1. Introduction
With the swift evolution of contemporary communication technology toward intelligent and diversified development, the battlefield electromagnetic environment has become progressively complex [
1]. Serving as a core approach to interrupt enemy command connections and attain military operational advantages, communication jamming has evolved into a key research focus within the field of electronic warfare. Miniaturized and distributed jammers, leveraging their advantages of low power consumption, flexible deployment, and strong concealment, have demonstrated enormous application potential in scenarios such as regional communication countermeasures and UAV swarm communication suppression, becoming a research hotspot [
2]. However, in strong electromagnetic interference (EMI) environments, high noise and unstable channels exacerbate the difficulty of jamming resource scheduling—networked collaboration among jammers is prone to interruption, making it challenging to obtain global jamming effect feedback. This results in distributed jamming resources failing to form effective synergy, and the system’s operational duration struggling to meet practical combat requirements [
3]. Therefore, how to achieve efficient scheduling of distributed jamming resources in strong electromagnetic interference environments, accomplish collaborative jamming objectives, and extend the system’s continuous operational time has become a crucial issue requiring urgent solutions.
Traditional centralized communication jamming resource scheduling methods pursue maximum jamming effectiveness by optimizing parameters such as jamming power, frequency bands, and time windows [
4]. Nevertheless, such methods exhibit significant limitations in modern adversarial communication environments. On one hand, the central decision-making unit is vulnerable to becoming a high-value target for enemy attacks, leading to insufficient system robustness [
5]. On the other hand, real-time collection and feedback of global channel state information (CSI) incur non-negligible latency and communication overhead, failing to meet the millisecond-level jamming response requirements in dynamic channel environments [
6]. Furthermore, the computational complexity and communication load of centralized methods grow superlinearly with the number of jamming nodes, conflicting with the practical demands of lightweight and distributed deployment of electronic warfare systems [
7]. This renders them inapplicable in dynamic, heterogeneous, and anti-destruction communication countermeasure scenarios.
Current research on distributed radar jamming resource scheduling has achieved certain progress. It enhances jamming effectiveness against radar systems through means such as joint antenna scheduling and power allocation, intelligent decision-making under the cognitive electronic warfare framework, and optimization of cooperative jamming strategies [
8,
9,
10,
11,
12,
13,
14,
15,
16,
17]. However, fundamental differences exist between radar jamming and communication jamming in core objectives, operational principles, evaluation metrics, and resource constraints: radar jamming aims to suppress or deceive radar detection, while communication jamming focuses on disrupting information transmission over communication links. The channel models, signal modulation methods, and effectiveness evaluation criteria of the two are completely distinct, resulting in the inability to directly migrate research achievements from distributed radar jamming to communication jamming scenarios [
18].
As a cutting-edge interdisciplinary field integrating electronic warfare and wireless communication, distributed communication jamming resource scheduling has evolved from early static, centralized, and single-point confrontation models to a complex systems engineering oriented towards space-air-ground integration, multi-agent collaboration, dynamic game theory, and real-time learning. Current research exhibits distinct characteristics of high interdisciplinarity, strong technological integration, and stringent practical combat constraints. Its development trend can be systematically analyzed from three dimensions: theoretical paradigms, technical paths, and practical challenges.
At the theoretical paradigm level, the research focus is undergoing a profound transition from “optimization-driven” to “learning-driven” and “game-driven”. Traditional methods, such as master-slave parallel scheduling based on genetic algorithms [
18], adaptive scheduling using the Improved Sparrow Search Algorithm (ISSA) [
10], and hyper-heuristic fuzzy multi-attribute evaluation models [
19], while engineering feasible in specific scenarios, are generally limited by inherent flaws such as strong dependence on CSI, high computational complexity, and weak generalization ability. In stark contrast, new paradigms centered on game theory and multi-agent reinforcement learning (MARL) have become mainstream. A systematic review in [
20] points out that zero-sum games, Stackelberg games, and Bayesian game frameworks have been widely used to model strategic interactions between jammers and communicating parties. MARL, through autonomous exploration and strategy convergence of distributed agents, achieves local optimality and system synergy without the need for global information. Notably, cutting-edge developments have transcended the improvement of single algorithms and advanced toward building a “cognition-decision-execution” closed loop: as an example, the Transformer and deep reinforcement learning-based cognitive communication jamming strategy introduced in [
21] integrates spectrum sensing, modulation identification with jamming action formulation. Ref. [
22] fuses multi-domain information (space, spectrum, power, time) through evolutionary reinforcement learning to address challenges such as multi-modal objective functions and complex constraints in multi-radar-multi-jammer countermeasures. This signifies that the field has entered a new phase centered on “autonomous evolution of intelligent agents”.
Global research on military communication countermeasures and resource scheduling has also achieved in-depth breakthroughs in recent years, with relevant studies focusing on the integration of new communication architectures, intelligent optimization algorithms and anti-jamming technologies for in-depth exploration [
23,
24,
25]. For 5G and beyond military communication systems, the technical characteristics of high speed, low latency, and high reliability impose more stringent requirements on the anti-jamming performance and resource scheduling efficiency of jamming systems, and the unique environmental adaptability requirements of military communications make distributed jamming resource scheduling schemes face more complex practical constraints [
24,
26]. In terms of jamming strategy design, related research has realized the improvement of communication secrecy and anti-jamming performance through power optimization and control jamming strategies, and verified the effectiveness of jamming power allocation in heterogeneous communication networks such as SWIPT-NOMA, providing a valuable reference for the power scheduling design of distributed jamming systems [
27]. At the theoretical algorithm level, the fusion of game theory and multi-agent reinforcement learning has become a mainstream research direction to solve distributed resource scheduling problems, and evolutionary dynamics and Nash equilibrium theory have been effectively applied to the strategy optimization of multi-agent jamming systems, laying an important theoretical foundation for the design of distributed jamming resource scheduling algorithms [
28]. In the field of extreme bandwidth communication, systematic analysis has been conducted on the jamming intrusion characteristics and countermeasure strategies of key 6G technologies such as millimeter wave and terahertz, and the unique jamming vulnerabilities of new communication technologies and corresponding anti-jamming technical systems have been summarized [
25]. However, research on distributed jamming resource scheduling for 600 MHz UHF band tactical air-ground communication remains relatively scarce, and the design of lightweight and autonomous scheduling algorithms for strong electromagnetic interference environments is still an urgent open problem in global research. This study thus fills the research gap in this field, and the proposed algorithm framework provides a feasible solution for the efficient scheduling of distributed jamming resources in 600 MHz UHF band tactical air-ground communication scenarios.
