1. Introduction
The Internet of Things (IoT) has rapidly expanded, connecting billions of devices from tiny sensors to cloud servers and enabling applications across smart homes, healthcare, industry, agriculture, and animal welfare monitoring. Yet the same scale and heterogeneity create acute security challenges: many devices are resource-constrained and lack mature protection, IoT environments are highly distributed and wireless, and devices frequently join/leave networks—together, these can open numerous attack vectors [
1,
2]. Ensuring confidentiality, integrity, and authenticity under such constraints remains difficult.
Major cloud platforms mandate strong transport security end-to-end, but constrained hardware often lacks hardware security modules or robust entropy sources, which undermines cryptographic protocols that depend on high-quality randomness [
3]. Weak entropy can render keys/nonces more predictable. Thus, beyond standard Transport Layer Security (TLS), practical IoT stacks benefit from dynamic keying and lightweight integrity mechanisms that tolerate limited entropy and computation.
Two complementary strategies are therefore salient: (i) dynamic key management that frequently re-derives per-session or even per-window keys to narrow exposure upon compromise; and (ii) leveraging additional/behavioral entropy to strengthen keys and integrity tags on low-power nodes. This work adopts both, but—crucially—situates them in an animal-centric setting where security failures translate into welfare consequences rather than mere SLA violations.
Within the domain of animal welfare IoT, ensuring security and usability becomes particularly critical. Animal monitoring traditionally depends on methods such as Radio Frequency Identification (RFID) or ear-tagging [
4], which are often invasive and stressful for animals, raising significant ethical concerns (shown in
Figure 1). Moreover, these identification techniques necessitate frequent manual handling and can be prone to human error, which is especially problematic in settings such as zoos or livestock farms with numerous visually similar animals. Consequently, developing non-intrusive yet secure authentication methods tailored specifically to animals has become essential.
Compared to general IoT applications, animal-centered deployments have unique value: they directly affect welfare management, veterinary decision-making, and ethical standards of care. Unlike industrial IoT, here a forged or misattributed sensor stream may cause unnecessary veterinary intervention, misallocation of food or medication, or overlooked signs of illness. Therefore, security is not only a technical issue but also an ethical requirement in animal IoT.
Beyond welfare monitoring itself, secure identity management is critical. Behavioural biometrics have been recognized as a viable authentication factor in wearables [
5,
6], yet no study has validated such approaches for animals. Without secure identification, attackers could inject forged telemetry or impersonate devices, leading to false alarms and unnecessary veterinary interventions. Prior analyses of Message Queuing Telemetry Transport (MQTT) integrity vulnerabilities [
7] underline how such risks are realistic in IoT deployments; in an animal context, their impact is amplified by welfare and ethical considerations.
In this study we focus on canines for three reasons. First, dogs are widely kept as companion animals and working partners (e.g., guide dogs, detection dogs), making their welfare monitoring socially relevant. Second, their diverse motion repertoire (e.g., running, shaking, sitting, lying) provides a rigorous testbed for activity recognition and behavioral fingerprinting. Third, an open canine inertial measurement units (IMU) dataset is publicly available, ensuring experimental reproducibility. While our experiments use dogs, they can be extended to other animals, such as cattle, horses, or zoo mammals, in future work.
Recent developments in animal-oriented IoT emphasize the need for secure and non-invasive identification. Studies on livestock monitoring and animal re-identification (Re-ID) demonstrate how biometric or visual-based identification supports welfare management, yet still lack embedded-layer authentication. For example, Alzahrani et al. (2024) proposed an edge-artificial intelligence (AI) framework for cattle pose recognition in farm IoT systems [
8], while Ahmed et al. (2023) introduced an animal Re-ID model achieving over 90% accuracy across multi-camera settings [
9]. However, these methods primarily address perception rather than cryptographic trust. Integrating behavioral biometrics into IoT-level security, therefore, fills an unaddressed gap between welfare analytics and secure communication.
Our research addresses these dual requirements by integrating behavioral fingerprinting derived from wearable IMUs with standard cryptographic primitives (MQTT/TLS and application-layer Hash-based Message Authentication Code (HMAC)) in a practical edge-IoT pipeline. This combined approach aims to provide lightweight, deployment-oriented telemetry integrity/provenance support while reducing operational burden and avoiding invasive identification tags.
Specifically, our prototype targets a zoo deployment scenario, where each wearable collar streams 100 Hz IMU windows to a central welfare dashboard via MQTT. A Raspberry Pi gateway at the edge performs on-device motion recognition. Behavioural fingerprinting is not used to grant trust independently; it triggers secondary checks when the signal is inconsistent or low-confidence, while reducing the need for manual collar–animal matching by zoo staff.
