Risk Reduction Strategies against Terrorist Acts in Urban Built Environments: Towards Sustainable and Human-Centred Challenges
Abstract
1. Introduction
1.1. Work Aims
2. Overview of Considerable Regulations and Classifications in Risk Management and Reduction Strategies for Terrorist Acts
2.1. Selection Methodology, Selected Materials and Review Organization Methods
2.2. Classifications of Terrorist Act Risk Management and Reduction Strategies
2.2.1. Target-Oriented Classifications
- Active actions, where a bi-univocal relation between overarching governances and urban users is activated by including prevention (i.e., active military intelligence), mitigation (i.e., active education of BE users) and security/safety (active surveillance solutions);
- Passive actions, in which any feedback is established by users and overarching rules/guidelines/indications are simply applied, by including prevention (i.e., passive normative regulations), mitigation (i.e., passive information of the BE users) and security/safety (i.e., passive control for urban space design and security).
- Safety strategies are essentially oriented towards the protection of the hosted users from all the failures that can appear in the BE. They limit the fatalities due to their use in some risk-increasing conditions, such as those of mass gathering events, as well as due to the consequences of the terrorist acts, such as injuries and deaths due to the attack-related emergency;
- Security strategies are essentially oriented towards the contrast of intentional actions due to the terrorist act and thus preserve the public order. They mainly include all the measures performed by the Security Forces before and during the attack.
2.2.2. Attack-Oriented Classification
2.2.3. Time-Dependent Classifications
2.2.4. Space-Dependent Classifications
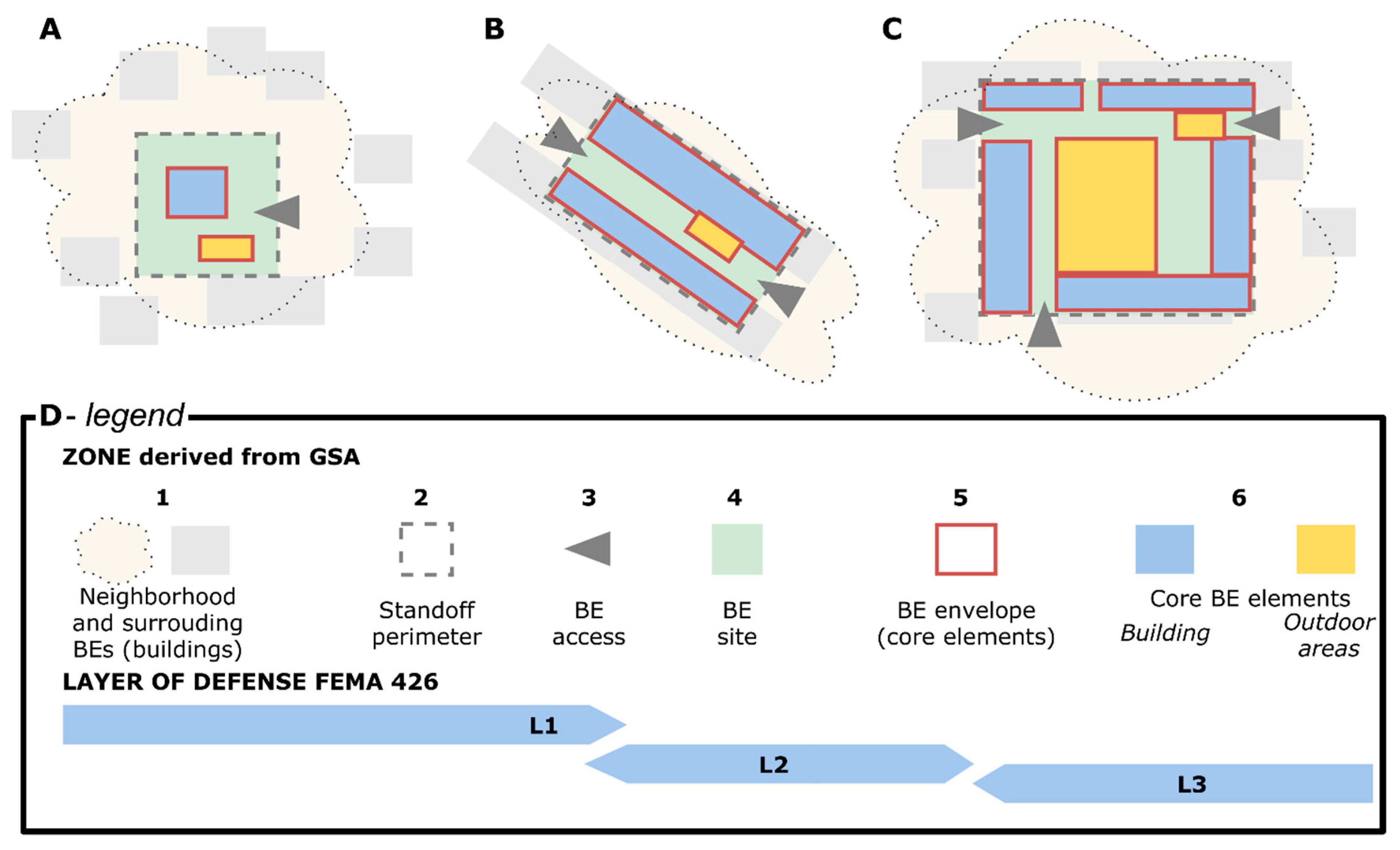
- The First (or Outer) Layer (in the following, L1) is composed of all the barriers placed at the borders of the considered open space (e.g., for isolated buildings, the property line; for complex linear or areal BEs in urban scenarios, the limit of the area considered to be protected by RMRSs). The urban areas and the BEs placed beyond L1 are not controlled by the BE stakeholders and users. L1-related RMRSs are essentially based on the possibility to create a limit for the BE-related RMRSs and to relate all the RMRSs involved in increasing urban resilience (e.g., involvement of the population, security and safety strategies for urban areas, security forces operation and counterterrorism actions) [3,13,29];
- The Second (or Middle) Layer (in the following, L2) is associated with the areas and objects deployed from the BE internal border to the exterior limit of the core elements. It refers to the physical envelope of subparts of the BE also outdoors, such as specific barriers enclosing areas in the BE, that are courtyards, gardens, restricted access areas in public open spaces (including those related to temporary BE use conditions, such as for mass gathering events). L2-related RMRSs provide a standoff into the open spaces in the BE, being under the direct control of their stakeholders. The site includes all the related areas, by referring to both those which can host the core elements (compare to the following Third Layer) and to the (outdoor) distribution spaces (e.g., access roads, evacuation paths, ancillary spaces);
- The Third (or Inner) Layer (in the following, L3) usually refers to the envelope and/or to the inside of the core elements, which can be majorly identified as attack goals. It can mainly involve specific buildings [46], but also outdoor areas, such as band stages, art stands, and observation areas open to the audience [44,54]. This layer separates “unsecured from secured areas”. As a consequence, L3-related RMRSs are effective to limit the possibility that a terrorist act could happen or affect the core of the BE.
2.2.5. Physical Versus Management-Oriented Classifications
- Security and safety planning strategies to be applied before and after the attack, based on risk assessment methodologies which can better identify the BE vulnerabilities;
- People’s involvement, improving risk awareness, preparedness and response of the users;
- Policies, regulation and finance (including insurance-oriented) supporting the hosted activities (mainly economic ones and those with social impact).
