Cybersecurity in Higher Education Institutions: A Systematic Review of Emerging Trends, Challenges and Solutions
Abstract
1. Introduction
- To identify and analyse current cybersecurity trends in HEIs. The SLR specifically seeks to explore the adoption of emerging technologies and the impact of digital transformation on the cybersecurity landscape of HEIs.
- To investigate the effectiveness of cybersecurity interventions and assess the impact of technical measures such as IDPSs, ZTAs, cloud computing, AI and remote learning on enhancing cybersecurity resilience.
- To understand the challenges faced by HEIs in cybersecurity implementation, particularly how the open and collaborative nature of HEIs influences their vulnerability to cyberthreats. The SLR further explores the organisational, technical and financial barriers to effective cybersecurity management.
- To provide actionable insights, best practices and recommendations for addressing cybersecurity risks in HEIs. The recommendations highlight future research areas and propose strategies for overcoming barriers, with the aim of advancing and improving the cybersecurity postures of HEIs.
2. Background—Overview of Related Literature
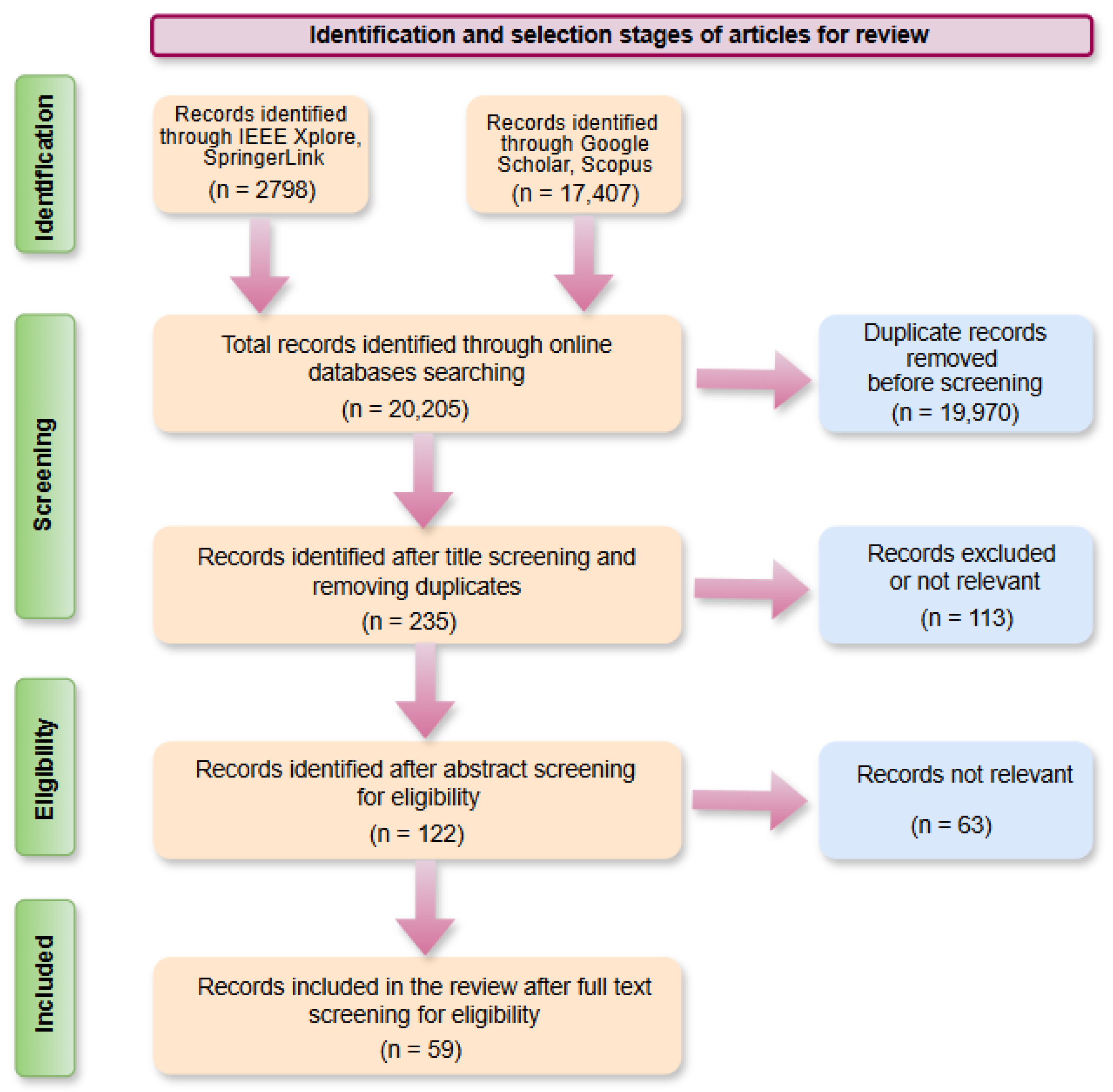
3. Methods
3.1. Research Questions
- RQ1—What are the most prevalent threats, vulnerabilities and current trends in cybersecurity practices within HEIs?
- RQ2—How effective are HEIs adapting to cybersecurity interventions and emerging trends such as IDPS, ZTA, cloud computing, AI and remote learning in mitigating cyberthreats?
- RQ3—What are the primary challenges, including budgetary constraints, resource limitations and organisational policies, impacting HEIs from implementing and maintaining robust cybersecurity measures?
- RQ4—What are the best practices for strengthening cybersecurity in HEIs, and key areas for future research to address unresolved challenges and emerging threats?
3.2. Eligibility Criteria
3.3. Quality Assessment
- High quality (≥80%).
- Moderate quality (60–79%).
- Low quality (<60%).
3.4. Data Extraction
3.5. Data Synthesis
- Initial Coding: Key statements, findings, challenges and proposed solutions were extracted from each study. Codes were assigned inductively, based on recurring security issues (e.g., phishing, ransomware, governance failures), technological themes (e.g., intrusion detection, access management) and institutional factors (e.g., user awareness, policy maturity).
