Quantum Computing for Healthcare: A Review
Abstract
1. Introduction
1.1. Introduction to Quantum Computing
1.2. Quantum Computing for Healthcare
1.3. Comparison with Related Surveys
| References | Year | Healthcare Focus | Security | Privacy | Architectures | Quantum Requirements | Machine/Deep Learning | Applications |
|---|---|---|---|---|---|---|---|---|
| Gyongyosi et al. [8] | 2019 | ✓ | ✓ | ✓ | ✓ | ✓ | ||
| Fernandez et al. [9] | 2019 | ✓ | ✓ | ✓ | ✓ | |||
| Gyongyosi et al. [10] | 2018 | ✓ | ✓ | |||||
| Arunachalam et al. [11] | 2017 | ✓ | ||||||
| Li et al. [12] | 2020 | ✓ | ✓ | |||||
| Shaikh et al. [19] | 2016 | ✓ | ✓ | ✓ | ✓ | |||
| Egger et al. [24] | 2020 | ✓ | ✓ | ✓ | ✓ | ✓ | ||
| Savchuk et al. [25] | 2019 | ✓ | ✓ | ✓ | ✓ | ✓ | ||
| Zhang et al. [13] | 2019 | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ |
| Mcgeoch et al. [26] | 2019 | ✓ | ✓ | ✓ | ✓ | |||
| Shanon et al. [14] | 2020 | ✓ | ✓ | |||||
| Duan et al. [27] | 2020 | ✓ | ✓ | ✓ | ✓ | ✓ | ||
| Preskill et al. [28] | 2018 | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ |
| Roetteler et al. [15] | 2018 | ✓ | ✓ | ✓ | ✓ | ✓ | ||
| Upretyet al. [20] | 2020 | ✓ | ✓ | ✓ | ✓ | ✓ | ||
| Rowell et al. [29] | 2018 | ✓ | ✓ | ✓ | ||||
| Padamvathi et al. [16] | 2016 | ✓ | ✓ | ✓ | ✓ | |||
| Nejatollahi et al. [30] | 2019 | ✓ | ✓ | ✓ | ✓ | |||
| Cuomo et al. [23] | 2020 | ✓ | ✓ | |||||
| Fingeruth et al. [31] | 2018 | ✓ | ✓ | |||||
| Huang et al. [21] | 2018 | ✓ | ✓ | ✓ | ✓ | |||
| Botsinis et al. [22] | 2018 | ✓ | ✓ | ✓ | ✓ | |||
| Ramezani et al. [17] | 2020 | ✓ | ✓ | ✓ | ||||
| Bharti et al. [18] | 2020 | ✓ | ✓ | ✓ | ✓ | |||
| Abbott et al. [32] | 2021 | ✓ | ✓ | ✓ | ||||
| Kumar et al. [33] | 2021 | ✓ | ✓ | ✓ | ✓ | |||
| Olgiati et al. [34] | 2021 | ✓ | ✓ | ✓ | ||||
| Gupta et al. [35] | 2022 | ✓ | ✓ | ✓ | ✓ | |||
| Kumar et al. [36] | 2022 | ✓ | ✓ | |||||
| Our Survey | 2022 | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ |
1.4. Contributions and Organization
- We present the first comprehensive review of quantum computing technologies for healthcare, covering its motivation, requirements, applications, challenges, architectures, and open research issues.
- We discuss the enabling technologies of quantum computing that act as building blocks for the implementation of quantum healthcare service provisioning.
- We discuss the core application areas of quantum computing and analyzed the critical importance of quantum computing in healthcare systems.
- We review the available literature on quantum computing and its inclination toward the development of future-generation healthcare systems.
- We discuss key requirements of quantum computing systems for the successful implementation of large-scale healthcare services provisioning and the security implications involved.
- We discuss current challenges, their causes, and future research directions for an efficient implementation of quantum healthcare systems.
2. Quantum Computing: History, Background, and Enabling Technologies
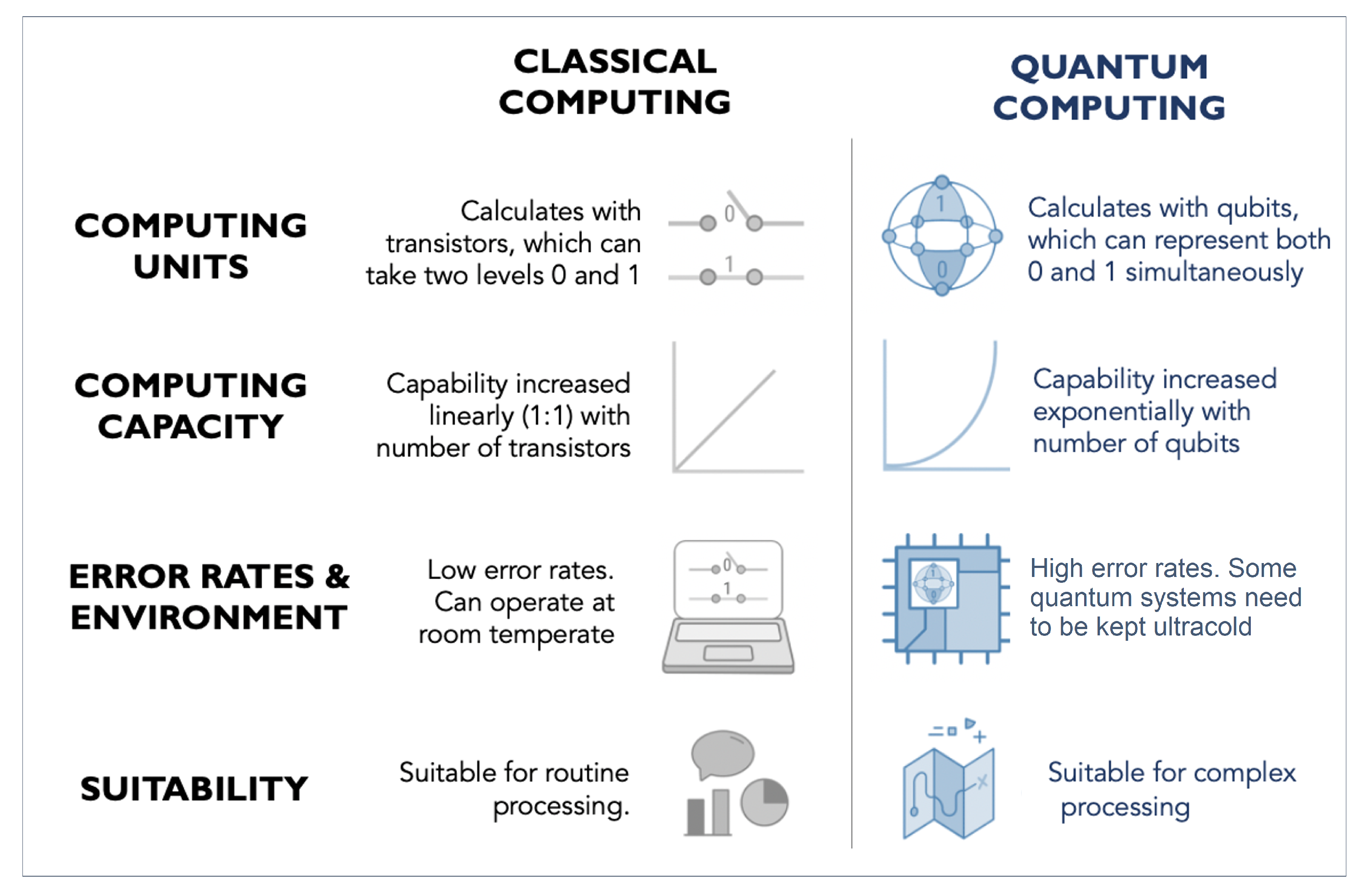
2.1. Quantum Computing vs. Classical Computing
- Quantum superposition refers to the fact that a spinning electron’s position cannot be pinpointed to any specific location at any time. On the contrary, it is calculated as a probability distribution in which the electron can exist at all locations at all times with varying probabilities. Quantum computers rely on quantum superposition, in that they use a group of qubits for calculations and, while classical computer bits may take on only states 0 and 1, qubits can be either a 0 or 1, or a linear combination of both. These linear combinations are termed superposition states. Since a qubit can exist in two states, the computing capacity of a qubit quantum computer grows exponentially in the form of .
- Quantum entanglement takes place in a highly intertwined pair of systems, such that knowledge of anyone immediately provides information about the other, regardless of the distance between them. This nonintuitive fact was described by Einstein as “spooky action at a distance”, because it went against the rule that information could never be communicated beyond light speed. Quantum entanglement in physics is when two systems such as photons or electrons are so highly interlinked that obtaining information about one’s state (for example, the direction of one electron’s upward spin) would provide instantaneous information about the other’s state, such as, for example, the direction of the second electron’s downward spin, no matter how far apart they are. Modifying one entangled qubit’s state therefore immediately perturbs the paired qubit’s state in quantum computers. Thereby, entanglement leads to the increased computational efficiency of quantum computers. Since processing one qubit provides knowledge about many qubits, doubling the number of qubits does not necessarily increase the number of entangled qubits. Quantum entanglement is therefore necessary for the exponentially faster performance of a quantum algorithm as compared with its classical counterpart.
- Quantum interference occurs because, at the subatomic scale, particles have wavelike properties. These wavelike properties are often attributed to location, for example, where around a nucleus an electron might be. Two in-phase waves, which is to say they peak at the same time, constructively interfere, and the resulting wave peaks twice as high. Two waves that are out-of-phase, on the other hand, peak at opposite times and destructively interfere; the resulting wave is completely flat. All other phase differences will have results somewhere in between, with either a higher peak for constructive interference or a lower peak for destructive interference. In quantum computing, interference is used to affect probability amplitudes when measuring the energy level of qubits.
