A Pairing-Based Three-Party Authenticated Encryption Scheme without Shared Secrets
Abstract
:1. Introduction
2. Preliminaries
- (i)
- Bilinearity:e(Q1 + Q2, W) = e(Q1, W)e(Q2, W);e(Q, W1 + W2) = e(Q, W1)e(Q, W2);
- (ii)
- Nondegeneracy:We say that in the group G2, the value e(Q, Q) is regarded as a generator provided that, in the group G1, Q is also a generator.
- (iii)
- Computability:There exists an efficient polynomial-time algorithm to compute e(P, Q) for any P, Q ∈ G1.
3. Proposed TPAE Construction
3.1. Participated Entity
3.2. Constituted Algorithms
3.3. Substantial Construction
| c ⊕ h2(W, σ, T) | ||
| = | c ⊕ h2(W, σ, h3(e(xaW, Yb))) | (by Equation (5)) |
| = | c ⊕ h2(W, σ, h3(e(xatP, Yb))) | (by Equation (1)) |
| = | c ⊕ h2(W, σ, h3(e(wYa, Yb))) | |
| = | c ⊕ h2(W, σ, T) | (by Equation (2)) |
| = | m | (by Equation (4)) |
| e(σ, Ys + h1(m, W, T)P) | ||
| = | e((xs + h1(m, W, T))−1W, Ys + h1(m, W, T)P) | (by Equation (3)) |
| = | e((xs + h1(m, W, T))−1W, (xs + h1(m, W, T))P) | |
| = | e(W, P) |
4. Security Model and Proof
- Step 1
- Randomly choose v1 ∈ Zq along with v2 ∈ {0, 1}k;
- Step 2
- Let W* = zP;
- Step 3
- Compute σ* = (xs + v1)−1W* and c* = mλ ⊕ v2;
- Step 4
- Add the record of (mλ, W*, null, v1) into h1-list;
- Step 5
- Add the record of (W*, σ*, null, v2) into h2-list.The ciphertext δ* = (W*, σ*, c*) is served as a target challenge for .
| ε | = | Pr[λ′ = λ] − 0.5 | | (by Definition 1) |
| ≤ 0.5Pr[¬PSG] | (by Equation (11)) | |
| = 0.5(Pr[QH3* ∨ EVerify_Fat]) | ||
| ≤ 0.5(Pr[QH3*] + Pr[EVerify_Fat]). |
- Step 1
- Randomly pick two integers d, v1 ∈ ;
- Step 2
- Run the Reg_U algorithm to get (xa, Ya, Certa) and (xb, Yb, Certb);
- Step 3
- Compute
- σ = dP,
- W = d(zP) + v1dP,
- T = h3(e(xaW, Yb)),
- c = m ⊕ h2(W, σ, T);
- Step 4
- Add the entry (m, W, T, v1) into h1-list;The ciphertext δ = (W, σ, c) is then returned to .
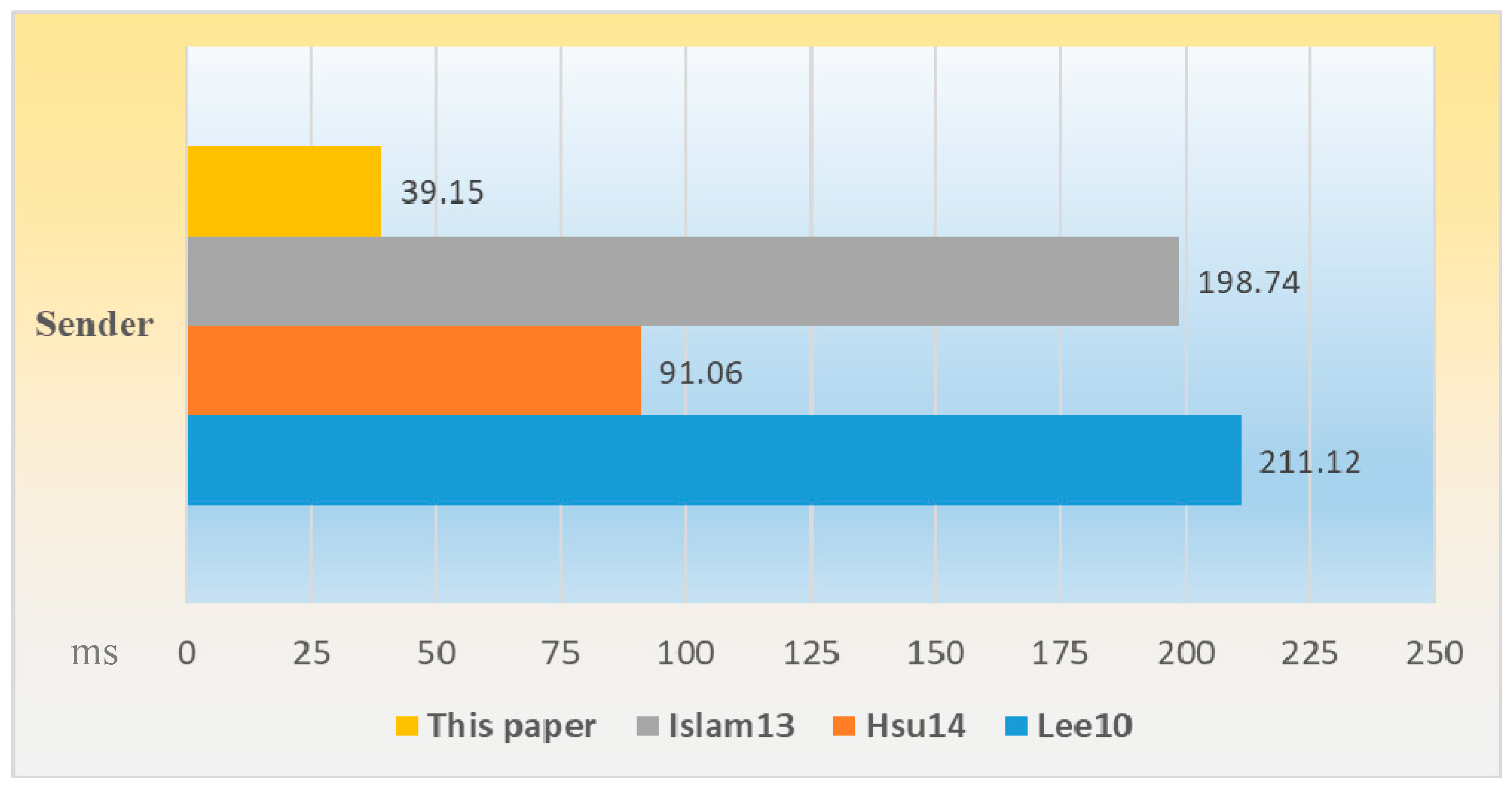
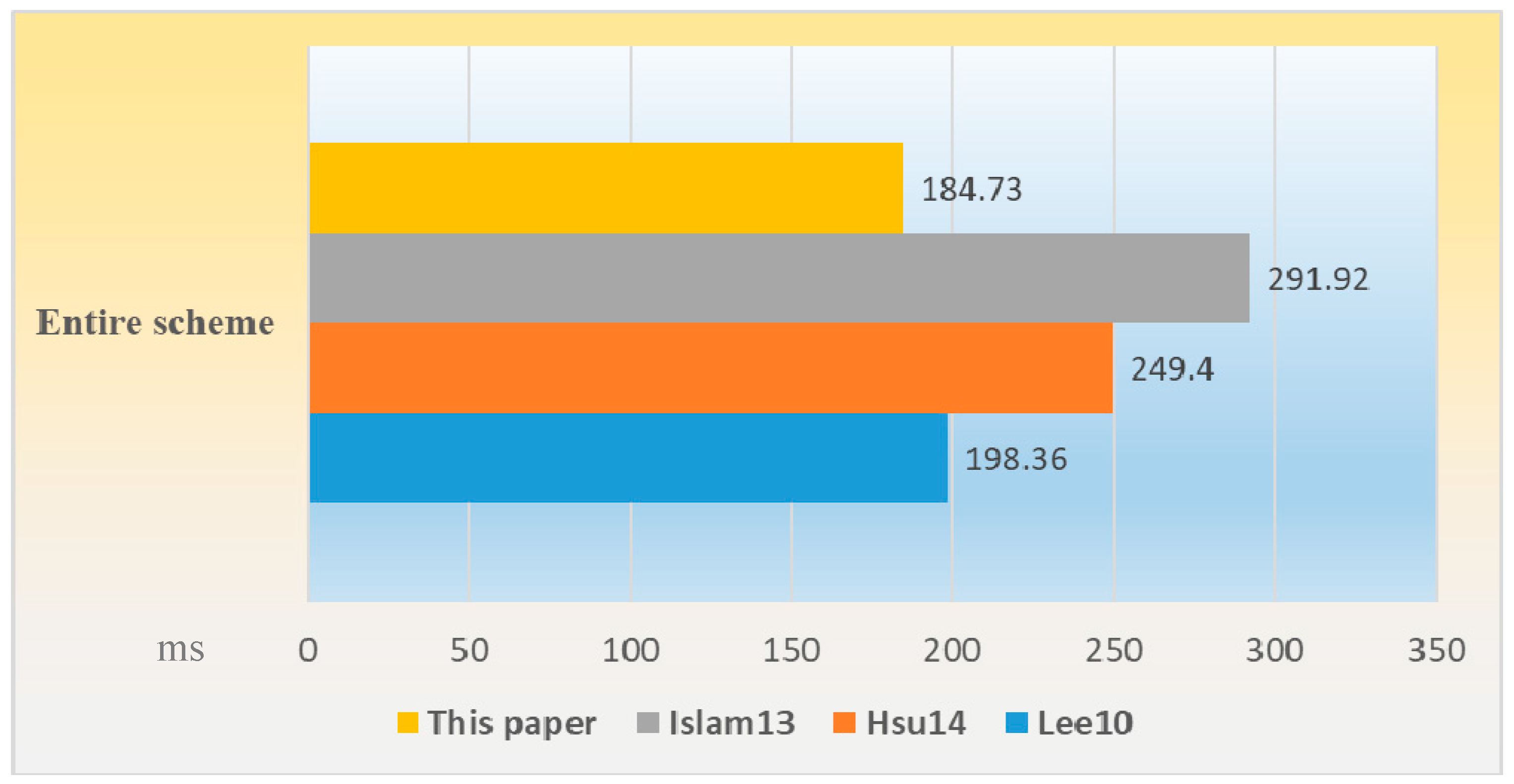
5. Performance Evaluation
