Cyber Approach for DDoS Attack Detection Using Hybrid CNN-LSTM Model in IoT-Based Healthcare
Abstract
1. Introduction
- We have implemented a hybrid deep learning model to identify and classify DDoS and IoT attacks in an IoT-based healthcare environment. The hybrid model makes DDoS attack detection accurate and efficient by combining the strengths of CNN and LSTM in terms of spatial and temporal features.
- The proposed CNN-LSTM-based hybrid system automatically learns characteristics from raw healthcare network traffic, adapts in real time, and effectively identifies attack paths to minimize disruptions to network operations and reduce false alarms.
- The IoT healthcare security and CICDDoS2019 datasets are used. Our model is assessed by contrasting its performance with that of CNN, LSTM, and the proposed deep learning techniques.
2. Related Works
2.1. Machine Learning Methods
2.2. Deep Learning Methods
2.3. Hybrid Methods
3. Proposed Approach
3.1. Architectural Design
3.2. Hybrid Model Design
3.3. Hybrid Model Overview
- ▪ Input Layer:
- ▪ Convolutional Layers (CNN Module):
- ▪ Flattening/Feature Transformation:
- ▪ LSTM Layers:
- ▪ Fully Connected Layer(s):
- ▪ Output Layer:
- ▪ Training and Optimization:
4. The Experimental Setup and Methodology
4.1. Data Acquisition
- Comprehensiveness and diversity of attack types: it contains 12 major families of volumetric and application-layer DDoS attacks (e.g., SYN, UDP, MSSQL, LDAP, NetBIOS, SSDP, PortMap, etc.). This diversity provides a robust foundation for training and evaluating deep learning models intended for heterogeneous IoT environments where various attack vectors may occur.
- Relevance to IoT-driven ecosystems: Although the dataset is not recorded in a healthcare-specific infrastructure, its traffic patterns, attack vectors, and device behaviors match those commonly observed in IoT-based systems, including healthcare IoT. Many medical IoT devices operate over similar protocols (HTTP, DNS, UDP, MQTT-like lightweight traffic), and the volumetric/application-layer attacks represented in CIC-DDoS2019 are the same categories observed in healthcare cyber incidents.
- High-quality traffic generation and realistic network setup: the dataset was captured by the Canadian Institute for Cybersecurity using a realistic enterprise-like network topology with background benign traffic. This ensures data quality, proper labeling, and realistic traffic behavior key factors for model generalizability.
