1. Introduction
The proliferation of smart objects and their connectivity have contributed to the realization of Internet of Things (IoT) paradigm; their features and services have revolutionized our daily life. These smart devices are equipped by different means of communication to access the Internet [
1], creating what it is called the smart environment. Different technologies such as WiFi, Bluetooth, NFC, and recently WiFi P2P (WiFi-Direct) can be used to enable IoT device-to-device (D2D) communication and providing more functionalities to enhance the user experience [
2].
Currently, all data traffic must pass through a fixed infrastructure in the different wireless cellular network generations, regardless of the device’s location. However, to avoid overloading the infrastructures, it is better to enable direct inter-device communication when possible. When devices are in proximity of each other, problems of radio access network load and core network load are observed [
3]. One of the methods used to overcome these limitations and effectively manage local group communication while offloading data from the cellular network is to establish direct communication between the nearby devices, and this kind of communication is called IoT D2D communication.
Unlike the conventional scenario, where cellular operators are the main middleware handling all inter-device communication within their communication range, IoT D2D communication is a new computing paradigm that allows two proximate mobile devices to directly connect and communicate with each other without the presence of any intermediate authority [
4].
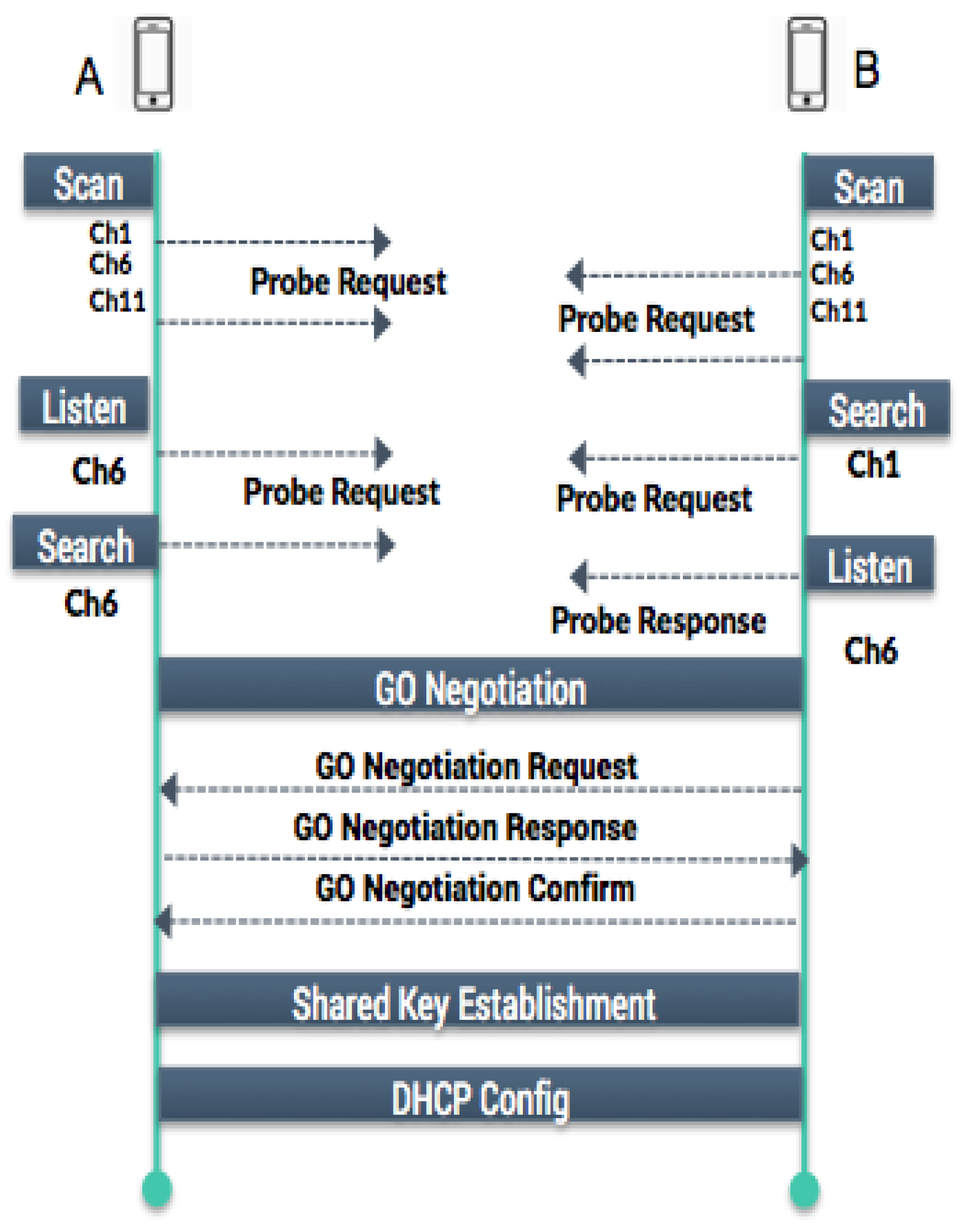
The IoT D2D concept is directly related to the used wireless technologies. D2D can be implemented with technologies such as Bluetooth, WiFi-Direct, and LTE Direct, to name a few. Each of them is characterized by its maximum transmission distance, maximum data rate, and the devices’ discovery mode, as summarized in
Table 1.
