Synergistic Phishing Intrusion Detection: Integrating Behavioral and Structural Indicators with Hybrid Ensembles and XAI Validation
Abstract
1. Introduction
- RQ1: How do behavioral interface cues, such as mouse-over actions, pop-up events, hidden iframes, and right-click restrictions, interact with structural and domain-based indicators on phishing websites?
- RQ2: To what extent do behavioral features improve the clustering and profiling of phishing campaigns compared to using only structural or technical attributes?
- RQ3: How does the integration of behavioral features with traditional indicators influence the performance of phishing intrusion detection models, particularly in terms of classification accuracy and macro F1 score?
- RQ4: How do the observed behavioral phishing indicators relate to established theories of deception, HCI, and trust formation?
- We provide empirical evidence that subtle behavioral deception cues, including mouse-over effects, right-click blocking, hidden iframes, and pop-up triggers, significantly enhance phishing intrusion detection when combined with traditional structural indicators, addressing a gap in prior work.
- We introduce a hierarchical hybrid architecture that integrates PCA-based dimensionality reduction, phishing campaign profiling through K Means clustering, and a stacked ensemble classifier specifically designed to capture both structural and behavioral intrusion signals.
- We advance the use of SHAP-based Explainable AI from descriptive visualization to a formal validation mechanism, demonstrating the specific diagnostic contribution of behavioral features and improving transparency, interpretability, and forensic trustworthiness.
- We establish a conceptual link between behavioral deception mechanisms, Human Computer Interaction principles, trust formation, and signal detection theory, showing how interface rule violations translate into measurable behavioral indicators that enhance intrusion detection and XAI-grounded security interpretation.
2. Literature Review
2.1. What Is Phishing: A Brief Background
2.2. Factors and Techniques Used in Phishing Detection
2.3. Related Works
3. Materials and Methods
3.1. Problem Definition
 +} be the set of all labeled websites in the dataset, where each website wi is represented by a structured features comprising behavioral indicators (b), URL-based (u), domain (d), webpage-based (w), and traffic and search engine (t). Thus, the full representation of the website is defined as in Equation (1). Let the label space C = {1, 0} where denote a phishing (malicious) website and indicate a legitimate (benign) website.
+} be the set of all labeled websites in the dataset, where each website wi is represented by a structured features comprising behavioral indicators (b), URL-based (u), domain (d), webpage-based (w), and traffic and search engine (t). Thus, the full representation of the website is defined as in Equation (1). Let the label space C = {1, 0} where denote a phishing (malicious) website and indicate a legitimate (benign) website.3.2. Study Framework
3.3. Data Preparation and Feature Categorization
3.4. Exploratory Data Analysis (EDA) Procedure
Feature Integration and Clustering
3.5. Detection Framework: Dimensionality Reduction, Clustering, and Classification Modelling
3.5.1. Principal Component Analysis (PCA)
- Compute covariance matrix (Equation (11)):
- 2.
- Compute eigenvectors and eigenvalues: Find and such that
- 3.
- Project the data onto the top k components: choose the top k eigenvectors that capture the most variance from the projection matrix . Then project
3.5.2. K-Means Clustering
3.5.3. Classification Approach
- Stacking Model A (Meta: Logistic Regression) used LogReg as its level-1 meta-learner while RF and XGBoost and Gradient Boosting and logistic regression operated as level-0 models.
- Stacking Model B (Meta: Support Vector Classifier) used RF and XGBoost and Gradient Boosting and Logistic Regression as level-0 models while SVC operated as the level-1 meta-learner. The level-0 models produced output that served as input to the level-1 meta-classifier for predictions.
- In stacknet model A, .
- In stacknet model B, .