The remainder of this paper is organized as follows:
Section 3 presents an algorithm of the proposed security framework.
Section 4 details the experimental evaluation.
Section 5 discusses implications and limitations.
2. Related Work
Behavioural biometrics treat motion sequences as a soft-biometric. Recent surveys outline the field’s rapid growth and its relevance to IoT [
5]. A recent survey by Ray-Dowling et al. (2023) consolidates three decades of motion-sequence biometrics and discusses their growing use in IoT and wearable security contexts [
10]. On the algorithmic side, Mekruksavanich & Jitpattanakul, 2024, showed that a squeeze-and-excitation hybrid convolutional neural network (CNN) can authenticate phone and watch wearers with 98% TPR at 0.8% FPR [
11]. Although primarily ‘human-centric’, the feature-attention ideas are directly portable to animal-mounted IMUs, yet no paper has validated such per-animal identity on-device. Our work explicitly fills this gap by demonstrating on-device behavioural fingerprinting for animals, thereby extending soft-biometric methods beyond human subjects.
The integration of edge computing with cloud services offers a multi-layered approach to IoT security, wherein computational tasks are distributed to balance performance and risk. Collaborative encryption and authentication frameworks have been proposed to exploit this architecture. For instance, Tan et al. introduce an adaptive encryption strategy spanning cloud–edge and edge–edge communications, combined with attribute-based access control and trust assessment of participating nodes [
12]. This multi-tier scheme dynamically adjusts encryption policies and continuously monitors threats, resulting in more resilient data sharing (e.g., in industrial IoT) without sacrificing efficiency. Another representative work is by Zhu et al. [
13], who design a chaotic mapping-based authentication protocol tailored to cloud-edge coordinated networks. Their cloud-edge IoT key agreement protocol uses lightweight chaos-derived cryptographic functions to achieve mutual authentication with device anonymity. Formal verification (using BAN logic and Scyther) and experiments showed this outperforms prior schemes in efficiency while preserving security. These examples illustrate the state-of-the-art in edge–cloud synergy for IoT security: the edge layer can handle time-sensitive encryption, local data filtering, or initial authentication, while the cloud provides heavy-duty cryptographic processing, cross-domain trust management, or global anomaly detection. By co-designing security protocols across device, edge, and cloud tiers, researchers have achieved reduced latency in threat response and robust, layered defenses. Overall, existing studies confirm that multi-layer collaboration (device/edge/cloud) can enhance encryption key management, authentication, and integrity verification in IoT systems. The challenge lies in optimizing the partitioning of security functions, recent solutions are making progress using techniques like hierarchical encryption, distributed trust, and real-time edge analytics to secure IoT data from the ground up. In contrast, our framework minimizes architectural complexity by focusing on lightweight dynamic key generation and HMAC integrity seals that can be deployed directly on collars and a single edge node, rather than requiring elaborate cloud–edge coordination. This design choice makes our solution feasible for animal-welfare deployments, where IT infrastructure and staff expertise are limited.
Applying AI (especially deep learning models like CNN and Long Short-Term Memory (LSTM)) to IoT sensor streams has proven effective for detecting security threats and data integrity issues in situ (i.e., on edge or embedded devices). Machine learning-based anomaly detection has become common in IoT contexts [
14,
15]. For example, CNNs and recurrent neural networks (RNNs) have been used to build intrusion detection systems (IDSs) that analyze network traffic or device telemetry for malicious patterns. Deshmukh et al. developed an optimized CNN-based IDS (IIDNet) that uses feature engineering and hyperparameter tuning to operate within IoT resource limits [
16]. On the UNSW-NB15 IoT cyberattack dataset, their framework achieved about 95.5% detection accuracy while significantly reducing computational overhead, outperforming many classical IDS models. Similarly, hybrid models combining CNNs with LSTMs can capture both spatial and temporal features of sensor data sequences. A recent study in Scientific Reports evaluates an enhanced LSTM–CNN model on IoT traffic data, finding it can reach 99.87% accuracy with only 0.13% false positives, substantially better than standalone CNN or LSTM models [
17]. These learning-based approaches enable edge or gateway devices to automatically flag abnormal readings (caused by attacks, faults, or tampering) in real time, thus providing an additional security layer beyond cryptography. Some works also target data integrity verification, e.g., CNN variants have been proposed to detect inconsistencies in multimodal industrial sensor data, signaling potential tampering or errors in critical systems. The key trend is bringing AI to the edge, through model compression, federated learning, or TinyML, so that even constrained IoT nodes can locally validate data and detect anomalies without constant cloud reliance. This reduces response time and bandwidth use for security monitoring. In summary, the literature over the past decade demonstrates numerous successful implementations of CNN/LSTM-based security analytics for IoT, from smart home anomaly detectors to industrial intrusion detection, indicating that AI-powered integrity checks on the edge are both feasible and highly effective in practice. Our approach differs in scope: rather than anomaly detection over generic network traffic, we employ CNNs directly on IMU motion windows for dual purposes—activity recognition and per-animal identity authentication. This focus not only secures the communication channel but also eliminates invasive tagging by turning natural motion into a biometric, a dimension absent from prior IDS-focused studies.