In this work we consider the use of WiFi P2P technology known as WiFi Direct due to its high bandwidth value with 250 Mbps surpassing the LTE Direct and Bluetooth [
5], also for its agreeable range which can expand to 200 m, and finally, for the easiest way to discover neighbors for D2D users using the ID Broadcast -the MAC address of mobile devices in most of cases.
Since IoT D2D communications are over wireless channels, which are broadcast in nature, many existing attacks can affect them and exploit their vulnerability. Hence, security solutions ensuring efficient authentication and confidentiality are a must [
6,
7]. To perform an efficient authentication between users, establishing a shared secret key is an important step. The common solution is the use of the traditional Diffie-Hellman key agreement; however, it suffers from its vulnerability to the man in the middle (MITM) Attack. On the other hand, relying on a hash value of the shared secret key can provide secrecy to the communication protocol, but the size of the information to be compared by IoT D2D users poses a problem. In previous works, the shared secret key must be compared visually or verbally by D2D users. We propose a solution to avoid this human mediation.
In this paper, we propose the Secure Key Exchange with QR Code (SeKeQ) protocol. Our proposal serves as a key establishment protocol between IoT D2D users using Diffie-Hellman for key exchange and SHA256 hash function for digital signature of the shared secret key. Furthermore, our proposal is fully autonomous and does not require human mediation. Finally, we use the generated secret key to ensure data confidentiality by encrypting the communication traffic over wireless channel. The performance evaluation comparing SeKeQ to other existing solutions shows that it can ensure a secure communication with fast key generation and less resource consumption.
The remainder of this paper is organized in the following fashion:
Section 2 presents an overview about WiFi-Direct and some cyber-attacks that may affect D2D communication. Afterwards, we discuss the related works in
Section 3.
Section 4 introduces the proposed protocol called SeKeQ for key exchange with QR Code.
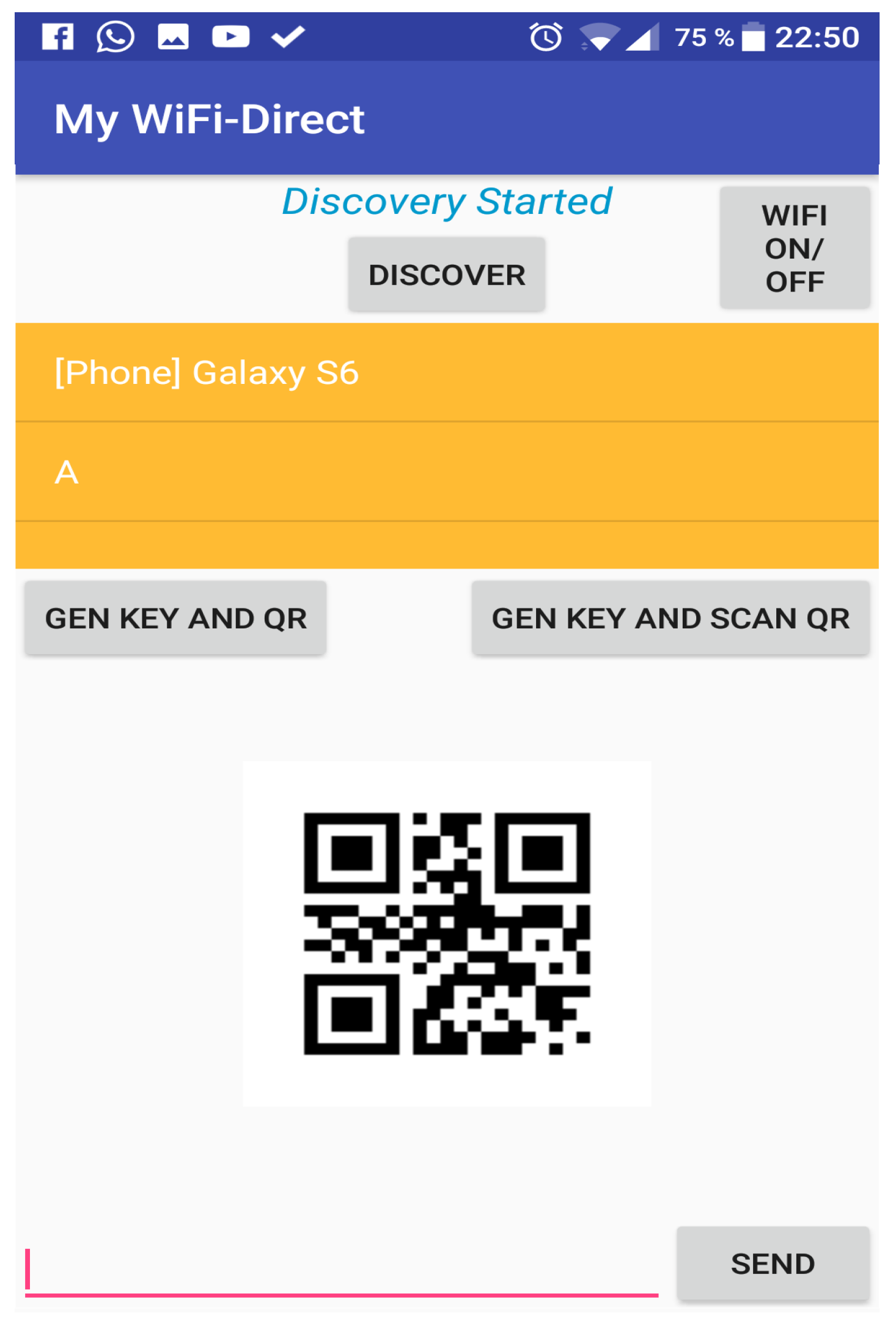
Section 5 shows the experimental setup represented by an implementation of our proposaed solution in an Android application.
