Enhancing the 3GPP V2X Architecture with Information-Centric Networking
Abstract
:1. Introduction
- We advocate NDN as a feasible network-layer option to be included within the purpose-built C-V2X architecture specified by the 3GPP. NDN can: (i) work alongside the legacy IP; and/or (ii) complement other non-IP based solutions conceived so far for V2X safety data delivery.
- We propose a set of design changes and enhancements to the 3GPP C-V2X architecture to fully enable NDN among the other non-IP networking solutions already supported. Such changes mainly encompass new functionalities in the V2X entities and other 3GPP network elements, new packet processing and resource allocation algorithms, novel packet fields. The viability of such modifications is also discussed and the performance is evaluated to unveil the benefits compared to a baseline non-NDN approach.
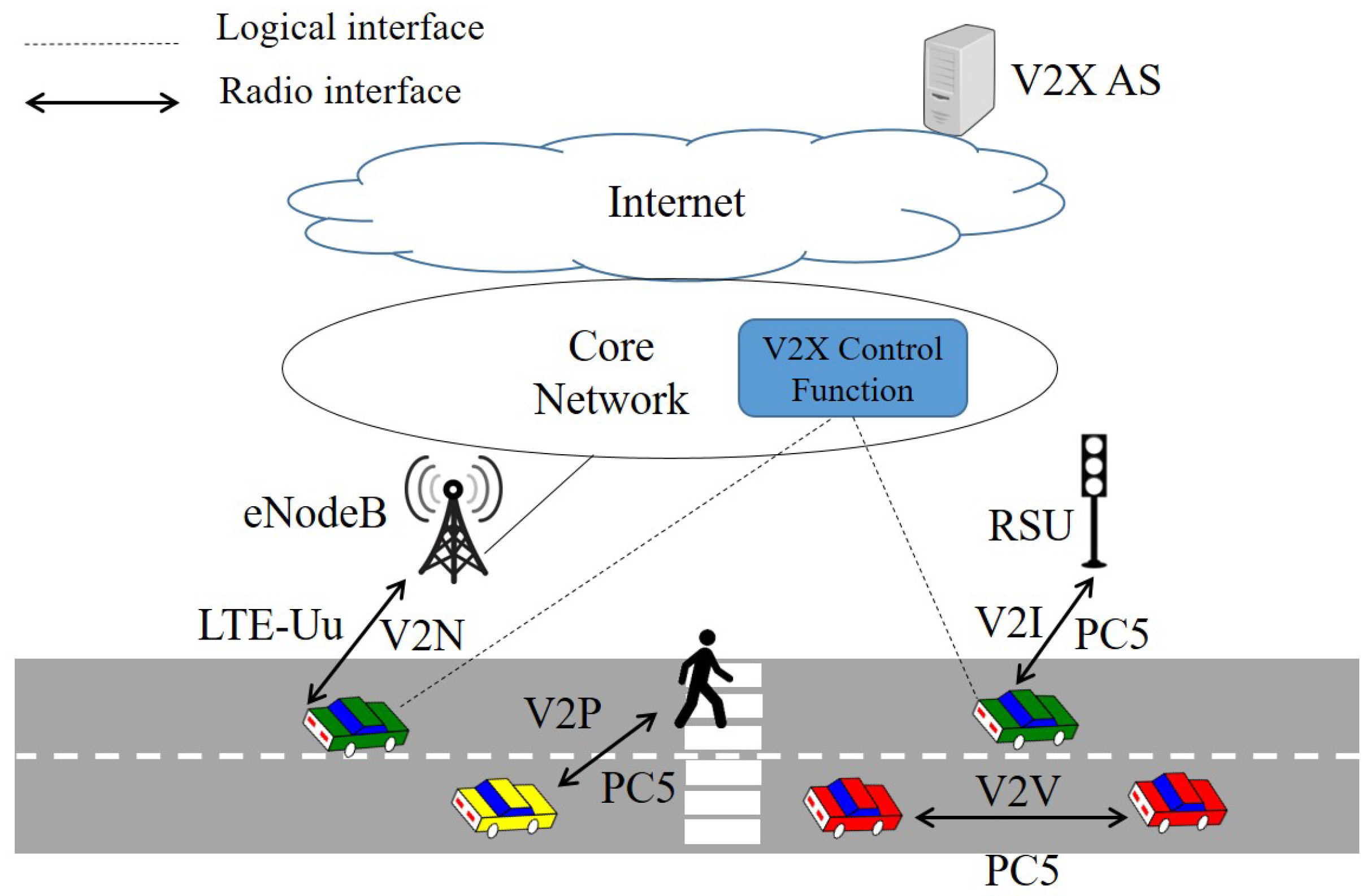
2. V2X Communications in 3GPP
2.1. V2X Communication Modes and Entities
2.2. V2X Communications over the PC5 Interface
- Mode 3 (or scheduled), according to which resource scheduling and interference management on the sidelink are assisted by the eNodeB, via control signaling over the LTE-Uu interface.