3.6. Model Explainability with Shapley Additive exPlanations (SHAP)
3.7. Model Evaluation
3.8. Experimental Setup
4. Results and Discussion
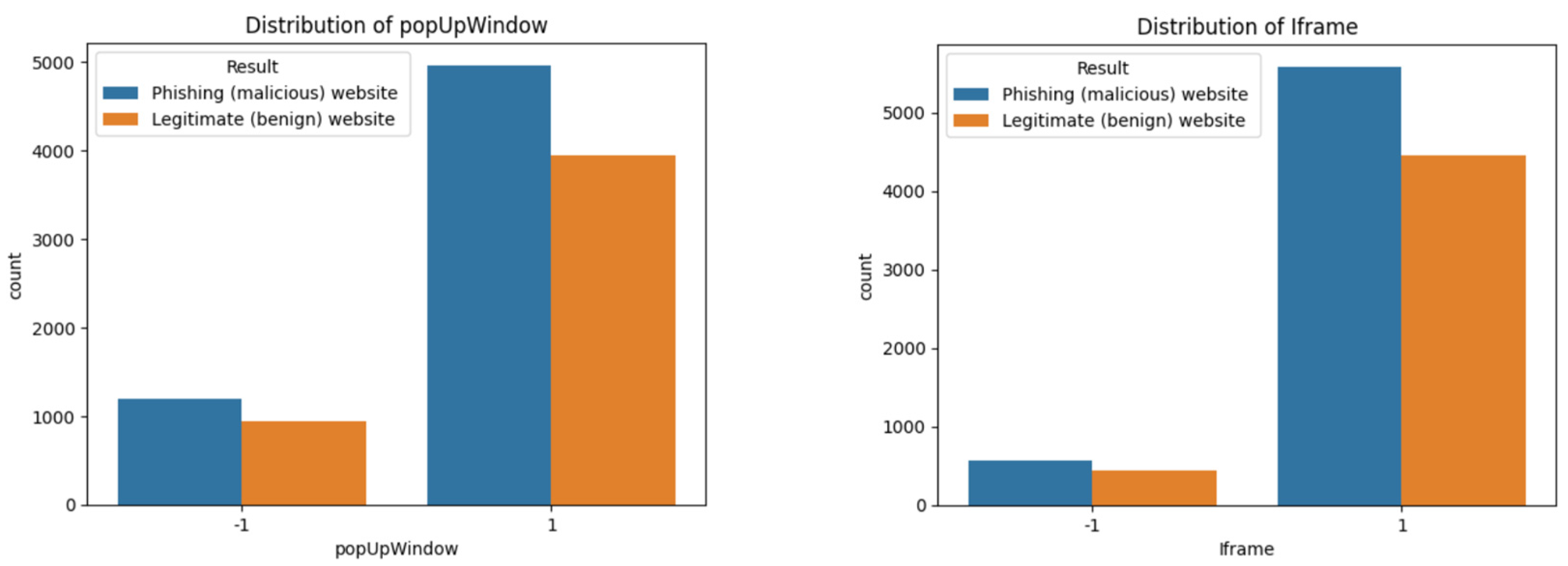
4.1. Exploratory Data Analysis (EDA) Findings
4.2. Clustering Analysis Using PCA and K-Means
4.3. Performance of Base Models Using Only Website Behavioral Features
4.4. Performance of Base Models with All Website Features
Model Performance Using Only Structural Features
4.5. Performance of Stacked Ensemble Models
4.6. Feature Importance and Explainability Analysis
4.7. Models Statistical Significance Testing Using McNemar’s Test
4.8. Comparative Analysis with Related Studies
4.9. Theoretical Implications
5. Limitations, Conclusions, and Future Work
5.1. Limitations and Conclusions
5.2. Future Work
Author Contributions
Funding
Data Availability Statement
Conflicts of Interest
Appendix A
Appendix A.1. Computational Steps for Stacked Ensemble Models A and B
| Algorithm A1: Training Procedure for Stacked Ensemble Models A and B | |
| Input: | |
| |
| Output: | |
| |
|
1. Initialize base models: RF ← RandomForestClassifier(n_estimators = 100) XGB ← XGBClassifier(n_estimators = 100) GB ← GradientBoostingClassifier(n_estimators = 100) LR ← LogisticRegression(max_iter = 1000) 2. Create Stacking Ensemble A: StackingClassifier_A ← Stack [RF,XGB,GB,LR] → Meta: LogisticRegression 3. Fit StackingClassifier_A on X_train,y_train 4. Create Stacking Ensemble B: StackingClassifier_B ← Stack [RF,XGB,GB,LR] → Meta: SVC (probability = True) 5. Fit StackingClassifier_B on X_train,y_train 6. Return trained StackingClassifier_A and StackingClassifier_B | |
Appendix A.2. Stacked Ensemble Models A and B Computational Complexity
| Component | Model(s) | Complexity |
| Base Learners | RF | O(T·d·n log n) |
| XGB, GB | O(T·d·n) | |
| LR | O(T·d·I) | |
| Meta Learner (Model A) | Logistic Regression | O(n·I) |
| Meta Learner (Model B) | SVC (probability) | O(n2) |
| Model A is more efficient for large datasets due to the linear meta-learner. Model B might become computationally expensive at the meta-level if the dataset is large, due to the quadratic complexity of SVC with probability estimation. | ||
Appendix B
Appendix B.1. Hyperparameter Search Space for Grid Search Optimization
| Model | Hyperparameter | Parameter Range (ε) |
| Random Forest (RF) | Number of Estimators (n_estimators) | {50, 100, 200} |
| Maximum Depth (max_depth) | {6, 8, 10} | |
| Gradient Boosting Classifier (GBC) | Number of Estimators (n_estimators) | {50, 100, 200} |
| Learning Rate (learning_rate) | {0.05, 0.1, 0.2} | |
| Maximum Depth (max_depth) | {3, 5, 7} | |
| LightGBM (LGBM) | Number of Leaves (num_leaves) | {31, 63, 127} |
| Support Vector Machine (SVM) | Regularization Parameter (C) | {0.1, 1, 10} |
| Kernel Type (kernel) | {rbf, poly} |
