Validating the Adoption of Heterogeneous Internet of Things with Blockchain
Abstract
1. Introduction
2. Related Works
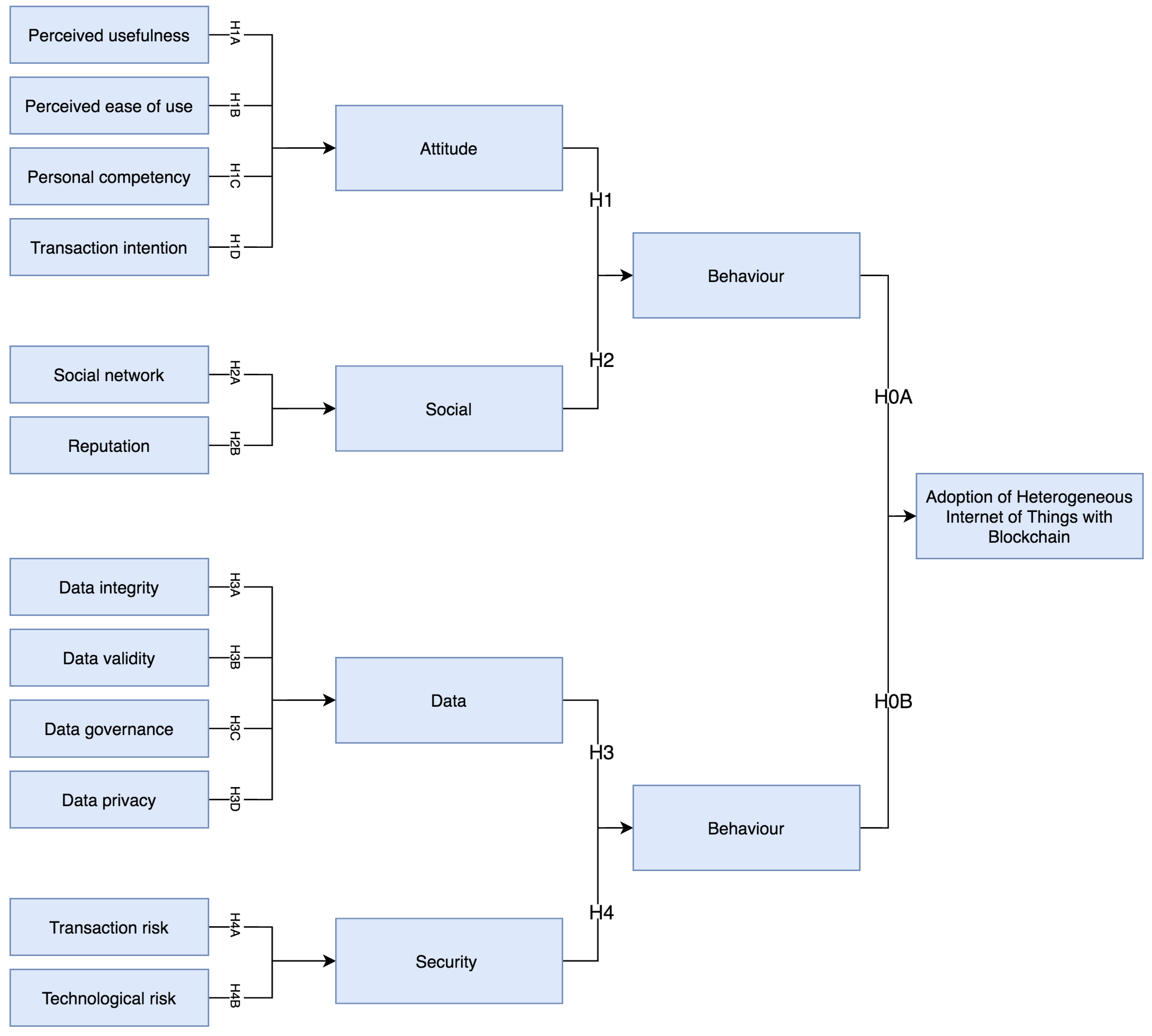
3. Conceptual Model and Research Hypotheses
3.1. Behaviour Factors
3.1.1. Attitude Related Factors
3.1.2. Social Related Factors
3.2. Trust Factors
3.2.1. Data Related Factors
3.2.2. Security Related Factors
4. Methodology
4.1. Data Collection and Measurement
4.2. Data Analysis and Results
4.3. Hypotheses Testing
5. Discussion
6. Conclusions
Author Contributions
Funding
Conflicts of Interest
References
- Panarello, A.; Tapas, N.; Merlino, G.; Longo, F.; Puliafito, A. Blockchain and iot integration: A systematic survey. Sensors 2018, 18, 2575. [Google Scholar] [CrossRef] [PubMed]
- Nakamoto, S. Bitcoin: A Peer-to-Peer Electronic Cash System; 2008. [Google Scholar]
- Casino, F.; Dasaklis, T.K.; Patsakis, C. A systematic literature review of blockchain-based applications: Current status, classification and open issues. Telemat. Inform. 2018, 36, 55–81. [Google Scholar] [CrossRef]
- Zheng, Z.; Xie, S.; Dai, H.N.; Chen, X.; Wang, H. Blockchain challenges and opportunities: A survey. Int. J. Web Grid Serv. 2018, 14, 352–375. [Google Scholar] [CrossRef]
- Makhdoom, I.; Abolhasan, M.; Abbas, H.; Ni, W. Blockchain’s adoption in IoT: The challenges, and a way forward. J. Netw. Comput. Appl. 2018, 125, 251–279. [Google Scholar] [CrossRef]
- Viriyasitavat, W.; Anuphaptrirong, T.; Hoonsopon, D. When blockchain meets internet of things: Characteristics, challenges, and business opportunities. J. Ind. Inf. Integr. 2019, 15, 21–28. [Google Scholar] [CrossRef]
- Wang, X.; Zha, X.; Ni, W.; Liu, R.P.; Guo, Y.J.; Niu, X.; Zheng, K. Survey on blockchain for Internet of Things. Comput. Commun. 2019, 136, 10–29. [Google Scholar] [CrossRef]
- Feng, Q.; He, D.; Zeadally, S.; Khan, M.K.; Kumar, N. A survey on privacy protection in blockchain system. J. Netw. Comput. Appl. 2018, 126, 45–58. [Google Scholar] [CrossRef]
- Adelmann, R.; Langheinrich, M.; Floerkemeier, C. Toolkit for bar code recognition and resolving on camera phones-jump starting the internet of things. In INFORMATIK 2006—Informatik für Menschen—Band 2, Beiträge der 36. Jahrestagung der Gesellschaft für Informatik eV (GI); Gesellschaft für Informatik eV: Bonn, Germany, 2006. [Google Scholar]
- Dachyar, M.; Zagloel, T.Y.M.; Saragih, L.R. Knowledge growth and development: Internet of things (IoT) research, 2006–2018. Heliyon 2019, 5, e02264. [Google Scholar] [CrossRef]
- Balasubramanian, V.; Zaman, F.; Aloqaily, M.; Al Ridhawi, I.; Jararweh, Y.; Salameh, H.B. A mobility management architecture for seamless delivery of 5G-IoT services. In Proceedings of the ICC 2019—2019 IEEE International Conference on Communications (ICC), Shanghai, China, 20–24 May 2019; pp. 1–7. [Google Scholar]