2.2. Brief History of Quantum Computing
2.3. Hardware Structure
2.4. Quantum Data Plane
2.5. Quantum Control and Measurement Plane
2.6. Control Processor Plane and Host Processor
2.7. Qubit Technologies
2.7.1. Trapped Ion Qubits
2.7.2. Superconducting Qubits
2.8. Lessons Learned: Summary and Insights
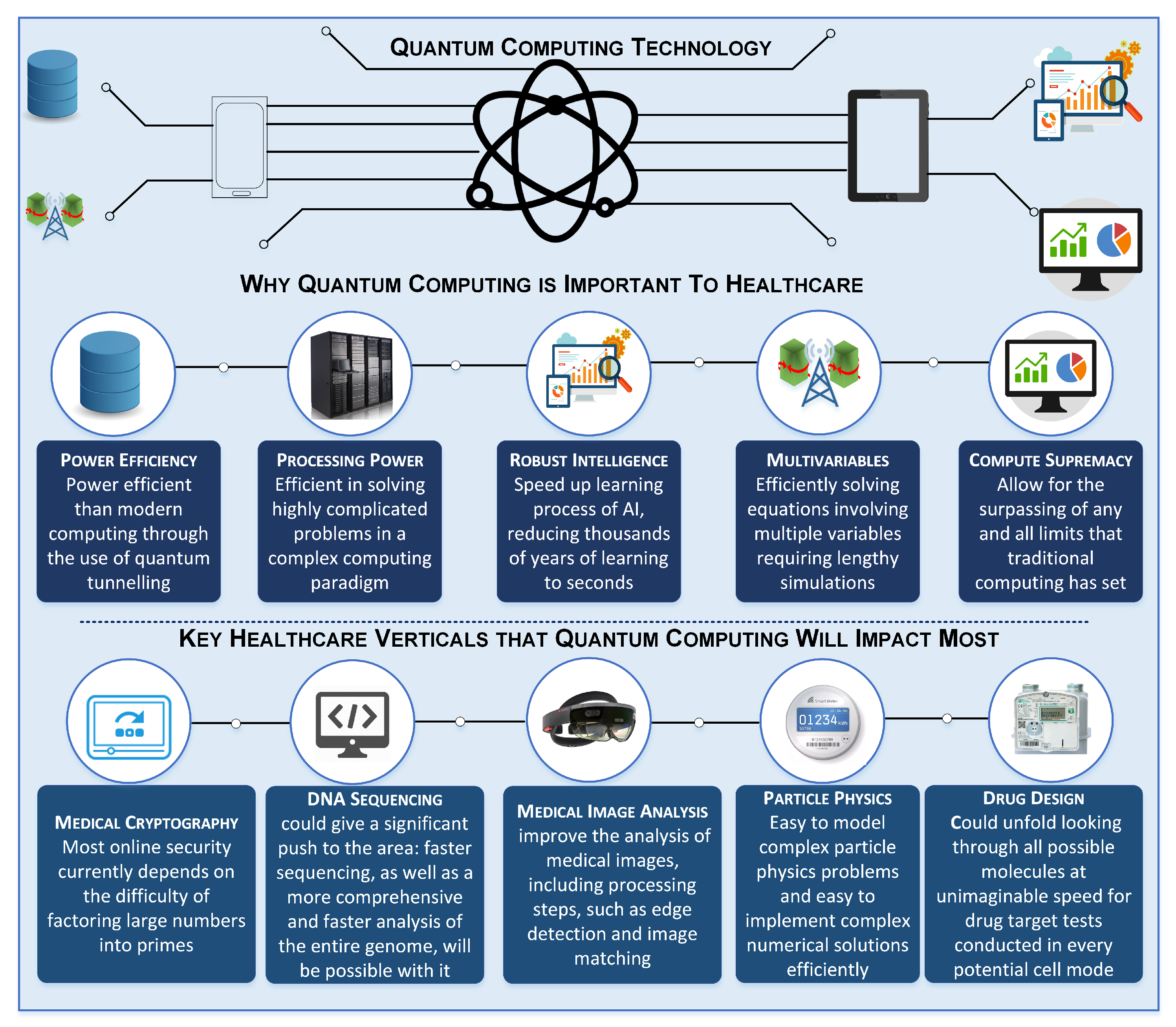
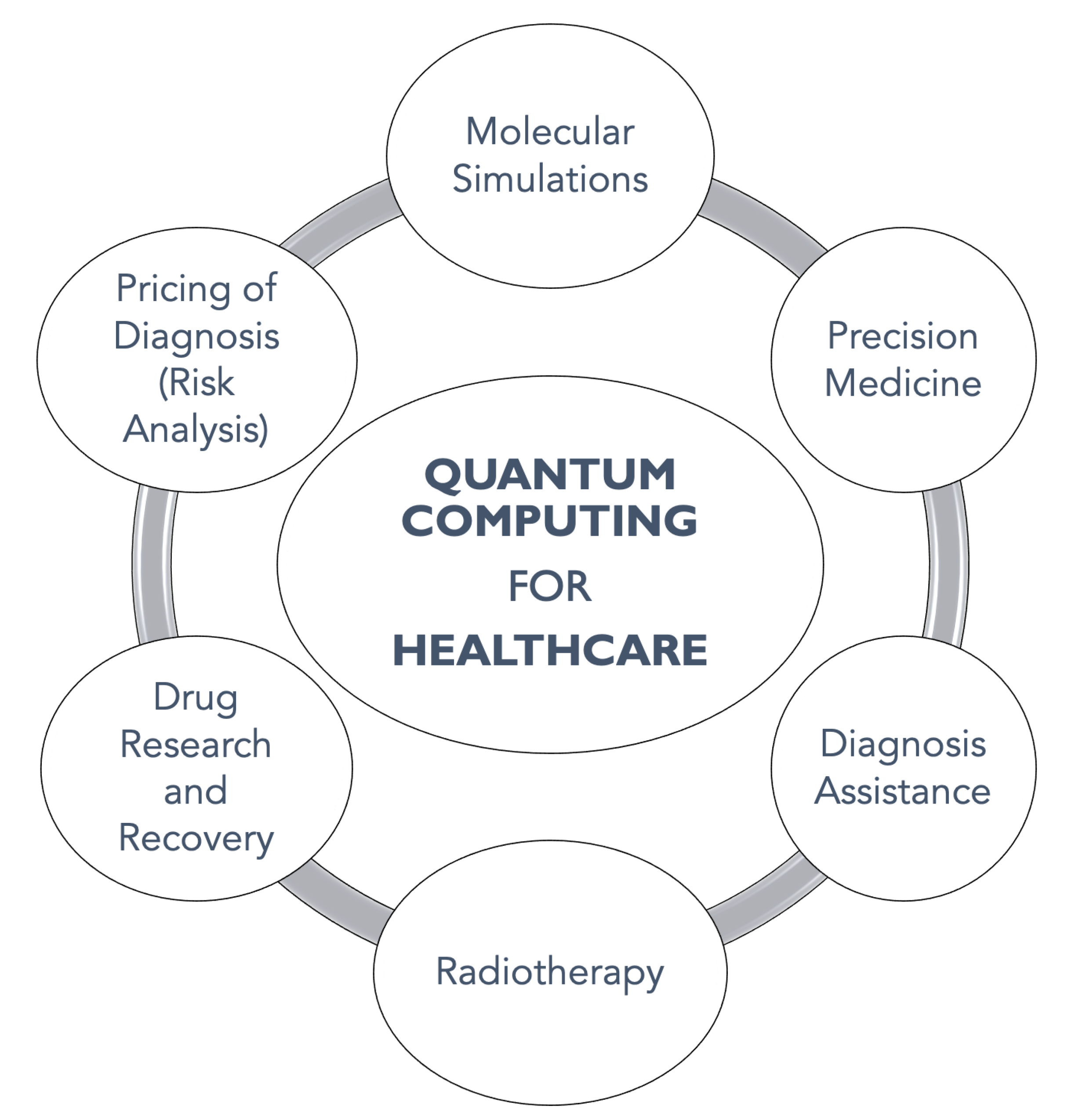
3. Applications of Quantum Computing for Healthcare
3.1. Molecular Simulations
3.2. Precision Medicine
3.3. Diagnosis Assistance
3.4. Radiotherapy
3.5. Drug Research and Discovery
3.6. Pricing of Diagnosis (Risk Analysis)
3.7. Lessons Learned: Summary and Insights
4. Requirements of Quantum Computing for Healthcare
4.1. Computational Power
4.2. High-Speed Connectivity (5G/6G Networks)
4.3. Quantum Communications Networks
4.4. Higher-Dimensional Quantum Communication
4.5. Scalability of Quantum Computing
4.6. Fault Tolerance
4.7. Quantum Availability of the Healthcare Systems
4.8. Deployment of Quantum Gates
4.9. Use of Distributed Topologies
4.10. Requirements for Physical Implementation
4.11. Quantum Machine Learning
4.12. Lessons Learned: Summary and Insights
5. Quantum Computing Architectures for Healthcare
5.1. Quantum Computing Architecture: A Brief Overview
5.2. Quantum Algorithm Design for Healthcare Applications
5.3. Quantum Computing Frameworks for Healthcare
5.4. Secure Quantum Computing for Healthcare
5.5. Actual Clinical Deployment of Quantum Computing
5.6. Lessons Learned: Summary and Insights
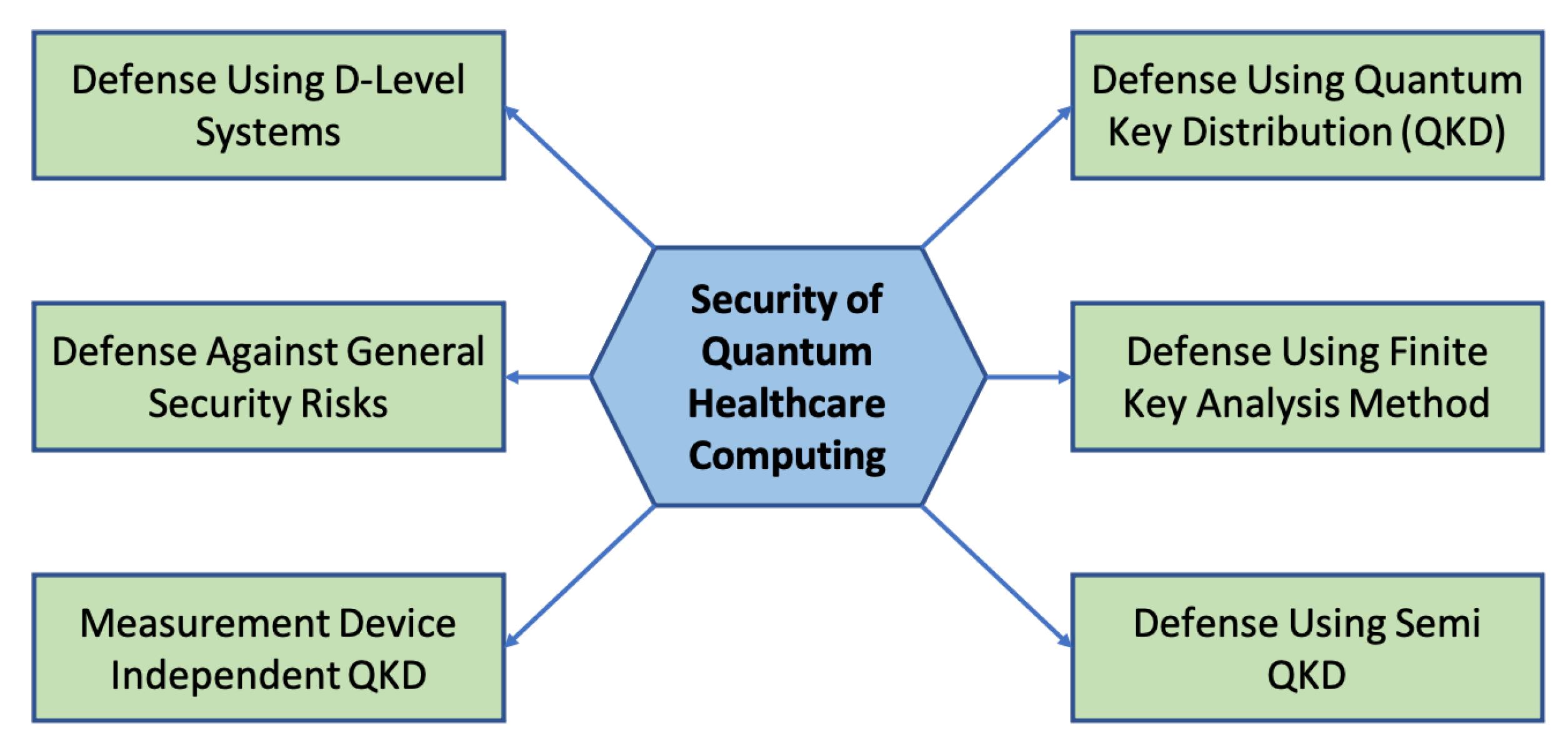
6. Security of Quantum Computing for Healthcare
6.1. Quantum Key Distribution
6.2. Defense Using D-Level Systems
6.3. Defense against General Security Risks
6.4. Defense Using Finite Key Analysis Method
6.5. Measurement-Device-Independent Quantum Key Distribution
| Author | Objective | Security Algorithm | Pros | Cons |
|---|---|---|---|---|
| Acin et al. [137] |
|
|
|
|
| Barret et al. [157] |
|
|
|
|
| Qi et al. [158] |
|
|
|
|
| Fung et al. [159] |
|
|
|
|
| Lydersen et al. [160] |
|
|
|
|
| Li et al. [161] |
|
|
|
|
| Lim et al. [162] |
|
|
|
|
| Broadbent et al. [163] |
|
|
|
|
| Cao et al. [164] |
|
|
|
|
| Li et al. [165] |
|
|
|
|
| Ma et al. [166] |
|
|
|
|
| Zhou et al. [167] |
|
|
|
|
| Tamaki et al. [168] |
|
|
|
|
| Zhao et al. [169] |
|
|
|
|
| Ma et al. [170] |
|
|
|
|
| Li et al. [171] |
|
|
|
|
6.6. Semiquantum Key Distribution
6.7. Lessons Learned: Summary and Insights
7. Open Issues and Future Research Directions
7.1. Quantum Computing for Big Data Processing
7.2. Quantum AI/ML Applications
7.3. Large-Scale Optimization
7.4. Quantum Computers for Simulation
7.5. Quantum Web and Cloud Services
7.6. Quantum Game Theory
7.7. Quantum Security Applications
7.8. Developing a Quantum Market Place
8. Conclusions
Funding
Data Availability Statement
Conflicts of Interest
References
- Flöther, F.; Murphy, J.; Murtha, J.; Sow, D. Exploring Quantum Computing Use Cases for Healthcare (IBM Expert Insights). Available online: https://www.ibm.com/thought-leadership/institute-business-value/report/quantum-healthcare# (accessed on 27 January 2023).
- Devi, A.; Kalaivani, V. Enhanced BB84 quantum cryptography protocol for secure communication in wireless body sensor networks for medical applications. Pers. Ubiquitous Comput. 2021, 1–11. [Google Scholar] [CrossRef]
- Sadki, S.; Bakkali, H.E. Towards negotiable privacy policies in mobile healthcare. In Proceedings of the Fifth International Conference on the Innovative Computing Technology (INTECH 2015), Galcia, Spain, 20–22 May 2015; pp. 94–99. [Google Scholar]
- Zinner, M.; Dahlhausen, F.; Boehme, P.; Ehlers, J.; Bieske, L.; Fehring, L. Toward the institutionalization of quantum computing in pharmaceutical research. Drug Discov. Today 2021, 27, 378–383. [Google Scholar] [CrossRef] [PubMed]
- Banchi, L.; Fingerhuth, M.; Babej, T.; Ing, C.; Arrazola, J.M. Molecular docking with Gaussian boson sampling. Sci. Adv. 2020, 6, eaax1950. [Google Scholar] [CrossRef] [PubMed]
- Li, R.Y.; Di Felice, R.; Rohs, R.; Lidar, D.A. Quantum annealing versus classical machine learning applied to a simplified computational biology problem. NPJ Quantum Inf. 2018, 4, 14. [Google Scholar] [CrossRef]
- Fedorov, V.V.; Leonov, S.L. Combinatorial and model-based methods in structuring and optimizing cluster trials. In Platform Trial Designs in Drug Development; Chapman and Hall/CRC: Boca Raton, FL, USA, 2018; pp. 265–286. [Google Scholar]
- Gyongyosi, L.; Imre, S. A survey on quantum computing technology. Comput. Sci. Rev. 2019, 31, 51–71. [Google Scholar] [CrossRef]
- Fernández-Caramés, T.M. From pre-quantum to post-quantum IoT security: A survey on quantum-resistant cryptosystems for the Internet of Things. IEEE Internet Things J. 2019, 7, 6457–6480. [Google Scholar] [CrossRef]
- Gyongyosi, L.; Imre, S.; Nguyen, H.V. A survey on quantum channel capacities. IEEE Commun. Surv. Tutor. 2018, 20, 1149–1205. [Google Scholar] [CrossRef]
- Arunachalam, S.; de Wolf, R. Guest column: A survey of quantum learning theory. ACM SIGACT News 2017, 48, 41–67. [Google Scholar] [CrossRef]
- Li, Y.; Tian, M.; Liu, G.; Peng, C.; Jiao, L. Quantum optimization and quantum learning: A survey. IEEE Access 2020, 8, 23568–23593. [Google Scholar] [CrossRef]
