1. Introduction
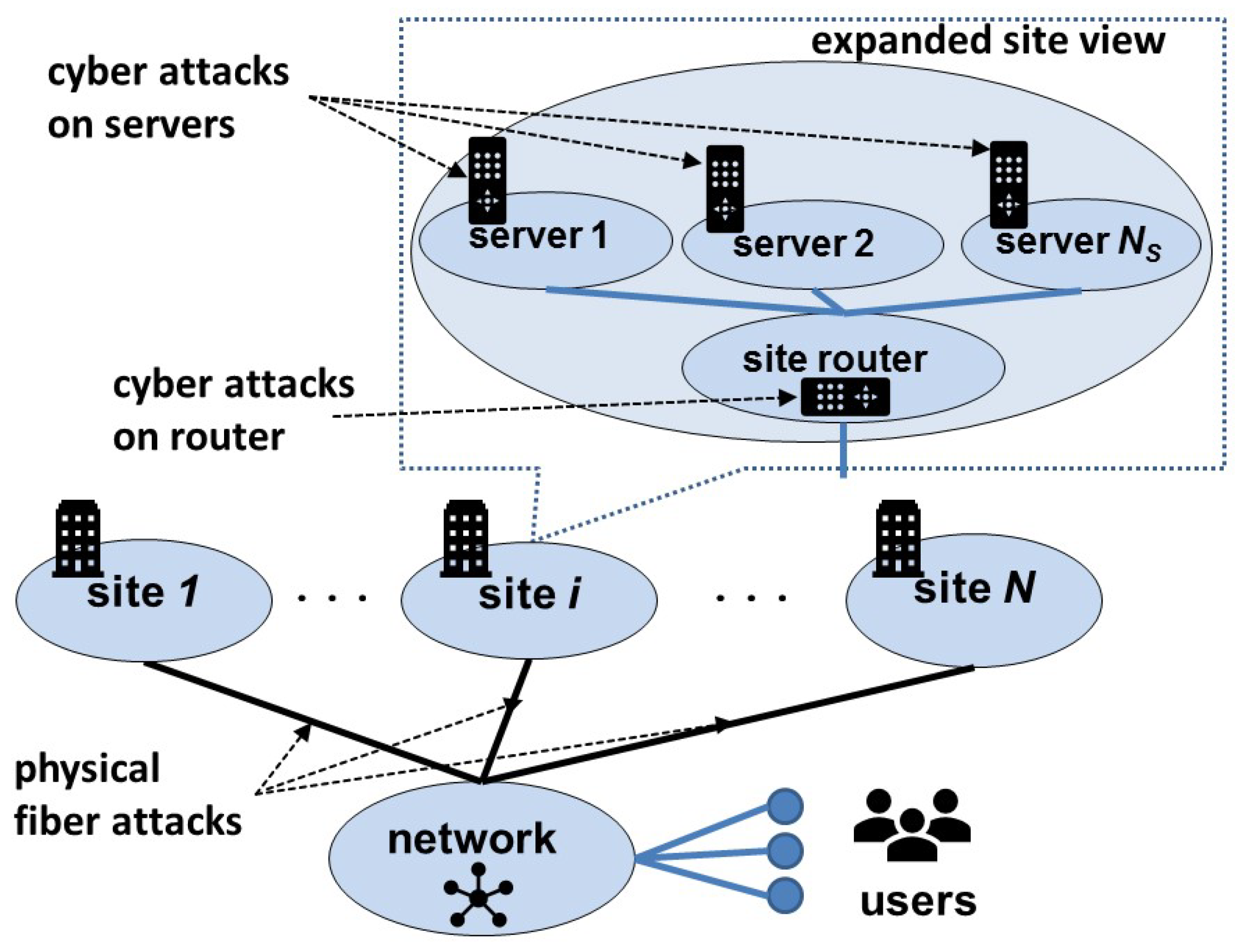
The operation of critical infrastructures such as metro systems, smart power grids, high-performance computing complexes, and cloud computing infrastructures requires the continued functioning of cyber components such as signals, servers, supervisory control and data acquisition (SCADA) systems, routers, and switches, and also physical components such as tracks, power lines, fiber lines, cooling systems, and power systems. Components of both types must be operational as individual units, and must also be available (i.e., accessible to other infrastructure components). The individual components are subject to direct attacks in that cyber attacks will disable individual cyber components and physical attacks will disable individual physical components, when the components have not been reinforced. Furthermore, critical correlations or inter-dependencies exist between cyber and physical components, which may be exploited to launch strategic component attacks that propagate the disruptions to several others. To counter such attacks, infrastructure providers have to explicitly account for the underlying cyber–physical correlations and adopt strategies that ensure the continued operation of both cyber and physical sub-infrastructures.