- AlHogail, A. Improving IoT technology adoption through improving consumer trust. Technologies 2018, 6, 64. [Google Scholar] [CrossRef]
- Negka, L.; Gketsios, G.; Anagnostopoulos, N.A.; Spathoulas, G.; Kakarountas, A.; Katzenbeisser, S. Employing Blockchain and Physical Unclonable Functions for Counterfeit IOT Devices Detection. In Proceedings of the International Conference on Omni-Layer Intelligent Systems, Crete, Greece, 5–7 May 2019; pp. 172–178. [Google Scholar]
- Rejeb, A.; Keogh, J.G.; Treiblmaier, H. Leveraging the Internet of Things and Blockchain Technology in Supply Chain Management. Future Internet 2019, 11, 161. [Google Scholar] [CrossRef]
- Mendki, P. Blockchain Enabled IoT Edge Computing. In Proceedings of the 2019 International Conference on Blockchain Technology (ICBCT 2019), San Diego, CA, USA, 25–30 June 2019; ACM: New York, NY, USA, 2019; pp. 66–69. [Google Scholar] [CrossRef]
- Spathoulas, G.; Giachoudis, N.; Damiris, G.P.; Theodoridis, G. Collaborative Blockchain-Based Detection of Distributed Denial of Service Attacks Based on Internet of Things Botnets. Futur. Internet 2019, 11, 226. [Google Scholar] [CrossRef]
- Tseng, L.; Wong, L.; Otoum, S.; Aloqaily, M.; Othman, J.B. Blockchain for managing heterogeneous internet of things: A perspective architecture. IEEE Netw. 2020, 34, 16–23. [Google Scholar] [CrossRef]
- Aloqaily, M.; Boukerche, A.; Bouachir, O.; Khalid, F.; Jangsher, S. An Energy Trade Framework Using Smart Contracts: Overview and Challenges. IEEE Netw. 2020. [Google Scholar] [CrossRef]
- Morkunas, V.J.; Paschen, J.; Boon, E. How blockchain technologies impact your business model. Bus. Horiz. 2019, 62, 295–306. [Google Scholar] [CrossRef]
- Zhang, S.; Lee, J.H. Analysis of the main consensus protocols of blockchain. ICT Express 2019, 6, 93–97. [Google Scholar] [CrossRef]
- Davis, F.D. Perceived usefulness, perceived ease of use, and user acceptance of information technology. MIS Q. 1989, 13, 319–340. [Google Scholar] [CrossRef]
- Fishbein, M.; Ajzen, I. Belief, Attitude, Intention, and Behavior Addison-Wesley; Wesley Publishing Co.: Reading, MA, USA, 1975. [Google Scholar]
- de Boer, P.S.; van Deursen, A.J.; Van Rompay, T.J. Accepting the Internet-of-Things in our homes: The role of user skills. Telemat. Inform. 2019, 36, 147–156. [Google Scholar] [CrossRef]
- Mital, M.; Chang, V.; Choudhary, P.; Papa, A.; Pani, A.K. Adoption of Internet of Things in India: A test of competing models using a structured equation modeling approach. Technol. Forecast. Soc. Chang. 2018, 136, 339–346. [Google Scholar] [CrossRef]
- Alanazi, M.; Soh, B. Behavioral Intention to Use IoT Technology in Healthcare Settings. Eng. Technol. Appl. Sci. Res. 2019, 9, 4769–4774. [Google Scholar]
