Digital Cloud Environment: Present Challenges and Future Forecast
Abstract
1. Introduction
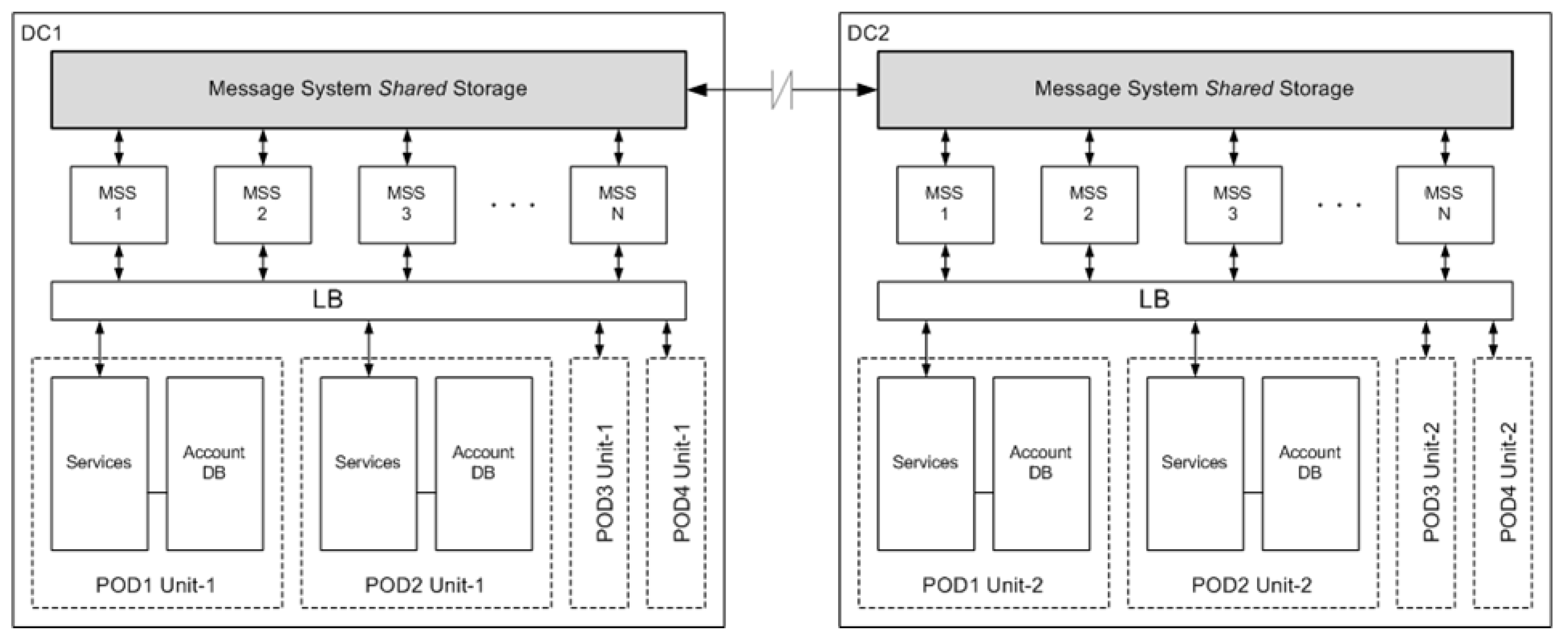
- A cloud service is now an integration of multiple platforms and applications of the internet of things (IoT) [1].
- The well-known problems of big data, including storing client accounts in a database, protocoling user activity in the logs, transferring real time dataflow, and processing big data analytics [2].
- A fast growing and, therefore, unpredictable user workload [3].
- The implementation of mobile applications leads to human activity spikes, not only in peak daytime but also in the late evenings and early mornings.
- Initially developed in the USA, many International IT companies go global for provisioning GCC services in all regions and time zones worldwide.
