The Next Generation Platform as A Service: Composition and Deployment of Platforms and Services
Abstract
1. Introduction
2. Related Work
3. The Next Generation PaaS: Architecture, Concepts, Processes, and Workflows
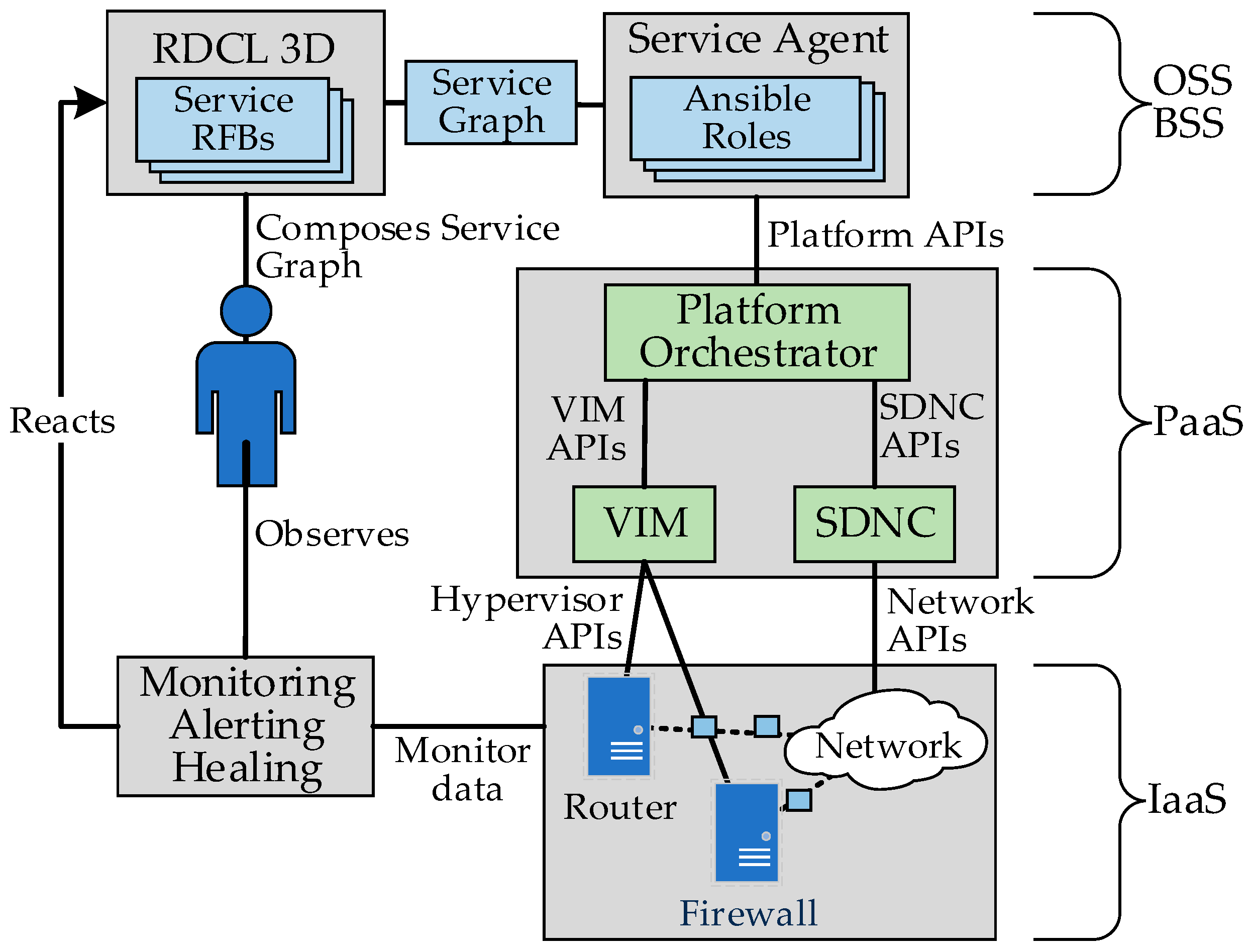
3.1. The NGPaaS Architecture
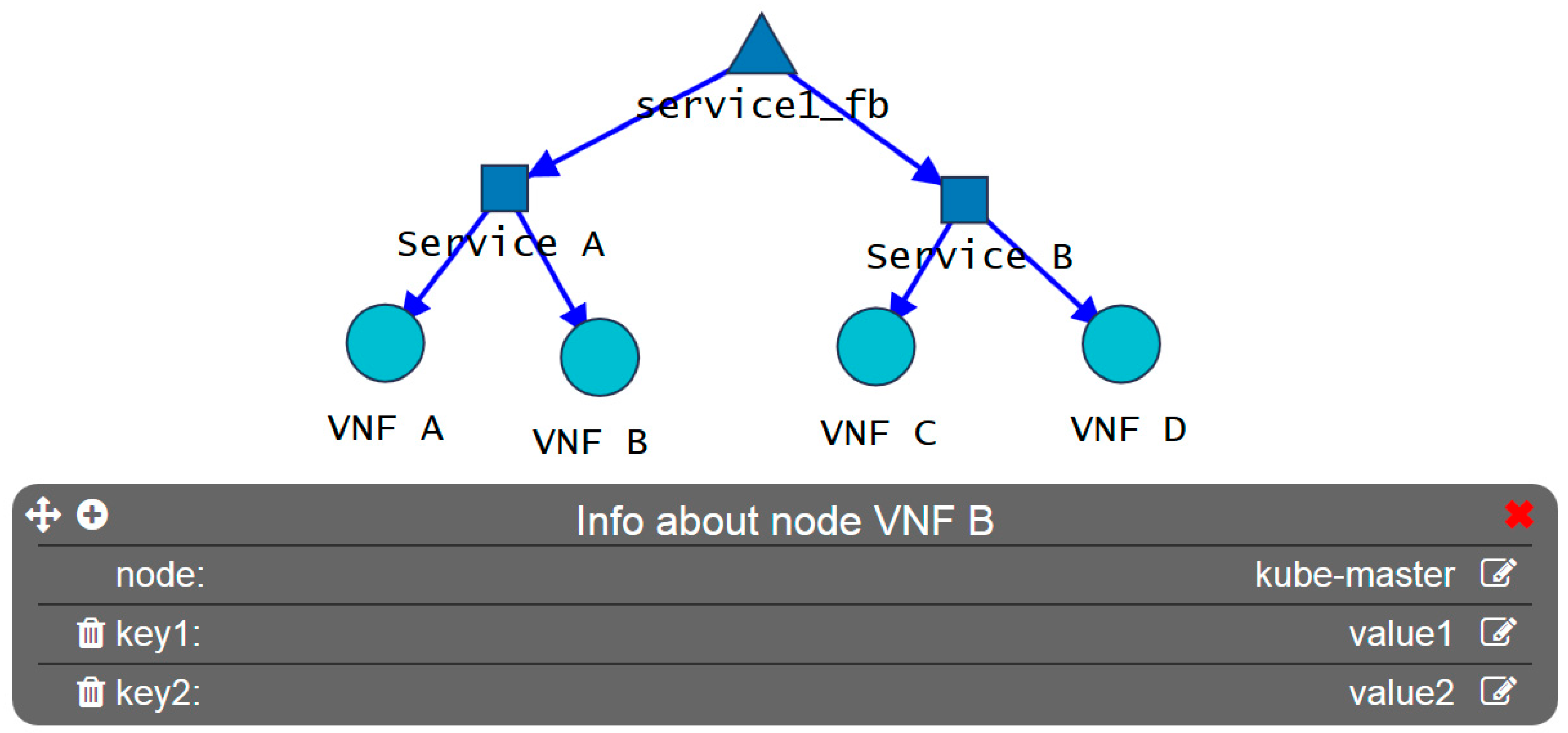
3.2. Reusable Functional Blocks
3.3. RFB Description and Composition Languages Design, Deploy and Direct Tool
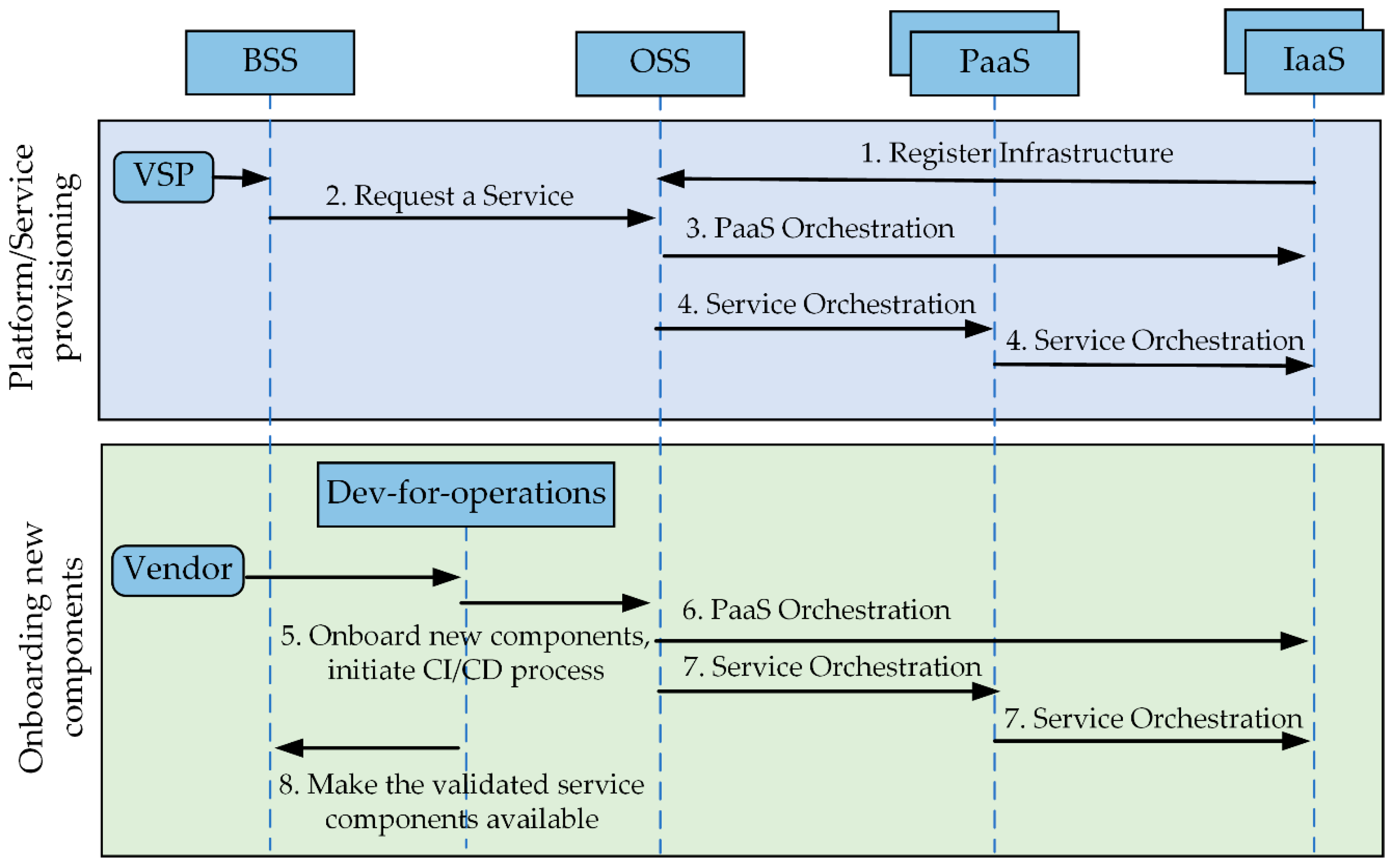
3.4. Processes and Workflows
4. Virtual Network Function as A Service, Overview
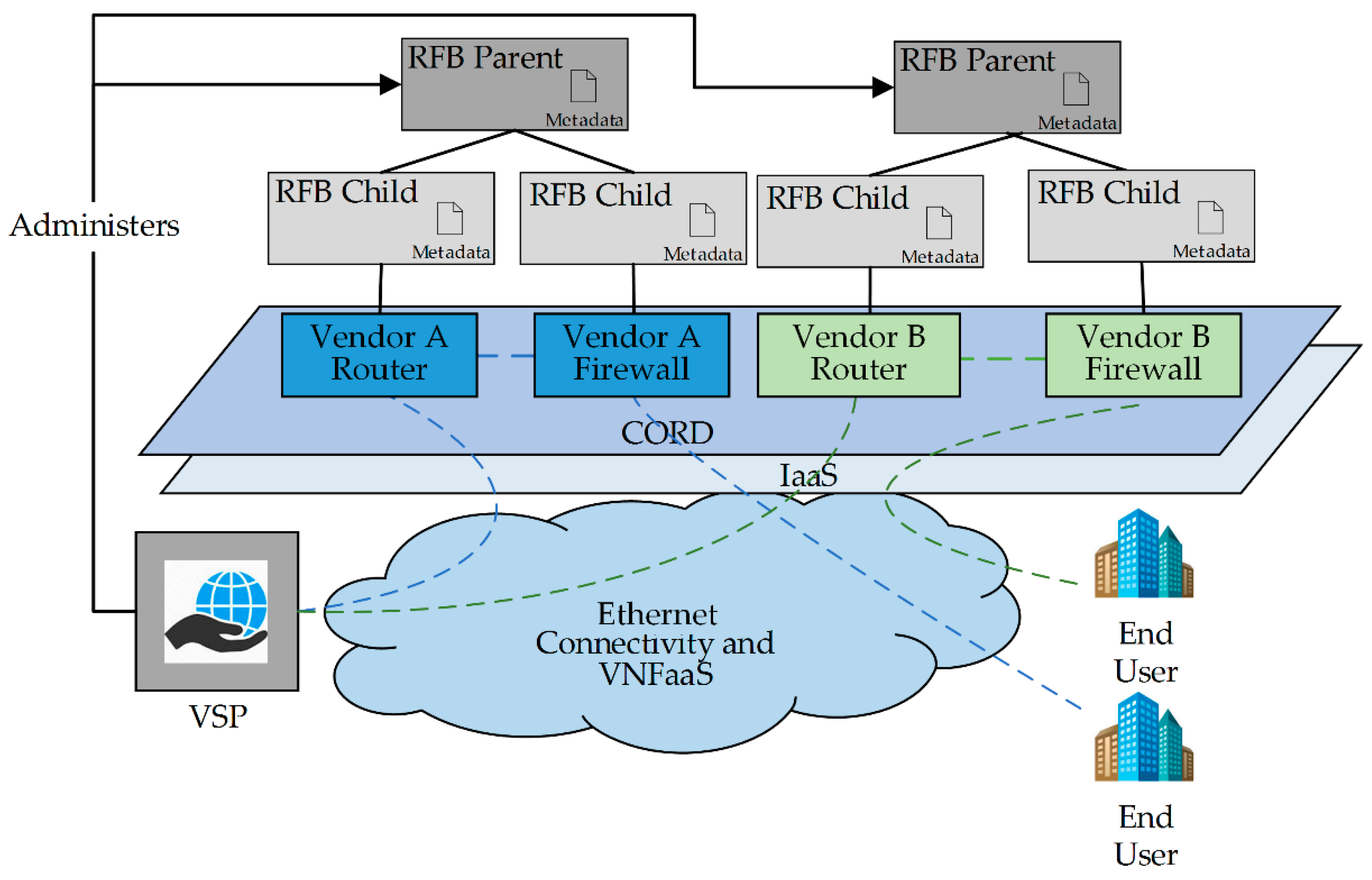
4.1. The Telco PaaS Use Case: Virtual Network Function as A Service (VNFaaS)
4.2. The VNFaaS Proof of Concept
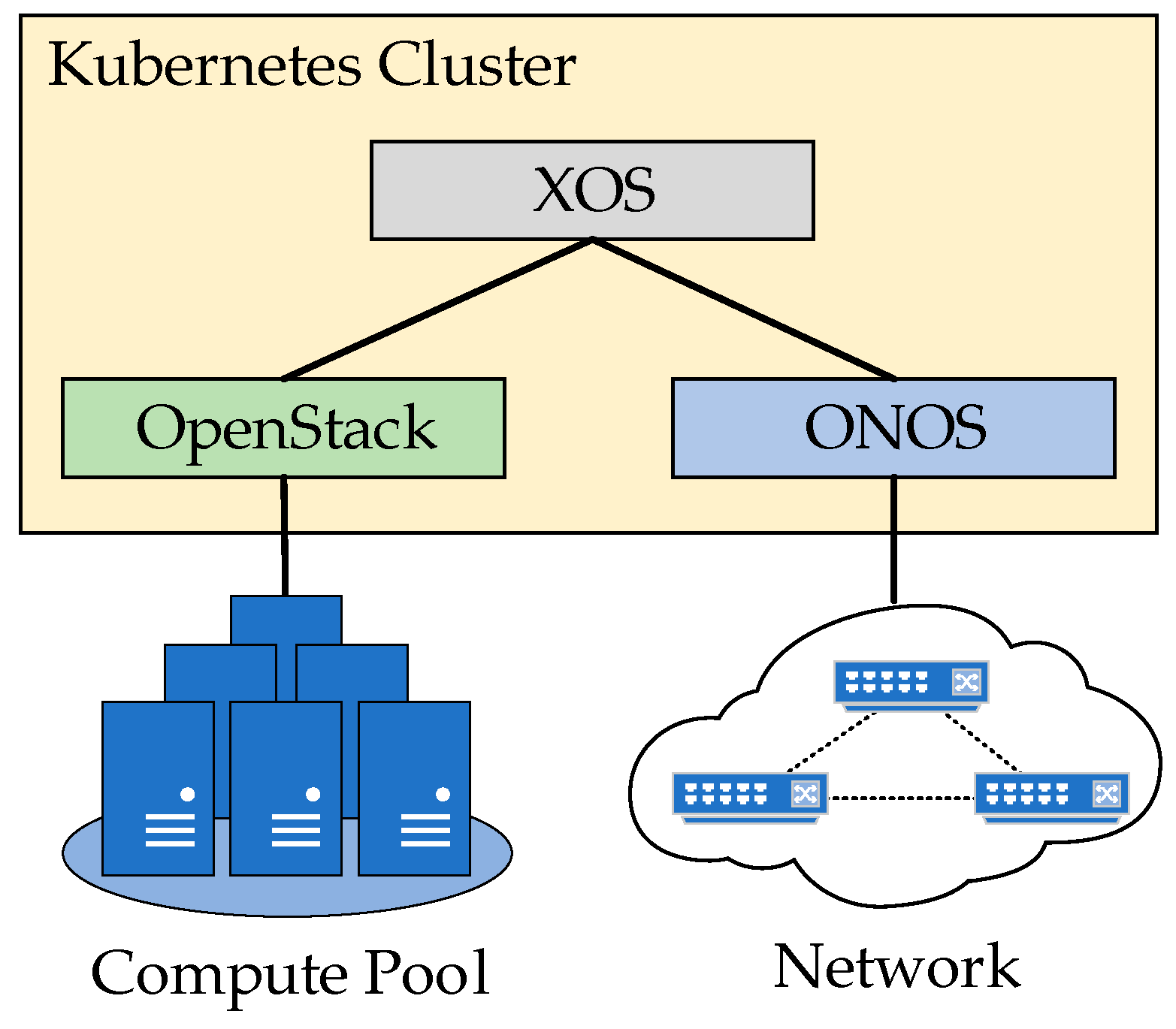
4.3. The Telco PaaS Platform: Central Office Re-Architected as A Datacentre (CORD)
4.4. Supported Virtual Network Functions (VNFs) and Value Added Services (VAS)