- Theme Development: Codes were grouped into broader thematic categories that reflected patterns across studies. Major themes included
- Prevailing cybersecurity threats in HEIs;
- Institutional vulnerabilities;
- Technical and administrative countermeasures;
- Human-centric factors;
- Governance and compliance issues;
- Capacity-building and training needs.
- Integrative Synthesis: Themes were analysed to highlight relationships, gaps and divergences among the studies. This stage produced an integrative interpretation of how challenges and solutions intersect within HEI environments, allowing the findings to be consolidated into a coherent framework. These are presented in the Discussion (Section 5) and Findings (Section 6).
3.6. Limitations
4. Motivation
5. Discussion
5.1. RQ1—What Are the Most Prevalent Threats, Vulnerabilities and Current Trends in Cybersecurity Practices Within HEIs?
5.2. RQ2—How Effective Are HEIs Adapting to Cybersecurity Interventions and Emerging Trends Such as IDPS, ZTA, Cloud Computing, AI and Remote Learning in Mitigating Cyberthreats?
5.3. RQ3—What Are the Primary Challenges, Including Budgetary Constraints, Resource Limitations and Organisational Policies, Impacting HEIs from Implementing and Maintaining Robust Cybersecurity Measures?
5.4. RQ4—What Are the Best Practices for Strengthening Cybersecurity in HEIs, and Key Areas for Future Research to Address Unresolved Challenges and Emerging Threats?
6. Findings and Effectiveness of Cybersecurity Approaches in HEIs
6.1. Integration of AI and ML in Cybersecurity
6.2. Cloud-Based Cybersecurity Implementation
6.3. Technology, Institutional Governance and Policy Interplay in Cybersecurity
| Category | Sub-Category | Description | Current Trends | Challenges | Solutions |
|---|---|---|---|---|---|
| Cybersecurity Threats | Malware Ransomware | Malicious software that disrupts or lacks access to institutional data. | Increasing incidents of ransomware attacks targeting university systems. | Lack of awareness and insufficient user training on phishing and malware. | Implement multi-factor authentication, educate staff, and use endpoint security tools [45,54]. |
| Phishing | Fraudulent attempts to obtain sensitive information by pretending to be a trustworthy entity. | Growing sophistication in phishing tactics, especially spear-phishing targeting students and staff. | Difficulty in differentiating legitimate communications from phishing attempts. | Regular training, email filtering tools, and simulated phishing exercises for staff and students [23,33,35]. | |
| Insider Threats | Cyberattacks originating from within the institution (e.g., disgruntled employees or students). | Rise in insider threats due to increased digital access. | Lack of strict access controls and monitoring. | Implement least-privilege access, conduct regular audits, and invest in monitoring systems [54]. | |
| Cybersecurity Frameworks | NIST | The National Institute of Standards and Technology’s framework for improving critical infrastructure cybersecurity. | NIST Cybersecurity Framework (CSF) increasingly adopted by universities. | Complexity of applying NIST CSF due to resource constraints in universities. | Develop a cybersecurity roadmap, align with NIST CSF, and train personnel to manage frameworks [57,58]. |
| ISO/IEC 27001 | The international standard for information security management systems (ISMSs). | Growing adoption of ISO/IEC 27001 in universities is to ensure compliance with data protection laws. | Difficulty in full certification due to budget constraints. | Create a phased implementation plan, seek third-party guidance, and align ISMSs with university priorities [24,46,58,59,71]. | |
| Data Privacy and Protection | GDPR Compliance | Adherence to the General Data Protection Regulation for handling student and staff data. | Increased pressure on universities to comply with GDPR, especially with international students. | Challenges in ensuring comprehensive data protection and audit trails across diverse systems. | Implement data encryption, anonymize student records, and integrate GDPR compliance in institutional policies [53]. |
| FERPA | The Family Educational Rights and Privacy Act, governing the privacy of student education records in the U.S. | FERPA compliance remains a top priority, especially with cloud-based services. | Mismanagement of access controls to student records and data. | Conduct regular FERPA training and audits, implement access control systems, and encrypt student data [45,52]. | |
| Cybersecurity Education | Curriculum Integration | Incorporating cybersecurity education into academic programmes and curricula. | Rise in courses dedicated to cybersecurity and data privacy. | Lack of adequately trained faculty and resources to teach specialized cybersecurity topics. | Develop interdisciplinary cybersecurity curricula, provide faculty training, and partner with industry for hands-on experience [23,37,48]. |