Section 6 summarizes our results and comparison with other proposals and security analysis. Finally,
Section 7 concludes the paper.
3. Related Works
Security and Privacy from Mobile Ad-hoc Networks to D2D has been discussed in [
14]. Security and Privacy requirements ensure that only authorized group users are able to consume group services, that data exchanged among group users must not be sent in clear nor changed or modified during transmission. Taking into account that D2D communication is mainly based on group concept, the most significant step is a shared secret among group users for key agreement procedure.
The authors in [
16] proposed key agreement for P2P based online social networks in a face to face pre-authentication through a location limited channels for identifying legitimate P2P users. They provide a Message Authentication Code as a customized hash function for digital signature ensuring simultaneous users identification for better efficiency and less messages to be authenticated. However, their proposal is limited by the weakness of the old used hash function and the key size. An implementation of [
17] has proved that an adversary can bypass the authentication as a normal group user exploiting the man in the middle attack. Another drawback that their hash-based protocol is not cost effective which makes it inadequate for devices with limited resources.
The authors in [
18] proposed a key agreement protocol based on Diffie-Hellman and Commitment Scheme. The aim was to overcome the vulnerability of MITM Attack that infects Diffie-Hellman key agreement in a first place, and to settle the comparison of large number of bits (128 bits-32 hexadecimal digits-) as the Hash Value of Diffie-Hellman key. The proposed commitment scheme is secure and provides a 20 bits (5 Hexadecimal digits) as the shared key and is quietly. However, this protocol requires a visual or verbal comparison to be mutually authenticated, which makes it a non-trivial task and remains a critical issue.
Another solution was discussed in [
19] where Diffie-Hellman key exchange (DHKE) and HMAC digital signature was proposed to provide authentication and to verify the identity of each user in D2D communication underlying LTE-Advanced networks (LTE-A). They also proposed a confidentiality protocol that encrypts data from source to destination by symmetric key encryption. However, many intermediarery nodes are involved in the key generation and key exchange processes, namely the the eNB (Evolved NodeB) and the GW (Gateway) that are responsible for this task. Since the channel might be compromised for a direct communication among devices, this solution is not feasible to secure in hostile environment.
In [
20] an ID-based AK protocol with signature is proposed. The security of AK protocols has relied on the intractability of the Diffie-Hellman problem and the related problem of computing discrete logarithms. Thereafter, they propose two efficient secure AK protocols satisfying perfect forward secrecy based on tripartite ID-based authenticated key agreement protocol with signature, and smart protocol based on ID-based authenticated key agreement protocol with key confirmation. Although Protocol 1 provides desirable security attributes. The second proposed protocol appears to have the security attributes of known-key security, perfect forward secrecy, unknown key-share and key control. However, both protocols stay limited to the less efficiency on message bandwidth where each entity sends two key components.
The SHC protocol proposed in [
21] refers to Short Hash Code represented by a Diffie-Hellman key agreement with MD5 Hash, this protocol takes as an input the DH key exchanged among mobile devices, then provides a message digit composed of 128 bits as an output. However, it stays limited to its hash code length, therefore, using at least 48 bits as the hexadecimal size of hash remains a necessary solution to prevent the man-in-the-middle attack.
In [
22] an authentication protocol called MANA algorithm which stands for Manual Authentication, and is based on a conventional MAC function which is HMAC [
23] in Key exchange; mobile devices generate Diffie-Hellman parameters with the addition of a commitment represented by a MAC (Message Authentication Code) value on each device and are considered as an output to be displayed on both devices for authentication but it remains unknown to an external attacker. However, its limitation remains on that the key size remains very short (around of 16–20 bits) and can be rapidly predicted within seconds by an adversary due to nowadays huge computers capacity, also this protocol shows its inefficiency on wireless channel with the addition of the high time length during the key exchange the DH parameter with unique MAC value generation on each group device.