In this paper, we consider a discrete component model of infrastructures with a large number of cyber and physical components, such as a metro system with hundreds of signals and sensors, a cloud computing infrastructure with thousands of servers, or a power grid with hundreds to thousands of sensors. The notations for various quantities are provided in
Table 1. The attacker launches
cyber or
physical component attacks but not both, and the provider reinforces
cyber and
physical components. The
cyber–physical interactions may render the otherwise operational components unavailable, whether they are reinforced or not. For example, a physical attack on a fiber connection to a server site of a cloud computing infrastructure shown in
Figure 1 may disconnect all servers (thousands in some cases) from the network, even if they are all fortified against cyber attacks.
In addition to component-level characterizations, the cyber and physical sub-infrastructures can be separately identified in several cases. Indeed, they may be operated by different domain experts. For example, in a power grid, SCADA systems are maintained by operations staff, and the power routes are maintained by power engineering staff. We consider the
cyber and
physical sub-infrastructures consisting entirely of cyber and physical components, respectively. Disruptions to either could disrupt the entire infrastructure. Let
denote the survival probability of the infrastructure, and
and
denote the marginal survival probabilities of cyber and physical sub-infrastructures, respectively. The
cyber–physical failure correlation function is the failure probability of cyber sub-infrastructure given the other’s failure, and is estimated using the structural properties of the infrastructure. Furthermore, we consider that
and
satisfy first-order differential conditions based on the
multiplier functions [
1] of cyber and physical sub-infrastructures, denoted by
and
, respectively, which are derived based on their component-level considerations. Together, these two characterizations [
2,
3] generalize the linearity and statistical independence conditions used in previous works [
4,
5] for this class of infrastructures with discrete cyber and physical components. The multiplier functions depend on
,
,
, and
, and also on additional infrastructure parameters (e.g., the number of power lines controlled by a SCADA system), and they provide an insightful abstraction. They appear in the estimates of survival probabilities of sub-infrastructures at Nash equilibrium (NE) and provide insights into the defense posture of the infrastructure.
We formulate a game between the provider and attacker with the following considerations:
- (a)
knowledge about the infrastructure is available to the attacker which is sufficient to launch component attacks;
- (b)
costs of attacks and reinforcements of components, denoted by and , respectively, are not available to the other player;
- (c)
components chosen by the provider to reinforce, and by the attacker to attack, are not revealed; and
- (d)
incidents and results of attacks on components are known to the provider and attacker.
The information in items (a) and (d) is available to both the provider and attacker, and that in item (b) is private. The provider and attacker minimize their respective utility functions, which are based on both types of information.
The
composite utility function [
1] to be minimized by the provider is the sum of two terms, representing the reward for keeping the infrastructure operational and the corresponding cost, respectively. It is given by
where
and
are the reward and cost multiplier functions, respectively, of the provider,
represents the reward of keeping the infrastructure operational, and
is the total cost of reinforcing cyber and physical components. The composite utility function to be minimized by the attacker is given by
where
and
are the reward and cost multiplier functions, respectively,
is the reward for rendering the infrastructure non-operational, and
is the total cost of cyber or physical attacks. These utility functions can be specialized to capture different provider and attacker considerations as shown in
Table 2, in particular by expressing them in terms of the survival probability of the infrastructure
. The
sum-form utility [
2] for the cyber–physical infrastructure provider is given by
where
is the expected reward in return for the reinforcement cost
of cyber and physical components. In certain infrastructures, players focus on the cost term only, and the reward of operating the infrastructure is not explicit. In such cases, the
product-form utility [
3] of the provider is given by
which represents the expected cost under infrastructure failure and thus represents the “wasted” effort.
The NE of this game represents the state of the infrastructure under the reinforcement and attack actions of the provider and attacker that attempt to minimize their respective utility functions based on their individual information (from which neither has a motivation to unilaterally deviate [
6]). The choices of provider and attacker, given by
and
, respectively, can be obtained using various available methods [
6,
7], which typically involves exploiting the scenario-specific details. Indeed, because of the large-scale and complexity feature of cyber–physical infrastructures, most game models obtain Nash equilibrium using numerical methods. Our objective in this paper is to show that critical insights about the infrastructure survival can be gained by deriving estimates of survival probabilities in terms of various correlations and multiplier functions, without requiring explicit solutions for
and
. To this end, we derive NE conditions that highlight the dependence of
on the cost terms, correlation function, multiplier functions, and cyber and physical sub-infrastructure survival probabilities, as well as their partial derivatives. Indeed, the effects of infrastructure parameters will be reflected in estimates of
via the multiplier functions, while the correlation effects are “separated” from them. In particular, the impacts of the two players’ strategies are captured using the
composite gain–cost terms and
gain–cost gradients that depend on gain and cost terms and their derivatives with respect to
and
(
and
), respectively, which are specialized versions of those proposed for systems of systems [
1]. The NE conditions reveal a direct dependence of
on the parameters of cyber and physical components and sub-infrastructures, as well as a close coupling between them through the correlation function. We also estimate the sensitivity functions of
using the partial derivatives of parameters
,
,
,
, and
that indicate their relative importance in the defense posture of the infrastructure.