- Zhang, H.; Ji, Z.; Wang, H.; Wu, W. Survey on quantum information security. China Commun. 2019, 16, 1–36. [Google Scholar] [CrossRef]
- Shannon, K.; Towe, E.; Tonguz, O.K. On the use of quantum entanglement in secure communications: A survey. arXiv 2020, arXiv:2003.07907. [Google Scholar]
- Roetteler, M.; Svore, K.M. Quantum computing: Codebreaking and beyond. IEEE Secur. Priv. 2018, 16, 22–36. [Google Scholar] [CrossRef]
- Padamvathi, V.; Vardhan, B.V.; Krishna, A. Quantum cryptography and quantum key distribution protocols: A survey. In Proceedings of the 2016 IEEE 6th International Conference on Advanced Computing (IACC), Bhimavaram, India, 27–28 February 2016; pp. 556–562. [Google Scholar]
- Ramezani, S.B.; Sommers, A.; Manchukonda, H.K.; Rahimi, S.; Amirlatifi, A. Machine learning algorithms in quantum computing: A survey. In Proceedings of the 2020 International Joint Conference on Neural Networks (IJCNN), Glasgow, UK, 19–24 July 2020; pp. 1–8. [Google Scholar]
- Bharti, K.; Haug, T.; Vedral, V.; Kwek, L.C. Machine learning meets quantum foundations: A brief survey. AVS Quantum Sci. 2020, 2, 034101. [Google Scholar] [CrossRef]
- Shaikh, T.A.; Ali, R. Quantum computing in big data analytics: A survey. In Proceedings of the 2016 IEEE International Conference on Computer and Information Technology (CIT), Nadi, Fiji, 8–10 December 2016; pp. 112–115. [Google Scholar]
- Uprety, S.; Gkoumas, D.; Song, D. A Survey of Quantum Theory Inspired Approaches to Information Retrieval. ACM Comput. Surv. (CSUR) 2020, 53, 1–39. [Google Scholar] [CrossRef]
- Huang, A.; Barz, S.; Andersson, E.; Makarov, V. Implementation vulnerabilities in general quantum cryptography. New J. Phys. 2018, 20, 103016. [Google Scholar] [CrossRef]
- Botsinis, P.; Alanis, D.; Babar, Z.; Nguyen, H.V.; Chandra, D.; Ng, S.X.; Hanzo, L. Quantum search algorithms for wireless communications. IEEE Commun. Surv. Tutor. 2018, 21, 1209–1242. [Google Scholar] [CrossRef]
- Cuomo, D.; Caleffi, M.; Cacciapuoti, A.S. Towards a distributed quantum computing ecosystem. IET Quantum Commun. 2020, 1, 3–8. [Google Scholar] [CrossRef]
- Egger, D.J.; Gambella, C.; Marecek, J.; McFaddin, S.; Mevissen, M.; Raymond, R.; Simonetto, A.; Woerner, S.; Yndurain, E. Quantum computing for Finance: State of the art and future prospects. IEEE Trans. Quantum Eng. 2020, 1. [Google Scholar] [CrossRef]
- Savchuk, M.; Fesenko, A. Quantum Computing: Survey and Analysis. Cybern. Syst. Anal. 2019, 55, 10–21. [Google Scholar] [CrossRef]
- McGeoch, C.C.; Harris, R.; Reinhardt, S.P.; Bunyk, P.I. Practical annealing-based quantum computing. Computer 2019, 52, 38–46. [Google Scholar] [CrossRef]
- Duan, S.; Cong, S.; Song, Y. A survey on quantum positioning system. Int. J. Model. Simul. 2021, 4, 265–283. [Google Scholar] [CrossRef]
- Preskill, J. Quantum Computing in the NISQ era and beyond. Quantum 2018, 2, 79. [Google Scholar] [CrossRef]
- Rowell, E.; Wang, Z. Mathematics of topological quantum computing. Bull. Am. Math. Soc. 2018, 55, 183–238. [Google Scholar] [CrossRef]
- Nejatollahi, H.; Dutt, N.; Ray, S.; Regazzoni, F.; Banerjee, I.; Cammarota, R. Post-quantum lattice-based cryptography implementations: A survey. ACM Comput. Surv. (CSUR) 2019, 51, 1–41. [Google Scholar] [CrossRef]
- Fingerhuth, M.; Babej, T.; Wittek, P. Open source software in quantum computing. PLoS ONE 2018, 13, e0208561. [Google Scholar] [CrossRef] [PubMed]
- Abbott, A. Quantum computers to explore precision oncology. Nat. Biotechnol. 2021, 39, 1324–1325. [Google Scholar] [CrossRef]
- Kumar, Y.; Koul, A.; Sisodia, P.S.; Shafi, J.; Kavita, V.; Gheisari, M.; Davoodi, M.B. Heart Failure Detection Using Quantum-Enhanced Machine Learning and Traditional Machine Learning Techniques for Internet of Artificially Intelligent Medical Things. Wirel. Commun. Mob. Comput. 2021, 2021, 1616725. [Google Scholar] [CrossRef]
- Olgiati, S.; Heidari, N.; Meloni, D.; Pirovano, F.; Noorani, A.; Slevin, M.; Azamfirei, L. A quantum-enhanced precision medicine application to support data-driven clinical decisions for the personalized treatment of advanced knee osteoarthritis: Development and preliminary validation of precisionKNEE QNN. medRxiv 2021, 2021, 1–5. [Google Scholar] [CrossRef]
- Gupta, S.; Modgil, S.; Bhatt, P.C.; Jabbour, C.J.C.; Kamble, S. Quantum computing led innovation for achieving a more sustainable COVID-19 healthcare industry. Technovation 2022, 120, 102544. [Google Scholar] [CrossRef]
- Kumar, A.; Bhushan, B.; Shriti, S.; Nand, P. Quantum Computing for Health Care: A Review on Implementation Trends and Recent Advances. Multimedia Technologies in the Internet of Things Environment, Volume 3; Springer: Berlin/Heidelberg, Germany, 2022; pp. 23–40. [Google Scholar]
- Sinitsyn, N.A. Computing with a single qubit faster than the computation quantum speed limit. Phys. Lett. A 2018, 382, 477–481. [Google Scholar] [CrossRef]
- Hanneke, D.; Home, J.; Jost, J.D.; Amini, J.M.; Leibfried, D.; Wineland, D.J. Realization of a programmable two-qubit quantum processor. Nat. Phys. 2010, 6, 13–16. [Google Scholar] [CrossRef]
- Balaganur, S. Man’s Race to Quantum Supremacy: The Complete Timeline; Analytics India Magazine: Bengaluru, India, 2019. [Google Scholar]