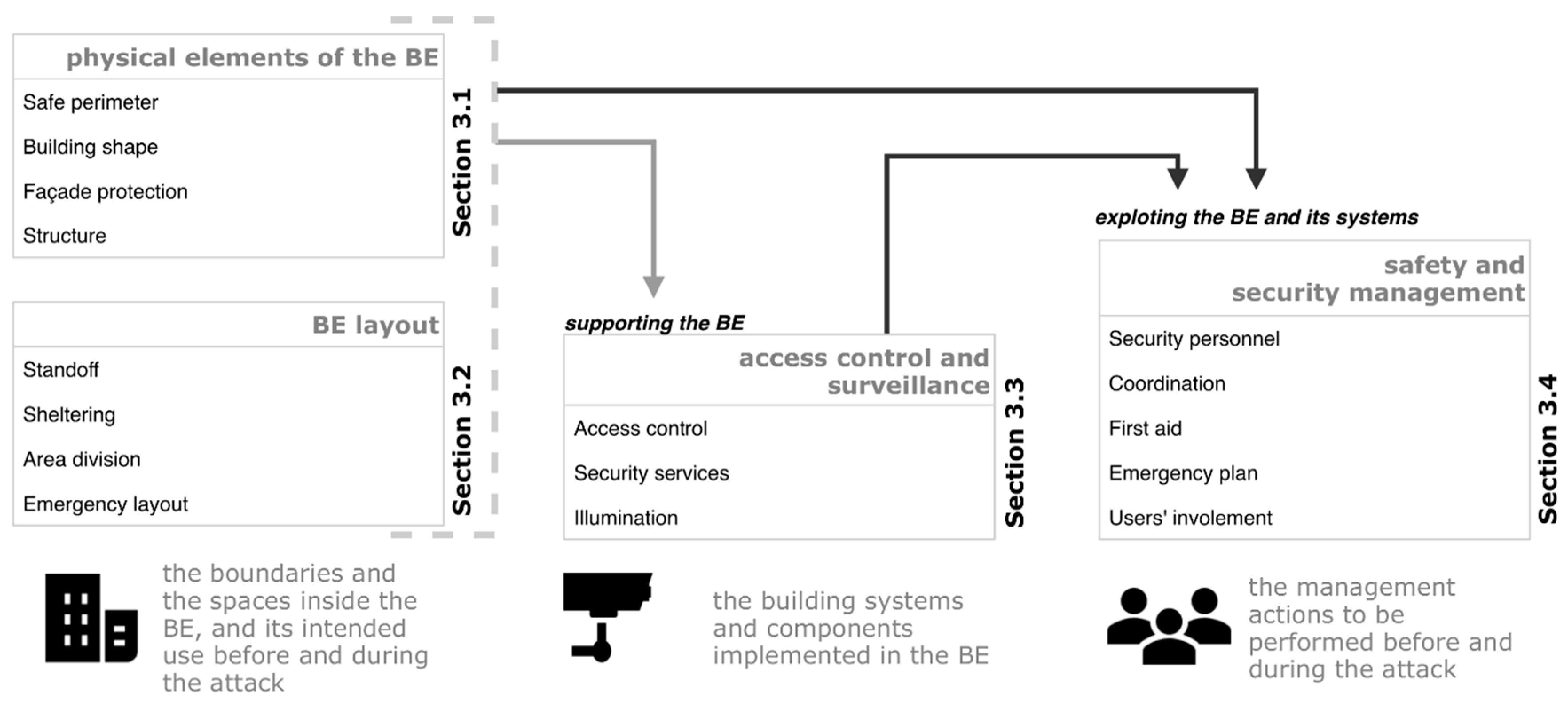
3. Classifying Existing Paradigms by Considering the BE Elements
- The design of the physical elements composing the open space in the BE, by focusing on those used as perimeters (e.g., building façades, barriers in outdoor areas) and those placed inside it (e.g., outdoor areas and buildings having a specific function and/or feature) (Section 3.1);
- BE layout, by involving RMRSs dealing with the organization of indoor and outdoor spaces, distance-related issues (i.e., standoff), and emergency facilities (Section 3.2);
- Access control and surveillance, dealing with the strategies to be implemented towards such goals on the border of/inside the BE (Section 3.3);
- Safety and security management, evidencing how safety and security staff actions could reduce the risk before/during the threat (Section 3.4).
3.1. RMRSs by the Design of the Physical Elements
- Resistance to impacts that usually depend on vehicle typology and speed;
- Geometric efficacy when solutions are a system of independent elements;
- Emergency compatibility to guarantee the possibility of moving out of the BE site (e.g., correct dimensioning of passages, barriers that can be knocked out by evacuees).
- Facing blast load effects. In this sense, these strategies firstly consider building geometry, size (e.g., horizontal development is preferred to a vertical one) and façade continuum (re-entrant corners, circular and concave forms). Furthermore, the immediate building surroundings could additionally ensure a positive effect, by using safe perimeter-based solutions (e.g., barriers against bombings, outdoor spaces plano-altimetric configuration, and so on);
- Preventing possible assaults of terrorists inside the buildings (e.g., intrusion and armed assaults or following bombing as internal threats) or in the immediate surroundings. In this sense, these strategies try to ensure the possibility of blocking views of the inside assets to perpetrators or improve the building control (see Section 3.3). As well for this attack type, the buffer zones could support such strategies while being combined with building orientation, vegetation use, building components and external area planning elements (e.g., obstruction screens and man-made hillsides).
- Laminated glass with an inner layer of polyvinyl butyral well secured into the frames is preferred. Concerning their position, windows are placed low down, reducing the distance of flying glass into the room.
- Security doors provide enhanced protection against forced entry and overall resilience of the outer shield of the building; moreover, doors should be bomb resistant, bullet resistant and extreme-intrusion-attempts resistant.
3.2. RMRSs by BE Layout
- The design of physical elements in the BE, adopting “Façade protection” measures to contrast the attack itself;
- The aforementioned “emergency layout” strategies by integrating them with the support of management solutions. In this sense, additional RMRSs can mainly concern: (1) correctly signalling the sheltering areas by means of signs or by using “emergency plan” related actions by safety and security staff members; (2) also promoting “users’ involvement” before the event;
- Additional “access control and surveillance” solutions to impede the attackers who could arrive at the shelters.
3.3. RMRSs by Access Control and Surveillance
3.4. RMRSs by Safety and Security Management
4. Challenges in a Holistic, Sustainable and Human-Centred Approach to Risk Reduction Strategies’ Classification and Evaluation
- Moving towards redundancy criteria of the resilient BE by combing different strategies to ensure that each of them could support the risk-reduction process (according to different operational procedures) in all the phases of the disaster;
- Selecting solutions to be effective for more than one terroristic threat/attack typology;
- Adopting a human-centred approach to include the behavioural reaction of the exposed individuals (especially in crowds) and of the terrorists, also in respect to the human–BE interactions (i.e., for the promotion of correct emergency behaviours);
- Including mass gathering conditions during strategy planning to ensure the safety and security aspects of different BE use situations;
- Considering the possibilities of connecting different BEs (at a local scale, e.g., indoor-outdoor; at a global/urban scale) to face the disaster;
- Promoting a psychological function of the strategies to ensure they are perceived as reliable by the citizen, to deter the terrorists but also to guarantee the liveability of the BE under normal use conditions.
5. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
Appendix A
| Country | Number of Documents | Document: Institutions and/or Authors (Year) Title [Language], Other Identification Data including Website |
|---|---|---|
| Australia | 3 | Live Performance Australia (2019) Audience and Crowd Management Hazard Guide [English] |
| Commonwealth of Australia (2017) Australia’s Strategy for Protecting Crowded Places from Terrorism [English] ISBN: 978-1-925593-95-2 | ||
| Australian Institute for Disaster Resilience (2018) Safe and Healthy Crowded Places [English] Handbook 15 | ||
| Czech Republic | 1 | Soft Targets Protection Institute/Kalvach, Z., et al., (2016). Basics of Soft Targets Protection—Guidelines (2nd Version), https://www.mvcr.cz/cthh/soubor/basics-of-soft-target-protection-guidelines.aspx |
| France | 3 | Ministère de la Culture et de la Communication (2016) Vigilance Attentat: les Bons Réflexes-Guide à Destination des Organisateurs de Rassemblements et Festivals Culturels [French] https://www.culture.gouv.fr/Actions-de-renforcement-et-de-surveillance-des-lieux-culturels |
| Ministère de la Culture et de la Communication (2016) Vigilance Attentat: les Bons Réflexes-Guide à Destination des Dirigeants D’établissements Culturels Patrimoniaux [French] https://www.culture.gouv.fr/Actions-de-renforcement-et-de-surveillance-des-lieux-culturels | ||
| Ministère de l’Intérieur, de la Culture et de la Communication, Secrétariat général de la Défense et de la Sécurité National (2017) Gérer la Sûreté et la Sécurité des événements et Sites Culturales [French] | ||
| India | 1 | National Disaster Management Authority (2014) Managing Crowd at Event and Venues of Mass Gathering [English] |
| Italy | 3 | Ministero degli interi (2017) Circolare 7/6/17 n.555/OP/0001991/2017/1 [Italian] |
| Ministero degli interi (2017) Direttiva 28/07/2017 n. 11001/110(10) [Italian] | ||
| Ministero degli interi (2018) Direttiva 18/07/2018 n. 11001/1/110/(10) [Italian] | ||
| UK | 3 | Home Office in partnership with the Department for Communities and Local Government (2012) Crowded Places: The Planning System and Counter-Terrorism [English] ISBN: 978-1-84987-392-5 |
| Pool Re/Julian Enoizi (2017) Terrorism Threat & Mitigation Report [English] | ||
| Home Office in partnership with the Centre for the Protection of National Infrastructure and the National Counter-Terrorism Security Office (2012) Protecting Crowded Places: Design and Technical Issues [English] ISBN: 978-1-84987-393-2 | ||
| United States | 5 | Joint Counterterrorism Assessment Team (JCAT) (2018) Planning and Preparedness Can Promote an Effective Response to a Terrorist Attack at Open-Access Events [English] |
| Homeland Security Science and Technology (2018) Planning Considerations: Complex Coordinated Terrorist Attacks [English] | ||
| Homeland Security Science and Technology (2009) Handbook for Rapid Visual Screening of Buildings to Evaluate Terrorism Risks [English] FEMA 455 | ||
| Homeland Security Science and Technology (2011) Reference Manual to Mitigate Potential Terrorist Attacks Against Buildings [English] FEMA-426/BIPS-06/Edition 2 | ||
| U.S. Department of Homeland Security (2006) Safe Rooms and Shelters Protecting People Against Terrorist Attacks [English] FEMA 453 |
Appendix B
| Bombing Attack | Armed Assault | Attack with a Cold Weapon | Vehicle Running into the Target | Arson | Unmanned Aircraft Systems | CBR Attacks | Hostage Taking | Crowd Attack | Facility Attacks | Total | |
|---|---|---|---|---|---|---|---|---|---|---|---|
| Safe perimeter | X | - | - | X | - | - | - | - | - | - | 2/10 |
| Building shape | X | X | X | X | - | - | - | - | - | - | 4/10 |
| Façade protection | X | X | - | - | - | - | - | - | - | - | 2/10 |
| Structure | X | - | - | - | - | - | - | - | - | - | 1/10 |
| Standoff | X | - | - | X | - | - | - | - | - | - | 2/10 |
| Sheltering | X | X | - | X | X | X | X | - | - | - | 6/10 |
| Area division | X | X | X | X | - | - | - | - | X | - | 5/10 |
| Emergency layout | X | X | X | X | - | - | - | - | X | - | 5/10 |
| Access control | X | X | X | - | X | - | X | X | X | - | 7/10 |
| Security service | X | X | X | - | X | - | - | X | X | - | 6/10 |
| Illumination | X | X | X | - | - | - | - | - | - | X | 4/10 |
| Security personnel | X | X | X | X | X | - | - | X | X | - | 7/10 |
| Coordination | X | X | X | X | X | X | X | X | X | X | 10/10 |
| First aid | X | X | X | X | X | X | X | X | X | - | 9/10 |
| Emergency plan | X | X | X | X | X | X | X | X | X | X | 10/10 |
| Users’ involvement | X | X | X | X | X | X | X | X | X | X | 10/10 |
 |
References
- IInstitute for Economics & Peace Global Terrorism Index 2019: Measuring the Impact of Terrorism. Available online: http://visionofhumanity.org/reports (accessed on 22 July 2020).
- National Consortium for the Study of Terrorism and Responses to Terrorism (START) Global Terrorism Database (GTD). Available online: www.start.umd.edu/gtd/search/ (accessed on 1 December 2019).
- Gordon, T.J.; Sharan, Y.; Florescu, E. Potential measures for the pre-detection of terrorism. Technol. Forecast. Soc. Change 2017, 123, 1–16. [Google Scholar] [CrossRef]
- UNDRR. Disaster Definitions-Global Disaster Loss Collection Initiative. Available online: https://www.desinventar.net/definitions.html (accessed on 22 July 2020).
- National Consortium for the Study of Terrorism and Responses to Terrorism (START). Global Terrorism Database Codebook: Inclusion Criteria and Variables; 2019; Available online: https://www.start.umd.edu/gtd/downloads/Codebook.pdf (accessed on 22 July 2020).