- Ethical and practical constraints: CIC-DDoS2019 therefore provides a safe, publicly accessible, and methodologically sound alternative while still capturing the essential characteristics of IoT Distributed Denial-of-Service behavior.
4.2. Data Pre-Processing
- ▪ Data Standardization:
- ▪ Data Cleaning:
- ▪ Categorical Data Encoding:
- ▪ Data Spliting:
- ▪ Features Extraction
- ▪ Anomaly Detection
5. Performance Evaluation
5.1. Model Training
5.2. Model Evaluation
5.3. Results
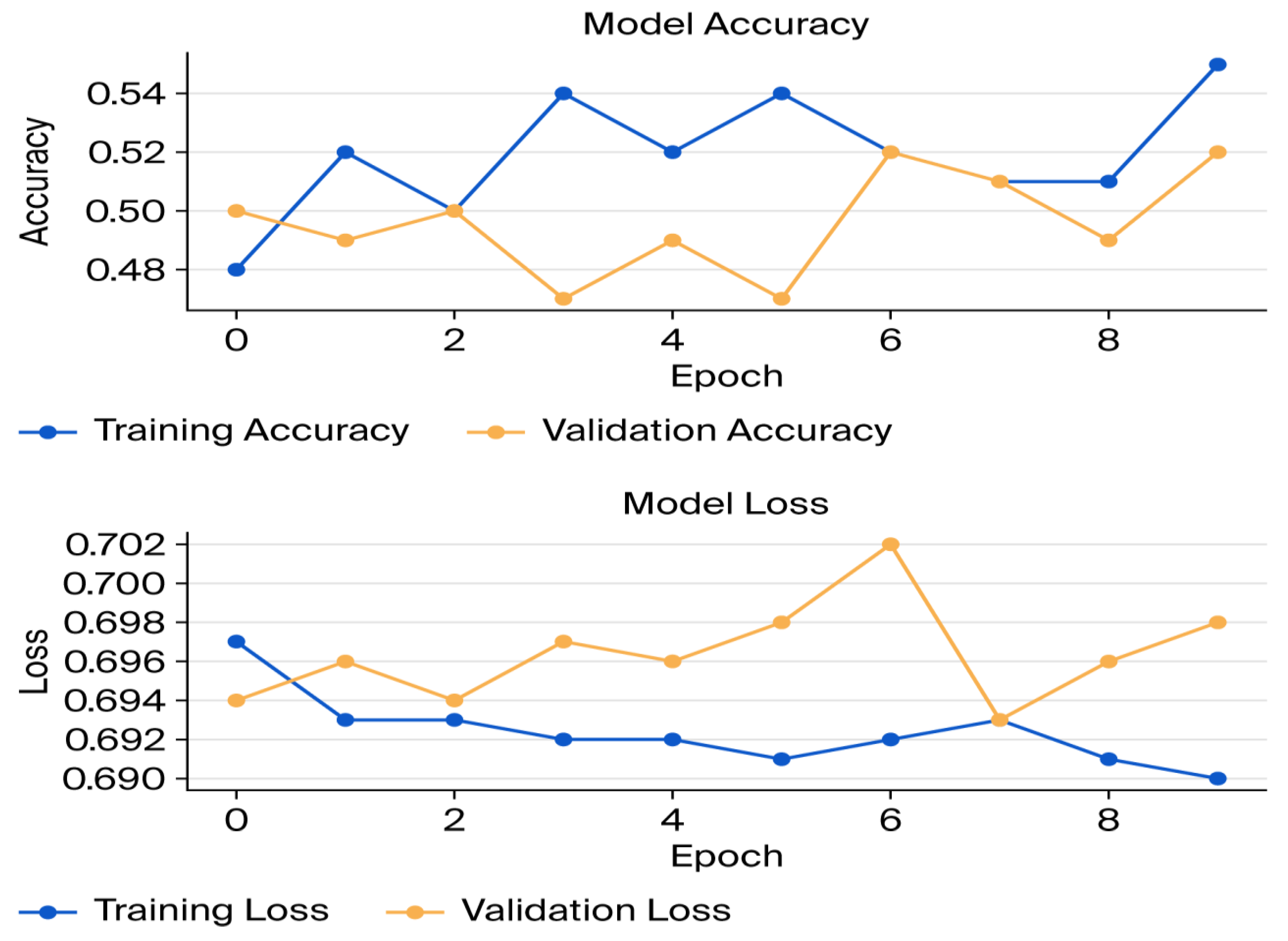
- ▪ Convolutional Neural Network (CNN)
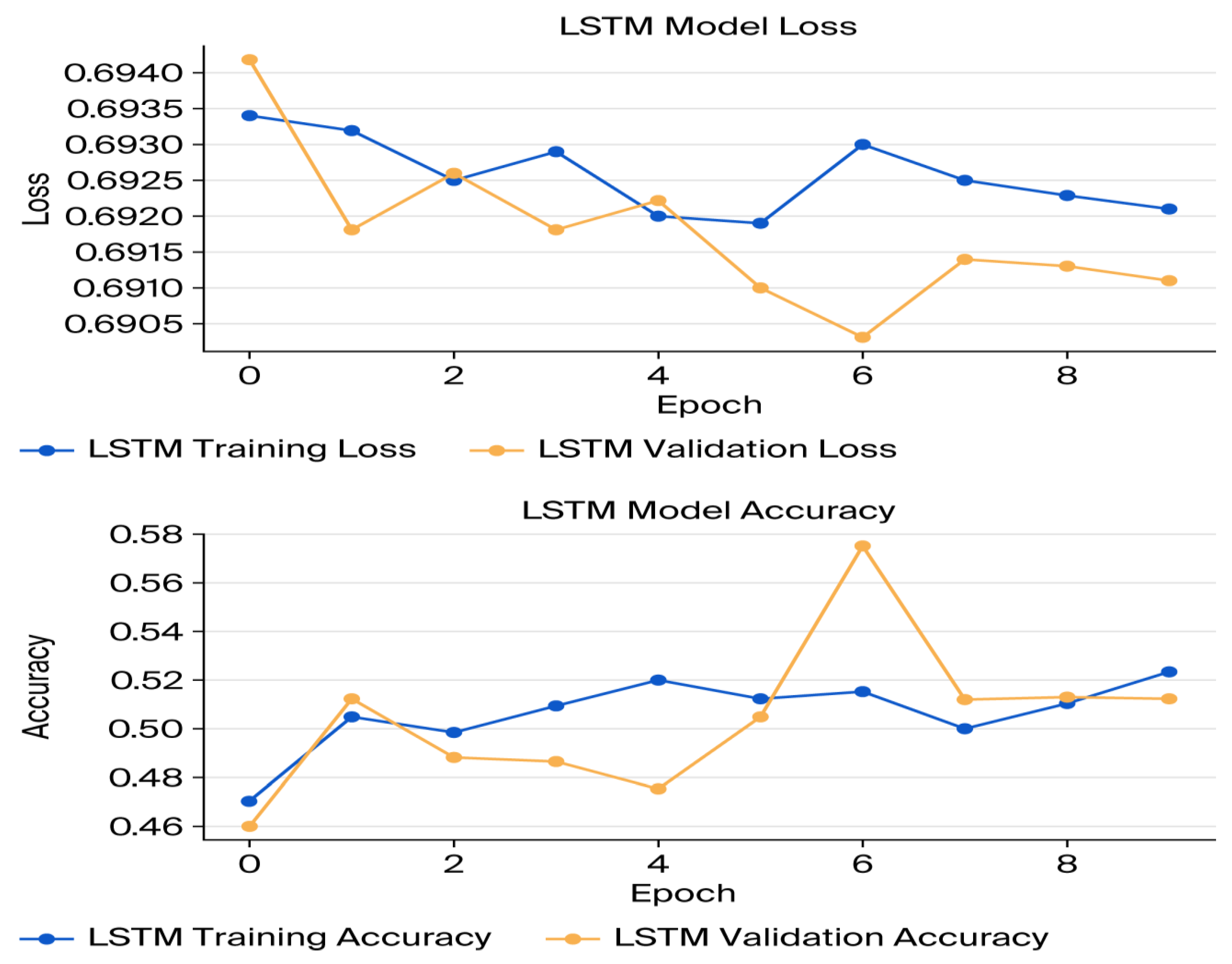
- ▪ LSTM Model
- ▪ Hybrid Model
5.4. Discussion
6. Conclusions
Author Contributions
Funding
Data Availability Statement
Conflicts of Interest
Abbreviations
| DDoS | Distributed Denial of Service |
| WBSNs | Wireless Body Sensor Networks |
| IoT | Internet of Things |
| CNN | Convolutional Neural Networks |
| LSTM | Long Short-Term Memory |
References
- Wakili, A.; Bakkali, S. Internet of Things in healthcare: An adaptive ethical framework for IoT in digital health. Clin. Ehealth 2024, 7, 92–105. [Google Scholar] [CrossRef]
- Sharma, N.; Jindal, N. Emerging artificial intelligence applications: Metaverse, IoT, cybersecurity, healthcare an overview. Multimed. Tools Appl. 2024, 83, 57317–57345. [Google Scholar] [CrossRef]
- Rahman, M.H.; Islam, T.; Amjad, M.H.H.; Shovon, M.S.S.; Chowdhury, M.E.; Ashakin, M.R.; Hossain, B.; Bhowmik, P.K.; Nurullah, M.; Sunny, A.R. Impact of Internet of Things (IoT) on Healthcare in Transforming Patient Care and Overcoming Operational Challenges. J. Angiother. 2024, 8, 10041. [Google Scholar] [CrossRef]
- Jansi, B.; Sumalatha, V. The security constructions and enhancements of smart wearable devices in modern technologies and health monitoring system. In Computational Intelligence for Clinical Diagnosis; Springer: Cham, Switzerland, 2023; pp. 461–471. [Google Scholar]
- Das, S.; Nayak, S.P.; Sahoo, B.; Nayak, S.C. Machine Learning in Healthcare Analytics: A State-of-the-Art Review. Arch. Comput. Methods Eng. 2024, 31, 3923–3962. [Google Scholar] [CrossRef]
