Intelligent Intrusion Detection of Grey Hole and Rushing Attacks in Self-Driving Vehicular Networks
Abstract
:1. Introduction
2. Related Works
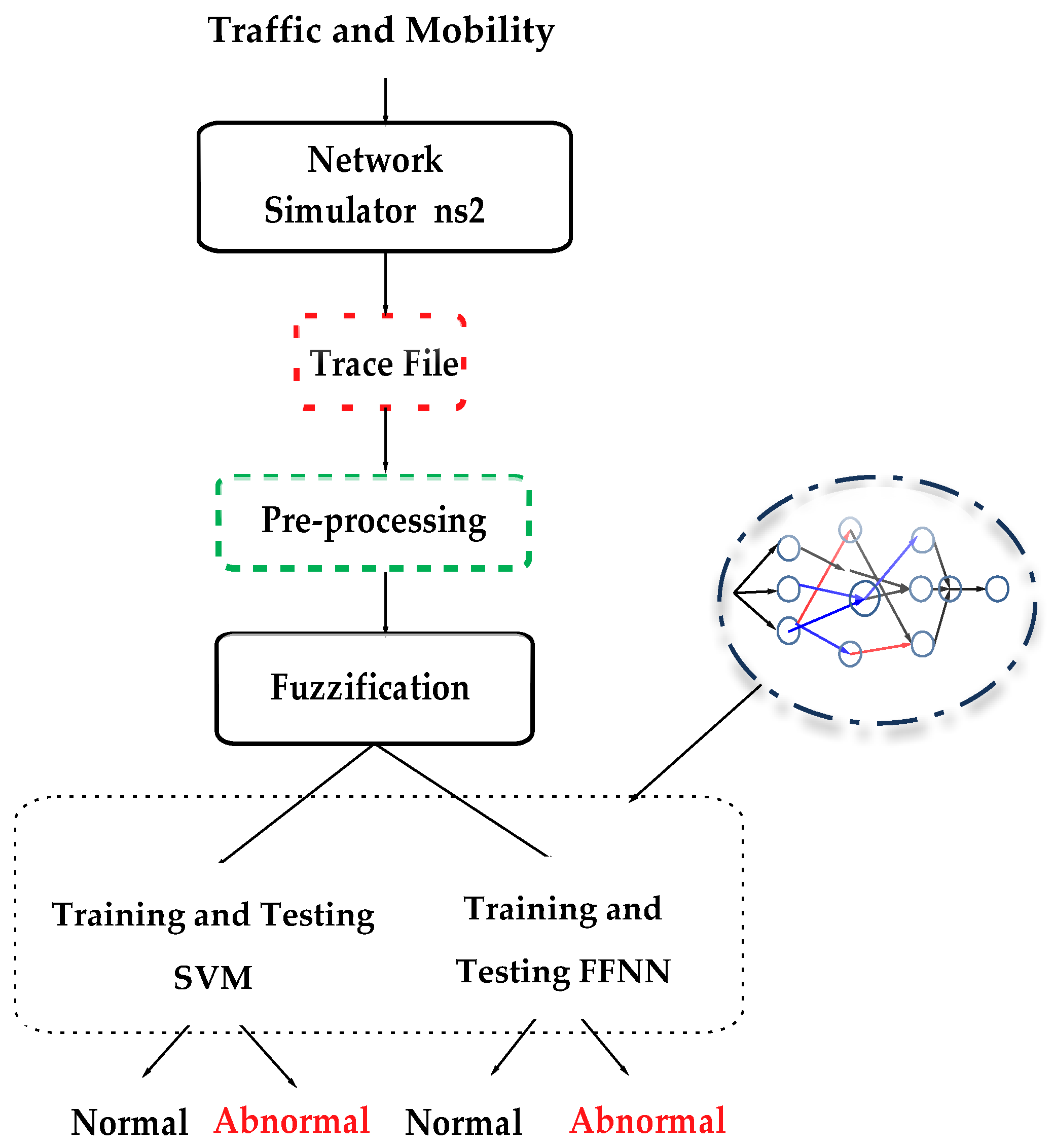
3. The Proposed Intrusion Detection System
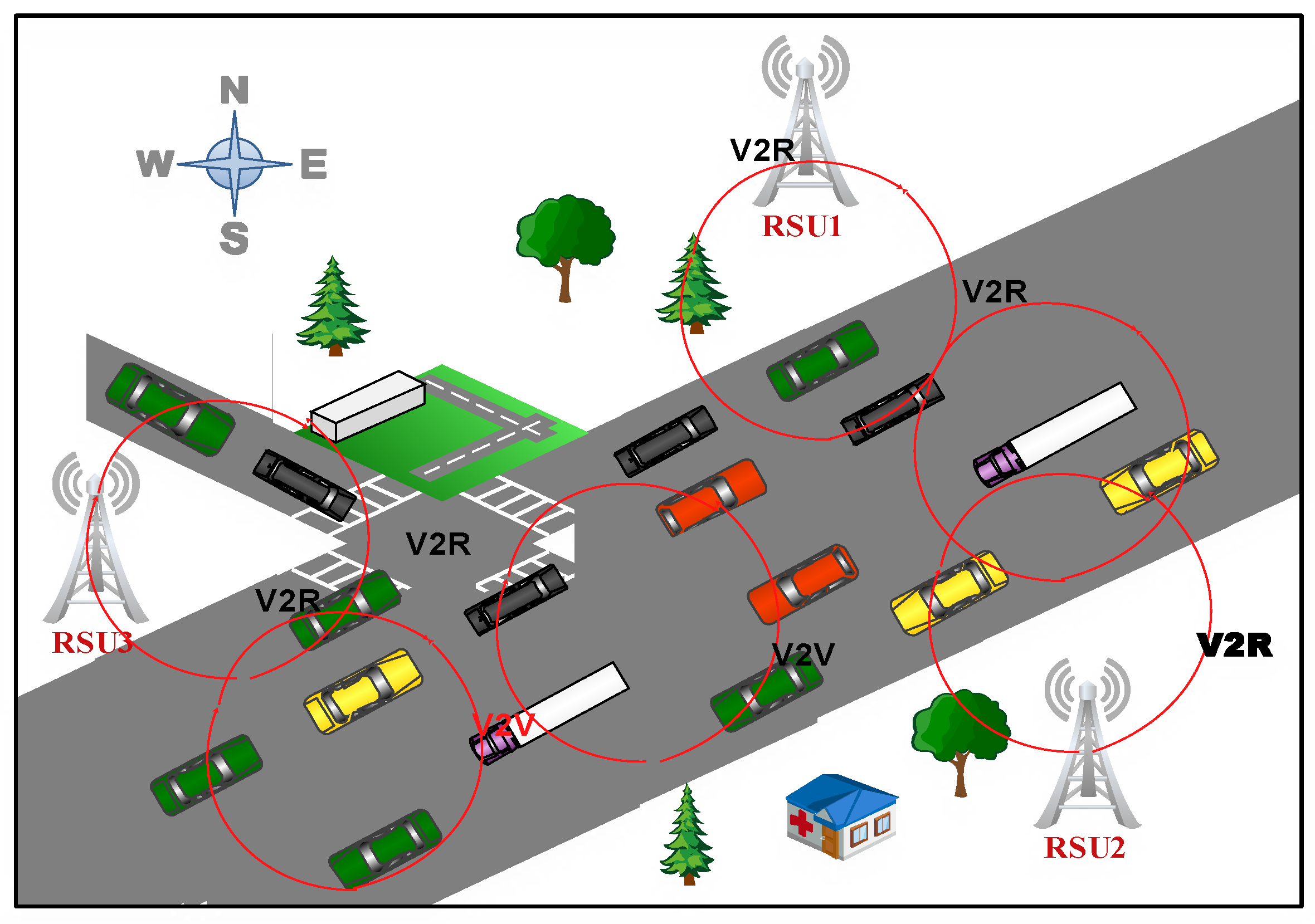
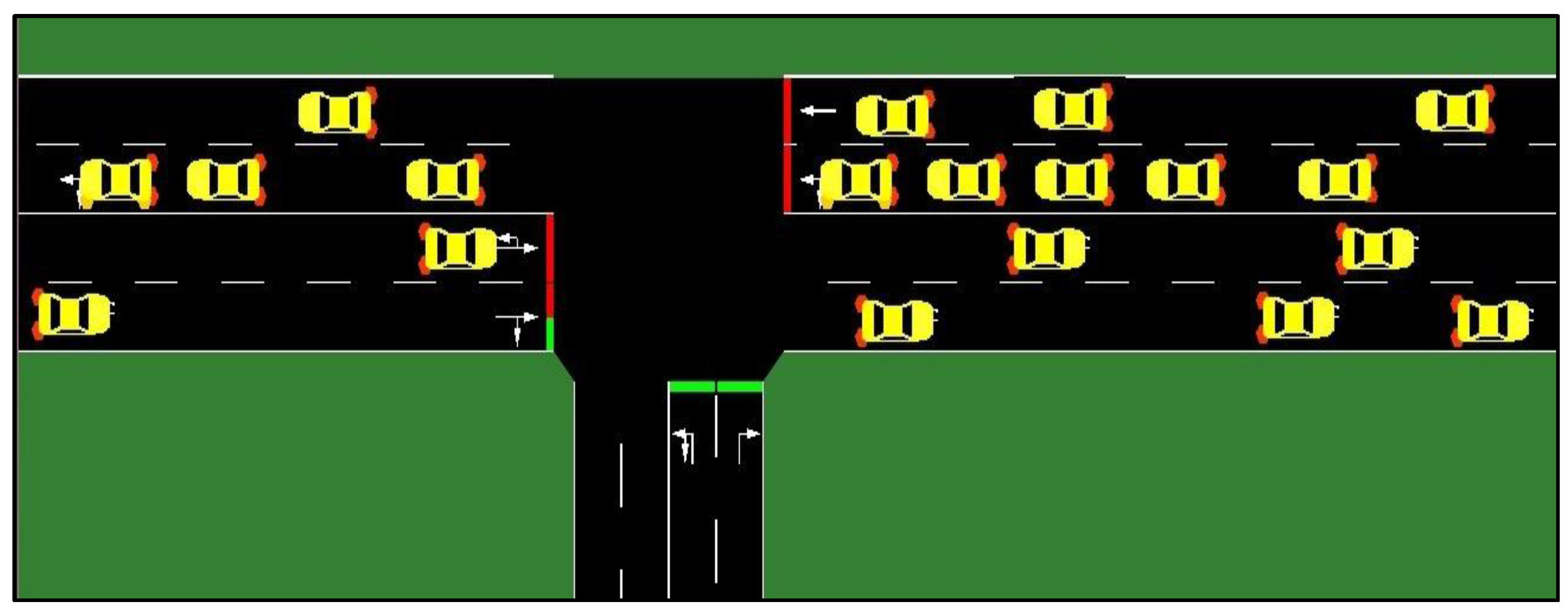
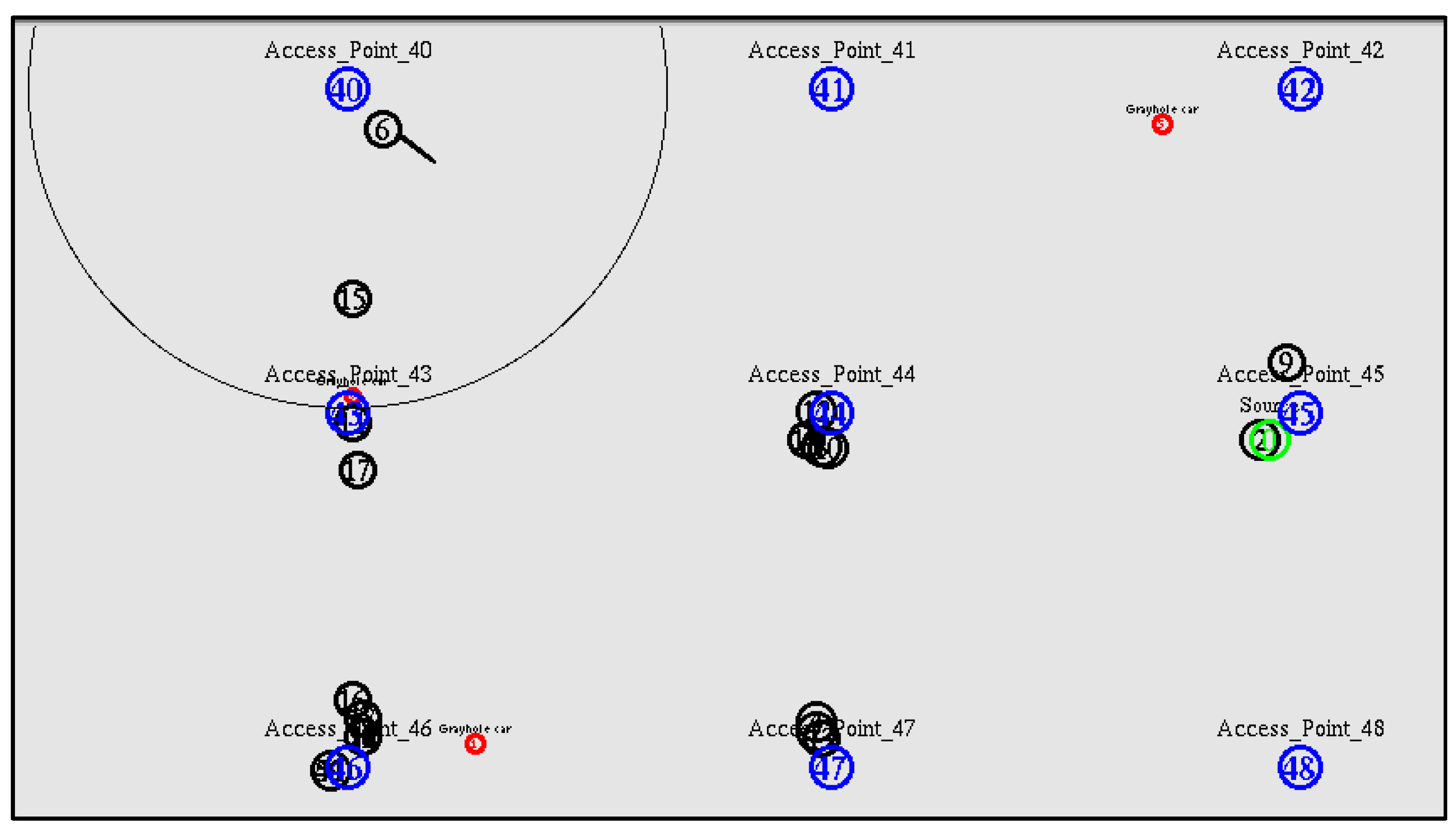
3.1. Simulation of Traffic and Mobility Scenarios
3.2. Feature Sets and Extraction
- Generate the trace file from ns-2.
- Use the AWK language to evaluate the output file from ns-2. The trace file is processed using the AWK language to determine the packet delivery rate (PDR), end-to-end delay and throughput.
- Produce 21 features that define normal and malicious behaviour.
- Choose 15 features that, based on our previous study [25], accurately reflect the behaviour of self-driving vehicles. Proportional Overlapping Score (POS) were used to extract significant features from the trace files.
| Algorithm POS Method | |
| 1. | inputs: “data1.csv”. |
| 2. | output: Sequence of the selected features. |
| 3. | install.packages(“propOverlap”). |
