Reviewing Cyber Security Social Engineering Training and Awareness Programs—Pitfalls and Ongoing Issues
Abstract
:1. Introduction
2. Methodology
3. Challenges of Trying to Keep a Step Ahead
3.1. Considerations with Social Engineering Training and Awareness Programs
3.1.1. Business Environmental
3.1.2. Social
3.1.3. Constitutional
3.1.4. Organizational
3.1.5. Economical
3.1.6. Personal
3.2. Review of Challenges Associated with Modern Social Engineering Training and Awareness Programs
3.3. Review of Challenges Associated with Traditional Social Engineering Training and Awareness Programs
3.4. Impacts of Challenges on the Security of Organizations
4. Strategies for Addressing Social Engineering Education and Awareness Challenges
5. Conclusions
Author Contributions
Funding
Conflicts of Interest
References
- Smith, A.; Papadaki, M.; Furnell, S.M. Improving awareness of social engineering attacks. In IFIP Advances in Information and Communication Technology; Springer: Berlin, Germany, 2013; Volume 406, pp. 249–256. [Google Scholar]
- Sallai, G. Social Engineering Audit and Security Awareness Programme; KPMG: Amstelveen, The Netherlands, 2016. [Google Scholar]
- Gollan, N.; Carew, N. Why Companies Are Exposed to Social Engineering. Available online: https://www.senseofsecurity.com.au/pdfs/Sense-of-Security-Whitepaper-Why-Companies-are-Exposed-to-Social%20Engineering-V1.0-09OCT2012.pdf (accessed on 15 March 2019).
- Aldawood, H.; Skinner, G. A Critical Appraisal of Contemporary Cyber Security Social Engineering Solutions: Measures, Policies, Tools and Applications. In Proceedings of the IEEE 26th International Conference on Systems Engineering, Sydney, Australia, 18–20 December 2018. [Google Scholar]
- Zulkurnain, A.U.; Hamidy, A.K.B.; Husain, A.B.; Chizari, H. Social engineering attack mitigation. Int. J. Math. Comput. Sci. 2015, 1, 188–198. [Google Scholar]
- Kumar, A.; Chaudhary, M.; Kumar, N. Social engineering threats and awareness: A survey. Eur. J. Adv. Eng. Technol. 2015, 2, 15–19. [Google Scholar]
- Castellano, G.; Leite, I.; Pereira, A.; Martinho, C.; Paiva, A.; McOwan, P.W. Detecting engagement in hri: An exploration of social and task-based context. In Proceedings of the 2012 International Conference on Privacy, Security, Risk and Trust (PASSAT) and 2012 International Confernece on Social Computing (SocialCom), Amsterdam, The Netherlands, 3–5 September 2012; pp. 421–428. [Google Scholar]
- Shostack, A. Threat Modeling: Designing for Security; John Wiley & Sons: Hoboken, NJ, USA, 2014. [Google Scholar]
- Beckers, K.; Pape, S. A serious game for eliciting social engineering security requirements. In Proceedings of the 2016 IEEE 24th International Requirements Engineering Conference (RE), Beijing, China, 12–16 September 2016; pp. 16–25. [Google Scholar]
- Aldawood, H.; Skinner, G. Educating and raising awareness on cyber security social engineering: A literature review. In Proceedings of the 2018 IEEE International Conference on Teaching, Assessment, and Learning for Engineering (TALE), Wollongong, NSW, Australia, 4–7 December 2018; pp. 62–68. [Google Scholar]
- Aldawood, H.; Skinner, G. Challenges of implementing training and awareness programs targeting cyber security social engineering. In Proceedings of the International Conferences on Cyber Security and Communication Systems, Melbourne, Australia, 10–12 December 2018. [Google Scholar]
- Aldawood, H.; Skinner, G. An academic review of current industrial and commercial cyber security social engineering solutions. In Proceedings of the 2019 the 3rd International Conference on Cryptography, Security and Privacy, Kuala Lumpur, Malaysia, 19–21 January 2019. [Google Scholar]
- Wang, D.; Cheng, H.; Wang, P.; Yan, J.; Huang, X. A security analysis of honeywords. In Proceedings of the 25th Annual Network and Distributed System Security Symposium, San Diego, CA, USA, 18–21 February 2018. [Google Scholar]
- Gulati, R. The Threat of Social Engineering and Your Defense Against It. Available online: https://www.scribd.com/document/55172071/The-Threat-of-Social-Engineering-and-Your-Defense-Against-It (accessed on 15 March 2019).