6. Conclusions
Author Contributions
Funding
Conflicts of Interest
Ethical Approval
References
- Diffie, W.; Hellman, M. New Directions in Cryptography. IEEE Trans. Inf. Theory 1976, IT-22, 644–654. [Google Scholar] [CrossRef]
- ElGamal, T. A Public Key Cryptosystem and a Signature Scheme Based on Discrete Logarithms. IEEE Trans. Inf. Theory 1985, IT-31, 469–472. [Google Scholar] [CrossRef]
- Rivest, R.; Shamir, A.; Adleman, L. A Method for Obtaining Digital Signatures and Public-Key Cryptosystems. Commun. ACM 1978, 21, 120–126. [Google Scholar] [CrossRef]
- Sekhar, M.R. Signatures Scheme with Message Recovery and Its Applications. Int. J. Comput. Math. 2004, 81, 285–289. [Google Scholar] [CrossRef]
- Schneider, S. Formal Analysis of a Non-Repudiation Protocol. In Proceedings of the 11th IEEE Computer Security Foundations Workshop, Rockport, MA, USA, 9–11 June 1998; IEEE Press: Piscataway, NJ, USA, 1998; pp. 54–65. [Google Scholar]
- Hou, F.; Wang, Z.; Tang, Y.; Liu, Z. Protecting Integrity and Confidentiality for Data Communication. In Proceedings of the 9th International Symposium on Computers and Communications (ISCC’04), Alexandria, Egypt, 28 June–1 July 2004; pp. 357–362. [Google Scholar]
- Jacob, J. A Uniform Presentation of Confidentiality Properties. IEEE Trans. Softw. Eng. 1991, 17, 1186–1194. [Google Scholar] [CrossRef]
- Horster, P.; Michel, M.; Peterson, H. Authenticated Encryption Schemes with Low Communication Costs. Electron. Lett. 1994, 30, 1212–1213. [Google Scholar] [CrossRef]
- Stallings, W. Cryptography and Network Security: Principles and Practices, 7th ed.; Pearson: London, UK, 2017. [Google Scholar]
- Araki, S.; Uehara, S.; Imamura, K. The Limited Verifier Signature and Its Application. IEICE Trans. Fundam. Electron. Comput. Sci. 1999, E82-A, 63–68. [Google Scholar]
- Zhang, F.; Kim, K. A Universal Forgery on Araki et al.’s Convertible Limited Verifier Signature Scheme. IEICE Trans. Fundam. Electron. Comput. Sci. 2003, E86-A, 515–516. [Google Scholar]