| 4. | source(“http://bioconductor.org/biocLite.R”). |
| 5. | biocLite(“Biobase”). |
| 6. | library(propOverlap). |
| 7. | ?propOverlap. |
| 8. | getwd(). |
| 9. | data <- read.csv(“data1.csv”,header=T). |
| 10. | str(data). |
| 11. | data <- t(data). |
| 12. | G <- data[1:23,] # define the features matrix 23. |
| 13. | G <- jitter(G). # to avoid the noise in data |
| 14. | class <- as.factor(data[24,]) #define class labels. |
| 15. | set.seed(1234). |
| 16. | selection <- Sel.Features(G, Class, K = 23,Verbose = TRUE) # the main function. |
| 17. | selection$Features. # extract the number of features. |
| 18. | selection$Measures. # extract name of features. |
3.3. Fuzzification of the Dataset
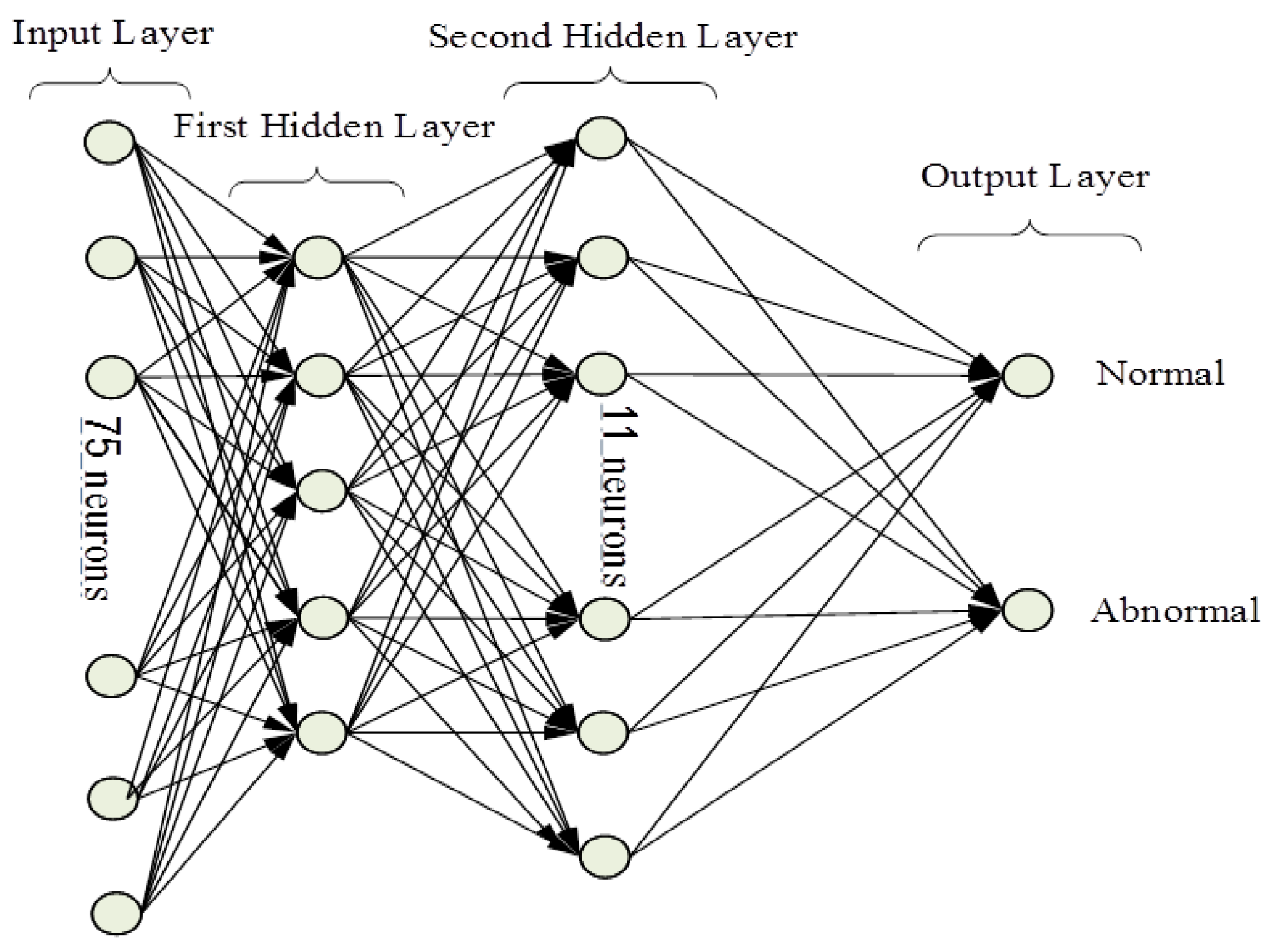
3.4. Intelligent Detection System
3.5. Generate Grey Hole and Rushing Attacks
3.6. Methodolgy
- 1st Stage
- (generation of the realistic world): Obtain the mobility and traffic model which shows the actual movement of vehicles in VANETs. The ns-2 in this stage made use of the output file from MOVE and SUMO as input to obtain a trace file that defines both normal and abnormal.