- Mode 4 (or autonomous), according to which resource scheduling and interference management on the sidelink are based on distributed algorithms implemented in vehicles. It is the only option for out-of-coverage conditions.
2.3. V2X Communications over the LTE-Uu Interface
3. NDN for V2X Communications
3.1. NDN Basics
- The forwarding strategy permits each NDN node to take actions related to the Interest forwarding, specifically to decide if, when and where forwarding the packet. Depending on the application requirements, the strategy may prioritize the delivery of certain packets or even transmit them in parallel over multiple interfaces. In the case of transmission over a wireless medium with access procedures managed in a distributed manner, the node may defer the packets in order to limit the collision probability with other potentially transmitting nodes. In the case that no route is available in the FIB, it may issue a negative acknowledgement (NACK) message indicating the error type toward the previous node.
- The content caching/replacement strategy permits each NDN node to decide whether to cache the incoming Data packet(s) and which buffered packets to replace in the case the CS is full. The simplest and most intuitive cache-and-replacement strategy implemented in NDN is cache-everything-everywhere with Least Frequently Used (LFU) replacement. This means that all nodes cache all Data packets and replace the least requested ones. More advanced policies have been proposed for data caching and replacement [14], with decisions performed according to a variety of parameters such as content popularity, freshness, and geographical validity of information.
3.2. NDN-Based Content Delivery for V2X: An Overview
4. Including NDN in the 3GPP V2X Architecture
4.1. Gap Analysis and Contribution of This Paper
