1. Introduction
Generation, transmission, sub-transmission, and distribution networks are the four arms that constitute the whole electrical grid. The most critical and vital protective devices in distribution networks are overcurrent relays (OCRs) and DOCRs, which operate in the event of a fault. The fundamental task of protective relays is to quickly identify a permanent fault and transmit the tripping signal to the circuit breaker. The accurate setting of primary relays (main relays) is at the core of the fundamental architecture governing protective coordination, which is subsequently backed up by secondary relays (backup relays) at regular intervals. In traditional distribution networks, OCRs are the primary protection devices due to the radial orientation of the network’s current [
1,
2]. The conventional electrical distribution network has recently been transformed into a microgrid as a consequence of the penetration of distributed generation (DG) units [
3,
4]. This resulted in the conception of microgrids, in which DGs can feed the distribution network with or without a power grid link [
5,
6]. Due to the multiple orientations of electric current in microgrids, protection schemes are based on DOCRs [
7,
8]. The DOCR setting parameters (
DSPs) contain the current setting parameter (
CSP) and the time setting multiplier parameter (
TSMP).
The
TSMP regulates the time required for the relay to trip, and the
CSP is equal to the current flowing through the secondary side of the relay’s current transformer (CT) [
9,
10]. The time-current characteristic of DOCRs is specified by both the current and time-setting parameters. Due to the nonlinearity of the POSP of DOCRs, nonlinear programming (NLP) is advised to answer the POSP [
11,
12]. In acknowledgment of the lack of advancement in heuristic and meta-heuristic optimization algorithms (MOAs) during the last decades, linear approaches (i.e., the simplex, two-phase simplex, and dual simplex programming) have been employed to assess the DOCR setting parameters [
13]. In this literature, the POSP was formed using linear programming (LP) with the notion that one of the
DSPs is given. In recent years, MOAs have been widely deployed to swiftly handle NLP without damaging the convexity of POSP. The noteworthy MOAs that have been employed to figure out the best outcomes of POSP include improved firefly optimization algorithm (IFOA) [
9], improved moth-flame optimization algorithm (IMFOA) [
10], imperialistic competition optimization algorithm (ICOA) [
11], improved seagull optimization algorithm (ISOA) [
12], chaotic search class topper optimization algorithm (CSCTOA) [
13], the genetic algorithm (GA) [
6,
8,
14,
15,
16,
17], grey wolf optimization algorithm (GWOA) [
17], and partial swam optimization (PSO) [
15,
18].
The disadvantages of MOAs, such as their penchant for early convergence at local points and the excess time needed to solve the POSP, can be alleviated by applying hybrid algorithms [
19,
20]. The outcomes achieved by hybrid algorithms in the referenced literature reveal the superiority of these techniques over others in tackling the malfunction of the DOCRs. In hybrid algorithms, the POSP is partitioned into sub-problems, each of which is addressed using a distinct strategy. In recent studies, hybrid algorithms, such as the hybrid whale optimization algorithm (HWOA) [
19], GA-LP [
20,
21], PSO-LP [
20], hybrid simulated annealing optimization algorithm (SAOA) and LP (HSAOA-LP) [
22], hybrid ant colony optimization algorithm (HACOA) [
23], hybrid gradient-based optimizer (HGBO) [
24,
25], hybrid opposition-based learning fractional order class topper optimization algorithm (HOBL-FOCTOA) [
26], IPA [
27], firefly algorithm (FA) and target remedy [
28], fuzzy logic and GA [
29], GA-PSO with differential evolution (DE) algorithm (GA-PSO-DE) [
30], and FA-LP [
31] have been devised. In addition, machine learning approaches facilitate the computation of
DSPs. Furthermore, ref. [
4] designed a protection scheme based on deep reinforcement learning (DRL) and long short-term memory (LSTM)-enhanced deep neural networks. Also, refs. [
5,
6,
7,
8] provided the clustering algorithms to group diverse network topologies into a small subset with k-means, pre-computed offline setup groups with storing memory, and self-organizing maps (SOM). To remedy the problem of low fault current contributions of inverter-based DGs (IBDGs), ref. [
1] intends harmonic DOCR (HDOCR) with leveraging the current injection capability of IBDGs; ref. [
2] exemplifies a third harmonic voltage produced by the IBDGs controller throughout fault currents; and ref. [
3] refers to virtual impedance-fault current limiters (IFCLs).