4.4.1. Core Services: Virtual Firewalls and Virtual Routers
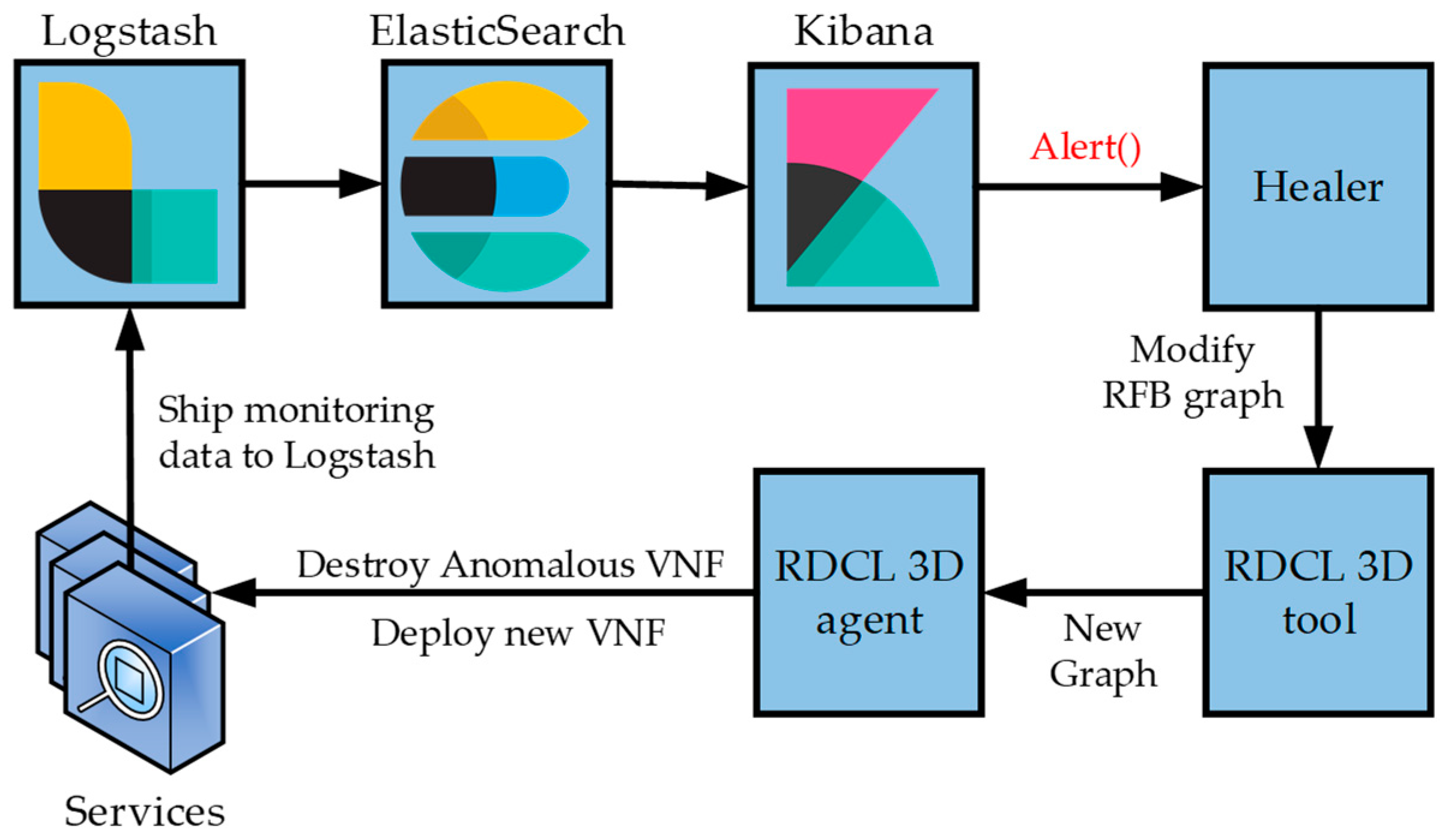
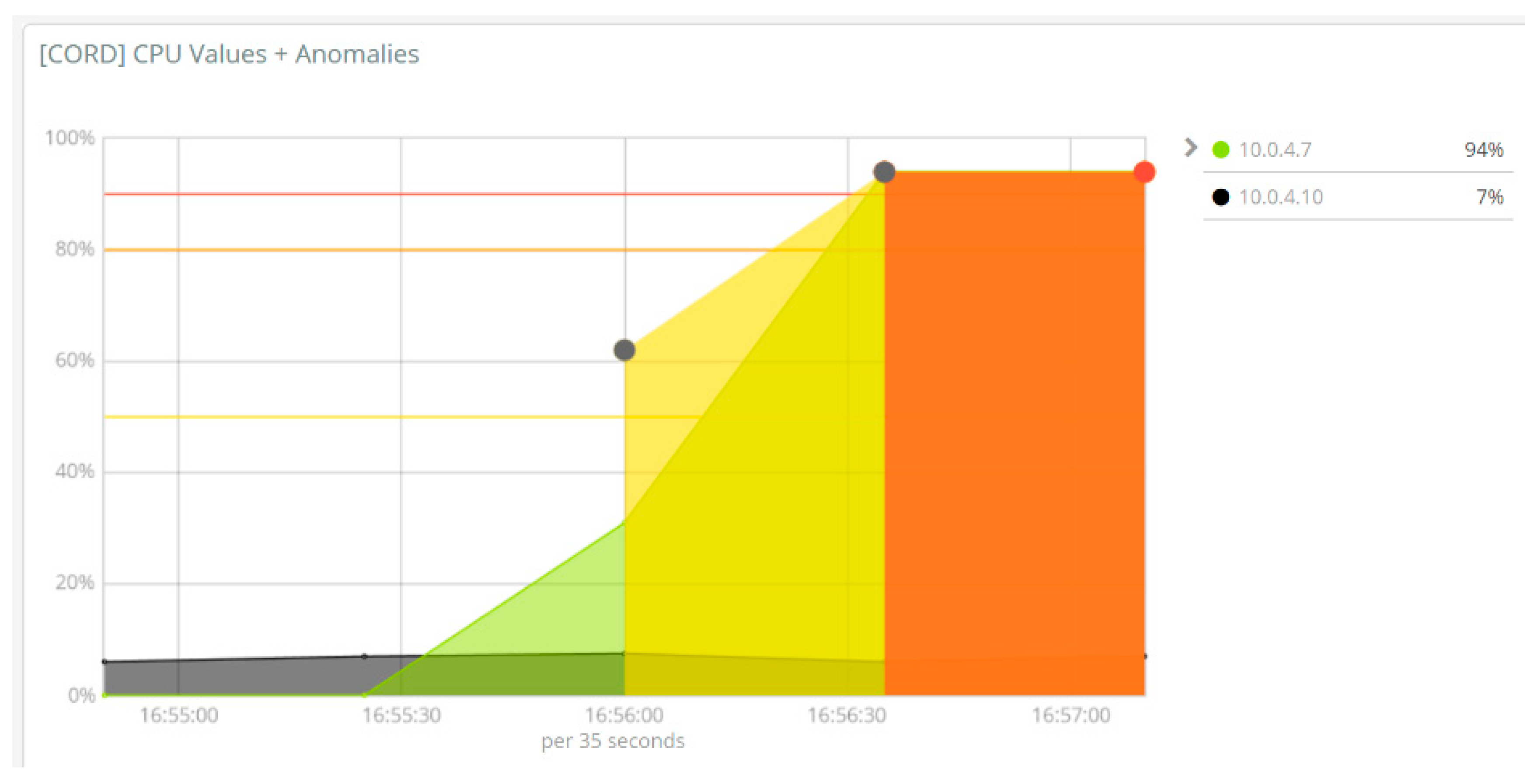
4.4.2. Value Added Services: Monitoring, Alerting, and Healing
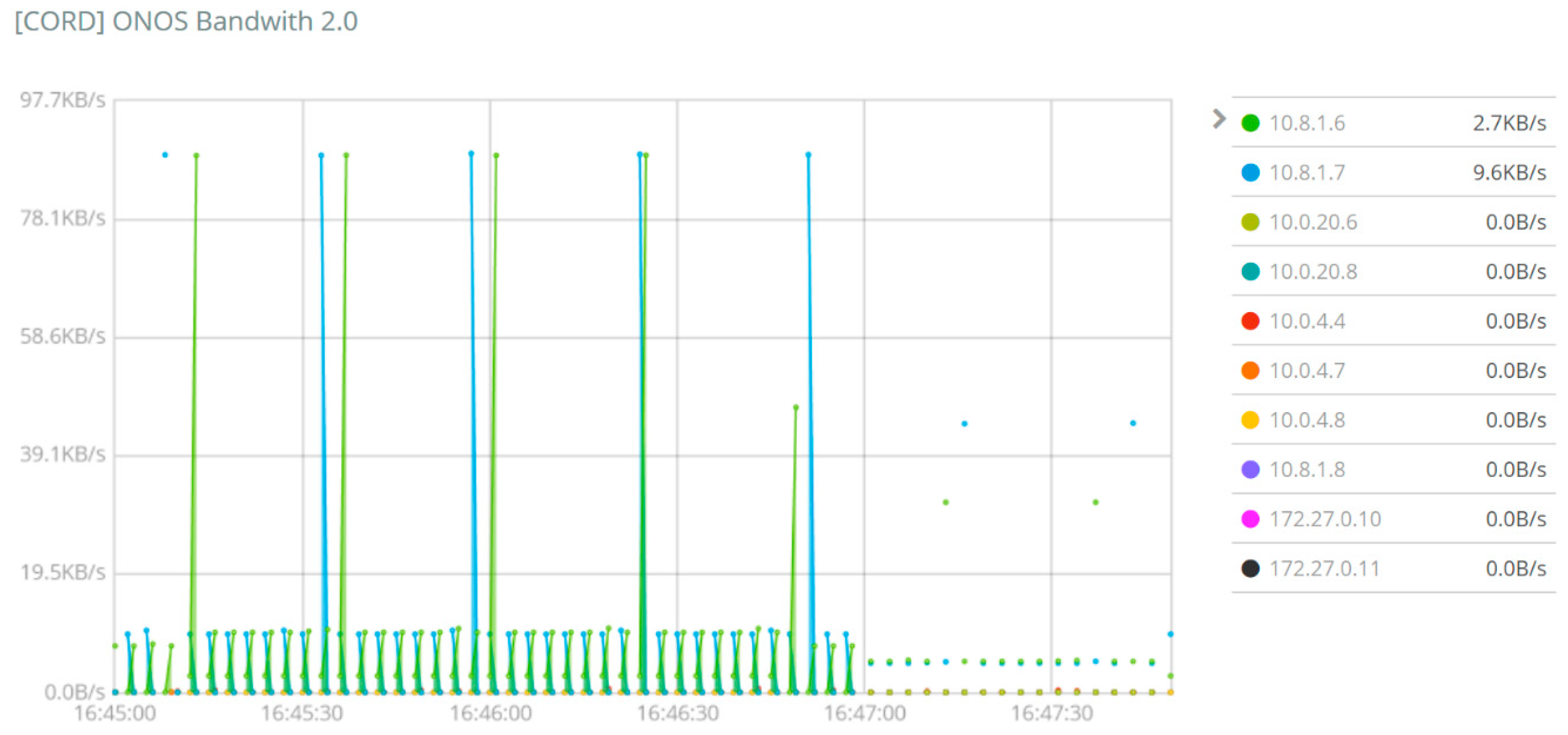
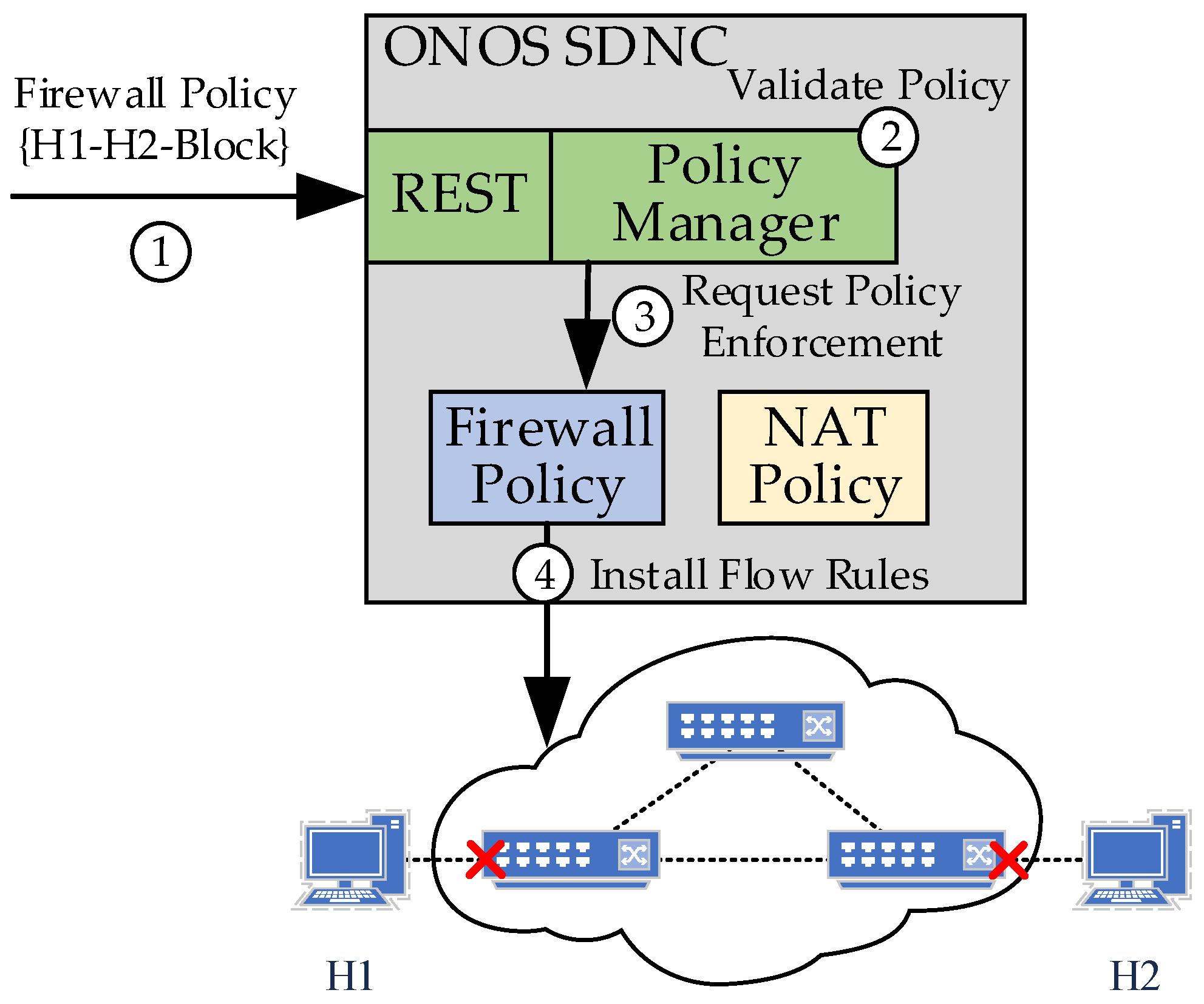
4.4.3. Value Added Services: Policy-Based Network Management
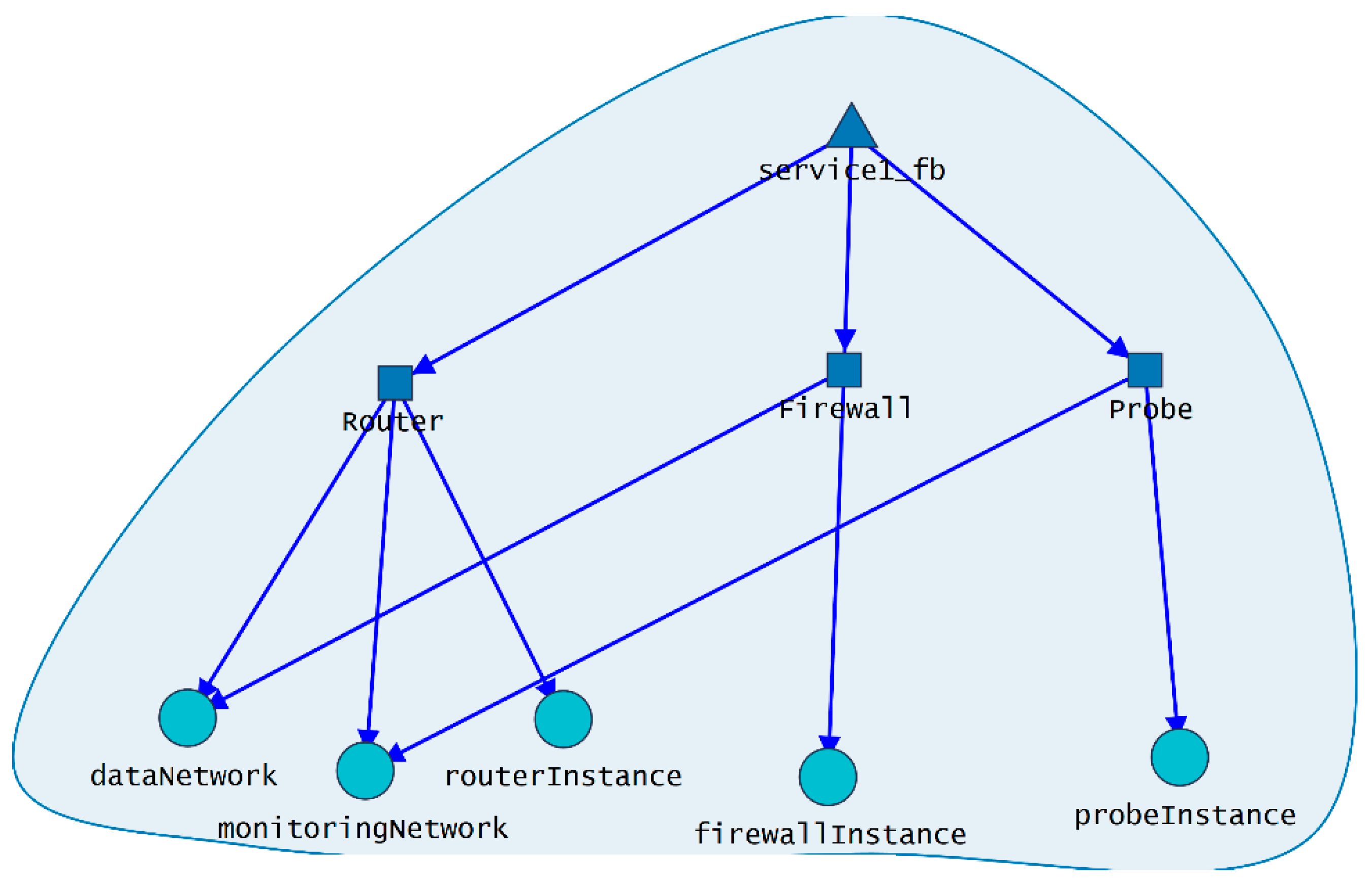
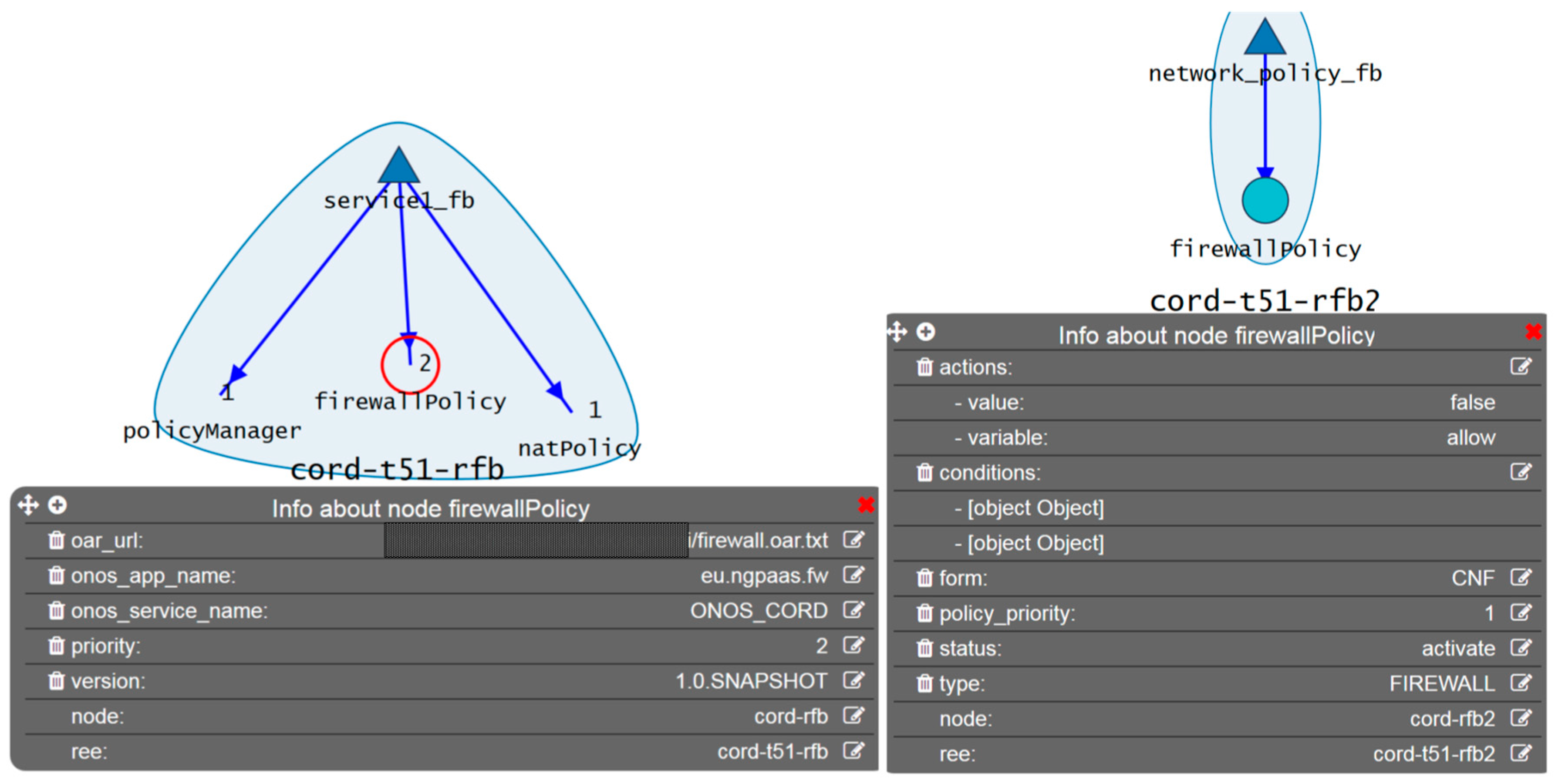
5. Virtual Network Function as A Service: Component RFBisation
5.1. RFBisation of the CORD Platform
5.2. RFBisation of Services and Value-Added Services
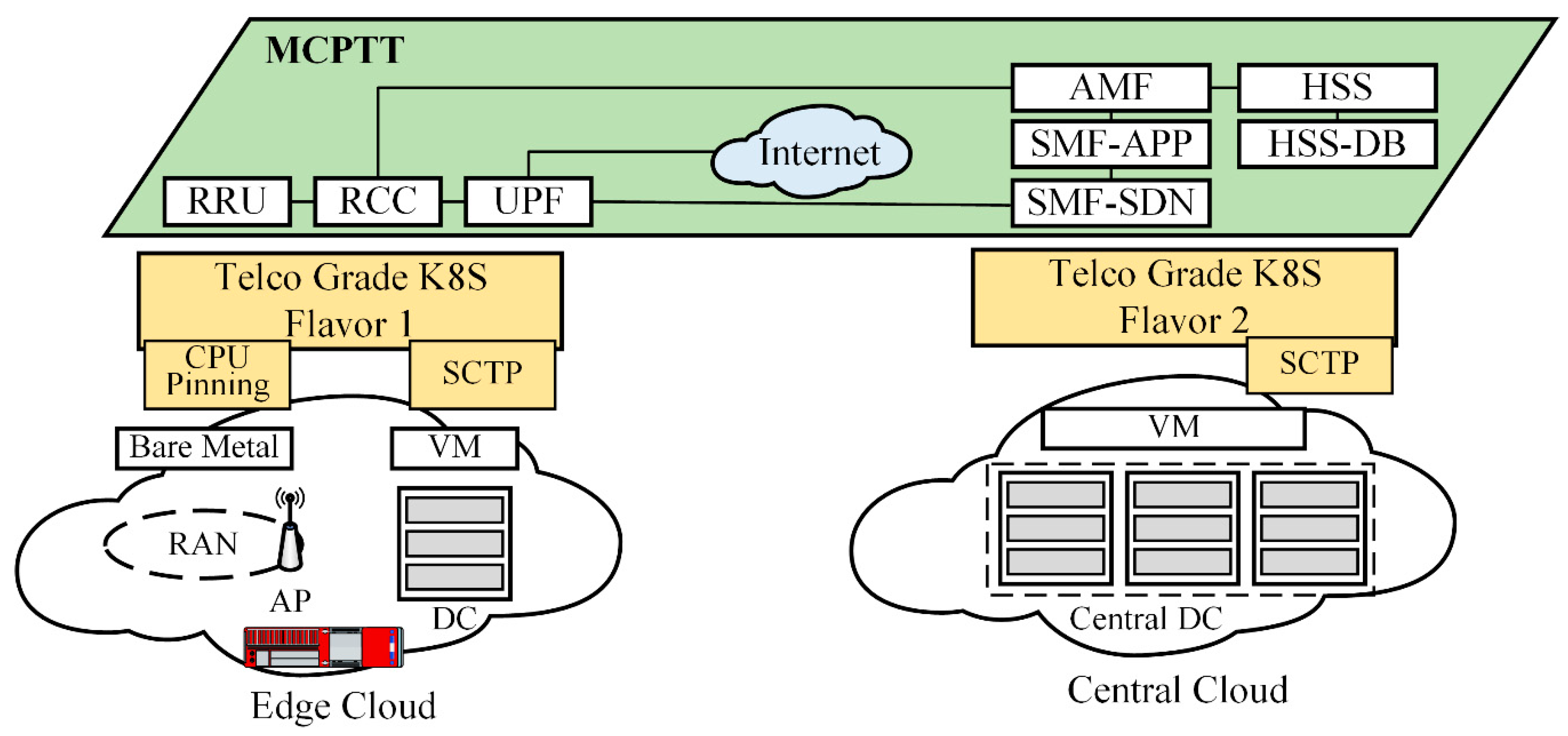
6. 5G Public Safety Use-Case
7. Discussion and Conclusions
Author Contributions
Funding
Conflicts of Interest
References
- Erfanian, J.; Smith, B. Network Functions Virtualisation—White Paper on NFV Priorities for 5G. Available online: https://portal.etsi.org/NFV/NFV_White_Paper_5G.pdf (accessed on 19 May 2019).