4. Evaluation
Our prototype targets a zoo deployment, where each collar streams 100 Hz IMU windows to a welfare dashboard. Because keepers are rarely IT specialists, password hygiene and key rotation are hard to enforce; leaked credentials could let an attacker forge “sick-animal” telemetry and trigger unnecessary veterinary interventions. The zoo also houses many visually similar animals, so re-assigning IMU collars after charging or cleaning is tedious, and RFID tags are either impractical (for small mammals) or risk invasive injury. Hence, our evaluation must answer two practical questions:
Taken together, the experiments cover transport protection (TLS), application-layer tamper-evident integrity sealing (dynamic-HMAC), and stream provenance support via behavioural fingerprinting, spanning from the transport layer (OSI L4) to the application layer (L7).
4.1. Experimental Setting
4.1.1. Edge AI Hardware
Raspberry Pi 4B (4 GiB, Cortex-A72@1.5 GHz), Raspbian 11.
4.1.2. Software
Mosquitto 2.0.11, Python 3.10.11, TensorFlow 2.15. All metrics are averaged over three cold-start runs (). Confidence intervals are the two-sided 95% interval , where is the run-to-run standard deviation. With this slightly under-estimates the critical value (2.26), but keeps notation concise; the exact t-interval is reported in the artefact.
4.1.3. Training/Validation/Test Split
For both the activity-recognition CNN and the identity (fingerprinting) CNN, segmented IMU windows were split into 80% for training and 20% for testing. Within the training portion, 10% of the data were reserved for validation during model fitting. The test set was held out throughout training and model selection and was used only for final performance reporting.
4.1.4. Training Hyperparameters
Both CNN models were trained using the Adam optimizer (learning rate
) with mini-batch training (batch size
). The activity-recognition model uses sparse categorical cross-entropy loss, while the fingerprinting model uses the class-balanced focal loss described in
Section 3.2. A validation split of 0.1 was used for model monitoring during training.
For every 0.5 s sensor window (
samples at 100 Hz) we log
where
is the HMAC transmitted by the collar and
the one recomputed at the edge.
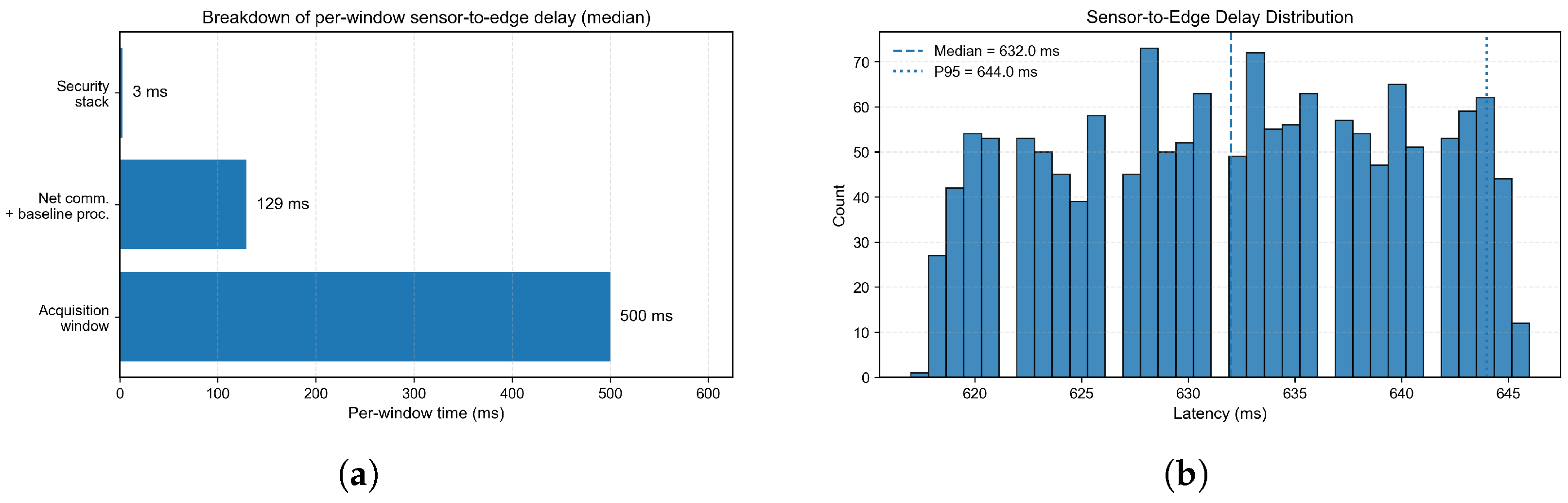
4.2. Sensor-to-Edge Delay
We instrumented the full pipeline using a non-blocking MQTT loop loop(timeout=0) on the Raspberry Pi, with a fixed sampling window of
samples (0.5 s). The reported sensor-to-edge elapsed time
L includes the fixed 0.5 s IMU acquisition window required to form each HAR window; we report the remaining network and edge-processing component separately below. Over
consecutive windows, the per-window sensor-to-edge elapsed time
L was
Because
L already includes the fixed 0.5 s IMU acquisition window required by the HAR task, the net communication and edge-processing component is on the order of 130 ms in steady state. As summarised in
Figure 3a, the delay budget is dominated by the acquisition window, followed by WLAN/TLS transport and baseline edge processing, while the security stack contributes only a few milliseconds. The few unusually small values close to