- Singh, M.; Singh, J.; Ravi, V.; Gupta, A.; Alahmadi, T.; Shivahare, B.; Diwakar, M.; Tayal, M.; Singh, P. A Healthcare System Employing Lightweight CNN for Disease Prediction with Artificial Intelligence. Open Public Health J. 2024, 17, e18749445302023. [Google Scholar] [CrossRef]
- Rahman, A.; Debnath, T.; Kundu, D.; Khan, M.S.I.; Aishi, A.A.; Sazzad, S.; Sayduzzaman, M.; Band, S.S. Machine learning and deep learning-based approach in smart healthcare: Recent advances, applications, challenges and opportunities. AIMS Public Health 2024, 11, 58–109. [Google Scholar] [CrossRef] [PubMed] [PubMed Central]
- Ullah, S.; Mahmood, Z.; Ali, N.; Ahmad, T.; Buriro, A. Machine learning-based dynamic attribute selection technique for ddos attack classification in iot networks. Computers 2023, 12, 115. [Google Scholar] [CrossRef]
- Gaur, V.; Kumar, R. Analysis of machine learning classifiers for early detection of DDoS attacks on IoT devices. Arab. J. Sci. Eng. 2022, 47, 1353–1374. [Google Scholar] [CrossRef]
- Syed, N.F.; Baig, Z.; Ibrahim, A.; Valli, C. Denial of service attack detection through machine learning for the IoT. J. Inf. Telecommun. 2020, 4, 482–503. [Google Scholar] [CrossRef]
- Altulaihan, E.; Almaiah, M.A.; Aljughaiman, A. Anomaly Detection IDS for Detecting DoS Attacks in IoT Networks Based on Machine Learning Algorithms. Sensors 2024, 24, 713. [Google Scholar] [CrossRef]
- Neto, E.C.P.; Dadkhah, S.; Ferreira, R.; Zohourian, A.; Lu, R.; Ghorbani, A.A. CICIoT2023: A Real-Time Dataset and Benchmark for Large-Scale Attacks in IoT Environment. Sensors 2023, 23, 5941. [Google Scholar] [CrossRef]
- Khempetch, T.; Wuttidittachotti, P. DDoS attack detection using deep learning. IAES Int. J. Artif. Intell. 2021, 10, 382. [Google Scholar] [CrossRef]
- Yan, F.; Zhang, G.; Zhang, D.; Sun, X.; Hou, B.; Yu, N. TL-CNN-IDS: Transfer learning-based intrusion detection system using convolutional neural network. J. Supercomput. 2023, 79, 17562–17584. [Google Scholar] [CrossRef]
- Chen, Y.; Qin, X.; Wang, J.; Yu, C.; Gao, W. Fedhealth: A federated transfer learning framework for wearable healthcare. IEEE Intell. Syst. 2020, 35, 83–93. [Google Scholar] [CrossRef]
- Elsayed, M.S.; Le-Khac, N.A.; Dev, S.; Jurcut, A.D. Ddosnet: A deep-learning model for detecting network attacks. In Proceedings of the IEEE 21st International Symposium on “A World of Wireless, Mobile and Multimedia Networks” (WoWMoM), Cork, Ireland, 31 August–3 September 2020; pp. 391–396. [Google Scholar]