Appendix B.2. Cross-Validated Grid Search Results for Stacking Models A and B
| Model | Accuracy | Std. Dev. | Meta-Learner | C Value | Learning_Rate (GB) | n_estimators (RF, XGB) |
| Model A | 0.973 | ±0.00 | Logistic Regression | 0.1 | 0.1 | 100 |
| Model A | 0.973 | ±0.00 | Logistic Regression | 1.0 | 0.1 | 100 |
| Model A | 0.972 | ±0.00 | Logistic Regression | 10.0 | 0.1 | 100 |
| Model B | 0.973 | ±0.00 | SVC (probability = True) | 0.1 | 0.1 | 100 |
| Model B | 0.970 | ±0.00 | SVC (probability = True) | 1.0 | 0.1 | 100 |
Appendix C. K-Means Clustering Results (K = 3 and K = 4) on PCA-Reduced Feature Spaces with 90%, 95%, and 99% Explained Variance Thresholds

References
- Gautam, A.; Prakash, A.; Kaushal, G. Artificial Intelligence in Cybersecurity. Int. J. Adv. Res. Sci. Commun. Technol. 2024, 4, 607–610. [Google Scholar] [CrossRef]
- Anti-Phishing Working Group (APWG). Phishing Activity Trends Report, Q1 2023. 2023. Available online: https://apwg.org (accessed on 12 June 2025).
- Tang, L.; Mahmoud, Q.H. A Survey of Machine Learning-Based Solutions for Phishing Website Detection. Mach. Learn. Knowl. Extr. 2021, 3, 672–694. [Google Scholar] [CrossRef]
- Taha, A. Intelligent ensemble learning approach for phishing website detection based on weighted soft voting. Mathematics 2021, 9, 2799. [Google Scholar] [CrossRef]
- Abdelhamid, N.; Ayesh, A.; Thabtah, F. Phishing detection based Associative Classification data mining. Expert Syst. Appl. 2014, 41, 5948–5959. [Google Scholar] [CrossRef]
- Salem, A.H.; Azzam, S.M.; Emam, O.E.; Abohany, A.A. Advancing Cybersecurity: A Comprehensive Review of AI-Driven Detection Techniques; Springer International Publishing: Berlin/Heidelberg, Germany, 2024; Volume 11. [Google Scholar]
- Yan, C.; Han, X.; Zhu, Y.; Du, D.; Lu, Z.; Liu, Y. Phishing behavior detection on different blockchains via adversarial domain adaptation. Cybersecurity 2024, 7, 45. [Google Scholar] [CrossRef]
- Alhuzali, A.; Alloqmani, A.; Aljabri, M.; Alharbi, F. In-Depth Analysis of Phishing Email Detection: Evaluating the Performance of Machine Learning and Deep Learning Models Across Multiple Datasets. Appl. Sci. 2025, 15, 3396. [Google Scholar] [CrossRef]
- Sahingoz, S.O.K.; Buber, E.; Demir, O.; Diri, B. Machine learning based phishing detection from URLs. Expert Syst. Appl. 2019, 117, 345–357. [Google Scholar] [CrossRef]
- Adane, K.; Beyene, B. Machine Learning and Deep Learning Based Phishing Websites Detection: The Current Gaps And Next Directions. Rev. Comput. Eng. Res. 2022, 9, 13–29. [Google Scholar] [CrossRef]
- Zieni, R.; Massari, L.; Calzarossa, M.C. Phishing or Not Phishing? A Survey on the Detection of Phishing Websites. IEEE Access 2023, 11, 18499–18519. [Google Scholar] [CrossRef]