- Hackett, R. Yahoo raises breach estimate to full 3 billion accounts, by far biggest known. Available online: http://fortune.com/2017/10/03/yahoo-breach-mail/ (accessed on 15 March 2019).
- Ragan, S. Weebly data breach affects 43 million customers. Available online: https://www.csoonline.com/article/3133031/weebly-data-breach-affects-43-million-customers.html (accessed on 15 March 2019).
- Heim, P. Resetting passwords to keep your files safe. Available online: https://blog.dropbox.com/topics/company/resetting-passwords-to-keep-your-files-safe (accessed on 15 March 2015).
- Weir, C. Cracking the Myspace List—First Impressions. Available online: https://reusablesec.blogspot.com/2016/07/cracking-myspace-list-first-impressions.html (accessed on 15 March 2019).
- Dudovskiy, J. Research methodology. Retr. Febr. 2016, 5, 2017. [Google Scholar]
- Long-Sutehall, T.; Sque, M.; Addington-Hall, J. Secondary analysis of qualitative data: A valuable method for exploring sensitive issues with an elusive population? J. Res. Nurs. 2011, 16, 335–344. [Google Scholar] [CrossRef]
- Ruggiano, N.; Perry, T.E. Conducting secondary analysis of qualitative data: Should we, can we, and how? Qual. Soc. Work 2017, 18, 81–97. [Google Scholar] [CrossRef]
- Kpakol, A. Re-Engineering Corporate Culture for Organizational Receptivity to Change. Eur. J. Bus. Manag. 2014, 6, 167–176. [Google Scholar]
- Apăvăloaie, E.-I. The impact of the internet on the business environment. Procedia Eco. Financ. 2014, 15, 951–958. [Google Scholar] [CrossRef]
- Wilcox, H.; Bhattacharya, M.; Islam, R. Social engineering through social media: An investigation on enterprise security. In Proceedings of the International Conference on Applications and Techniques in Information Security, Lisbon, Portugal, 16–20 November 2014; pp. 243–255. [Google Scholar]
- Greitzer, F.L.; Strozer, J.R.; Cohen, S.; Moore, A.P.; Mundie, D.; Cowley, J. Analysis of unintentional insider threats deriving from social engineering exploits. In Proceedings of the 2014 IEEE Security and Privacy Workshops (SPW), San Jose, CA, USA, 17–18 May 2014; pp. 236–250. [Google Scholar]
- Airehrour, D.; Vasudevan Nair, N.; Madanian, S. Social engineering attacks and countermeasures in the new zealand banking system: Advancing a user-reflective mitigation model. Information 2018, 9, 110. [Google Scholar] [CrossRef]
- Wilcox, H.; Bhattacharya, M. Countering social engineering through social media: An enterprise security perspective. In Lecture Notes in Computer Science (Including Subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics); Springer: Cham, Switzerland, 2015; Volume 9330, pp. 54–64. [Google Scholar]
- Alseadoon, I.; Chan, T.; Foo, E.; Gonzales Nieto, J. Who is more susceptible to phishing emails? A saudi arabian study. In Proceedings of the 23rd Australasian Conference on Information Systems, Geelong, Australia, 3–5 December 2012; pp. 1–11. [Google Scholar]
- Mohebzada, J.G.; El Zarka, A.; BHojani, A.H.; Darwish, A. Phishing in a university community: Two large scale phishing experiments. In Proceedings of the 2012 International Conference on Innovations in Information Technology (IIT), Abu Dhabi, UAE, 18–20 March 2012; pp. 249–254. [Google Scholar]
- Dhamija, R.; Tygar, J.D.; Hearst, M. Why phishing works. In Proceedings of the SIGCHI Conference on Human Factors in Computing Systems, New York, NY, USA, 22–27 April 2006; pp. 581–590. [Google Scholar]
- Sheng, S.; Holbrook, M.; Kumaraguru, P.; Cranor, L.F.; Downs, J. Who falls for phish? A demographic analysis of phishing susceptibility and effectiveness of interventions. In Proceedings of the SIGCHI Conference on Human Factors in Computing Systems, New York, NY, USA, 10–15 April 2010; pp. 373–382. [Google Scholar]
- Justin, S.; Anastasios, A. Social engineering as a threat to societies: The cambridge analytica case. Available online: https://www.realcleardefense.com/articles/2018/07/18/social_engineering_as_a_threat_to_societies_the_cambridge_analytica_case_113620.html (accessed on 15 March 2019).