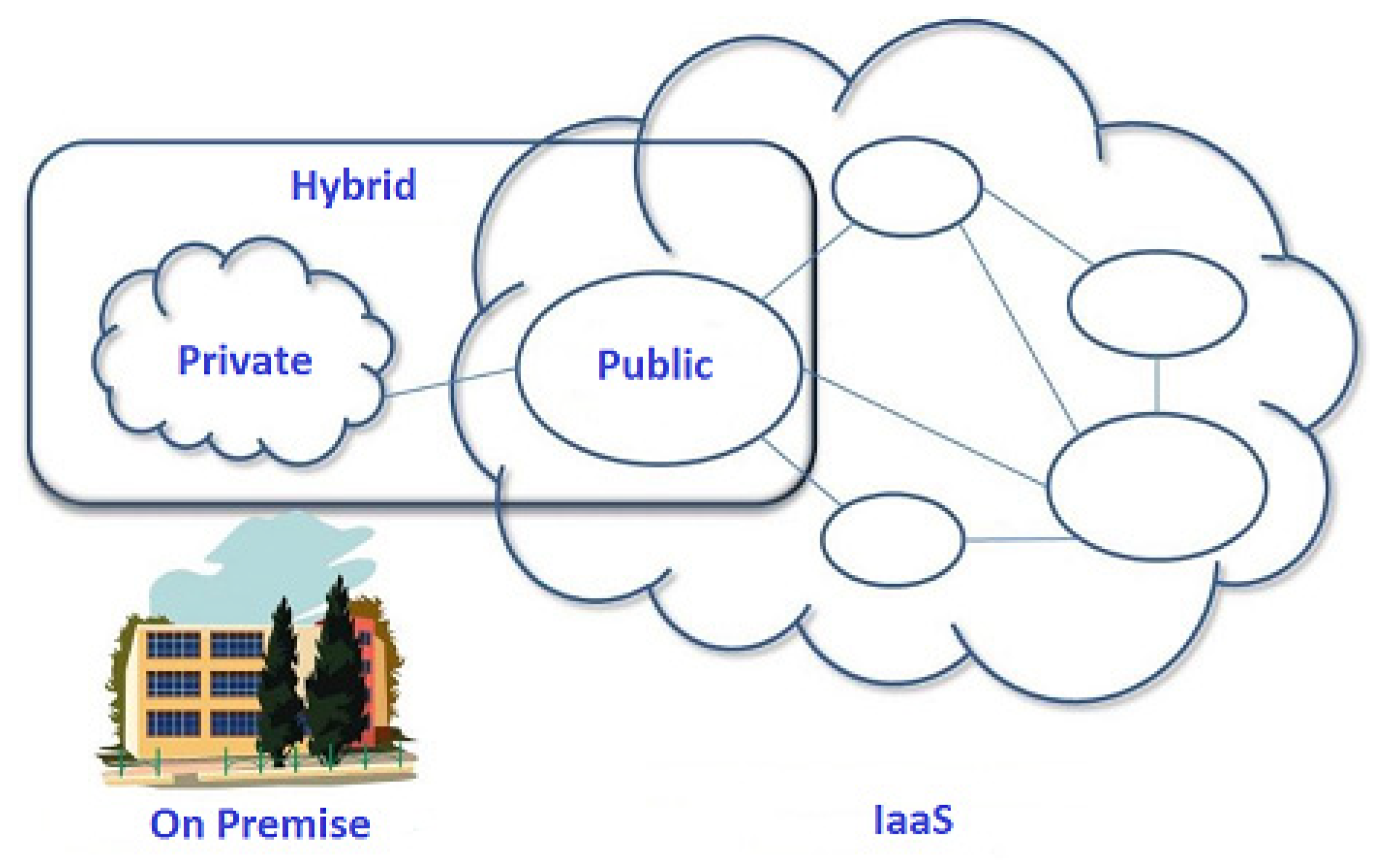
- The virtualization of the digital environment and migration from private to public cloud services, such as software as a service (SaaS), platform as a service (PaaS), infrastructure as a service (IaaS), load balancer as a Service (LBaaS), database as a service (DBaaS), etc.
- Increasing cyber security problems and new sources of threats when moving from private to public clouds.
- State government standards, banking rules, and other local regional limitations.
- Existing monitoring solutions [7] provide only built-in system metrics like memory, CPU, disk space, or network throughput, but not specific business items like HTTP requests per second, the number of actively logged-in users, server connections, calls count, and others.
