Leveraging Structural Symmetry for IoT Security: A Recursive InterNetwork Architecture Perspective †
Abstract
1. Introduction
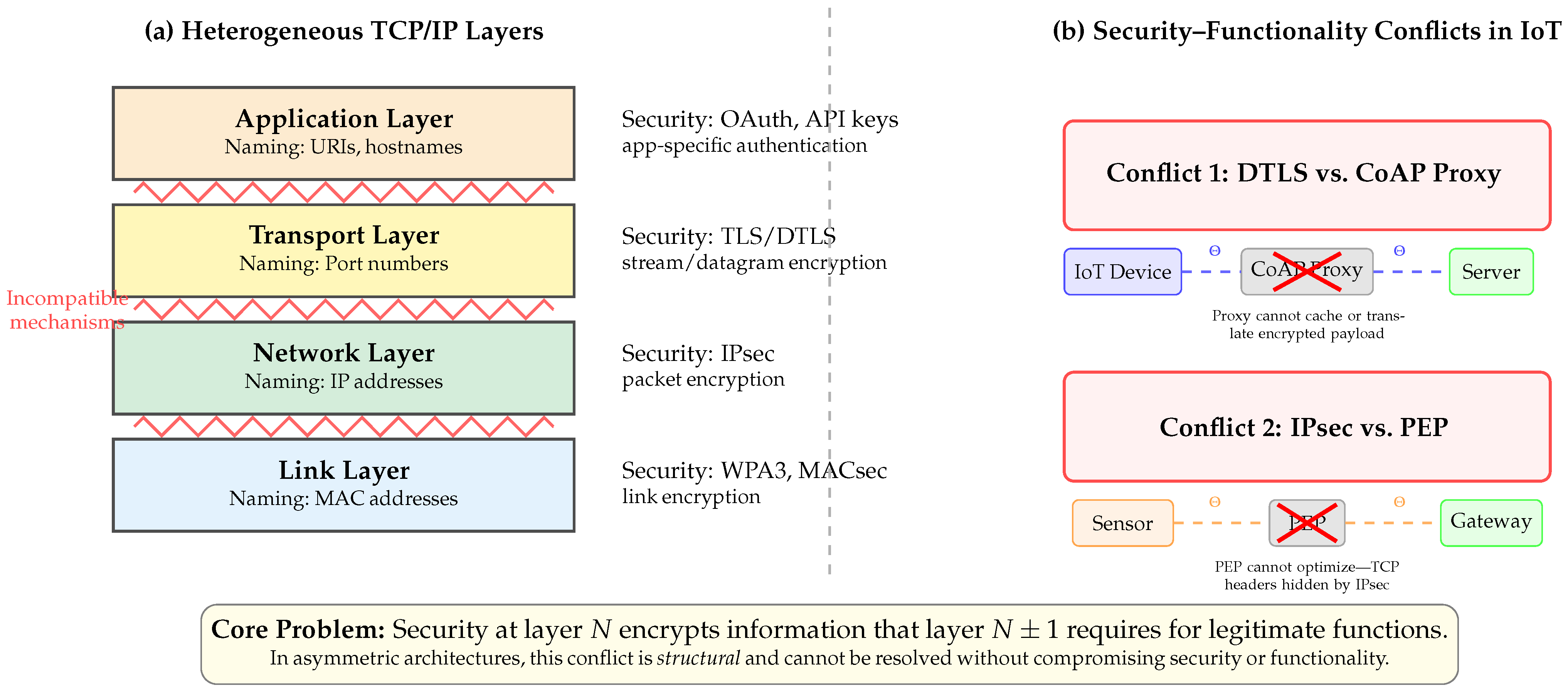
- Mechanism asymmetry: Each protocol layer implements security through different mechanisms—encryption algorithms, authentication handshakes, access control lists—that do not compose cleanly. A vulnerability patched at one layer may remain exploitable through another.
- Scope asymmetry: Security boundaries do not align with communication boundaries. Transport-layer security protects end-to-end connections, but IoT data often traverses proxies, gateways, and edge processors that legitimately need access to payload contents.
- Policy asymmetry: Different layers enforce different policies through incompatible mechanisms. Network-layer firewalls cannot enforce application-layer access controls; transport-layer encryption cannot implement network-layer traffic shaping.
- Semantic asymmetry: The meaning of “secure communication” differs across layers. Network-layer security protects packets; transport-layer security protects streams; application-layer security protects objects. These semantic mismatches create coverage gaps.
- Symmetric mechanisms ensure uniform security coverage. Because every DIF implements the same security functions—authentication, access control, encryption, integrity verification—there are no “security-free” layers. Unlike TCP/IP, where protocols like 6LoWPAN lack native security mechanisms [5], RINA guarantees that security capabilities exist at every layer by construction.
- Symmetric structure enables formal verification. Security properties verified for one DIF hold structurally for all DIFs. This dramatically reduces the verification burden compared to heterogeneous stacks where each layer requires independent security analysis.
- Symmetric interfaces eliminate cross-layer conflicts. Because all DIFs present the same API, security mechanisms at one layer cannot inadvertently break functionality at another. The PEP problem dissolves: intermediate DIFs can legitimately access and process traffic within their scope without violating end-to-end security guarantees of higher-layer DIFs.
- Diagnosis of asymmetry-induced vulnerabilities: We systematically analyze current IoT network stacks, demonstrating how their architectural asymmetry creates security gaps, redundant functionality, and irreconcilable conflicts between security and performance. Our aim is to show that IoT security failures are mainly structural rather than incidental.
- Symmetry-based architectural solution: We present RINA as a foundation for IoT security, explicating how its recursive self-similarity, mechanism invariance, and controlled policy variance address each category of asymmetry-induced vulnerability. We formalize the relationship between RINA’s symmetry properties and specific security guarantees.
- Attack-to-symmetry mapping: We provide a systematic classification of IoT attacks across network, middleware, and application layers, mapping each attack type to the RINA symmetry properties that enable its mitigation. This mapping is analyzed to assess whether RINA’s security advantages derive from architectural principles rather than ad hoc countermeasures.
- Empirical validation of recursive security: We reinterpret quantitative experimental results from our previous work [12] through the symmetry framework developed in this paper. This analysis tests the recursive security hypothesis—that security mechanisms operating within RINA’s symmetric DIF boundaries outperform equivalent mechanisms that ignore the recursive structure—and examines the conditions under which scope-aligned detection provides measurable advantages.
- Cross-domain applicability: We demonstrate RINA’s practical applicability through use cases spanning smart homes, healthcare monitoring, autonomous vehicles, and industrial edge computing. These cases illustrate how structural symmetry enables consistent security guarantees across heterogeneous IoT domains—a property unattainable in asymmetric architectures.
2. Challenges in Current IoT Network Stacks
2.1. TCP/IP-Based Stack
2.2. Information-Centric Networking (ICN)-Based Stack
3. Summary of IoT Networking Challenges
3.1. IoT Network Stack Challenges (Ch1)
3.2. Redundant Functionality Across Layers (Ch2)
- Application layer: Protocols like HTTPS or MQTT over TLS;
- Network layer: IPsec for encrypting IP packets;
- Link layer: WPA3 for Wi-Fi or Bluetooth Low Energy (BLE) secure connections.
3.3. Challenges with Global Addressability and Large Address Spaces (Ch3)
3.4. Balancing Security, Performance, and Resource Constraints (Ch4)
3.5. Repetition and Evolution of Attacks (Ch5)
3.6. Future Extensions and Emerging Technologies (Ch6)
- AI-Driven Security: The integration of artificial intelligence and machine learning into IoT networks enables predictive security measures but also opens up new attack vectors, such as adversarial machine learning attacks [40].
- Blockchain for IoT: Distributed ledger technologies offer promising solutions for device authentication and data integrity but introduce scalability and energy consumption challenges in resource-constrained IoT environments [41].
- Edge Computing Security: The shift toward edge computing in IoT networks reduces latency but decentralizes security controls, necessitating new approaches to ensure data protection at the network edge [42].
- Tactile Internet: Ultra-low-latency applications like remote surgery and autonomous vehicles require security measures that can operate at unprecedented speeds without compromising effectiveness.
- Massive IoT: The sheer scale of device numbers in future deployments will necessitate scalable security solutions capable of efficiently managing billions of endpoints.
- Cognitive IoT: As IoT devices become more intelligent and autonomous, ensuring the integrity of their decision-making processes becomes crucial, introducing the concept of “cognitive security.”