- Costa, L.P.d.S.; Figueira, A.C.R. Political risk and internationalization of enterprises: A literature review. Cadernos EBAPE 2017, 15, 63–87. [Google Scholar] [CrossRef]
- Gardner, B.; Thomas, V. Building an Information Security Awareness Program: Defending against Social Engineering and Technical Threats; Elsevier: Amsterdam, The Netherlands, 2014. [Google Scholar]
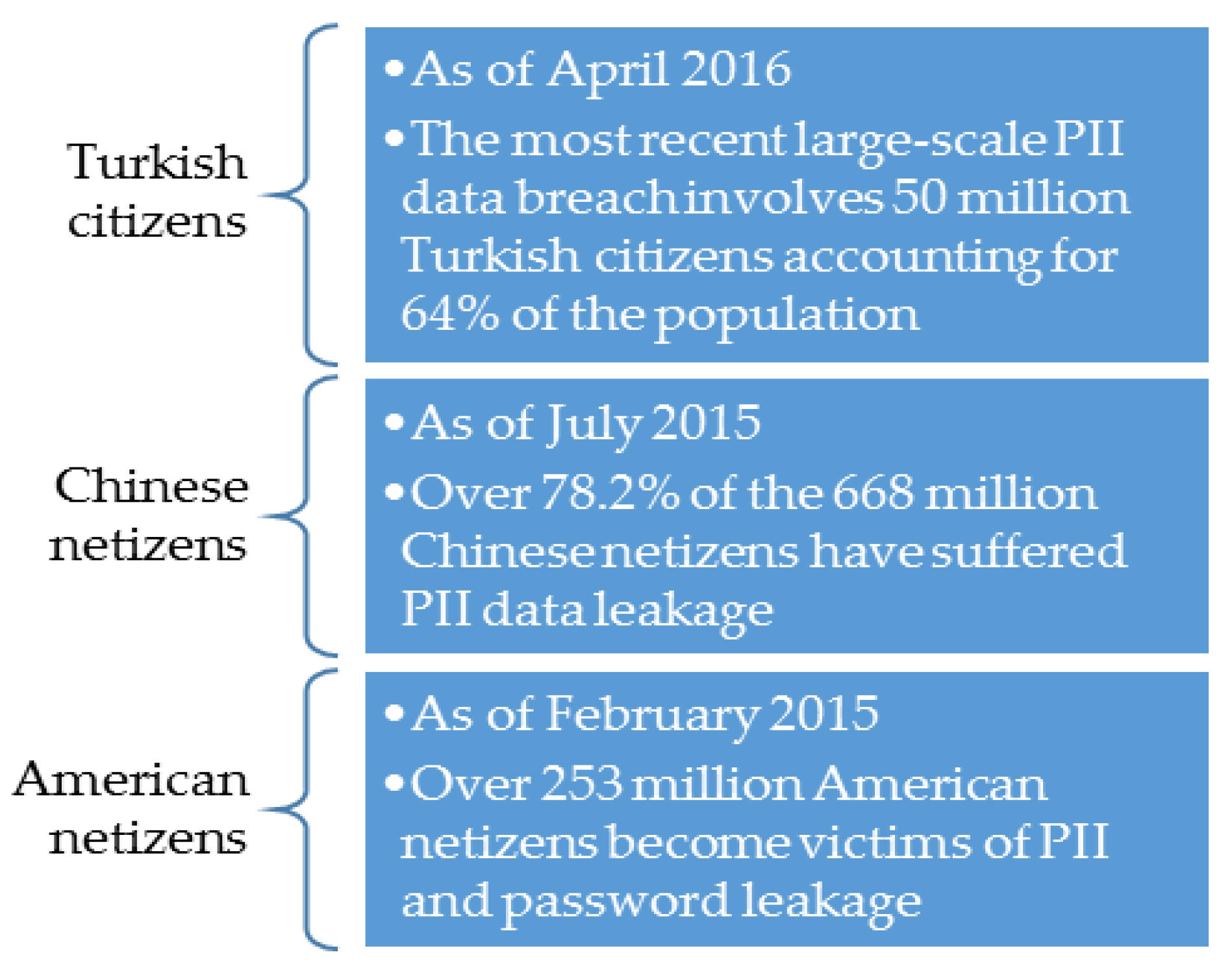
- Chappell, S. Turkey: Personal data of 50 million citizens leaked online, hackers claim. Euronews, 6 April 2016. [Google Scholar]
- Yan, W. Nearly 80 Percent of Internet Users Suffer Identity Leaks. Available online: http://www.chinadaily.com.cn/china/2015-07/24/content_21400381.htm (accessed on 18 March 2019).
- Pham, T. Four Years Later, Anthem Breached Again: Hackers Stole Credentials. Available online: https://duo.com/blog/four-years-later-anthem-breached-again-hackers-stole-employee-credentials (accessed on 15 March 2019).
- Krombholz, K.; Hobel, H.; Huber, M.; Weippl, E. Advanced social engineering attacks. J. Inf. Secur. Appl. 2015, 22, 113–122. [Google Scholar] [CrossRef]
- Thomas, K.; Li, F.; Zand, A.; Barrett, J.; Ranieri, J.; Invernizzi, L.; Markov, Y.; Comanescu, O.; Eranti, V.; Moscicki, A. Data breaches, phishing, or malware? Understanding the risks of stolen credentials. In Proceedings of the 2017 ACM SIGSAC Conference on Computer and Communications Security, Dallas, TX, USA, 30 October–3 November 2017; pp. 1421–1434. [Google Scholar]