2. Related Works
- Confidentiality (C) of sensitive information
- Integrity (I) of the database (DB) information
- Availability (A) of cloud service Data (D)
- Availability of a Virtual (V) server as a whole
3. Basic GCC Architecture Models and Cyber Security Issues
- Significant decrease of IT expenses for maintaining DCs on premises
- Minimize the IT department to support end users
- Low level of IT personnel skills required
- Flexible scalability of cloud computing resources and capacity planning
- Support IT services related to backups, disaster recovery, etc.
4. Public Cloud Computing Resources
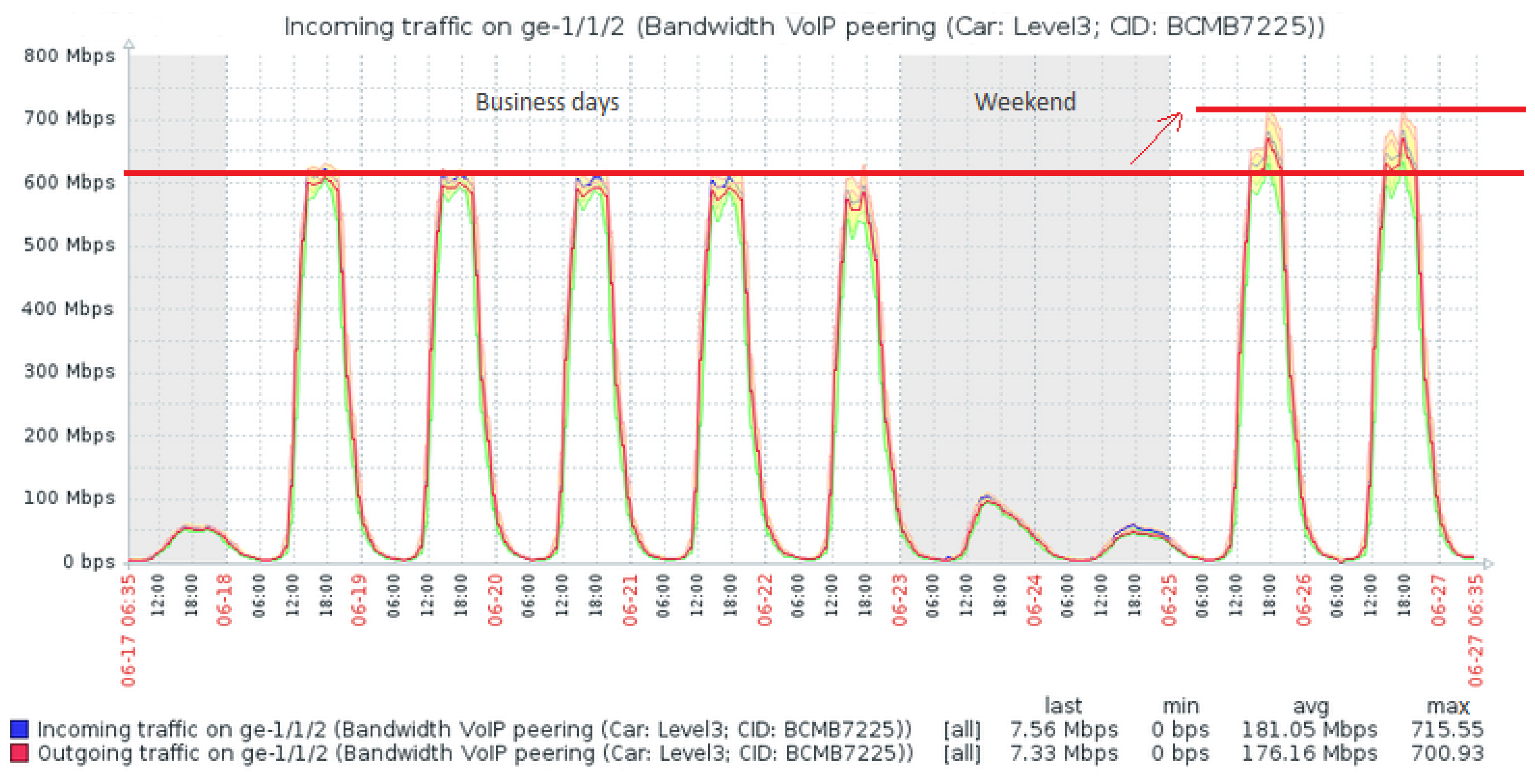
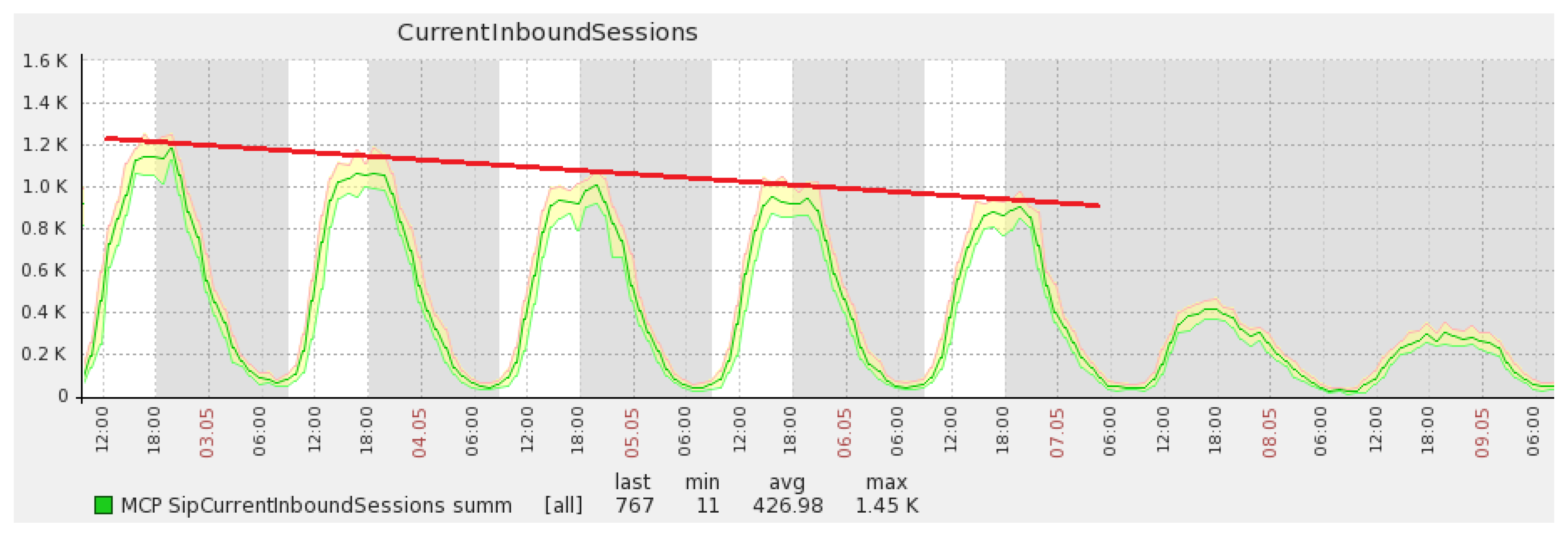
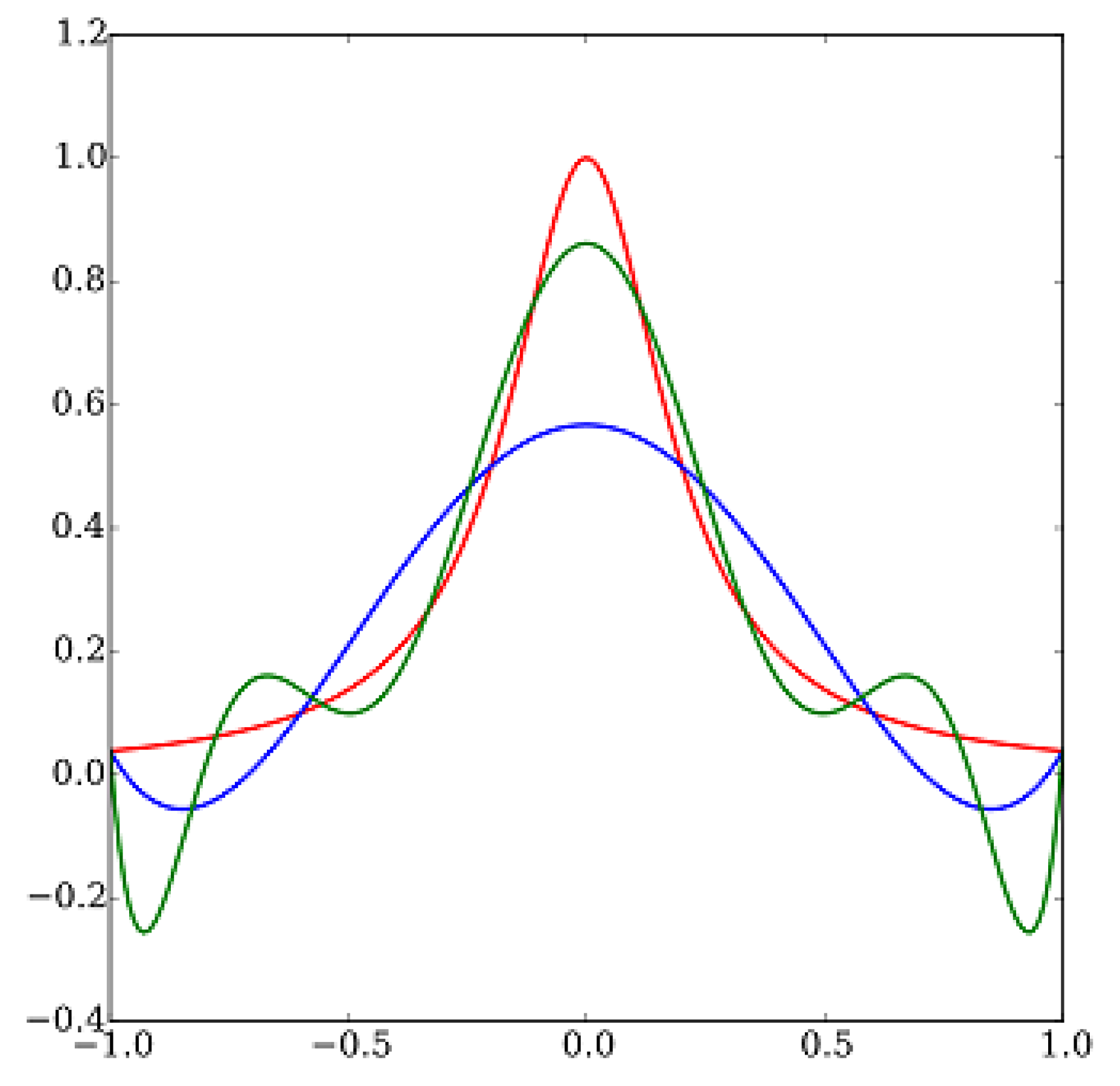
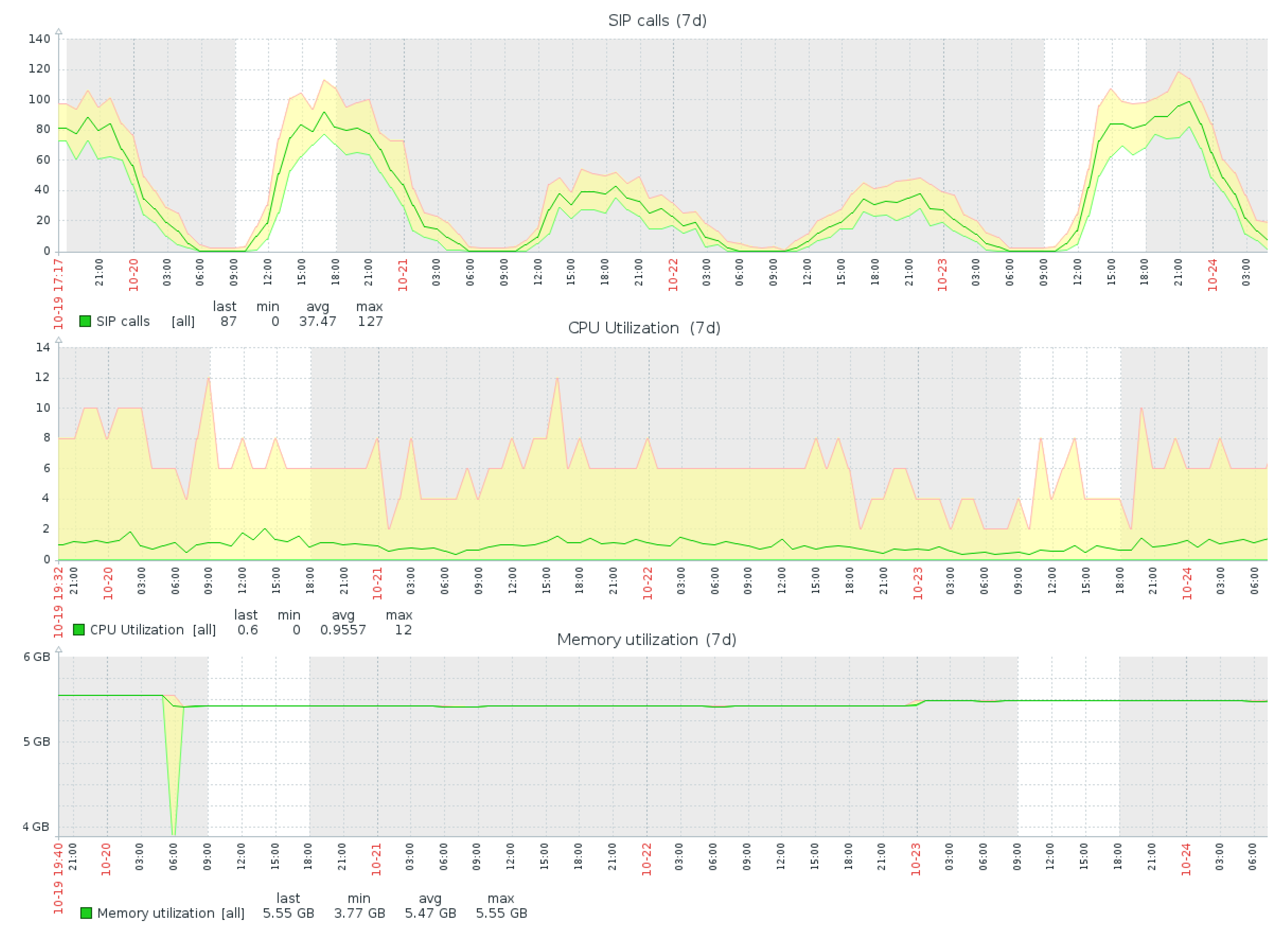
5. Monitoring System and Prediction Models
- Open-source code, allowing customization and implementation of new data models (prediction models in our case).
- Enterprise-class product, supporting the server pool of up to 15,000 remote hosts with a total rate of 500 monitoring values per second.
- Free software to install from scratch and free for annual upgrades without affecting the customized code.
- Built-in templates with system metrics like CPU, RAM, disk I/O, etc., allowing monitoring of new hosts in “one click”.