- Kavya, S.; Sumathi, D. Staying ahead of phishers: A review of recent advances and emerging methodologies in phishing detection. Artif. Intell. Rev. 2024, 58, 50. [Google Scholar] [CrossRef]
- Taha, M.A.; Jabar, H.D.A.; Mohammed, W.K. A Machine Learning Algorithms for Detecting Phishing Websites: A Comparative Study. Iraqi J. Comput. Sci. Math. 2024, 5, 275–286. [Google Scholar] [CrossRef]
- Buller, D.B.; Burgoon, J.K. Interpersonal Deception Theory. Commun. Theory 1996, 6, 203–242. [Google Scholar] [CrossRef]
- Fogg, B.J. Prominence-Interpretation theory: Explaining how people assess credibility online. In Proceedings of the Human Factors in Computing Systems, Ft. Lauderdale, FL, USA, 5–10 April 2023; pp. 722–723. [Google Scholar] [CrossRef]
- Fogg, B.J.; Soohoo, C.; Danielson, D.R.; Marable, L.; Stanford, J.; Tauber, E.R. How do users evaluate the credibility of Web sites?: A study with over 2500 participants. In Proceedings of the 2003 Conference on Designing for User Experiences DUX’03, San Francisco, CA, USA, 6–7 June 2003; pp. 1–15. [Google Scholar] [CrossRef]
- Li, W.; Manickam, S.; Chong, Y.-W.; Leng, W.; Nanda, P. A State-of-the-Art Review on Phishing Website Detection Techniques. IEEE Access 2024, 12, 187976–188012. [Google Scholar] [CrossRef]
- Hossain, A.; Khin, L.; Wison, G. An Intelligent Phishing Detection and Protection Scheme Using a Fusion of Images, Frames and Text. 2020. Available online: https://www.researchgate.net/publication/353482275_An_Intelligent_Phishing_Detection_and_Protection_Scheme_using_a_fusion_of_Images_Frames_and_Text (accessed on 10 June 2025).
- Jain, A.K.; Gupta, B.B. A machine learning based approach for phishing detection using hyperlinks information. J. Ambient. Intell. Humaniz. Comput. 2018, 10, 2015–2028. [Google Scholar] [CrossRef]
- Safi, A.; Singh, S. A systematic literature review on phishing website detection techniques. J. King Saud Univ. Comput. Inf. Sci. 2023, 35, 590–611. [Google Scholar] [CrossRef]
- Li, Y.; Yang, Z.; Chen, X.; Yuan, H.; Liu, W. A stacking model using URL and HTML features for phishing webpage detection. Futur. Gener. Comput. Syst. 2019, 94, 27–39. [Google Scholar] [CrossRef]
- Karim, A.; Shahroz, M.; Mustofa, K.; Belhaouari, S.B.; Joga, S.R.K. Phishing Detection System Through Hybrid Machine Learning Based on URL. IEEE Access 2023, 11, 36805–36822. [Google Scholar] [CrossRef]
- Hamadouche, S.; Boudraa, O.; Gasmi, M. Combining Lexical, Host, and Content-based features for Phishing Websites detection using Machine Learning Models. ICST Trans. Scalable Inf. Syst. 2024, 11, 1–15. [Google Scholar] [CrossRef]
- Joshi, A.; Lloyd, L.; Westin, P.; Seethapathy, S. Using Lexical Features for Malicious URL Detection—A Machine Learning Approach. arXiv 2019, arXiv:1910.06277. Available online: http://arxiv.org/abs/1910.06277 (accessed on 10 June 2025).