3.7. Cross-Domain Synergy and Interoperability (Ch7)
- Protocol Diversity: Each domain has evolved specialized protocols optimized for its specific use cases. For instance, healthcare IoT devices often utilize HL7 FHIR for data exchange, whereas industrial IoT systems might rely on OPC UA or MQTT. Bridging these protocol gaps without compromising functionality or security remains a significant challenge [45].
- Security Paradigms: Security requirements vary dramatically across domains. Healthcare IoT demands strict compliance with privacy regulations like HIPAA, industrial IoT prioritizes integrity and availability, smart home devices must balance user convenience with security, and automotive IoT requires real-time guarantees for safety-critical functions [46].
- Data Interoperability: Beyond protocol compatibility, ensuring semantic interoperability of data across domains is crucial. Developing a common data model that can represent diverse IoT data while preserving context and meaning poses a significant challenge [47].
- Regulatory Compliance: Different domains are governed by distinct regulatory frameworks. Harmonizing these regulations—especially in cross-border scenarios—adds another layer of complexity [48].
- Developing flexible, domain-agnostic communication frameworks that can adapt to various protocol requirements.
- Creating comprehensive security models that accommodate diverse security needs while maintaining a cohesive security posture.
- Establishing standardized data models and ontologies to ensure semantic interoperability across domains.
4. Methodology
4.1. Qualitative Analysis
4.2. Quantitative Experimental Validation
4.3. Research Steps
- Analysis of Security Challenges: Identification and categorization of IoT vulnerabilities.
- Architectural Analysis: In-depth examination of RINA’s design principles versus traditional stacks.
- Qualitative Feature Assessment: Mapping RINA capabilities to specific IoT threats.
- Use Case Development: Illustrating practical applications in diverse scenarios (e.g., smart homes, healthcare).
- Experimental Validation: Reinterpretation of the quantitative simulation and statistical results of RINA-based security mechanisms (results of a previous study [12]) through a systematic analysis.
5. Recursive InterNetwork Architecture (RINA)
5.1. Introduction
5.2. IPCP’s Mechanisms
5.2.1. Data Transfer
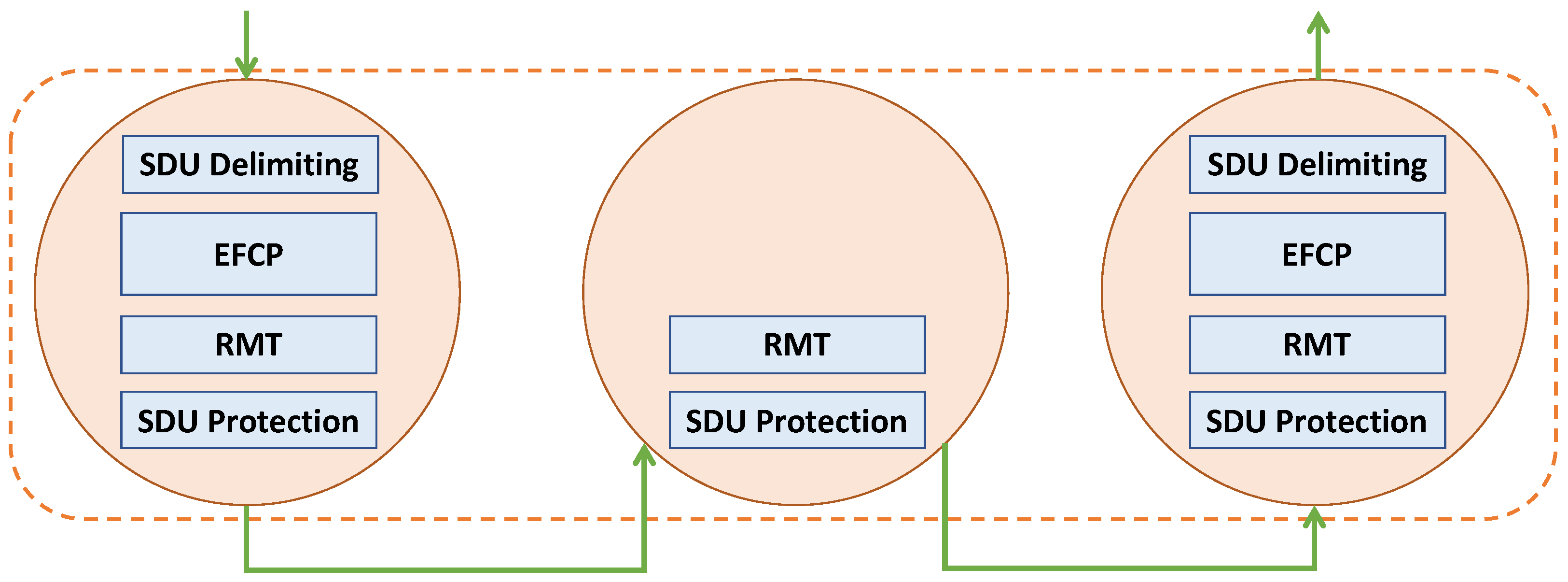
- Delimiting: This function encodes Service Data Units (SDUs) that arrive from the upper DIF within Protocol Data Units (PDUs).
- Error and Flow-Control Protocol (EFCP): This protocol ensures reliable data transmission using its two sub-protocols: Data Transfer Protocol (DTP) and Data Transfer Control Protocol (DTCP). DTP primarily concerns with the transmission and segmentation of data, while DTCP provides additional control functions, such as congestion control and error checking.
- Relaying and Multiplexing Task (RMT): This task performs routing of PDUs to output ports of the DIF or upwards. It utilizes the routing information provided by the layer management to determine the optimal path for data transmission.
- SDU Protection: This mechanism performs encryption, compression, error-code calculation, and Time-To-Live (TTL) setting.
5.2.2. Data Transfer Control
- Error Control: This component keeps track of any errors that may occur during data transmission. It uses a variety of error detection and correction techniques to maintain data integrity throughout the transmission process.
- Flow Control: This component manages the rate of data transmission ensuring that the receiver is not overwhelmed with data and can process incoming data effectively.
- Retransmission Control: This component monitors for lost or corrupted data packets. In the event of packet loss or corruption, it initiates a retransmission request, ensuring reliable data delivery.
- Congestion Control: This component monitors network congestion and implements measures to alleviate it. This can include reducing the data transmission rate.
5.2.3. Layer Management
- Resource Allocation: The Resource Allocator (RA) manages resource allocation and monitors the resources in the DIF by sharing information with other DIF IPC Processes and the performance of supporting DIFs.
- Routing: Routing performs the analysis of the information maintained by the Resource Information Base (RIB) to provide connectivity input to the creation of a forwarding function. The choice of routing algorithms in a particular DIF is a matter of policy.
- Security Coordination: Security coordination is responsible for implementing a consistent security profile for the IPC Process, coordinating all the security-related functions (authentication, access control, confidentiality, integrity) and also executing some of them (auditing, credential management).
- Namespace Management: The Name Space Manager (NSM) embedded in the DIF is responsible for mapping application names to IPC Process addresses. The NSM maintains a mapping between external application names and IPC Process addresses where there is the potential for a binding within the same processing system.
- Flow Allocation: The Flow Allocator is responsible for creating and managing an instance of IPC, i.e., a flow. The Flow Allocator-Instance (FAI) determines what policies will be utilized to provide the characteristics requested in the Allocate.
- Enrollment: The Enrollment process involves a new member joining the DIF. This process includes address assignment, information exchange about operational parameters, and updating the RIB with the latest information on routing, directory, resource allocation, etc. The new member then becomes a full member of the DIF.
5.3. Error and Flow-Control Protocol (EFCP)
5.4. Symmetry Properties of RINA
5.4.1. Structural Self-Similarity
5.4.2. Mechanism Invariance and Policy Variance
- Symmetric security mechanisms: Every DIF inherently supports authentication, access control, and SDU protection—there are no “security-free” layers as found in protocols like 6LoWPAN.
- Asymmetric security policies: A sensor-level DIF may employ lightweight encryption suitable for constrained devices, while a backbone DIF implements stronger cryptographic policies, without architectural modification.
5.4.3. Controlled Symmetry-Breaking for Security
- Address space asymmetry: Addresses are meaningful only within their DIF scope, creating an information asymmetry between internal members and external entities. An attacker outside a DIF cannot observe or predict internal addresses—a form of protective asymmetry.