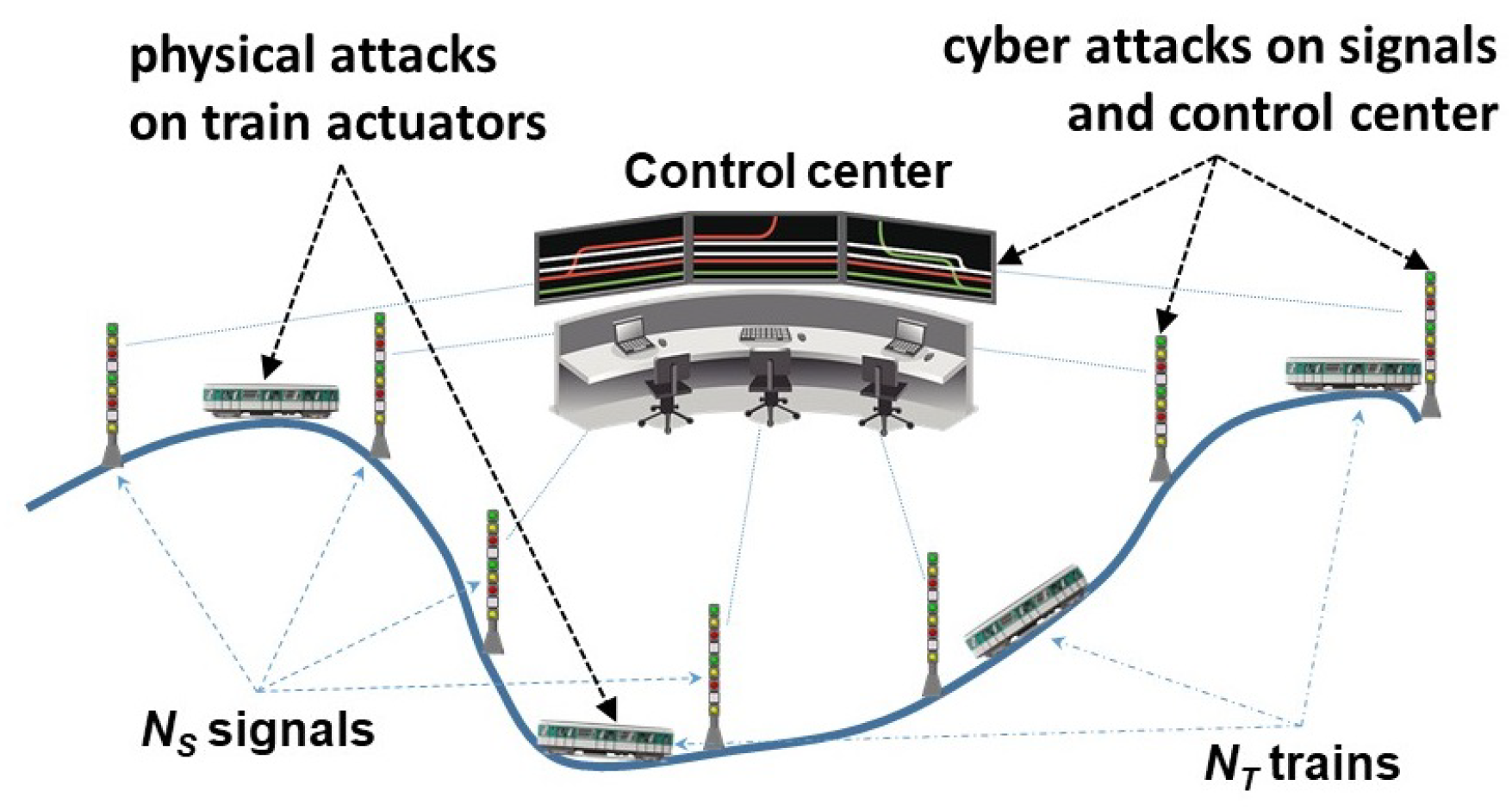
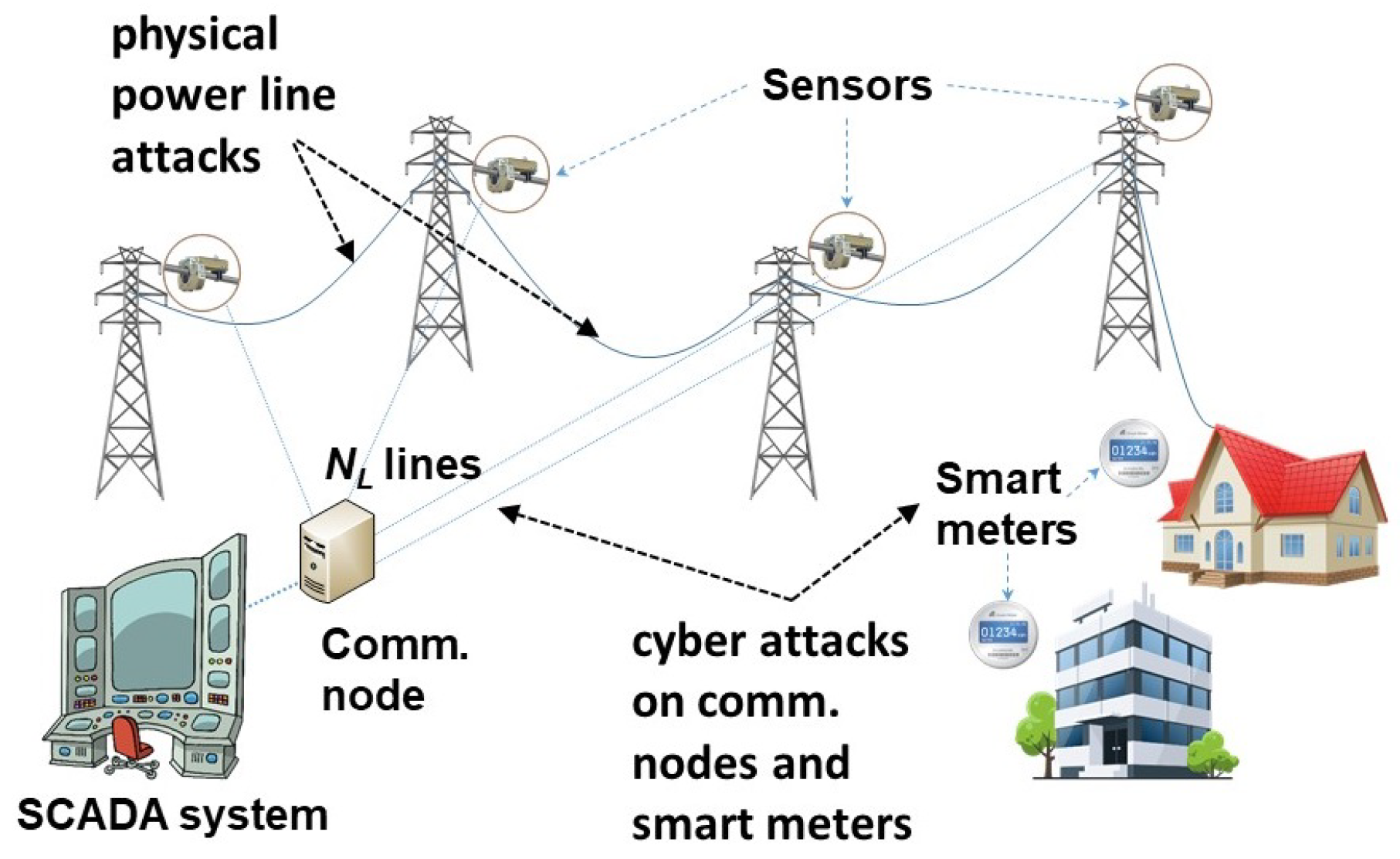
The contributions of this paper are as follows. We unify the analysis of previously separate sum-form [
2] and product-form [
3] formulations, and provide a deeper treatment of NE, including second-order conditions which are not considered in prior work. Although a special case of a system of systems [
1], our formulation provides a more focussed treatment of cyber and physical sub-infrastructures. Our results provide insights into the defense postures of (simplified models) three infrastructures, including metro systems and smart power grids (new here), and cloud computing infrastructures from [
8]. We first consider cases where both cyber and physical components are uniform (
Section 3.2), namely, signals and trains of metro systems, servers and fiber connections for cloud infrastructures, and SCADA system and power lines for smart power grids. Then, we consider different types of cyber components (
Section 5), namely signals and the centralized traffic controls for a metro system, servers and routers for the cloud infrastructure, and SCADA system components and smart meters for the smart power grid. We explicitly derive NE conditions and sensitivity functions for these scenarios.
The organization of this paper is as follows. We compare our formulation with other related work in
Section 2. In
Section 3, we present a discrete component model for cyber–physical infrastructures, and discuss the failure correlation function and the differential conditions on sub-infrastructure survival probabilities. We present the game theoretic formulation in
Section 4, and derive NE conditions and sensitivity estimates. We also describe two special cases, OR systems in