in
Figure 3b occur during the TLS handshake and warm-up phase, and have negligible impact on the reported median.
4.3. Sustained Throughput
Figure 4 shows the per-minute message rate for 20 concurrent collars. After a brief warm-up (TLS handshake + XLAJIT), the broker stabilises at
CPU stays below 1.4% and RAM under 396 MB, leaving headroom for at least 50 collars.
To strengthen the scalability evidence beyond the 20-collar baseline, we conducted a stress test with 50 concurrent simulated collar clients publishing messages in the same format and at the same per-client rate. The aggregated results are summarised in
Table 2. We logged the broker/edge resource usage and message ingress rate every 30 s over a ∼6 min run. The observed message rate stabilised around a median of 2414.5 msgs/min (range: 390–2466 msgs/min across the run), while CPU utilisation remained low (median 2.8%, max 11.2%) and memory usage stayed stable (median 1.58 GB).
4.4. Network Variability Stress Test
To complement the controlled laboratory measurements, we evaluated the robustness of the end-to-end pipeline under network variability by injecting delay jitter and packet loss in the collar-to-edge path on the same Raspberry Pi testbed.
Table 3 reports the receiver-side acceptance breakdown with the freshness bound Δ = 2000 ms and both monotonic and duplicate checks enabled. Across three runs, the pipeline maintained an acceptance rate of ≈99.3%, with no stale/monotonic/duplicate rejections observed in these settings.
4.5. Dynamic–HMAC Tamper Detection
To stress-test the integrity layer, we corrupt each 0.5 s window by flipping one random byte (8 bits) with probability
. This setup follows prior MQTT integrity stress tests that inject random corruption into the payload (often described as bit/byte flipping) [
7]. Algorithm 2 shows the verification. This setting reflects accidental corruption and opportunistic tampering that aims to alter data silently. Evaluating adaptive forgeries (e.g., replay or recomputation of tags under partial motion knowledge) requires an explicit threat model and additional experiments, which are discussed in
Section 3.9.
| Algorithm 2 Pseudo-code for PSK derivation and HMAC verification |
| Require: window w (50 samples), integer millisecond timestamp |
| 1: |
| 2: |
|
3: |
|
4: |
|
5: |
|
6: Transmit |
| Ensure: On receive: |
|
unpack |
|
derive from and as above |
|
if then accept else reject |
The per-window PSK is derived by the following:
Performing an N-point real FFT on the 50-sample window.
Summing the magnitudes of the last eight frequency bins to obtain a coarse high-frequency energy .
Concatenating (where is the 64-bit timestamp).
Hashing with SHA-256 and truncating to the first 16 bytes (128 bits).
The resulting PSK is then used as the HMAC key over the raw window bytes. Any window whose tag fails verification is rejected for 100% of the 1200 forged windows, consistent with the
forgery bound of HMAC-SHA-256 [
25].