| Cybersecurity Certifications | Providing certifications and training programmes for students and staff. | Growing importance of certifications (e.g., CompTIA Security+, CISSP) for both students and staff in higher education. | Financial costs and time constraints for students pursuing certifications. | Offer subsidized certification programmes, develop partnerships with certification bodies, and promote flexible study options [50]. | |
| Technology Infrastructure | Cloud Security | Protection of data and services hosted on cloud platforms (e.g., AWS, Azure). | Increasing shift to cloud-based infrastructure, making data more vulnerable to breaches. | Difficulty in securing cloud configurations and third-party provider risks. | Use cloud security best practices, enable strong access management, and choose reputable cloud service providers [4,11,30,31,68]. |
| Network Security | Protection of university networks from unauthorized access and attacks. | Integration of advanced network security protocols (e.g., SDN, firewalls and VPNs). | Overwhelming volume of traffic and limited ability to monitor and secure all endpoints. | Invest in next-gen firewalls, intrusion detection systems (IDSs) and network segmentation [5,20,64]. | |
| Governance and Policies | Risk Management | Identifying, assessing and mitigating cybersecurity risks to the institution. | Growing need for formalized cybersecurity risk management strategies within higher education institutions. | Limited resources for risk management and failure to assess evolving threats. | Develop comprehensive risk management policies, allocate resources for regular risk assessments, and involve stakeholders [62,69]. |
| Incident Response | The process of preparing for and responding to cybersecurity incidents. | Emergence of dedicated cybersecurity incident response teams (CIRT) and plans in universities. | Difficulty in coordinating responses and lack of trained personnel for high-impact incidents. | Develop and test incident response plans, conduct tabletop exercises, and designate incident response teams [8]. | |
| Emerging Technologies | AI and Machine Learning | Utilizing AI/ML for detecting anomalies, automating threat detection and improving response times. | Integration of AI/ML-driven solutions to monitor and respond to cybersecurity threats. | High cost of implementation and complexity of training AI models. | Invest in AI-driven security tools and ML algorithms, and partner with research institutions to develop tools [2,7,8,9,15,37,38,60,61,62,64,65]. |
| Blockchain | Using blockchain technology to enhance security, especially for securing academic records and credentials. | Growing interest in using blockchain to verify academic credentials and secure digital transactions. | Lack of understanding and adoption of blockchain in traditional academic systems. | Pilot blockchain initiatives for academic credential verification and ensure security through decentralized networks [39,40,45]. |
6.4. Enhancing Security Incident and Event Management (SIEM) Systems
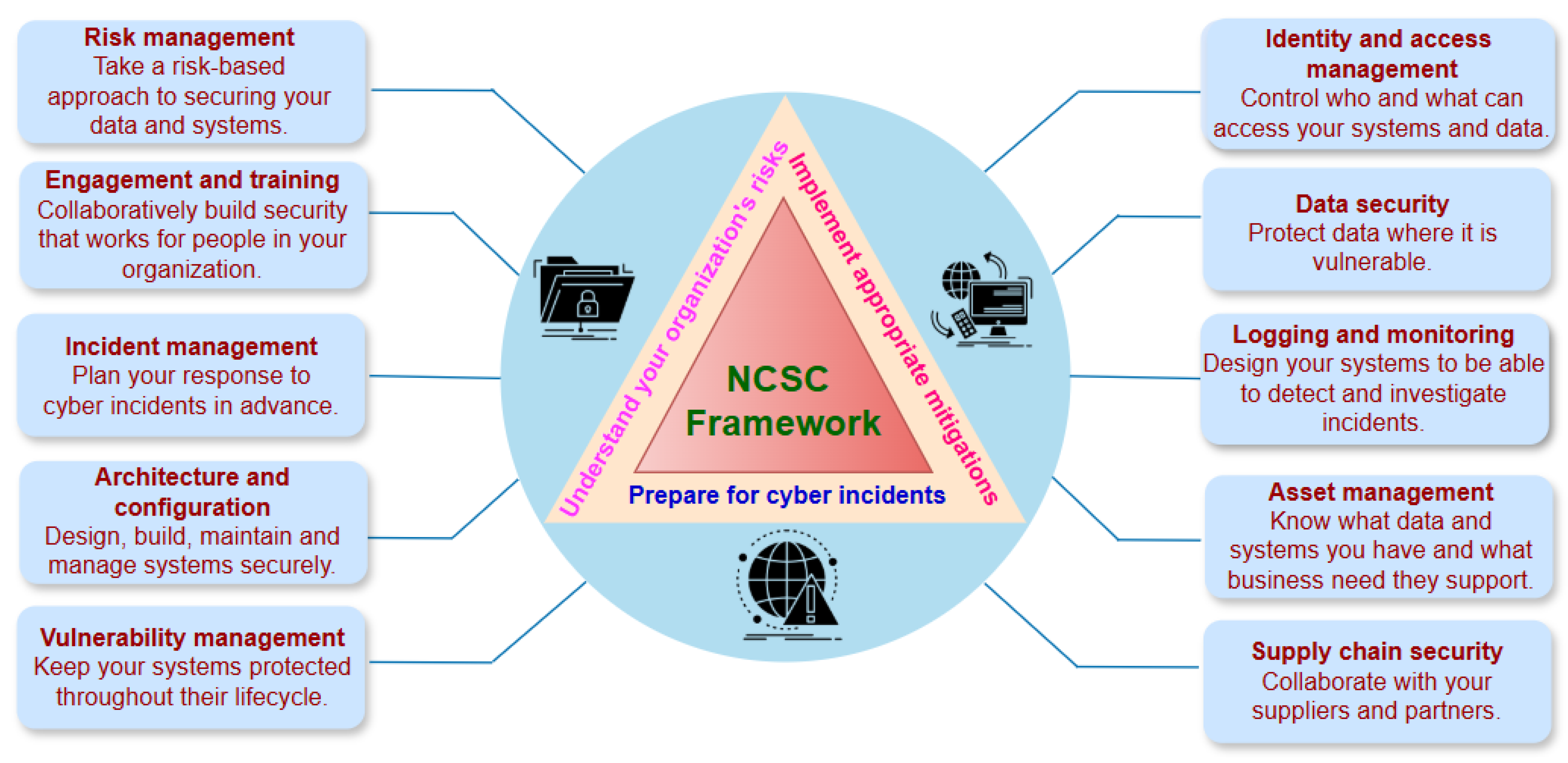
7. Suggestions and Recommendations for Cybersecurity Practices in HEIs
- Proper assessment and classification of overall security units and information assets by HEIs for the purpose of conducting detailed analysis of potential cyberthreats. This involves risk assessment and management to identify compliance requirements and potential security breaches associated with cybersecurity interventions.
- Establishment of a formidable information security team to effectively coordinate an information security management programme by employing third-party security audits to implement remediation decisions and continuous improvement measures in the event of security gaps and weaknesses.
- Providing adequate training and awareness to members of HEI communities on the need to always protect their information through regular session timeouts. Considering the substantial amounts of information at the disposal of faculty members, including funding accounts and student grades, these timeouts on every workstation are necessary to prevent vulnerabilities.
- By using secure protocols, HEIs can safeguard the corporate network and end users can protect their home network. Data will be encrypted and secured during transmission.
- Short-Term Actions (0–12 months):
- Establish or reinforce cybersecurity governance structures, including clear roles for IT, academic and administrative units.
- Conduct institution-wide security awareness training tailored to staff, students and researchers.
- Implement baseline security controls (MFA, patch management, access control, secure configurations).
- Develop and disseminate incident response procedures and communication protocols.
- Medium-Term Actions (1–3 years):
- Deploy advanced security monitoring solutions (e.g., SIEM, behavioural analytics).
- Formalize risk management processes aligned with ISO 27001 or NIST CSF.
- Integrate cybersecurity into academic curricula and research project guidelines.
- Strengthen data management frameworks, including data classification and retention policies.
- Long-Term Actions (3+ years):
- Build dedicated cybersecurity research and Security Operations Centers (SOCs) within the institution.
