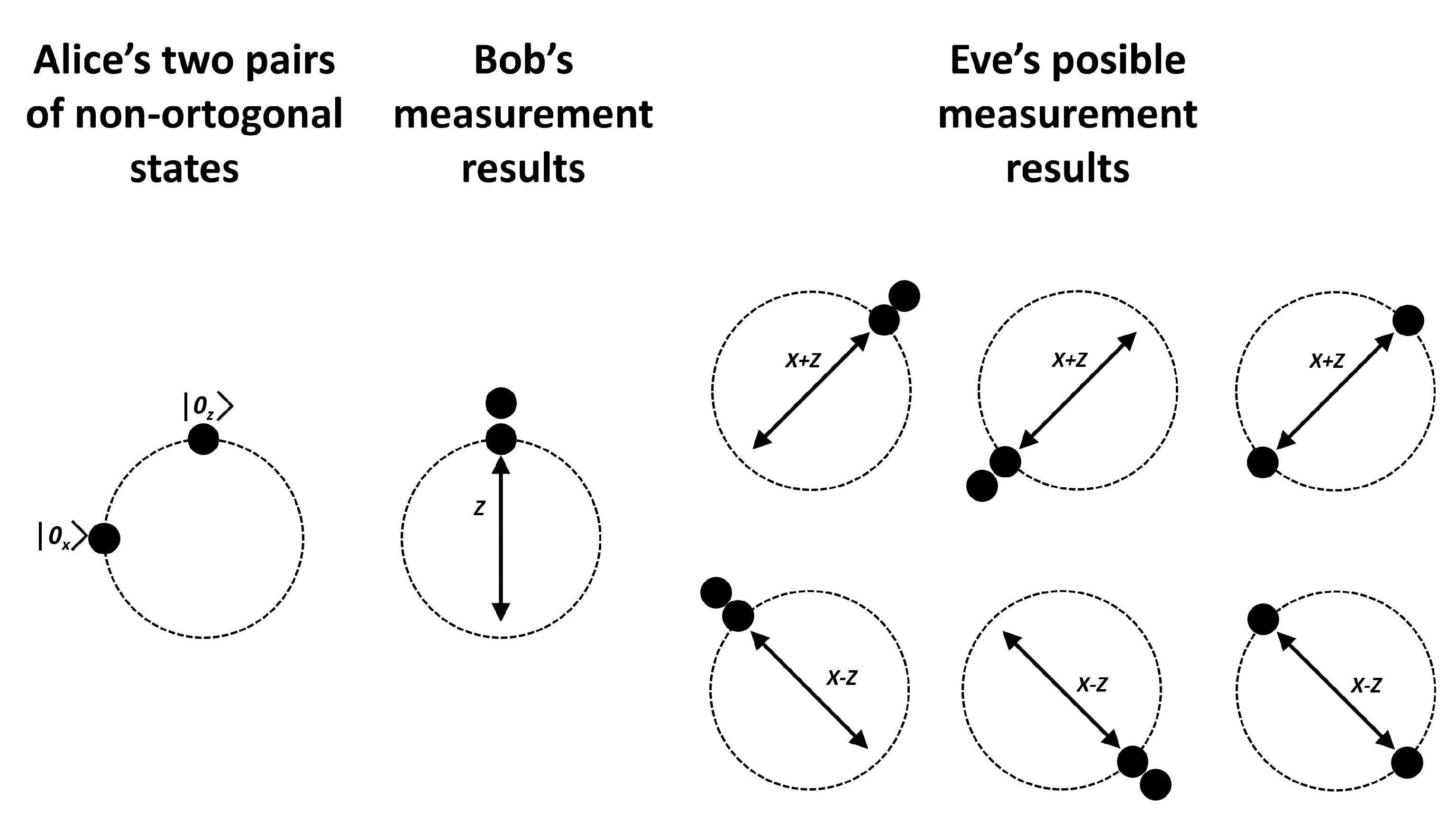
Figure 8.