- Almaraz-Rivera, J.G.; Perez-Diaz, J.A.; Cantoral-Ceballos, J.A. Transport and application layer DDoS attacks detection to IoT devices by using machine learning and deep learning models. Sensors 2022, 22, 3367. [Google Scholar] [CrossRef]
- Aswad, F.M.; Ahmed, A.M.S.; Alhammadi, N.A.M.; Khalaf, B.A.; Mostafa, S.A. Deep learning in distributed denial-of-service attacks detection method for Internet of Things networks. J. Intell. Syst. 2023, 32, 20220155. [Google Scholar] [CrossRef]
- Hossain, M.D.; Ochiai, H.; Fall, D.; Kadobayashi, Y. LSTM-based network attack detection: Performance comparison by hyper parameter values tuning. In Proceedings of the 7th IEEE International Conference on Cyber Security and Cloud Computing (CSCloud)/6th IEEE International Conference on Edge Computing and Scalable Cloud (EdgeCom), New York, NY, USA, 1–3 August 2020; pp. 62–69. [Google Scholar]
- Nguyen, X.H.; Le, K.H. Robust detection of unknown DoS/DDoS attacks in IoT networks using a hybrid learning model. Internet Things 2023, 23, 100851. [Google Scholar] [CrossRef]
- Hizal, S.; Cavusoglu, U.; Akgun, D. A novel deep learning-based intrusion detection system for IoT DDoS security. Internet Things 2024, 28, 101336. [Google Scholar] [CrossRef]
- Abbas, S.; Bouazzi, I.; Ojo, S.; Al Hejaili, A.; Sampedro, G.A.; Almadhor, A.; Gregus, M. Evaluating deep learning variants for cyber-attacks detection and multi-class classification in IoT networks. PeerJ Comput. Sci. 2024, 10, e1793. [Google Scholar] [CrossRef]
- Ain, N.U.; Sardaraz, M.; Tahir, M.; Abo Elsoud, M.W.; Alourani, A. Securing IoT Networks Against DDoS Attacks: A Hybrid Deep Learning Approach. Sensors 2025, 25, 1346. [Google Scholar] [CrossRef]
- Ullah, Z.; Arif, F.; Haq, Q.M.; Khan, N.A.; Din, I.U.; Almogren, A.; Khan, M.A.; Alsaleh, O.; Guizani, M. Hybrid CNN-LSTM Model for DDoS Attack Detection in Internet of Things-based Healthcare Industry 5.0. IEEE Internet Things J. 2025, 12, 46075–46082. [Google Scholar] [CrossRef]
- Ibraheem, M.K.I.; Al-Abadi, A.A.J.; Mohamed, M.B.; Fakhfakh, A. A Security-Enhanced Energy Conservation with Enhanced Random Forest Classifier for Low Execution Time Framework (S-2EC-ERF) for Wireless Sensor Networks. Appl. Sci. 2024, 14, 2244. [Google Scholar] [CrossRef]