- Foster inter-institutional collaboration networks for threat intelligence sharing.
- Adopt AI-driven cybersecurity tools and autonomous response capabilities.
- Institutionalize continuous improvement cycles through audit and drill exercises.
8. Conclusions
Supplementary Materials
Author Contributions
Funding
Data Availability Statement
Conflicts of Interest
Abbreviations
| AI | Artificial Intelligence |
| CC | Cloud Computing |
| CSF | Cybersecurity Framework |
| CSP | Cloud Service Provider |
| DDoS | Distributed Denial-of-Service |
| FERPA | Family Educational Rights and Protection Act |
| GDPR | General Data Protection Regulation |
| HEIs | Higher Education Institutions |
| HIDS | Host Intrusion Detection System |
| IAM | Identity and Access Management |
| IDPS | Intrusion Detection and Prevention System |
| IDS | Intrusion Detection System |
| IoT | Internet of Things |
| LMSs | Learning Management Systems |
| MFA | Multi-Factor Authentication |
| ML | Machine Learning |
| NCSC | National Cyber Security Center |
| NIST | National Institute of Standards and Technology |
| PII | Personally Identifiable Information |
| PRISMA | Preferred Reporting Items for Systematic Reviews and Meta-Analysis |
| SIEM | Security Incident and Event Management |
| SLR | Systematic Literature Review |
| VCA | Video Conferencing Applications |
| ZTA | Zero Trust Architecture |
Appendix A
| No. | Reference | Score (%) | Quality | Comment |
|---|---|---|---|---|
| 1 | [28] | 65 | Moderate | Peer-reviewed but short format. |
| 2 | [33] | 84 | High | Peer-reviewed empirical study in strong journal. |
| 3 | [34] | 85 | High | Strong empirical study; open access peer review. |
| 4 | [4] | 70 | Moderate | Qualitative study in indexed journal (regional). |
| 5 | [52] | 62 | Moderate | Policy/law focus; valuable context. |
| 6 | [30] | 60 | Moderate | Conference proceedings. |
| 7 | [31] | 60 | Moderate | Conference/industry focus. |
| 8 | [38] | 70 | Moderate-High | Book chapter with empirical focus. |
| 9 | [13] | 80 | High | IEEE magazine/journal; conceptual but reputable. |
| 10 | [70] | 62 | Moderate | Conference proceedings with general coverage. |
| 11 | [29] | 78 | Moderate-High | Scoping review in reputable journal. |
| 12 | [35] | 72 | Moderate-High | Niche journal; empirical study. |
| 13 | [50] | 78 | Moderate-High | Strong topic fit; peer-reviewed. |
| 14 | [60] | 62 | Moderate | Conference paper; conceptual. |
| 15 | [53] | 78 | Moderate-High | Legal analysis in peer venue. |
| 16 | [1] | 78 | Moderate-High | Peer-reviewed journal; empirical synthesis. |
| 17 | [40] | 80 | High | Applied scheme in peer-reviewed reputable journal. |
| 18 | [68] | 78 | Moderate-High | Peer-reviewed journal survey. |
| 19 | [20] | 64 | Moderate | Regional conference proceedings. |
| 20 | [27] | 62 | Moderate | Regional outlet; peer-reviewed. |
| 21 | [37] | 82 | High | Comprehensive review in reputable journal. |
| 22 | [44] | 82 | High | Reputable journal; multivocal review type. |
| 23 | [21] | 77 | Moderate-High | Journal article addressing policy; peer-reviewed. |
| 24 | [39] | 78 | Moderate-High | Reputable journal; applied scheme. |
| 25 | [14] | 66 | Moderate | Conference paper on HEI cybersecurity. |
| 26 | [24] | 82 | High | Systematic review; good evidence synthesis. |
| 27 | [17] | 92 | High | Authoritative guideline; high reliability. |
| 28 | [61] | 66 | Moderate | Conference survey on AI for detection. |
| 29 | [41] | 76 | Moderate-High | Journal article on institutional strategies. |
| 30 | [32] | 66 | Moderate | Technical DDoS detection paper. |
| 31 | [19] | 55 | Moderate-Low | Reviewed journal; narrative survey. |
| 32 | [36] | 58 | Moderate-Low | Non-reviewed journal; systematic review. |
| 33 | [16] | 56 | Moderate-Low | Regional journal; variable rigour. |
| 34 | [18] | 90 | High | Method guidance in BMJ series. |
| 35 | [11] | 68 | Moderate | Peer-reviewed, education-oriented. |
| 36 | [58] | 68 | Moderate | Peer-reviewed journal; comparative framework article. |
| 37 | [3] | 76 | Moderate-High | Peer-reviewed; empirical model. |
| 38 | [22] | 70 | Moderate | Peer-reviewed regional journal; case study. |
| 39 | [64] | 66 | Moderate | Technical conference paper. |
| 40 | [43] | 78 | Moderate-High | Peer-reviewed survey. |
| 41 | [25] | 72 | Moderate-High | Critical review in indexed journal. |
| 42 | [72] | 64 | Moderate | Peer-reviewed regional journal. |
| 43 | [46] | 60 | Moderate | Peer-reviewed engineering journal; deductive research. |
| 44 | [5] | 68 | Moderate | Peer-reviewed journal; technical evaluation paper. |
| 45 | [48] | 62 | Moderate | Peer-reviewed journal with variable rigour. |
| 46 | [7] | 66 | Moderate | IEEE conference; technical content but shorter format. |
| 47 | [45] | 80 | High | Reputable IEEE journal; rigorous content. |
| 48 | [47] | 64 | Moderate | Journal of variable indexing. |
| 49 | [6] | 80 | High | IEEE Open Journal; rigorous content. |