- Authentication asymmetry: The enrollment process creates a binary asymmetry between authenticated (DIF member) and unauthenticated (non-member) entities. This asymmetry is fundamental to RINA’s access control model.
- Trust boundary asymmetry: Each DIF constitutes a trust domain with its own security policies. Cross-DIF communication requires explicit policy negotiation, preventing the implicit trust assumptions that plague flat network architectures.
5.4.4. Operational Implications of Symmetry
Op1: Verification Reuse Across Layers
Op2: Uniform Security Control Placement
Op3: Scope-Aligned Observability
Op4: Composable Security Guarantees

6. Comprehensive Security Features of RINA
6.1. Secure Distributed IPC Facilities (SD)
6.2. Hidden Addresses (HAs)
6.3. Decoupled Synchronization and Port Allocation (PA)
6.4. Port-Independent Communication (PI)
6.5. Soft-State Connection Management (SS)
- Reduction in Connection Misuse Risks: The absence of explicit control messages for connection establishment and termination minimizes opportunities for malicious actors to exploit these messages to illegitimately establish, hijack, or disrupt connections. By eliminating such control signals, RINA reduces the avenues available for attack.
- Mitigation of Denial-of-Service Attacks: RINA’s soft-state management mitigates DoS attacks like SYN floods, which exploit control messages in traditional protocols like TCP. By removing reliance on these control messages, RINA decreases the likelihood of attackers successfully overwhelming the network with illegitimate connection requests.
- Efficient Resource Management: Automatic deletion of inactive connection states after 2 × MPL ensures that resources are not unnecessarily consumed by stale connections. This efficiency is crucial for IoT devices with limited computational resources, reducing the risk of resource exhaustion attacks where an attacker attempts to deplete system resources by establishing numerous connections.
- Enhanced Privacy: By not maintaining long-lived connection states, RINA makes it more challenging for adversaries to track and monitor user activities. Traditional networks with persistent connection states can inadvertently facilitate user profiling and surveillance. RINA’s transient connection states enhance privacy protections for users and devices within the network.
6.6. Connection Management Independent Authentication (IA)
6.7. Variable Address Space (VA)
6.8. RINA’s DAFs (DF)
6.9. Common Distributed Application Protocol (CDAP)
6.10. Multi-Layer Security (ML)
6.11. Communication Through a Common DIF (CC)
6.12. Authentication (AU)
6.13. Integrated Firewall Functionality (BF)
6.14. Programmable Distributed IPC Facilities (PD)
6.15. Access Control (AC)
6.16. Insiders Resistance (IR)
6.17. QoS (QS)
6.18. Mobility (MO)
6.19. Resiliency (RS)
6.20. Performance Improvements (PR)
6.21. Complexity Reduction (CR)
6.22. Arbitrary Arrangement (AA)
- Performance Enhancing Proxies (PEPs): In a satellite communication scenario, a DIF could be inserted between the ground station and the satellite to optimize protocol behavior for high-latency links, improving throughput without compromising end-to-end security.
- Multipath Routing: In a data center environment, multiple DIFs could be arranged to provide redundant paths between servers, enhancing both performance and reliability. Each path could implement different security policies based on the sensitivity of the data being transmitted.
- In-network Resource Sharing: In an IoT deployment, a DIF could be dedicated to managing shared resources among devices, such as a common data cache or processing unit, with access controlled through RINA’s built-in security mechanisms.
- A lower-level DIF could be configured with stringent security policies, handling encryption and authentication for all traffic passing through it. This DIF would serve as a secure foundation for higher-level DIFs, effectively isolating critical security functions from general network operations.
- An intermediate DIF could be designed to manage fine-grained access control policies. This DIF would leverage RINA’s inherent authentication and authorization mechanisms to ensure that sensitive information is only accessible to authorized IPCPs, whether they represent personnel, devices, or applications.
- A higher-level DIF could be established for comprehensive network monitoring and security analytics. This DIF would collect and analyze data from lower DIFs, utilizing RINA’s recursive nature to detect anomalies and potential security breaches across the entire stack. It could implement advanced threat detection algorithms without interfering with the operations of other DIFs.
- Multiple DIFs at various levels could be arranged to implement a defense-in-depth strategy. For example, one DIF might focus on perimeter security, another on internal traffic segregation, and yet another on application-level security, all working in concert to provide layered protection.
7. Leveraging RINA for Enhanced IoT Security
7.1. Threat Model
- Assets
- Confidentiality, integrity, and availability of user data carried in Service Data Units (SDUs) across all Distributed IPC Facilities (DIFs).
- Control-plane state of Flow Allocators, Enrollment processes, and policy modules that govern IPC Processes (IPCPs).
- Continuity of critical services (e.g., health monitoring, industrial control) that depend on timely delivery.
- Adversary capabilities
- External network attacker able to eavesdrop, inject, replay, or drop packets on links that cross administrative or DIF boundaries.
- Compromised IoT node with legitimate credentials for a single DIF, attempting privilege escalation or lateral movement.
- Malicious cloud/edge service that hosts application logic but not lower-layer IPCPs.
- Assumptions
- Physical tampering, side-channel attacks, and radio-jamming are out of scope. These attacks operate below the network architecture layer—physical tampering and side-channel attacks require hardware-level countermeasures (e.g., tamper-evident enclosures, constant-time cryptographic implementations), while radio-jamming demands physical-layer defenses (e.g., spread-spectrum, frequency hopping) that are orthogonal to protocol design.
- DIF enrollment relies on pre-provisioned public-key credentials (or an equivalent trust-anchor) and cannot be bypassed.
- Cryptographic primitives are perfect; attacks target protocol logic, policy misconfiguration, or resource exhaustion.
- Attacker goals
- Security objectives
- O1
- Preventing unauthorized DIF enrollment and address spoofing.
- O2
- Detecting and containing insider misbehaviour within a single DIF.
- O3
- Maintaining availability under volumetric or state-exhaustion attacks.
- O4
- Preserving end-to-end data confidentiality and integrity across heterogeneous DIF paths.
7.2. Attack Classification and Mitigation
- Network Layer Attacks: These include threats that target the fundamental communication infrastructure of IoT systems, such as Denial of Service (DoS), routing attacks, and man-in-the-middle interventions.
- Middleware Layer Attacks: This category encompasses threats that exploit vulnerabilities in the software layer bridging IoT devices and applications, including data injection attacks and unauthorized access attempts.
- Application Layer Attacks: These attacks target the user-facing components of IoT systems, including phishing, malware infections, and data theft.
7.2.1. Network Layer Attacks
7.2.2. Middleware Layer Attacks
7.2.3. Application Layer Attacks
7.3. Adhering to Foundational Security Principles
7.4. Addressing IoT Architectural Challenges
7.4.1. Network Stack Challenge
7.4.2. Repeated Functionality
7.4.3. Address Space Challenge
7.4.4. Security and Performance Conflict
7.4.5. Repeating Attacks Challenge
7.4.6. Future Trend Challenge
7.4.7. RINA’s Resilience to Adversarial ML Attacks
7.4.8. Domain Synergy Challenge
7.5. Attack Case Study: Mirai Botnet Attack
7.5.1. Attack Vector
- Automated Scanning and Infection: Mirai continuously scanned IP address spaces to detect open Telnet ports (TCP/23 and TCP/2323). Upon finding an accessible device, it attempted to log in using a list of 61 common default username and password combinations hard-coded into the malware.
- Exploitation of Default Credentials: Many IoT devices shipped with factory-default login credentials that users rarely changed. This oversight provided an easy entry point for Mirai to gain unauthorized access.
- Memory-Resident Payload: The malware resided in the device’s volatile memory, making it resilient to detection but also meaning that a simple reboot could remove it. However, due to persistent vulnerabilities, devices often became reinfected shortly after rebooting.
- Command and Control (C&C) Infrastructure: Infected devices reported back to centralized C&C servers, awaiting instructions to participate in coordinated DDoS attacks.
7.5.2. How RINA Could Have Prevented the Attack
- Authentication and Access Control: RINA mandates mutual authentication before any communication is established between devices. Each interaction requires entities to verify each other’s identities using robust authentication protocols. This approach eliminates the reliance on weak or default credentials, as unauthorized devices cannot participate in the network without proper authentication.
- Fine-Grained Network Isolation through DIFs: RINA introduces Distributed IPC Facilities (DIFs), which are layers providing Inter-Process Communication (IPC) services with specific policies and mechanisms. By organizing devices into separate DIFs based on trust levels, functionality, or security requirements, RINA prevents unauthorized lateral movement. Even if a device were compromised, the malware’s ability to spread would be confined within that DIF, limiting the overall impact.