Section 4.2 and statistically independent sub-infrastructures in
Section 4.3, wherein the cyber–physical correlation effects are somewhat simplified. We discuss NE conditions for applications of metro systems, cloud computing infrastructures, and smart power grids in
Section 5. We conclude in
Section 6.
2. Related Work
Critical infrastructures are vital to national security [
9], and there are numerous published reports, books, and studies on identifying [
10] and securing [
11,
12,
13,
14] critical infrastructures. A detailed scientific analysis of critical infrastructures is provided in [
15]. The author draws insights that critical infrastructures are complex systems, and their architecture is the most crucial factor in deciding their reliability and resilience. Securing cyber–physical networks has been studied extensively from various perspectives [
16,
17,
18,
19,
20]. A risk assessment approach is used in [
21] to identify and address the vulnerabilities of a cyber–physical system, without explicitly using the interactions between the attacker and the provider. Consequently, the quantification of risk and correlations is somewhat limited. Although cyber–physical networks form an integral part of many critical infrastructures such as energy, information technology, and transportation systems, these works primarily cater to applications on power systems and smart power grids. To our best knowledge, there has not been any study that rigorously models the correlations between cyber and physical components in a general system. Our objective is to develop such a general formulation and illustrate its generality by using models of various applications, such as metro systems, cloud computing infrastructures, and smart power grids.