The conventional methods of POSP were founded on the immutability of the grid topology (fixed topology (FT)). Nonetheless, electrical equipment failures (i.e., outages of lines, loads, DGs, synchronous machines, etc.) may alter the structure of the distribution grid [
3]. This issue causes the
CSP and fault currents of the network to fluctuate, ultimately resulting in incorrect relay operation [
5,
6]. To prevent the violation (i.e., miscoordination) of DOCRs, the literature advocated incorporating contingencies such as line outages [
32], DG outages [
33,
34], a single contingency for all presumed equipment [
3], and an islanding mode [
1,
2,
3] into the POSP.
Hence, a comprehensive literature review is provided in
Table 1 to establish the existing knowledge and gaps for microgrid protection in terms of published year, dual-setting DOCR, double inverse characteristic of DOCR, and multiple setting groups (MSGs).
DOCR, HDOCR, standard characteristic of DOCR (SCD), non-standard characteristic of DOCR (N-SCD), smart selection of SCD (SSSCD), FT, N-1 contingency, N-2 contingencies, island mode, POSP of DOCR based on communication assisted scheme (PCAC), multi-objective optimization of problem (MOOP), and optimization algorithm.
In this table, the literature review has been summarized. As seen, there is a research gap in the literature because N-2 contingencies have not been studied in the available references in the POSP of DOCR.
In previous decades, a blackout occurred in Europe on 4 November 2006, and in India on 30–31 July 2012, as a result of cascading events [
35,
36]. The following report excerpt is also included in [
37], which contains the annual report for Nordic and Baltic system disruption statistics in 2020.
“Bus 1 (420 kV) in Halden was out of service due to a circuit breaker failure in Sweden. Simultaneously, Bus 2 (420 kV) in Halden is out of service for maintenance. Due to these events, 310 MWh of energy were not supplied, including the interruption of 240 MW of industrial load such as the production of paper”.
Consequently, according to the cited literature and a recent report of power grid disturbances, simultaneous events result in a significant grid disconnection. The possibility of these occurrences is imminent and will result in substantial economic and reliability losses for sensitive loads.
In this paper, the DOCR setting parameters are determined by evaluating N-2 contingencies in order to safeguard the network against a blackout. Cascading failures dramatically increase the problem model’s complexity and size. In order to reduce the dimensions of the POSP, an innovative technique named N-K-ESRT is offered. As a result of this technique’s foundation, all contingency scenarios are reduced to a much smaller subset, and the POSP only analyzes these chosen contingencies. Subsequently, an innovative clustering technique, namely the fuzzy zero-violation clustering algorithm (F-ZVCA), is applied to group the chosen contingencies in order to avoid the miscoordination of DOCRs. The IPA, SAOA, and pattern search optimization algorithm (PSOA) are ultimately employed to pinpoint the DSPs for each cluster. The most noteworthy contributions of this paper might be summarized as follows:
An innovative scale reduction technique called N-K-ESRT is utilized to decrease the scale of the N-2 contingencies.
The F-ZVCA is proposed to eradicate the DOCR’s miscoordination and reduce the scope of the POSP.
The distinguish MOAs are recommended for determining the best DSPs.
The offered solving procedure is applied to three AC microgrids, including a real distribution system (named TESKO2 feeder), besides the IEEE Std. 399-1997 and IEEE 14 bus systems.