- Jaoude, J.A.; Saade, R. Blockchain Factors for Consumer Acceptance. Int. J. Bus. Manag. Technol. 2017. [Google Scholar]
- Pokrovskaia, N.N.; Spivak, V.A.; Snisarenko, S.O. Developing Global Qualification-Competencies Ledger on Blockchain Platform. In Proceedings of the 2018 XVII Russian Scientific and Practical Conference on Planning and Teaching Engineering Staff for the Industrial and Economic Complex of the Region (PTES), St. Petersburg, Russia, 14–15 November 2018; pp. 209–212. [Google Scholar]
- Venkatesh, V.; Morris, M.G.; Davis, G.B.; Davis, F.D. User acceptance of information technology: Toward a unified view. MIS Q. 2003, 27, 425–478. [Google Scholar] [CrossRef]
- Folkinshteyn, D.; Lennon, M. Braving Bitcoin: A technology acceptance model (TAM) analysis. J. Inf. Technol. Case Appl. Res. 2016, 18, 220–249. [Google Scholar] [CrossRef]
- Knauer, F.; Mann, A. What is in It for Me? Identifying Drivers of Blockchain Acceptance among German Consumers. J. Br. Blockchain Assoc. 2019, 3, 10484. [Google Scholar] [CrossRef]
- Dong, X.; Chang, Y.; Wang, Y.; Yan, J. Understanding usage of Internet of Things (IOT) systems in China. Inf. Technol. People 2017, 30, 117–138. [Google Scholar] [CrossRef]
- Jaafreh, A. The Effect Factors in the Adoption of Internet of Things (IoT) Technology in the SME in KSA: An Empirical Study’. IRMBR Int. Rev. Manag. Bus. Res. 2018, 7, 135–148. [Google Scholar] [CrossRef][Green Version]
- Goleman, D. Emotional Intelligence; Bantam Books: New York, NY, USA, 2006. [Google Scholar]
- Gronau, N.; Ullrich, A.; Teichmann, M. Development of the industrial IoT competences in the areas of organization, process, and interaction based on the learning factory concept. Procedia Manuf. 2017, 9, 254–261. [Google Scholar] [CrossRef]
- Atzori, L.; Iera, A.; Morabito, G.; Nitti, M. The social internet of things (siot)—When social networks meet the internet of things: Concept, architecture and network characterization. Comput. Netw. 2012, 56, 3594–3608. [Google Scholar] [CrossRef]
- Guo, B.; Yu, Z.; Zhou, X.; Zhang, D. Opportunistic IoT: Exploring the social side of the internet of things. In Proceedings of the 2012 IEEE 16th International Conference on Computer Supported Cooperative Work in Design (CSCWD), Wuhan, China, 23–25 May 2012; pp. 925–929. [Google Scholar]
- Buccafurri, F.; Lax, G.; Nicolazzo, S.; Nocera, A. Overcoming limits of blockchain for IoT applications. In Proceedings of the 12th International Conference on Availability, Reliability and Security, Reggio Calabria, Italy, 29 August–1 September 2017; pp. 1–6. [Google Scholar]
- Xu, R.; Zhang, L.; Zhao, H.; Peng, Y. Design of network media’s digital rights management scheme based on blockchain technology. In Proceedings of the 2017 IEEE 13th International Symposium on Autonomous Decentralized System (ISADS), Bangkok, Thailand, 22–24 March 2017; pp. 128–133. [Google Scholar]