Game-theoretic methods have been extensively applied to capture the interactions between providers and attackers of critical infrastructures [
22] to develop strategies to ensure their continued operation in the presence of evolving threats. Such interactions are being increasingly analyzed ever since the 9/11 attacks [
23], after which there has been an increased emphasis on protecting critical infrastructures. Most of these studies use sequential models with the provider as the first mover and the attacker as the second. This is useful in enabling analysts to draft preemptive recommendations [
24]. Game theory has been used widely in the field of cyber–physical network security [
25,
26,
27]. An overview of the game-theoretic models in network security is provided in [
28]. However, these works do not consider the physical components that are critical to the functioning of cyber networks.
Several infrastructures to support power distribution, transportation, and agriculture have been analyzed using game-theoretic approaches. They typically employ complex dynamic models of the underlying physical systems [
11]—in particular, using partial differential equations. Both game-theoretic formulations and their solutions are quite extensive for such infrastructures, including: multiple-period games [
29] that address multiple time-scales of system dynamics; incomplete information games [
30,
31,
32] that account for partial knowledge about the system dynamics and attack models; and multiple-target games [
33,
34] that account for possibly competing objectives. A comprehensive review of the defense and attack models in various game-theoretic formulations has been presented in [
35].
Game-theoretic methods have been developed specifically to address the system reliability and robustness for several applications [
22], which are particularly applicable to critical infrastructures. Recently, there have been increasing levels of integration of cyber components, including computing and networking devices, into several critical infrastructures. This contributes to faster information transmission and processing, but also lead to unprecedented security vulnerabilities due to the underlying cyber–physical correlations [
36]. While many existing formulations utilize detailed dynamic infrastructure models, the cyber–physical correlations have only recently been explicitly addressed, and in a limited way [
36]. Because of the large scale and complexity of cyber–physical systems, most game models obtain Nash equilibrium using numerical methods. The current paper analytically presents players’ best responses and provides insights for defense strategy at NE.
Due to the wide spectrum of the game-theoretic methods used for critical infrastructures, we now briefly consider the ones that are directly related to our discrete cyber–physical component models. These are much simpler than others used in infrastructures such as power distribution, transportation, and agriculture [
11]. For example, partial differential equations that model traffic dynamics. In terms of overall goals, they belong to formulations that integrate system reliability and robustness parameters [
22], which are applied for example to smart power grids [
37], cloud computing infrastructures [
38], and power systems [
39]. Within this class, Stackelberg games are an important subclass, wherein the provider chooses actions based on instantaneous information. They lead to more reactive and sensitive responses to dynamic disruptions compared to long-term strategies used in Markov game models [
37,
40].
Stackelberg formulations have been applied to discrete models of cyber–physical infrastructures in various forms [
36], and an important subset is formulated using the number of cyber and physical components that are attacked or reinforced. These formulations capture infrastructures with a large number of components, and are coarser than formulations that consider the attack and defense of individual cyber and physical components [
41]. The correlation function was proposed in [
2] to capture the dependencies between the survival probabilities of cyber and physical sub-infrastructures; this is a generalization of simple linear forms studied earlier in [
4,
5]. First-order differential conditions on the sub-infrastructure survival probabilities are proposed in [
2] as a generalization of the statistical independence and contest survival functions [
42], and the role of multiplier functions on these conditions has been further expanded in [
1].
We now place our formulation and results within the broader context above. The composite utility functions described in the introduction generalize the sum-form [
2] and product-form [
3] utility functions used for infrastructures with discrete components. The composite utility functions have been applied to more general systems of systems (SOS) in [
1,
43], and here we customize them to cyber–physical sub-infrastructures. The resultant NE conditions unify the previous results by using composite gain–cost terms (Theorem 1), and also provide second-order NE derivative conditions (Theorem 2), which together enable us to apply them to more detailed and newer (metro system) infrastructure models. SOS have been studied under a similar formulation [
43,
44], and also under additional conditions due to an asymmetric role played by the inter-connection network [
1,
45,
46]. The current paper explicitly targets the cyber and physical sub-infrastructures, provides in-depth results based on cyber–physical correlations, and also addresses the second-order NE conditions that have not been addressed in earlier works on cyber–physical infrastructures [
2,
3]. To make the presentation self-contained, we provide or re-state definitions of various terms needed for our formulation (
Section 3) from the references.
4. Game-Theoretic Formulation
The provider’s objective is to make the infrastructure resilient by reinforcing and cyber and physical components, respectively, to minimize the utility function. For uniform component reinforcement costs, we have , where and are reinforcement costs of cyber and physical components, respectively. The attacker’s objective is to disrupt the infrastructure by attacking or cyber and physical components, respectively (but not both), in order to minimize the utility function. For uniform component attack costs, we use , where and are the attack costs of cyber and physical components, respectively, and only one of and is non-zero.