4.2. Application Scenarios
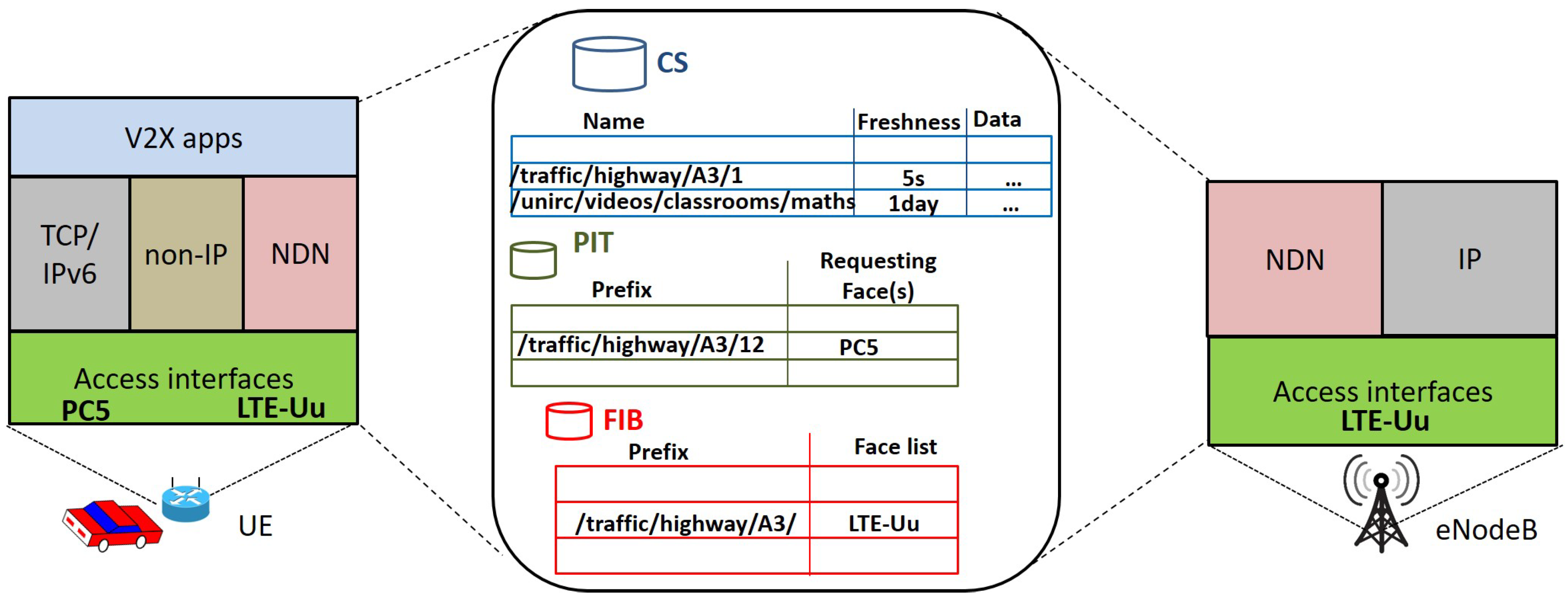
4.3. Protocol Stack
5. 3GPP V2X-NDN Forwarding Strategy
5.1. Content Naming Scheme
5.2. Interest Processing at the Transmitting UE
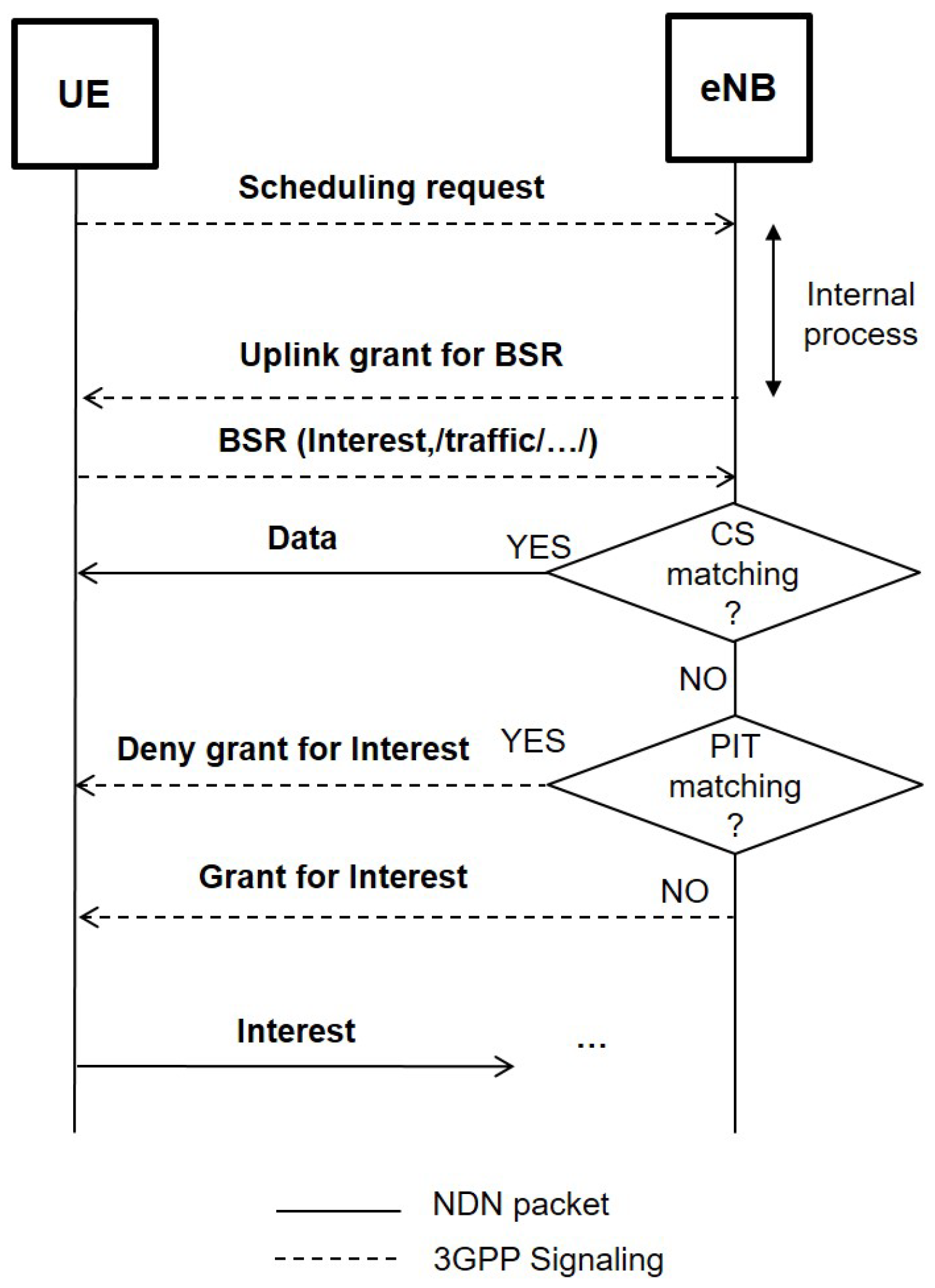
5.3. Interest and Data Processing at the eNodeB
5.4. Interest Processing at the Receiving UE
- -
- The UE first looks in the CS. If a matching is found, it will answer with a Data packet over the same interface it has received the request. Specifically:
- If the outgoing interface is PC5 Mode 4, the UE directly broadcasts the Data packet. To avoid collisions with other provider UEs, smart deferral schemes can be implemented similarly to those deployed for NDN-IEEE 802.11 networks, as described in Section 3.2.
- If the outgoing interface is PC5 Mode 3 or LTE-Uu, the UE sends a grant request for Data transmission to the eNodeB. In both cases, the request piggybacks the name of the Data and, therefore, the eNodeB decides if granting resources according to the name-aware resource allocation scheme previously described.
- -
- If the CS matching fails, then the UE looks in the PIT. If a matching is found, it updates the entry by recording the incoming interface and discards the Interest.
- -
- If the PIT matching also fails, the UE has to decide whether to further relay the Interest or not and, therefore, it looks in the FIB. If a name matching is found, the Interest is forwarded accordingly, otherwise it is discarded. Depending on the outgoing interface, the UE may broadcast the Interest over the PC5 while implementing smart deferral schemes to avoid collisions in Mode 4, or it may send a named grant request to the eNodeB for the Interest transmission over PC5 Mode 3 or LTE-Uu. Again, the eNodeB may grant or refuse the transmission according to the name-aware resource allocation scheme.