- Fu, D.; Fang, L. Blockchain-based trusted computing in social network. In Proceedings of the 2016 2nd IEEE International Conference on Computer and Communications (ICCC), Chengdu, China, 14–17 October 2016; pp. 19–22. [Google Scholar]
- Al-Saqaf, W.; Seidler, N. Blockchain technology for social impact: Opportunities and challenges ahead. J. Cyber. Policy 2017, 2, 338–354. [Google Scholar] [CrossRef]
- Ferrag, M.A.; Derdour, M.; Mukherjee, M.; Derhab, A.; Maglaras, L.; Janicke, H. Blockchain technologies for the internet of things: Research issues and challenges. IEEE Internet Things J. 2018, 6, 2188–2204. [Google Scholar] [CrossRef]
- Barger, V.; Peltier, J.W.; Schultz, D.E. Social media and consumer engagement: A review and research agenda. J. Res. Interact. Mark. 2016, 10, 268–287. [Google Scholar] [CrossRef]
- Salloum, S.A.; Mhamdi, C.; Al Kurdi, B.; Shaalan, K. Factors affecting the adoption and meaningful use of social media: A structural equation modeling approach. Int. J. Inf. Technol. Lang. Stud. 2018, 2, 96–109. [Google Scholar]
- Alsaleh, D.A.; Elliott, M.T.; Fu, F.Q.; Thakur, R. Cross-cultural differences in the adoption of social media. J. Res. Interact. Mark. 2019. [Google Scholar] [CrossRef]
- Javaid, A.; Zahid, M.; Ali, I.; Khan, R.J.U.H.; Noshad, Z.; Javaid, N. Reputation System for IoT Data Monetization Using Blockchain. In Proceedings of the International Conference on Broadband and Wireless Computing, Communication and Applications, Antwerp, Belgium, 7–9 November 2019; Springer: Cham, Switzerland, 2019; pp. 173–184. [Google Scholar]
- Zheng, Z.; Xie, S.; Dai, H.; Chen, X.; Wang, H. An overview of blockchain technology: Architecture, consensus, and future trends. In Proceedings of the 2017 IEEE International Congress on Big Data (BigData Congress), Honolulu, HI, USA, 25–30 June 2017; pp. 557–564. [Google Scholar]
- Liu, B.; Yu, X.L.; Chen, S.; Xu, X.; Zhu, L. Blockchain based data integrity service framework for IoT data. In Proceedings of the 2017 IEEE International Conference on Web Services (ICWS), Honolulu, HI, USA, 25–30 June 2017; pp. 468–475. [Google Scholar]
- Wei, P.; Wang, D.; Zhao, Y.; Tyagi, S.K.S.; Kumar, N. Blockchain data-based cloud data integrity protection mechanism. Future Gener. Comput. Syst. 2020, 102, 902–911. [Google Scholar] [CrossRef]
- Machado, C.; Fröhlich, A.A.M. Iot data integrity verification for cyber-physical systems using blockchain. In Proceedings of the 2018 IEEE 21st International Symposium on Real-Time Distributed Computing (ISORC), Singapore, 29–31 May 2018; pp. 83–90. [Google Scholar]
- Lu, Y. The blockchain: State-of-the-art and research challenges. J. Ind. Inf. Integr. 2019, 15, 80–90. [Google Scholar] [CrossRef]