At the technical path level, core breakthroughs are concentrated in two major directions. Firstly, distributed collaborative architectures have become key to addressing the scalability of large-scale networks. For distributed jamming networks composed of heterogeneous nodes such as Unmanned Aerial Vehicle (UAV) clusters, Low Earth Orbit (LEO) satellites, and ground stations, researchers no longer pursue centralized global optimality but emphasize low-overhead consensus and robust collaboration among nodes. Ref. [
29] thoroughly analyzes the beamforming power attenuation caused by positioning and latency errors in UAV distributed arrays during cooperative jamming; ref. [
30] optimizes LEO satellite downlink distributed jamming using the Non-dominated Sorting Genetic Algorithm (NSGA-II), balancing coverage and energy efficiency; and research on large-scale network control in [
31] provides scalability theoretical support for the application of distributed AI in jamming scheduling. Secondly, robustness and uncertainty management have been elevated to an unprecedented level. Real electromagnetic environments are highly dynamic and partially observable. Therefore, relevant Joint Antenna Scheduling and Power Allocation (JASPA) schemes [
8] and Anti-Deception Jamming Joint Radar-Target Assignment and Power Scheduling (ADJ-JRAPS) [
9] directly embed deception parameters and target motion uncertainties into state estimation and optimization objectives; some studies in [
32] specifically focus on how to utilize unused pilots for robust channel estimation and jamming detection under random pilot jamming attacks.
Nevertheless, severe challenges persist. The primary challenge is achieving low-overhead consensus: in distributed networks with limited bandwidth and unstable links, designing lightweight communication protocols to enable massive jamming nodes to complete strategy synchronization within milliseconds remains an open problem. Secondly, the NP-hard nature of joint jamming-communication optimization has not been fundamentally resolved. Existing algorithms still face issues such as slow convergence and susceptibility to local optima under large-scale and multi-constraint conditions. Thirdly, the generalization ability in real electromagnetic environments is insufficient: most algorithms perform well in idealized simulation environments but experience significant performance degradation when confronted with complex multipath, time-varying fading, and unknown jamming patterns, lacking unified and authoritative evaluation benchmarks and test platforms. These challenges, combined with the incompleteness, lag, and ambiguity of information perception by jammers in strong electromagnetic environments [
3], as well as the localized and differentiated environmental perception characteristics of airborne and ground jammers due to spatial layout differences [