| 50 | [23] | 60 | Moderate | Narrative review in domain journal; broad scope. |
| 51 | [16] | 67 | Moderate | Education conference; evaluation study. |
| 52 | [71] | 65 | Moderate | Conference paper on SIEM analysis. |
| 53 | [9] | 66 | Moderate | Conference; technical focus on threat intelligence. |
| 54 | [51] | 60 | Moderate | Conference proceeding; moderate scope. |
| 55 | [15] | 67 | Moderate | Conference proceedings; technical ML application. |
| 56 | [26] | 80 | High | Systematic review on MFA frameworks. |
| 57 | [10] | 82 | High | Recent journal article in Computers; strong relevance. |
| 58 | [62] | 80 | High | Peer-reviewed journal; strong content. |
| 59 | [67] | 78 | Moderate-High | Recent peer-reviewed, indexed journal. |
References
- Abad-Segura, E.; González-Zamar, M.-D.; Infante-Moro, J.C.; Ruipérez García, G. Sustainable Management of Digital Transformation in Higher Education: Global Research Trends. Sustainability 2020, 12, 2107. [Google Scholar] [CrossRef]
- Yusuf, A.; Pervin, N.; Román-González, M. Generative AI and the Future of Higher Education: A Threat to Academic Integrity or Reformation? Evidence from Multicultural Perspectives. Int. J. Educ. Technol. High. Educ. 2024, 21, 21. [Google Scholar] [CrossRef]
- Alyoussef, I.Y. Acceptance of E-Learning in Higher Education: The Role of Task-Technology Fit with the Information Systems Success Model. Heliyon 2023, 9, e13751. [Google Scholar] [CrossRef]
- Odeh, M.; Garcia-Perez, A.; Warwick, K. Cloud Computing Adoption at Higher Education Institutions in Developing Countries: A Qualitative Investigation of Main Enablers and Barriers. Int. J. Inf. Educ. Technol. 2017, 7, 921–927. [Google Scholar] [CrossRef]
- Prabowo, W.A.; Fauziah, K.; Nahrowi, A.S.; Faiz, M.N.; Muhammad, A.W. Strengthening Network Security: Evaluation of Intrusion Detection and Prevention Systems Tools in Networking Systems. Int. J. Adv. Comput. Sci. Appl. 2023, 14, 1–10. [Google Scholar] [CrossRef]
- Joshi, H. Emerging Technologies Driving Zero Trust Maturity Across Industries. IEEE Open J. Comput. Soc. 2025, 6, 25–36. [Google Scholar] [CrossRef]
- Chokkanathan, K.; Karpagavalli, S.M.; Priyanka, G.; Vanitha, K.; Anitha, K.; Shenbagavalli, P. AI-Driven Zero Trust Architecture: Enhancing Cyber-Security Resilience. In Proceedings of the 2024 8th International Conference on Computational System and Information Technology for Sustainable Solutions (CSITSS), Bengaluru, India, 7–9 November 2024; pp. 1–6. [Google Scholar] [CrossRef]
- Wahed, M.A.; Alzboon, M.S.; Alqaraleh, M.; Halasa, A.; Al-Batah, M.; Bader, A.F. Comprehensive Assessment of Cybersecurity Measures: Evaluating Incident Response, AI Integration, and Emerging Threats. In Proceedings of the 2024 7th International Conference on Internet Applications, Protocols, and Services (NETAPPS), Kuala Lumpur, Malaysia, 6–7 November 2024; pp. 1–8. [Google Scholar] [CrossRef]
- Singh, A.; Kanishka; Dubey, S.K. Analytical Approach Towards Cybersecurity Through AI-Enabled Threat Intelligence. In Proceedings of the 2024 11th International Conference on Reliability, Infocom Technologies and Optimization (Trends and Future Directions) (ICRITO), Noida, India, 14–15 March 2024; pp. 1–6. [Google Scholar] [CrossRef]
- Lallie, H.S.; Thompson, A.; Titis, E.; Stephens, P. Analysing Cyber Attacks and Cyber Security Vulnerabilities in the University Sector. Computers 2025, 14, 49. [Google Scholar] [CrossRef]
- Wolfschwenger, P.; Sabitzer, B.; Lavicza, Z. Cloud Adoption and Digital Transformation in the Context of Education: A Phenomenological Study. In Proceedings of the 2022 IEEE Frontiers in Education Conference (FIE), Uppsala, Sweden, 8–11 October 2022; pp. 1–9. [Google Scholar] [CrossRef]
- Amankulovich, K.S.; Tokhirovich, M.J.; Bakhridinovich, K.T.; Kuvandikovich, T.U.; Ananth, C.; Kumar, T.A. Leveraging Artificial Intelligence in Online Educational Platforms to Enhance Continuous Professional Development in the Teaching Profession. In Proceedings of the 2024 Second International Conference Computational and Characterization Techniques in Engineering & Sciences (IC3TES), Lucknow, India, 15–16 November 2024; pp. 1–5. [Google Scholar] [CrossRef]
- Pflaum, A.A.; Gölzer, P. The IoT and Digital Transformation: Toward the Data-Driven Enterprise. IEEE Pervasive Comput. 2018, 17, 87–91. [Google Scholar] [CrossRef]
- Kryshtanovych, M.; Kozlovskiy, Y.; Chubinska, N.; Huzii, I.; Lukashevska, U. Ensuring Cybersecurity for Higher Educational Institutions. In Proceedings of the 2021 IEEE 8th International Conference on Problems of Infocommunications, Science and Technology (PIC S&T), Kharkiv, Ukraine, 5–7 October 2021; pp. 183–186. [Google Scholar] [CrossRef]
- Strang, K.D.; Rao Vajjhala, N. Exploring Cybersecurity Risks in Higher Education Environments with Machine Learning. In Proceedings of the 2024 4th International Conference on Pervasive Computing and Social Networking (ICPCSN), Salem, India, 3–4 May 2024; pp. 1–6. [Google Scholar] [CrossRef]