The other solution, named UMAC [
24] (Universal-Hashing MAC) and it is a one-time authenticator; a long sub-key is calculated once for authenticating mobile users and have not to be revealed to an attacker, it is based on HMAC with SHA1 hash algorithm. However, this solution takes more time for performing authentication credentials among mobile devices due to the HMAC function and its slow nature on generating the message authentication code. In addition, this UMAC occupies memory resources more than the ordinary during key generation by performing the HMAC value in first step followed by the SHA1 with its 160 bits.
The approach we present in the current study outpeforms other proposals in term of security, performance, time lapse and memory consumption. First, the designed SeKeQ protocol is very strong regarding security considerations because of the SHA256 hash algrothim used that is hard to be broken by adversaries with the addition of AES protocol used for encryption of transmitted messages during communication of legitimate users. In addition, the protocol shows the fastest time of key generation and exchange time compared to other algorithms while maintaining an optimized consumption of memory size allocation and CPU usage. All these metrics results the best performance of the SeKeQ protocol compared to SHC, MANA and UMAC.
Our proposed SeKeQ outperforms the existing works in term of security performance, time lapse, and memory occupancy thanks to the use of SHA256 hash with the encryption of transmitted inter-users messages using AES, thus, making SeKeQ hard to break by the different kinds of adversaries. In addition, the protocol shows the fastest time of key generation and exchange compared to the existing works while maintaining an optimized occupancy of memory and acceptable CPU usage.
4. SeKeQ: Secure Key Exchange with QR Code Protocol
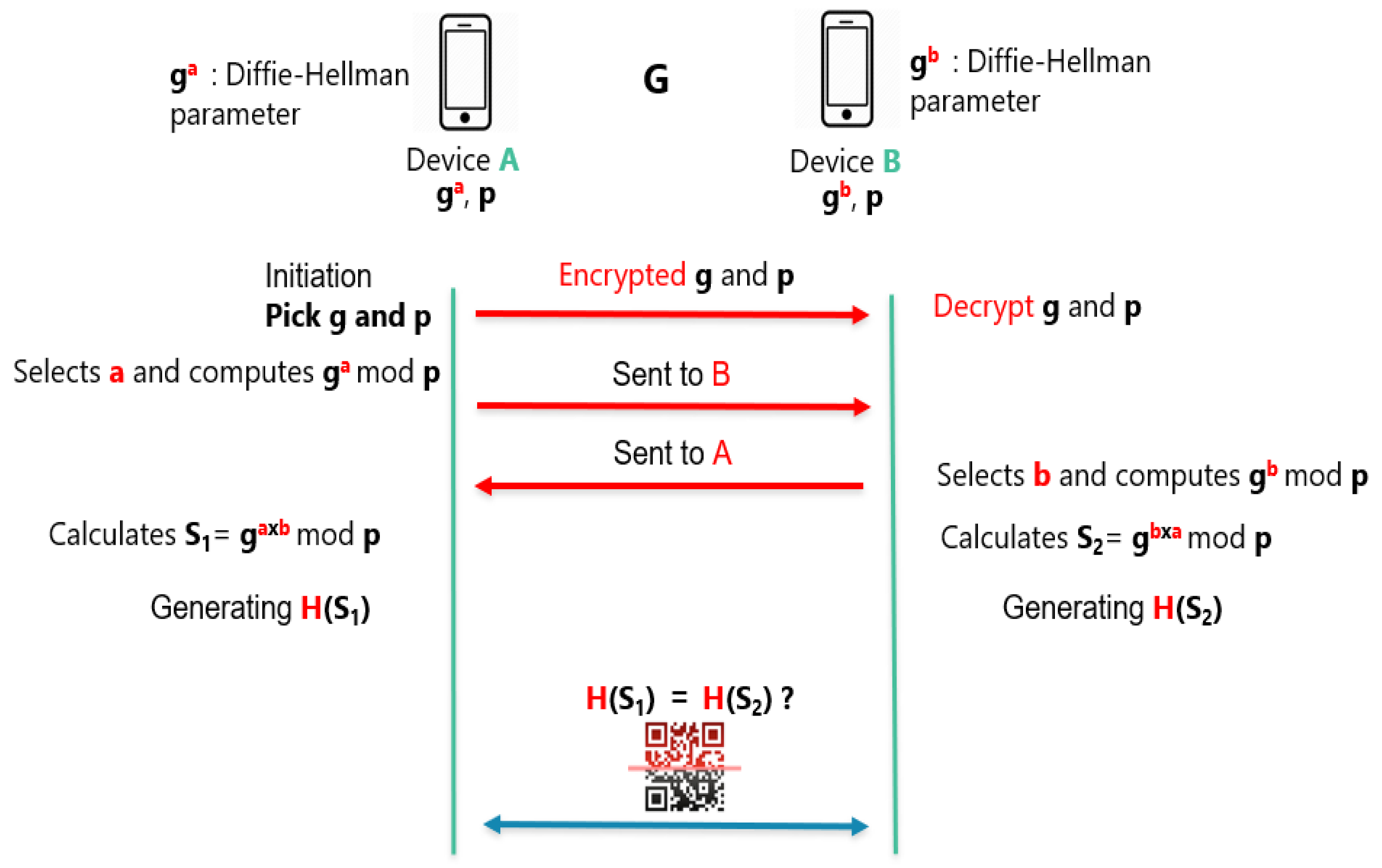
Our protocol SeKeQ works as follows; Devices A and B agree on finite group G from with multiplication modulo a prime number p. In addition, users generate random numbers for key exchange on field. They exchange these random numbers modulo p on our key agreement process.