- Hong, J.; Kim, T.; Liu, J.; Park, N.; Kim, S.-W. Phishing URL Detection with Lexical Features and Blacklisted Domains. In Adaptive Autonomous Secure Cyber Systems; Springer International Publishing: Cham, Switzerland, 2020; pp. 253–267. [Google Scholar]
- Haq, Q.E.U.; Faheem, M.H.; Ahmad, I. Detecting Phishing URLs Based on a Deep Learning Approach to Prevent Cyber-Attacks. Appl. Sci. 2024, 14, 10086. [Google Scholar] [CrossRef]
- Prakash, P.; Kumar, M.; Kompella, R.R.; Gupta, M. PhishNet: Predictive Blacklisting to Detect Phishing Attacks. In Proceedings of the 2010 Proceedings IEEE INFOCOM, San Diego, CA, USA, 14–19 March 2010; pp. 1–5. [Google Scholar] [CrossRef]
- Rashid, F.; Doyle, B.; Han, S.C.; Seneviratne, S. Phishing URL detection generalisation using Unsupervised Domain Adaptation. Comput. Netw. 2024, 245, 110398. [Google Scholar] [CrossRef]
- Catal, C.; Giray, G.; Tekinerdogan, B.; Kumar, S.; Shukla, S. Applications of Deep Learning for Phishing Detection: A Systematic Literature Review; Springer: London, UK, 2022; Volume 64. [Google Scholar]
- Al-Sarem, M.; Saeed, F.; Al-Mekhlafi, Z.G.; Mohammed, B.A.; Al-Hadhrami, T.; Alshammari, M.T.; Alreshidi, A.; Alshammari, T.S. An optimized stacking ensemble model for phishing websites detection. Electronics 2021, 10, 1285. [Google Scholar] [CrossRef]
- Mohamed, N.; Taherdoost, H.; Madanchian, M. Enhancing Spear Phishing Defense with AI: A Comprehensive Review and Future Directions. ICST Trans. Scalable Inf. Syst. 2024, 12, 1–10. [Google Scholar] [CrossRef]
- Calzarossa, M.C.; Giudici, P.; Zieni, R. An assessment framework for explainable AI with applications to cybersecurity. Artif. Intell. Rev. 2025, 58, 150. [Google Scholar] [CrossRef]
- Molnar, C. Interpretable Machine Learning: A Guide for Making Black Box Models Explainable, 2nd ed.; Independently Published: Chicago, IL, USA, 2020; Available online: https://books.google.com/books/about/Interpretable_Machine_Learning.html?id=jBm3DwAAQBAJ (accessed on 10 June 2025).
- Smith, G. Top Phishing Statistics for 2025: Latest Figures and Trends. 2025. Available online: https://www.stationx.net/phishing-statistics/ (accessed on 10 June 2025).
- Hoxhunt. Phishing Trends Report (Updated for 2025). 2025. Available online: https://hoxhunt.com/guide/phishing-trends-report? (accessed on 10 June 2025).
- Egress. Must-Know Phishing Statistics for 2025. 2024. Available online: https://www.egress.com/blog/security-and-email-security/must-know-phishing-statistics-for-2025? (accessed on 10 June 2025).
- National University. 101 Cybersecurity Statistics and Trends for 2025. 2025. Available online: https://www.nu.edu/blog/cybersecurity-statistics/? (accessed on 10 June 2025).