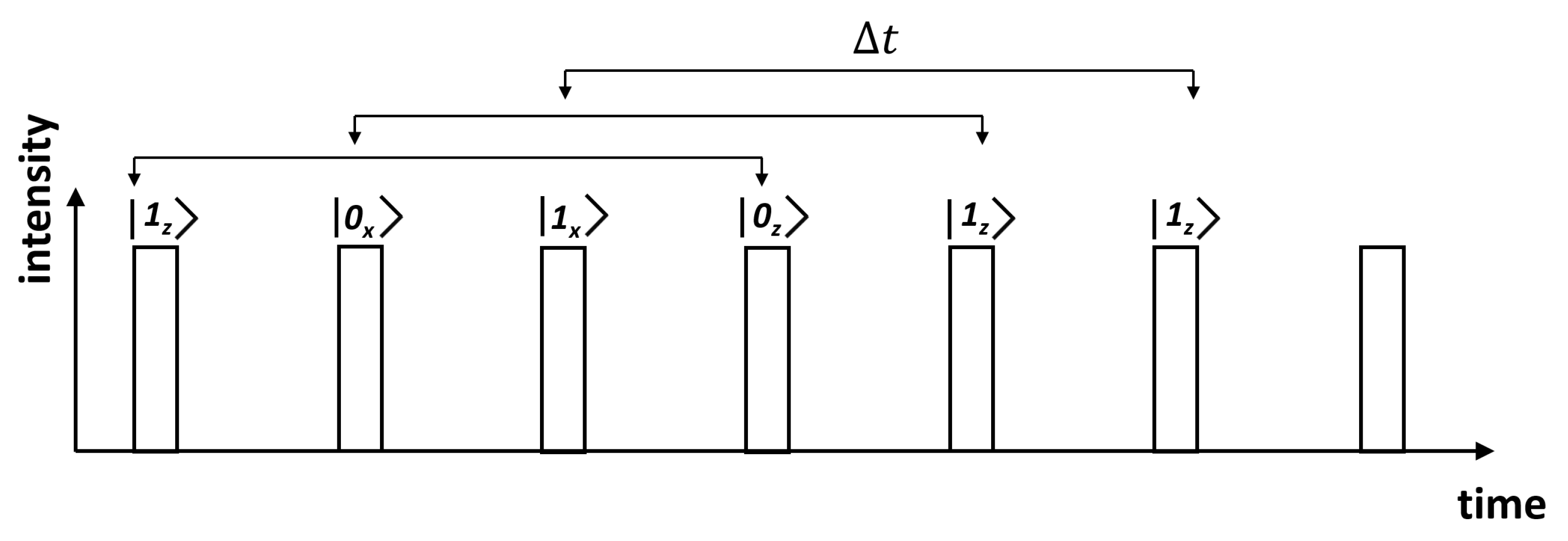
Alice sends a pair of non-orthogonal states to Bob who obtains a double matching detection at his optical detectors. Eve has a copy of such states, however she has a 0.5 chance to choose the correct measurement basis (X or Z). Furthermore, the probability to get a double matching detection event is 0.5. Therefore, Eve’s probability to get Bob’s result is just 0.25.
Figure 8.
Alice sends a pair of non-orthogonal states to Bob who obtains a double matching detection at his optical detectors. Eve has a copy of such states, however she has a 0.5 chance to choose the correct measurement basis (X or Z). Furthermore, the probability to get a double matching detection event is 0.5. Therefore, Eve’s probability to get Bob’s result is just 0.25.
Figure 9.
Alice sends a pair of non-orthogonal states to Bob who obtains a double matching detection event at his optical detectors. Eve has a copy of such states, however he has a 0.5 chance to choose the optimal measurement basis, in this case the basis. Despite Eve choose between bases or , the chance to guess Bob’s result is so she obtains an inconclusive result with . From here, the probability for Eve to obtain Bob’s measurement result is 0.28125.
Figure 9.