Random byte flips model accidental corruption and non-adaptive payload tampering (A0). To better reflect practical IoT threats within our stated scope, we further evaluate (i) replay attacks (A1) and (ii) motion-pattern spoofing by partial-window splicing without tag recomputation (A0). The aggregated outcomes are summarised in
Table 4. Because a replayed packet is byte-identical, the integrity seal alone cannot detect replay; therefore, we pair it with a receiver-side freshness/replay filter using a freshness bound Δ = 2000 ms, a monotonic timestamp check, and duplicate suppression.
In the replay experiments, delayed packets are rejected as either stale (when ) or monot (when timestamps violate monotonicity), consistent with the intended role of the filter for mitigating simple replay (A1). In the injection/splicing experiments, the adversary replaces 10–50% of the payload samples using segments from other windows while keeping the original timestamp and HMAC tag unchanged; these packets are rejected as HMAC fail, illustrating that the integrity seal detects non-adaptive payload modification without recomputing a valid tag (A0).
4.6. Entropy Analysis of Dynamic PSK
Let
be the random variable for byte
i of the 128-bit PSK. The Shannon entropy per byte is defined as [
26]
The min-entropy is
which bounds an adversary’s single-guess success probability by
.
To assess the unpredictability of our motion-derived PSK, we harvested 1000 windows of chest IMU data (fixed timestamp) and computed and for . The results are as follows:
According to NIST SP 800-90B [
27],
bits per byte suffices for cryptographic randomness in embedded systems. Extrapolating to the full 128-bit PSK yields a maximum single-guess success rate of
, Under a pure guessing model (i.e., without side information), this corresponds to a negligible success probability for randomly guessing a matching 16-byte value; we report it as an empirical indicator of variability rather than a security proof under active attack.
These results suggest that the motion-derived value exhibits substantial variability in our benign data-collection setting. In this paper, we therefore use it as a lightweight per-window keying material for integrity binding.
To verify the robustness of motion-derived entropy, we compared dynamic (walking/running) and near-static (lying down) IMU windows. The analysis showed that even during resting periods, the derived keys retained high randomness, with average byte-level entropy around 7 bits and minimum entropy above 6 bits. This indicates that entropy remains virtually undiminished under low-motion conditions and continues to exceed the 6 bits/byte lower bound recommended by NIST SP 800-90B.
As an additional feasibility check beyond the canine dataset, we repeated the same entropy computation on a goat IMU dataset [
28]. The derived per-window keying material exhibited similar variability (average byte-level Shannon entropy around 7.8 bits and minimum entropy above 6 bits per byte in this benign setting), suggesting that the empirical entropy behaviour is not limited to one species. This result is reported as a preliminary indicator rather than a security proof or a generalisation guarantee.
4.7. Behavioural Finger-Printing
Single -Window Performance: The re-balanced TCN yields 83.9% accuracy on subjects held out for testing. When genuine legit and imposter fake streams are interleaved, we obtain on-the-fly decision rates of
and
over 2180 windows (
Figure 5).
Operational Ramifications and Mitigation: The fingerprinting network outputs a softmax probability vector over subjects. While we report closed-set identification accuracy and FAR/FRR for comparability, practical deployments typically require a verification-style decision with a configurable operating point. Given an expected identity for a collar stream, we accept the auxiliary fingerprinting signal only if , where is a confidence threshold. Varying yields a FAR/FRR trade-off, so acceptable error targets must be specified at the operating point relevant to the application (e.g., prioritizing a low FAR when the consequence of mis-attribution is high, while tolerating a higher FRR as operational friction). Under our auxiliary usage, a false accept (FAR) corresponds to attributing a window to an incorrect subject, which can contaminate downstream welfare analytics or mask collar–animal mis-association; a false reject (FRR) corresponds to failing to confirm the expected subject and mainly increases operational overhead by triggering re-checks. To limit the impact of occasional misclassifications, conservative decision logic can be applied at the edge (e.g., majority voting or K-consecutive agreement over a short horizon, and treating low-confidence outputs as “uncertain” rather than switching identity immediately), with an operator-in-the-loop confirmation during re-pairing events. Fingerprinting is applied continuously on streaming windows, so practical decisions need not rely on a single window. For illustration, if per-window correctness is 83.9%, then under a simple independence assumption, a majority vote over consecutive windows yields an expected correct majority of ≈96.8% (and ≈98.4% for ). This illustrates why conservative temporal aggregation can substantially reduce the impact of occasional window-level misclassifications; the concrete choice of K and threshold should be set based on the acceptable FAR/FRR trade-off in the target workflow.