- Wang, X.; Yu, G.; Zha, X.; Ni, W.; Liu, R.P.; Guo, Y.J.; Zheng, K.; Niu, X. Capacity of Blockchain based Internet-of-Things: Testbed and Analysis. Internet Things 2019, 8, 100109. [Google Scholar] [CrossRef]
- Dasgupta, A.; Gill, A.Q.; Hussain, F.K. A Conceptual Framework for Data Governance in IoT-enabled Digital IS Ecosystems. DATA 2019. [Google Scholar] [CrossRef]
- Sicari, S.; Rizzardi, A.; Cappiello, C.; Miorandi, D.; Coen-Porisini, A. Toward data governance in the internet of things. In New Advances in the Internet of Things; Springer: Cham, Switzerland, 2018; pp. 59–74. [Google Scholar]
- Zyskind, G.; Nathan, O. Decentralizing privacy: Using blockchain to protect personal data. In Proceedings of the 2015 IEEE Security and Privacy Workshops, San Jose, CA, USA, 21–22 May 2015; pp. 180–184. [Google Scholar]
- Liang, X.; Shetty, S.; Tosh, D.; Kamhoua, C.; Kwiat, K.; Njilla, L. Provchain: A blockchain-based data provenance architecture in cloud environment with enhanced privacy and availability. In Proceedings of the 17th IEEE/ACM International Symposium on Cluster, Cloud and Grid Computing, Madrid, Spain, 14–17 May 2017; pp. 468–477. [Google Scholar]
- Cha, S.C.; Chen, J.F.; Su, C.; Yeh, K.H. A blockchain connected gateway for BLE-based devices in the internet of things. IEEE Access 2018, 6, 24639–24649. [Google Scholar] [CrossRef]
- Park, C.; Kim, Y.; Jeong, M. Influencing factors on risk perception of IoT-based home energy management services. Telemat. Inform. 2018, 35, 235–2365. [Google Scholar] [CrossRef]
- Brous, P.; Janssen, M.; Herder, P. The dual effects of the Internet of Things (IoT): A systematic review of the benefits and risks of IoT adoption by organizations. Int. J. Inf. Manag. 2019. [Google Scholar] [CrossRef]
- Nikou, S. Factors driving the adoption of smart home technology: An empirical assessment. Telemat. Inform. 2019, 45, 101283. [Google Scholar] [CrossRef]
- Ahluwalia, S.; Mahto, R.V.; Guerrero, M. Blockchain technology and startup financing: A transaction cost economics perspective. Technol. Forecast. Soc. Chang. 2020, 151, 119854. [Google Scholar] [CrossRef]
- Schmidt, C.G.; Wagner, S.M. Blockchain and supply chain relations: A transaction cost theory perspective. J. Purch. Supply Manag. 2019, 25, 100552. [Google Scholar] [CrossRef]
- Roy, D.G.; Das, P.; De, D.; Buyya, R. QoS-aware secure transaction framework for internet of things using blockchain mechanism. J. Netw. Comput. Appl. 2019, 144, 59–78. [Google Scholar]
- Macaulay, T. Chapter 3—Requirements and Risk Management. In RIoT Control; Macaulay, T., Ed.; Morgan Kaufmann: Boston, MA, USA, 2017; pp. 57–79. [Google Scholar] [CrossRef]
- Wang, Q.; Zhu, X.; Ni, Y.; Gu, L.; Zhu, H. Blockchain for the IoT and industrial IoT: A review. Internet Things 2019, 100081. [Google Scholar] [CrossRef]