Devices A and B agree in clear over wireless channel on prime large p and a generator g from field, we call them the key pair. They are exchanged as follows, A creates its own Diffie-Hellman key pair with 2048 bits key size and initializes its Diffie-Hellman Key Agreement object. Then, A encodes its public key, and sends it over to B. On device B, it has received A public key in an encoded format, it instantiates a Diffie-Hellman public key from the encoded key material. B gets the Diffie-Hellman parameters associated with A public key. Then, it must use the same parameters when it generates its own key pair. At this stage, both A and B have completed the Diffie Hellman agreement on the key pair p and g.
Then A selects its private random number a and calculates and sends the result publicly to B. Now, B selects its private random number b and calculates and sends this result to A. In the next step, the calculation of the shared secret begins, A takes B public result and raises it to the power of its private number a mod p to obtain the shared secret, called . Then, B takes A public result and raises it to the power of its private number b mod p resulting on a shared secret called . It is worth noticing that both devices did the same calculation. As we see, it is an efficient key agreement protocol but still vulnerable to the Man in the Middle attack. Which makes the studies fundamental to enhance the secrecy of the algorithm.
In the next step, and to provide a high security level, Devices A and B put their shared keys and , respectively, to a one way hash function, which is, in our case, SHA-256. They generate , the hash value of for device A and the hash value of for device B. The hash value is a large number. In our case, the hash value is represented by 32 Hexadecimal digits.
We should obtain
, since
and
are equal which is the adequate case for verifying the integrity of the shared secret key. However, the hash value have to be compared manually by D2D devices. The authors in [
18] proposed a key agreement based on Diffie-Hellman and commitment scheme. They succeed at reducing the large size of the hash value
, resulting 5 Hexadecimal digits as the size of the shared secret key. However, this proposal is still inefficient because it requires that the shared secret have to be compared visually or verbally by D2D users. To overcome this limitation, we propose an automatic key comparison process of the shared secret key by the use of the QR Code as an additional step of our SeKeQ protocol.
The QR code is a type of two-dimensional bar code (or matrix code) consisting of black modules or points arranged in a square with a white background. The arrangement of these points defines the information contained in the code. This information can be a website, text, phone number or an SMS [
25]. It is first generated containing the desired data which can go up to 4000 characters, and displayed as a picture on a computer, smartphone or printed on a paper. Then, with nowadays large mobile devices, using the device camera, the QR is scanned and results its content at high speeds. The QR Code have multiple application uses, such as storing information of patients in the medical field, scanning passenger’s coordination for accessing a facilities and private zones. In addition, it can be used for reliable verification of products before packaging. Companies use the QR Code for their banners, to make clients scan it to get more information about the publicity, or even it can be used for sending an email, setting a professional appointment and nowadays, stores uses the QR code for allowing their clients to know about a product by scanning a QR and getting more information. In our protocol, it is used to store the hash value of the shared secret key calculated on the P2P GO device.
Automatic key comparison process works as follows, since
and
should be equal, device A that is the Group Owner will fetch the value of its calculated result
into a new generated QR Code. By the following, device B, acting as a P2P client—with the help of the back camera—can scan the generated QR Code that contains the device A result
and save it as a new string called
N. Now, a system comparison will be in device B, comparing the scanned value
N with the value of its result
. If it matches, the communication between A and B is performed automatically without any verbal or visual comparison and both devices can start sharing their data now. The scenario of key exchange between users is shown in
Figure 2.
Providing a shared key as an authentication proposal among devices is securely efficient. However, while we generate the key exchange, we use it to guarantee data confidentiality. Making sure that data is not sent in clear over public channels and avoiding the possibility of a Man in the middle or Eavesdropping attack.
Since the devices are mutually authenticated, End-to-end encryption is used based on the generated shared secret key. Thereafter, we convert the key in an AES key format as a symmetric encryption key from the shared key. If the communication between users is a chat scenario, the messages are encrypted before getting ready to be sent. A user who wants to send a message, uses its shared secret key to provide an AES symmetric key for message encryption. After receiving the message in an encoded format, and while we are using symmetric encryption, which means that the encryption and decryption key are the same. The receiver uses the shared key to generate the AES key and decrypts the message.
6. Results and Discussion
The design of the key exchange protocol is based on the traditional Diffie-Hellman key agreement protocol, SHA256 hash function for digital signature of the shared secret and AES encryption to provide data confidentiality.