- Enhanced reporting web user interface with graphs and analysis tools.
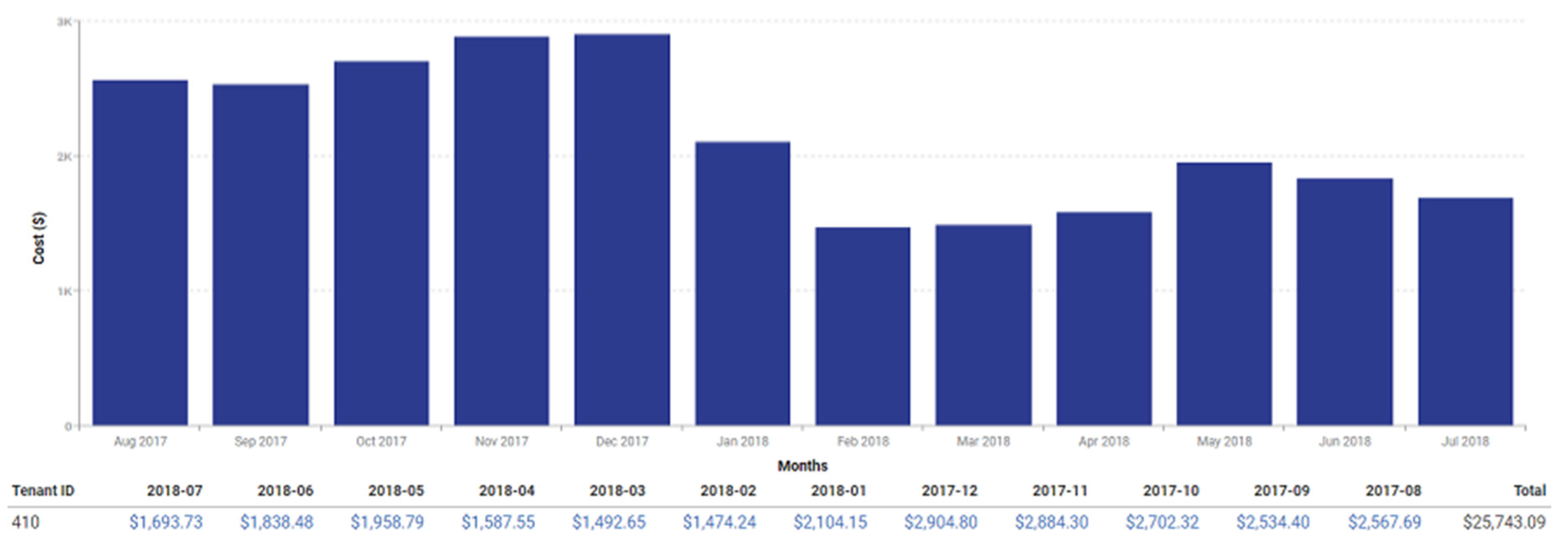
6. Implementation and Experimental Results
7. Conclusions
Supplementary Materials
Author Contributions
Funding
Acknowledgments
Conflicts of Interest
References
- Mescheryakov, S.; Shchemelinin, D. Deployment and Monitoring of Internet Multiservice System in the Cloud; Monograph. Scientific and Practical Edition; LAP Lambert Academic Publishing: Saarbrücken, Germany, 2018; 101p, ISBN 978-613-9-96321-8. Available online: https://www.lap-publishing.com/catalog/details/store/fr/book/978-613-9-96321-8/deployment-and-monitoring-of-internet-multiservice-system-in-the-cloud?search=mescheryakov (accessed on 12 March 2020).