- Cozzolino, A. Humanitarian Logistics; SpringerBriefs in Business; Springer: Berlin/Heidelberg, Germany, 2012; ISBN 978-3-642-30185-8. [Google Scholar]
- Jore, S.H. The Conceptual and Scientific Demarcation of Security in Contrast to Safety. Eur. J. Secur. Res. 2019, 4, 157–174. [Google Scholar] [CrossRef]
- Coaffee, J.; O’Hare, P.; Hawkesworth, M. The visibility of (in) security: The aesthetics of planning urban defences against terrorism. Secur. Dialogue 2009, 40, 489–511. [Google Scholar] [CrossRef]
- Cuesta, A.; Abreu, O.; Balboa, A.; Alvear, D. A new approach to protect soft-targets from terrorist attacks. Saf. Sci. 2019, 120, 877–885. [Google Scholar] [CrossRef]
- Beňová, P.; Hošková-Mayerová, Š.; Navrátil, J. Terrorist attacks on selected soft targets. J. Secur. Sustain. Issues 2019, 8, 453–471. [Google Scholar] [CrossRef]
- Zoli, C.; Steinberg, L.J.; Grabowski, M.; Hermann, M. Terrorist critical infrastructures, organizational capacity and security risk. Saf. Sci. 2018, 110, 121–130. [Google Scholar] [CrossRef]
- National Research Council. Infrastructure for the 21st Century: Framework for a Research Agenda; National Academies Press: Washington, DC, USA, 1987; ISBN 978-0-309-07814-6. [Google Scholar]
- Karlos, V.; Larcher, M.; Solomos, G. Review on Soft Target/Public Space Protection Guidance; Publications Office of the European Union: Luxemburg, 2018; ISBN 978-92-79-79907-5. [Google Scholar]
- Woo, G. Understanding the Principles of Terrorism Risk Modeling from Charlie Hebdo Attack in Paris. Def. Against Terror. Rev. 2015, 7, 1–11. [Google Scholar]
- French, E.L.; Birchall, S.J.; Landman, K.; Brown, R.D. Designing public open space to support seismic resilience: A systematic review. Int. J. Disaster Risk Reduct. 2019, 34, 1–10. [Google Scholar] [CrossRef]
- Koren, D.; Rus, K. The potential of open space for enhancing urban seismic resilience: A literature review. Sustainability 2019, 11, 5942. [Google Scholar] [CrossRef]
- Sharifi, A. Resilient urban forms: A review of literature on streets and street networks. Build. Environ. 2019, 147, 171–187. [Google Scholar] [CrossRef]
- Bennett, B. Understanding, Assessing, and Responding to Terrorism; John Wiley & Sons, Inc.: Hoboken, NJ, USA, 2017; ISBN 9781119237792. [Google Scholar]
- Lapkova, D.; Kotek, L.; Kralik, L. Soft Targets–Possibilities of Their Identification. In Proceedings of the 29th DAAAM International Symposium; Katalinic, B., Ed.; DAAAM International: Vienna, Austria, 2018; pp. 0369–0377. ISBN 978-3-902734-20-4. [Google Scholar]
- Marchment, Z.; Gill, P. Modelling the spatial decision making of terrorists: The discrete choice approach. Appl. Geogr. 2019, 104, 21–31. [Google Scholar] [CrossRef]
- Kılıçlar, A.; Uşaklı, A.; Tayfun, A. Terrorism prevention in tourism destinations: Security forces vs. civil authority perspectives. J. Destin. Mark. Manag. 2018, 8, 232–246. [Google Scholar] [CrossRef]
- Zhu, R.; Lin, J.; Becerik-Gerber, B.; Li, N. Human-building-emergency interactions and their impact on emergency response performance: A review of the state of the art. Saf. Sci. 2020, 127, 104691. [Google Scholar] [CrossRef]
- Dai, Q.; Zhu, X.; Zhuo, L.; Han, D.; Liu, Z.; Zhang, S. A hazard-human coupled model (HazardCM) to assess city dynamic exposure to rainfall-triggered natural hazards. Environ. Model. Softw. 2020, 127, 104684. [Google Scholar] [CrossRef]
- Gayathri, H.; Aparna, P.M.; Verma, A. A review of studies on understanding crowd dynamics in the context of crowd safety in mass religious gatherings. Int. J. Disaster Risk Reduct. 2017, 25, 82–91. [Google Scholar] [CrossRef]
- Wagner, N.; Agrawal, V. An agent-based simulation system for concert venue crowd evacuation modeling in the presence of a fire disaster. Expert Syst. Appl. 2014, 41, 2807–2815. [Google Scholar] [CrossRef]
- Li, J.; Li, J.; Yuan, Y.; Li, G. Spatiotemporal distribution characteristics and mechanism analysis of urban population density: A case of Xi’an, Shaanxi, China. Cities 2019, 86, 62–70. [Google Scholar] [CrossRef]
- Home Office in partnership with the Department for Communities and Local Government. Crowded Places: The Planning System and Counter-Terrorism; 2012; ISBN 978-1-84987-392-5. Available online: https://assets.publishing.service.gov.uk/government/uploads/system/uploads/attachment_data/file/375208/Crowded_Places-Planning_System-Jan_2012.pdf (accessed on 22 July 2020).
- Mistretta, P.; Garau, C.; Pintus, S. Beni Comuni dello Spazio Urbano; CUEC editrice: Cagliari, Italy, 2014; ISBN 978-88-8467-884-3. [Google Scholar]
- Laufs, J.; Borrion, H.; Bradford, B. Security and the smart city: A systematic review. Sustain. Cities Soc. 2020, 55, 102023. [Google Scholar] [CrossRef]
- Home Office in partnership with the Department for Communities and Local Government. Protecting Crowded Places: Design and Technical Issues; Home Office, 2014. Available online: https://assets.publishing.service.gov.uk/government/uploads/system/uploads/attachment_data/file/302016/DesignTechnicalIssues2014.pdf (accessed on 22 July 2020).
- Albores, P.; Shaw, D. Government preparedness: Using simulation to prepare for a terrorist attack. Comput. Oper. Res. 2008, 35, 1924–1943. [Google Scholar] [CrossRef]
- Joint Counterterrorism Assessment Team (JCAT). Planning and Preparedness Can Promote an Effective Response to a Terrorist Attack at Open-Access Events; 2018. Available online: https://www.dni.gov/files/NCTC/documents/jcat/firstresponderstoolbox/First-Responders-Toolbox---Planning-Promotes-Effective-Response-to-Open-Access-Events.pdf (accessed on 22 July 2020).