- Wu, T.S.; Hsu, C.L. Convertible Authenticated Encryption Scheme. J. Syst. Softw. 2002, 62, 205–209. [Google Scholar] [CrossRef]
- Huang, H.F.; Chang, C.C. An Efficient Convertible Authenticated Encryption Scheme and Its Variant. In Proceedings of the 5th International Conference on Information and Communications Security (ICICS 2003), Huhehaote, China, 10–13 October 2003; pp. 382–392. [Google Scholar]
- Lv, J.; Wang, X.; Kim, K. Practical Convertible Authenticated Encryption Schemes Using Self-Certified Public Keys. Appl. Math. Comput. 2005, 169, 1285–1297. [Google Scholar] [CrossRef]
- Yang, F.Y. A Secure Scheme for Authenticated Encryption. Cryptology ePrint Archive, Report 2005/456. 2005. Available online: http://eprint.iacr.org/2005/456 (accessed on 11 February 2019).
- Chien, H.Y. Selectively Convertible Authenticated Encryption in the Random Oracle Model. Comput. J. 2008, 51, 419–434. [Google Scholar] [CrossRef]
- Lee, C.C.; Hwang, M.S.; Tzeng, S.F. A New Convertible Authenticated Encryption Scheme Based on the ElGamal Cryptosystem. Int. J. Found. Comput. Sci. 2009, 20, 351–359. [Google Scholar] [CrossRef]
- Wu, T.S.; Lin, H.Y. Secure Convertible Authenticated Encryption Scheme Based on RSA. Informatica-Lithuan 2009, 33, 481–486. [Google Scholar]
- Lin, H.Y.; Hsu, C.L. A Novel Identity-Based Key-Insulated Convertible Authenticated Encryption Scheme. Int. J. Found. Comput. Sci. 2011, 22, 739–756. [Google Scholar] [CrossRef]
- Hsu, C.L.; Lin, H.Y. New Identity-Based Key-Insulated Convertible Multi-Authenticated Encryption Scheme. J. Netw. Comput. Appl. 2011, 34, 1724–1731. [Google Scholar] [CrossRef]
- Lin, H.Y. Group-Oriented Data Access Structure Using Threshold-CAE Scheme and Its Extension. Inf. Technol. Control 2014, 43, 252–263. [Google Scholar] [CrossRef]
- Lin, H.Y. “PCMAE: A Proxy Convertible Multi-AE Scheme and Its Variant. Inf. Technol. Control 2017, 46, 530–545. [Google Scholar] [CrossRef]