- Rudenko, A.O.; Mescheryakov, S.V.; Shchemelinin, D.A. ASE International Conferences on Big Data Science and Computing. St. Petersb. State Polytech. Univ. J. 2015, 1, 110–119. [Google Scholar] [CrossRef]
- Efimov, V.; Mescheryakov, S.; Shchemelinin, D. Adaptive Control of Cloud Computing Resources in the Internet Telecommunication Multiservice System. In Proceedings of the 6th International Congress on Ultra Modern Telecommunications and Control Systems (ICUMT), St. Petersburg, Russia, 6–8 October 2014; pp. 387–393, ISBN 978-1-4799-5291-5. Available online: https://ieeexplore.ieee.org/document/7002117?arnumber=7002117 (accessed on 12 March 2020). [CrossRef]
- Efimov, V.V.; Mescheryakov, S.V.; Shchemelinin, D.A.; Yakovlev, K.A. Integration and Continuous Service Delivery in Globally Distributed Computing System. Hum. Sci. Univ. J. 2017, 30, 13–20. [Google Scholar]
- Efimov, V.; Mescheryakov, S.; Shchemelinin, D. Integration Data Model for Continuous Service Delivery in Cloud Computing System. In Communications in Computer and Information Science; Springer International Publishing: Basel, Switzerland, 2017; Volume 700, pp. 87–97. ISBN 978-3-319-66836-9. Available online: https://www.springer.com/gp/book/9783319668352 (accessed on 12 March 2020). [CrossRef]
- Ardulov, Y.; Mescheryakov, S.; Shchemelinin, D. Dynamic Load Balancing and Continuous Service Delivery in a Big Cloud Infrastructure. In Proceedings of the 42nd International IT Conference by Computer Measurement Group (CMG), La Jolla, CA, USA, 7–10 November 2016; Available online: https://www.cmg.org/publications/conference-proceedings/conference-proceedings2016/ (accessed on 11 November 2016).
- Mescheryakov, S.V.; Shchemelinin, D.A. Analytical Overview of Zabbix International Conference 2013. St. Petersb. State Polytech. Univ. J. 2014, 1, 91–98. [Google Scholar]
- Buinevich, M.; Izrailov, K.; Vladyko, A. Metric of vulnerability at the base of the life cycle of software representations. In Proceedings of the 20th International Conference on Advanced Communication Technology (ICACT), Chuncheon, Korea, 11–14 February 2018; ISBN 979-11-88428-01-4. [Google Scholar] [CrossRef]
- Buinevich, M.; Vladyko, A. Forecasting Issues of Wireless Communication Networks’ Cyber Resilience for an Intelligent Transportation System: An Overview of Cyber Attacks. Information 2019, 10, 27. [Google Scholar] [CrossRef]
- Buinevich, M.; Izrailov, K.; Stolyarova, E.; Vladyko, A. Combine method of forecasting VANET cybersecurity for application of high priority way. In Proceedings of the 20th International Conference on Advanced Communication Technology (ICACT), Chuncheon, Korea, 11–14 February 2018; pp. 266–271, ISBN 979-11-88428-01-4. [Google Scholar] [CrossRef]
- Kalaiprasath, R.; Elankavi, R.; Udayakumar, R. Cloud Security and Compliance—A Semantic Approach in End-to-End Security. Int. J. Smart Sens. Intell. Syst. 2017, 10, 482–494. [Google Scholar] [CrossRef]
- Suthar, F.; Khanna, S.; Patel, J. A Survey on Cloud Security Issues. Int. J. Comput. Sci. Eng. 2019, 7, 120–123. [Google Scholar] [CrossRef]
- Wu, J.; Feng, Y.; Sun, P. Sensor Fusion for Recognition of Activities of Daily Living. Sensors 2018, 18, 4029. [Google Scholar] [CrossRef] [PubMed]
- Mescheryakov, S.; Shchemelinin, D. Capacity Management of Java Based Business Applications Running on Virtualized Environment. In Proceedings of the 39th International IT Capacity and Performance Conference by Computer Measurement Group (CMG), La Jolla, CA, USA, 4–8 November 2013; Available online: http://www.cmg.org/publications/conference-proceedings/conference-proceedings-2013/ (accessed on 7 November 2013).
- Ardulov, Y.; Mescheryakov, S.; Shchemelinin, D. Monitoring and Remediation of Cloud Services Based on 4R Approach. In Proceedings of the 41st International IT Capacity and Performance Conference by Computer Measurement Group (CMG), San Antonio, TX, USA, 2–5 November 2015; Available online: http://www.cmg.org/publications/conference-proceedings/conference-proceedings2015/ (accessed on 5 November 2015).
- Genesys Telecommunications Laboratories. Available online: https://www.genesys.com/ (accessed on 12 March 2020).