- Wang, D.; Zhang, Z.; Wang, P.; Yan, J.; Huang, X. Targeted online password guessing: An underestimated threat. In Proceedings of the 2016 ACM SIGSAC Conference on Computer and Communications Security, Vienna, Austria, 24–28 October 2016; pp. 1242–1254. [Google Scholar]
- Butavicius, M.; Parsons, K.; Pattinson, M.; McCormac, A. Breaching the human firewall: Social engineering in phishing and spear-phishing emails. arXiv, 2016; arXiv:1606.00887. [Google Scholar]
- Financial Services Sector—Specific Plan 2015. Available online: https://www.dhs.gov/sites/default/files/publications/nipp-ssp-financial-services-2015-508.pdf (accessed on 15 March 2019).
- Atkins, B.; Huang, W. A study of social engineering in online frauds. Open J. Soc. Sci. 2013, 1, 23. [Google Scholar] [CrossRef]
- Abawajy, J. User preference of cyber security awareness delivery methods. Behav. Inf. Technol. 2014, 33, 237–248. [Google Scholar] [CrossRef]
- Frumento, E.; Puricelli, R.; Freschi, F.; Ariu, D.; Weiss, N.; Dambra, C.; Cotoi, I.; Roccetti, P.; Rodriguez, M.; Adrei, L. The Role of Social Engineering in Evolution of Attacks. Available online: https://www.dogana-project.eu/images/PDF_Files/D2.1-The-role-of-SE-in-the-evolution-of-attacks.pdf (accessed on 15 March 2019).