- Bhattacharya, T.; Veeramalla, S.; Tanniru, V. A Survey on Retrieving Confidential Data Using Phishing Attack. In Proceedings of the 2023 Congress in Computer Science, Computer Engineering, & Applied Computing (CSCE), Las Vegas, NV, USA, 24–27 July 2023; pp. 2528–2535. [Google Scholar] [CrossRef]
- Alhashmi, S.; Alneyadi, A.; Alshehhi, M.; Lamaazi, H. Mobile and Web Applications Clones: A Comprehensive Study. In Proceedings of the 2023 International Wireless Communications and Mobile Computing (IWCMC), Marrakesh, Morocco, 19–23 June 2023; pp. 464–469. [Google Scholar] [CrossRef]
- Akanbi, O.A.; Amiri, I.S.; Fazeldehkordi, E. A Machine-Learning Approach to Phishing Detection and Defense; Elsevier: Amsterdam, The Netherlands, 2014. [Google Scholar]
- Basit, A.; Zafar, M.; Liu, X.; Javed, A.R.; Jalil, Z.; Kifayat, K. A comprehensive survey of AI-enabled phishing attacks detection techniques. Telecommun. Syst. 2021, 76, 139–154. [Google Scholar] [CrossRef]
- Wang, Y.; Ma, W.; Xu, H.; Liu, Y.; Yin, P. A Lightweight Multi-View Learning Approach for Phishing Attack Detection Using Transformer with Mixture of Experts. Appl. Sci. 2023, 13, 7429. [Google Scholar] [CrossRef]
- Zhou, J.; Cui, H.; Li, X.; Yang, W.; Wu, X. A Novel Phishing Website Detection Model Based on LightGBM and Domain Name Features. Symmetry 2023, 15, 180. [Google Scholar] [CrossRef]
- Adebowale, M.A.; Lwin, K.T.; Hossain, M.A. Intelligent phishing detection scheme using deep learning algorithms. J. Enterp. Inf. Manag. 2020, 36, 747–766. [Google Scholar] [CrossRef]
- Dhanavanthini, P.; Chakkravarthy, S.S. Phish-Armour: Phishing detection using deep recurrent neural networks. Soft Comput. 2023. [Google Scholar] [CrossRef]
- Calzarossa, M.C.; Giudici, P.; Zieni, R. How robust are ensemble machine learning explanations? Neurocomputing 2025, 630, 129686. [Google Scholar] [CrossRef]
- Lim, B.; Huerta, R.; Sotelo, A.; Quintela, A.; Kumar, P. EXPLICATE: Enhancing Phishing Detection through Explainable AI and LLM-Powered Interpretability. arXiv 2025, arXiv:2503.20796. [Google Scholar] [CrossRef]
- Kumar, P.P.; Jaya, T.; Rajendran, V. SI-BBA—A novel phishing website detection based on Swarm intelligence with deep learning. Mater. Today Proc. 2023, 80, 3129–3139. [Google Scholar] [CrossRef]
- Rasymas, T.; Dovydaitis, L. Detection of Phishing URLs by Using Deep Learning Approach and Multiple Features Combinations. Balt. J. Mod. Comput. 2020, 8, 471–483. [Google Scholar] [CrossRef]
- Elkouay, A.; Moussa, N.; Madani, A. Graph-Based phishing detection: URLGBM model driven by machine learning. Int. J. Comput. Appl. 2024, 46, 481–495. [Google Scholar] [CrossRef]
- Jakob, N. Usability Engineering; Academic Press Limited: London, UK, 1993. [Google Scholar]
- Jo, J.; Cho, J.; Moon, J. A malware detection and extraction method for the related information using the ViT attention mechanism on Android operating system. Appl. Sci. 2023, 13, 6839. [Google Scholar] [CrossRef]
- Shaukat, M.W.; Amin, R.; Muslam, M.M.A.; Alshehri, A.H.; Xie, J. A hybrid approach for alluring ads phishing attack detection using machine learning. Sensors 2023, 23, 8070. [Google Scholar] [CrossRef]
- Moussavou Boussougou, M.K.; Park, D.-J. Attention-based 1D CNN-BiLSTM hybrid model enhanced with FastText word embedding for Korean voice phishing detection. Mathematics 2023, 11, 3217. [Google Scholar] [CrossRef]
- Nti, I.K.; Somanathan, A.R. A Scalable RF-XGBoost Framework for Financial Fraud Mitigation. IEEE Trans. Comput. Soc. Syst. 2022, 11, 1556–1563. [Google Scholar] [CrossRef]
- Yadollahi, M.M.; Shoeleh, F.; Serkani, E.; Madani, A.; Gharaee, H. An Adaptive Machine Learning Based Approach for Phishing Detection Using Hybrid Features. In Proceedings of the 2019 5th International Conference on Web Research (ICWR), Tehran, Iran, 24–25 April 2019; pp. 281–286. [Google Scholar] [CrossRef]