3. Protection Optimization Setting Problem
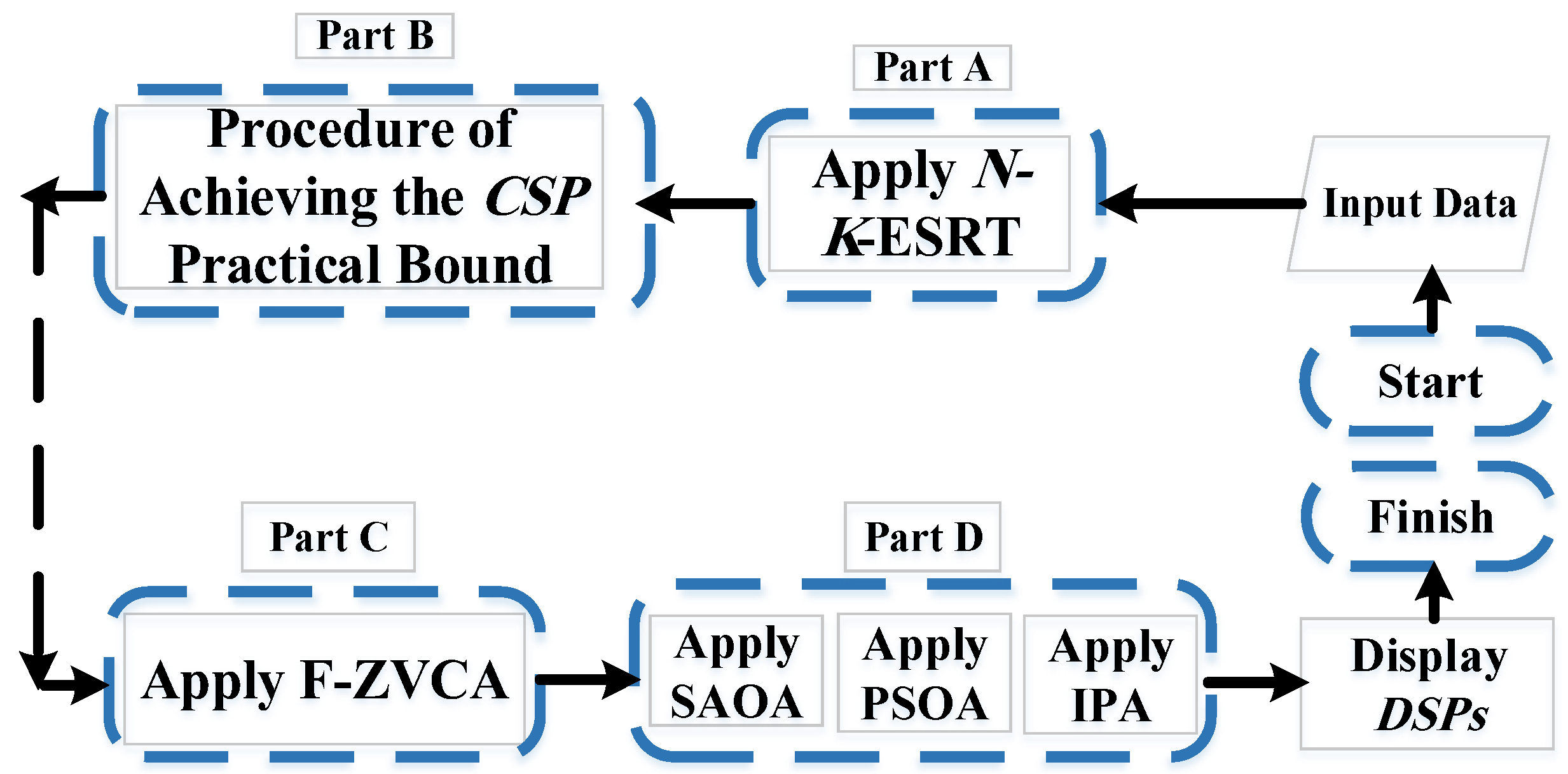
The POSP is divided into four parts, as shown in
Figure 1. The
N-K-ESRT as Part A (
Section 3.1) is initially applied to
N-2 contingencies, and the chosen contingencies are identified. After that, the limitations of
CSP are determined by the procedure described in Part B (
Section 3.2). Next, F-ZVCA is performed to group the findings of
N-K-ESRT in Part C (
Section 3.3). In conclusion, MOAs will optimize the values of
DSPs as Part D (
Section 3.4). Each part is described in depth below.