- Dynamic Addressing and Naming: Unlike the static and globally routable IP addresses exploited by Mirai, RINA uses dynamic addressing within each DIF. Addresses are not exposed globally and are only meaningful within their specific context. This obscurity makes it significantly more challenging for attackers to discover and target devices en masse, as there is no uniform addressing scheme to exploit.
- Policy-Based Flow Management and Traffic Monitoring: RINA’s architecture allows for customizable flow management policies at each DIF. Network administrators can implement policies to monitor for abnormal traffic patterns, such as the rapid scanning and high-volume traffic characteristic of botnet activity. Suspicious flows can be throttled, redirected, or terminated, thereby mitigating the propagation of malware and participation in DDoS attacks.
- Secure Enrollment and Bootstrapping: The enrollment process in RINA ensures that devices are authenticated and authorized before joining a DIF. This process can include checks for up-to-date firmware, compliance with security policies, and validation of cryptographic credentials. Such rigorous vetting prevents compromised or non-compliant devices from integrating into the network.
- Simplified and Consistent Security Policies: RINA’s recursive nature allows for consistent application of security policies across all layers of the network. This uniformity reduces complexity and the likelihood of configuration errors that could introduce vulnerabilities. Administrators can define security policies once and have them propagate throughout the network hierarchy.
- Resilience to Single Points of Failure: RINA’s architecture avoids reliance on centralized servers or services that could become focal points for attacks. Distributed management and control can reduce the risk of widespread disruption resulting from the compromise of a single component.
7.6. Comparative Analysis of RINA and Other IoT Security Solutions
8. Employing RINA in IoT—A Qualitative Use Case Study
8.1. Home
8.2. Health
8.3. Secure Multicast
8.4. Cognitive Security in Autonomous Vehicle Networks
- Local Cognition DIF: Manages onboard sensor data and immediate decision-making.
- Vehicle-to-Vehicle (V2V) DIF: Handles secure communication and decision-making between nearby vehicles.
- Vehicle-to-Infrastructure (V2I) DIF: Manages interactions with city infrastructure and broader traffic management systems.
8.5. Enabling Secure Edge Computing in Smart Manufacturing
- 1.
- Secure Edge Nodes: RINA’s authentication mechanism (Section 6.12) ensures that only authorized edge devices can join the network. Each edge node would be part of a secure DIF, with its own authentication and access control policies.
- 2.
- Data Isolation: RINA’s multi-layer approach (Section 6.10) allows for the creation of separate DIFs for different types of data or processes. For example:
- A DIF for real-time control data;
- A DIF for less time-sensitive monitoring data;
- A DIF for edge-to-cloud communication.
This segregation enhances security by limiting the potential impact of a breach. - 3.
- Secure Data Processing: RINA’s secure DIFs (Section 6.1) provide a protected environment for edge computation. Machine learning models for predictive maintenance can operate within a dedicated DIF, ensuring the integrity of both the model and the data it processes.
- 4.
- Flexible Security Policies: RINA’s programmable DIFs (Section 6.14) allow for the implementation of context-aware security policies. For instance, stricter policies could be applied to DIFs handling sensitive production data.
- 5.
- Efficient Resource Utilization: RINA’s Quality of Service mechanisms (Section 6.17) can be used to optimally allocate edge computing resources, ensuring critical processes receive priority.
- 6.
- Scalability: As the number of edge devices grows, RINA’s recursive structure allows for seamless scaling. New edge nodes can be easily integrated into existing DIFs or new DIFs can be created as needed.
- 7.
- Secure Edge-to-Cloud Communication: For data that need to be sent to the cloud, RINA’s layered security approach ensures end-to-end protection. The edge-to-cloud DIF can implement additional security measures such as encryption and access controls.
- Sensor-level DIF: Manages communication between individual sensors/actuators and their local edge nodes. This DIF would be optimized for low-latency, secure data collection.
- Edge Compute DIF: Coordinates computation tasks across edge nodes. This DIF would implement load balancing and resource allocation policies to ensure efficient use of edge resources.
- Process Control DIF: Handles real-time control data for manufacturing processes. This DIF would have strict QoS policies to ensure timely delivery of critical control signals.
- Predictive Maintenance DIF: Manages the ML models and data for predictive maintenance. This DIF would implement specific security policies to protect the integrity of the ML models and the data they process.
- Edge-to-Cloud DIF: Handles communication between the edge network and cloud services. This DIF would implement additional security measures for data leaving the local network.
9. Empirical Validation of the Symmetry Scoping Principle
9.1. The Recursive Security Hypothesis
9.2. Experimental Framework Overview
9.2.1. Symmetry-Aligned Detection Architecture
9.2.2. Attack Scenarios
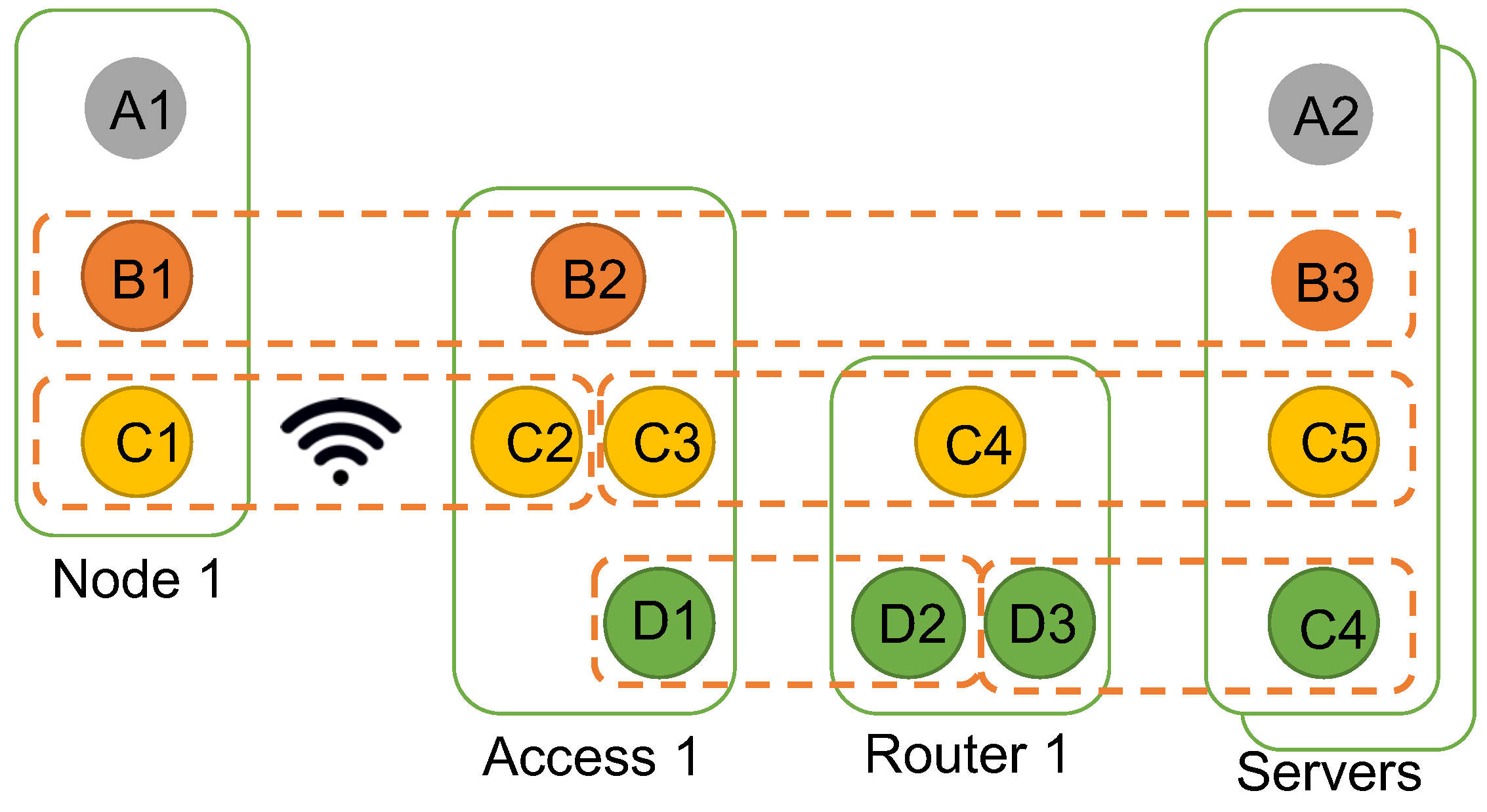
- S1—Edge DoS: A spatially confined attack where one sensor floods its Edge-DIF uplink. The malicious signal is tightly scoped to a single DIF.