- 2nd Stage
- (ns-2): We made use of the output file extracted from the former stage as input files for the ns-2 in this stage. We replicate normal, rushing attacks and grey holes to create two files: Network Animator (NAM) file and trace file.
- 3rd Stage
- (data extraction): Here we revisit stage two to extract all the features that were found in the trace file. Nonetheless, our proposed system can, however, work with a reduced feature set of just fifteen important features selected from all of the features [19]. Decreasing the number of features has an important effect in escalating the rate of detection and reducing the rate of false alarms.
- 4th Stage
- (pre-processing): Here, we convert some letters and symbols to numerical values using the selected features that were pre-processed. We also want to use these selected features to generate a homogenous distribution to balance the various types of classes in the data collection so as to increase the efficiency of the rate of detection and normalization process to turn all the values of the features between 0 and 1 according to Equation (4):
- 5th Stage
- (fuzzy set): In this stage, we convert the ordinary data that were generated in Stage 4 into fuzzified data. The process here can be used in solving some common problems that usually occur in the data set like the lack of clarity and overlap.
- 6th Stage
- (training and testing phase—FFNN): Stage 5 data are used to train and test the FFNN. We also obtain the rate of detection for both normal and abnormal behaviour in this stage and then determine the four alarm types.
- 7th Stage
- (training and testing phase—SVM): Here, in parallel to Stage 6, the training and testing of the SVM is carried out with fuzzified data, which was obtained in Stage 5 in order to identify the efficiency of the security system in the identification of rushing vehicles and grey hole in comparison to normal vehicles.
- 8th Stage
- (Comparison): Here, we compare both of the proposed intrusion detection systems that are based on categories, the number of false alarms, rate of detection, standard deviation and rate of error.