- Van Lingen, F.; Yannuzzi, M.; Jain, A.; Irons–Mclean, R.; Lluch, O.; Carrera, D.; Perez, J.L.; Gutierrez, A.; Montero, D.; Marti, J.; et al. The Unavoidable Convergence of NFV, 5G, and Fog: A Model-Driven Approach to Bridge Cloud and Edge. IEEE Commun. Mag. 2017, 55, 28–35. [Google Scholar] [CrossRef]
- Van Rossem, S.; Sayadi, B.; Roullet, L.; Mimidis, A.; Paolino, M.; Veitch, P.; Berde, B.; Labrador, I.; Ramos, A.; Tavernier, W.; et al. A Vision for the Next Generation Platform-as-a-Service. In Proceedings of the 2018 IEEE 5G World Forum (5GWF), Silicon Valley, CA, USA, 9–11 July 2018; pp. 14–19. [Google Scholar]
- Mimidis Kentis, A.; Ollora Zaballa, E.; Soler, J.; Bessem, S.; Roullet, L.; Van Rossem, S.; Pinneterre, S.; Paolino, M.; Raho, D.; Du, X.; et al. The Next Generation Platform as a Service Cloudifying Service Deployments in Telco-Operators Infrastructure. In Proceedings of the 25th International Conference on Telecommunications (ICT 2018), Saint Malo, France, 26–28 June 2018; pp. 399–404. [Google Scholar]
- Salsano, S.; Lombardo, F.; Pisa, C.; Greto, P.; Blefari-Melazzi, N. RDCL 3D, a model agnostic web framework for the design and composition of NFV services. In Proceedings of the 2017 IEEE Conference on Network Function Virtualization and Software Defined Networks (NFV-SDN), Berlin, Germany, 6–8 November 2017; pp. 216–222. [Google Scholar]
- Peterson, L. “CORD: Central Office Re-Architected as a Datacenter,” Open Networking Lab White Paper. November 2015. Available online: http://opencord.org/wp-content/uploads/2016/03/CORD-Whitepaper.pdf (accessed on 19 May 2019).
- Quittek, J. “Network Functions Virtualisation (NFV); Management and Orchestration” Gs Nfv-Man 001 V1.1.1. 2014, Volume 1, pp. 1–184. Available online: https://www.etsi.org/deliver/etsi_gs/NFV-MAN/001_099/001/01.01.01_60/gs_nfv-man001v010101p.pdf (accessed on 19 May 2019).