3.1. N-K Events Scale Reduction Technique
Professional standards mandate that microgrids be safeguarded against a single event, or
N-1 contingency [
39,
40,
41]. Nevertheless, it is conceivable that
K events occurred simultaneously, which is alluded to as
N-K contingencies. Technically, the POSP does not need to take into consideration the three or four simultaneous outages (
K ≥ 3). This is due to the fact that the probabilities of these component failures are multiplied by each other, and the possibility of such occurrences is exceedingly low [
42]. The incidence of
N-2 contingencies results in the disconnection of critical industrial loads and a sharp rise in energy not supplied (ENS) [
43,
44,
45]. In light of this, the POSP of DOCRs is assessed, considering
N-2 events. However, managing
N-2 contingencies is significantly more difficult due to their vast number, especially in large-scale systems. Accordingly, the
N-K-ESRT is recommended as an innovative solution to this problem. Due to the construction of
N-K-ESRT, the number of all
N-2 probable events will greatly decrease. The
N-K-ESRT puts all supposed outage-related equipment (lines, DGs, generators, etc.) into a subset. Next, the maximum and minimum voltage limits of each network’s bus are calculated for all
N-2 outages. Following this, the process selects the
N-2 outages that result in the highest and lowest voltages for each bus. Given that the amount of current flowing through a line is directly proportional to the voltage difference between its corresponding buses, this technique encompasses the entire spectrum of network currents for all
N-2 events.
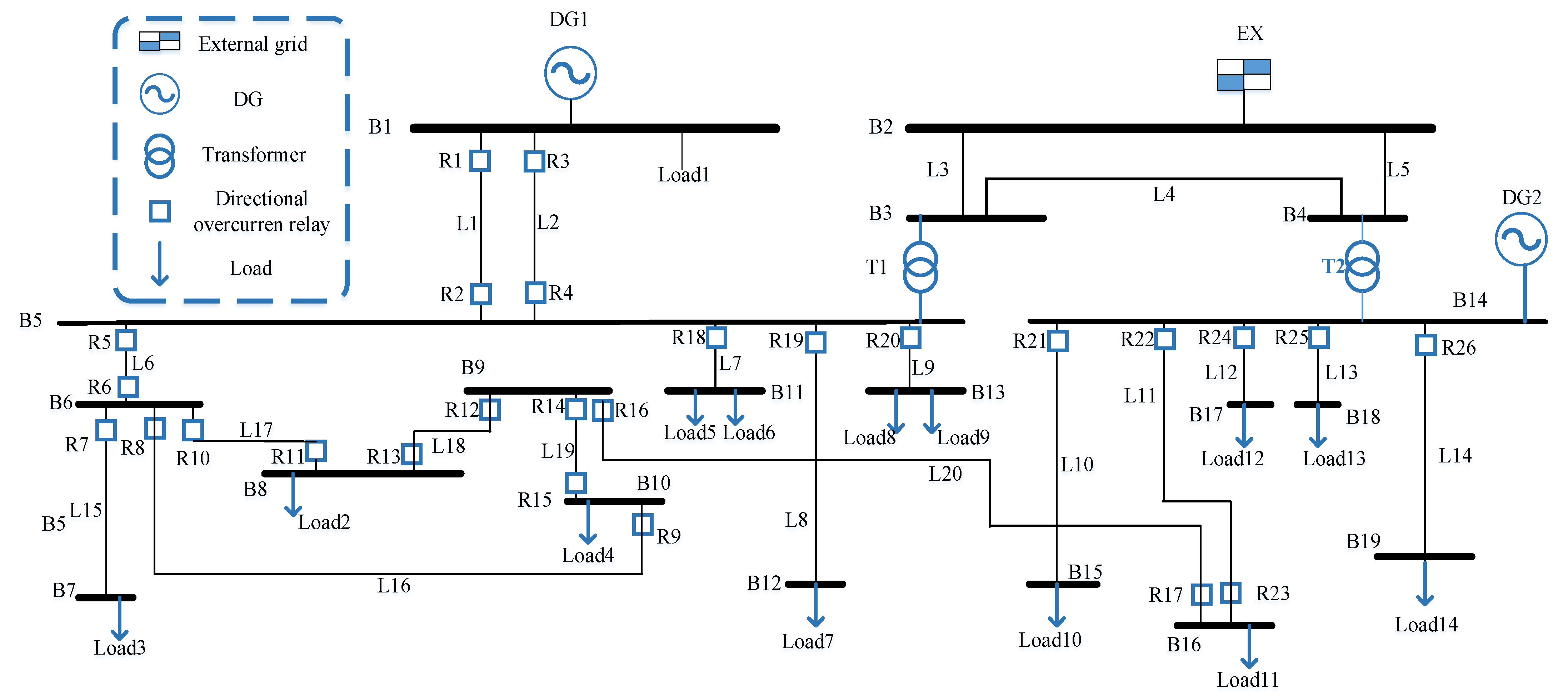
Consider
Figure 2 as a sample network for judging this approach.