- RingCentral International Telecommunications Company. Available online: https://www.ringcentral.com/whyringcentral/company.html (accessed on 12 March 2020).
- Bortyakov, D.E.; Mescheryakov, S.V.; Shchemelinin, D.A. Integrated Management of Big Data Traffic Systems in Distributed Production Environments. St. Petersb. State Polytech. Univ. J. 2014, 1, 105–113. [Google Scholar]
- Stamford, C. Gartner Says by 2020 “Cloud Shift” Will Affect More Than $1 Trillion in IT Spending. Gartner Analytic Report. 2016. Available online: https://www.gartner.com/newsroom/id/3384720 (accessed on 20 November 2018).
- Microsoft Research Blog. Personal communication. 2020. Available online: https://www.microsoft.com/en-us/research/blog/category/case-studies/ (accessed on 12 March 2020).
- Harvey, C. Comparing the Top 10 Private Cloud Providers. Datamation. 2017. Available online: https://www.datamation.com/cloud-computing/private-cloud-providers.html (accessed on 27 April 2017).
- AWS Instance Details and Prices. Available online: https://aws.amazon.com/ec2/previous-generation/ (accessed on 12 March 2020).
- Zabbix Enterprise-Class Monitoring System. Available online: https://www.zabbix.com/ (accessed on 12 March 2020).
- Kucherova, K.N.; Mescheryakov, S.V.; Shchemelinin, D.A. Using Predictive Monitoring Models in Cloud Computing Systems. In Communications in Computer and Information Science; Springer International Publishing: Basel, Switzerland, 2018; Volume 919, pp. 1–12. ISBN 978-3-319-99447-5. Available online: https://www.springer.com/gp/book/9783319994468 (accessed on 12 March 2020). [CrossRef]
- Kucherova, K.; Mescheryakov, S.; Shchemelinin, D. Cloud Monitoring—Focusing on Forecasting. In Proceedings of the 42nd International IT Conference by Computer Measurement Group (CMG), La Jolla, CA, USA, 7–10 November 2016; Available online: https://www.cmg.org/publications/conference-proceedings/conference-proceedings2016/ (accessed on 11 November 2016).
- Runge’s Phenomenon, Wikipedia. Available online: https://en.wikipedia.org/wiki/Runge’s_phenomenon (accessed on 12 March 2020).

| World Market, $ billion | 2016 | 2017 | 2018 | 2019 | 2020 |
|---|---|---|---|---|---|
| Software as a Service (SaaS) | 38.57 | 46.33 | 55.14 | 64.87 | 75.73 |
| Platform as a Service (PaaS) | 7.17 | 8.85 | 10.62 | 12.58 | 14.8 |
| Infrastructure as a Service (IaaS) | 25.29 | 34.6 | 45.56 | 57.9 | 71.55 |
| Load Balancer as a Service (LBaaS) | 90.26 | 104.52 | 118.52 | 133.57 | 151.1 |
| Database as a Service (DBaaS) | 40.81 | 43.77 | 47.56 | 51.65 | 56.18 |
| IT Security | 7.15 | 8.77 | 10.43 | 12.16 | 14 |
| Total | 209.24 | 246.84 | 287.82 | 332.72 | 383.36 |
| Risk | Risk Management |
|---|---|
| External fraud | Review the company’s security policy and protect the data |