33], further highlight the inadequate adaptability of existing methods in non-networked distributed jamming collaborative scheduling. The imperfection of the jamming effectiveness evaluation system exacerbates this predicament.
In terms of jamming effectiveness evaluation, traditional metrics such as J/S and jamming success rate exhibit poor applicability when directly migrated to distributed scenarios [
34]. The former pursues full suppression of the received power of all communication nodes, causing some jammers to operate continuously at high intensity and resulting in uneven battery consumption [
35]. The latter only counts the number of successful jamming instances after jamming ends, without constraining power consumption during the jamming process, which easily leads to rapid battery depletion of jammers in critical positions and failure to achieve sustained effective jamming [
36]. Additionally, forcing all jammers to share global information for scheduling would significantly increase communication overhead, making it difficult to implement in harsh communication scenarios.
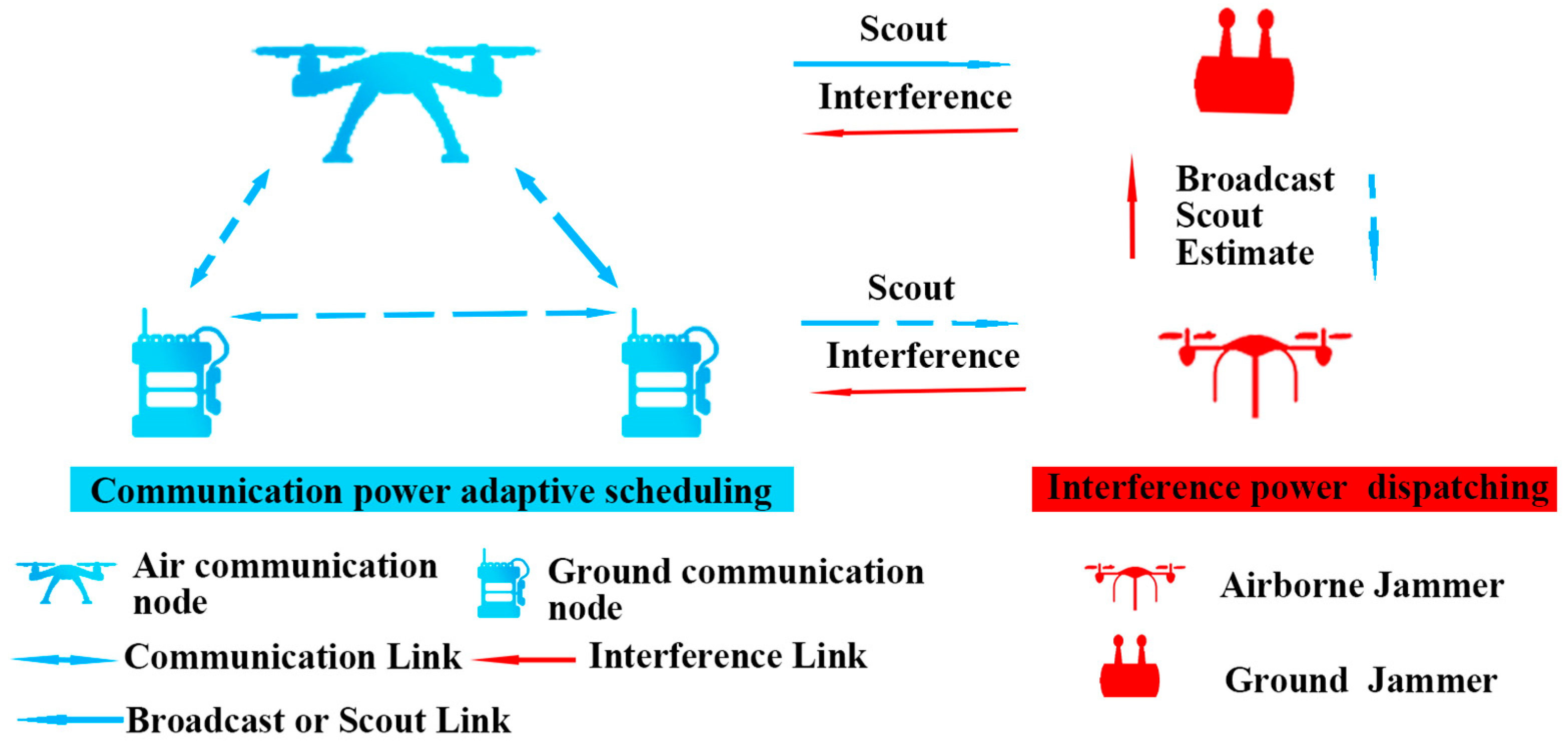
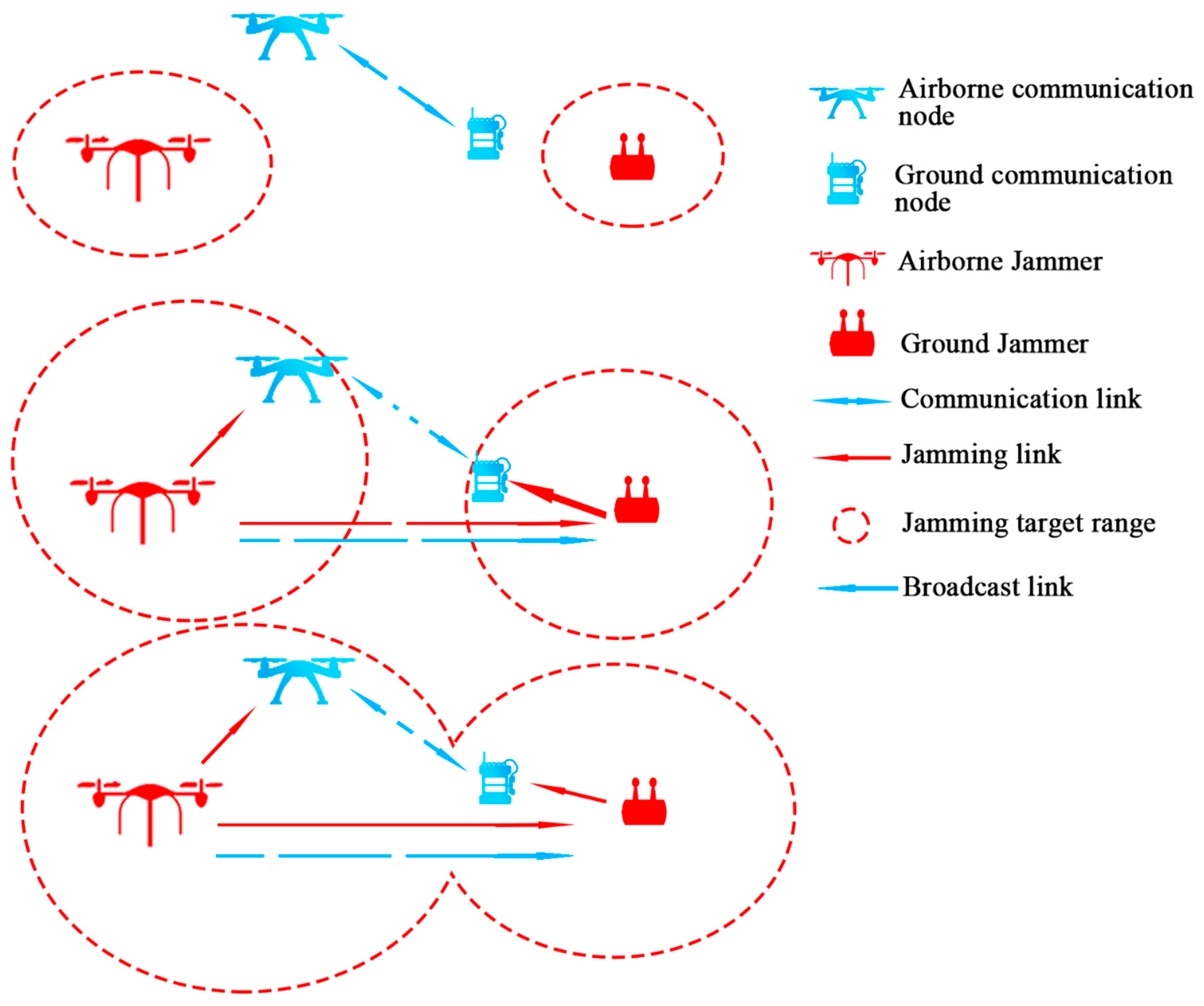
To address the aforementioned issues, this paper focuses on distributed communication jamming resource scheduling in strong electromagnetic interference environments. It establishes a mathematical model for air–ground joint communication countermeasures, proposes the constraint condition of “overall limited jamming” and the evaluation index of “multistage J/S”, and designs the CCBA along with supporting collaborative strategies to achieve efficient scheduling of jamming resources and significantly extend system operational duration.
The main contributions of this paper are as follows:
A mathematical model for air–ground joint communication countermeasures in strong electromagnetic interference environments is established, and the constraint condition of “overall limited jamming” is proposed. Under the premise of ensuring an overall degradation in communication network quality, it provides flexible space for jamming resource scheduling, effectively saves jammer power, and adapts to the power constraint characteristics of distributed jammers. In the scenario setup of this paper, a strong EMI environment is defined as a condition with ground noise ≥ −95 dBW, low-altitude noise ≥ −105 dBW, and a jammer disconnection rate ≥ 60%; a weak EMI environment is defined as ground noise < −105 dBW, low-altitude noise < −115 dBW, and a jammer disconnection rate < 30%.
A “multistage J/S” analysis and evaluation index is proposed. Targeting the three types of communication antennas (vehicle-mounted, elevated, and UAV-lifted) of communication nodes, it refines the effectiveness analysis dimensions of the communication countermeasure process, more reasonably characterizes jamming effects and resource scheduling algorithm characteristics, and addresses the insufficient applicability of traditional evaluation metrics.