- Watabe, S.; Serikow, M.; Kawabata, S.; Zagoskin, A. Scaling Law in Large Quantum Devices with Dissipation. In Proceedings of the APS March Meeting Abstracts, Virtual, 15–19 March 2021. [Google Scholar]
- Boixo, S.; Isakov, S.V.; Smelyanskiy, V.N.; Babbush, R.; Ding, N.; Jiang, Z.; Bremner, M.J.; Martinis, J.M.; Neven, H. Characterizing quantum supremacy in near-term devices. Nat. Phys. 2018, 14, 595–600. [Google Scholar] [CrossRef]
- Zhong, H.S.; Wang, H.; Deng, Y.H.; Chen, M.C.; Peng, L.C.; Luo, Y.H.; Qin, J.; Wu, D.; Ding, X.; Hu, Y.; et al. Quantum computational advantage using photons. Science 2020, 370, 1460–1463. [Google Scholar] [CrossRef] [PubMed]
- Hu, X.M.; Huang, C.X.; Sheng, Y.B.; Zhou, L.; Liu, B.H.; Guo, Y.; Zhang, C.; Xing, W.B.; Huang, Y.F.; Li, C.F.; et al. Long-distance entanglement purification for quantum communication. Phys. Rev. Lett. 2021, 126, 010503. [Google Scholar] [CrossRef] [PubMed]
- Porter, J. Google Confirms ’Quantum Supremacy’ Breakthrough. Available online: https://www.theverge.com/2019/10/23/20928294/google-quantum-supremacy-sycamore-computer-qubit-milestone (accessed on 16 June 2021).
- Preskill, J. Fault-tolerant quantum computation. In Introduction to Quantum Computation and Information; World Scientific: Singapore, 1998; pp. 213–269. [Google Scholar]
- Moser, J.K. Lectures on Hamiltonian Systems; CRC Press: Boca Raton, FL, USA, 2020. [Google Scholar]
- Lanyon, B.P.; Weinhold, T.J.; Langford, N.K.; Barbieri, M.; James, D.F.; Gilchrist, A.; White, A.G. Experimental demonstration of a compiled version of Shor’s algorithm with quantum entanglement. Phys. Rev. Lett. 2007, 99, 250505. [Google Scholar] [CrossRef]
- National Academies of Sciences, Engineering, and Medicine. Quantum Computing: Progress and Prospects; The National Academies Press: Washington, DC, USA, 2019. [Google Scholar] [CrossRef]
- Childs, H. Applications of Cloud-Based Quantum Computers with Cognitive Computing Algorithms in Automated, Evidence-Based Virginia Geriatric Healthcare. Auctus J. Undergrad. Res. Creat. Available online: https://scholarscompass.vcu.edu/cgi/viewcontent.cgi?article=1075&context=auctus (accessed on 27 January 2023).
- Outeiral, C.; Strahm, M.; Shi, J.; Morris, G.M.; Benjamin, S.C.; Deane, C.M. The prospects of quantum computing in computational molecular biology. Wiley Interdiscip. Rev. Comput. Mol. Sci. 2021, 11, e1481. [Google Scholar] [CrossRef]
- Grimsley, H.R.; Economou, S.E.; Barnes, E.; Mayhall, N.J. An adaptive variational algorithm for exact molecular simulations on a quantum computer. Nat. Commun. 2019, 10, 3007. [Google Scholar] [CrossRef] [PubMed]
- Hu, F.; Wang, B.N.; Wang, N.; Wang, C. Quantum machine learning with D-wave quantum computer. Quantum Eng. 2019, 1, e12. [Google Scholar] [CrossRef]
- Yordanov, Y.S.; Arvidsson-Shukur, D.R.; Barnes, C.H. Efficient quantum circuits for quantum computational chemistry. Phys. Rev. A 2020, 102, 062612. [Google Scholar] [CrossRef]
- Malviya, R.; Sundram, S. Exploring potential of quantum computing in creating smart healthcare. Open Biol. J. 2022, 9, 56–57. [Google Scholar] [CrossRef]
- Marinho, M.M.; Almeida-Neto, F.W.Q.; Marinho, E.M.; da Silva, L.P.; Menezes, R.R.; Dos Santos, R.P.; Marinho, E.S.; de Lima-Neto, P.; Martins, A.M. Quantum computational investigations and molecular docking studies on amentoflavone. Heliyon 2021, 7, e06079. [Google Scholar] [CrossRef] [PubMed]
- Langione, M.; Bobier, J.F.; Meier, C.; Hasenfuss, S.; Schulze, U. Will Quantum Computing Transform Biopharma R&D? Available online: https://www.bcg.com/publications/2019/quantum-computing-transform-biopharma-research-development (accessed on 27 January 2023).
- Sarkar, A.; Al-Ars, Z.; Bertels, K. Estimating algorithmic information using quantum computing for genomics applications. Appl. Sci. 2021, 11, 2696. [Google Scholar] [CrossRef]
- Zinner, M.; Dahlhausen, F.; Boehme, P.; Ehlers, J.; Bieske, L.; Fehring, L. Quantum computing’s potential for drug discovery: Early stage industry dynamics. Drug Discov. Today 2021, 26, 1680–1688. [Google Scholar] [CrossRef] [PubMed]
- Birtwistle, M. Saving Lives and Averting Costs? The Case for Earlier Diagnosis Just Got Stronger; Cancer Research UK: London, UK, 22 September 2014. [Google Scholar]
- Singh, H.; Meyer, A.N.; Thomas, E.J. The frequency of diagnostic errors in outpatient care: Estimations from three large observational studies involving US adult populations. BMJ Qual. Saf. 2014, 23, 727–731. [Google Scholar] [CrossRef] [PubMed]
- Niraula, D.; Jamaluddin, J.; Matuszak, M.M.; Haken, R.K.T.; Naqa, I.E. Quantum deep reinforcement learning for clinical decision support in oncology: Application to adaptive radiotherapy. Sci. Rep. 2021, 11, 23545. [Google Scholar] [CrossRef] [PubMed]
- Pakela, J. Quantum Inspired Machine Learning Algorithms for Adaptive Radiotherapy. Ph.D. Thesis, University of Michiga, Ann Arbor, MI, USA, 2021. [Google Scholar]
- Flöther, F.F. The state of quantum computing applications in health and medicine. arXiv 2023, arXiv:2301.09106. [Google Scholar]
- Garzia, J.M. How Quantum Computing Could Remake Chemistry. Available online: https://www.scientificamerican.com/article/how-quantum-computing-could-remake-chemistry/ (accessed on 27 January 2023).