- Green, D.M.; Swets, J.A. Signal Detection Theory and Psychophysics; Wiley & Sons, Inc.: New York, NY, USA, 1974; Volume 27. [Google Scholar]
- Mohammad, R.M.; Thabtah, F.; McCluskey, L. Predicting phishing websites based on self-structuring neural network. Neural Comput. Appl. 2014, 25, 443–458. [Google Scholar] [CrossRef]
- Omari, K. Comparative Study of Machine Learning Algorithms for Phishing Website Detection. Int. J. Adv. Comput. Sci. Appl. 2023, 14, 417–425. [Google Scholar] [CrossRef]
- Lakshmi, L.; Reddy, M.P.; Santhaiah, C.; Reddy, U.J. Smart Phishing Detection in Web Pages Using Supervised Deep Learning Classification and Optimization Technique ADAM. Wirel. Pers. Commun. 2021, 118, 3549–3564. [Google Scholar] [CrossRef]
















| Ref. | Methodology (Machine Learning or AI Module) | Study Objectives | Input Features | Research Gap (Limitation) |
|---|---|---|---|---|
| [44] | Deep Learning (Convolutional Neural Networks) | Design and develop a deep learning-based phishing detection solution leveraging URL and website content (images, text, frames). | These include URL features, website images, text content, and frames. | The computational complexity of deep learning might limit its application in resource-constrained environments. |
| [45] | Deep Learning (Recurrent Neural Networks) | Achieve high accuracy in detecting malicious URLs using RNNs, focusing solely on URL text. | URL text. | The system is limited to URL text analysis and may not detect phishing sites with benign-looking URLs but malicious content. |
| [47] | Explainable AI, Large Language Models | Develop an AI framework for real-time phishing detection with enhanced interpretability to build user trust. | Not specified. | Preliminary results require further validation in real-world scenarios. |
| [48] | Swarm Intelligence (Binary Bat Algorithm), Deep Learning | Propose a deep learning-based swarm intelligence-binary bat algorithm for detecting phishing URLs. | URL features. | Computational complexity may hinder real-time applications. |
| [49] | Deep Learning (CNN, LSTM) | Compare different feature combinations (lexical, character-level, and word-level embeddings) for phishing URL classification. | These include lexical features, character-level embeddings, and word-level embeddings. | The computational complexity of deep learning might limit its application in resource-constrained environments. |
| [13] | Machine Learning (Random Forest, Decision Tree, XGBoost) | Compare the performance of various machine learning algorithms in detecting phishing websites. | Website features. | The study is limited to specific algorithms and may not reflect the performance of other models. |
| Features Category | Features |
|---|---|
| Behavioral | ‘on_mouseover,’ ‘RightClick,’ ‘popUpWindow,’ ‘Iframe’ |
| URL-based | ‘having_IP_Address,’ ‘URL_Length,’ ‘Shortening_Service,’ ‘having_At_Symbol,’ ‘double_slash_redirecting,’ ‘Prefix_Suffix’ |
| Domain | ‘having_Sub_Domain,’ ‘SSLfinal_State,’ ‘Domain_registeration_length,’ ‘age_of_domain,’ DNSRecord’ |
| Webpage-based | ‘Favicon,’ ‘port,’ HTTPS_token,’ Request_URL,’ ‘URL_of_Anchor,’ ‘Links_in_tags,’ ‘SFH,’ ‘Submitting_to_email,’ ‘Abnormal_URL,’ ‘Redirect’ |
| Traffic & Search Engine | ‘web_traffic,’ ‘Page_Rank,’ ‘Google_Index,’ ‘Links_pointing_to_page,’ ‘Statistical_report’ |
| Model | Hyperparameters |
|---|---|
| Random Forest (RF) | n_estimators = 100, max_features = ’sqrt’, criterion = ’gini’, random_state = 42 |
| XGBoost (XGB) | n_estimators = 100, eval_metric = ’logloss’, use_label_encoder = False, objective = ’binary:logistic’, random_state = 42 |