Cross-Species Feasibility Check (Goat Dataset): To avoid over-claiming species-agnostic performance while still assessing whether the pipeline is inherently tied to canines, we conducted a small pilot on a separate internal goat IMU dataset (five subjects). Using the same windowing procedure and the same fingerprinting pipeline, we obtained an overall identification accuracy of 86% on 56,814 windows (macro-F1: 0.87; weighted-F1: 0.86). We present this result as a feasibility sanity check rather than a comprehensive generalisation study; systematic validation across species, sensor hardware, and mounting conditions remains future work.
4.8. Edge-Side Computation Overhead
To isolate pure processing cost, we replayed
cached windows (≈50 s of sensor data) on the Raspberry Pi and enabled each security layer in turn.
Figure 6 reports the median processing time per window on the edge node:
Because these ≈200 ms are additive to the 0.5 s acquisition window and ≈0.27 s WLAN/TLS transport, the full sensor-to-edge delay
L in
Figure 3 is close to 1 s. Importantly, the security stack itself contributes less than 3 ms (≈1–2%) on top of the application-driven sensing and transport time.
Generality: While our main evaluation uses a public canine dataset, the proposed pipeline is not conceptually tied to a single species. Our pilot goat-dataset results provide preliminary evidence of feasibility across species; however, comprehensive validation across sensor hardware, mounting conditions, and additional species remains an important direction for future work.
5. Discussion
5.1. Validation Results Summary
The Evaluation section presented quantitative results for sensor-to-edge delay, throughput, and authentication accuracy. In this Discussion, we interpret these results in terms of practical usability and potential improvements.
5.1.1. Latency Bottlenecks
The 632 ms median sensor-to-edge delay in
Figure 3 is dominated by (i) the 500 ms IMU acquisition window required by the HAR task, and (ii) a delay of ≈130 ms for WLAN/TLS transport and edge-side processing.
Of the latter, the security stack (dynamic-HMAC and fingerprint CNN) accounts for less than 3 ms per window (
Figure 6), i.e., under 2% of the total delay.
We additionally compare the MQTT client loop modes. Using a blocking MQTT loop introduces additional queuing/servicing delay in our pipeline, yielding a noticeably larger per-window sensor-to-edge delay distribution (
Figure 7). For the main results reported in
Figure 3, we therefore adopt a non-blocking MQTT loop loop(timeout=0) to avoid this implementation-induced latency inflation.
5.1.2. Throughput Head-Room
During the test, CPU utilization never exceeds 1.4% and memory usage remains under 396 MB. In contrast, our micro-benchmarks show that Mosquitto 2.0 on a Pi 4B can sustain over 50,000 msgs/min without degradation. Therefore, the measured workload of approximately 2360 msgs/min (20 collars) corresponds to less than 5% of the broker’s measured capacity, indicating substantial throughput headroom for larger deployments.
This indicates ample scalability for medium-scale deployments (hundreds of collars), but further stress tests in heterogeneous multi-broker settings are left for future work.
5.1.3. Security Payoff Versus Cost
Dynamic-HMAC and fingerprint-CNN add merely 0.7 ms (0.3%) and 2.8 ms (1.4%) of local processing time, respectively, while providing deployment-oriented integrity/provenance benefits within our stated threat model: the per-window seal detects accidental corruption and non-adaptive manipulation (A0), the timestamp-based freshness filter mitigates simple replay (A1), and fingerprinting supports stream provenance checks to reduce operational mis-association. These mechanisms are not intended to provide cryptographic-grade guarantees against fully adaptive forgers who can recompute valid tags (A2). This demonstrates that lightweight motion-derived keys can meaningfully improve security with negligible performance trade-off.
5.1.4. Formal Security Verification
To strengthen and contextualize our security claims, we conducted an automated symbolic analysis of the message-level sealing mechanism using the Tamarin prover. We emphasize that this verification targets the application-layer construction (dynamic PSK derivation + HMAC + timestamped delivery), rather than proving the correctness of TLS itself. Consistent with common protocol-analysis practice, the model considers a Dolev–Yao adversary that can intercept, replay, and inject messages on an untrusted network.
Baseline Finding Under a Strong Attacker Model
In our deployed stack, MQTT/TLS is intended to provide transport confidentiality and integrity; thus, a purely passive network attacker should not observe plaintext IMU windows. However, when transport confidentiality is not assumed in the symbolic model (e.g., to evaluate the intrinsic robustness of the application-layer construction if the secure channel is abstracted away or compromised), the baseline key derivation
becomes computable from observable message components. Tamarin produces a counterexample trace showing that authenticity-style properties are not satisfied against an adaptive forger in this stronger model. This result aligns with our stated scope: the dynamic-HMAC seal is positioned as a tamper-evident integrity binding against accidental corruption and non-adaptive manipulation (A0), and the timestamp-based filter mitigates simple replay (A1), while cryptographic message authentication against a fully adaptive forger (A2) is explicitly not claimed (
Section 3.9).