- Cao, Y.; Romero, J.; Olson, J.P.; Degroote, M.; Johnson, P.D.; Kieferová, M.; Kivlichan, I.D.; Menke, T.; Peropadre, B.; Sawaya, N.P.; et al. Quantum chemistry in the age of quantum computing. Chem. Rev. 2019, 119, 10856–10915. [Google Scholar] [CrossRef]
- Huggins, W.J.; O’Gorman, B.A.; Rubin, N.C.; Reichman, D.R.; Babbush, R.; Lee, J. Unbiasing fermionic quantum Monte Carlo with a quantum computer. Nature 2022, 603, 416–420. [Google Scholar] [CrossRef]
- Egger, D.J.; Gutiérrez, R.G.; Mestre, J.C.; Woerner, S. Credit risk analysis using quantum computers. IEEE Trans. Comput. 2020, 70, 2136–2145. [Google Scholar] [CrossRef]
- Woerner, S.; Egger, D.J. Quantum risk analysis. NPJ Quantum Inf. 2019, 5, 15. [Google Scholar] [CrossRef]
- Bova, F.; Goldfarb, A.; Melko, R.G. Commercial applications of quantum computing. EPJ Quantum Technol. 2021, 8, 2. [Google Scholar] [CrossRef]
- Giani, A.; Eldredge, Z. Quantum computing opportunities in renewable energy. SN Comput. Sci. 2021, 2, 393. [Google Scholar] [CrossRef]
- Chamola, V.; Jolfaei, A.; Chanana, V.; Parashari, P.; Hassija, V. Information security in the post quantum era for 5G and beyond networks: Threats to existing cryptography, and post-quantum cryptography. Comput. Commun. 2021, 176, 99–118. [Google Scholar] [CrossRef]
- Kwiat, P.; Mitchell, J.; Schwindt, P.; White, A. Grover’s search algorithm: An optical approach. J. Mod. Opt. 2000, 47, 257–266. [Google Scholar] [CrossRef]
- Bouchard, F.; England, D.; Bustard, P.J.; Heshami, K.; Sussman, B. Quantum communication with ultrafast time-bin qubits. PRX Quantum 2022, 3, 010332. [Google Scholar] [CrossRef]
- Stanco, A.; Santagiustina, F.B.; Calderaro, L.; Avesani, M.; Bertapelle, T.; Dequal, D.; Vallone, G.; Villoresi, P. Versatile and concurrent fpga-based architecture for practical quantum communication systems. IEEE Trans. Quantum Eng. 2022, 3, 1–8. [Google Scholar] [CrossRef]
- Wehner, S.; Elkouss, D.; Hanson, R. Quantum internet: A vision for the road ahead. Science 2018, 362, eaam9288. [Google Scholar] [CrossRef]
- Cacciapuoti, A.S.; Caleffi, M.; Tafuri, F.; Cataliotti, F.S.; Gherardini, S.; Bianchi, G. Quantum internet: Networking challenges in distributed quantum computing. IEEE Netw. 2019, 34, 137–143. [Google Scholar] [CrossRef]
- Young, N. An Introduction to Hilbert Space; Cambridge University Press: Cambridge, UK, 1988. [Google Scholar]
- Salakhutdinov, R.; Hinton, G. Deep Boltzmann Machines. In Proceedings of the Artificial Intelligence and Statistics, PMLR, Clearwater Beach, FL, USA, 16–18 April 2009; pp. 448–455. [Google Scholar]
- Neven, H.; Denchev, V.S.; Rose, G.; Macready, W.G. Training a large scale classifier with the quantum adiabatic algorithm. arXiv 2009, arXiv:0912.0779. [Google Scholar]
- Paler, A.; Polian, I.; Nemoto, K.; Devitt, S.J. Fault-tolerant, high-level quantum circuits: Form, compilation and description. Quantum Sci. Technol. 2017, 2, 025003. [Google Scholar] [CrossRef]
- Farhi, E.; Goldstone, J.; Gutmann, S. A quantum approximate optimization algorithm. arXiv 2014, arXiv:1411.4028. [Google Scholar]
- Gyongyosi, L. Quantum state optimization and computational pathway evaluation for gate-model quantum computers. Sci. Rep. 2020, 10, 14220. [Google Scholar] [CrossRef]
- Farhi, E.; Goldstone, J.; Gutmann, S.; Neven, H. Quantum algorithms for fixed qubit architectures. arXiv 2017, arXiv:1703.06199. [Google Scholar]
- Van Meter, R.D. Architecture of a quantum multicomputer optimized for Shor’s factoring algorithm. arXiv 2006, arXiv:quantph/0607065. [Google Scholar]
- Ekert, A.; Jozsa, R. Quantum computation and Shor’s factoring algorithm. Rev. Mod. Phys. 1996, 68, 733. [Google Scholar] [CrossRef]
- Van Meter, R.; Devitt, S.J. Local and distributed quantum computation. arXiv 2016, arXiv:1605.06951. [Google Scholar]
- Ahsan, M.; Meter, R.V.; Kim, J. Designing a million-qubit quantum computer using a resource performance simulator. ACM J. Emerg. Technol. Comput. Syst. (JETC) 2015, 12, 1–25. [Google Scholar] [CrossRef]
- Wan, K.H.; Dahlsten, O.; Kristjánsson, H.; Gardner, R.; Kim, M. Quantum generalisation of feedforward neural networks. NPJ Quantum Inf. 2017, 3, 36. [Google Scholar] [CrossRef]
- Altaisky, M.V.; Zolnikova, N.N.; Kaputkina, N.E.; Krylov, V.A.; Lozovik, Y.E.; Dattani, N.S. Towards a feasible implementation of quantum neural networks using quantum dots. Appl. Phys. Lett. 2016, 108, 103108. [Google Scholar] [CrossRef]
- Blakestad, R.; Ospelkaus, C.; VanDevender, A.; Amini, J.; Britton, J.; Leibfried, D.; Wineland, D.J. High-fidelity transport of trapped-ion qubits through an X-junction trap array. Phys. Rev. Lett. 2009, 102, 153002. [Google Scholar] [CrossRef]
- Brown, K.R.; Kim, J.; Monroe, C. Co-designing a scalable quantum computer with trapped atomic ions. NPJ Quantum Inf. 2016, 2, 16034. [Google Scholar] [CrossRef]
- Cirac, J.I.; Zoller, P. Quantum computations with cold trapped ions. Phys. Rev. Lett. 1995, 74, 4091. [Google Scholar] [CrossRef] [PubMed]
- Duan, L.M.; Madsen, M.; Moehring, D.; Maunz, P.; Kohn, R., Jr.; Monroe, C. Probabilistic quantum gates between remote atoms through interference of optical frequency qubits. Phys. Rev. A 2006, 73, 062324. [Google Scholar] [CrossRef]
- Hensinger, W.; Olmschenk, S.; Stick, D.; Hucul, D.; Yeo, M.; Acton, M.; Deslauriers, L.; Monroe, C.; Rabchuk, J. T-junction ion trap array for two-dimensional ion shuttling, storage, and manipulation. Appl. Phys. Lett. 2006, 88, 034101. [Google Scholar] [CrossRef]
- Hucul, D.; Inlek, I.V.; Vittorini, G.; Crocker, C.; Debnath, S.; Clark, S.M.; Monroe, C. Modular entanglement of atomic qubits using photons and phonons. Nat. Phys. 2015, 11, 37–42. [Google Scholar] [CrossRef]
- Monz, T.; Nigg, D.; Martinez, E.A.; Brandl, M.F.; Schindler, P.; Rines, R.; Wang, S.X.; Chuang, I.L.; Blatt, R. Realization of a scalable Shor algorithm. Science 2016, 351, 1068–1070. [Google Scholar] [CrossRef] [PubMed]
- Lamata, L. Basic protocols in quantum reinforcement learning with superconducting circuits. Sci. Rep. 2017, 7, 1609. [Google Scholar] [CrossRef] [PubMed]
- Kerenidis, I.; Prakash, A. Quantum recommendation systems. arXiv 2016, arXiv:1603.08675. [Google Scholar]
- Benedetti, M.; Realpe-Gómez, J.; Perdomo-Ortiz, A. Quantum-assisted Helmholtz machines: A quantum–classical deep learning framework for industrial datasets in near-term devices. Quantum Sci. Technol. 2018, 3, 034007. [Google Scholar] [CrossRef]
- Copsey, D.; Oskin, M.; Impens, F.; Metodiev, T.; Cross, A.; Chong, F.T.; Chuang, I.L.; Kubiatowicz, J. Toward a scalable, silicon-based quantum computing architecture. IEEE J. Sel. Top. Quantum Electron. 2003, 9, 1552–1569. [Google Scholar] [CrossRef]
- Jones, N.C.; Van Meter, R.; Fowler, A.G.; McMahon, P.L.; Kim, J.; Ladd, T.D.; Yamamoto, Y. Layered architecture for quantum computing. Phys. Rev. X 2012, 2, 031007. [Google Scholar] [CrossRef]
- Svore, K.M.; Aho, A.V.; Cross, A.W.; Chuang, I.; Markov, I.L. A layered software architecture for quantum computing design tools. Computer 2006, 39, 74–83. [Google Scholar] [CrossRef]
- Spiller, T.P.; Munro, W.J.; Barrett, S.D.; Kok, P. An introduction to quantum information processing: Applications and realizations. Contemp. Phys. 2005, 46, 407–436. [Google Scholar] [CrossRef]
- Meter, R.v.; Oskin, M. Architectural implications of quantum computing technologies. ACM J. Emerg. Technol. Comput. Syst. (JETC) 2006, 2, 31–63. [Google Scholar] [CrossRef]
- DiVincenzo, D.P. The physical implementation of quantum computation. Fortschritte Phys. Prog. Phys. 2000, 48, 771–783. [Google Scholar] [CrossRef]
- Steane, A.M. Quantum computer architecture for fast entropy extraction. arXiv 2002, arXiv:quant-ph/0203047. [Google Scholar] [CrossRef]
- Steane, A.M. How to build a 300 bit, 1 giga-operation quantum computer. arXiv 2004, arXiv:quant-ph/0412165. [Google Scholar] [CrossRef]
- Linke, N.M.; Maslov, D.; Roetteler, M.; Debnath, S.; Figgatt, C.; Landsman, K.A.; Wright, K.; Monroe, C. Experimental comparison of two quantum computing architectures. Proc. Natl. Acad. Sci. USA 2017, 114, 3305–3310. [Google Scholar] [CrossRef]
- Sengupta, K.; Srivastava, P.R. Quantum algorithm for quicker clinical prognostic analysis: An application and experimental study using CT scan images of COVID-19 patients. BMC Med. Inform. Decis. Mak. 2021, 21, 227. [Google Scholar] [CrossRef]
- Hussain, M.; Wei, L.F.; Abbas, F.; Rehman, A.; Ali, M.; Lakhan, A. A multi-objective quantum-inspired genetic algorithm for workflow healthcare application scheduling with hard and soft deadline constraints in hybrid clouds. Appl. Soft Comput. 2022, 128, 109440. [Google Scholar] [CrossRef]
- SEEQC UK Receives 7.99M Grant from Innovate UK to Build Quantum Enhanced Computer for Pharmaceutical R&D|Silicon Canals. Available online: https://siliconcanals.com/crowdfunding/seeqc-uk-receives-7-99m-grant/. (accessed on 18 February 2023).