4.1. Nash Equilibrium Conditions
The Nash equilibrium conditions are derived by equating the corresponding derivatives of the utility functions (as shown in
Section 1) to zero, which yields
where
for the provider. We define
as the
composite gain–cost term, and
as the
gain–cost gradient with respect to
,
. For the attacker, we similarly obtain, for
,
4.2. OR Systems
The OR subsystems are a special case where the probability of simultaneous failures of cyber and physical sub-infrastructures is negligible. [
4]. Here, the infrastructure will fail if either of the cyber or physical sub-infrastructures fail, such that
, or equivalently
. In these (theoretical) systems, the dependence of
on system parameters at NE is easier to derive and interpret, since it is determined entirely by Condition 3 without involving
. We have a much simpler form of Condition 2 given by
and
. At NE, we have
wherein
and
are called the cyber and physical
scaled gain–cost gradients, respectively. Using Condition 3, we obtain the following estimates for the survival probabilities of cyber and physical sub-infrastructures:
These estimates for cyber and physical sub-infrastructures depend mainly on the corresponding scaled gain–cost gradients, and thus represent a “separation” of the cyber and physical parts at this level. In this sense, OR systems constitute an important analytical case wherein the cyber–physical correlations between the sub-infrastructures may be ignored. In addition, these estimates provide the sensitivity information of the survival probabilities of cyber and physical sub-infrastructures, and they depend only on the derivatives of the corresponding probabilities. Although they do not involve the failure correlation function , the cyber–physical interactions are still captured by and at the component level. Both survival probability estimates and are proportional to the corresponding weighted cost and reward functions, and are inversely proportional to their weighted derivatives. This seemingly counter-intuitive trend applies only to the set of Nash equilibria, and not to the overall system behavior.
4.3. Statistical Independence of Cyber and Physical Sub-Infrastructures
We consider that the cyber sub-infrastructure failures are statistically independent such that
and
. At NE, we have
We now substitute expressions for
and
based on Condition 3, and obtain the system of equations:
Qualitatively, at NE, the survival probability estimates of cyber and physical sub-infrastructures and have an inverse relationship, but their product is determined by and in a manner similar to the individual probabilities and of OR systems. However, unlike OR systems, statistical independence is not sufficient to decouple the estimates and so that they depend solely on and , respectively.
4.4. NE Sensitivity Functions
We now derive estimates for and at NE using the scaled gain–cost gradients and failure correlation function to obtain qualitative information about their sensitivities to different parameters from the provider’s perspective.
Theorem 1. Under Conditions 1, 2, and 3, an estimate of the survival probability of physical sub-infrastructure at the Nash equilibrium for isand, for , is An estimate of the survival probability of cyber sub-infrastructure is Proof: At NE, we have
and
. By using the formulae in Condition 2, we have
We now substitute expressions for
and
based on Condition 3, and obtain the system of equations:
The expression for is obtained by solving for using the above quadratic equation, and the expression for follows from the equation above it. □
Compared to OR Systems, there are significant cyber–physical interactions at the sub-infrastructure level in both and . In particular, depends on both and its partial derivatives with respect to , and the partial derivatives of and with respect to and , as expected. Its dependence on is implicit through the failure correlation function . The qualitative behavior of is quite similar with respect to , but its dependence on is also through f. They are both affected by and , and each of them in turn depends on the number of both cyber and physical component attacks and reinforcements. Thus, the estimates and reflect the correlations between the sub-infrastructures explicitly through f, as well as those captured by the survival probabilities of individual sub-infrastructures.
Theorem 1 utilizes
, which captures the failure effects of physical sub-infrastructure on the cyber sub-infrastructure. Alternatively, we can utilize
, which captures the failure effects of cyber sub-infrastructure on the physical sub-infrastructure. In this case, we obtain a quadratic expression in
. Then, we can estimate
in terms of
by solving the quadratic equation as in Theorem 1. Additionally, results expressed in terms of
and
can be converted between each other using the following expression:
The qualitative effects of and on the sensitivity function estimates is quite similar, and their choice is determined by their functional forms and the accuracy with which they can be estimated.
The estimates in Theorem 1 are based on the first-order derivatives of utility functions, and their minimization leads to second-order derivative conditions, which in turn provides an upper bound on as follows:
Theorem 2. Under Conditions 1, 2, and 3, an upper bound on the survival probability of physical sub-infrastructure at the Nash equilibrium for is Proof: At NE, the first derivative of the utility function is given by
where
. The second derivative condition is given by
which in turn provides a bound on
as follows,
The upper bound on then follows from Condition 2 by using and . □
This theorem indicates that the ratio of the correlation function and its derivatives and could limit the achievable . The cost term and can counter this effect somewhat, but can add to this effect.