6. Evaluation Methodology
6.1. Simulation Tools and Settings
6.2. Performance Metrics
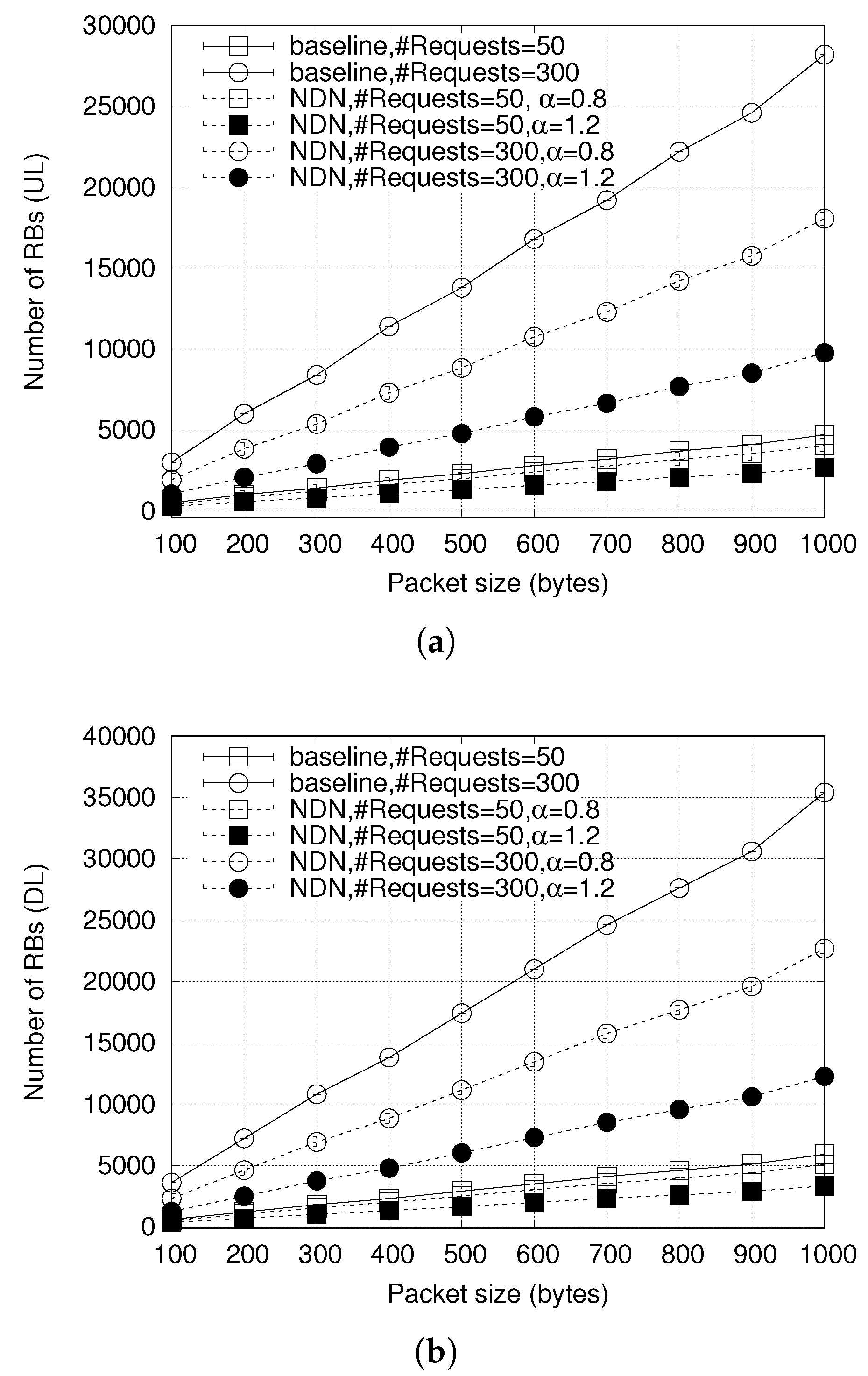
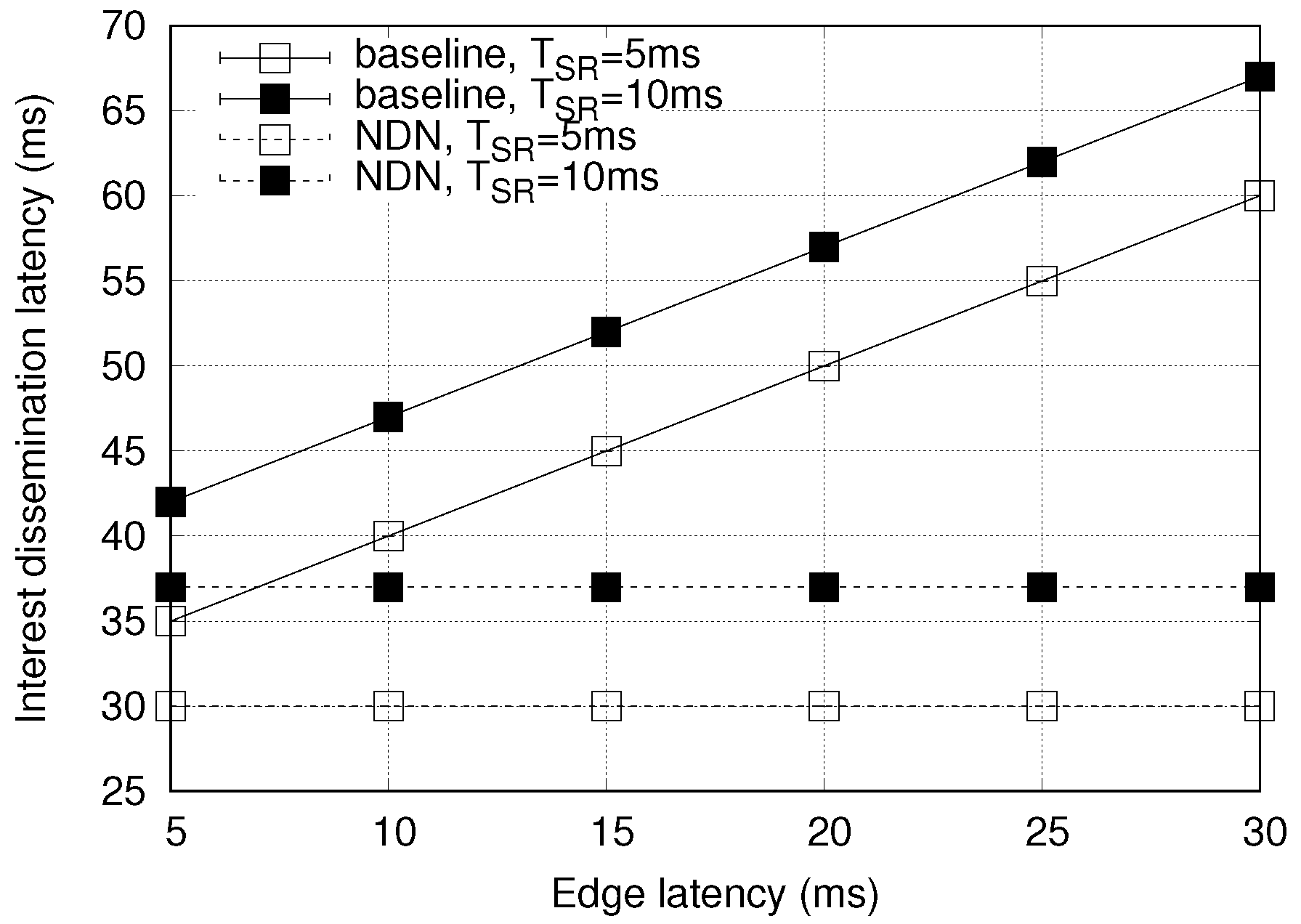
7. Results
8. Conclusions
Author Contributions
Acknowledgments
Conflicts of Interest
Abbreviations
| 3GPP | Third Generation Partnership Project |
| 5G | Fifth Generation |
| ACK | Acknowledgement |
| AS | Application Server |
| BSR | Buffer Status Report |
| CQI | Channel Quality Indicator |
| CP | Control Plane |
| CS | Content Store |
| DL | Downlink |
| eMBMS | evolved Multimedia Broadcast/Multicast Service |
| ETSI | European Telecommunications Standards Institute |
| FIB | Forwarding Information Base |
| ICN | Information Centric Networking |
| IEEE | Institute of Electrical and Electronics Engineer |
| IP | Internet Protocol |
| IoV | Internet of Vehicles |
| IRTF | Internet Engineering Task Force |
| LFU | Least Frequently Used |
| LTE | Long Term Evolution |
| MCS | Modulation and Coding Scheme |
| MEC | Multi-Access Edge Computing |
| MNO | Mobile Network Operator |
| NACK | Negative Acknowledgement |
| NDN | Named Data Networking |
| PIT | Pending Interest Table |
| PUCCH | Physical Uplink Control Channel |
| RAN | Radio Access Network |
| RB | Resource Block |
| RTO | Retransmission timeout |
| SDO | Standard Development Organization |
| SR | Scheduling Request |
| TTL | Time-to-live |
| UE | User Equipment |
| UL | Uplink |
| UP | User Plane |
| URL | Uniform Resource Locator |
| URLLC | Ultra-reliable and low-latency communication |
| V2P | Vehicle-to-Pedestrian |
| V2X | Vehicle-to-Everything |
| V2V | Vehicle-to-Vehicle |
| VUE | Vehicular User Equipment |
| VRU | Vulnerable Road User |
| WSMP | WAVE Short Message Protocol |
References
- Kaiwartya, O.; Abdullah, A.H.; Cao, Y.; Altameem, A.; Prasad, M.; Lin, C.; Liu, X. Internet of Vehicles: Motivation, Layered Architecture, Network Model, Challenges, and Future Aspects. IEEE Access 2016, 4, 5356–5373. [Google Scholar] [CrossRef]
- 3GPP. TS 23.285 V15.2.0. In Technical Specification Group Services and System Aspects; Architecture Enhancements for V2X Services, Release 15; 3rd Generation Partnership Project: Sophia Antipolis, France, 2018. [Google Scholar]
- Ahlgren, B.; Dannewitz, C.; Imbrenda, C.; Kutscher, D.; Ohlman, B. A survey of information-centric networking. IEEE Commun. Mag. 2012, 50, 26–36. [Google Scholar] [CrossRef]