- Salem, M.; Samara, K.; Pray, J.; Hussein, M. Evaluating the Effectiveness of Online Cybersecurity Program in Higher Education. In Proceedings of the 2024 IEEE Global Engineering Education Conference (EDUCON), Kos Island, Greece, 8–11 May 2024; pp. 1–9. [Google Scholar] [CrossRef]
- Page, M.J.; McKenzie, J.E.; Bossuyt, P.M.; Boutron, I.; Hoffmann, T.C.; Mulrow, C.D.; Shamseer, L.; Tetzlaff, J.M.; Akl, E.A.; Brennan, S.E.; et al. The PRISMA 2020 Statement: An Updated Guideline for Reporting Systematic Reviews. BMJ 2021, 372, n71. [Google Scholar] [CrossRef]
- Sarri, G.; Patorno, E.; Yuan, H.; Guo, J.; Bennett, D.; Wen, X.; Zullo, A.R.; Largent, J.; Panaccio, M.; Gokhale, M.; et al. Framework for the Synthesis of Non-Randomised Studies and Randomised Controlled Trials: A Guidance on Conducting a Systematic Review and Meta-Analysis for Healthcare Decision Making. BMJ EBM 2022, 27, 109–119. [Google Scholar] [CrossRef]
- Jawaid, S.A. Cyber Security Threats to Educational Institutes: A Growing Concern for the New Era of Cybersecurity. Int. J. Data Sci. Big Data Anal. 2022, 2, 11–17. [Google Scholar] [CrossRef]
- Arina, A. Network Security Threats to Higher Education Institutions. Cent. East. Eur. EDem EGov (OCG) 2022, 341, 323–333. [Google Scholar] [CrossRef]
- Fouad, N.S. Securing Higher Education against Cyberthreats: From an Institutional Risk to a National Policy Challenge. J. Cyber Policy 2021, 6, 137–154. [Google Scholar] [CrossRef]
- Eltahir, M.E.; Ahmed, O.S. Cybersecurity Awareness in African Higher Education Institutions: A Case Study of Sudan. Inf. Sci. Lett. 2023, 12, 171–183. [Google Scholar] [CrossRef]
- Mouwers-Singh, C.; Musikavanhu, T.B. A Narrative Review on Enhancing Cybersecurity in Higher Education Institutions: The Role of Continuous Training and Awareness. Expert J. Bus. Manag. 2024, 12, 67–73. [Google Scholar]
- Merchan-Lima, J.; Astudillo-Salinas, F.; Tello-Oquendo, L.; Sanchez, F.; Lopez-Fonseca, G.; Quiroz, D. Information security management frameworks and strategies in higher education institutions: A systematic review. Ann. Telecommun. 2021, 76, 255–270. [Google Scholar] [CrossRef]
- Nuñez, M.; Palmer, X.-L.; Potter, L.; Aliac, C.J.; Velasco, L.C. ICT Security Tools and Techniques among Higher Education Institutions: A Critical Review. Int. J. Emerg. Technol. Learn. 2023, 18, 4–22. [Google Scholar] [CrossRef]
- Syahreen, M.; Hafizah, N.; Maarop, N.; Maslinan, M. A Systematic Review on Multi-Factor Authentication Framework. Int. J. Adv. Comput. Sci. Appl. 2024, 15, 1043–1050. [Google Scholar] [CrossRef]
- Arina, A.; Anatolie, A. Cyber Security Threat Analysis in Higher Education Institutions as a Result of Distance Learning. Int. J. Sci. Technol. Res. 2021, 10, 128–133. Available online: https://api.semanticscholar.org/CorpusID:233293525 (accessed on 26 March 2025).
- Dobre, I. Learning Management Systems for Higher Education—An Overview of Available Options for Higher Education Organizations. Procedia-Soc. Behav. Sci. 2015, 180, 313–320. [Google Scholar] [CrossRef]
- Al-Samarraie, H. A Scoping Review of Videoconferencing Systems in Higher Education: Learning Paradigms, Opportunities, and Challenges. Int. Rev. Res. Open Distrib. Learn. 2019, 20, 121–140. [Google Scholar] [CrossRef]
- Yi, H.; Nie, Z.; Li, W. Implementation of Learning Management System Based on Cloud Computing. In Proceedings of the 2017 4th IEEE International Conference on Information Science and Control Engineering (ICISCE), Changsha, China, 21–23 July 2017; pp. 380–384. [Google Scholar] [CrossRef]
- Zahran, R.M.; Walker-Gleaves, C.; Walker-Gleaves, A. Exposition of Integrating Cloud Computing in Information and Communication Technology Courses in Higher Education. In Proceedings of the 2017 9th IEEE-GCC Conference and Exhibition (GCCCE), Manama, Bahrain, 8–11 May 2017; pp. 1–9. [Google Scholar] [CrossRef]
- Hassan, K.F.; Manaa, M.E. Detecting Distributed Denial of Service Attacks in Internet of Things Networks Using Machine Learning in Fog Computing. In Proceedings of the 2022 5th IEEE International Conference on Engineering Technology and its Applications (IICETA), Al-Najaf, Iraq, 31 May–1 June 2022; pp. 323–328. [Google Scholar] [CrossRef]
- Sun, J.C.-Y.; Yu, S.-J.; Lin, S.S.J.; Tseng, S.-S. The Mediating Effect of Anti-Phishing Self-Efficacy between College Students’ Internet Self-Efficacy and Anti-Phishing Behavior and Gender Difference. Comput. Hum. Behav. 2016, 59, 249–257. [Google Scholar] [CrossRef]
- Gavett, B.E.; Zhao, R.; John, S.E.; Bussell, C.A.; Roberts, J.R.; Yue, C. Phishing Suspiciousness in Older and Younger Adults: The Role of Executive Functioning. PLoS ONE 2017, 12, e0171620. [Google Scholar] [CrossRef]
- Broadhurst, R.; Skinner, K.; Sifniotis, N.; Matamoros-Macias, B.; Ipsen, Y. Phishing and Cybercrime Risks in a University Student Community. Int. J. Cybersecur. Intell. Cybercrime 2019, 2, 4–23. [Google Scholar] [CrossRef]