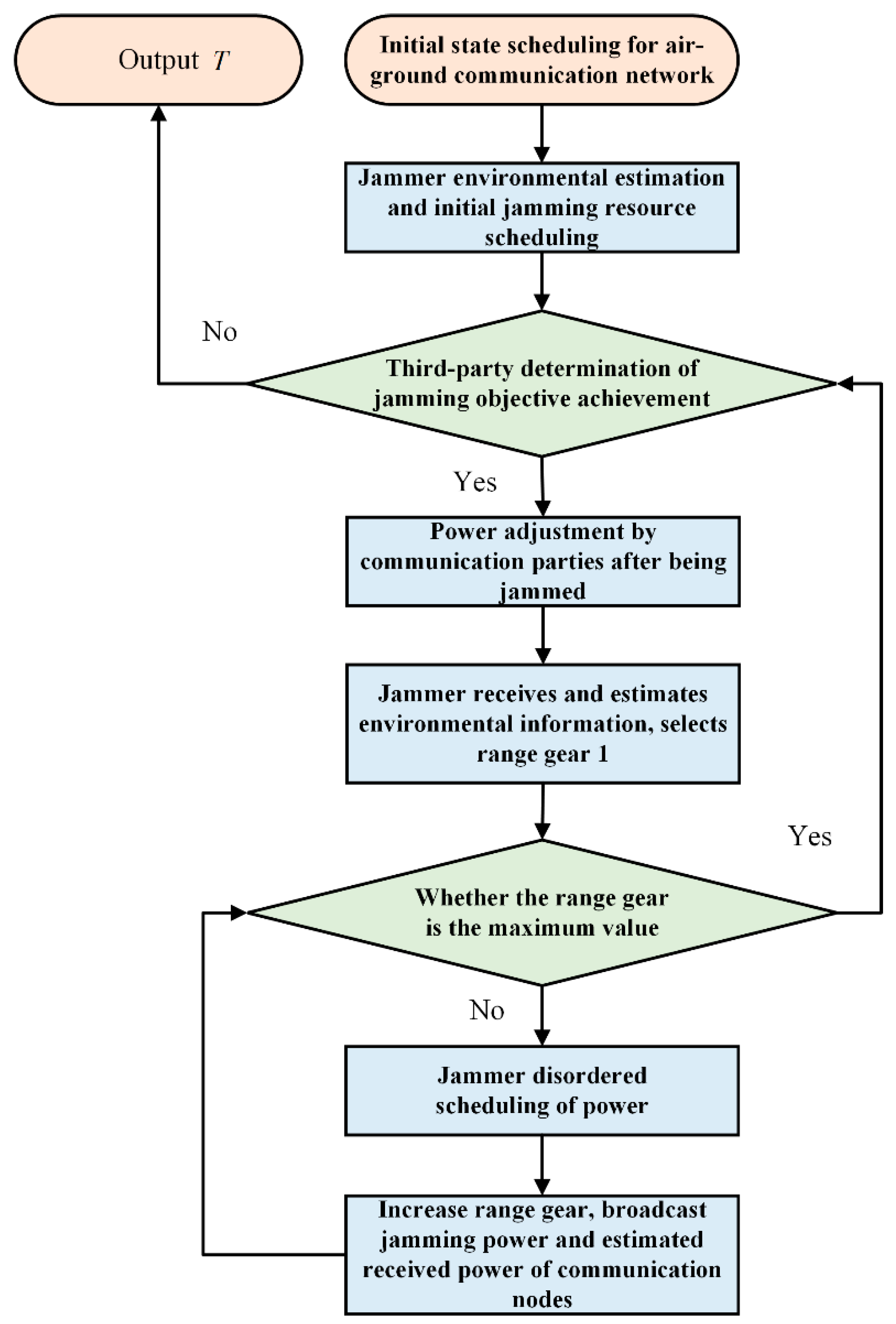
The CCBA is designed. Aiming at the difficulty of networked collaboration in strong electromagnetic interference environments, it integrates strategies such as concentric circle broadcast collaboration, electromagnetic environment estimation, and limited random power scheduling to achieve balanced scheduling of scattered jamming resources. While extending system operational duration, it stably achieves the jamming target of reducing communication network quality.
The structure of the remaining sections of this paper is as follows.
Section 2 elaborates on the mathematical model for communication countermeasures, while
Section 3 expounds on the design and implementation of the CCBA.
Section 4 presents the details of simulation experiments and the corresponding result analysis, and
Section 5 draws the main conclusions of the study and puts forward prospects for future research work.
4. Simulation Experiment
4.1. Parameter Setting of the Simulation Scenario
All simulation experiments in this section are carried out based on the non-spread spectrum wireless communication interface with 600 MHz fixed frequency and 1 MHz bandwidth, which is a typical application scenario of battlefield short-range air-ground tactical communication, and the relevant parameter settings are in line with engineering practice.