- Khelifi, H.; Luo, S.; Nour, B.; Moungla, H.; Faheem, Y.; Hussain, R.; Ksentini, A. Named Data Networking in Vehicular Ad hoc Networks: State-of-the-Art and Challenges. IEEE Commun. Surv. Tutor. 2019. [Google Scholar] [CrossRef]
- 3GPP. TS 22.185 V15.0.0. In Technical Specification Group Services and System Aspects; Service Requirements for V2X Services. Release 15; 3rd Generation Partnership Project: Sophia Antipolis, France, 2018. [Google Scholar]
- Giust, F.; Sciancalepore, V.; Sabella, D.; Filippou, M.C.; Mangiante, S.; Featherstone, W.; Munaretto, D. Multi-access Edge Computing: The driver behind the wheel of 5G-connected cars. IEEE Commun. Stand. Mag. 2018, 2, 66–73. [Google Scholar] [CrossRef]
- 3GPP. TR 36.213 V14.5.0. In Evolved Universal Terrestrial Radio Access (E-UTRA); Physical Layer Procedures (Release 14). Technical Report; 3rd Generation Partnership Project: Sophia Antipolis, France, 2017. [Google Scholar]
- IEEE 1609.3: IEEE Standard for Wireless Access in Vehicular Environments (WAVE)—Networking Services; IEEE: Piscataway, NJ, USA, 2016.
- 3GPP. TS 36.331, v 15.6.0, Technical Specification Group Radio Access Network (RAN); Evolved Universal Terrestrial Radio Access (E-UTRA); Radio Resource Control (RRC); Protocol Specification; Release 15; 3rd Generation Partnership Project: Sophia Antipolis, France, 2019. [Google Scholar]
- Zhang, L.; Afanasyev, A.; Burke, J.; Jacobson, V.; Crowley, P.; Papadopoulos, C.; Wang, L.; Zhang, B. Named data networking. ACM SIGCOMM Comput. Commun. Rev. 2014, 44, 66–73. [Google Scholar] [CrossRef]
- Bouk, S.H.; Ahmed, S.H.; Hussain, R.; Eun, Y. Named Data Networking’s Intrinsic Cyber-Resilience for Vehicular CPS. IEEE Access 2018, 6, 60570–60585. [Google Scholar] [CrossRef]
- Kerrache, C.A.; Lagraa, N.; Hussain, R.; Ahmed, S.H.; Benslimane, A.; Calafate, C.T.; Cano, J.C.; Vegni, A.M. TACASHI: Trust-aware communication architecture for social internet of vehicles. IEEE Internet Things J. 2019, 6, 5870–5877. [Google Scholar] [CrossRef]
- Yi, C.; Abraham, J.; Afanasyev, A.; Wang, L.; Zhang, B.; Zhang, L. On the role of routing in named data networking. In Proceedings of the 1st ACM Conference on Information-Centric Networking, Paris, France, 24–26 September 2014; pp. 27–36. [Google Scholar]
- Zhang, M.; Luo, H.; Zhang, H. A survey of caching mechanisms in information-centric networking. IEEE Commun. Surv. Tutor. 2015, 17, 1473–1499. [Google Scholar] [CrossRef]