- Nassoura, A.B. Cybersecurity Technologies and Practices in Higher Education Institutions: A Systematic Review. Webology 2022, 19, 1152–1167. [Google Scholar]
- Bécue, A.; Praça, I.; Gama, J. Artificial Intelligence, Cyber-Threats and Industry 4.0: Challenges and Opportunities. Artif. Intell. Rev. 2021, 54, 3849–3886. [Google Scholar] [CrossRef]
- Alhawi, O.M.K.; Baldwin, J.; Dehghantanha, A. Leveraging Machine Learning Techniques for Windows Ransomware Network Traffic Detection. In Cyber Threat Intelligence; Dehghantanha, A., Conti, M., Dargahi, T., Eds.; Advances in Information Security; Springer International Publishing: Cham, Switzerland, 2018; Volume 70, pp. 93–106. [Google Scholar] [CrossRef]
- Guha Roy, D.; Srirama, S.N. A Blockchain-based Cyber Attack Detection Scheme for Decentralized Internet of Things Using Software-Defined Network. Softw. Pract. Exp. 2021, 51, 1540–1556. [Google Scholar] [CrossRef]
- Al-Abassi, A.; Karimipour, H.; Dehghantanha, A.; Parizi, R.M. An Ensemble Deep Learning-Based Cyber-Attack Detection in Industrial Control System. IEEE Access 2020, 8, 83965–83973. [Google Scholar] [CrossRef]
- Cheng, E.C.K.; Wang, T. Institutional Strategies for Cybersecurity in Higher Education Institutions. Information 2022, 13, 192. [Google Scholar] [CrossRef]
- Lund, B.D.; Lee, T.-H.; Wang, Z.; Wang, T.; Mannuru, N.R. Zero Trust Cybersecurity: Procedures and Considerations in Context. Encyclopedia 2024, 4, 1520–1533. [Google Scholar] [CrossRef]
- Kang, H.; Liu, G.; Wang, Q.; Meng, L.; Liu, J. Theory and Application of Zero Trust Security: A Brief Survey. Entropy 2023, 25, 1595. [Google Scholar] [CrossRef]
- Buck, C.; Olenberger, C.; Schweizer, A.; Völter, F.; Eymann, T. Never Trust, Always Verify: A Multivocal Literature Review on Current Knowledge and Research Gaps of Zero-Trust. Comput. Secur. 2021, 110, 102436. [Google Scholar] [CrossRef]
- Rivera, J.J.D.; Muhammad, A.; Song, W.-C. Securing Digital Identity in the Zero Trust Architecture: A Blockchain Approach to Privacy-Focused Multi-Factor Authentication. IEEE Open J. Commun. Soc. 2024, 5, 2792–2814. [Google Scholar] [CrossRef]
- Singh, C.; Thakkar, R.; Warraich, J. IAM Identity Access Management—Importance in Maintaining Security Systems Within Organizations. Eur. J. Eng. Technol. Res. 2023, 8, 30–38. [Google Scholar] [CrossRef]
- Hassan, O.F.; Fatai, F.O.; Aderibigbe, O.; Akinde, A.O.; Onasanya, T.; Sanusi, M.A.; Odukoya, O. Enhancing Cybersecurity through Cloud Computing Solutions in the United States. Intell. Inf. Manag. 2024, 16, 176–193. [Google Scholar] [CrossRef]
- Abrahams, T.O.; Ewuga, S.K.; Dawodu, S.O.; Adegbite, A.O.; Hassan, A.O. A Review of Cybersecurity Strategies in Modern Organizations: Examining the Evolution and Effectiveness of Cybersecurity Measures for Data Protection. Comput. Sci. It Res. J. 2024, 5, 1–25. [Google Scholar] [CrossRef]
- Ibrahim, F. Importance of Cybersecurity in Educational Institutions. Bachelor’s Thesis, University of Pecs, Pécs, Hungary, 2024. [Google Scholar] [CrossRef]
- Catota, F.E.; Morgan, M.G.; Sicker, D.C. Cybersecurity education in a developing nation: The Ecuadorian environment. J. Cybersecur. 2019, 5, tyz001. [Google Scholar] [CrossRef]
- Siphambili, N. Exploring Cybersecurity Implications in Higher Education. In Proceedings of the 23rd European Conference on Cyber Warfare and Security (ECCWS), Jyväskylä, Finland, 27–29 June 2024; Volume 23, pp. 526–531. [Google Scholar] [CrossRef]
- Parks, C. Beyond compliance: Students and FERPA in the age of big data. J. Intellect. Freedom Priv. 2017, 2, 23–33. [Google Scholar] [CrossRef]
- Hoofnagle, C.J.; Van Der Sloot, B.; Borgesius, F.Z. The European Union General Data Protection Regulation: What It Is and What It Means. Inf. Commun. Technol. Law 2019, 28, 65–98. [Google Scholar] [CrossRef]
- Boonkrong, S. Multi-Factor Authentication. In Authentication and Access Control; Apress: Berkeley, CA, USA, 2021; pp. 133–162. [Google Scholar] [CrossRef]
- Salem, I.E.; Mijwil, M.; Abdulqader, A.W.; Ismaeel, M.M.; Alkhazraji, A.; Alaabdin, A.M.Z. Introduction to The Data Mining Techniques in Cybersecurity. Mesopotamian J. Cybersecur. 2022, 2022, 28–37. [Google Scholar] [CrossRef]
- National Cyber Security Centre (NCSC). 10 Steps to Cyber Security. 2021. Available online: https://www.ncsc.gov.uk/collection/10-steps (accessed on 26 February 2025).
- Calder, A. NIST Cybersecurity Framework: A Pocket Guide; IT Governance Publishing Ltd.: Ely, UK, 2018; p. 78. [Google Scholar] [CrossRef]
- Alshar’e, M. Cyber security framework selection: Comparison of NIST and ISO27001. Appl. Comput. J. 2023, 3, 245–255. [Google Scholar] [CrossRef]
- ISO/IEC 27000:2022; Information Security Management Systems. ISO/IEC: Geneva, Switzerland, 2022. Available online: https://www.iso.org/isoiec-27001-information-security.html (accessed on 26 March 2025).