- Dillman, D. Mail and Internet Surveys: The Tailored Design Method; Wiley & Sons: New York, NY, USA, 2000. [Google Scholar]
- Likert, R. A technique for the measurement of attitudes. Arch. Psychol. 1932, 22, 140. [Google Scholar]
- Cavana, R.; Delahaye, B.; Sekeran, U. Applied Business Research: Qualitative and Quantitative Methods; John Wiley & Sons: Hoboken, NJ, USA, 2001. [Google Scholar]
- Alduais, N.; Abdullah, J.; Jamil, A.; Audah, L.; Alias, R. Sensor node data validation techniques for realtime IoT/WSN application. In Proceedings of the 2017 14th International Multi-Conference on Systems, Signals & Devices (SSD), Marrakech, Morocco, 28–31 March 2017; pp. 760–765. [Google Scholar]
| Dimension Hypotheses | Domain Hypotheses | Description of Survey Questions |
|---|---|---|
| H1 Attitude-related factors have a positive influence on behavior intention towards IoT technology adoption | H1A: Perceived usefulness has a positive effect on IoT blockchain technology adoption. | To measure the increase in the operating efficiency and system performance within the work environment. |
| H1B: Perceived ease of use has a positive effect on IoT blockchain technology adoption. | To measure the ease of apply IoT technology and its integration with other technologies. | |
| H1C: Personal competency has a significant effect on IoT blockchain technology adoption. | To measure the level of cognitive knowledge. | |
| H1D: Transaction intention has a significant positive effect on IoT blockchain technology adoption. | To measure the level of transparency and clarity. | |
| H2 Social influence related factors have a positive influence on behavior intention towards IoT | H2A: Social network has a positive effect on IoT blockchain technology adoption. | To study social impact through a secure network and open source. |
| H2B: Reputation has a significant positive effect of social on IoT blockchain technology adoption. | To measure the role of IoT blockchain technology in managing data and trusting it through distributed systems. | |
| H3 Data related factors have a positive influence on trust towards IoT | H3A: Data integrity has a positive effect on IoT blockchain technology adoption. | To study the effect of IoT blockchain technology on the data integrity that are consistent with the objective of the data creators. |
| H3B:Data validity has a positive influence on IoT blockchain technology adoption. | To study the level of IoT blockchain technology outputs in correctly and reasonably. | |
| H3C: Data governance has a significant effect on IoT blockchain technology adoption. | To measure the contributions of IoT blockchain technology to ensuring the preservation, protection and control of data by the authorized persons. | |
| H3D: Data privacy has a positive influence on IoT blockchain technology adoption. | To measure the extent of IoT blockchain technology in ensuring the privacy and confidentiality of data. | |