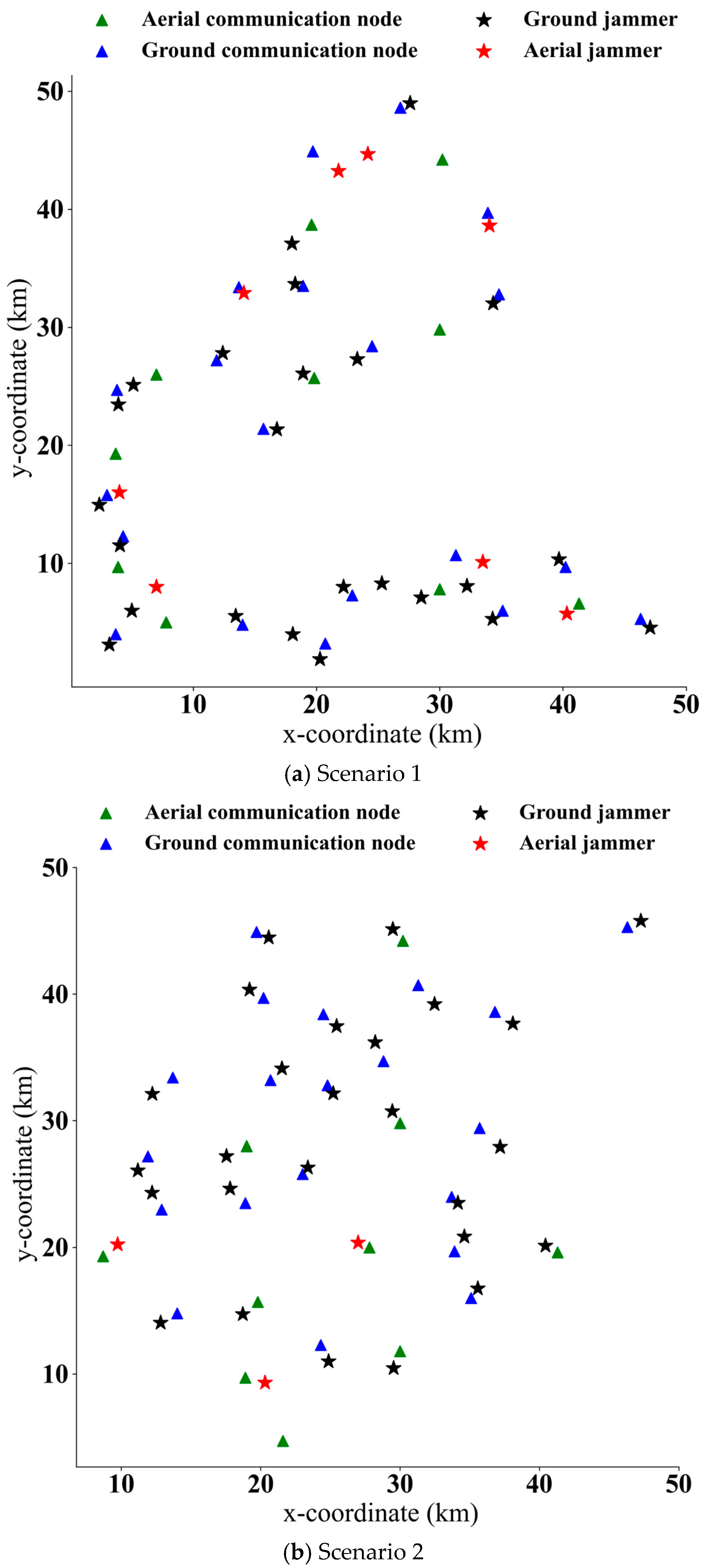
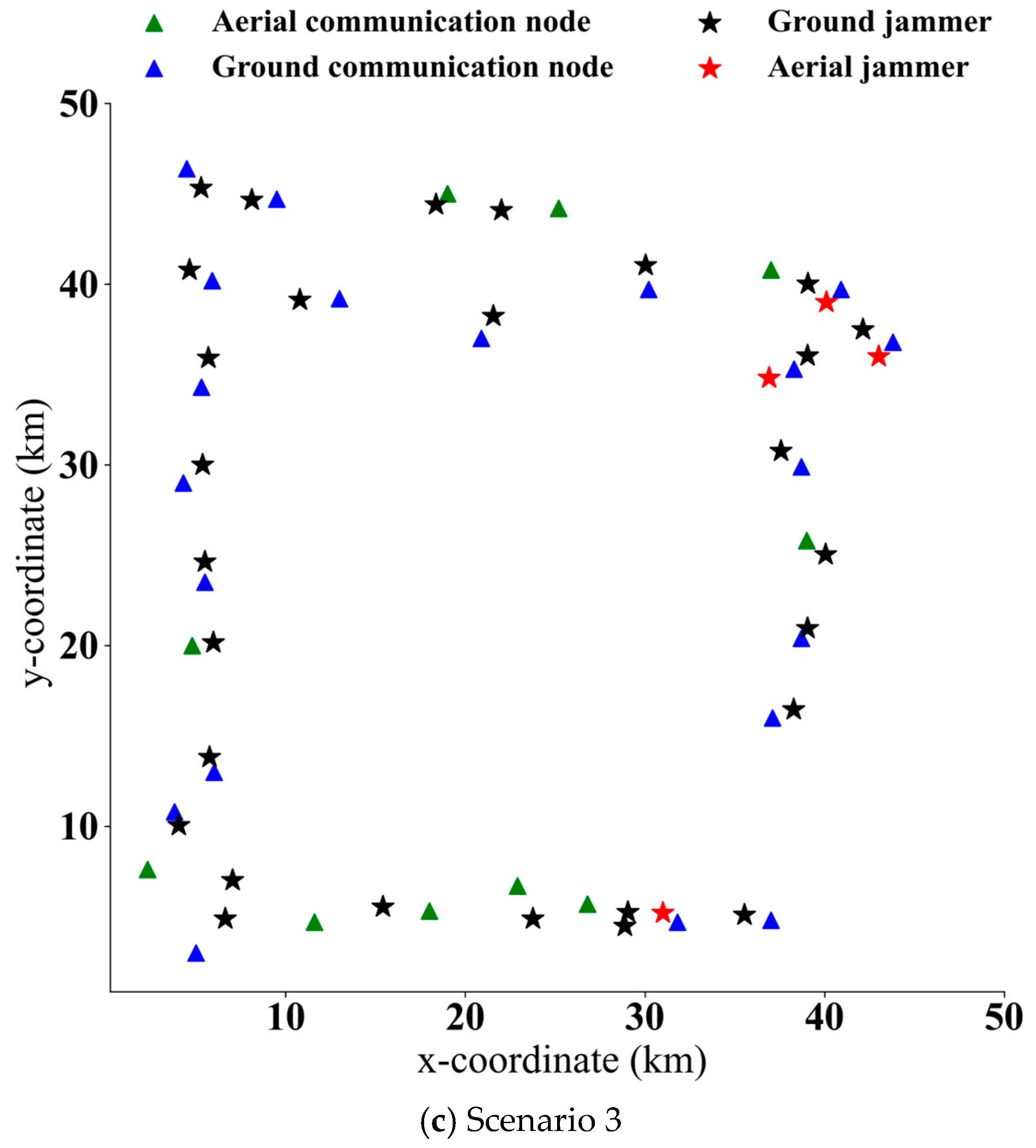
This paper designs three simulation scenarios, as shown in
Figure 4 and
Table 1.
Figure 4a depicts an air–ground communication network distributed along a highway,
Figure 4b shows a centrally deployed air–ground communication network, and
Figure 4c illustrates a ring-deployed air–ground communication network. The static jammer layout adopted in the simulation experiments is premised on achieving overall jamming with full-power jamming.