Optional Seeded Hardening and Its Assumptions
We additionally modeled an optional hardening variant in which the per-window key derivation incorporates an extra long-term per-device secret S (“seed”), e.g., . Under the same Dolev–Yao setting (without assuming a secure channel), Tamarin verifies the corresponding authenticity properties for this seeded variant, indicating that adding a single device secret can restore cryptographic message authentication at the application layer.
Discussion: Seed Provisioning Risk and Deployment Trade-Offs
The seeded variant introduces a new requirement: securely provisioning and protecting S. In practice, S could be pre-provisioned (e.g., manufacturer or offline enrollment) or established during an initial pairing phase over a trusted channel. If the trust anchor used during provisioning (e.g., CA/certificate validation) is compromised, S may be exposed, which is a generic risk shared by any credential distributed over the same channel. Therefore, we treat the seeded variant as an optional hardening direction rather than a mandatory component of our current deployment, which primarily relies on correctly configured MQTT/TLS for transport confidentiality/integrity and uses dynamic–HMAC as a lightweight tamper-evident seal within the scoped threat model.
5.1.5. Recognition Accuracy and Misclassification
Our fingerprint CNN achieved 83.9% recognition accuracy across dogs. While encouraging, single-window identity classification is not reliable enough to serve as an independent authentication mechanism. In our design, fingerprinting is treated as an auxiliary consistency/provenance signal to reduce the likelihood of persistent mis-attribution in long-running streams. Operationally, its impact can be moderated by selecting an application-appropriate operating point (confidence threshold ) and by applying temporal aggregation (e.g., majority voting or K-consecutive agreement) so that occasional misclassifications do not immediately translate into identity changes. For example, a simple majority vote yields an expected correct majority of ≈96.8% under an independence assumption. In addition, low-confidence outputs can be handled conservatively (“uncertain” state) to trigger secondary checks during collar re-pairing rather than granting trust by itself.
5.2. Animal–Computer Interaction
In animal-welfare IoT deployments, Animal–Computer Interaction (ACI) plays a pivotal role beyond simply monitoring physiological or behavioral data. Effective ACI requires seamlessly integrating security measures into daily animal care workflows, ensuring that systems remain secure without burdening caregivers, who typically have minimal technical training.
Our proposed behavioural fingerprinting approach contributes to this vision by providing an auxiliary stream-level consistency cue for collar–animal association through subtle differences in motion patterns. Traditionally, assigning wearable sensors or RFID tags to animals demands careful manual record-keeping and frequent interventions—tasks that quickly become impractical in large zoological facilities. Moreover, intrusive tagging methods can be uncomfortable or even harmful, particularly to smaller animals.
By leveraging behavioural biometrics from wearable IMUs, our framework can help reduce the manual burden associated with collar assignment and re-assignment. In practice, the fingerprinting signal should be used conservatively (e.g., with confidence thresholding and short-horizon temporal smoothing) and can trigger a re-pairing confirmation step when the signal is inconsistent, rather than replacing record-keeping entirely. This advantage reduces staff workload, decreases handling stress on animals, and helps reduce human errors common in manual identity assignment, improving operational efficiency.
Furthermore, under our scoped threat model, fingerprinting is not relied upon as a primary security barrier against adaptive impersonation. Instead, it provides an additional provenance cue that can make silent collar–animal mis-association less likely to persist and can prompt secondary checks when abnormal inconsistencies occur.
This integrated ACI approach thus not only addresses IoT security concerns but also actively supports the practical, humane, and efficient management of animal welfare systems. Future extensions could explore federated learning to continuously enhance model accuracy while maintaining privacy, or adaptive models capable of recognizing and authenticating multiple species simultaneously.
5.3. Limitations and Future Work
Although our study demonstrates strong practical value, several limitations remain to be addressed. First, the current deployment uses only a single IMU sensor, lacking contextual information that could significantly enhance the interpretation of animal behaviors, such as heart rate variability, GPS location, or environmental conditions. Incorporating multimodal data could further improve activity recognition accuracy and animal welfare assessment reliability. Energy efficiency is critical for collar wearables. In practice, the collar-side duty cycle can be reduced by leveraging an IMU with FIFO batching and a low-power microcontroller that remains in deep sleep for most of the time and periodically wakes to burst-read buffered samples and transmit aggregated updates. A detailed, hardware-specific power measurement campaign is left as future deployment work.