- Open Source MANO. Available online: https://osm.etsi.org/ (accessed on 19 May 2019).
- 5G Tango. Available online: https://www.5gtango.eu/ (accessed on 19 May 2019).
- Nogales, B.; Vidal, I.; Lopez, D.R.; Rodriguez, J.; Garcia-Reinoso, J.; Azcorra, A. Design and Deployment of an Open Management and Orchestration Platform for Multi-Site NFV Experimentation. IEEE Commun. Mag. 2019, 57, 20–27. [Google Scholar] [CrossRef]
- Yilma, G.M.; Yousaf, F.Z.; Sciancalepore, V.; Costa-Perez, X. On the Challenges and KPIs for Benchmarking Open-Source NFV MANO Systems: OSM vs. ONAP. Available online: https://arxiv.org/ftp/arxiv/papers/1904/1904.10697.pdf (accessed on 19 May 2019).
- Alvarez, F.; Breitgand, D.; Griffin, D.; Andriani, P.; Rizou, S.; Zioulis, N.; Moscatelli, F.; Serrano, J.; Keltsch, M.; Trakadas, P.; et al. An Edge-to-Cloud Virtualized Multimedia Service Platform for 5G Networks. IEEE Trans. Broadcast. 2019, 1–12. [Google Scholar] [CrossRef]
- Tarafdar, N.; Lin, T.; Ly-Ma, D.; Rozhko, D.; Leon-Garcia, A.; Chow, P. Building the Infrastructure for Deploying FPGAs in the Cloud. In Hardware Accelerators in Data Centers; Kachris, C., Falsafi, B., Soudris, D., Eds.; Springer International Publishing: Cham, Switzerland, 2019; pp. 9–33. [Google Scholar]
- Chiotakis, S.; Pinneterre, S.; Paolino, M. vFPGAmanager: A Hardware-Software Framework for Optimal FPGA Resources Exploitation in Network Function Virtualization. In Proceedings of the 2019 European Conference on Networks and Communications (EuCNC), Valencia, Spain, 18–21 June 2019; Available online: http://www.virtualopensystems.com/en/research/scientific-contributions/vfpgamanager-eucnc2019/ (accessed on 19 May 2019).