| Gradient Boosting (GB) | n_estimators = 100, learning_rate = 0.1, loss = ’log_loss’, max_depth = 3, random_state = 42 |
| Logistic Regression (LR) | penalty = ’l2′, solver = ’lbfgs’, max_iter = 1000, C = 0.1 |
| SVC | C = 0.1 |
| K-Means Clustering | n_clusters = 2 (final), with sensitivity analysis for K = 2, 3, 4; random_state = 42 |
| Principal Component Analysis (PCA) | n_components = 0.95 (final), with sensitivity analysis for 90%, 95%, 99% explained variance |
| PCA Variance (%) | Components | K = 2 (Silh/DB) | K = 3 (Silh/DB) | K = 4 (Silh/DB) |
|---|---|---|---|---|
| 90% | 19 | 0.2921/1.7888 | 0.3046/1.5290 | 0.1290/2.0189 |
| 95% | 23 | 0.2796/1.8457 | 0.2907/1.5848 | 0.1201/2.1135 |
| 99% | 28 | 0.2797/1.9096 | 0.2850/1.6354 | 0.1140/2.1650 |
| Model | Behavioral Only | Structural Only | Combined | |||
|---|---|---|---|---|---|---|
| Accuracy | Macro F1 | Accuracy | Macro F1 | Accuracy | Macro F1 | |
| Random Forest | 0.50 | 0.40 | 0.91 | 0.91 | 0.97 | 0.97 |
| XGBoost | 0.50 | 0.40 | 0.91 | 0.91 | 0.97 | 0.97 |
| Gradient Boosting | 0.50 | 0.40 | 0.90 | 0.90 | 0.94 | 0.94 |
| Logistic Regression | 0.50 | 0.40 | 0.88 | 0.88 | 0.91 | 0.91 |
| Model | Meta-Learner | Training Time (s) | Testing Time (s) |
|---|---|---|---|
| Stacked A | Logistic Regression | 9.87 | 0.11 |
| Stacked B | Support Vector Classifier (SVC) | 12.15 | 0.31 |
| Reference | Dataset | Dataset Description | Technique | Evaluation Metrics | |
|---|---|---|---|---|---|
| F1-Score (%) | Accuracy (%) | ||||
| [44] | PhishTank, Common Crawl, OpenPhish | Uses URL, text, images, frame content (per paper) | Hybrid deep learning (CNN & LSTM) | X | 93.28 |
| [45] | PhishTank, Common Crawl, OpenPhish | URL-based features only | Federated Learning + Deep NN | 90.50 | 90.50 |
| [13] | UCI Phishing Websites Dataset | Structured features from URLs | RF, DT, XGBoost | X | 94.57–96.89 |
| [48] | PhishTank, Alexa, UNB ISCX 2016 | Character-level URL features only | Deep learning (1D CNN) | X | 94.8 |
| [49] | PhishTank + public benign URL sources | Character & word-level embeddings; lexical features | Deep neural network (CNN + GRU, char & word embeddings) | X | 94.4 |
| [58] | UCI Phishing Websites Dataset | Structured features from URLs | Functional Tree | 96.1 | 96.07 |
| [59] | UCI Phishing Websites Dataset | Structured features from URLs | LR, KNN, SVM, NB, DT, RF and Gradient Boosting | 96.9 | 97.2 |
| [60] | UCI Phishing Websites Dataset | Structured features from URLs | DNN + Adam | X | 96 |
| Our study | UCI Phishing Dataset | Features include URL + behavioral metadata | Stacking, XGBoost, Random Forest | 97 | 97 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2026 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license.
Share and Cite
Nti, I.K.; Ozer, M.; Li, C. Synergistic Phishing Intrusion Detection: Integrating Behavioral and Structural Indicators with Hybrid Ensembles and XAI Validation. Future Internet 2026, 18, 30. https://doi.org/10.3390/fi18010030
Nti IK, Ozer M, Li C. Synergistic Phishing Intrusion Detection: Integrating Behavioral and Structural Indicators with Hybrid Ensembles and XAI Validation. Future Internet. 2026; 18(1):30. https://doi.org/10.3390/fi18010030
Chicago/Turabian StyleNti, Isaac Kofi, Murat Ozer, and Chengcheng Li. 2026. "Synergistic Phishing Intrusion Detection: Integrating Behavioral and Structural Indicators with Hybrid Ensembles and XAI Validation" Future Internet 18, no. 1: 30. https://doi.org/10.3390/fi18010030
APA StyleNti, I. K., Ozer, M., & Li, C. (2026). Synergistic Phishing Intrusion Detection: Integrating Behavioral and Structural Indicators with Hybrid Ensembles and XAI Validation. Future Internet, 18(1), 30. https://doi.org/10.3390/fi18010030