- S2—Tunnel Hijack: A cross-layer attack where an on-path relay manipulates traffic across multiple DIFs. The malicious signal spans the entire recursive hierarchy.
- S3—Cross-Layer Flood: A distributed attack where multiple sensors each generate small traffic increases that aggregate into significant volume at higher layers.
9.3. Interpreting Results Through the Symmetry Lens
9.3.1. Mechanism 1: Context Reduction Through Scope Alignment
- The local detector observes only traffic patterns within its DIF scope;
- Legitimate traffic from other DIFs cannot dilute or mask the attack signature;
- The decision boundary need only distinguish normal from abnormal patterns within that scope.
9.3.2. Mechanism 2: Symmetry Enables Verification Reuse
9.3.3. Mechanism 3: Controlled Symmetry-Breaking Reveals Limitations
9.4. Quantifying Symmetry’s Security Contribution
9.5. Validation of the Symmetry Scoping Principle
- Symmetry Test: Identical detection mechanisms (same algorithms, same architectures) operated successfully at every DIF layer, confirming that RINA’s structural self-similarity enables mechanism reuse across the recursive hierarchy.
- Scoping Test: Detection performance improved when each mechanism’s observable scope matched exactly one DIF’s communication scope, confirming that scope alignment provides measurable security benefits.
- Composition Test: The combination of multiple scope-aligned detectors provided defense-in-depth without the integration complexity that would arise from heterogeneous detection approaches, confirming that symmetric mechanisms compose cleanly.
10. Discussion
10.1. Strategies for RINA Deployment in IoT Ecosystems
10.1.1. Leveraging RINA’s Compatibility Features
10.1.2. Integration Strategies for Non-RINA Capable Devices
10.1.3. Incremental RINA Adoption
10.1.4. RINA on Resource-Constrained Devices
10.1.5. Comprehensive Deployment Frameworks
10.1.6. Bridging Legacy Applications
10.1.7. Empirical Evidence of RINA’s Runtime Efficiency on Resource-Constrained IoT Hardware
10.2. Applicability to Critical Infrastructure Domains
10.3. Migration Roadmap
10.4. Further Research Directions
10.4.1. Empirical Validation on Resource-Constrained Hardware
- RQ1: What is the memory footprint and CPU overhead of IPCP enrollment and authentication on Class 1 constrained devices (e.g., ∼10 KB RAM)?
- RQ2: How do RINA’s SDU protection mechanisms compare to DTLS in energy consumption per secured transaction?
10.4.2. Cross-Layer Threat Detection in Recursive Architectures
- RQ3: Can lightweight information sharing between adjacent DIF detectors improve cross-layer threat detection without sacrificing the locality benefits demonstrated in Section 9?
- RQ4: What fusion mechanisms optimally balance detection latency against accuracy for RINA’s recursive structure?
10.4.3. Incremental Deployment and Legacy Interoperability
- RQ5: What security guarantees can be preserved when RINA networks interface with legacy IP-based IoT segments via shim DIFs?
- RQ6: What is the minimum “RINA-enabled” fraction of an IoT deployment needed to achieve measurable security improvements?
11. Conclusions
Author Contributions
Funding
Data Availability Statement
Acknowledgments
Conflicts of Interest
Abbreviations
| IoT | Internet of Things |
| RINA | Recursive InterNetwork Architecture |
| DIF | Distributed IPC Facility |
| DAF | Distributed Application Facility |
| IPC | Inter-Process Communication |
| IPCP | IPC Process |
| CDAP | Common Distributed Application Protocol |
| SDU | Service Data Unit |
| PDU | Protocol Data Unit |
| QoS | Quality of Service |
| DoS | Denial of Service |
| MITM | Man-in-the-Middle |
| PEP | Performance Enhancing Proxy |
| DTLS | Datagram Transport Layer Security |
| CoAP | Constrained Application Protocol |
References
- Shelupanov, A.; Evsyutin, O.; Konev, A.; Kostyuchenko, E.; Kruchinin, D.; Nikiforov, D. Information Security Methods—Modern Research Directions. Symmetry 2019, 11, 150. [Google Scholar] [CrossRef]
- Rescorla, E.; Modadugu, N. Datagram Transport Layer Security Version 1.2. RFC 6347. 2012. Available online: https://www.rfc-editor.org/info/rfc6347 (accessed on 2 January 2026).
- Grammatikis, P.I.R.; Sarigiannidis, P.G.; Moscholios, I.D. Securing the Internet of Things: Challenges, threats and solutions. Internet Things 2019, 5, 41–70. [Google Scholar] [CrossRef]
- Teymoori, P.; Welzl, M.; Stein, G.; Grasa, E.; Riggio, R.; Rausch, K.; Siracuss, D. Congestion control in the Recursive Internetwork Architecture (RINA). In Proceedings of the IEEE International Conference on Communications (ICC), Next Generation Networking and Internet Symposium, Kuala Lumpur, Malaysia, 23–27 May 2016. [Google Scholar]
- Granjal, J.; Monteiro, E.; Silva, J.S. Security for the Internet of Things: A Survey of Existing Protocols and Open Research Issues. IEEE Commun. Surv. Tutor. 2015, 17, 1294–1312. [Google Scholar] [CrossRef]
- IoT Analytics. State of the IoT 2020: 12 Billion IoT Connections, Surpassing Non-IoT for the First Time. 2020. Available online: https://iot-analytics.com/state-of-the-iot-2020-12-billion-iot-connections-surpassing-non-iot-for-the-first-time/ (accessed on 2 January 2026).
- Grand View Research, Inc. Internet of Things (IoT) Market to Reach $2.65 Trillion by 2030. 2024. Available online: https://www.grandviewresearch.com/press-release/global-iot-market (accessed on 2 January 2026).
- Andrea, I.; Chrysostomou, C.; Hadjichristofi, G. Internet of things: Security vulnerabilities and challenges. In Proceedings of the 2015 IEEE Symposium on Computers and Communication (ISCC), Larnaca, Cyprus, 6–9 July 2015; IEEE: New York, NY, USA, 2015; pp. 180–187. [Google Scholar]
- Yang, Y.; Wu, L.; Yin, G.; Li, L.; Zhao, H. A Survey on Security and Privacy Issues in Internet-of-Things. IEEE Internet Things J. 2017, 4, 1250–1258. [Google Scholar] [CrossRef]
- Fei, W.; Ohno, H.; Sampalli, S. A Systematic Review of IoT Security: Research Potential, Challenges, and Future Directions. ACM Comput. Surv. 2023, 56, 111. [Google Scholar] [CrossRef]
- Day, J. Patterns in Network Architecture: A Return to Fundamentals; Prentice Hall: Boston, MA, USA, 2007. [Google Scholar]
- Ramezanifarkhani, T.; Teymoori, P. Learning-in-the-Middle: Explicit-Recursion Anomaly Detection for Critical Infrastructures. In ESORICS 2025 International Workshops: AutonomousCyber 2025, CPS4CIP 2025, DisA 2025, HS3 2025, MIST 2025, Revised Selected Papers, Part III; Lecture Notes in Computer Science; Springer Nature: Toulouse, France, 2025. [Google Scholar]
- Ramezanifarkhani, T.; Teymoori, P. Securing the Internet of Things with Recursive InterNetwork Architecture (RINA). In Proceedings of the 2018 International Conference on Computing, Networking and Communications (ICNC), Maui, HI, USA, 5–8 March 2018; IEEE: New York, NY, USA, 2018; pp. 188–194. [Google Scholar]
- IEEE Std 802.15.4-2011 (Revision of IEEE Std 802.15.4-2006); IEEE Standard for Local and Metropolitan Area Networks–Part 15.4: Low-Rate Wireless Personal Area Networks (LR-WPANs). IEEE-SA: Piscataway, NJ, USA, 2011; pp. 1–314. [CrossRef]
- Montenegro, G.; Schumacher, C.; Kushalnagar, N. IPv6 over Low-Power Wireless Personal Area Networks (6LoWPANs): Overview, Assumptions, Problem Statement, and Goals. RFC 4919. 2007. Available online: https://www.rfc-editor.org/info/rfc4919 (accessed on 2 January 2026).