All anticipated equipment for
N-2 contingencies in a subset consists of nine components, including DG1 and DG2, load 1 and load 2, lines (i.e., L1, L2, and L3), and generators (i.e., Gen. 1 and Gen. 2). In order to implement the intended technique, the earlier specified equipment must be taken out of service in two simultaneous events, and the voltage of the buses (i.e., B1, B2, B3, and B4) must be measured in each of these occurrences. For example, one of the
N-2 events led to the lowest voltage value in B1, and another led to the highest voltage value in the same bus. The
N-K-ESRT has picked these two occurrences as the chosen contingencies for B1. The POSP automatically applies this approach to each bus, resulting in eight occurrences based on (8) for the sample network’s buses (i.e.,
NUESRT equals two times the number of buses in the network under investigation). Rather, if all
N-2 outages are considered, 36 occurrences (called
OCC) will need to be investigated as (9) [
46]. POSP is able to access the “maximum voltage violation study” for cascading events with the help of the Power Factory 15.1.7 DIgSILENT software. The result of this analysis reveals which of these 36 scenarios has the greatest and least noticeable impact on the network bus voltage. So, this method has led to a 75% decrease in the number of
N-2 events in the sample network, which would help reduce the size of the problem and speed up the POSP. It should be emphasized that, with the rise of assuming equipment for
N-2 events, this technique will be more beneficial than before.
3.2. The Procedure of Achieving the CSP Practical Bound (PA-CSP-PB) for the POSP
To facilitate the description of this section,
Figure 2 serves as the sample network (as depicted in the
N-K-ESRT section), and
Figure 3 (consisting of parts A–K) provides the flowchart of PA-
CSP-PB. The idea of this section is to acquire the
CSP practical range of R
M (shown in
Figure 2) according to (6) and (7), which can be applied to the rest of the DOCRs. First, the maximum network current passing through the R
M is used to determine the least bound of (7) for the R
M. This is accomplished by employing the Newton–Raphson load flow (NR-LF) to compute the current flowing through L1 (seen in part A).
The picked current for the next part (part B) is the maximum current passing through the L1 (
) for all eight network configurations, which is attained by (10). As described in the preceding section, the
N-K-ESRT identifies eight occurrences of two simultaneous outages. Subsequently,
among these eight occurrences, one is chosen as the R
M’s maximum current. Additionally, (11) adds 20% to the
, named
. This issue is due to the necessity of preventing a false trip caused by a maximum load current rather than a permanent fault (shown in part C). As seen in part D, (13) obtains the plug setting (
) for the following approach, using (12) as an asset. The plug setting is the percent of R
M’s CT winding, which varies from 50% to 200% in 25% increments. The ratio between the primary (
CTP) and secondary (
CTS) windings of a CT is denoted by (12) and written as
CTR. In accordance with PA-
CSP-PB, the plug setting is rounded up and
is recalculated by (13) as part E. Next, the current flowing through the secondary side of the CT (
) is calculated using the formula (14) and is illustrated in part F. This current (
) is the same current that should be deemed the lowest bound in (7). Particularly, the relation specified in (15) will suffice as the
CSP bound of POSP. Accordingly, the lower limit of (15) is the greatest value between
and
(seen in part G). Selecting the maximum value at the lower limit of (15) is intended to prevent network power interruptions. The upper limit of (15) also represents the least value between
and
. Note that the minimal short circuit current (i.e.,
) employed in the case studies is equivalent to the single-phase ground fault current stipulated by standard
IEC 60909-2001 [
47] (part H). Similar to the preceding process that established the lower limit of the
CSP, the short circuit current value used in the next part is the lowest short circuit current among all
N-K-ESRT’s topologies based on (16) and depicted in part J. The fault current determined by (16) is the maximum bound of (7). Now, the upper limit of (15) is the minimum value between the
and
(part K). Considering that the L1 should be rendered inoperable in the event of a short circuit, the minimum value was set at the upper limit of (15). The PA-
CSP-PB will perform all the described steps for each relay. The PA-
CSP-PB relations can be defined as:
3.3. Fuzzy Zero-Violation Clustering Algorithm
Multiple setting groups are a function of the utilized relays that permit the DOCRs to have several
DSP groups, only one of which operates in the present grid structure [
5,
6,
7,
8]. To employ DOCR’s MSG, similar
DSPs are placed in the right cluster using clustering algorithms. Given that there are four MSGs in DOCR, the
N-K-ESRT must be divided into four clusters (or less than four clusters). Clustering is a mathematical technique for categorizing several similar data points into distinct groups [
6]. As an innovative clustering algorithm, the F-ZVCA groups all topologies obtained by
N-K-ESRT into separate clusters using the procedure outlined below. The concept of F-ZVCA comes from k-means clustering, fuzzy C-means clustering, and POSP trial and error.