- Wu, T.S.; Lin, H.Y.; Ting, P.Y. A Publicly Verifiable PCAE Scheme for Confidential Applications with Proxy Delegation. Trans. Emerg. Telecommun. Technol. 2012, 23, 172–185. [Google Scholar] [CrossRef]
- Hsu, C.L.; Lin, H.Y. Convertible Authenticated Encryption Scheme with Hierarchical Access Control. Appl. Math. Inf. Sci. 2014, 8, 1239–1246. [Google Scholar] [CrossRef]
- Lin, H.Y.; Hsu, C.L.; Huang, S.K. Improved Convertible Authenticated Encryption Scheme with Provable Security. Inf. Process. Lett. 2011, 111, 661–666. [Google Scholar] [CrossRef]
- Lin, H.Y.; Wu, T.S.; Huang, S.K. An Efficient Strong Designated Verifier Proxy Signature Scheme for Electronic Commerce. J. Inf. Sci. Eng. 2012, 28, 771–785. [Google Scholar]
- Lin, H.Y.; Wu, T.S.; Huang, T.Y.; Yeh, Y.S. Self-Certified Proxy Convertible Authenticated Encryption Scheme. In Proceedings of the 8th International Conference on Intelligent System Design and Applications (ISDA 2008), Kaohsiung, Taiwan, 26–28 November 2008; pp. 479–483. [Google Scholar]
- Lu, C.F.; Hsu, C.L.; Lin, H.Y. Provably Convertible Multi-Authenticated Encryption Scheme for Generalized Group Communications. Inf. Sci. 2012, 199, 154–166. [Google Scholar] [CrossRef]
- Wu, T.S.; Chen, Y.S.; Lin, H.Y.; Chang, T.K. Authenticated Encryption Scheme Based on Paillier System with Verifiable Public Keys. Commun. Comput. Secur. 2012, 2, 1–5. [Google Scholar] [CrossRef]
- Wu, T.S.; Lin, H.Y. Efficient Self-Certified Proxy CAE Scheme and Its Variants. J. Syst. Softw. 2009, 82, 974–980. [Google Scholar] [CrossRef]
- Wu, T.S.; Lin, H.Y.; Tsao, S.H.; Ting, P.Y. On the Construction of DL-Based Convertible Authenticated Encryption Scheme with Message Linkages. Inf. Int. Interdiscip. J. 2013, 16, 7983–7994. [Google Scholar]
- ISO/IEC 9594-8. Information Technology—Open Systems Interconnection—The Directory: Public-Key and Attribute Certificate Frameworks; International Organization for Standardization: Geneva, Switzerland, 2001. [Google Scholar]