| H4 Security related factors have a positive influence on trust towards IoT | H4A: Transaction risk has a positive impact on the intention to use blockchain technology in IoT. | To measure the operations executed through IoT blockchain technology led to reduce the risk percentage. |
| H4B: Technology risk positively affects the intention to use blockchain technology in IoT. | To measure IoT technology led to reduces the risk of thirdparty service failures. |
| SI.No | Item/Construct | No. of Items | Mean | Standard Deviation | Cronbach’s Alpha Value |
|---|---|---|---|---|---|
| 1 | Perceived Usefulness | 2 | 4.35 | 0.68211 | 0.898 |
| 2 | Perceived Ease of Use | 2 | 3.98 | 0.87286 | 0.9 |
| 3 | Personal Competency | 2 | 3.57 | 1.05105 | 0.91 |
| 4 | Transaction Intention | 2 | 4.23 | 0.66655 | 0.896 |
| 5 | Social Network | 3 | 4.13 | 0.63175 | 0.898 |
| 6 | Reputation | 3 | 3.98 | 0.73201 | 0.897 |
| 7 | Data Integrity | 2 | 4.3 | 0.64556 | 0.903 |
| 8 | Data Validity | 2 | 4.25 | 0.57621 | 0.899 |
| 9 | Data Governance | 2 | 4.27 | 0.68488 | 0.896 |
| 10 | Data Privacy | 2 | 4.23 | 0.75849 | 0.894 |
| 11 | Transaction Risk | 2 | 4.12 | 0.74804 | 0.9 |
| 12 | Technology Risk | 2 | 3.93 | 0.78164 | 0.9 |
| PU | PEoU | PC | TI | SN | RE | DI | DV | DG | DP | TRR | TER | ||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| PU | Pearson Correlation | 1 | |||||||||||
| Sig. (2- tailed) | |||||||||||||
| PEoU | Pearson Correlation | 0.592 | 1 | ||||||||||
| Sig. (2- tailed) | 0.000 | ||||||||||||
| PC | Pearson Correlation | 0.330 | 0.509 | 1 | |||||||||
| Sig. (2- tailed) | 0.004 | 0.000 | |||||||||||
| TI | Pearson Correlation | 0.652 | 0.560 | 0.390 | 1 | ||||||||
| Sig. (2- tailed) | 0.000 | 0.000 | 0.000 | ||||||||||
| SN | Pearson Correlation | 0.486 | 0.380 | 0.212 | 0.549 | 1 | |||||||
| Sig. (2- tailed) | 0.000 | 0.000 | 0.057 | 0.000 | |||||||||
| RE | Pearson Correlation | 0.550 | 0.554 | 0.410 | 0.491 | 0.515 | 1 | ||||||
| Sig. (2- tailed) | 0.000 | 0.000 | 0.000 | 0.000 | 0.000 | ||||||||
| DI | Pearson Correlation | 0.401 | 0.219 | 0.186 | 0.414 | 0.550 | 0.487 | 1 | |||||
| Sig. (2- tailed) | 0.000 | 0.050 | 0.097 | 0.000 | 0.000 | 0.000 | |||||||
| DV | Pearson Correlation | 0.436 | 0.373 | 0.349 | 0.547 | 0.545 | 0.504 | 0.771 | 1 | ||||
| Sig. (2- tailed) | 0.000 | 0.001 | 0.001 | 0.000 | 0.000 | 0.000 | 0.000 | ||||||
| DG | Pearson Correlation | 0.582 | 0.414 | 0.439 | 0.550 | 0.590 | 0.582 | 0.561 | 0.588 | 1 | |||
| Sig. (2- tailed) | 0.000 | 0.000 | 0.000 | 0.000 | 0.000 | 0.000 | 0.000 | 0.000 | |||||
| DP | Pearson Correlation | 0.513 | 0.523 | 0.506 | 0.604 | 0.428 | 0.483 | 0.336 | 0.484 | 0.535 | 1 | ||