- Castellanos, S. Quantum Computing May Speed Drug Discovery, Biogen Test Suggests. The Wall Street Journal. Available online: https://www.wsj.com/articles/BL-CIOB-12236 (accessed on 27 January 2023).
- Liu, Z.; Liang, X.; Huang, M. Design of Logistic Regression Health Assessment Model Using Novel Quantum PSO. In Proceedings of the 2018 IEEE 3rd International Conference on Cloud Computing and Internet of Things (CCIOT), Dalian, China, 20–21 October 2018; pp. 39–42. [Google Scholar]
- Javidi, B. 3D imaging with applications to displays, quantum imaging, optical security, and healthcare. In Proceedings of the 2015 14th Workshop on Information Optics (WIO), Kyoto, Japan, 1–5 June 2015; pp. 1–3. [Google Scholar]
- Datta, S.; Newell, B.; Lamb, J.; Tang, Y.; Schoettker, P.; Santucci, C.; Pachta, T.G.; Joshi, S.; Geman, O.; Vanegas, D.C.; et al. Aptamers for Detection and Diagnostics (ADD) is a Proposed Mobile App Acquiring Optical Data from Conjugated Quantum Nanodots to Identify Molecules Indicating Presence of SARS-CoV-2 Virus: Why Public Health and Healthcare Need Smartphone Sensors as a Platform for Early Detection and Prevention. ChemRxiv. Available online: https://chemrxiv.org/engage/chemrxiv/article-details/617c108926b9c744380acf48 (accessed on 27 January 2023).
- Koyama, T.; Shibata, N.; Kino, S.; Sugiyama, A.; Akikusa, N.; Matsuura, Y. A Compact Mid-Infrared Spectroscopy System for Healthcare Applications Based on a Wavelength-Swept, Pulsed Quantum Cascade Laser. Sensors 2020, 20, 3438. [Google Scholar] [CrossRef] [PubMed]
- Naresh, V.S.; Nasralla, M.M.; Reddi, S.; García-Magariño, I. Quantum Diffie–Hellman Extended to Dynamic Quantum Group Key Agreement for e-Healthcare Multi-Agent Systems in Smart Cities. Sensors 2020, 20, 3940. [Google Scholar] [CrossRef] [PubMed]
- Janani, T.; Brindha, M. A secure medical image transmission scheme aided by quantum representation. J. Inf. Secur. Appl. 2021, 59, 102832. [Google Scholar] [CrossRef]
- Qiu, L.; Cai, F.; Xu, G. Quantum digital signature for the access control of sensitive data in the big data era. Future Gener. Comput. Syst. 2018, 86, 372–379. [Google Scholar] [CrossRef]
- Abd EL-Latif, A.A.; Abd-El-Atty, B.; Abou-Nassar, E.M.; Venegas-Andraca, S.E. Controlled alternate quantum walks based privacy preserving healthcare images in Internet of Things. Opt. Laser Technol. 2020, 124, 105942. [Google Scholar] [CrossRef]
- Bhavin, M.; Tanwar, S.; Sharma, N.; Tyagi, S.; Kumar, N. Blockchain and quantum blind signature-based hybrid scheme for healthcare 5.0 applications. J. Inf. Secur. Appl. 2021, 56, 102673. [Google Scholar] [CrossRef]
- Abd El-Latif, A.A.; Abd-El-Atty, B.; Hossain, M.S.; Rahman, M.A.; Alamri, A.; Gupta, B.B. Efficient quantum information hiding for remote medical image sharing. IEEE Access 2018, 6, 21075–21083. [Google Scholar] [CrossRef]
- Perumal, A.M.; Nadar, E.R.S. Architectural framework and simulation of quantum key optimization techniques in healthcare networks for data security. J. Ambient. Intell. Humaniz. Comput. 2021, 12, 7173–7180. [Google Scholar] [CrossRef]
- Helgeson, H.L.; Peyerl, C.K.; Solheim-Witt, M. Quantum physics principles and communication in the acute healthcare setting: A pilot study. EXPLORE J. Sci. Health 2016, 12, 408–415. [Google Scholar] [CrossRef]
- Hastings, J. Modern nursing and modern physics: Does quantum theory contain useful insights for nursing practice and healthcare management? Nurs. Philos. 2002, 3, 205–212. [Google Scholar] [CrossRef]
- Porter-O’Grady, T. Quantum mechanics and the future of healthcare leadership. J. Nurs. Adm. 1997, 27, 15–20. [Google Scholar] [CrossRef]
- Latif, S.; Qadir, J.; Farooq, S.; Imran, M.A. How 5G wireless (and concomitant technologies) will revolutionize healthcare? Future Internet 2017, 9, 93. [Google Scholar] [CrossRef]
- Brooks, C. Quantum Trends and the Internet of Things. Available online: https://www.forbes.com/sites/cognitiveworld/2019/12/05/quantum-trends-and-the-internet-of-things/?sh=148479943eb0 (accessed on 16 June 2021).
- Bennett, C.H.; Brassard, G. Quantum cryptography: Public key distribution and coin tossing. arXiv 2020, arXiv:2003.06557. [Google Scholar] [CrossRef]
- Shor, P.W.; Preskill, J. Simple proof of security of the BB84 quantum key distribution protocol. Phys. Rev. Lett. 2000, 85, 441. [Google Scholar] [CrossRef] [PubMed]
- Rapeaux, A.B.; Constandinou, T.G. Implantable brain machine interfaces: First-in-human studies, technology challenges and trends. Curr. Opin. Biotechnol. 2021, 72, 102–111. [Google Scholar] [CrossRef] [PubMed]
- Cerf, N.J.; Bourennane, M.; Karlsson, A.; Gisin, N. Security of quantum key distribution using d-level systems. Phys. Rev. Lett. 2002, 88, 127902. [Google Scholar] [CrossRef]
- Waks, E.; Zeevi, A.; Yamamoto, Y. Security of quantum key distribution with entangled photons against individual attacks. Phys. Rev. A 2002, 65, 052310. [Google Scholar] [CrossRef]
- Hwang, W.Y. Quantum key distribution with high loss: Toward global secure communication. Phys. Rev. Lett. 2003, 91, 057901. [Google Scholar] [CrossRef] [PubMed]
- Iblisdir, S.; Van Assche, G.; Cerf, N. Security of quantum key distribution with coherent states and homodyne detection. Phys. Rev. Lett. 2004, 93, 170502. [Google Scholar] [CrossRef] [PubMed]
- Biham, E.; Boyer, M.; Boykin, P.O.; Mor, T.; Roychowdhury, V. A proof of the security of quantum key distribution. J. Cryptol. 2006, 19, 381–439. [Google Scholar] [CrossRef]
- Acín, A.; Brunner, N.; Gisin, N.; Massar, S.; Pironio, S.; Scarani, V. Device-independent security of quantum cryptography against collective attacks. Phys. Rev. Lett. 2007, 98, 230501. [Google Scholar] [CrossRef] [PubMed]
- McKague, M. Device independent quantum key distribution secure against coherent attacks with memoryless measurement devices. New J. Phys. 2009, 11, 103037. [Google Scholar] [CrossRef]
- Zhao, Y.; Qi, B.; Lo, H.K.; Qian, L. Security analysis of an untrusted source for quantum key distribution: Passive approach. New J. Phys. 2010, 12, 023024. [Google Scholar] [CrossRef]
- Marøy, Ø.; Lydersen, L.; Skaar, J. Security of quantum key distribution with arbitrary individual imperfections. Phys. Rev. A 2010, 82, 032337. [Google Scholar] [CrossRef]
- Pawłowski, M.; Brunner, N. Semi-device-independent security of one-way quantum key distribution. PHysical Rev. A 2011, 84, 010302. [Google Scholar] [CrossRef]
- Masanes, L.; Pironio, S.; Acín, A. Secure device-independent quantum key distribution with causally independent measurement devices. Nat. Commun. 2011, 2, 238. [Google Scholar] [CrossRef] [PubMed]
- Masanes, L.; Renner, R.; Christandl, M.; Winter, A.; Barrett, J. Full security of quantum key distribution from no-signaling constraints. IEEE Trans. Inf. Theory 2014, 60, 4973–4986. [Google Scholar] [CrossRef]
- Leverrier, A.; García-Patrón, R.; Renner, R.; Cerf, N.J. Security of continuous-variable quantum key distribution against general attacks. Phys. Rev. Lett. 2013, 110, 030502. [Google Scholar] [CrossRef]
- Moroder, T.; Curty, M.; Lim, C.C.W.; Zbinden, H.; Gisin, N. Security of distributed-phase-reference quantum key distribution. Phys. Rev. Lett. 2012, 109, 260501. [Google Scholar] [CrossRef]
- Zhang, H.; Mao, Y.; Huang, D.; Li, J.; Zhang, L.; Guo, Y. Security analysis of orthogonal-frequency-division-multiplexing–based continuous-variable quantum key distribution with imperfect modulation. Phys. Rev. A 2018, 97, 052328. [Google Scholar] [CrossRef]
- Lupo, C.; Ottaviani, C.; Papanastasiou, P.; Pirandola, S. Continuous-variable measurement-device-independent quantum key distribution: Composable security against coherent attacks. Phys. Rev. A 2018, 97, 052327. [Google Scholar] [CrossRef]
- Pironio, S.; Masanes, L.; Leverrier, A.; Acín, A. Security of device-independent quantum key distribution in the bounded-quantum-storage model. Phys. Rev. X 2013, 3, 031007. [Google Scholar] [CrossRef]
- Beaudry, N.J.; Lucamarini, M.; Mancini, S.; Renner, R. Security of two-way quantum key distribution. Phys. Rev. A 2013, 88, 062302. [Google Scholar] [CrossRef]
- Vazirani, U.; Vidick, T. Fully device independent quantum key distribution. Commun. ACM 2019, 62, 133. [Google Scholar] [CrossRef]
- Sheridan, L.; Scarani, V. Security proof for quantum key distribution using qudit systems. Phys. Rev. A 2010, 82, 030301. [Google Scholar] [CrossRef]
- Cai, R.Y.; Scarani, V. Finite-key analysis for practical implementations of quantum key distribution. New J. Phys. 2009, 11, 045024. [Google Scholar] [CrossRef]