6.1. Security Analysis
Mobile users A and B calculate and respectively as the short authentication string for mutual authentication and then, they apply hash function for the shared key.
We assume that another device E is launching a Man In The Middle Attack by pretending to B to be A. First, it listens on the wireless channel and collects g and p, known as The key pair. It selects e and calculates . Next, it sends the hash value to B. After receiving B’s answer (hash value of ), E cannot edit hash value and resend it to A. Thus, in the mutual authentication step, A and B compare with but is different from and .
As a result, the key exchange scenario has been performed correctly. To provide confidentiality of all transmitted messages, the calculated shared secret is used to ensure AES encryption generating the symmetric key with a size of 128 bits that is hard to be broken by adversaries.
6.2. Performance Evaluation
To show the efficiency of our proposal, a comparison with the related solutions is needed. To this end, our experiments are based on the study in [
29], in which the authors provided a comparison between different key exchange protocols considering different metrics: Performance, Experiments, Disk space and Security.
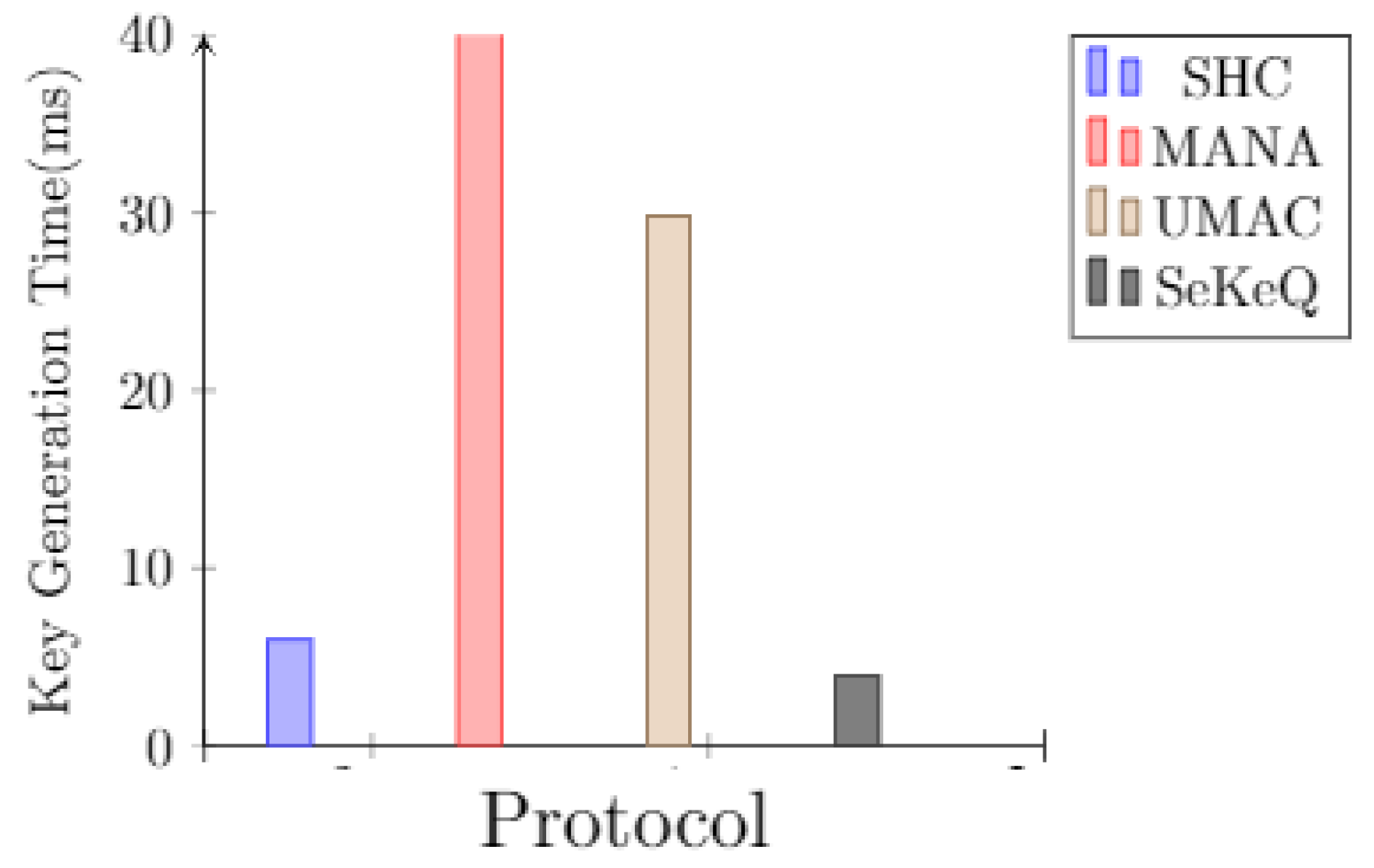
For an efficient comparison, we implement our SeKeQ protocol with the related solutions. Taking first, the SHC (Short Hash Code) using Diffie-Hellman key agreement with MD5 Hash. Secondly, the MANA (Manual Authentication) algorithm that actually use Diffie-Hellman for key exchange and HMAC for digital signature. The third solution, UMAC (Universal Message Authentication Code); the one-time authenticator based on HMAC with SHA1.