- Li, X.; Wang, X.; Liu, F.; Xu, H. DHL: Enabling Flexible Software Network Functions with FPGA Acceleration. In Proceedings of the 2018 IEEE 38th International Conference on Distributed Computing Systems (ICDCS), Vienna, Austria, 2–6 July 2018; pp. 1–11. [Google Scholar]
- Zhang, Q.; Liu, F.; Zeng, C. Adaptive Interference-Aware VNF Placement for Service-Customized 5G Network Slices. 2019. Available online: https://pdfs.semanticscholar.org/5aea/e87f05bb4a5f08b9fae9a135863c4eaeea59.pdf?_ga=2.233200922.503865865.1558267333-871421267.1558267333 (accessed on 19 May 2019).
- Fei, X.; Liu, F.; Xu, H.; Jin, H. Adaptive VNF Scaling and Flow Routing with Proactive Demand Prediction. In Proceedings of the IEEE INFOCOM 2018—IEEE Conference on Computer Communications, Honolulu, HI, USA, 15–19 April 2018; pp. 486–494. [Google Scholar]
- Miao, W.; Min, G.; Wu, Y.; Huang, H.; Zhao, Z.; Wang, H.; Luo, C. Stochastic Performance Analysis of Network Function Virtualization in Future Internet. IEEE J. Select. Areas Commun. 2019, 37, 613–626. [Google Scholar] [CrossRef]
- Wang, T.; Xu, H.; Liu, F. Multi-Resource Load Balancing for Virtual Network Functions. In Proceedings of the 2017 IEEE 37th International Conference on Distributed Computing Systems (ICDCS), Atlanta, GA, USA, 5–8 June 2017; pp. 1322–1332. [Google Scholar]
- Fei, X.; Liu, F.; Xu, H.; Jin, H. Towards Load-Balanced VNF Assignment in Geo-Distributed NFV Infrastructure. In Proceedings of the 2017 IEEE/ACM 25th International Symposium on Quality of Service (IWQoS), Vilanova i la Geltrú, Spain, 14–16 June 2017; pp. 1–10. [Google Scholar]
- Mfula, H.; Nurminen, J.K. Self-Healing Cloud Services in Private Multi-Clouds. In Proceedings of the 2018 International Conference on High Performance Computing & Simulation (HPCS), Orleans, France, 16–20 July 2018; pp. 165–170. [Google Scholar]
- Zhijing, L.; Zhao, B.; Zheng, H.; Ge, Z.; Mahimkar, A.; Wang, J.; Emmons, J.; Ogden, L. Predictive Analysis in Network Function Virtualization. In Proceedings of the Acm Sigcomm Internet Measurement Conference, Imc. Association for Computing Machinery, Boston, MA, USA, 31 October–2 November 2018; pp. 161–167. [Google Scholar]
- Acker, A.; Schmidt, F.; Gulenko, A.; Kao, O. Online Density Grid Pattern Analysis to Classify Anomalies in Cloud and NFV Systems. In Proceedings of the 2018 IEEE International Conference on Cloud Computing Technology and Science (CloudCom), Nicosia, Cyprus, 10–13 December 2018; pp. 290–295. [Google Scholar]
- Röck, C.; Kolb, S. Nucleus—Unified Deployment and Management for Platform as a Service, University of Bamberg. Tech. Rep. 2016, 49. Available online: https://www.uni-bamberg.de/pi/forschung/publikationen/16-04-nucleus-unified-deployment-and-management-for-platform-as-a-service/ (accessed on 19 May 2019).
- Van Rossem, S.; Tavernier, W.; Colle, D.; Pickavet, M.; Demeester, P. Introducing Development Features for Virtualized Network Services. IEEE Commun. Mag. 2018, 56, 184–192. [Google Scholar] [CrossRef]
- Veitch, P.; Broadbent, A.; Rossem, S.V.; Sayadi, B.; Natarianni, L.; Al Jammal, B.; Roullet, L.; Mimidis, A.; Ollora, E.; Soler, J.; et al. Re-Factored Operational Support Systems for the Next Generation Platform-as-a-Service (NGPaaS). In Proceedings of the 2018 IEEE 5G World Forum (5GWF), Silicon Valley, CA, USA, 9–11 July 2018; pp. 1–5. [Google Scholar]
- Berde, B.; Van Rossem, S.; Ramos, A.; Orru, M.; Shatnawi, A. Dev-for-Operations and Multi-Sided Platform for Next Generation Platform as a Service. In Proceedings of the European Conference on Networks and Communications (EuCNC), Ljubljana, Slovenia, 18–21 June 2018; pp. 1–5. [Google Scholar]
- ETSI NFV ISG, Network Functions Virtualisation (NFV); Network Service Templates Specification. ETSI GS NFV-IFA 014 V2.1.1 (2016–10). Available online: https://www.etsi.org/deliver/etsi_gs/NFV-IFA/001_099/014/02.01.01_60/gs_NFV-IFA014v020101p.pdf (accessed on 19 May 2019).
- Red Hat Ansible. Available online: https://www.ansible.com (accessed on 19 May 2019).
- Bianchi, G.; Biton, E.; Blefari-Melazzi, N.; Borges, I.; Chiaraviglio, L.; de la Cruz Ramos, P.; Eardley, P.; Fontes, F.; McGrath, M.J.; Natarianni, L.; et al. Superfluidity: A Flexible Functional Architecture for 5G Networks: G. Bianchi et al. Trans. Emerging Tel. Tech. 2016, 27, 1178–1186. [Google Scholar] [CrossRef]
- Cisco Cloud Service Router 100V Series. Available online: https://www.cisco.com/c/en/us/products/routers/cloud-services-router-1000v-series/index.html (accessed on 19 May 2019).
- Fortinet- FortiGate Virtual Appliance. Available online: https://www.fortinet.com/content/dam/fortinet/assets/data-sheets/FortiGate_VM.pdf (accessed on 19 May 2019).
- Elastic Stack. Available online: https://www.elastic.co/ (accessed on 19 May 2019).
- Ferran, C.; Mimidis-Kentis, A.; Bonourn, N.; Soler, J. Policy Framework Prototype for ONOS. In Proceedings of the 2019 IEEE Conference on Network Softwarization (NetSoft), Paris, France, 24–28 June 2019; Available online: http://orbit.dtu.dk/files/170742254/PID5809349.pdf (accessed on 19 May 2019).
- Kubernetes. Available online: https://kubernetes.io/ (accessed on 19 May 2019).
- The Helm Package Manager for Kubernetes. Available online: https://helm.sh/ (accessed on 19 May 2019).
- NGPaaS Deliverable 5.6: Final platform prototype for 5G PaaS. June 2019. Available online: http://ngpaas.eu/projectoutcomes/#ngpaasdeliverables (accessed on 19 May 2019).