- Thubert, P.; Hui, J. Compression Format for IPv6 Datagrams over IEEE 802.15.4-Based Networks. RFC 6282. 2011. Available online: https://www.rfc-editor.org/info/rfc6282 (accessed on 2 January 2026).
- Rescorla, E. The Transport Layer Security (TLS) Protocol Version 1.3. RFC 8446. 2018. Available online: https://www.rfc-editor.org/info/rfc8446 (accessed on 2 January 2026).
- Rescorla, E.; Tschofenig, H.; Modadugu, N. The Datagram Transport Layer Security (DTLS) Protocol Version 1.3. RFC 9147. 2022. Available online: https://www.rfc-editor.org/info/rfc9147 (accessed on 2 January 2026).
- Shelby, Z.; Hartke, K.; Bormann, C. The Constrained Application Protocol (CoAP). RFC 7252. 2014. Available online: https://www.rfc-editor.org/info/rfc7252 (accessed on 2 January 2026).
- Amadeo, M.; Campolo, C.; Quevedo, J.; Corujo, D.; Molinaro, A.; Iera, A.; Aguiar, R.L.; Vasilakos, A.V. Information-centric networking for the internet of things: Challenges and opportunities. IEEE Netw. 2016, 30, 92–100. [Google Scholar] [CrossRef]
- Ravindran, R.; Zhang, Y.; Grieco, L.A.; Lindgren, A.; Burke, J.; Ahlgren, B.; Azgin, A. Design Considerations for Applying ICN to IoT. Internet-Draft draft-irtf-icnrg-icniot-03, Internet Engineering Task Force. Work in Progress. 2019. Available online: https://datatracker.ietf.org/doc/html/draft-irtf-icnrg-icniot-03 (accessed on 2 January 2026).
- Fang, C.; Yao, H.; Wang, Z.; Wu, W.; Jin, X.; Yu, F.R. A survey of mobile information-centric networking: Research issues and challenges. IEEE Commun. Surv. Tutor. 2018, 20, 2353–2371. [Google Scholar] [CrossRef]
- Day, J.; Matta, I.; Mattar, K. Networking is IPC: A guiding principle to a better Internet. In Proceedings of the ACM CoNEXT, Madrid, Spain, 9–12 December 2008; p. 67. [Google Scholar]
- Suarez, J.; Quevedo, J.; Vidal, I.; Corujo, D.; Garcia-Reinoso, J.; Aguiar, R.L. A secure IoT management architecture based on Information-Centric Networking. J. Netw. Comput. Appl. 2016, 63, 190–204. [Google Scholar] [CrossRef]
- Caini, C.; Firrincieli, R.; Lacamera, D. PEPsal: A Performance Enhancing Proxy for TCP satellite connections. IEEE Aerosp. Electron. Syst. Mag. 2007, 22, 7–16. [Google Scholar] [CrossRef]
- Thai, T.T.; Pacheco, D.M.L.; Lochin, E.; Arnal, F. SatERN: A PEP-less solution for satellite communications. In Proceedings of the IEEE International Conference on Communications (ICC), Kyoto, Japan, 5–9 June 2011. [Google Scholar]
- Bimschas, D.; Hellbrück, H.; Mietz, R.; Pfisterer, D.; Römer, K.; Teubler, T. Middleware for smart gateways connecting sensornets to the internet. In Proceedings of the 5th International Workshop on Middleware Tools, Services and Run-Time Support for Sensor Networks, Bangalore, India, 30 November 2010; ACM: New York, NY, USA, 2010; pp. 8–14. [Google Scholar]
- Kang, B.; Kim, D.; Choo, H. Internet of Everything: A large-scale autonomic IoT gateway. IEEE Trans. Multi-Scale Comput. Syst. 2017, 3, 206–214. [Google Scholar] [CrossRef]
- Hassija, V.; Chamola, V.; Saxena, V.; Jain, D.; Goyal, P.; Sikdar, B. A survey on IoT security: Application areas, security threats, and solution architectures. IEEE Access 2019, 7, 82721–82743. [Google Scholar] [CrossRef]
- Alexander, R.; Brandt, A.; Vasseur, J.; Hui, J.; Pister, K.; Thubert, P.; Levis, P.; Struik, R.; Kelsey, R.; Winter, T. RPL: IPv6 Routing Protocol for Low-Power and Lossy Networks. RFC 6550. 2012. Available online: https://www.rfc-editor.org/info/rfc6550 (accessed on 2 January 2026).
- Das, L.; Gupta, M.; Anand, P.; Ahuja, L.; Bibhu, V.; Pateria, J. Recent Aspects of IPv6 on Security Challenges in IoT. In Proceedings of the 2023 10th International Conference on Computing for Sustainable Global Development (INDIACom), New Delhi, India, 15–17 March 2023; IEEE: New York, NY, USA, 2023; pp. 890–896. [Google Scholar]
- Čolaković, A.; Hadžialić, M. Internet of Things (IoT): A review of enabling technologies, challenges, and open research issues. Comput. Netw. 2018, 144, 17–39. [Google Scholar] [CrossRef]
- A Al-Ofeishat, H.; Alshorman, R. Build a Secure Network using Segmentation and Micro-segmentation Techniques. Int. J. Comput. Digit. Syst. 2023, 14, 1499–1508. [Google Scholar] [CrossRef]
- Liu, L.; Stroulia, E.; Nikolaidis, I.; Miguel-Cruz, A.; Rincon, A.R. Smart homes and home health monitoring technologies for older adults: A systematic review. Int. J. Med. Inform. 2016, 91, 44–59. [Google Scholar] [CrossRef] [PubMed]
- Sharma, R.; Sharma, N. Attacks on resource-constrained IoT devices and security solutions. Int. J. Softw. Sci. Comput. Intell. 2022, 14, 1–21. [Google Scholar] [CrossRef]
- Noor, M.b.M.; Hassan, W.H. Current research on Internet of Things (IoT) security: A survey. Comput. Netw. 2019, 148, 283–294. [Google Scholar] [CrossRef]
- Huang, J.; Duan, Q.; Zhao, Y.; Zheng, Z.; Wang, W. Multicast routing for multimedia communications in the Internet of Things. IEEE Internet Things J. 2016, 4, 215–224. [Google Scholar] [CrossRef]
- Sicari, S.; Rizzardi, A.; Grieco, L.A.; Coen-Porisini, A. Security, privacy and trust in Internet of Things: The road ahead. Comput. Netw. 2015, 76, 146–164. [Google Scholar] [CrossRef]
- Alaba, F.A.; Othman, M.; Hashem, I.A.T.; Alotaibi, F. Internet of Things security: A survey. J. Netw. Comput. Appl. 2017, 88, 10–28. [Google Scholar] [CrossRef]
- Kalakoti, R.; Bahsi, H.; Nõmm, S. Improving IoT Security with Explainable AI: Quantitative Evaluation of Explainability for IoT Botnet Detection. IEEE Internet Things J. 2024, 11, 18237–18254. [Google Scholar] [CrossRef]
- Huan, N.T.Y.; Zukarnain, Z.A. A Survey on Addressing IoT Security Issues by Embedding Blockchain Technology Solutions: Review, Attacks, Current Trends, and Applications. IEEE Access 2024, 12, 69765–69782. [Google Scholar] [CrossRef]
- Karakaya, A.; Ulu, A. A survey on post-quantum based approaches for edge computing security. Wiley Interdiscip. Rev. Comput. Stat. 2024, 16, e1644. [Google Scholar] [CrossRef]
- Williams, P.; Dutta, I.K.; Daoud, H.; Bayoumi, M. A survey on security in internet of things with a focus on the impact of emerging technologies. Internet Things 2022, 19, 100564. [Google Scholar] [CrossRef]
- Marinakis, V.; Doukas, H. An advanced IoT-based system for intelligent energy management in buildings. Sensors 2018, 18, 610. [Google Scholar] [CrossRef]
- Al-Fuqaha, A.; Guizani, M.; Mohammadi, M.; Aledhari, M.; Ayyash, M. Internet of things: A survey on enabling technologies, protocols, and applications. IEEE Commun. Surv. Tutor. 2015, 17, 2347–2376. [Google Scholar] [CrossRef]
- Lin, J.; Yu, W.; Zhang, N.; Yang, X.; Zhang, H.; Zhao, W. A Survey on Internet of Things: Architecture, Enabling Technologies, Security and Privacy, and Applications. IEEE Internet Things J. 2017, 4, 1125–1142. [Google Scholar] [CrossRef]
- Ganzha, M.; Paprzycki, M.; Pawłowski, W.; Szmeja, P.; Wasielewska, K. Semantic interoperability in the Internet of Things: An overview from the INTER-IoT perspective. J. Netw. Comput. Appl. 2017, 81, 111–124. [Google Scholar] [CrossRef]
- Bringhenti, D.; Valenza, F.; Basile, C. Toward cybersecurity personalization in smart homes. IEEE Secur. Priv. 2021, 20, 45–53. [Google Scholar] [CrossRef]
- Käbisch, S.; Kamiya, T.; McCool, M.; Charpenay, V.; Kovatsch, M. Web of Things (WoT) Architecture. W3c Recommendation, W3C. 2020. Available online: https://www.w3.org/TR/2020/REC-wot-architecture-20200409/ (accessed on 2 January 2026).