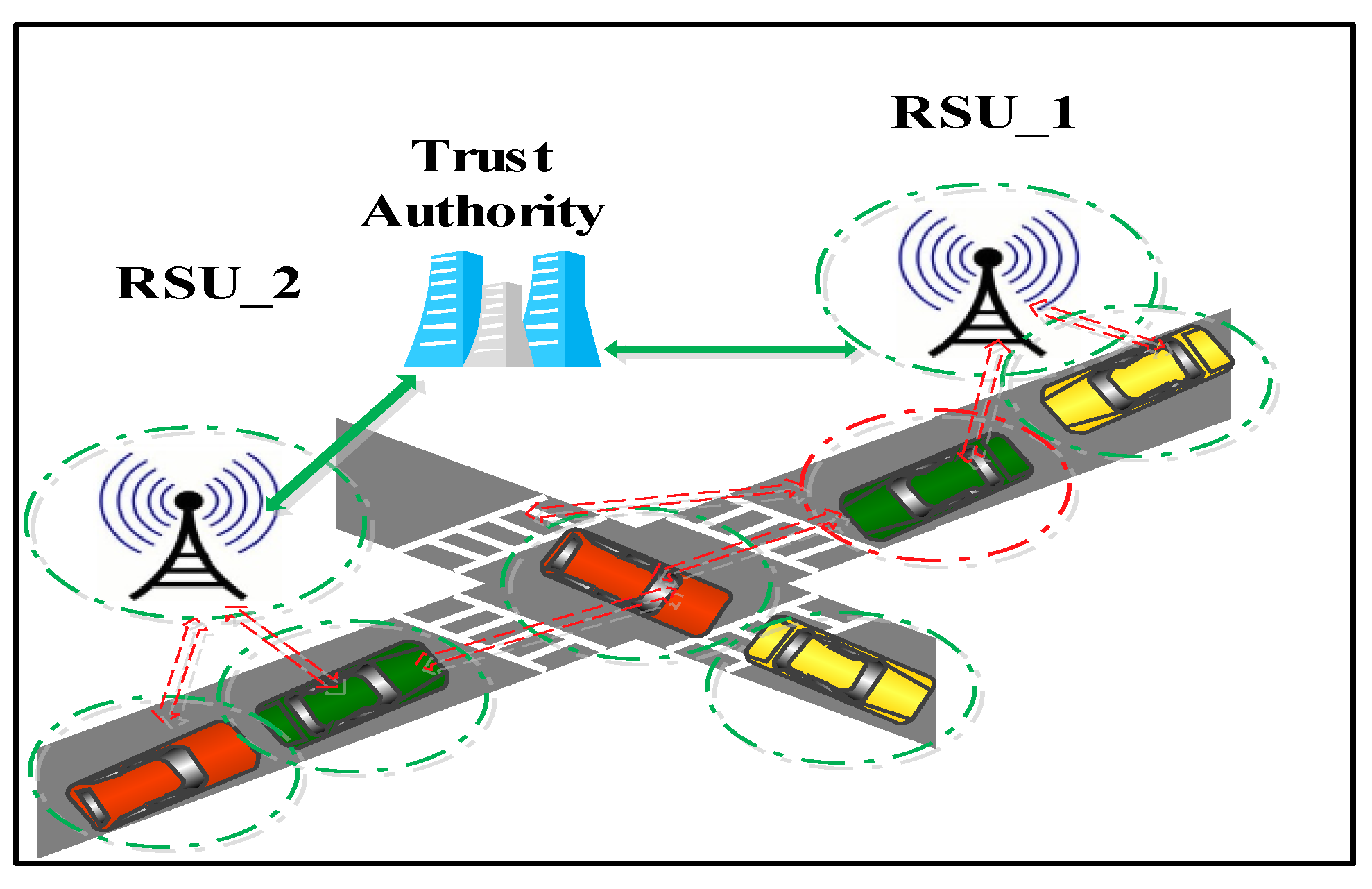
4. Response Mechanism
- TAs are responsible for authorization communication between RSUs and vehicles. They contain all vital information about traffic statistics and streets. The Certificate Revocation List (CRL) is published periodically by the TAs to their RSUs and it has the capability of detecting, receiving and communicating messages to TAs. The TAs and RSU are the building blocks of the system and are considered trusted entities of the system.
- RSUs provide the backbone communication of self-driving vehicles. These vehicles depend heavily on these vital units in VANETs. The wired communication between immobile infrastructures on the road site with TAs is an authentication feature [40].
- Every vehicle is equipped with an Identification On-Board Unit (ID-OBU), which allows it to share local traffic data and control information between vehicles in their radio zone.
- trusted element because of its wired connection to TAs;
- low delay;
- low bit error rates; and
- high bandwidth.
4.1. Data Link Layer
- The data link layer provides basic addressing and access control to the physical layer on VANETs of self-driving and semi self-driving vehicles.
- It facilitates vehicle communication among the subnet, which is done through a reconfiguration requirement.
4.2. Safe Mode
5. Experimental Results
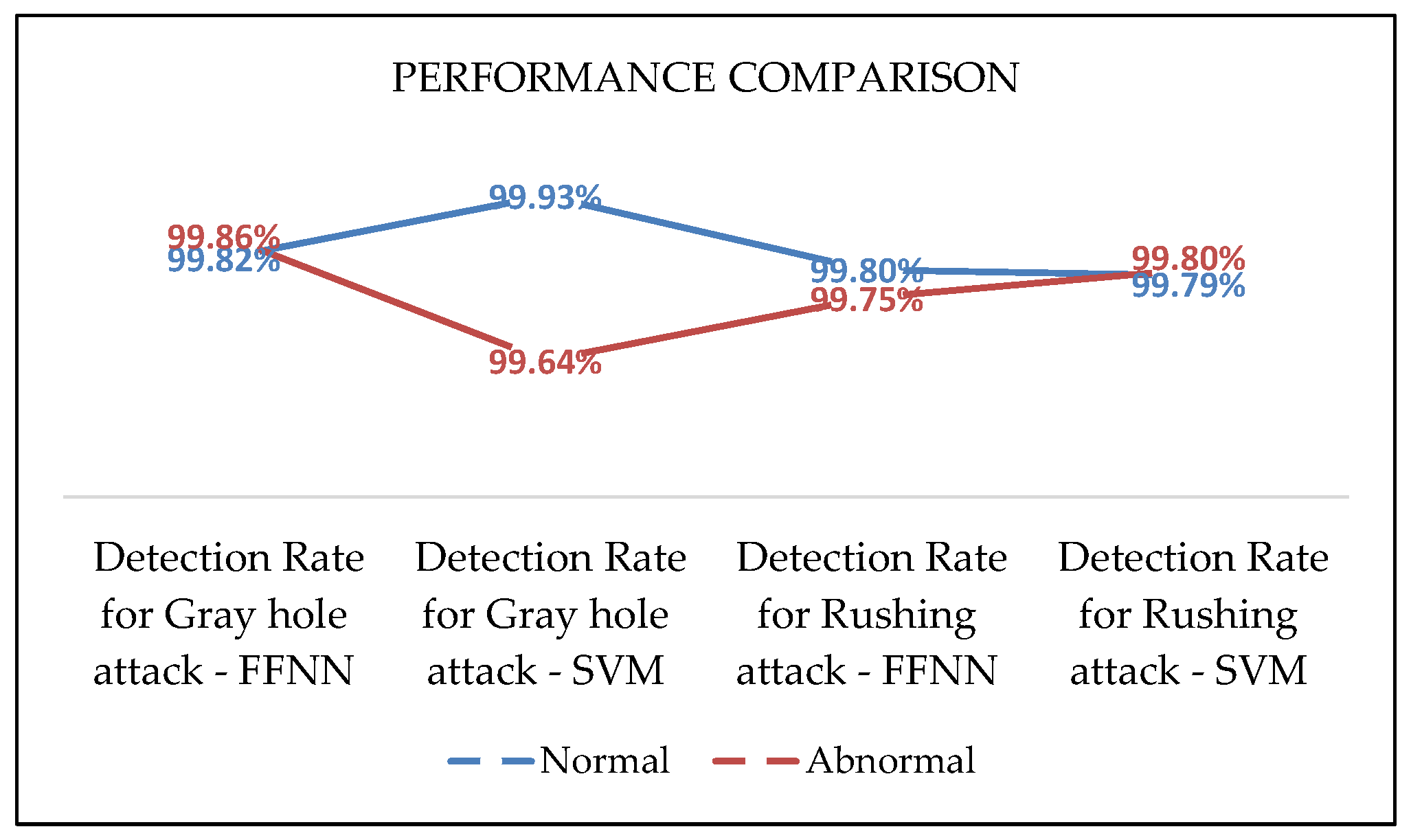
5.1. Detection System Phase
5.1.1. Testing Neural Network to Detect Grey Hole Attacks
5.1.2. Testing Neural Network to Detect Rushing Attack
5.2. Response Mechanism Protocol Phase
5.2.1. Normal Behaviour
5.2.2. Abnormal Behaviour
6. Discussion
7. Conclusions
Acknowledgments
Author Contributions
Conflicts of Interest
References
- Alheeti, K.A.; Gruebler, A.; McDonald-Maier, K.D.; Fernando, A. Prediction of DoS Attacks in External Communication for Self-driving. In Proceedings of the IEEE International Conference on Consumer Electronic (ICCE), Las Vegas, NV, USA, 7–11 January 2016.
- Wyglinski, M.; Huang, X.; Padir, T.; Lai, L.; Eisenbarth, T.; Enkatasubramanian, K. Security of Autonomous Systems Employing Embedded Computing and Sensors. Micro IEEE 2013, 33, 80–86. [Google Scholar] [CrossRef]
- Breu, J.; Brakemeier, A.; Menth, M. A quantitative study of Cooperative Awareness Messages in production VANETs. EURASIP J. Wirel. Commun. Netw. 2014, 1, 1–8. [Google Scholar] [CrossRef]
- Koscher, K.; Czeskis, A.; Roesner, F.; Patel, S.; Kohno, T.; Checkoway, S.; McCoy, D.; Kantor, B.; Anderson, D.; Shacham, H.; et al. Experimental security analysis of a modern automobile. In Proceedings of the IEEE Symposium on Security and Privacy, Oakland, CA, USA, 16–19 May 2010.