- Liu, H.; Chen, H.; Hong, R.; Liu, H.; You, W. Mapping knowledge structure and research trends of emergency evacuation studies. Saf. Sci. 2020, 121, 348–361. [Google Scholar] [CrossRef]
- Lin, J.; Zhu, R.; Li, N.; Becerik-Gerber, B. How occupants respond to building emergencies: A systematic review of behavioral characteristics and behavioral theories. Saf. Sci. 2020, 122, 104540. [Google Scholar] [CrossRef]
- Kalvach, Z. Basics of soft Targets Protection-Guidelines, 2nd ed.; Soft Targets Protection Institute, z.ú.: Prague, Czech Republic, 2016. [Google Scholar]
- Bernardini, G.; Lovreglio, R.; Quagliarini, E. Proposing behavior-oriented strategies for earthquake emergency evacuation: A behavioral data analysis from New Zealand, Italy and Japan. Saf. Sci. 2019, 116, 295–309. [Google Scholar] [CrossRef]
- Gin, J.L.; Stein, J.A.; Heslin, K.C.; Dobalian, A. Responding to risk: Awareness and action after the September 11, 2001 terrorist attacks. Saf. Sci. 2014, 65, 86–92. [Google Scholar] [CrossRef]
- Alnabulsi, H.; Drury, J.; Templeton, A. Predicting collective behaviour at the Hajj: Place, space and the process of cooperation. Philos. Trans. R. Soc. B Biol. Sci. 2018, 373, 20170240. [Google Scholar] [CrossRef]
- Templeton, A.; Neville, F. Modeling Collective Behaviour: Insights and Applications from Crowd Psychology. In Crowd Dynamics; Gibelli, L., Ed.; Springer Nature Switzerland AG: Cham, Switzerland, 2020; Volume 2, pp. 55–81. ISBN 9783030504502. [Google Scholar]
- Li, S.; Zhuang, J.; Shen, S. A three-stage evacuation decision-making and behavior model for the onset of an attack. Transp. Res. Part C Emerg. Technol. 2017, 79, 119–135. [Google Scholar] [CrossRef]
- Quagliarini, E.; Currà, E.; Fatiguso, F.; Mochi, G.; Salvalai, G. Resilient and User-Centered Solutions for a Safer Built Environment Against Sudden and Slow Onset Disasters: The BE S2ECURe Project. In Sustainability in Energy and Buildings 2020. Smart Innovation, Systems and Technologies; Littlewood, J., Howlett, R.J., Jain, L.C., Eds.; Springer: Singapore, 2021; Volume 203. [Google Scholar]
- NaCTSO-National Counter Terrorism Security Office. Crowded Places Guidance; NaCTSO-National Counter Terrorism Security Office: London, UK, 2017. [Google Scholar]
- Federal Emergency Management Agency. Risk Management Series. Handbook for Rapid Visual Screening of Buildings to Evaluate Terrorism Risks (FEMA 455); Federal Emergency Management Agency: Washington, DC, USA, 2009. [Google Scholar]
- Bernardini, G.; Quagliarini, E.; D’Orazio, M. Grandi eventi e terrorismo: La progettazione consapevole della sicurezza delle persone. Antincendio 2017, 12, 12–28. [Google Scholar]
- GSA. The Site Security Design Guide; 2007. Available online: https://www.gsa.gov/real-estate/design-construction/urban-developmentgood-neighbor-program/good-neighbor-resources/policy-guides (accessed on 22 July 2020).
- Federal Emergency Management Agency. Buildings and Infrastructure Protection Series. Reference Manual to Mitigate Potential Terrorist Attacks Against Buildings (FEMA-426/BIPS-06), 2nd ed.; Federal Emergency Management Agency: Washington, DC, USA, 2011.
- Coaffee, J.; Fussey, P. Constructing resilience through security and surveillance: The politics, practices and tensions of security-driven resilience. Secur. Dialogue 2015, 46, 86–105. [Google Scholar] [CrossRef]
- Peleson, M. Progettare contro il terrorismo. L’architettura Della Sicurezza. Anal. Anal. Sicur. 2019. (In Italian). Available online: https://www.analisidifesa.it/wp-content/uploads/2018/11/arch-sicu-3.pdf (accessed on 22 July 2020).
- Karlos, V.; Larcher, M.; Solomos, G. Review on vehicle barrier protection guidance. JRC Sci. Policy Rep. 2017. [Google Scholar] [CrossRef]
- Federal Emergency Management Agency. FEMA 430: Site and Urban Design for Security: Guidance Against Potential Terrorist Attacks; Federal Emergency Management Agency: Washington, DC, USA, 2007. [Google Scholar]
- Coaffee, J. Beyond Concrete Barriers Innovation in Urban Furniture and Security in Public Space; GCDN Commissioned Research, 2018; Available online: https://gcdn.net/wp-content/uploads/2018/01/GCDN-Urban-Furniture-Study-A4-FINAL-highres_web.pdf (accessed on 22 July 2020).
- Australian Institute for Resilience Disaster. Safe and Healthy Crowded Places Handbook. Aust. Disaster Resil. Handb. Collect. 2018, 15. Available online: https://www.police.sa.gov.au/__data/assets/pdf_file/0003/582240/safe-and-healthy-crowded-places-handbook.pdf (accessed on 22 July 2020).
- Ministero dell’interno. Circolare del 18 Luglio 2018-Modelli Organizzativi e Procedurali per Garantire alti Livelli di Sicurezza in Occasione di Manifestazioni Pubbliche; Gabinetto del Ministero dell'interno: Rome, Italy, 2018. (In Italian) [Google Scholar]
- US department of Homeland Security. Planning Considerations: Complex Coordinated Terrorist Attacks; 2018. Available online: https://www.fema.gov/sites/default/files/2020-07/planning-considerations-complex-coordinated-terrorist-attacks.pdf (accessed on 22 July 2020).
- Estrada, M.A.R.; Koutronas, E. Terrorist attack assessment: Paris November 2015 and Brussels March 2016. J. Policy Model. 2016, 38, 553–571. [Google Scholar] [CrossRef]
- Li Piani, T. Progettazione strutturale e funzione sociale dello spazio (quale) vulnerabilità e soluzione al terrorismo urbano. In Sicurezza, Terrorismo E Società-International Journal-Italian Team for Security, Erroristic Issues & Managing Emergencies; Educatt - Università Cattolica del Sacro Cuore: Milan, Italy, 2018; pp. 7–15, (In Italian). ISSN 2421-4442. [Google Scholar]
- Federal Emergency Management Agency. Risk Management Series. Safe Rooms and Shelters. Protecting People Against Terrorist Attacks (FEMA 453); Federal Emergency Management Agency: Washington, DC, USA, 2006.
- Ghazi, N.M.; Abaas, Z.R. Toward liveable commercial streets: A case study of Al-Karada inner street in Baghdad. Heliyon 2019, 5, e01652. [Google Scholar] [CrossRef]
- Templeton, A.; Drury, J.; Philippides, A. Placing Large Group Relations into Pedestrian Dynamics: Psychological Crowds in Counterflow. Collect. Dyn. 2020, 4, A23. [Google Scholar] [CrossRef]
- Sommer, M.; Njå, O.; Lussand, K. Police officers’ learning in relation to emergency management: A case study. Int. J. Disaster Risk Reduct. 2017, 21, 70–84. [Google Scholar] [CrossRef]
- Abreu, O.; Cuesta, A.; Balboa, A.; Alvear, D. On the use of stochastic simulations to explore the impact of human parameters on mass public shooting attacks. Saf. Sci. 2019, 120, 941–949. [Google Scholar] [CrossRef]
- Ministère de l’Intérieur, Ministère de la Culture et de la Communication; Secrétariat Général de la Défense et de la Sécurité Nationale. Gérer la Sureté et la Sécurité Des Événements et Sites Culturels; 2017. Available online: https://www.culture.gouv.fr/Espace-documentation/Rapports/GERER-LA-SURETE-ET-LA-SECURITE-DES-EVENEMENTS-ET-SITES-CULTURELS (accessed on 22 July 2020).