Alice sends a pair of non-orthogonal states to Bob who obtains a double matching detection event at his optical detectors. Eve has a copy of such states, however he has a 0.5 chance to choose the optimal measurement basis, in this case the basis. Despite Eve choose between bases or , the chance to guess Bob’s result is so she obtains an inconclusive result with . From here, the probability for Eve to obtain Bob’s measurement result is 0.28125.
Table 1.
Comparison of reconciliation methods as presented in [
22].
Table 1.
Comparison of reconciliation methods as presented in [
22].
| Reconciliation | Method | Advantages | Disadvantages |
|---|
| Interactive | Binary [16] | Easy and simple | Large communication overhead |
| Cascade [17] | Easy and simple | |
| Strong ability of error correction | |
| Code based | Winnow [18] | Communication time depending on the rate | Additional errors (Hamming) |
| | | Great Efficiency |
| LDPC [19] | Correction of errors as Cascade | |
| Improvement of the safety of the protocol | |
Table 2.
Measurement results after a double detection event (matching and non-matching). In the matching case, Bob measures the two quantum states with coincident results. Only double matching events encode a bit. The shared bit comes from the compatible measurement.
Table 2.
Measurement results after a double detection event (matching and non-matching). In the matching case, Bob measures the two quantum states with coincident results. Only double matching events encode a bit. The shared bit comes from the compatible measurement.
| | Bob’s Basis Measurement |
|---|
| Alice’s Non-Orthogonal Pairs | Matching Event | Non-Matching Event |
|---|
| X | Z | X | Z |
|---|
| (, ) | (, ) | (, ) | (, ) | (, ) |
| (, ) | (, ) | (, ) | (, ) | (, ) |
| (, ) | (, ) | (, ) | (, ) | (, ) |
| (, ) | (, ) | (, ) | (, ) | (, ) |
Table 3.
There are 6 useful frames: , where and 8 useless frames , where .
Table 3.
There are 6 useful frames: , where and 8 useless frames , where .
| Useful Frames | Useless Frames |
|---|
| | | |
| | | |
| | | |
| | | | |
Table 4.
There exist four possible Matching Results (MR) for frames. The bit produced by a double matching event is represented inside the ket notation with the symbol •. Additionally, each MR has been identified with a binary code left to each frame. After the sifting process such MR code will become part of the secret key.
Table 4.
There exist four possible Matching Results (MR) for frames. The bit produced by a double matching event is represented inside the ket notation with the symbol •. Additionally, each MR has been identified with a binary code left to each frame. After the sifting process such MR code will become part of the secret key.
| MR=00 | MR=10 |
| MR=01 | MR=11 |
Table 5.
To the left we see the 6 usable frames that Alice can prepare to be sent over the quantum channel. Provided Bob obtains the two (required) Matching Results he computes the sifting bits applying the xor function to each column (they are written at the bottom of each frame). The sifting bits which are publicly announced, conform the set that does not contain redundancy, so that Alice can identify without ambiguity Bob’s Matching Results.
Table 5.
To the left we see the 6 usable frames that Alice can prepare to be sent over the quantum channel. Provided Bob obtains the two (required) Matching Results he computes the sifting bits applying the xor function to each column (they are written at the bottom of each frame). The sifting bits which are publicly announced, conform the set that does not contain redundancy, so that Alice can identify without ambiguity Bob’s Matching Results.
| Alice | Bob |
|---|
| | | | |
| | | | |
| | | | |
| | | | |
| | | | |
| | | | |
Table 6.
The sifting bits obtained by Bob (written at the bottom of each frame) must be produced from at least two different Matching Results. At the right of each frame we have indicated the corresponding original Alice’s frame.
Table 6.
The sifting bits obtained by Bob (written at the bottom of each frame) must be produced from at least two different Matching Results. At the right of each frame we have indicated the corresponding original Alice’s frame.
| | | |
| | | |
| | | |
| | | |
Table 7.