- Hadnagy, C.; Aharoni, M.; O’Gorman, J. Social Engineering Capture the Flag Results. In Proceedings of the Defcon 18, Las Vegas, NV, USA, 30 July–1 August 2010. [Google Scholar]
- Magee, T. The Most Common Social Engineering Attacks. Available online: https://www.techworld.com/picture-gallery/security/most-common-social-engineering-attacks-3681385/ (accessed on 15 March 2019).
- Reicher, H. Building inclusive education on social and emotional learning: Challenges and perspectives–a review. Int. J. Inclus. Educ. 2010, 14, 213–246. [Google Scholar] [CrossRef]
- Conteh, N.Y.; Schmick, P.J. Cybersecurity: Risks, vulnerabilities and countermeasures to prevent social engineering attacks. Int. J. Adv. Comput. Res. 2016, 6, 31. [Google Scholar] [CrossRef]
- Pazey, B.L.; Cole, H.A. The role of special education training in the development of socially just leaders: Building an equity consciousness in educational leadership programs. Educ. Admin. Q. 2013, 49, 243–271. [Google Scholar] [CrossRef]
- Jansson, K. A Model for Cultivating Resistance to Social Engineering Attacks. Ph.D. Thesis, Nelson Mandela Metropolitan University, Port Elizabeth, South Africa, September 2011. [Google Scholar]
- Mann, I. Hacking the Human: Social Engineering Techniques and Security Countermeasures; Routledge: London, UK, 2017. [Google Scholar]
- Hadnagy, C. Social Engineering: The Art of Human Hacking; John Wiley & Sons: Hoboken, NJ, USA, 2010. [Google Scholar]
- Jacobs, J.R. Measuring the Effectiveness of the Usb Flash Drive as a Vector for Social Engineering Attacks on Commercial and Residential Computer Systems; Embry Riddle Aeronautical University: Cadiz, Spain, 2011. [Google Scholar]
- Bhakta, R.; Harris, I.G. Semantic analysis of dialogs to detect social engineering attacks. In Proceedings of the 2015 IEEE International Conference on Semantic Computing (ICSC), Anaheim, CA, USA, 7–9 February 2015; pp. 424–427. [Google Scholar]
- Fujikawa, M.; Nishigaki, M. A study of prevention for social engineering attacks using real/fake organization. In Proceedings of the 2011 Sixth International Conference on Availability, Reliability and Security, Vienna, Austria, 22–26 August 2011; pp. 597–602. [Google Scholar]
- Irani, D.; Balduzzi, M.; Balzarotti, D.; Kirda, E.; Pu, C. Reverse social engineering attacks in online social networks. In Proceedings of the International Conference on Detection of Intrusions and Malware, and Vulnerability Assessment, Amsterdam, The Netherlands, 7–8 July 2011; pp. 55–74. [Google Scholar]
- Bullée, J.-W.H.; Montoya, L.; Pieters, W.; Junger, M.; Hartel, P.H. The persuasion and security awareness experiment: Reducing the success of social engineering attacks. J. Exp. Criminol. 2015, 11, 97–115. [Google Scholar] [CrossRef]
- Peery, J.; Pasalar, C. Designing the Learning Experiences in Serious Games: The Overt and the Subtle—The Virtual Clinic Learning Environment; Informatics; Multidisciplinary Digital Publishing Institute: Basel, Switzerland, 2018; p. 30. [Google Scholar]
- Shostack, A. Elevation of Privilege: Drawing Developers into Threat Modeling. In Proceedings of the 3GSE, San Diego, CA, USA, 18 Auguest 2014. [Google Scholar]
- Line, M.B.; Moe, N.B. Understanding collaborative challenges in it security preparedness exercises. In Proceedings of the IFIP International Information Security Conference, Hamburg, Germany, 26–28 May 2015; pp. 311–324. [Google Scholar]
- Hadnagy, C. Unmasking the Social Engineer: The Human Element of Security; John Wiley & Sons: Hoboken, NJ, USA, 2014. [Google Scholar]