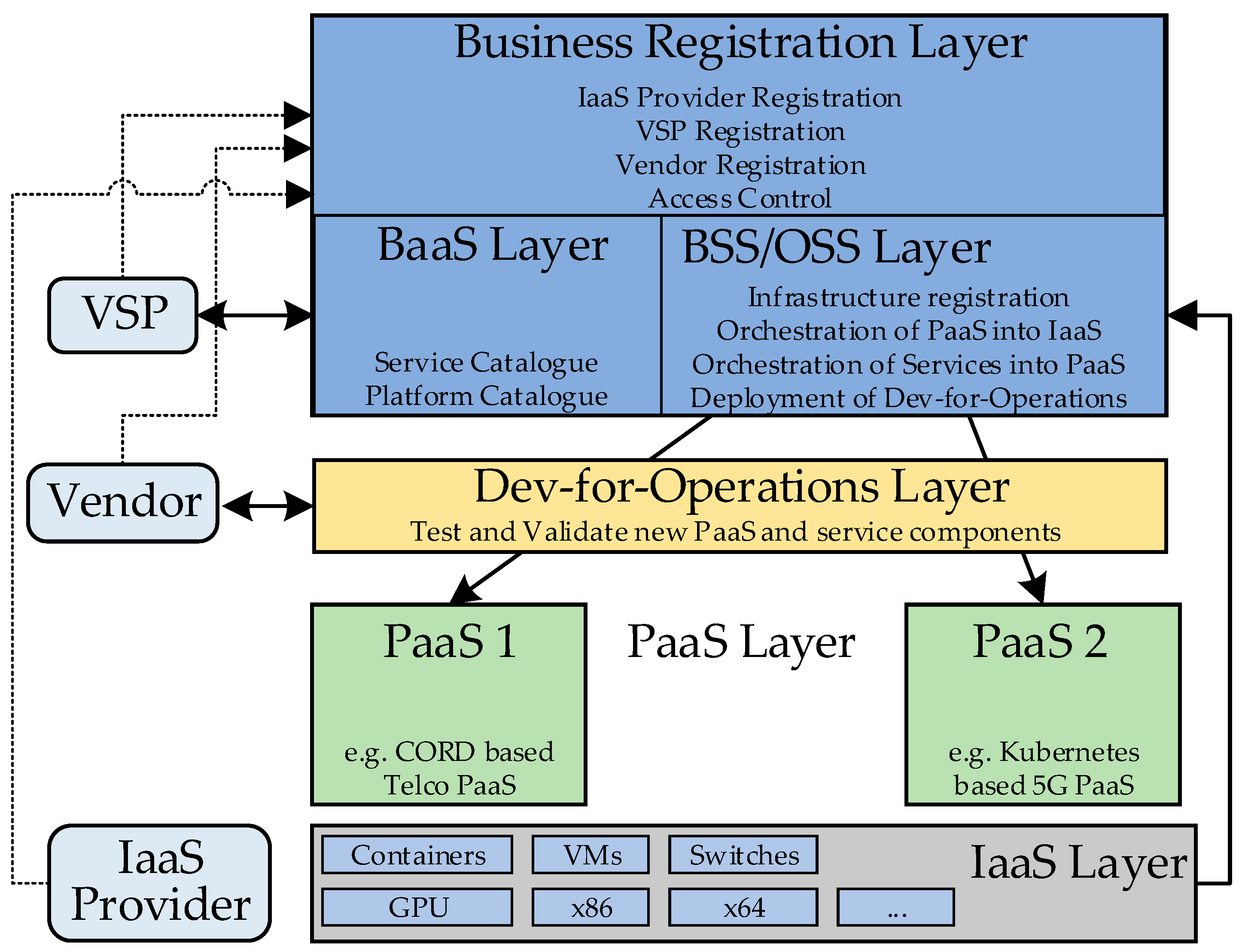



| NGPaaS Layer | Description |
|---|---|
| Business Registration | Registers all stakeholders that participate in NGPaaS (VSPs, Vendors, etc.). It also includes the resolution of access and execution rights. |
| BaaS | A customisable catalogue from which to order service or platform workloads. |
| BSS/OSS | Responsible for inventory registration, global supervision, and deployment of services and platforms on their execution environments. In our prototype, the BSS/OSS role [26] is fulfilled by the RDCL 3D tool. |
| Dev-for-Operations | An environment to support the innovative NGPaaS Dev-for-Operations model—an evolution of the existing DevOps model to facilitate new types of interaction and development methods between multiple stakeholders. This environment is where staging and development are performed to bring new PaaS or service components into NGPaaS [27]. |
| PaaS | PaaS components are deployed on the available (declared) infrastructure. These PaaS components form the framework to manage the VNFs included in the requested services. More than one PaaS instances can be active and managed at the same time by the OSS/BSS. |
| IaaS | This layer relates to the cloud infrastructure available to the NGPaaS operator. |
| NGPaaS Process | Details |
|---|---|
| Infrastructure registration | A generic provisioning process to support the broad spectrum of available infrastructure technologies. According to the use-case and the required services, the appropriate infrastructure nodes are leased and registered in the OSS. |
| PaaS orchestration | Refers to the deployment of selected PaaS components on the appropriate IaaS. The PaaS could be Kubernetes, CORD, or any other platform. The PaaS components can be aggregated flexibly and modelled as RFBs. This capability could not be implemented using ETSI MANO, which is focused only on VNFs and assumes the platform is already deployed. |
| Service orchestration | A service is provided by deploying VNFs as sets of RFBs. The target execution environment of each VNF is included in the metadata of the related RFBs, which also specify the runtime aspect: VM, container, Unikernel, FPGA Bitstream, etc. The execution environment of a service component is a pre-deployed PaaS which supports the runtime aspects of the RFB. |
| Onboarding new components | The design rule in NGPaaS is “everything is an RFB” (VNF, ancillary services like orchestration, SDN controller, etc.). Therefore, all the components could be updated, upgraded, swapped, etc. This can be done through the usage of the Dev-for-Operations processes. |
| RFB Category | Details |
|---|---|
| Pre-deployment Configuration RFBs | Responsible for configuring the target infrastructure node for the subsequent deployment of the CORD platform. An example is the cloning of remote source code repositories so that CORD can be later built from. |
| Deployment RFBs | These are the core RFBs, that when executed will provide with a functional CORD deployment on the infrastructure node. The majority of them are tied to the deployment of groups of containers, through the Helm tool. An example is the deployment of the XOS orchestrator or the ONOS SDNC. |
| Post-deployment configuration RFBs | These configure a CORD deployment for a specific use case or resolve possible issues that might have risen during the deployment of the CORD platform. An example is the registration of the CORD compute node to the ONOS SDNC. |
| RFB Name | RFB Role |
|---|---|
| k8s | Deploys Kubernetes, which manages all Docker containers comprising CORD. |
| Ingress | Deploys Ingress, a component related to Kubernetes which facilitates external access to services running in the cluster. |
| rabbitMq | Deploys RabbitMQ, the message broker used in OpenStack |
| Ceph | A set of RFBs that deploy ceph, the distributed storage component of OpenStack |
| marriaDB | Deploys marriaDB, the database for OpenStack |
| memCached | Deploys memcached, the distributed memory caching system for OpenStack |
| Heat | Deploys Heat, the OpenStack orchestrator. |
| Glance | Deploys Glance, the OpenStack image registry. |
| Keystone | Deploys Keystone, the OpenStack identity service. |
| openvSwitch | Deploys an OpenvSwitch, instance that connects all OpenStack VMs. |
| Nova | Deploys Nova, the computing service of OpenStack. |
| Neutron | Deploys Neutron, the networking service of OpenStack. In CORD Neutron is responsible for creating the networks connecting the different VMs. |
| openstackChart | Deploys the OpenStack service synchronizer of CORD. |
| addressManagerChart | Deploys a set of components, which enable public connectivity for VNFs. |
| onosChart | Deploys the ONOS synchronizer in CORD. |
| xosChart | Deploys the XOS synchronizer in CORD. |
| ngpaasserviceChart | Deploys the ngpaasService synchronizer. It also onboards the service model. |
| localVolumeChart | Deploys the persistent storage component of CORD. |
| clientSetup | Deploys the OpenStack client (Command Line Interface). |
| Libvirt | Deploys libvirt, the virtualisation service to be used by OpenStack |
| Docker | Deploys Docker on the target node. |
| dockerImageDownload | Downloads all CORD related Docker Images |
© 2019 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Mimidis-Kentis, A.; Soler, J.; Veitch, P.; Broadbent, A.; Mobilio, M.; Riganelli, O.; Van Rossem, S.; Tavernier, W.; Sayadi, B. The Next Generation Platform as A Service: Composition and Deployment of Platforms and Services. Future Internet 2019, 11, 119. https://doi.org/10.3390/fi11050119
Mimidis-Kentis A, Soler J, Veitch P, Broadbent A, Mobilio M, Riganelli O, Van Rossem S, Tavernier W, Sayadi B. The Next Generation Platform as A Service: Composition and Deployment of Platforms and Services. Future Internet. 2019; 11(5):119. https://doi.org/10.3390/fi11050119
Chicago/Turabian StyleMimidis-Kentis, Angelos, Jose Soler, Paul Veitch, Adam Broadbent, Marco Mobilio, Oliviero Riganelli, Steven Van Rossem, Wouter Tavernier, and Bessem Sayadi. 2019. "The Next Generation Platform as A Service: Composition and Deployment of Platforms and Services" Future Internet 11, no. 5: 119. https://doi.org/10.3390/fi11050119
APA StyleMimidis-Kentis, A., Soler, J., Veitch, P., Broadbent, A., Mobilio, M., Riganelli, O., Van Rossem, S., Tavernier, W., & Sayadi, B. (2019). The Next Generation Platform as A Service: Composition and Deployment of Platforms and Services. Future Internet, 11(5), 119. https://doi.org/10.3390/fi11050119