- Song, T.T.; Wen, Q.Y.; Guo, F.Z.; Tan, X.Q. Finite-key analysis for measurement-device-independent quantum key distribution. Phys. Rev. A 2012, 86, 022332. [Google Scholar] [CrossRef]
- Curty, M.; Xu, F.; Cui, W.; Lim, C.C.W.; Tamaki, K.; Lo, H.K. Finite-key analysis for measurement-device-independent quantum key distribution. Nat. Commun. 2014, 5, 3732. [Google Scholar] [CrossRef]
- Zhou, C.; Xu, P.; Bao, W.S.; Wang, Y.; Zhang, Y.; Jiang, M.S.; Li, H.W. Finite-key bound for semi-device-independent quantum key distribution. Opt. Express 2017, 25, 16971–16980. [Google Scholar] [CrossRef]
- Wang, W.; Tamaki, K.; Curty, M. Finite-key security analysis for quantum key distribution with leaky sources. New J. Phys. 2018, 20, 083027. [Google Scholar] [CrossRef]
- Barrett, J.; Colbeck, R.; Kent, A. Memory attacks on device-independent quantum cryptography. Phys. Rev. Lett. 2013, 110, 010503. [Google Scholar] [CrossRef] [PubMed]
- Qi, B.; Fung, C.H.F.; Lo, H.K.; Ma, X. Time-shift attack in practical quantum cryptosystems. arXiv 2005, arXiv:quant-ph/0512080. [Google Scholar] [CrossRef]
- Fung, C.H.F.; Qi, B.; Tamaki, K.; Lo, H.K. Phase-remapping attack in practical quantum-key-distribution systems. Phys. Rev. A 2007, 75, 032314. [Google Scholar] [CrossRef]
- Lydersen, L.; Wiechers, C.; Wittmann, C.; Elser, D.; Skaar, J.; Makarov, V. Hacking commercial quantum cryptography systems by tailored bright illumination. Nat. Photonics 2010, 4, 686–689. [Google Scholar] [CrossRef]
- Li, H.W.; Wang, S.; Huang, J.Z.; Chen, W.; Yin, Z.Q.; Li, F.Y.; Zhou, Z.; Liu, D.; Zhang, Y.; Guo, G.C.; et al. Attacking a practical quantum-key-distribution system with wavelength-dependent beam-splitter and multiwavelength sources. Phys. Rev. A 2011, 84, 062308. [Google Scholar] [CrossRef]
- Lim, C.C.W.; Portmann, C.; Tomamichel, M.; Renner, R.; Gisin, N. Device-independent quantum key distribution with local Bell test. Phys. Rev. X 2013, 3, 031006. [Google Scholar] [CrossRef]
- Broadbent, C.J.; Marshall, K.; Weedbrook, C.; Howell, J.C. Device-independent quantum key distribution with generalized two-mode Schrödinger cat states. Phys. Rev. A 2015, 92, 052318. [Google Scholar]
- Lo, H.K.; Curty, M.; Qi, B. Measurement-device-independent quantum key distribution. Phys. Rev. Lett. 2012, 108, 130503. [Google Scholar]
- Li, Z.; Zhang, Y.C.; Xu, F.; Peng, X.; Guo, H. Continuous-variable measurement-device-independent quantum key distribution. Phys. Rev. A 2014, 89, 052301. [Google Scholar]
- Ma, X.C.; Sun, S.H.; Jiang, M.S.; Gui, M.; Liang, L.M. Gaussian-modulated coherent-state measurement-device-independent quantum key distribution. Phys. Rev. A 2014, 89, 042335. [Google Scholar] [CrossRef]
- Zhou, C.; Bao, W.S.; Zhang, H.l.; Li, H.W.; Wang, Y.; Li, Y.; Wang, X. Biased decoy-state measurement-device-independent quantum key distribution with finite resources. Phys. Rev. A 2015, 91, 022313. [Google Scholar] [CrossRef]
- Tamaki, K.; Lo, H.K.; Fung, C.H.F.; Qi, B. Phase encoding schemes for measurement-device-independent quantum key distribution with basis-dependent flaw. Phys. Rev. A 2012, 85, 042307. [Google Scholar] [CrossRef]
- Zhao, Y.; Zhang, Y.; Xu, B.; Yu, S.; Guo, H. Continuous-variable measurement-device-independent quantum key distribution with virtual photon subtraction. Phys. Rev. A 2018, 97, 042328. [Google Scholar] [CrossRef]
- Ma, H.X.; Huang, P.; Bai, D.Y.; Wang, S.Y.; Bao, W.S.; Zeng, G.H. Continuous-variable measurement-device-independent quantum key distribution with photon subtraction. Phys. Rev. A 2018, 97, 042329. [Google Scholar] [CrossRef]
- Li, C.Y. Fault-tolerant measurement-device-independent quantum key distribution in a decoherence-free subspace. Quantum Inf. Process. 2018, 17, 287. [Google Scholar] [CrossRef]
- Boyer, M.; Kenigsberg, D.; Mor, T. Quantum key distribution with classical Bob. In Proceedings of the 2007 First International Conference on Quantum, Nano, and Micro Technologies (ICQNM’07), Guadeloupe, France, 2–6 January 2007; p. 10. [Google Scholar]
- Boyer, M.; Gelles, R.; Kenigsberg, D.; Mor, T. Semiquantum key distribution. Phys. Rev. A 2009, 79, 032341. [Google Scholar]
- Lu, H.; Cai, Q.Y. Quantum key distribution with classical Alice. Int. J. Quantum Inf. 2008, 6, 1195–1202. [Google Scholar] [CrossRef]
- Zou, X.; Qiu, D.; Li, L.; Wu, L.; Li, L. Semiquantum-key distribution using less than four quantum states. Phys. Rev. A 2009, 79, 052312. [Google Scholar]
- Maitra, A.; Paul, G. Eavesdropping in semiquantum key distribution protocol. Inf. Process. Lett. 2013, 113, 418–422. [Google Scholar] [CrossRef]
- Krawec, W.O. Mediated semiquantum key distribution. Phys. Rev. A 2015, 91, 032323. [Google Scholar] [CrossRef]
- Zou, X.; Qiu, D.; Zhang, S.; Mateus, P. Semiquantum key distribution without invoking the classical party’s measurement capability. Quantum Inf. Process. 2015, 14, 2981–2996. [Google Scholar] [CrossRef]
- Liu, Z.R.; Hwang, T. Mediated Semi-Quantum Key Distribution Without Invoking Quantum Measurement. Ann. Phys. 2018, 530, 1700206. [Google Scholar] [CrossRef]
- Sun, Z.; Du, R.; Long, D. Semi-quantum key distribution protocol using Bell state. arXiv 2011, arXiv:1106.2910. [Google Scholar]
- Jian, W.; Sheng, Z.; Quan, Z.; Chao-Jing, T. Semiquantum key distribution using entangled states. Chin. Phys. Lett. 2011, 28, 100301. [Google Scholar]
- Yu, K.F.; Yang, C.W.; Liao, C.H.; Hwang, T. Authenticated semi-quantum key distribution protocol using Bell states. Quantum Inf. Process. 2014, 13, 1457–1465. [Google Scholar] [CrossRef]
- Li, Q.; Chan, W.H.; Zhang, S. Semiquantum key distribution with secure delegated quantum computation. Sci. Rep. 2016, 6, 19898. [Google Scholar] [CrossRef]
- He, J.; Li, Q.; Wu, C.; Chan, W.H.; Zhang, S. Measurement-device-independent semiquantum key distribution. Int. J. Quantum Inf. 2018, 16, 1850012. [Google Scholar] [CrossRef]
- Zhu, K.N.; Zhou, N.R.; Wang, Y.Q.; Wen, X.J. Semi-quantum key distribution protocols with GHZ states. Int. J. Theor. Phys. 2018, 57, 3621–3631. [Google Scholar] [CrossRef]
- Krawec, W.O. Restricted attacks on semi-quantum key distribution protocols. Quantum Inf. Process. 2014, 13, 2417–2436. [Google Scholar] [CrossRef]
- Yang, Y.G.; Sun, S.J.; Zhao, Q.Q. Trojan-horse attacks on quantum key distribution with classical Bob. Quantum Inf. Process. 2015, 14, 681–686. [Google Scholar] [CrossRef]
- Krawec, W.O. Security of a semi-quantum protocol where reflections contribute to the secret key. Quantum Inf. Process. 2016, 15, 2067–2090. [Google Scholar] [CrossRef]
- Boyer, M.; Katz, M.; Liss, R.; Mor, T. Experimentally feasible protocol for semiquantum key distribution. Phys. Rev. A 2017, 96, 062335. [Google Scholar] [CrossRef]
- Shafqat, S.; Kishwer, S.; Rasool, R.U.; Qadir, J.; Amjad, T.; Ahmad, H.F. Big data analytics enhanced healthcare systems: A review. J. Supercomput. 2020, 76, 1754–1799. [Google Scholar] [CrossRef]
- Ali, F.; El-Sappagh, S.; Islam, S.R.; Kwak, D.; Ali, A.; Imran, M.; Kwak, K.S. A smart healthcare monitoring system for heart disease prediction based on ensemble deep learning and feature fusion. Inf. Fusion 2020, 63, 208–222. [Google Scholar] [CrossRef]
- Ma, Y.; Tresp, V. Quantum machine learning algorithm for knowledge graphs. ACM Trans. Quantum Comput. 2021, 2, 1–28. [Google Scholar] [CrossRef]
- Chehimi, M.; Chaccour, C.; Saad, W. Quantum Semantic Communications: An Unexplored Avenue for Contextual Networking. arXiv 2022, arXiv:2205.02422. [Google Scholar]
- Solenov, D.; Brieler, J.; Scherrer, J.F. The potential of quantum computing and machine learning to advance clinical research and change the practice of medicine. Mo. Med. 2018, 115, 463. [Google Scholar]
- Sutskever, I.; Hinton, G.E.; Taylor, G.W. The recurrent temporal restricted Boltzmann machine. In Proceedings of the Advances in Neural Information Processing Systems, Vancouver, BC, Canada, 7–10 December 2009; pp. 1601–1608. [Google Scholar]
- Bruynseels, K.; Santoni de Sio, F.; van den Hoven, J. Digital twins in health care: Ethical implications of an emerging engineering paradigm. Front. Genet. 2018, 9, 31. [Google Scholar] [CrossRef]
- Rasheed, K.; Qayyum, A.; Ghaly, M.; Al-Fuqaha, A.; Razi, A.; Qadir, J. Explainable, trustworthy, and ethical machine learning for healthcare: A survey. Comput. Biol. Med. 2022, 149, 106043. [Google Scholar] [CrossRef]
- Cleveland Clinic. Cleveland Clinic and IBM Begin Installation of IBM Quantum System One. Cleaveland Clin. Newsroom. Available online: https://newsroom.ibm.com/2022-10-18-Cleveland-Clinic-and-IBM-Begin-Installation-of-IBM-Quantum-System-One (accessed on 27 January 2023).