All experiments were conducted on a platform equipped with an Intel(R) Core(TM) i5-8300H CPU (2.30 GHz), 16.0 GB RAM, and an NVIDIA GTX 1080Ti GPU. The software environment was built on Anaconda 23.7.4, with PyCharm 2023.2.1 (Professional Edition, runtime version: 17.0.8+7-b1000.8 amd64) as the IDE, and key dependencies including anaconda_depends_2023.09 and PyTorch 1.13.1. The simulation experiment parameters used in this paper are shown in
Table 2. In a strong electromagnetic interference environment, ground communication nodes can use elevated antennas or UAV-lifted antennas to improve communication quality.
In a strong electromagnetic interference environment, before implementing distributed communication jamming, communication nodes transmit signals at maximum power, and the receiving status of communication nodes is shown in
Table 3.
The receiving status of the jamming side is shown in
Table 4.
If all distributed communication jammers impose jamming at maximum power, all communication nodes in the three scenarios will suffer from high-intensity jamming.
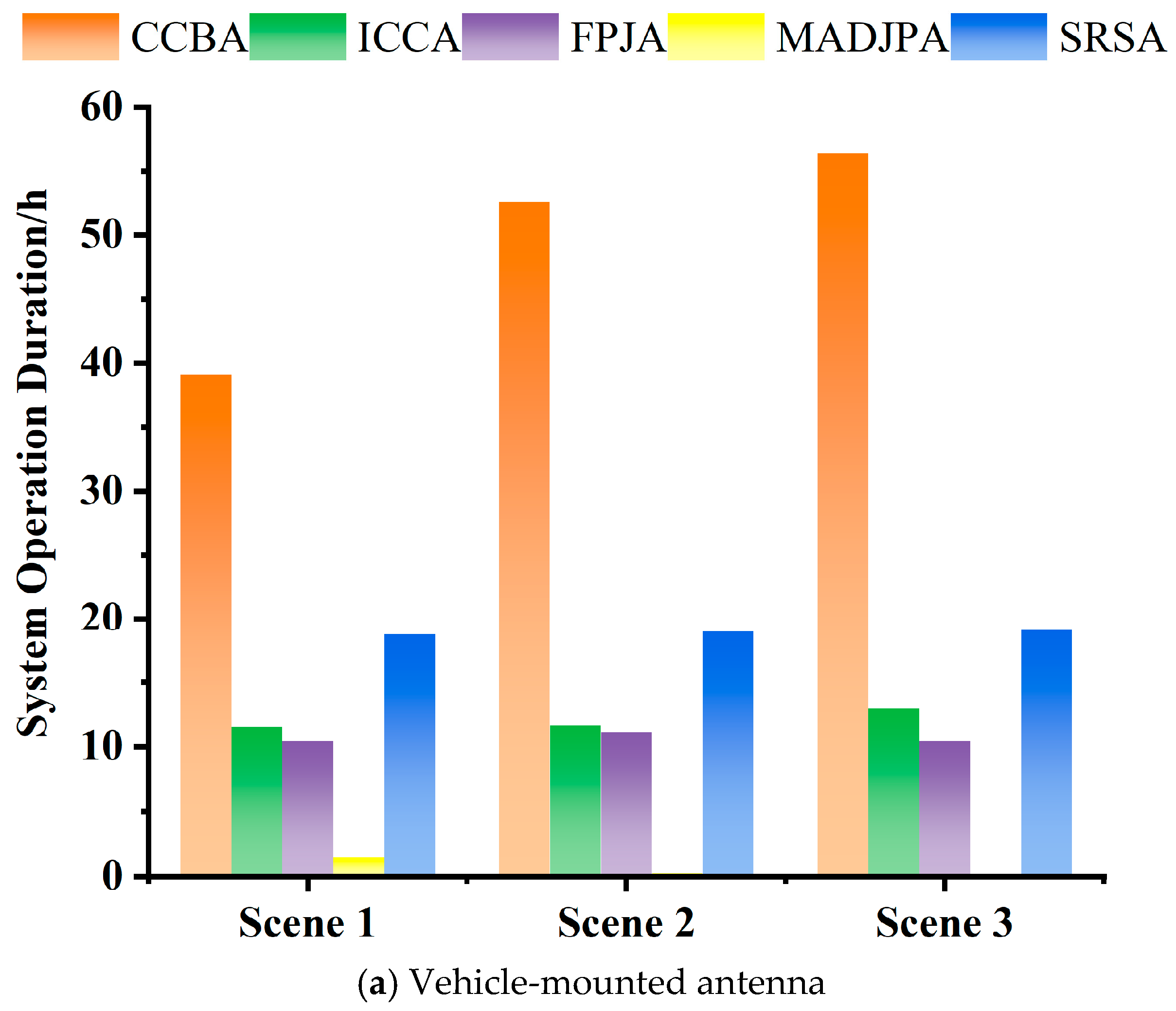
4.2. Comparison Results and Analysis of System Operation Duration
The CCBA is compared with the intelligent concentric circle algorithm (ICCA) [
3], full-power jamming algorithm (FPJA), simple random search algorithm (SRSA), and MADJPA [
36]. The algorithms are run 30 times, and the average values are taken.
When ground communication nodes use vehicle-mounted antennas, the system operation duration of CCBA is extended by 109%, 178.3%, and 196.3% compared with the comparative algorithms in Scenario 1, Scenario 2, and Scenario 3, as shown in
Table 5.
When ground communication nodes use elevated antennas, the system operation duration of CCBA is extended by 66.8%, 155.6%, and 166.9% compared with the comparative algorithms in Scenario 1, Scenario 2, and Scenario 3, as shown in
Table 6.
When ground communication nodes use UAV-lifted antennas, the system operation duration of CCBA is extended by 248.7%, 269.6%, and 223% compared with the comparative algorithms in Scenario 1, Scenario 2, and Scenario 3, as shown in
Table 7.
MADJPA trains based on the initial communication network status but lacks power adjustment strategies for communication nodes and sample generation mechanisms. With insufficient training under single-sample conditions, its training time is shorter, making it difficult to cope with drastic adjustments after communication nodes are disturbed. FPJA and SRSA do not use external information and adopt fixed strategies to set jammer power, resulting in shorter decision-making durations. The ICCA saves a small amount of time by not using broadcast strategies.