We used Python Scripts for implementing the studied algorithms (SeKeQ, UMAC, MANA and SHC) to compare time lapse, memory size allocation, CPU consumption and network throughput during the calculation and generation of the shared secret key between users. The experimentation for comparison were made on virtual devices and were not implemented for Android OS.Implementation results are shown in
Figure 4,
Figure 5,
Figure 6,
Figure 7 and
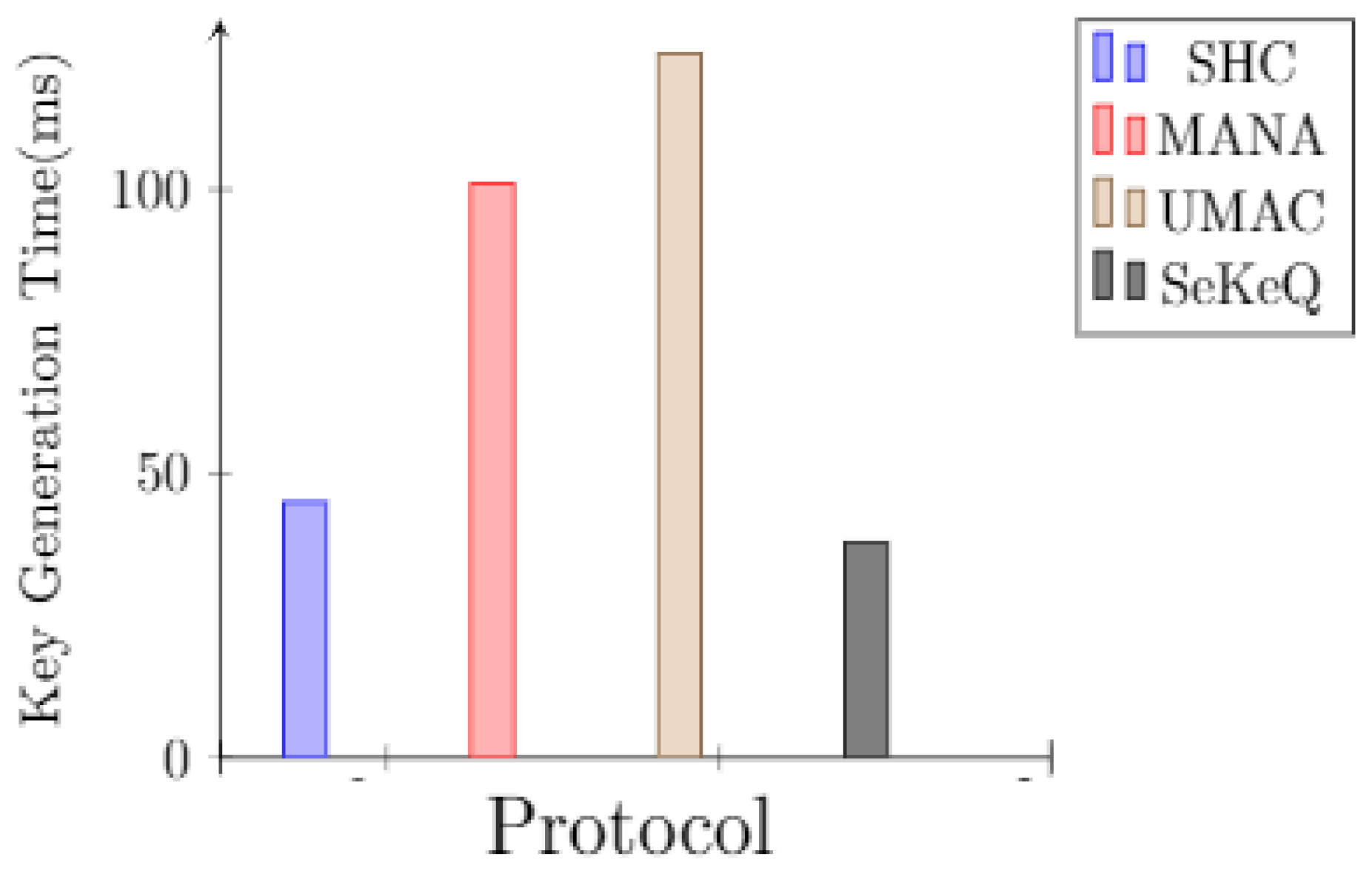
Figure 8. The figure below shows the cryptographic operations involved in the calculation of the shared key between users of each protocol. Comparing the amount of time for generating keys with the energy consumption of the shared secret with the time needed for generating keys on different bandwidths for each of the studied protocols. Time generation is represented in milliseconds, while size in memory is represented in Megabytes. Whereas, The network throughput is represented in kilobytes per second (Kb/s).