- Bazzi, A.; Masini, B.M.; Zanella, A.; De Castro, C.; Raffaelli, C.; Andrisano, O. Cellular aided vehicular named data networking. In Proceedings of the 2014 International Conference on Connected Vehicles and Expo (ICCVE), Vienna, Austria, 3–7 November 2014; pp. 747–752. [Google Scholar]
- Amadeo, M.; Campolo, C.; Molinaro, A. Priority-based content delivery in the Internet of vehicles through named data networking. J. Sens. Actuator Netw. 2016, 5, 17. [Google Scholar] [CrossRef]
- Anastasiades, C.; Weber, J.; Braun, T. Dynamic unicast: Information-centric multi-hop routing for mobile ad-hoc networks. Comput. Netw. 2016, 107, 208–219. [Google Scholar] [CrossRef]
- Amadeo, M.; Campolo, C.; Molinaro, A. A novel hybrid forwarding strategy for content delivery in wireless information-centric networks. Comput. Commun. 2017, 109, 104–116. [Google Scholar] [CrossRef]
- Wisitpongphan, N.; Tonguz, O.K.; Parikh, J.S.; Mudalige, P.; Bai, F.; Sadekar, V. Broadcast storm mitigation techniques in vehicular ad hoc networks. IEEE Wirel. Commun. 2007, 14, 84–94. [Google Scholar] [CrossRef]
- Amadeo, M.; Campolo, C.; Molinaro, A. Enhancing content-centric networking for vehicular environments. Comput. Netw. 2013, 57, 3222–3234. [Google Scholar] [CrossRef]
- Ahmed, S.H.; Bouk, S.H.; Yaqub, M.A.; Kim, D.; Song, H. DIFS: Distributed interest forwarder selection in vehicular named data networks. IEEE Trans. Intell. Transp. Syst. 2017, 19, 3076–3080. [Google Scholar] [CrossRef]
- Bouk, S.H.; Ahmed, S.H.; Park, K.J.; Eun, Y. Efficient Data Broadcast Mitigation in Multisource Named- Content Discovery for Vehicular CPS. IEEE Commun. Lett. 2019, 23, 1644–1647. [Google Scholar] [CrossRef]
- Grassi, G.; Pesavento, D.; Pau, G.; Vuyyuru, R.; Wakikawa, R.; Zhang, L. VANET via named data networking. In Proceedings of the IEEE Conference on Computer Communications Workshops (INFOCOM WKSHPS), Toronto, ON, Canada, 27 April–2 May 2014; pp. 410–415. [Google Scholar]
- Liu, X.; Nicolau, M.J.; Costa, A.; Macedo, J.; Santos, A. A geographic opportunistic forwarding strategy for vehicular named data networking. In Intelligent Distributed Computing IX; Springer: Cham, Switzerland, 2016; pp. 509–521. [Google Scholar]
- Kuai, M.; Hong, X.; Yu, Q. Density-aware delay-tolerant interest forwarding in vehicular named data networking. In Proceedings of the 2016 IEEE 84th Vehicular Technology Conference (VTC-Fall), Montreal, QC, Canada, 18–21 September 2016; pp. 1–5. [Google Scholar]