Second, while most activity classes achieved stable performance, Body shake showed a noticeably lower recall in our current dataset. This is largely attributable to severe class imbalance and the short, sporadic duration of shake events, which makes fixed-length window classification prone to missed detections. In our current prototype, shake recognition is treated as an auxiliary cue rather than a primary welfare indicator. Future work will collect more shake instances and explore edge-friendly remedies such as re-sampling, focal loss, or a lightweight event-centric detector specialized in rare behaviours. Third, our behavioural fingerprint model currently exhibits a relatively high false rejection rate (FRR > 5%) for dogs with limited or sparsely collected motion data. Future work should explore metric-learning strategies such as ArcFace or triplet loss methods, which could significantly reduce the FRR. However, these approaches typically demand greater computational resources; thus, careful optimization or edge-friendly adaptations, like quantization-aware training or federated learning, will be necessary.
Fourth, although our architecture is designed to be adaptable to different sensors and species, the transferability and robustness of our behavioural fingerprint approach to other animal species (e.g., horses, cattle, or smaller mammals) have not been comprehensively validated. Different species may exhibit diverse behavioral repertoires and motion characteristics, which could necessitate model adjustments or dedicated training datasets.
Lastly, large-scale deployments involving multiple brokers, heterogeneous network conditions, or cross-domain trust management were beyond the scope of this study. Future research should include stress-testing under realistic multi-node network environments to validate scalability and identify potential bottlenecks or vulnerabilities. Additionally, our approach relies on a long-term trust anchor for transport confidentiality/integrity and does not aim to provide cryptographic-grade authentication if an attacker can observe plaintext windows and recompute seals or if endpoints are fully compromised.
6. Conclusions
This study set out to design and experimentally evaluate a lightweight security architecture deployable on IMU-based animal collars and Raspberry Pi gateways without specialised cryptographic hardware. By integrating standard TLS 1.2 encryption, dynamic-HMAC integrity seals based on motion-derived entropy, and a behavioural fingerprint classifier, our work makes three significant contributions to the fields of IoT security and Animal–Computer Interaction:
Lightweight integrity and provenance framework. We present a practical, multi-layer telemetry protection pipeline for animal-wearable sensing: TLS protects the transport channel, a per-window dynamic–HMAC provides tamper-evident integrity sealing against silent corruption and non-adaptive manipulation, and behavioural fingerprinting supports stream provenance checks to mitigate operational mis-association in zoo deployments.
Efficient and sustainable performance. Comprehensive evaluation demonstrated that sensor-to-edge delay remained under 1 s (median 632 ms), sufficient for timely welfare alerts, and sustained a throughput of windows, fully matching 20 IMU collar streaming rates. The computational overhead from the security layers amounted to less than 3 ms, underscoring the practicality of our entirely software-based protection on widely available single-board computers.
Enhanced operational usability for animal care. The automatic animal authentication capability removes the necessity of manual collar–animal reassignment, substantially reducing caregiver workload and animal handling stress. This practical advancement not only ensures accurate data attribution but also makes casual tampering or misattribution of “sick-animal” telemetry harder to carry out unnoticed, thereby reducing unnecessary veterinary interventions and enhancing overall welfare monitoring efficiency in resource-constrained zoo environments.
These findings can guide animal facility managers toward implementing secure and efficient welfare-monitoring networks without extensive hardware modifications or specialized IT expertise. The zero-state collar design further simplifies deployment, maintenance, and key management, significantly reducing operational overhead. Concretely, beyond a standard IMU collar, the required extensions are lightweight and off-the-shelf, e.g., (i) an edge gateway (a Raspberry Pi-class device) running an MQTT broker/client and the verification/inference pipeline, (ii) a stable WLAN access point (or an existing facility network) for collar-to-edge connectivity, and (iii) basic credential provisioning (e.g., a broker username/password and CA certificate) for TLS-enabled MQTT. No additional invasive tags (e.g., RFID/ear tags) are required.
Looking ahead, the framework’s versatility and robustness could be further enhanced by incorporating multimodal sensor data, advanced metric-learning strategies to decrease FRR, systematic battery optimization tests under extended use, and rigorous validation in diverse, multi-species scenarios. Overall, our investigation confirms that a carefully designed, software-centric IoT security stack effectively balances cyber-resilience and practical usability, setting a foundation for safer and more effective animal-welfare management systems.