- Festag, S. Counterproductive (safety and security) strategies: The hazards of ignoring human behaviour. Process. Saf. Environ. Prot. 2017, 110, 21–30. [Google Scholar] [CrossRef]
- Bruyelle, J.-L.; O’Neill, C.; El-Koursi, E.-M.; Hamelin, F.; Sartori, N.; Khoudour, L. Improving the resilience of metro vehicle and passengers for an effective emergency response to terrorist attacks. Saf. Sci. 2014, 62, 37–45. [Google Scholar] [CrossRef]
- Wang, J.; Ni, S.; Shen, S.; Li, S. Empirical study of crowd dynamic in public gathering places during a terrorist attack event. Phys. A Stat. Mech. Appl. 2019, 523, 1–9. [Google Scholar] [CrossRef]
- Wang, C.; Wang, J. Risk-Field Based Modeling for Pedestrian Emergency Evacuation Combined with Alternative Route Strategy. Math. Probl. Eng. 2017, 2017, 1–10. [Google Scholar] [CrossRef]
- Liu, Q. A social force approach for the defensive strategy of security guards in a terrorist attack. Int. J. Disaster Risk Reduct. 2020, 46, 101605. [Google Scholar] [CrossRef]
- Manley, M.; Kim, Y.S.; Christensen, K.; Chen, A. Airport Emergency Evacuation Planning: An Agent-Based Simulation Study of Dirty Bomb Scenarios. IEEE Trans. Syst. Man. Cybern. Syst. 2016, 46, 1390–1403. [Google Scholar] [CrossRef]
- Chen, C.; Tong, Y.; Shi, C.; Qin, W. An extended model for describing pedestrian evacuation under the threat of artificial attack. Phys. Lett. A 2018, 382, 2445–2454. [Google Scholar] [CrossRef]
- Liu, Q. A social force model for the crowd evacuation in a terrorist attack. Phys. A Stat. Mech. Appl. 2018, 502, 315–330. [Google Scholar] [CrossRef]
- Şahin, C.; Rokne, J.; Alhajj, R. Human behavior modeling for simulating evacuation of buildings during emergencies. Phys. A Stat. Mech. Appl. 2019, 528, 121432. [Google Scholar] [CrossRef]
| General Classification Criteria (Section Number) | Main Classification Options | Differences in RMRSs | Main References |
|---|---|---|---|
| Target-oriented (Section 2.2.1) | Hard/soft target | Based or not based on restricted access control, invasive surveillance and strongly protected BE border limits | [10,11,18] |
| Level of (in)visibility | Perception by the BE users due to the level of implementation in the BE | [8] | |
| BE main intended use | Differences of operational procedures in BE use and BE configuration due to the normal use by occupants and stakeholders | [13,42,43] | |
| Safety/security | Limiting failures and protecting the public versus limiting intentional damages and protecting the public order | [7,44] | |
| Attack-oriented (Section 2.2.2) | Threat type | Where/from where the attack is performed by the terrorists | [43] |
| Typology of attack | Facing the effects of weapons used by the assaulters | [10,19,35,42] | |
| Time-dependent (Section 2.2.3) | Before/during | Effectiveness before the attack (e.g., to deter it) or during it (e.g., to manage the consequences) | [35] |
| Space-dependent (Section 2.2.4) | Different zones (layer of defence) of the BE | Area/line of application of the strategy in the BE layout in respect to the surrounding and internal elements | [44,45,46] |
| Physical versus Management (Section 2.2.5) | physical/management | Implemented into physical elements of the BE or by using operational procedures (based on staff actions) | [13,32,42] |
| High Visibility | Integrated | Invisible | |
|---|---|---|---|
| ACTIVE MEASURES |
|
| N.A. |
| PASSIVE MEASURES |
|
|
|
| BE Classification | Examples of Intended Uses | Related Main RMRSs |
|---|---|---|
| Public spaces | commercial (mainly, great shopping centres), sporting (stadia, arenas and playgrounds in general, both indoor and outdoor); | Closely combined with those related to additional safety fields, i.e., fire safety and workers’ safety and health, especially for those hosted by buildings in the BE |
| entertainment (e.g., theatres, cinemas); | ||
| accommodation facilities (e.g., hotels) | ||
| restaurants and bars/pubs | ||
| BEs hosting mass gathering events or possible crowd conditions (both indoor and outdoor, e.g., pedestrian areas) | ||
| BEs for the community, having also a symbolic feature as a terrorist target | BEs for education (mainly, schools) | Grouped in with similar crowd conditions and partially controlled access systems (e.g., depending on the different areas of the BE, such as for schools or hospitals), and also correlated to RMRSs for public spaces |
| BEs for religion (e.g., churches, temples) | ||
| healthcare centres (e.g., hospitals) | ||
| BEs for transportation | public spaces for transportation (e.g., airports, train stations, harbours) | Possibility of areas with restricted access and also need to coordinate the RMRSs by contemporarily involving the BE occupants’ and passengers’ (onboard the means of transport) safety, the modelling of specific damage and injuries due to the transportation hub typology, and the business continuity elements |
| the means of transport themselves | ||
| Other BEs (almost private ones) | BEs as working places | Low complexity strategies thanking the possibility of access control in the areas, thus intervening in specific elements of the BE or in management issues (also compare with Section 2.2.4 classification) |
| residential buildings |
| GTD Classification (Modus Operandi) | Attack Typologies | Specifications | Terms of the Effects | |
|---|---|---|---|---|
| Short | Long | |||
| Bombing/Explosion | Bombing attack | Explosive devices (including Improvised Explosive Devices—IDEs), directly placed in the BE; car bomb (parked); suicide bombing attack and car bomb driven by a suicide attacker running into the target, based on the terrorist’s actions in the BE; bomb delivered by mail | x | x |
| Armed Assault | Armed assault (pistol, machine gun and so on) | It implies one or more active shooters (including sniper’s assault), and which lead to an assassination | x | |
| Attack with a cold weapon (e.g., knife) | By one or more active terrorists | x | ||
| Vehicle running into the target | It could be performed in open spaces in the BE or towards the BE elements perimeter | x | ||
| Arson | It can be essentially fought by combining RMRSs with fire safety strategies | x | x | |
| Unmanned aircraft systems | It can be used to perform direct attacks as well as to support the use of other weapons or to collect information before an attack | x | ||
| Chemical, Biological and Radiological (CBR) attacks | It can be performed in different ways, as for bombing attack-related ones | x | ||
| Barricade Incident; Kidnapping; Hijacking | Hostage-taking and barricade situations | In transportation BEs, also hijacking | x | |
| Unarmed Assault | Crowd attack to a soft target | Such as in case of insurrections | x | |
| Facility/Infrastructure Attack | Facility attacks | It can compromise the functionality of a BE by limiting/affecting the state of their infrastructural elements (e.g., water or electrical supply, cyberterrorism towards the BE facilities), thus provoking not only physical damages but also economic and social ones | x (disruption) | |
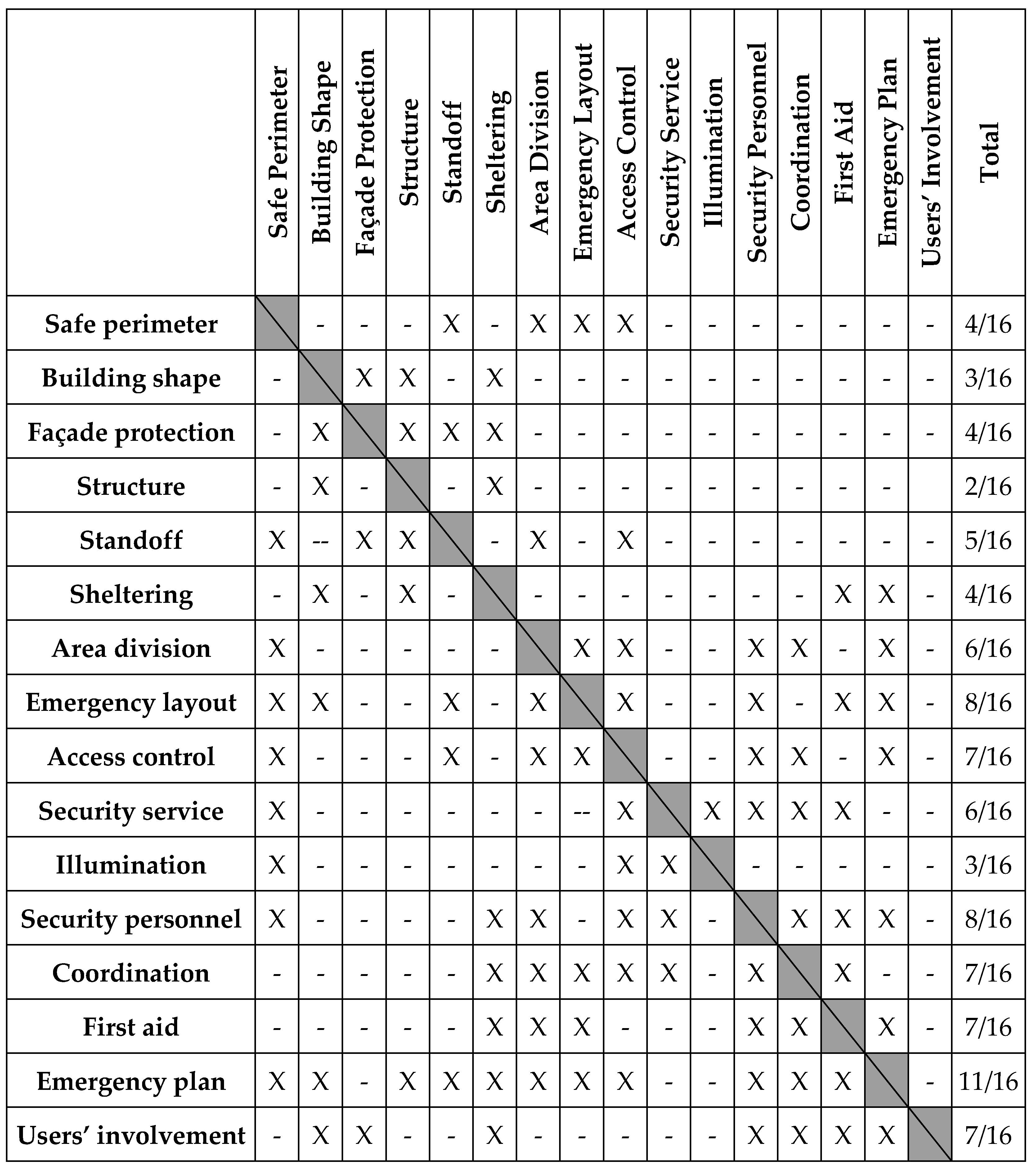