- Ahmed, S.H.; Bouk, S.H.; Yaqub, M.A.; Kim, D.; Gerla, M. CONET: Controlled data packets propagation in vehicular named data networks. In Proceedings of the 2016 13th IEEE Annual Consumer Communications & Networking Conference (CCNC), Las Vegas, NV, USA, 9–12 January 2016; pp. 620–625. [Google Scholar]
- Amadeo, M.; Molinaro, A.; Campolo, C.; Sifalakis, M.; Tschudin, C. Transport layer design for named data wireless networking. In Proceedings of the IEEE Conference on Computer Communications Workshops (INFOCOM WKSHPS), Toronto, ON, Canada, 27 April–2 May 2014; pp. 464–469. [Google Scholar]
- Bouk, S.H.; Ahmed, S.H.; Kim, D.; Park, K.J.; Eun, Y.; Lloret, J. LAPEL: Hop limit based adaptive PIT entry lifetime for vehicular named data networks. IEEE Trans. Veh. Technol. 2018, 67, 5546–5557. [Google Scholar] [CrossRef]
- Amadeo, M.; Campolo, C.; Molinaro, A. Named data networking for priority-based content dissemination in VANETs. In Proceedings of the IEEE 27th Annual International Symposium on Personal, Indoor, and Mobile Radio Communications (PIMRC), Valencia, Spain, 4–8 September 2016; pp. 1–6. [Google Scholar]
- Li, Y.; Shi, X.; Lindgren, A.; Hu, Z.; Zhang, P.; Jin, D.; Zhou, Y. Context-Aware Data Dissemination for ICN-Based Vehicular Ad Hoc Networks. Information 2018, 9, 263. [Google Scholar] [CrossRef]
- 3GPP. TR 22.891 V14.2.0. In Technical Specification Group Services and System Aspects; Feasibility Study on New Services and Markets Technology Enablers; Stage 1; 3rd Generation Partnership Project: Sophia Antipolis, France, 2016. [Google Scholar]
- Suthar, P.; Stolic, M.; Jangam, A.; Trossen, D.; Ravindran, R. Native Deployment of ICN in LTE, 4G Mobile Networks. Technical Report, ICN Research Group, Internet-Draft, 2019. Available online: https://tools.ietf.org/html/draft-irtf-icnrg-icn-lte-4g-04 (accessed on 17 September 2019).
- Batista, P.; Araújo, I.; Linder, N.; Laraqui, K.; Klautau, A. Testbed for ICN media distribution over LTE radio access networks. Comput. Netw. 2019, 150, 70–80. [Google Scholar] [CrossRef]
- Ravindran, R.; Suthar, P.; Trossen, D.; Wang, C.; White, G. Enabling ICN in 3GPP’s 5G NextGen Core Architecture. Technical Report, ICN Research Group, Internet-Draft, 2019. Available online: https://tools.ietf.org/html/draft-ravi-icnrg-5gc-icn-04 (accessed on 17 September 2019).