- Fuller, A.; Fan, Z.; Day, C.; Barlow, C. Digital twin: Enabling technologies, challenges and open research. IEEE Access 2020, 8, 108952–108971. [Google Scholar] [CrossRef]
- Creswell, J.W.; Poth, C.N. Qualitative Inquiry and Research Design: Choosing Among Five Approaches; Sage Publications: Thousand Oaks, CA, USA, 2016. [Google Scholar]
- Patton, M.Q. Qualitative Research & Evaluation Methods: Integrating Theory and Practice; Sage Publications: Thousand Oaks, CA, USA, 2014. [Google Scholar]
- Robert, K.Y. Case Study Research and Applications: Design and Methods; Sage Publications: Thousand Oaks, CA, USA, 2017. [Google Scholar]
- Boddapati, G.; Day, J.; Matta, I.; Chitkushev, L. Assessing the security of a clean-slate internet architecture. In Proceedings of the 20th IEEE International Conference on Network Protocols (ICNP), Austin, TX, USA, 30 October–2 November 2012; IEEE: New York, NY, USA, 2012. [Google Scholar]
- Grasa, E.; Rysavy, O.; Lichtner, O.; Asgari, H.; Day, J.; Chitkushev, L. From protecting protocols to layers: Designing, implementing and experimenting with security policies in RINA. In Proceedings of the 2016 IEEE International Conference on Communications (ICC), Kuala Lumpur, Malaysia, 22–27 May 2016; pp. 1–7. [Google Scholar] [CrossRef]
- Leon, S.; Perello, J.; Grasa, E.; Lopez, D.R.; Aranda, P.A.; Careglio, D. Benefits of Programmable Topological Routing Policies in RINA-Enabled Large-Scale Datacenters. In Proceedings of the Global Communications Conference, Washington, DC, USA, 4–8 December 2016; IEEE: New York, NY, USA, 2016. [Google Scholar]
- Small, J. Patterns in Network Security: An Analysis of Architectural Complexity in Securing Recursive Inter-Network Architecture Networks. Master’s Thesis, Boston University Metropolitan College, Boston, MA, USA, 2012. [Google Scholar]
- Pouzin Society. 2019. Available online: https://pouzinsociety.org/rina-workshop-2019-presentations/ (accessed on 2 January 2026).
- Next Generation Protocols (NGP) ETSI Industry Specification Group (ISG). GR NGP 009—V1.1.1—Next Generation Protocols (NGP); An Example of a Non-IP Network Protocol Architecture Based on RINA Design Principles; Technical Report; ETSI: Valbonne, France, 2019. [Google Scholar]
- Sarabia-Jácome, D.; Grasa, E.; Catalán, M. RINAsense: An open-source, low-power IoT sensor node for Recursive InterNetwork Architecture (RINA) Experimentation. HardwareX 2025, 24, e00719. [Google Scholar] [CrossRef]
- Watson, R.W. Timer-based mechanisms in reliable transport protocol connection management. Comput. Netw. 1981, 5, 47–56. [Google Scholar] [CrossRef]
- Kepçeoğlu, B.; Murzaeva, A.; Demirci, S. Performing energy consuming attacks on IoT devices. In Proceedings of the 2019 27th Telecommunications Forum (TELFOR), Belgrade, Serbia, 26–27 November 2019; pp. 1–4. [Google Scholar] [CrossRef]
- Aldabbas, H.; Amin, R. A novel mechanism to handle address spoofing attacks in SDN based IoT. Clust. Comput. 2021, 24, 3011–3026. [Google Scholar] [CrossRef]
- Kunchok, T.; Kirubanand, V. A lightweight hybrid encryption technique to secure IoT data transmission. Int. J. Eng. Technol. 2018, 7, 236–240. [Google Scholar] [CrossRef]
- Liu, J.; Xiao, Y.; Chen, H.; Ozdemir, S.; Dodle, S.; Singh, V. A survey of payment card industry data security standard. IEEE Commun. Surv. Tutor. 2010, 12, 287–303. [Google Scholar]
- Molina Zarca, A.; Bagaa, M.; Bernal Bernabe, J.; Taleb, T.; Skarmeta, A.F. Semantic-Aware Security Orchestration in SDN/NFV-Enabled IoT Systems. Sensors 2020, 20, 3622. [Google Scholar] [CrossRef]
- Mathas, C.M.; Vassilakis, C.; Kolokotronis, N.; Zarakovitis, C.C.; Kourtis, M.A. On the Design of IoT Security: Analysis of Software Vulnerabilities for Smart Grids. Energies 2021, 14, 2818. [Google Scholar] [CrossRef]
- Gaixas, S.L.; Perelló, J.; Careglio, D.; Gras, E.G. Assuring QoS Guarantees for Heterogeneous Services in RINA Networks with ΔQ. In Proceedings of the 2016 IEEE International Conference on Cloud Computing Technology and Science, Luxembourg, 12–15 December 2016; IEEE: New York, NY, USA, 2016. [Google Scholar]
- Protogerou, A.; Papadopoulos, S.; Drosou, A.; Tzovaras, D.; Refanidis, I. A graph neural network method for distributed anomaly detection in IoT. Evol. Syst. 2021, 12, 19–36. [Google Scholar] [CrossRef]
- Ishakian, V.; Akinwumi, J.; Esposito, F.; Matta, I. On supporting mobility and multihoming in recursive internet architectures. Comput. Commun. 2012, 35, 1561–1573. [Google Scholar] [CrossRef]
- Trouva, E.; Grasa, E.; Day, J.; Matta, I.; Chitkushev, L.T.; Bunch, S.; de Leon, M.P.; Phelan, P.; Hesselbach-Serra, X. Transport over Heterogeneous Networks Using the RINA Architecture. In Proceedings of the 9th IFIP TC 6 International Conference on Wired/Wireless Internet Communications, Vilanova i la Geltrú, Spain, 15–17 June 2011. [Google Scholar]
- Marek, M.; Teymoori, P.; Gjessing, S.; Welzl, M. High-Rate data transfer with Congestion-Aware multipath routing. In Proceedings of the 2019 IEEE Globecom Workshops (GC Wkshps), Waikoloa, HI, USA, 9–13 December 2019; IEEE: New York, NY, USA, 2019; pp. 1–6. [Google Scholar]
- Neelam, B.S.; Shimray, B.A. Applicability of rina in iot communication for acceptable latency and resiliency against device authentication attacks. In Proceedings of the 2021 6th International Conference for Convergence in Technology (I2CT), Pune, India, 2–4 April 2021; IEEE: New York, NY, USA, 2021; pp. 1–7. [Google Scholar]
- Trouva, E.; Grasa, E.; Day, J.; Matta, I.; Chitkushev, L.T.; Phelan, P.; De Leon, M.P.; Bunch, S. Is the Internet an unfinished demo? Meet RINA! In Proceedings of the TERENA Networking Conference, Vilnius, Lithuania, 31 May–3 June 2010; pp. 1–12. [Google Scholar]
- Marcu, I.; Suciu, G.; Bălăceanu, C.; Vulpe, A.; Drăgulinescu, A.M. Arrowhead Technology for Digitalization and Automation Solution: Smart Cities and Smart Agriculture. Sensors 2020, 20, 1464. [Google Scholar] [CrossRef] [PubMed]
- Schiller, E.; Aidoo, A.; Fuhrer, J.; Stahl, J.; Ziörjen, M.; Stiller, B. Landscape of IoT security. Comput. Sci. Rev. 2022, 44, 100467. [Google Scholar] [CrossRef]
- New Mirai Variant Hits Target with 54-Hour DDoS. 2016. Available online: https://www.infosecurity-magazine.com/news/new-mirai-variant-hits-target-with/ (accessed on 2 January 2026).