| RMRS | Redundancy about Attack Typology and Source (External/Internal) | Applicability to Indoor, Outdoor, Both | Coordination with Other RMRSs | Adaptable for Existing BE | Main Application Context (Intended Use; Overcrowding) | Costs |
|---|---|---|---|---|---|---|
| Design of the physical elements of the BE | ||||||
| Safe perimeter | 2/10—external | Outdoor: around buildings and specific targets, or to circumscribe areas in a wider open space | 4/16 | Adaptable, through punctual installations | For hard targets, because of its complexity level | Depending on adopted technologies and BE perimeter length |
| Building shape | 4/10—external/internal | Principally outdoor but specific measures (i.e., escape routes, shelters) are adaptable in indoors as well | 3/16 | Not adaptable | Specific for public buildings with a high number of visitors | Sustainable for new BEs or full BE elements renewal |
| Façade protection | 2/10 | Protecting single buildings | 4/16 | Generally, solutions are related to new facades (which can alter the aspects of the original elements). Interventions on existing openings have a lower impact. | Specific for public buildings with a high number of visitors | New reinforced facades can be put in place with limited costs (depending on the building typology). Interventions on existing openings are encouraged due to their lower costs with respect to the protection increase advantages. |
| Structure | 1/10 | Indoor: relative to building’s structural system | 2/16 | Preservation of historic buildings could be affected, unless there are focused interventions | Encouraged only for institutional public buildings with many visitors | Depending on intervention type, structural typology and building dimensions |
| BE layout | ||||||
| Standoff | 2/10 | Distances applied to the outdoors can be adapted for some indoor conditions | 5/16 | Possible massive impact, if applied together with Safe Perimeter. Otherwise, adaptable to the historical layout using management actions. | Specific for strategic buildings but extendable to soft targets with visitors and temporary mass gatherings | Depending on land use issues to guarantee the distances in case of new constructions. In existing BEs, costs concern the space use management |
| Sheltering | 6/10 | Shelters can be placed inside buildings or constitute a safe area in the outdoor BE | 4/16 | Adaptable if limited to the definition of shelter areas and their accessibility (management issues); incompatible considering interventions on building facades and structures. | Considering attacks to single and strategic buildings with something/someone to protect | Low costs if limited to existing shelter areas; elevated cost otherwise |
| Area division | 5/10 | Both | 6/16 | The adaptability is related to the area configuration and dimension | Specific for mass gathering events in open spaces | Low costs associated with physical solutions (e.g., open space perimeter), but management and operational issues should be evaluated (e.g., organizing activities in the spaces and their relation; access controls) |
| Emergency layout | 5/10 | Outdoor or within strategic buildings and hard targets | 8/16 | Adaptable for each situation | Adaptable in each event typology | Depending on the extension of the emergency area in relation to the BE activities |
| RMRS | Redundancy about Attack Typology and Source (External/Internal) | Applicability to Indoor, Outdoor, Both | Coordination with Other RMRSs | Adaptable for Existing BE | Main Application Context (Intended Use; Overcrowding) | Costs |
|---|---|---|---|---|---|---|
| Access control and surveillance in the BE | ||||||
| Access control | 7/10 | Applicable to circumscribed areas in open spaces/inside abuilding | 7/16 | Adaptable for existing BE because of the possibility to circumscribe areas (i.e., outdoor perimeter) | Adaptable for events with considerable crowding conditions (mass gathering events) | Depending on the number of access/control points and to the employed technologies/personnel |
| Security service | 6/10 | Employable in indoor and outdoor conditions | 6/16 | Adaptable for existing (including historical) BEs through not invasive installations | Adaptable to private and public buildings, and also in open spaces and mass gatherings | Depending on the BE dimension to monitor and on the adopted technologies |
| Illumination | 4/10 | For outdoor spaces; in indoor, mainly for scarce luminance condition of buildings | 3/16 | Adaptable for existing (including historical) BEs with possible restrictions at technological level (e.g., systems integration/installation) | Adaptable both to private and public buildings, both in open spaces and mass gatherings | Depending on the number of installed devices, and their operational and maintenance issues |
| Safety and security management in the BE | ||||||
| Security personnel | 7/10 | Employable in indoor and outdoor conditions | 8/16 | Adaptable in each condition | Personnel could support an emergency in whatever building. It is strongly recommended in mass gathering events, especially outdoors | Depending on building dimension and floors. In mass gatherings, depending on event area extension and number of participants |
| Coordination | 10/10 | Always recommended | 7/16 | Not dependent on the BE typology | Necessary in each case; it requires special consideration for some hard targets or mass gathering events | Low-cost improvement of performances is possible, but costs could be related to the employed technology |
| First aid | 9/10 | Always needed; support from external rescuers’ actions | 7/16 | Adaptable in each condition | Mandatory for mass gathering and in hard targets of the BE | Low costs by considering the direct possibility to save lives |
| Emergency plan | 10/10 | Always needed | 11/16 | Adaptable in each condition | Recommended in any cases, especially in mass gathering events and in hard targets of the BE | Depending on management and operational phases; they could be elevated considering case by case (e.g., cost of personnel considering their number) |
| Users’ involvement | 10/10 | Users should be involved in the same manner for both indoor and outdoor scenarios. However, the provided data will be different | 7/16 | Not dependent on the BE typology | Users should be formed to face disaster both in BE normal use and in case of events with overcrowding conditions | Financing informative campaign can be considered as an investment on citizen safety; costs for users’ involvement are also related to evacuation guiding tools for mobile devices (e.g., apps) |
| RMRS | Interactions with Behavioural Issues | Perceived as Reliable and Slightly Invasive for Citizens | Employable for Mass Gathering Conditions | Possibility to Be Represented in Crowd Evacuation Simulators |
|---|---|---|---|---|
| Design of the physical elements of the BE | ||||