- Wang, X.; Chen, M.; Taleb, T.; Ksentini, A.; Leung, V.C. Cache in the air: Exploiting content caching and delivery techniques for 5G systems. IEEE Commun. Mag. 2014, 52, 131–139. [Google Scholar] [CrossRef]
- Roger, S.; Martín-Sacristán, D.; Garcia-Roger, D.; Monserrat, J.F.; Spapis, P.; Kousaridas, A.; Ayaz, S.; Kaloxylos, A. Low-Latency Layer-2-Based Multicast Scheme for Localized V2X Communications. IEEE Trans. Intell. Transp. Syst. 2019, 20, 2962–2975. [Google Scholar] [CrossRef]
- Wang, L.; Wakikawa, R.; Kuntz, R.; Vuyyuru, R.; Zhang, L. Data naming in vehicle-to-vehicle communications. In Proceedings of the 2012 Proceedings IEEE INFOCOM Workshops, Orlando, FL, USA, 25–30 March 2012; pp. 328–333. [Google Scholar]
- Pesavento, D.; Grassi, G.; Palazzi, C.E.; Pau, G. A naming scheme to represent geographic areas in NDN. In Proceedings of the 2013 IFIP Wireless Days (WD) 2013, Valencia, Spain, 13–15 November 2013; pp. 1–3. [Google Scholar]
- 3GPP. TS 24.386 V14.3.0. In Technical Specification Group Core Network and Terminals; User Equipment (UE) to V2X Control Function; Protocol Aspects; Stage 3 (Release 14); 3rd Generation Partnership Project: Sophia Antipolis, France, 2017. [Google Scholar]
- Kim, W.; Lee, E.K. LTE Network Enhancement for Vehicular Safety Communication. Mob. Inf. Syst. 2017, 2017, 8923782. [Google Scholar] [CrossRef]
| Communication Modes | V2V, V2P, V2I | V2N |
|---|---|---|
| Radio interface | PC5 | LTE-Uu |
| Spectrum | 5.9 GHz | 3.5 GHz |
| Traffic primitive | Multicast/Broadcast | Unicast, Multicast (eMBMS) |
| Traffic type | IPv6, non-IP | IPv6 |
| Access mode | Newly added Scheduled and Autonomous modes | Legacy mode |
| Parameter | Notation | Value |
|---|---|---|
| Transmission processing delay | 1 ms | |
| Scheduling procedure delay | 8 ms | |
| Waiting time for the SR opportunity | Varying | |
| Interest transmission time in both UL/DL | 1 ms | |
| Decoding delay at the eNodeB | 1 ms | |
| MCH Scheduling Period | 10 ms | |
| Decoding delay at the receiver UE | 1.5 ms | |
| Application-layer receiver processing | 3 ms | |
| Processing time at the V2X AS | Varying |
| Zipf’s Parameter | Baseline | Legacy NDN | Our Proposal | |||
|---|---|---|---|---|---|---|
| Requests = 50 | Requests = 300 | Requests = 50 | Requests = 300 | Requests = 50 | Requests = 300 | |
| = 0.8 | 100 | 600 | 93.13 | 492.15 | 86.26 | 384.3 |
| = 1.2 | 100 | 600 | 78.27 | 403.86 | 56.54 | 205.72 |
| Entity | Proposed Change(s) |
|---|---|
| UE | - Addition of the NDN layer and relevant data structures and routines |
| - Name-driven outgoing interface(s) selection | |
| eNodeB | - Addition of the NDN layer and relevant data structures and routines |
| - Name-aware resource allocation | |
| V2X Control Function | Advertisement/pre-configuration of naming conventions and main prefix names for an easier convergence |
| V2X AS | eNodeB’s FIB population |
© 2019 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Amadeo, M.; Campolo, C.; Molinaro, A.; Harri, J.; Rothenberg, C.E.; Vinel, A. Enhancing the 3GPP V2X Architecture with Information-Centric Networking. Future Internet 2019, 11, 199. https://doi.org/10.3390/fi11090199
Amadeo M, Campolo C, Molinaro A, Harri J, Rothenberg CE, Vinel A. Enhancing the 3GPP V2X Architecture with Information-Centric Networking. Future Internet. 2019; 11(9):199. https://doi.org/10.3390/fi11090199
Chicago/Turabian StyleAmadeo, Marica, Claudia Campolo, Antonella Molinaro, Jerome Harri, Christian Esteve Rothenberg, and Alexey Vinel. 2019. "Enhancing the 3GPP V2X Architecture with Information-Centric Networking" Future Internet 11, no. 9: 199. https://doi.org/10.3390/fi11090199
APA StyleAmadeo, M., Campolo, C., Molinaro, A., Harri, J., Rothenberg, C. E., & Vinel, A. (2019). Enhancing the 3GPP V2X Architecture with Information-Centric Networking. Future Internet, 11(9), 199. https://doi.org/10.3390/fi11090199