In
Figure 5, the system operation duration of CCBA is extended by 66.8% compared with the comparative algorithms. Experimental results show that CCBA can efficiently complete jamming resource scheduling. When the jammer networking is blocked, a single jammer cannot obtain the real-time feedback of overall jamming effects, making it impossible to optimize the solution search accordingly. The comparative algorithms lack electromagnetic environment estimation, power scheduling, and collaborative strategies for independent jammers, which makes it difficult to meet the requirements of overall communication countermeasures.
In the complex air-ground confrontation layout and electromagnetic environment, the local information reconnaissance by a single jammer is insufficient to infer global information, leading to the scheduling failure of the MADJPA algorithm even when jammer power is sufficient, thus reducing the system operation duration.
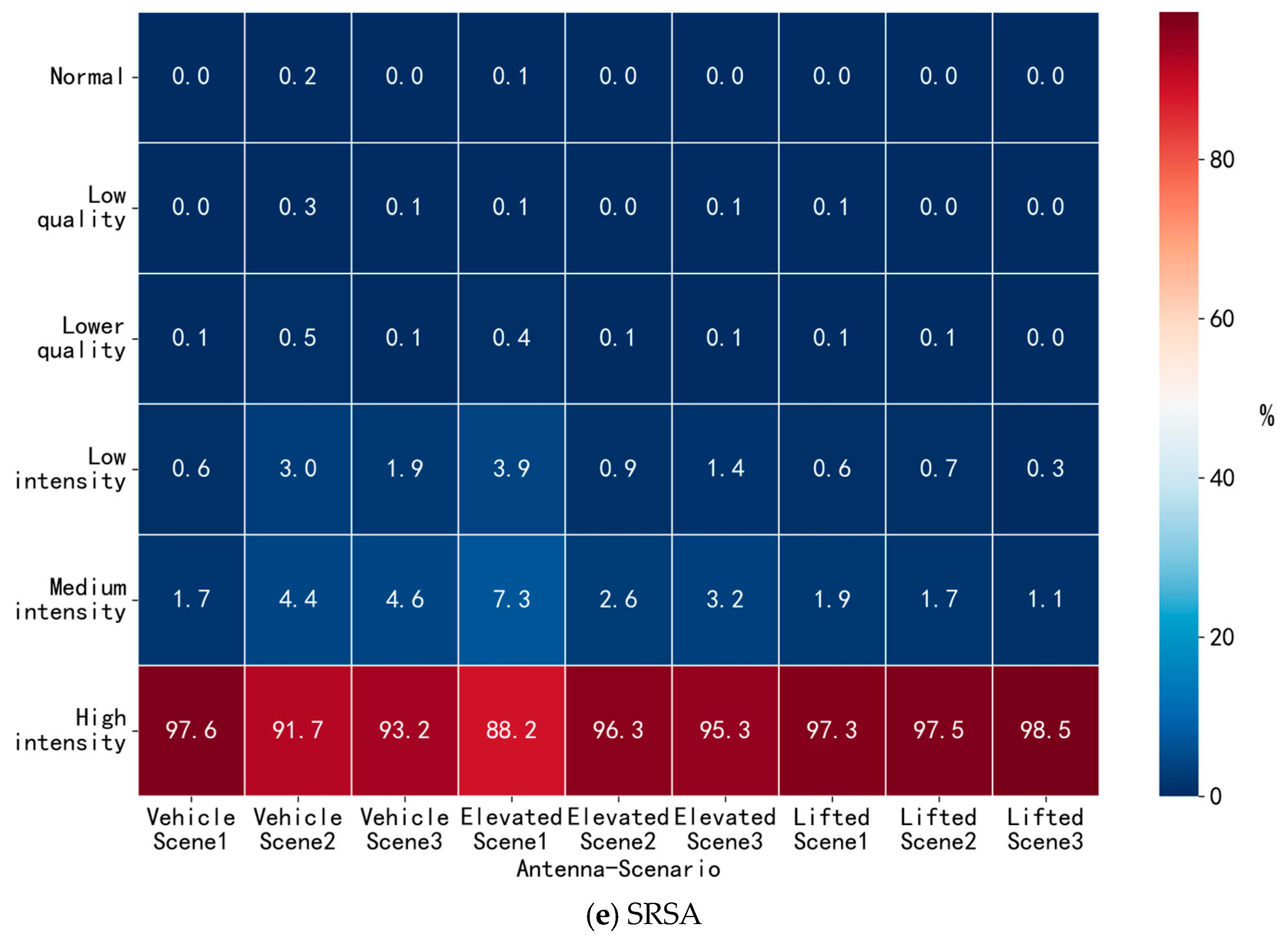
4.3. Results and Analysis of Communication Party’s Disturbed State
After the communication countermeasure process is completed, in order to analyze the disturbed state of the communication party in a more refined manner, an analysis index of “multistage J/S” is proposed. The multistage J/S makes a detailed division between high-intensity jamming and normal communication, statistics the duration distribution of the receiving power of each communication node in the six communication receiving states, and calculates its proportion. As shown in Equation (17),
represents the time proportion of the
-th communication node in the first communication receiving state, and
is the duration of the
-th communication node in the first communication receiving state.
Figure 6 shows that the proportion of high-intensity jamming by CCBA is not less than 50%, and the proportion of normal signal reception by communication nodes is no more than 6%. Compared with the comparative algorithms, CCBA extends the system operation duration and appropriately reduces the proportion of high-intensity jamming, enabling flexible and effective jamming on the overall communication network.
The proposal of “overall limited jamming” reduces the restrictive conditions of communication jamming, providing space for the algorithm to flexibly adjust the jamming power. The electromagnetic environment estimation strategy, range gear strategy, environmental noise threshold strategy, power upper limit strategy for disconnected states, and limited random power scheduling strategy reduce the release of redundant power and extend the system operation duration.
4.4. Proposition, Proof and Analysis of Overall Limited Jamming
Proposition 1. (Overall limited jamming improves the energy efficiency of jammer network).