- Gonzalez, C. Cloud based QC with Amazon Braket. Digit. Welt 2021, 5, 14–17. [Google Scholar] [CrossRef]
- Rigetti, C.; Blais, A.; Devoret, M. Protocol for universal gates in optimally biased superconducting qubits. Phys. Rev. Lett. 2005, 94, 240502. [Google Scholar] [CrossRef]
- Axelrod, R. Effective choice in the prisoner’s dilemma. J. Confl. Resolut. 1980, 24, 3–25. [Google Scholar] [CrossRef]
- Pardalos, P.M.; Migdalas, A.; Pitsoulis, L. Pareto Optimality, Game Theory and Equilibria; Springer Science & Business Media: New York, NY, USA, 2008; Volume 17. [Google Scholar]
- Mailath, G.J. Do people play Nash equilibrium? Lessons from evolutionary game theory. J. Econ. Lit. 1998, 36, 1347–1374. [Google Scholar]
- Qayyum, A.; Qadir, J.; Bilal, M.; Al-Fuqaha, A. Secure and Robust Machine Learning for Healthcare: A Survey. IEEE Rev. Biomed. Eng. 2020, 14, 156–180. [Google Scholar] [CrossRef] [PubMed]
- Qayyum, A.; Usama, M.; Qadir, J.; Al-Fuqaha, A. Securing connected & autonomous vehicles: Challenges posed by adversarial machine learning and the way forward. IEEE Commun. Surv. Tutor. 2020, 22, 998–1026. [Google Scholar]
- Qayyum, A.; Ijaz, A.; Usama, M.; Iqbal, W.; Qadir, J.; Elkhatib, Y.; Al-Fuqaha, A. Securing Machine Learning in the Cloud: A Systematic Review of Cloud Machine Learning Security. Front. Big Data 2020, 3. [Google Scholar] [CrossRef] [PubMed]
- Business Wire. D-Wave Launches in AWS Marketplace. Available online: https://www.businesswire.com/news/home/20221021005086/en/D-Wave-Launches-in-AWS-Marketplace (accessed on 23 October 2022).

| 3GPP | Third-Generation Partnership Project |
| 5G | Fifth Generation |
| ADD | Aptamers for Detection and Diagnostics |
| AI | Artificial Intelligence |
| DH | Diffie–Hellman |
| ECC | Elliptic Curve Cryptography |
| EHR | Electronic Health Records |
| IC | Integrated Circuit |
| IoT | Internet of Things |
| IT | Information Technology |
| ML | Machine Learning |
| MRI | Magnetic Resonance Imaging |
| NIST | National Institute of Standards and Technology |
| QAOA | Quantum Approximate Optimization Algorithm |
| QKD | Quantum Key Distribution |
| QoS | Quality of Service |
| Qubits | Quantum Bits |
| RSA | Rivest–Shamir–Adleman |
| SDK | Software-Development Kits |
| TLS | Transport Layer Security |
| TSP | Traveling Salesman Problem |
| VLSI | Very Large Circuits Integration |
| Requirements | Challenges | Solutions |
|---|---|---|
| Computational power |
|
|
| High-speed connectivity (5G/6G networks) |
|
|
| Higher-dimensional quantum computing |
|
|
| Scalability of quantum computing |
|
|
| Fault tolerance |
|
|
| Quantum availability of the healthcare systems |
|
|
| Deployment of quantum gates |
|
|
| Use of distributed topologies |
|
|
| Requirements for physical implementation |
|
|
| Quantum ML |
|
|
| Technique | Healthcare | Security | Performance | Scalability | IoT | Key Feature |
|---|---|---|---|---|---|---|
| Liu et al. [113] | ✓ | × | ✓ | × | × | Logistic regression |
| Janani et al. [118] | ✓ | ✓ | ✓ | × | ✓ | Blockchain |
| Qiu et al. [119] | × | ✓ | ✓ | ✓ | × | Digital signature |
| Helgeson et al. [124] | ✓ | × | × | × | × | Survey |
| Latif et al. [120] | ✓ | ✓ | ✓ | ✓ | × | Quantum walks |
| Bhavin et al. [121] | ✓ | ✓ | × | ✓ | ✓ | Blockchain |
| Javidi [114] | ✓ | × | ✓ | × | × | 3D images visualization |
| Childs [49] | ✓ | × | ✓ | × | × | Cloud computing |
| Perumal et al. [123] | ✓ | ✓ | × | × | × | Qubits quantum |
| Latif et al. [122] | ✓ | ✓ | × | × | × | Quantum watermarking |
| Hastings [125] | ✓ | × | × | × | × | Literature review |
| Grady et al. [126] | × | × | × | × | × | Quantum leadership |
| Datta et al. [115] | ✓ | × | ✓ | × | ✓ | Smartphone app |
| Koyama et al. [116] | ✓ | × | ✓ | ✓ | ✓ | High-speed wavelet |
| Narseh et al. [117] | ✓ | × | ✓ | ✓ | ✓ | DH extension |
| Author | Objective | Security Algorithm | Pros | Cons |
|---|---|---|---|---|
| Cerf et al. [132] |
|
|
|
|
| Waks et al. [133] |
|
|
|
|
| Hwang [134] |
|
|
|
|
| Iblisdir et al. [135] |
|
|
|
|
| Biham et al. [136] |
|
|
|
|
| Acin et al. 2020 [137] |
|
|
|
|
| Mckague et al. 2019 [138] |
|
|
|
|
| Zhao et al. [139] |
|
|
|
|
| Author | Objective | Security Algorithm | Pros | Cons |
|---|---|---|---|---|
| Maroy et al. [140] |
|
|
|
|
| Sheridan et al. [151] |
|
|
|
|
| Pawlowski [141] |
|
|
|
|
| Masanes et al. [142] |
|
|
|
|
| Moroder et al. [145] |
|
|
|
|
| Beaudry et al. [149] |
|
|
|
|
| Leverrier et al. 2019 [144] |
|
|
|
|
| Prionio et al. [148] |
|
|
|
|
| Masnes et al. [143] |
|
|
|
|
| Vazirani et al. [150] |
|
|
|
|
| Zhang et al. [146] |
|
|
|
|
| Lupo et al. [147] |
|
|
|
|
| Author | Objective | Security Algorithm | Pros | Cons |
|---|---|---|---|---|
| Cai et al. [152] |
|
|
|
|
| Song et al. [153] |
|
|
|
|
| Curty et al. [154] |
|
|
|
|
| Zhou et al. [155] |
|
|
|
|
| Author | Objective | Security Algorithm | Pros | Cons |
|---|---|---|---|---|
| Boyer et al. [173] |
|
|
|
|
| Boyer 2017 et al. [189] |
|
|
|
|
| Lu 2008 et al. [174] |
|
|
|
|
| Zou et al. [175] |
|
|
|
|
| Maitra et al. [176] |
|
|
|
|
| Krawec et al. [177] |
|
|
|
|
| Zou et al. [178] |
|
|
|
|
| Liu et al. [179] |
|
|
|
|
| Sun et al. [180] |
|
|
|
|
| Jian et al. [181] |
|
|
|
|
| Yu et al. [182] |
|
|
|
|
| Li et al. [183] |
|
|
|
|
| Li et al. [183] |
|
|
|
|
| He et al. [184] |
|
|
|
|
| Zhu et al. [184] |
|
|
|
|
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2023 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Ur Rasool, R.; Ahmad, H.F.; Rafique, W.; Qayyum, A.; Qadir, J.; Anwar, Z. Quantum Computing for Healthcare: A Review. Future Internet 2023, 15, 94. https://doi.org/10.3390/fi15030094
Ur Rasool R, Ahmad HF, Rafique W, Qayyum A, Qadir J, Anwar Z. Quantum Computing for Healthcare: A Review. Future Internet. 2023; 15(3):94. https://doi.org/10.3390/fi15030094
Chicago/Turabian StyleUr Rasool, Raihan, Hafiz Farooq Ahmad, Wajid Rafique, Adnan Qayyum, Junaid Qadir, and Zahid Anwar. 2023. "Quantum Computing for Healthcare: A Review" Future Internet 15, no. 3: 94. https://doi.org/10.3390/fi15030094
APA StyleUr Rasool, R., Ahmad, H. F., Rafique, W., Qayyum, A., Qadir, J., & Anwar, Z. (2023). Quantum Computing for Healthcare: A Review. Future Internet, 15(3), 94. https://doi.org/10.3390/fi15030094