| Sig. (2- tailed) | 0.000 | 0.000 | 0.000 | 0.000 | 0.000 | 0.000 | 0.002 | 0.000 | 0.000 | ||||
| TRR | Pearson Correlation | 0.441 | 0.402 | 0.327 | 0.555 | 0.477 | 0.487 | 0.336 | 0.356 | 0.434 | 0.616 | 1 | |
| Sig. (2- tailed) | 0.000 | 0.000 | 0.003 | 0.000 | 0.000 | 0.000 | 0.002 | 0.001 | 0.000 | 0.000 | |||
| TER | Pearson Correlation | 0.333 | 0.387 | 0.455 | 0.367 | 0.664 | 0.395 | 0.369 | 0.426 | 0.426 | 0.633 | 0.469 | 1 |
| Sig. (2- tailed) | 0.002 | 0.000 | 0.000 | 0.001 | 0.000 | 0.000 | 0.001 | 0.000 | 0.000 | 0.000 | 0.000 |
| Path Relationship | Pathcoefficient Standardized Coefficients () | p-Value | t-Value | Hypothesis Validation | |
|---|---|---|---|---|---|
| H1: Attitude—Behavior Intention | 0.832 | 0 | 24.864 | 0.885 | Supported |
| H1A: Perceived Usefulness—Attitude | 0.728 | 0.005 | 10.648 | 0.581 | Supported |
| H1B: Perceived Ease of Use—Attitude | 0.626 | 0 | 14.149 | 0.711 | Supported |
| H1C: Personal Competency—Attitude | 0.47 | 0 | 10.687 | 0.588 | Supported |
| H1D: Transaction Intention—Attitude | 0.754 | 0.005 | 11.059 | 0.605 | Supported |
| H2: Social—Behavior Intention | 0.828 | 0.002 | 15.602 | 0.755 | Supported |
| H2A: Social Network—Social | 0.799 | 0 | 14.295 | 0.721 | Supported |
| H2B: Reputation—Social | 0.722 | 0.002 | 17.362 | 0.792 | Supported |
| H3: Data—Trust | 0.94 | 0 | 26.357 | 0.898 | Supported |
| H3A: Data Integrity—Data | 0.627 | 0 | 9.964 | 0.557 | Supported |
| H3B: Data Validity—Data | 0.762 | 0 | 12.237 | 0.655 | Supported |
| H3C: Data Governance—Data | 0.676 | 0 | 14.513 | 0.727 | Supported |
| H3D: Data Privacy—Data | 0.568 | 0 | 11.593 | 0.63 | Supported |
| H4: Security—Trust | 0.728 | 0 | 17.013 | 0.786 | Supported |
| H4A: Transaction Risk—Security | 0.745 | 0 | 14.347 | 0.723 | Supported |
| H4B: Technology Risk—Security | 0.724 | 0 | 15.232 | 0.746 | Supported |
| H0A: Behavior Intention—Adopting Blockchain in IoT | 0.904 | 0 | 34.336 | 0.936 | Supported |
| H0B: Trust—Adopting Blockchain in IoT | 0.923 | 0 | 24.331 | 0.882 | Supported |
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
AlSuwaidan, L.; Almegren, N. Validating the Adoption of Heterogeneous Internet of Things with Blockchain. Future Internet 2020, 12, 107. https://doi.org/10.3390/fi12060107
AlSuwaidan L, Almegren N. Validating the Adoption of Heterogeneous Internet of Things with Blockchain. Future Internet. 2020; 12(6):107. https://doi.org/10.3390/fi12060107
Chicago/Turabian StyleAlSuwaidan, Lulwah, and Nuha Almegren. 2020. "Validating the Adoption of Heterogeneous Internet of Things with Blockchain" Future Internet 12, no. 6: 107. https://doi.org/10.3390/fi12060107
APA StyleAlSuwaidan, L., & Almegren, N. (2020). Validating the Adoption of Heterogeneous Internet of Things with Blockchain. Future Internet, 12(6), 107. https://doi.org/10.3390/fi12060107