- Gil, F.; Chamarro, A.; Oberst, U. Po-14: Addiction to online social networks: A question of "fear of missing out"? J. Behav. Addict. 2015, 4, 51–52. [Google Scholar]
- Beckers, K.; Krautsevich, L.; Yautsiukhin, A. Analysis of social engineering threats with attack graphs. In Data Privacy Management, Autonomous Spontaneous Security, and Security Assurance; Springer: Cham, Switzerland, 2015; pp. 216–232. [Google Scholar]
- Molok, N.N.A.; Chang, S.; Ahmad, A. Information Leakage through Online Social Networking: Opening the Doorway for Advanced Persistence Threats. In Proceedings of the 8th Australian Information Security Mangement Conference, Perth, Australia, 30 November 2010. [Google Scholar]
- Kim, E.B. Recommendations for information security awareness training for college students. Inf. Manag. Comput. Secur. 2014, 22, 115–126. [Google Scholar] [CrossRef]
- Talib, S.; Clarke, N.L.; Furnell, S.M. An analysis of information security awareness within home and work environments. In Proceedings of the 2010 International Conference on Availability, Reliability and Security, Krakow, Poland, 15–18 February 2010; pp. 196–203. [Google Scholar]
- Olusegun, O.J.; Ithnin, N.B. People Are the Answer to Security: Establishing a Sustainable Information Security Awareness Training (ISAT) Program in Organization. arXiv, 2013; arXiv:1309.0188. [Google Scholar]
- Ghafir, I.; Prenosil, V.; Alhejailan, A.; Hammoudeh, M. Social engineering attack strategies and defence approaches. In Proceedings of the 2016 IEEE 4th International Conference on Future Internet of Things and Cloud (FiCloud), Vienna, Austria, 22–24 August 2016; pp. 145–149. [Google Scholar]
- Caputo, D.D.; Pfleeger, S.L.; Freeman, J.D.; Johnson, M.E. Going spear phishing: Exploring embedded training and awareness. IEEE Secur. Privacy 2014, 12, 28–38. [Google Scholar] [CrossRef]
- Vishwanath, A.; Herath, T.; Chen, R.; Wang, J.; Rao, H.R. Why do people get phished? Testing individual differences in phishing vulnerability within an integrated, information processing model. Decis. Support Syst. 2011, 51, 576–586. [Google Scholar] [CrossRef]
- Halevi, T.; Lewis, J.; Memon, N. Phishing, personality traits and facebook. arXiv, 2013; arXiv:1301.7643. [Google Scholar]
- Kansal, P. Online privacy concerns and consumer reactions: Insights for future strategies. J. Indian Bus. Res. 2014, 6, 190–212. [Google Scholar] [CrossRef]
- Hardy, C.A.; Williams, S.P. Managing information risks and protecting information assets in a web 2.0 era. In Proceedings of the Bled eConference, Bled, Slovenia, 20–23 June 2010; p. 25. [Google Scholar]
- Workman, M.; Bommer, W.H.; Straub, D. Security lapses and the omission of information security measures: A threat control model and empirical test. Comput. Hum. Behav. 2008, 24, 2799–2816. [Google Scholar] [CrossRef]
- Colwill, C. Human factors in information security: The insider threat–who can you trust these days? Inf. Secur. Tech. Rep. 2009, 14, 186–196. [Google Scholar] [CrossRef]
- Young, K. Policies and procedures to manage employee internet abuse. Comput. Hum. Behav. 2010, 26, 1467–1471. [Google Scholar] [CrossRef]
- Abraham, S.; Chengalur-Smith, I. An overview of social engineering malware: Trends, tactics, and implications. Technol. Soc. 2010, 32, 183–196. [Google Scholar] [CrossRef]
- Luo, X.; Brody, R.; Seazzu, A.; Burd, S. Social engineering: The neglected human factor for information security management. Inf. Resour. Manag. J. 2011, 24, 1–8. [Google Scholar] [CrossRef]
- Chitrey, A.; Singh, D.; Singh, V. A comprehensive study of social engineering based attacks in india to develop a conceptual model. Int. J. Inf. Netw. Secur. 2012, 1, 45. [Google Scholar] [CrossRef]