- Alheeti, K.A.; Gruebler, A.; McDonald-Maier, K.D. On the Detection of Grey hole and Rushing Attacks in Self-Driving Vehicular Networks. In Proceedings of 7th Computer Science and Electronic Engineering Conference (CEEC), Colchester, UK, 24–25 September 2015.
- Nzouonta, J.; Rajgure, N.; Wang, G.; Borcea, C. VANET routing on city roads using real-time vehicular traffic information. IEEE Trans. Veh. Technol. 2009, 58, 3609–3626. [Google Scholar] [CrossRef]
- Surmukh, S.; Kumari, P.; Agrawal, S. Comparative Analysis of Various Routing Protocols in VANET. In Proceedings of 5th IEEE International Conference on Advanced Computing & Communication Technologies, Haryana, India, 21–22 February 2015.
- Kenney, J. Dedicated Short-Range Communications (DSRC) Standards in the United States. Proc. IEEE. 2011, 99, 1162–1182. [Google Scholar] [CrossRef]
- Chetan, V.S.; Benni, N.S.; Bhushan, C. Security framework for VANET for privacy preservation. In Proceedings of the 2013 Fourth International Conference on Computing, Communications and Networking Technologies (ICCCNT), Tiruchengode, India, 4–6 July 2013.
- Raya, M.; Papadimitratos, P.; Hubaux, J. Securing vehicular communications. IEEE Wirel. Commun. Mag. 2006, 13, 8–15. [Google Scholar] [CrossRef]
- Usha, G.; Bose, S. Impact of Gray hole attack on ad hoc networks. In Proceedings of the International Conference on IEEE, Information Communication and Embedded Systems (ICICES), Chennai, India, 21–22 February 2013.
- Reddy, K.G.; Thilagam, P.S.; Rao, B.N. Cross-layer IDS for rushing attack in wireless mesh networks. In Proceedings of the Second International Conference on Computational Science, Engineering and Information Technology, Coimbatore, India, 26–28 October 2012.
- Assila, A.; Jabri, I.; Ltifi, A. Secure Architecture Dedicated for VANET Alarm Messages Authentication through Semantic Verification. In Proceedings of the 6th International Conference on IEEE Sciences of Electronics, Technologies of Information and Telecommunications (SETIT), Sousse, Tunisia, 21–24 March 2012.
- Alheeti, K.A.; Al-Jabouri, L.; McDonald-Maier, K.D. Increasing the Rate of Intrusion Detection based on a Hybrid Technique. In Proceedings of the 5th IEEE International Conference on Computer Science and Electronic Engineering (CEEC’13), Colchester, UK, 17–18 September 2013.
- Zaidi, K.; Milojevic, M.; Rakocevic, V.; Nallanathan, A.; Rajarajan, M. Host Based Intrusion Detection for VANETs: A Statistical Approach to Rogue Node Detection. IEEE Trans. Veh. Technol. 2015, 99, 1–6. [Google Scholar] [CrossRef]
- Banerjee, S. Detection/Removal of Cooperative Black and Gray Hole Attack in Mobile Ad-Hoc Networks. In Proceedings of the World Congress on Engineering and Computer Science (WCECS), San Francisco, CA, USA, 22–24 October 2008.