4.5. Sum-Form and Product-Form Utility Functions
The utility functions can be specialized to reflect different aspects of the infrastructure, in particular explicitly expressing the terms using
. Corresponding to the
sum-form in
Section 1, the utility of the attacker is given by
where
is the expected reward for the cost
of cyber or physical attacks. Similarly, the
product-form utility of the attacker is given by
which represents the expected cost when the infrastructure survives the attacks and thus represents “wasted” effort. The individual terms of the utility functions for sum- and product-forms are simplified as shown in
Table 3 for the provider.
Special cases of Theorem 1 for sum- and product-forms are presented in [
2,
4], and the second-order condition in Theorem 2 provides us with additional conditions on achievable
. In particular, for the sum-form utility of the provider, the second derivative condition is
which provides an upper bound on
. And for the product-form utility of the provider, the second derivative condition is
which provides an upper bound on
.
4.6. Survival Probabilities of Sub-Infrastructures
It is instructive to compare the individual survival probabilities of cyber and physical sub-infrastructures and , respectively, since the minimum of the two determines the survival probability of the infrastructure. Using the equations from the proof of Theorem 1, we have
In this section, for simplicity we denote
,
,
, and
by
,
,
, and
, respectively. By dividing the above two equations by
and
, respectively, and eliminating the term
by subtraction, we obtain the following condition:
Then, by using
, we obtain the following relationship between
and
:
By comparing the right hand side to
, the condition
is equivalent to
where ≐ is either ≤ or ≥ based on the sign of the denominator above. If ≐ is ≤, then the above condition is not satisfied if the right hand side is negative, which in turn corresponds to the signs of the two terms
and
being the opposite. On the other hand, if ≐ is ≥, then this condition is not true if the right hand side is greater than 1. These two boundary conditions determine that one of the two conditions
and
is true. In the other cases, this relationship is not that simply determined, and can take a more complicated form.
For the special case , we have
Then, the condition
leads to a quadratic equation with the following solution:
The boundary conditions in this case can be derived as in the general case. However, a different line of analysis done in this case in [
5] provides a much simpler characterization of the relationship between
and
. It yields the following simpler condition:
where
and
. Then, the relationship between
and
is described by 12 different regions determined solely by
,
,
, and
such that in each region exactly one of the two conditions
and
is true.
5. Application Examples
In this section, we expand the three examples from
Section 3.2 by taking more component details into account. First, we consider different types of cyber and physical components such that
,
is the number of cyber components of type
i, and
,
is the number of physical components of type
j. Thus, in terms of the original indices, we have
and
. We define sub-infrastructures consisting of only cyber components of type
i and physical components of type
j, with their survival probabilities denoted by
and
, respectively. Now we generalize Condition 3 as follows.
Condition 4. The survival probabilities of cyber and physical sub-infrastructures are given byfor , , corresponding to cyber components of type i, andfor , , corresponding to physical components of type j. The component failures are considered statistically independent for different types in [
5] such that
where
and
denote the probabilities of reinforced cyber component of type
i and reinforced physical component of type
j, respectively;
and
denote the probabilities of cyber component of type
i and physical component of type
j without reinforcement, respectively; and
and
denote the number of type
i cyber components and type
j physical components, respectively. These conditions in turn lead to the special case of Condition 4: for
,
,
We consider that these conditions are satisfied in both of the following examples.
5.1. Cloud Computing Infrastructure
The simple cloud computing infrastructure model of Example 1 in
Section 3.2 is expanded to include a gateway router at each site, which connects to all servers at the site. A cyber attack on a gateway router will also have essentially the same effect as a physical fiber attack—namely, disconnecting all servers at the site. A fiber attack requires physical proximity, whereas a router cyber attack may be remotely launched, thereby representing different types of costs. Cyber components now belong to two classes, namely, servers and routers, such that
where
and
denote the number of reinforced servers and routers, respectively. Similarly, we have
, where
and
denote the number of servers and routers attacked, respectively. Then, for the two cyber sub-infrastructures, we have the failure correlation functions
and
, wherein the physical failures are amplified by
for the servers but are the same for routers. Thus, the composite failure correlation function
is given as follows:
Then, the survival probabilities of cyber-reinforced components are computed separately for the servers and routers, which are denoted by
and
, respectively. The probability that a cyber-reinforced server survives fiber or router attacks is given by
which now depends on both physical attacks on fiber and cyber attack on routers. An estimate of the probability that a cyber-reinforced router survives a physical fiber attack is given by
since a cyber attack on a reinforced router has no impact and a fiber attack will disconnect only one router. If the router is not cyber-reinforced, then we have
which additionally depends on
. By using these estimates for the router, we have
which increases in the number of cyber router attacks but decreases in the number of attacks on non-reinforced routers. If the cyber component, server or router, is not reinforced, it will be brought down by a direct cyber attack or indirectly by fiber attack, but the latter will have a greater impact. However, cyber attacks on servers and routers will have different impacts on the availability of the infrastructure. That is, a server attack will only bring it down, but a router attack will make all
servers unavailable. In some current infrastructures,
could be on the order of thousands. Thus, for a server that is not cyber-reinforced, we use the estimate
which reflects the additional lowering of survival probability inversely proportional to the level of cyber attack
, and to
but amplified by a factor
. Thus, for servers, we have
which increases in the number of server attacks but decreases in the attacks on non-reinforced routers and fibers.