- Alavi, R.; Islam, S.; Mouratidis, H.; Lee, S. Managing social engineering attacks-considering human factors and security investment. In Proceedings of the HAISA, Lesvos, Greece, 1–3 July 2015; pp. 161–171. [Google Scholar]
- Shah, S.; Mehtre, B.M. An overview of vulnerability assessment and penetration testing techniques. J. Comput. Virol. Hack. Tech. 2015, 11, 27–49. [Google Scholar] [CrossRef]
- Parsons, K.; McCormac, A.; Butavicius, M.; Pattinson, M.; Jerram, C. Determining employee awareness using the human aspects of information security questionnaire (hais-q). Comput. Secur. 2014, 42, 165–176. [Google Scholar] [CrossRef]
- Bosworth, S.; Kabay, M.E.; Whyne, E. Computer Security Handbook; John Wiley & Sons: Hoboken, NJ, USA, 2014. [Google Scholar]
- Tsohou, A.; Karyda, M.; Kokolakis, S. Analyzing the role of cognitive and cultural biases in the internalization of information security policies: Recommendations for information security awareness programs. Comput. Secur. 2015, 52, 128–141. [Google Scholar] [CrossRef]
- Glaspie, H.W.; Karwowski, W. Human factors in information security culture: A literature review. In Proceedings of the International Conference on Applied Human Factors and Ergonomics, Orlando, FL, USA, 21–25 July 2017; pp. 269–280. [Google Scholar]
- Tsohou, A.; Karyda, M.; Kokolakis, S.; Kiountouzis, E. Managing the introduction of information security awareness programmes in organisations. Eur. J. Inf. Syst. 2015, 24, 38–58. [Google Scholar] [CrossRef]
- Bartnes, M.; Moe, N.B. Challenges in it security preparedness exercises: A case study. Comput. Secur. 2017, 67, 280–290. [Google Scholar] [CrossRef]
- Beckers, K.; Fries, V.; Groen, E.C.; Pape, S. Creativity techniques for social engineering threat elicitation: A controlled experiment. In Proceedings of the REFSQ Workshops, Essen, Germany, 27 February 2017. [Google Scholar]
- Bhardwaj, T.; Sharma, T.K.; Pandit, M.R. Social engineering prevention by detecting malicious urls using artificial bee colony algorithm. Available online: https://link.springer.com/chapter/10.1007/978-81-322-1771-8_31 (accessed on 15 March 2019).
- Knowbe4. Security Awareness Training. Available online: https://www.itsecuritytraining.com.au/resources/knowbe4-security-awareness-training (accessed on 15 March 2019).
- Mataracioglu, T.; Ozkan, S. User awareness measurement through social engineering. arXiv, 2011; arXiv:1108.2149. [Google Scholar]
| Target | Attack Date | Passwords Revealed on | No. of Passwords Compromised |
|---|---|---|---|
| Yahoo | 2013 | October 2017 | 3 billion [15] |
| Weebly | February 2016 | October 2016 | 43 million [16] |
| Dropbox | 2012 | May 2016 | 68 million [17] |
| Myspace | 2008 | May 2016 | 360 million [18] |
© 2019 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Aldawood, H.; Skinner, G. Reviewing Cyber Security Social Engineering Training and Awareness Programs—Pitfalls and Ongoing Issues. Future Internet 2019, 11, 73. https://doi.org/10.3390/fi11030073
Aldawood H, Skinner G. Reviewing Cyber Security Social Engineering Training and Awareness Programs—Pitfalls and Ongoing Issues. Future Internet. 2019; 11(3):73. https://doi.org/10.3390/fi11030073
Chicago/Turabian StyleAldawood, Hussain, and Geoffrey Skinner. 2019. "Reviewing Cyber Security Social Engineering Training and Awareness Programs—Pitfalls and Ongoing Issues" Future Internet 11, no. 3: 73. https://doi.org/10.3390/fi11030073
APA StyleAldawood, H., & Skinner, G. (2019). Reviewing Cyber Security Social Engineering Training and Awareness Programs—Pitfalls and Ongoing Issues. Future Internet, 11(3), 73. https://doi.org/10.3390/fi11030073