- Pointcheval, D.; Stern, J. Security Arguments for Digital Signatures and Blind Signatures. J. Cryptol. 2000, 13, 361–369. [Google Scholar] [CrossRef]
- Lee, J.S.; Chang, J.H.; Lee, D.H. Forgery Attacks on Kang et al.’s Identity-Based Strong Designated Verifier Signature Scheme and Its Improvement with Security Proof. Comput. Electr. Eng. 2010, 36, 948–954. [Google Scholar] [CrossRef]
- Islam, S.K.H.; Biswas, G.P. Provably Secure Certificateless Strong Designated Verifier Signature Scheme Based on Elliptic Curve Bilinear Pairings. J. King Saud Univ.-Comput. Inf. Sci. 2013, 25, 51–61. [Google Scholar]
- Cao, X.; Kou, W.; Du, X. A Pairing-Free Identity-Based Authenticated Key Agreement Protocol with Minimal Message Exchanges. Inf. Sci. 2010, 180, 2895–2903. [Google Scholar] [CrossRef]

| Symbol | Description |
|---|---|
| C1 | To execute a bilinear pairing computation |
| C2 | To execute an exponentiation computation over G2 |
| C3 | To execute a scalar multiplication over G1 |
| Sender | Each Recipient | Entire Scheme | |
|---|---|---|---|
| Lee10 | 4C1 + 4C3 | 2C1 + C3 | 8C1 + 6C3 |
| Hsu14 | 2C1 + 8C3 | 3C1 + 3C3 | 8C1 + 14C3 |
| Islam13 | 6C1 + 6C3 + 2C2 | C1 + C3 + C2 | 8C1 + 8C3 + 4C2 |
| This paper | C1 + 3TM | 3C1 + 2C3 | 7C1 + 7C3 |
© 2019 by the author. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Lin, H.-Y. A Pairing-Based Three-Party Authenticated Encryption Scheme without Shared Secrets. Symmetry 2019, 11, 605. https://doi.org/10.3390/sym11050605
Lin H-Y. A Pairing-Based Three-Party Authenticated Encryption Scheme without Shared Secrets. Symmetry. 2019; 11(5):605. https://doi.org/10.3390/sym11050605
Chicago/Turabian StyleLin, Han-Yu. 2019. "A Pairing-Based Three-Party Authenticated Encryption Scheme without Shared Secrets" Symmetry 11, no. 5: 605. https://doi.org/10.3390/sym11050605
APA StyleLin, H.-Y. (2019). A Pairing-Based Three-Party Authenticated Encryption Scheme without Shared Secrets. Symmetry, 11(5), 605. https://doi.org/10.3390/sym11050605