- Vuong, T.; Loukas, G.; Gan, D. Performance evaluation of cyber-physical intrusion detection on a robotic vehicle. In Proceedings of the IEEE Computer and Information Technology, Ubiquitous Computing and Communications, Dependable, Autonomic and Secure Computing, Pervasive Intelligence and Computing (CIT/IUCC/DASC/PICOM), Liverpool, UK, 26–28 October 2015.
- Sedjelmaci, H.; Senouci, S.M. An accurate and efficient collaborative intrusion detection framework to secure vehicular networks. Comput. Electr. Eng. 2015, 43, 33–47. [Google Scholar] [CrossRef]
- Bouali, T.; Senuci, S.; Sedjelmaci, H. A distributed detection and prevention scheme from malicious nodes in vehicular networks. Int. J. Commun. Syst. 2016, 49, 1683–1704. [Google Scholar] [CrossRef]
- Zhang, Y.; Lee, W. Intrusion detection in wireless ad-hoc networks. In Proceedings of the 6th annual International Conference on Mobile Computing and Networking, Boston, MA, USA, 6–11 August 2000.
- Pavani, K.; Damodaram, A. Anomaly Detection System for Routing Attacks in Mobile Ad Hoc Networks. Int. J. Netw. Secur. 2014, 6, 13–26. [Google Scholar]
- Issariyakul, T.; Hossain, E. Introduction to Network Simulator ns-2, 2nd ed.; Springer: New York, NY, USA; Dordrecht, The Netherlands; Heidelberg, Germany; London, UK, 2012. [Google Scholar]
- Alheeti, K.A.; Venus, W.; Suleiman, M. The Affect of Fuzzification on Neural Networks Intrusion Detection System. In Proceedings of the IEEE Computer Society, Xi’an, China, 25–27 May 2009.
- Selvamani, K.; Anbuchelian, S.; Kanimozhi, S.; Elakkiya, R.; Bose, S.; Kannan, A. A hybrid framework of intrusion detection system for resource consumption based attacks in wireless ad-hoc networks. In Proceedings of the IEEE International Conference Systems and informatics (ICSAI), Yantai, China, 19–20 May 2012.
- Alheeti, K.A.; Gruebler, A.; McDonald-Maier, K.D. An Intrusion Detection System against Black Hole Attacks on the Communication Network of Self-Driving Cars. In Proceedings of the IEEE Sixth International Conference on Emerging Security Technologies (EST), Braunschweig, Germany, 3–5 September 2015.
- Using Artificial Intelligence to Create a Low Cost Self-Driving car. Available online: http://budisteanu.net/Download/ISEF%202%20Autonomous%20car%20Doc%20particle.pdf (accessed on 7 November 2015).
- The Network Simulator- ns-2. Available online: http:// www.isi.edu/nsnam/ns (accessed on 12 April 2016).
- Danquah, W.; Altilar, D. Hybrist Mobility Model—A Novel Hybrid Mobility Model for VANET Simulations. Int. J. Comput. Appl. 2014, 86, 15–21. [Google Scholar]
- Pandey, A. Simulation of Traffic Movement in VANETs Using Sumo. Ph.D. Thesis, National Institute of Technology, Rourkela, India, 2013. [Google Scholar]
- Car 2 Car Communication Consortium. The Handbook for Vehicle-to X Cooperative Systems Simulation. Available online: https://www.car-2-car.org/index.php?id=5 (accessed on 10 June 2015).
- DLR—Institute of Transportation Systems, SUMO—Simulation of Urban MObility. Available online: http://sumo.sourceforge.net/doc/current/docs/userdoc/Data/Scenarios/TAPASCologne.html,2011 (accessed on 15 March 2016).
- Dean, A. Neural Network Vision for Robot Driving. Available online: https://www.ri.cmu.edu/pub_files/ pub2/pomerleau_dean_1995_1/pomerleau_dean_1995_1.pdf (accessed on 8 April 2016).
- Study of Network Simulator 2. Available online: http://www.isi.edu/nsnam/ns/ns-documentation.html (accessed on 10 September 2015).
- Khan, N.; Usmani, Z. Performance Analysis of Modelling Wireless Network in Campus Environment; Topology Elsevier: Amsterdam, The Netherlands, 2008. [Google Scholar]
- Zhou, L.; Hass, Z. Security Ad hoc Networks. IEEE Netw. Mag. 1999, 13, 24–30. [Google Scholar] [CrossRef]
- Mahmoud, O.; Harrison, A.; Perperoglou, A.; Gul, A.; Khan, Z.; Metodiev, M.V.; Lausen, B. A feature selection method for classification within functional genomics experiments based on the proportional overlapping score. BMC Bioinform. 2014, 15, 1–20. [Google Scholar] [CrossRef] [PubMed]
- Official Site for PropOverlap Package. Available online: http://cran.r-project.org/web/packages/ propOverlap/index.html (accessed on 7 April 2016).
- Guanrong, C. Introduction to Fuzzy Sets, Fuzzy Logic and Fuzzy Control Systems, 2nd ed.; CRC Press: Houston, TX, USA, 2001; ISBN 0-8493-1658-8. [Google Scholar]
- Alheeti, K.A.; Gruebler, A.; McDonald-Maier, K.D. An intrusion detection system against malicious attacks on the communication network of driverless cars. In Proceedings of the 12th Annual IEEE Consumer Communications and Networking Conference (CCNC), Las Vegas, NV, USA, 9–12 January 2015.
- Peng, Y.; Abichar, Z.; Chang, J. Roadside-aided routing (RAR) in vehicular networks. In Proceedings of the IEEE International Conference on Communications ICC 2006, Istanbul, Turkey, 11–15 June 2006.