- Geluvaraj, B.; Satwik, P.M.; Ashok Kumar, T.A. The Future of Cybersecurity: Major Role of Artificial Intelligence, Machine Learning, and Deep Learning in Cyberspace. In International Conference on Computer Networks and Communication Technologies; Springer: Singapore, 2018; Volume 15, pp. 739–747. [Google Scholar] [CrossRef]
- Salih, A.; Zeebaree, S.T.; Ameen, S.; Alkhyyat, A.; Shukur, H.M. A Survey on the Role of Artificial Intelligence, Machine Learning and Deep Learning for Cybersecurity Attack Detection. In Proceedings of the 2021 7th IEEE International Engineering Conference “Research & Innovation amid Global Pandemic” (IEC), Erbil, Iraq, 24–25 February 2021; pp. 61–66. [Google Scholar] [CrossRef]
- Ali, S.M.; Razzaque, A.; Yousaf, M.; Ali, S.S. A Novel AI-Based Integrated Cybersecurity Risk Assessment Framework and Resilience of National Critical Infrastructure. IEEE Access 2025, 13, 12427–12446. [Google Scholar] [CrossRef]
- Afolalu, O.; Tsoeu, M.S. Artificial Intelligence as the Next Frontier in Cyber Defense: Opportunities and Risks. Electronics 2025, 14, 4853. [Google Scholar] [CrossRef]
- Islam, M.T.; Syfullah, M.K.; Islam, J.; Quadir, H.M.S.; Rashed, M.G.; Das, D. Exploring the Potential: ML vs. DL in Network Security with Explainable AI (XAI) Insights. In Proceedings of the 2023 26th IEEE International Conference on Computer and Information Technology (ICCIT), Cox’s Bazar, Bangladesh, 13–15 December 2023; pp. 1–6. [Google Scholar] [CrossRef]
- Elbes, M.; Hendawi, S.; AlZu’bi, S.; Kanan, T.; Mughaid, A. Unleashing the Full Potential of Artificial Intelligence and Machine Learning in Cybersecurity Vulnerability Management. In Proceedings of the 2023 IEEE International Conference on Information Technology (ICIT), Amman, Jordan, 9–10 August 2023; pp. 276–283. [Google Scholar] [CrossRef]
- Su, J. Why Cloud Computing Cyber Security Risks Are on the Rise: Report; Forbes: Jersey City, NJ, USA, 25 July 2019; Available online: https://www.forbes.com/sites/jeanbaptiste/2019/07/25/why-cloud-computing-cyber-security-risks-are-on-the-rise-report/13a36bfc5621 (accessed on 8 March 2025).
- Afolalu, O.; Tsoeu, M.S. Enterprise Networking Optimization: A Review of Challenges, Solutions, and Technological Interventions. Future Internet 2025, 17, 133. [Google Scholar] [CrossRef]
- Ahmad, W.; Rasool, A.; Javed, A.R.; Baker, T.; Jalil, Z. Cyber Security in IoT-Based Cloud Computing: A Comprehensive Survey. Electronics 2021, 11, 16. [Google Scholar] [CrossRef]
- Rothrock, R.A.; Kaplan, J.; Van Der Oord, F. The Board’s Role in Managing Cybersecurity Risks. MIT Sloan Manag. Rev. 2018, 59, 12–15. [Google Scholar]
- Spremić, M.; Šimunic, A. Cyber Security Challenges in Digital Economy. In Proceedings of the World Congress on Engineering, London, UK, 4–6 July 2018; Volume 1, pp. 341–346. Available online: https://api.semanticscholar.org/CorpusID:211547880 (accessed on 26 March 2025).
- Sashwin, K.; Nithika, K.S.; Priyadharshini, S.; Maduvant, S.P.; Saranya. Analysis, Trends, and Utilization of Security Information and Event Management (SIEM) in Critical Infrastructures. In Proceedings of the 2024 10th IEEE International Conference on Advanced Computing and Communication Systems (ICACCS), Coimbatore, India, 14–15 March 2024; Volume 1, pp. 1980–1984. [Google Scholar] [CrossRef]
- ProkoPowicz, D.; Golkebiowska, A.; Such-Pyrgiel, M. The Role of Big Data and Data Science in the Context of Information Security and Cybersecurity. J. Mod. Sci. 2023, 53, 9–42. [Google Scholar] [CrossRef]

| Framework | Key | Included | Excluded |
|---|---|---|---|
| Population (P) | Higher education institutions (HEIs) |
|
|
| Intervention (I) | Cybersecurity measures and frameworks |
|
|
| Comparison (C) | Modern versus traditional approaches or lack of adequate cybersecurity practices |
|
|
| Outcomes (O) | Cybersecurity effectiveness and challenges |
|
|
| Study Design (S) | Relevant research types |
|
|
| Time Frame (T) | Period of study |
|
|
| Category | Variables Extracted |
|---|---|
| Study information | Author(s), year of publication, region. |
| Study design | Study type (empirical, conceptual, case study, experimental/framework proposal), research design, data sources. |
| Population/context | Type of HEI, scale of deployment, user groups involved (students, faculty, IT staff, administrators). |
| Cybersecurity challenges addressed | Threat (phishing, ransomware), data breaches, access control weaknesses, governance gaps or technical vulnerabilities. |
| Intervention/solution | Technical controls, administrative policies, human-centric training programmes, policy-based frameworks, security tools, governance models, detection and prevention mechanisms. |
| Methodological approach | Qualitative, quantitative, evaluation metrics. |
| Outcomes and effectiveness | Reported impact, performance, adoption, limitations. |
| Key findings | Main contributions and insights, implications for HEIs, relevance to cybersecurity posture. |
| Notable gaps | Limitations reported by the authors, unresolved problems or future research recommendations. |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Afolalu, O.; Tsoeu, M.S. Cybersecurity in Higher Education Institutions: A Systematic Review of Emerging Trends, Challenges and Solutions. Future Internet 2025, 17, 575. https://doi.org/10.3390/fi17120575
Afolalu O, Tsoeu MS. Cybersecurity in Higher Education Institutions: A Systematic Review of Emerging Trends, Challenges and Solutions. Future Internet. 2025; 17(12):575. https://doi.org/10.3390/fi17120575
Chicago/Turabian StyleAfolalu, Oladele, and Mohohlo Samuel Tsoeu. 2025. "Cybersecurity in Higher Education Institutions: A Systematic Review of Emerging Trends, Challenges and Solutions" Future Internet 17, no. 12: 575. https://doi.org/10.3390/fi17120575
APA StyleAfolalu, O., & Tsoeu, M. S. (2025). Cybersecurity in Higher Education Institutions: A Systematic Review of Emerging Trends, Challenges and Solutions. Future Internet, 17(12), 575. https://doi.org/10.3390/fi17120575