The Sifting String (SS) which is publicly announced is constructed with the sifting bits and the measured bits. To achieve a secret bit (sb) each SS must be correlated at least to two Matching Results (MR).
Table 7.
The Sifting String (SS) which is publicly announced is constructed with the sifting bits and the measured bits. To achieve a secret bit (sb) each SS must be correlated at least to two Matching Results (MR).
| SS | MR | Frame | sb | MR | Frame | sb |
|---|
| Sifting | Measured | (See Table 4) | (See Table 3) | (See Table 4) | (See Table 3) |
|---|
| 00 | 00 | 10 | | 0 | 11 | | 1 |
| 00 | 11 | 00 | | 0 | 01 | | 1 |
| 01 | 10 | 01 | | 0 | 11 | | 1 |
| 01 | 01 | 10 | | 0 | 01 | | 1 |
| 10 | 01 | 00 | | 0 | 11 | | 1 |
| 10 | 10 | 00 | | 0 | 10 | | 1 |
| 11 | 11 | 11 | | 0 | 10 | | 1 |
Table 8.
We list the set of valid Sifting Strings (SS) for each frame . Provided Alice has sent an specific frame to Bob, he returns the SS which must be one of the listed here, otherwise an error is detected. We analyze if an error is detectable when occurs in the 1st (or 2nd) measured bit.
Table 8.
We list the set of valid Sifting Strings (SS) for each frame . Provided Alice has sent an specific frame to Bob, he returns the SS which must be one of the listed here, otherwise an error is detected. We analyze if an error is detectable when occurs in the 1st (or 2nd) measured bit.
| Frame | Valid Sifting Strings (SS) | MR | 1st Bit | Detection | 2nd Bit | Detection | 1st and 2nd Bits | Detection |
|---|
| SS | 10 | 10,10 | yes | 01,01 | yes | 11,11 | no |
| SS | 01 | 00,00 | no | 00,11 | yes | 01,01 | yes |
| SS | 00 | 00,11 | yes | 00,00 | no | 10,10 | yes |
| SS | 11 | 10,01 | no | 01,10 | no | 00,00 | no |
| SS | 00 | 10,01 | no | 10,10 | yes | 00,00 | yes |
| SS | 01 | 00,11 | no | 00,00 | yes | 01,10 | yes |
| SS | 11 | 11,11 | no | 00,00 | yes | 01,10 | yes |
| SS | 10 | 01,01 | no | 10,10 | yes | 00,00 | yes |
| SS | 01 | 01,01 | no | 01,10 | yes | 00,00 | yes |
| SS | 10 | 11,11 | no | 00,00 | yes | 10,10 | yes |
| SS | 00 | 00,11 | no | 00,00 | yes | 10,10 | yes |
| SS | 11 | 10,01 | no | 01,10 | yes | 00,00 | yes |
| SS | 01 | 01,01 | yes | 01,10 | no | 00,00 | yes |
| SS | 11 | 00,00 | yes | 11,11 | no | 10,01 | yes |
| SS | 00 | 00,00 | yes | 00,11 | no | 10,01 | yes |
| SS | 10 | 01,01 | yes | 10,10 | no | 00,00 | yes |
| SS | 11 | 01,10 | yes | 10,01 | yes | 11,11 | no |
| SS | 01 | 00,11 | yes | 00,00 | no | 01,10 | yes |
| SS | 00 | 00,00 | no | 00,11 | yes | 10,01 | yes |
| SS | 10 | 01,01 | no | 10,10 | no | 00,00 | no |
| SS | 00 | 10,01 | yes | 10,10 | no | 00,00 | yes |
| SS | 01 | 00,00 | yes | 00,11 | no | 01,01 | yes |
| SS | 10 | 00,00 | yes | 11,11 | no | 01,01 | yes |
| SS | 11 | 10,01 | yes | 01,10 | no | 00,00 | yes |
Table 9.