- Alasmary, W.; Zhuang, W. Mobility impact in IEEE 802.11 p infrastructure less vehicular networks. Ad Hoc Netw. 2012, 10, 222–230. [Google Scholar] [CrossRef]
- Van, E.; Klein, W.; Karagiannis, G.; Heijenk, G. Exploring the Solution Space of Beaconing in VANETs. In Proceedings of the First IEEE Vehicular Networking Conference, VNC2009, Tokyo, Japan, 28–30 October 2009.
- Campolo, C.; Vinel, A.; Molinaro, A.; Koucheryavy, Y. Modeling broadcasting in IEEE 802.11p/WAVE vehicular networks. IEEE Commun. Lett. 2011, 15, 199–201. [Google Scholar] [CrossRef]
- Whitehouse, R.; Scott, M. Implementation of Data link Layer Protocols for a Network Simulator; Computer Science Tripos Part II; Homerton College, University of Cambridge: Cambridge, UK, 2011. [Google Scholar]
- Holma, H.; Antti, T. Wcdma for Umts, 3rd ed.; Wiley: Chichester, UK, 2000. [Google Scholar]
- Camps-Valls, G.; Bruzzone, L. (Eds.) Kernel Methods for remote Sensing Data Analysis; Section 5.64; Wiley: New York, NY, USA, 2009; pp. 78–79.
| Parameter | Value |
|---|---|
| Simulator | ns-2.35RC7 |
| Simulation time | 499 s |
| Number of nodes | 40 Vehicles |
| Number of RSUs | 9 RSUs |
| Type of Traffic | Constant Bit Rate (CBR) |
| Topology | 600 × 600 (m) |
| Transport Protocol | UDP |
| Packet Size | 512 |
| Routing Protocol | AODV |
| Channel type | Wireless |
| Queue Length | 50 packets |
| Number of Road Lanes | 2 |
| Radio Propagation Model | Two Ray Ground |
| MAC protocol | IEEE 802.11p |
| Speed | 30 m/s |
| Interface queue type | Priority Queue |
| Network Interface type | Physical Wireless |
| Mobility Models | Manhattan Mobility Model |
| Basic Trace | IP Trace | AODV Trace |
|---|---|---|
| Packet ID Payload Size and Type Source and Destination MAC Ethernet | IP Source and Destination | Packet Tagged Hop Counts Broadcast ID Destination IP with Sequence number Source IP with Sequence number |
| Parameter | Value |
|---|---|
| Train Param. Epochs | 46 |
| Train Param. Lr | |
| Train Param. Goal | 0 |
| Train Param. min_grad | |
| Gaussian Radial Basis Function | 1 |
| BoxConstraint |
| IDS | ||||
|---|---|---|---|---|
| Class | Accuracy | Time/s | Error Rate | SD |
| SVM-Normal | 99.93% | 0.12 | 0.21 | 0.429 |
| SVM-Abnormal | 99.64% | |||
| Class | Accuracy | Time/s | Error Rate | SD |
| FFNN-Normal | 99.82% | 0.99 | 0.15 | 0.102 |
| FFNN-Abnormal | 99.86% | |||
| Alarm Type | FFNN | SVM |
|---|---|---|
| True positive | 99.92% | 99.88% |
| True negative | 99.75% | 99.89% |
| False negative | 0.08% | 0.11% |
| False positive | 0.25% | 0.12% |
| IDS | ||||
|---|---|---|---|---|
| Class | Accuracy | Time/s | Error Rate | SD |
| SVM-Normal | 99.79% | 0.23 | 0.18% | 0.139 |
| SVM-Abnormal | 99.80% | |||
| Class | Accuracy | Time/s | Error Rate | SD |
| FFNN-Normal | 99.80% | 1.01 | 0.19% | 0.127 |
| FFNN-Abnormal | 99.75% | |||
| Alarm Type | FFNN | SVM |
|---|---|---|
| True positive | 99.86% | 99.70% |
| True negative | 99.78% | 99.92% |
| False negative | 0.12% | 0.30% |
| False positive | 0.22% | 0.07% |
| Class | PR | DR | CR | MSE |
|---|---|---|---|---|
| FFNN-IDS | 99.76% | 99.83% | 99.89% | 0.167% |
| SVM-IDS | 99.90% | 99.84% | 99.79% | 0.150% |
| Performance Metrics | Without Response System | With Response System |
|---|---|---|
| Generated Packets | 8226 | 8226 |
| Received Packets | 5769 | 8153 |
| Packet Delivery Ratio | 70.13% | 99.11% |
| Totally Dropped Packets | 3074 | 74 |
| Average End-to-End Delay | 202.17 ms | 22.63 ms |
| Performance Metrics | Without Response System | With Response System |
|---|---|---|
| Generated Packets | 8226 | 8226 |
| Received Packets | 3555 | 6216 |
| Packet Delivery Ratio | 43.21% | 75.56% |
| Totally Dropped Packets | 4878 | 2010 |
| Average End-to-End Delay | 72.90 ms | 44.65 ms |
© 2016 by the authors; licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC-BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Ali Alheeti, K.M.; Gruebler, A.; McDonald-Maier, K. Intelligent Intrusion Detection of Grey Hole and Rushing Attacks in Self-Driving Vehicular Networks. Computers 2016, 5, 16. https://doi.org/10.3390/computers5030016
Ali Alheeti KM, Gruebler A, McDonald-Maier K. Intelligent Intrusion Detection of Grey Hole and Rushing Attacks in Self-Driving Vehicular Networks. Computers. 2016; 5(3):16. https://doi.org/10.3390/computers5030016
Chicago/Turabian StyleAli Alheeti, Khattab M., Anna Gruebler, and Klaus McDonald-Maier. 2016. "Intelligent Intrusion Detection of Grey Hole and Rushing Attacks in Self-Driving Vehicular Networks" Computers 5, no. 3: 16. https://doi.org/10.3390/computers5030016
APA StyleAli Alheeti, K. M., Gruebler, A., & McDonald-Maier, K. (2016). Intelligent Intrusion Detection of Grey Hole and Rushing Attacks in Self-Driving Vehicular Networks. Computers, 5(3), 16. https://doi.org/10.3390/computers5030016