| Access issues | Monitor health check to ensure the cloud service is stable |
| Internal fraud | Ask external cloud provider to track and log the user’s activities |
| Vendor failure | Need alternative cloud vendor in case of a primary outage |
| Cloud outage | Need backup network channel in case of a primary failure |
| VM Instance | Virtual CPUs | Memory, GB | Storage Performance | VM Bandwidth, Mbps | Network Performance |
|---|---|---|---|---|---|
| m4.large | 2 | 8 | Optimized | 450 | Moderate |
| m4.xlarge | 4 | 16 | Optimized | 750 | High |
| m4.2xlarge | 8 | 32 | Optimized | 1000 | High |
| m4.4xlarge | 16 | 64 | Optimized | 2000 | High |
| m4.10xlarge | 40 | 160 | Optimized | 4000 | 10 Gigabit |
| m4.16xlarge | 64 | 256 | Optimized | 10,000 | 25 Gigabit |
| VM Instance | Virtual CPUs | Memory, GB | Storage Performance | Storage Volume, GB | Price per Hour for OS Linux |
|---|---|---|---|---|---|
| m4.large | 2 | 8 | Optimized | 1 x 4 SSD | $0.1 |
| m4.xlarge | 4 | 16 | Optimized | 1 x 8 SSD | $0.2 |
| m4.2xlarge | 8 | 32 | Optimized | 1 x 16 SSD | $0.4 |
| m4.4xlarge | 16 | 64 | Optimized | 1 x 32 SSD | $0.8 |
| m4.10xlarge | 40 | 160 | Optimized | 2 x 40 SSD | $2.0 |
| m4.16xlarge | 64 | 256 | Optimized | 2 x 80 SSD | $3.2 |
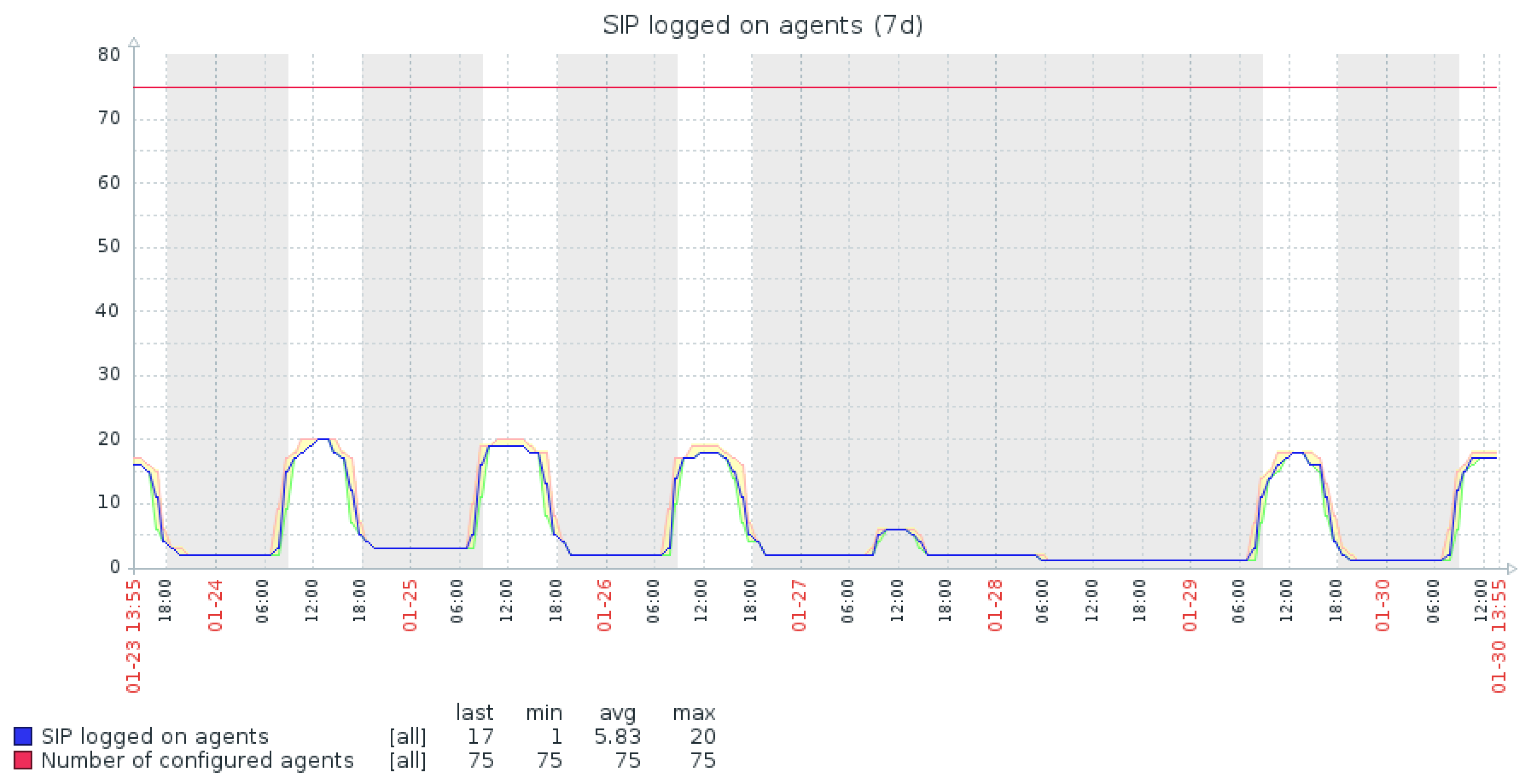
| AWS Region/VM | # of Configured Agents | Max # of Logged on Agents | Max/avg CPU Usage per Core, % | Max Memory Usage, % | AWS Instance Type | Recommended AWS Type | Price Savings, $ per Year |
|---|---|---|---|---|---|---|---|
| euw1/vmp-400 | 75 | 20 | 87/25 | 40 | m3.large | m3.medium | $3504 |
| euw2/vmp-400 | 75 | 0 | 0/0 | 0 | m3.large | m3.medium | $3504 |
| use1/vmp-220 | 414 | 121 | 95/25 | 50 | m3.large | m3.medium | $3504 |
| euw1/vmp-080 | 1854 | 610 | 95/50 | 50 | m3.xlarge | m4.large | $3504 |
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Mescheryakov, S.; Shchemelinin, D.; Izrailov, K.; Pokussov, V. Digital Cloud Environment: Present Challenges and Future Forecast. Future Internet 2020, 12, 82. https://doi.org/10.3390/fi12050082
Mescheryakov S, Shchemelinin D, Izrailov K, Pokussov V. Digital Cloud Environment: Present Challenges and Future Forecast. Future Internet. 2020; 12(5):82. https://doi.org/10.3390/fi12050082
Chicago/Turabian StyleMescheryakov, Serg, Dmitry Shchemelinin, Konstantin Izrailov, and Victor Pokussov. 2020. "Digital Cloud Environment: Present Challenges and Future Forecast" Future Internet 12, no. 5: 82. https://doi.org/10.3390/fi12050082
APA StyleMescheryakov, S., Shchemelinin, D., Izrailov, K., & Pokussov, V. (2020). Digital Cloud Environment: Present Challenges and Future Forecast. Future Internet, 12(5), 82. https://doi.org/10.3390/fi12050082