The survival probabilities of physical fiber components depend on
such that
and
By combining the two formulae for fiber, we have
which increases in the number of physical attacks. Similar to the case of the metro system, in addition to
and
, where
, the survival probabilities of cyber and physical sub-infrastructures are determined by the correlation function
, as described in
Section 4.6.
5.2. Metro System
We refine the metro system model of Example 2 in
Section 3.2 to include multiple traffic control centers, each connecting to all signals of a single line. A cyber attack on a control center will disconnect all signals of its line and disrupt all trains running on that line. Now, we separate the cyber components into two classes, namely, control centers and signals, and
such that
and
denote the number of reinforced control centers and signals, respectively. Similarly,
, such that
and
denote the number of control centers and signals attacked, respectively. Since we focus on the smooth running of the trains, it is more instructive to carry out the analysis in terms of the failure correlation function
. Then, for the sub-infrastructures, we have the failure correlation functions
and
, wherein the physical failures are amplified by
for control centers and by
for the signals. We now estimate the composite failure correlation function
as follows:
where
and
are the probabilities of a cyber attack on a control center and a signal of the metro system, respectively, and
and
are conditional failure probabilities of the control center and signal, respectively, given that the cyber sub-infrastructure of the metro system failed.
The probability that a physically-reinforced actuator on a train survives cyber attacks on a control center or signal is given by
which now depends on both cyber attacks on control centers and signals. If the actuator is not physically-reinforced, then we have
which additionally decreases with respect to
. By using these estimates for an actuator, we have
which increases in the number of physical attacks on actuators, but decreases in the number of cyber attacks on control centers and signals. Since the term
appears in the denominator,
in Theorem 1 decreases with the number of physical attacks
, and increases with
and
, which are the number of cyber attacks on the control centers and signals exceeding the reinforcements, respectively. The latter condition may appear counter-intuitive at the surface, but note that it only characterizes the states that satisfy NE conditions. An analogous dependence of
on the parameters
,
,
, and
(shown in Theorem 1) is less direct, since
appears inside the square root but is qualitatively somewhat similar since they appear in the denominator.
The cyber component survival probabilities are computed separately for the reinforced control centers and signals, denoted by and , respectively. The survival probabilities of cyber components are given by and where . Then we have where , which increases in the total number of cyber attacks on the specific type of component. Since the term appears in the denominator, in Theorem 1 decreases with the number of cyber attacks , where .
Note that the net effect of the number of attacks and reinforcements on the survival probabilities of cyber and physical sub-infrastructures is also determined by the correlation function as described in
Section 4.6, in addition to
and
, where
.
5.3. Smart Power Grid Infrastructure
The power grid model described in Example 3 in
Section 3.2 is expanded to include smart meters on the lines that provide the demand information to generation and distribution control systems. The smart meters can be attacked by cyber means to manipulate the demand information (e.g., to make it zero). We group the cyber components into two classes, namely, communication nodes and smart meters, such that
, where
and
are the number of reinforced communication nodes and smart meters, respectively. Similarly, we have
, where
and
are the number of communication nodes and smart meters attacked, respectively. Since the electricity transmission in the grid takes place on the physical sub-infrastructure, it is more instructive to carry out the analysis in terms of the failure correlation function
. As in the metro system example, for the sub-infrastructures, we have the failure correlation functions
and
, wherein the attacks on communication nodes are amplified by the number of lines
controlled by each of them, but are the same for smart meter attacks. Then, we utilize the estimate
where
and
are the probabilities of an attack on a communication node and smart meter, respectively, and
and
are conditional failure probabilities of a communication node and smart meter, respectively, given that the cyber sub-infrastructure failed.
Then, the survival probabilities of cyber components are estimated separately for the communication nodes and smart meters. The survival probabilities of the power supply lines with and without reinforcement are denoted by
and
, respectively. A communication node or a smart meter may be disabled by cyber means, which will disrupt the power flow on the lines so that
for physically-reinforced power lines. Note that cyber attacks on communication nodes are amplified by
times compared to attacks on smart meters. Each power line can be directly disrupted by physical means such that it can be brought down if not reinforced, and thus we have
which reflects the amplified effect of cyber attacks on communication nodes compared to physical line attacks. Combining the two formulae, we have
which increases in the number of attacks on non-reinforced power lines and decreases in the number of attacks on non-reinforced communication nodes and non-reinforced smart meters, but the former effect is amplified
times. The survival probabilities of cyber components are given by
and
where
. Then, we have
where
, which increases in the total number of cyber attacks. As in the previous examples, the net effect of the number of attacks and reinforcements on the survival probabilities of cyber and physical sub-infrastructures is also determined by the correlation function (in addition to
and
, where
) as described in
Section 4.6.