- Al Hayajneh, A.; Bhuiyan, M.Z.A.; McAndrew, I. Improving internet of things (IoT) security with software-defined networking (SDN). Computers 2020, 9, 8. [Google Scholar] [CrossRef]
- Minoli, D.; Occhiogrosso, B. Blockchain mechanisms for IoT security. Internet Things 2018, 1, 1–13. [Google Scholar] [CrossRef]
- Sha, K.; Yang, T.A.; Wei, W.; Davari, S. A survey of edge computing-based designs for IoT security. Digit. Commun. Netw. 2020, 6, 195–202. [Google Scholar] [CrossRef]
- Rizinski, M.; Day, J.; Chitkushev, L. IoT Architecture based on RINA. In Proceedings of the 7th International Workshop on RINA, Co-Located with IEEE ICIN 2020, Paris, France, 24–27 February 2020; IEEE: New York, NY, USA, 2020. [Google Scholar]
- Park, C.S. Security architecture for secure multicast coap applications. IEEE Internet Things J. 2020, 7, 3441–3452. [Google Scholar] [CrossRef]
- Ciko, K.; Welzl, M. First contact: Can switching to RINA save the internet? In Proceedings of the 6th International Workshop on the Recursive InterNetwork Architecture (RINA 2019), Co-Located with IEEE ICIN 2019; IEEE: New York, NY, USA, 2019; pp. 37–42. [Google Scholar]
- Ciko, K.; Welzl, M.; Marek, M. TAPS and RINA: Do they fit together? In Proceedings of the 7th International Workshop on RINA 2020, Co-Located with IEEE ICIN 2020; IEEE: Paris, France, 2020. [Google Scholar]





| Cat. | Challenge/Attack | Type | RINA Features and Rationale |
|---|---|---|---|
| Network Layer | Denial-of-Service | P, C | AU (outsiders cannot initiate flows), PI (no listening ports to flood), SS (stale connections auto-expire), QS (excess traffic dropped at first hop) |
| Spoofing | P | HA (addresses hidden from external view), AU (identity verification required), PA (port allocation unpredictable) | |
| Sinkhole | C, D | CD (secure routing within DIF), ML (attack confined to single layer), BF (suspicious routing filtered) | |
| Wormhole | C, D | CD (DIF isolation limits tunnel endpoints), ML (cross-layer tunnels detectable), BF (anomalous paths filtered) | |
| Man-in-the-Middle | P, C | CD (encrypted DIF communication), AU (mutual authentication), PA (connection state unpredictable), IR (large field space resists guessing) | |
| Routing Info. Attacks | P, D | CD (routing tables protected within DIF), HA (topology obscured), AU (only members inject routes), BF (invalid updates filtered) | |
| Sybil | P, C | CD (identities scoped to DIF), AU (enrollment prevents fake identities) | |
| Unauthorized Access | P | AU (authentication required), AC (granular permissions), IA (auth precedes connection) | |
| Middleware | SQL Injection | P, D | AU (authenticated database access), AC (query permissions enforced), PD (custom validation policies) |
| Flooding | P, C | QS (bandwidth limits enforced per-flow, excess dropped) | |
| Signature Wrapping | P | AU (signature verification), DF (secure application protocol), CP (standardized message format) | |
| MITM (Middleware) | P | CD (channel encryption), AU (endpoint verification), HA (intermediaries cannot target endpoints) | |
| Cloud Malware Injection | P, D | AU (service authentication), AC (deployment permissions), PD (integrity policies), BF (malicious traffic filtered) | |
| Application | Phishing | P | CD (communication restricted to DIF members), AU (sender verification), AC (interaction permissions) |
| Malicious Virus/Worm | P, D | AU (code origin verified), BF (propagation traffic filtered) | |
| Malicious Scripts | P, D | DF (application-layer integrity), PD (custom script validation policies) | |
| Sniffing | P | CD (SDU protection encrypts payload) | |
| Brute Force/Dictionary | P | AU (lockout policies, strong credential requirements) | |
| False Data Injection | P, D | CD (integrity verification), DF (application-level data validation) | |
| Properties | Privacy | P | CD (data confidentiality), ML (scope-limited exposure), CC (communication boundaries), PD (privacy policies) |
| Authentication and Non-rep. | P | AU (identity binding at enrollment) | |
| Access Control | P | AC (CDAP-based authorization) | |
| Integrity and Confidentiality | P | CD (SDU protection), DF (end-to-end application security) | |
| Architectural (Section 3) | Ch1: Network Stack | A | CD (security embedded per-layer), ML (consistent mechanisms), RS (multicast support), CR (reduced complexity) |
| Ch2: Redundant Functionality | A | CD (single security mechanism), PD (policy customization), AA (no protocol duplication) | |
| Ch3: Address Space Mgmt. | A | ML (hierarchical scoping), HA (local addressing), VA (scalable allocation) | |
| Ch4: Security–Perf. Conflict | A | CD (security without breaking optimization), ML (layer-appropriate policies), AA (PEP-compatible) | |
| Ch5: Recurring Attacks | P, C | CD (structural defenses), AU (consistent authentication), IR (insider resistance) | |
| Ch6: Future Extensions | A | CP (extensible protocol), PD (adaptable policies), QS, MO, RS, PR | |
| Ch7: Cross-Domain Synergy | A | CD, DF (secure bridging), CP (common protocol), ML, CC, RS, AA |
| Criterion | RINA | TCP/IP | SDN | Blockchain | Edge Comp. | ICN |
|---|---|---|---|---|---|---|
| Security Integration | Embedded | Layered add-on | Overlay | Data-centric | Requires add-on | Content-native |
| Architectural Flexibility | High | Low | High | Low | Medium | Medium |
| Massive IoT Scalability | High | Limited | Medium † | Low | Medium | High |
| Resource Efficiency | High | Medium | Low ‡ | Low | Variable | Medium |
| Implementation Complexity | Low | High | Medium | High | Medium | Medium |
| End-to-End Security | Consistent | Layer gaps | Controller-dep. | Strong (data) | Interface gaps | Content only |
| Deployment Maturity | Emerging | Ubiquitous | Established | Growing | Mainstream | Research |
| Use Case | Key Challenges | RINA Features Applied | Expected Benefits |
|---|---|---|---|
| Smart Home (Section 8.1) | Device heterogeneity, legacy integration, access control | AU, AC, CD, ML, PD | Unified security policy, simplified device enrollment, isolated guest access |
| Healthcare Monitoring (Section 8.2) | Legacy device support, data sensitivity, regulatory compliance | AU, CD, DF, ML, CC | Secure legacy integration via IoT sub-manager, end-to-end encryption, audit trails |
| Secure Multicast (Section 8.3) | Scalable key distribution, group management | RS, CD, ML | Native multicast support, per-DIF group policies, reduced bandwidth overhead |
| Autonomous Vehicles (Section 8.4) | Real-time constraints, V2X communication, adaptive security | PD, QS, MO, CD | Context-aware security policies, seamless handover, QoS guarantees |
| Edge Computing/Smart Manufacturing (Section 8.5) | Data isolation, edge-cloud security, ML model protection | ML, CD, PD, QS, AU | Isolated DIFs per data type, secure edge processing, scalable deployment |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2026 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license.
Share and Cite
Teymoori, P.; Ramezanifarkhani, T. Leveraging Structural Symmetry for IoT Security: A Recursive InterNetwork Architecture Perspective. Computers 2026, 15, 125. https://doi.org/10.3390/computers15020125
Teymoori P, Ramezanifarkhani T. Leveraging Structural Symmetry for IoT Security: A Recursive InterNetwork Architecture Perspective. Computers. 2026; 15(2):125. https://doi.org/10.3390/computers15020125
Chicago/Turabian StyleTeymoori, Peyman, and Toktam Ramezanifarkhani. 2026. "Leveraging Structural Symmetry for IoT Security: A Recursive InterNetwork Architecture Perspective" Computers 15, no. 2: 125. https://doi.org/10.3390/computers15020125
APA StyleTeymoori, P., & Ramezanifarkhani, T. (2026). Leveraging Structural Symmetry for IoT Security: A Recursive InterNetwork Architecture Perspective. Computers, 15(2), 125. https://doi.org/10.3390/computers15020125