| Safe perimeter | Barriers should be designed by considering the users’ perception and the behaviours in an emergency (e.g., in evacuation), being correlated to emergency layout and plan strategies | Barriers offer a reliable perception, while their invasive aspect or not depends on their different typology | Emergency layout elements (e.g., gathering areas/evacuation paths) can be additionally protected by such measures | The BE geometry and obstacles for attackers can be represented in a virtual environment. Moreover, such data can also influence the pedestrians’ evacuation dynamic |
| Building shape | By constituting temporary shelters, hiding places, and recovery areas | Not generally invasive since it is still included within the general architectural features of the BE | N.A. | Plan geometry of each building in the simulated BE |
| Façade protection | N.A. | Not generally invasive if related to new constructions but it could be in the case of intervention on an existing building in relation to the employed technology | N.A. | Effects (i.e., damages) of the attack on the BE elements |
| Structure | N.A. | N.A. | N.A. | Attack damages reduction possibility on buildings |
| BE layout | ||||
| Standoff | N.A. | It could be perceived as a negative element in relation to area division, due to the modification/definition of the particular fruition mode of the BE | Standoff distances in the positioning of hazardous facilities or equipment | Plan geometry of the BE |
| Sheltering | Shelters are designed considering users safety and eventual necessities during the emergency | Yes | Safe areas should be predisposed where to direct the evacuation | Safe places play an attractiveness role where to refuge |
| Area division | Area division is defined in the function of crowd dynamics and human behaviours | Area division is often heavily perceived with a negative impact | Area division is mandatory in some regulations in relation to the entity of the event | Plan geometry of the BE, maximum crowd capacity, main intended use and related hosted users’ typologies/activities affecting the evacuees’ behaviours |
| Emergency layout | The emergency layout is planned by considering the supposed number of users, their typologies and their behaviours (e.g., by using evacuation simulators) | Users should be aware of the safety measures and emergency facilities | The emergency layout is strongly recommended, especially in mass gathering events, because of the higher impact of crowd conditions on the emergency (i.e., evacuation) process | Input data for the environment definition (e.g., available evacuation paths, safe areas according to the emergency plan) |
| RMRS | Interactions with Behavioural Issues | Perceived as Reliable and Slightly Invasive for Citizens | Employable for Mass Gathering Conditions | Possibility to be Represented in Crowd Evacuation Simulators |
|---|---|---|---|---|
| Access control and surveillance in the BE | ||||
| Access control | Access control is aimed to discourage the attackers | Access control could be strongly invasive in relation to employed tools and users’ fruition modes (e.g., because of access timing) but perceived as a positive protective measure | It is strongly recommended or mandatory in relation to the event entity | As an element to control input data related to the simulated pedestrian’s presence in the environment |
| Security service | Employable to discourage attackers and to detect suspected behaviours | The solution can be visible or invisible depending on the employed technology generally perceived as positive | Video Surveillance could give an important contribution to monitoring the situation in mass gatherings | Integration of monitoring tools in the emergency to simulate “intelligent” solutions application (i.e., input data for emergency detection and evacuation management) |
| Illumination | Employable to discourage attackers and to detect suspected behaviours | A visible solution, non-invasive and perceived as positive | Necessary for control and emergency purposes (access/egress points and emergency facilities), but it should be compatible with specific events (e.g., entertainment with specific illumination requirements) | Effects of illumination degree on the motion of individuals and on the selection of specific paths, also during the emergency and evacuation process |
| Safety and security management if the BE | ||||
| Security personnel | Employable to discourage attackers and to intervene in case of suspected behaviours | A visible solution, non-invasive and perceived as positive | It is strongly recommended or mandatory that its number depends on the amount of hosted people | Personnel constitute a source of instructions able to modify pedestrian’s evacuation |
| Coordination | N.A. | N.A. | The efficiency of emergency response is sensibly improved | Simultaneous and coordinated employment of different countermeasures |
| First aid | Adequate to users’ typologies and number | Solution perceived as positive. Generally also visible before the emergency. | It is strongly recommended or mandatory in case of mass gatherings | Representable as a reduction in victims’ amount and as rescuers’ motion towards specific areas |
| Emergency plan | Emergency plans should be developed by considering possible human behaviours and actions (e.g., by using evacuation simulators) | It should be known by the users | It is strongly recommended or mandatory in relation to the event entity | It can constitute the amount of data that can be assessed preventively and considered as an input to the emergency simulation |
| Users’ involvement | Indications issued to users should be related to their spontaneous reactions performed in hazard situations | People that know what to do in case of emergency will feel safer | Users’ proper behaviour could support the evacuation decisions from a bottom-up approach, to support the rescuers and the emergency staff | Capabilities of the users to perform right behaviours |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2021 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Quagliarini, E.; Fatiguso, F.; Lucesoli, M.; Bernardini, G.; Cantatore, E. Risk Reduction Strategies against Terrorist Acts in Urban Built Environments: Towards Sustainable and Human-Centred Challenges. Sustainability 2021, 13, 901. https://doi.org/10.3390/su13020901
Quagliarini E, Fatiguso F, Lucesoli M, Bernardini G, Cantatore E. Risk Reduction Strategies against Terrorist Acts in Urban Built Environments: Towards Sustainable and Human-Centred Challenges. Sustainability. 2021; 13(2):901. https://doi.org/10.3390/su13020901
Chicago/Turabian StyleQuagliarini, Enrico, Fabio Fatiguso, Michele Lucesoli, Gabriele Bernardini, and Elena Cantatore. 2021. "Risk Reduction Strategies against Terrorist Acts in Urban Built Environments: Towards Sustainable and Human-Centred Challenges" Sustainability 13, no. 2: 901. https://doi.org/10.3390/su13020901
APA StyleQuagliarini, E., Fatiguso, F., Lucesoli, M., Bernardini, G., & Cantatore, E. (2021). Risk Reduction Strategies against Terrorist Acts in Urban Built Environments: Towards Sustainable and Human-Centred Challenges. Sustainability, 13(2), 901. https://doi.org/10.3390/su13020901