- Ullah, K.; Ahsan, M.; Hasanat, S.M.; Haris, M.; Yousaf, H.; Raza, S.F.; Tandon, R.; Abid, S.; Ullah, Z. Short-Term Load Forecasting: A Comprehensive Review and Simulation Study with CNN-LSTM Hybrids Approach. IEEE Access 2024, 12, 111858–111881. [Google Scholar] [CrossRef]
- Nkoro, E.C.; Njoku, J.N.; Nwakanma, C.I.; Lee, J.M.; Kim, D.S. Zero-Trust Marine Cyberdefense for IoT-Based Communications: An Explainable Approach. Electronics 2024, 13, 276. [Google Scholar] [CrossRef]
- Wang, Z.; Chen, H.; Yang, S.; Luo, X.; Li, D.; Wang, J. A lightweight intrusion detection method for IoT based on deep learning and dynamic quantization. PeerJ Comput. Sci. 2023, 9, e1569. [Google Scholar] [CrossRef]







| Layers | Parameter |
|---|---|
| Input | (batch, T, F) where T = timesteps in window (e.g., 50), F = selected features (20). |
| Conv1D | (filters = 64, kernel_size = 3, activiation = ‘ReLU’) |
| MaxPool1D | (pool_size = 2) |
| Dropout | (0.2) |
| LSTM | (64, relu) |
| Dropout | (0.5) |
| Dense | (num_classes, activation = ‘softmax’ or sigmoid) |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2026 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license.
Share and Cite
Belhaj Mohamed, M.; Bouzidi, D.; Khalid Ibraheem, M.; Al-Abadi, A.A.J.; Fakhfakh, A. Cyber Approach for DDoS Attack Detection Using Hybrid CNN-LSTM Model in IoT-Based Healthcare. Future Internet 2026, 18, 52. https://doi.org/10.3390/fi18010052
Belhaj Mohamed M, Bouzidi D, Khalid Ibraheem M, Al-Abadi AAJ, Fakhfakh A. Cyber Approach for DDoS Attack Detection Using Hybrid CNN-LSTM Model in IoT-Based Healthcare. Future Internet. 2026; 18(1):52. https://doi.org/10.3390/fi18010052
Chicago/Turabian StyleBelhaj Mohamed, Mbarka, Dalenda Bouzidi, Manar Khalid Ibraheem, Abdullah Ali Jawad Al-Abadi, and Ahmed Fakhfakh. 2026. "Cyber Approach for DDoS Attack Detection Using Hybrid CNN-LSTM Model in IoT-Based Healthcare" Future Internet 18, no. 1: 52. https://doi.org/10.3390/fi18010052
APA StyleBelhaj Mohamed, M., Bouzidi, D., Khalid Ibraheem, M., Al-Abadi, A. A. J., & Fakhfakh, A. (2026). Cyber Approach for DDoS Attack Detection Using Hybrid CNN-LSTM Model in IoT-Based Healthcare. Future Internet, 18(1), 52. https://doi.org/10.3390/fi18010052