Bob measures the quantum pair (), but produces . This error is identified half of the times using . Similarly, Bob receives () but results in . This error is successfully managed half of the times using . The second and fourth rows show the erroneous cases. The errors are represented with bars above the bits: in and in .
Table 9.
Bob measures the quantum pair (), but produces . This error is identified half of the times using . Similarly, Bob receives () but results in . This error is successfully managed half of the times using . The second and fourth rows show the erroneous cases. The errors are represented with bars above the bits: in and in .
| Alice | Bob |
|---|
| | | | |
| | | | |
| | | | |
| | | | |
Table 10.
Error correction map for undetected errors. From
Table 8 we list all erroneous cases that keep undetected. The bit underlined in the ket notation flips into the the bit underlined in the Sifting String. Some errors are identified using the auxiliary frames
and
. If detection of error is not possible the frame must be removed. For this reason frame
is ambiguous and must be removed.
Table 10.
Error correction map for undetected errors. From
Table 8 we list all erroneous cases that keep undetected. The bit underlined in the ket notation flips into the the bit underlined in the Sifting String. Some errors are identified using the auxiliary frames
and
. If detection of error is not possible the frame must be removed. For this reason frame
is ambiguous and must be removed.
| Frame | Quantum Pair | Sifting String | Detection Frame | Sifting String | Error-Bit | Correction Code |
|---|
| | | - | - | 1st | remove |
| | |
| | - | - | 2nd | remove |
| | | |
| | | - | - | 1st | remove |
| | |
| | | 01,10 | 1st | SS |
| SS |
| | | - | - | 1st | remove |
| | |
| | | 10,10 | 1st | SS |
| SS |
Table 11.
Error correction map for undetected errors (cont). Frame is ambiguous and will be discarded.
Table 11.
Error correction map for undetected errors (cont). Frame is ambiguous and will be discarded.
| Frame | Quantum Pair | Sifting String | Detection Frame | Sifting String | Error-Bit | Correction |
|---|
| | | - | - | 2nd | remove |
| | |
| | | 10,10 | 2nd | SS |
| SS |
| | | - | - | 1st | remove |
| | |
| | - | - | 2nd | remove |
| | | |
| | | | 01,10 | 2nd | SS |
| SS |
| | - | - | 2nd | remove |
| | |
Table 12.
We list usable (4) frames, it must be included (4) frames , , and to verify errors by means of the null quantum pairs.
Table 12.
We list usable (4) frames, it must be included (4) frames , , and to verify errors by means of the null quantum pairs.
| | | |
Table 13.
If an error is detected using
or
, then Alice corrects the error according to
Table 10 and
Table 11. If no error is found Alice uses the secret bits listed here.
Table 13.
If an error is detected using
or
, then Alice corrects the error according to
Table 10 and
Table 11. If no error is found Alice uses the secret bits listed here.
| SS | MR | Frame | sb | MR | Frame | sb |
|---|
| 00 | | 0 | 01 | | 1 |
| 11 | | 0 | 10 | | 1 |
| 01 | | 0 | 11 | | 1 |
| 10 | | 0 | 01 | | 1 |
| 00 | | 0 | 11 | | 1 |
| 00 | | 0 | 10 | | 1 |
Table 14.
Simulation of the protocol when have been registered 1000 double matching detection events. Tests were performed in an Intel Core i7-8750H 2.2 GHz, 12GB RAM.
Table 14.
Simulation of the protocol when have been registered 1000 double matching detection events. Tests were performed in an Intel Core i7-8750H 2.2 GHz, 12GB RAM.
| QBER | Time (ms) | Secret Bits | Throughput (Kbps) |
|---|
| 54.0146 | 59,873.7 | 1108.90435 |
| 57.6022 | 58,911.2 | 1025.13229 |
| 54.0614 | 52,630.1 | 972.532054 |
| 55.6709 | 48,830.9 | 877.799205 |
| 60.9381 | 46,706.4 | 773.520113 |
| 78.4297 | 40,960.0 | 522.251137 |