For the non-spread spectrum communication system in this study, the overall limited jamming strategy can strictly improve the energy efficiency of the jammer network (i.e., and ) if the following two conditions are satisfied:
1. The minimum jamming target is achieved: the proportion of disturbed communication nodes ;
2. The total transmit power of CCBA meets: and .
Notation: is defined as the energy efficiency of the jammer network, representing the number of disturbed communication nodes per unit transmit power; is the proportion of disturbed communication nodes; is the total transmit power of the jammer network in one scheduling cycle.
Proof. 1. Comparison with FPJA:
According to the definition of energy efficiency, .
Combining Condition 1 (
) and Condition 2 (
), we can derive:
Thus, is strictly proven.
2. Comparison with ICCA:
Simulation results show that ICCA cannot stably meet the minimum jamming target in strong EMI environments, i.e., .
Combining Condition 2 (
), rearranging the inequality gives
□
The essential difference between the overall limited jamming strategy and traditional jamming strategies (FPJA, ICCA) lies in the jamming optimization goal and power allocation logic, which is the core reason for its higher energy efficiency. The specific comparative analysis is as follows:
FPJA takes the full suppression of all communication nodes as the only jamming goal, and all jammers operate at the maximum transmit power during the entire jamming process without considering power redundancy and actual jamming demand. This extreme jamming mode leads to two critical problems: first, a large amount of redundant power is consumed for the suppression of low-priority communication nodes, resulting in a sharp reduction in the effective operation duration of the jammer network; second, the fixed full-power mode cannot adapt to the dynamic adjustment of the communication party’s transmit power, and the jamming power cannot be flexibly adjusted according to the actual electromagnetic environment. In contrast, the overall limited jamming strategy abandons the blind pursuit of full-node suppression, and only requires the overall degradation of the communication network to meet the preset threshold ( ≥ 0.8). It allows jammers to reduce transmit power for low-demand jamming nodes and avoid continuous high-power operation, which fundamentally eliminates the power redundancy of FPJA. Under the premise of achieving the actual tactical jamming goal, the strategy significantly reduces the total power consumption of the jammer network, and thus obtains a much higher energy efficiency than FPJA.
ICCA is a jamming resource scheduling algorithm designed for non-networked cooperative scenarios, whose core design idea is to optimize jamming target selection through distance-tier scheduling and adopt non-uniform power setting to achieve dynamic jamming in non-networked environments. However, inherent limitations in its design logic lead to insufficient energy efficiency: first, ICCA focuses on local jamming of individual communication nodes based on distance tiers, lacking a global jamming effect evaluation mechanism oriented to the overall network quality. It fails to form effective superposition of distributed jamming resources, making it difficult to balance the overall jamming effect and power consumption; second, ICCA’s power scheduling relies solely on local reconnaissance information of individual jammers, without considering the collaborative complementarity between distributed jammers. This independent decision-making mode easily leads to uneven power consumption of the jammer network and invalid power consumption caused by overlapping jamming coverage; third, ICCA adopts a relatively deterministic power scheduling strategy, which lacks flexible adjustment mechanisms based on dynamic changes in the electromagnetic environment and communication node states. It cannot adapt to the real-time adjustment of the communication party’s transmit power, resulting in unnecessary high-intensity jamming and wasted energy. In contrast, the overall limited jamming strategy takes the overall jamming effect of the network as the core constraint, and each jammer adjusts its transmit power based on the estimated electromagnetic environment and broadcast information of adjacent jammers, realizing collaborative allocation of distributed jamming resources. By strictly limiting the proportion of disturbed nodes and the J/S threshold, it avoids blind local jamming and invalid power consumption. While ensuring the achievement of the overall jamming target ( ≥ 0.8), it realizes balanced power consumption of the jammer network. The flexible power allocation mechanism based on the overall goal enables the strategy to adapt to dynamic changes in the battlefield environment, and its energy efficiency is significantly higher than that of ICCA due to more rational power utilization and stronger collaborative scheduling capabilities.
In summary, the core theoretical innovation of the overall limited jamming strategy is that it reconstructs the jamming optimization goal of the distributed jammer network from “local node full suppression” (FPJA) or “local node tiered jamming” (ICCA) to “overall network quality degradation”, and establishes a flexible power allocation mechanism based on this goal. This theoretical design fundamentally solves the problems of serious power redundancy (FPJA) and insufficient global coordination and dynamic adaptability (ICCA) of traditional strategies, and thus achieves the improvement of energy efficiency and the extension of system operation duration under the premise of satisfying tactical jamming demand.
5. Conclusions and Future Prospects
This study is verified under the planar LOS scenario for the 600 MHz fixed-frequency and 1 MHz bandwidth communication system, and the concentric circle broadcasting strategy in
Figure 2 is applicable to this scenario; the research on 3D NLOS scenario will be the key direction of our future work, including the design of 3D path loss model and airspace range gear division.
In the case of network blockage in a strong electromagnetic interference environment, CCBA coordinates jammers using the range gear strategy and concentric circle broadcasting strategy under the condition of uncertain decision-making order. It adopts the electromagnetic environment estimation strategy, limited random power scheduling strategy, and final power release strategy to meet the overall confrontation requirements. Based on the position-based environmental noise threshold strategy and the power upper limit strategy for disconnected states, CCBA eliminates redundant operations of random search.
Simulation experiments show that the evaluation index of overall limited jamming proposed in this paper, which takes the acceptable overall communication jamming effect as the optimization goal, is feasible and can adapt to the distributed communication jamming requirements in harsh environments. The proposed multistage J/S index enables more precise and reasonable analysis of jamming effects. The analysis of jammer residual power can evaluate the scheduling of heterogeneous jammers and the uniform power consumption. For the air–ground communication system, the CCBA extends the system operation duration by 66.8–269.6% compared with the traditional algorithms (ICCA, FPJA, MADJPA, SRSA) while maintaining effective jamming effects (the proportion of high-intensity jamming is not less than 50%), and realizes the balanced scheduling of jammer power with low communication overhead in the strong EMI environment.
In future research, more communication countermeasure means and mechanisms can be introduced to better simulate intense battlefield communication confrontations [
38]. For example, the communication side can adopt frequency hopping strategies, intelligent reflecting surface antennas, mobile transfer of communication equipment, etc. [
39]. The jamming side can introduce frequency hopping strategies, mobile transfer of aerial jammers, jamming pattern selection, etc. The environment can be set as complex terrains such as mountainous areas and urban areas.