Assigning each topology to its appropriate cluster involves the following six steps, which are shown in
Figure 4:
Step 1: Initially, time center points are randomly considered as the centers of the clusters (OTC1, OTC2, OTC3, and OTC4). These center points indicate the total operating time (OT) of the network’s primary relays. For instance, OTC1 is identified as the time center point for the “C1” cluster (i.e., cluster 1).
Step 2: Secondly, fault current center locations designated (including and ) are picked at random as supplementary cluster centers. These center points reflect the total fault current ratio between the main DOCRs and their backup relays. In this particular case, the fault current centroid point of “C2” (i.e., cluster 2) is shown as .
Step 3: Subsequently, the total operation time of the main relays is decided based on (17) for all derived topologies (OTS1, OTS2… etc.) with the help of (1) and the default TSMP = 1, and CSP = ICSP. For example, OTS3 signifies the total operation time of the main DOCRs for the “S3” topology.
Step 4: Fourth, using (18), the distance of OTS1 from all time center points (i.e., OTC1, OTC2… etc.) is determined and designated as DOTS1-C1, DOTS1-C2, … This procedure is done for each resultant topology (i.e., DOTS2-C1… DOTS3-C1…).
Step 5: Using the formula in (19), a fuzzy parameter denoted is derived by (20). Equation (19) signifies the average ratio between the fault current of the primary DOCR and their backup relays. is computed for any topologies coming from N-K-ESRT. In essence, (19) demonstrates that the fluctuations in the short-circuit level were significant for each topology; presumably, that topology should have a higher probability of being conveyed.
(Note: The resultant topologies should be more likely to be clustered together when the values are closest to each other among all ones.)
Step 6: Equation (21) is determined between each derived topology and the clusters using (20) and (18). Among the values obtained for topology ‘S1’, including:S1-C1, S1-C2, topology ‘S1’ is allocated to the cluster with the smallest S-C value. Lastly, steps 1 through 6 are repeated until the clusters’ constituents are no longer altered.
The F-ZVCA will therefore exhibit its results if the POSP has no miscoordination across all clusters. If miscoordination has occurred, F-ZVCA relocates the specific topology to a different cluster. As stated previously, the specified topology must be transmitted from its cluster to another cluster with the maximum possible value of (21). This topology should be transmitted to the succeeding cluster if (19) has the greatest value deviation compared to the other topologies generated by
N-K-ESRT. The relationships associated with F-ZVCA can be described as follows:
3.4. Meta-Heuristic Optimization Algorithms
After the
N-K-ESRT and F-ZVCA reduce the dimensions of the POSP, the
DPSs are produced employing three MOAs, encompassing IPA, SAOA, and PSOA. The IPA handles both vastness and spread as well as smallness and concentration problems and may be retrieved from either
NaN or
Inf results [
48]. Besides, SAOA is a technique for answering both constrained and unconstrained optimization issues. Accepting poorer solutions throughout the optimization procedure while retaining the ability to escape local points is a distinguishing feature of SAOA [
22]. On the other hand, PSOA is highly valuable for nonlinear programming problems and has the potential to substantially optimize local search. Refer to [
22,
48,
49] for details on the IPA, SAOA, and PSOA, respectively.