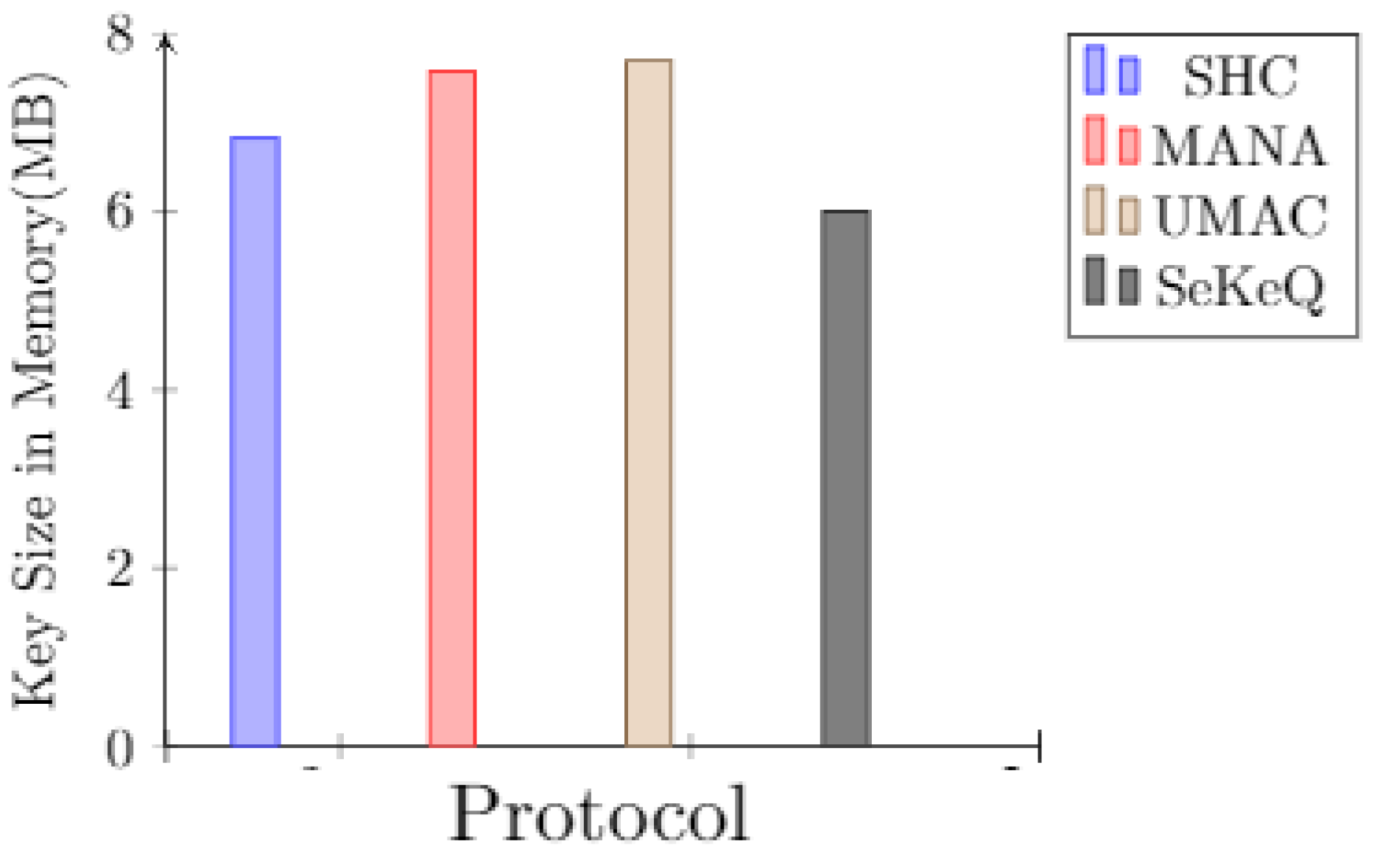
As known, one of the features of key based authentication, their ability to provide smaller key sizes as presented in
Figure 5. In addition, their rapidity on generating keys that is done within seconds as illustrated in
Figure 4. The MD5 hash used in SHC has 128 bits size of hash, it occupies 7 Mb during its 6 ms for key exchange. The length of the keys with HMAC as used in MANA can not surpass 20 bits, however it needs more than 8 Mb and remains the slowest with 40 ms when exchanging keys. While HMAC based SHA-1 proposed for UMAC algorithm is 160 bits and shows the same value in memory as the MANA while it takes 30 ms for key exchange. Finally, our protocol SeKeQ has 256 bits in length and we can obtain a better power and delay performance by representing 5.8 MB of key size allocation in memory and a perfect time for establishing the shared secret among devices with just 4 ms and shows good values compared to the others. Key size in memory has also an impact on the wireless channel performance, the more it is reduced, the more we get less communication overhead, less data overload, and better bandwidth on exchanging data among cellular devices.
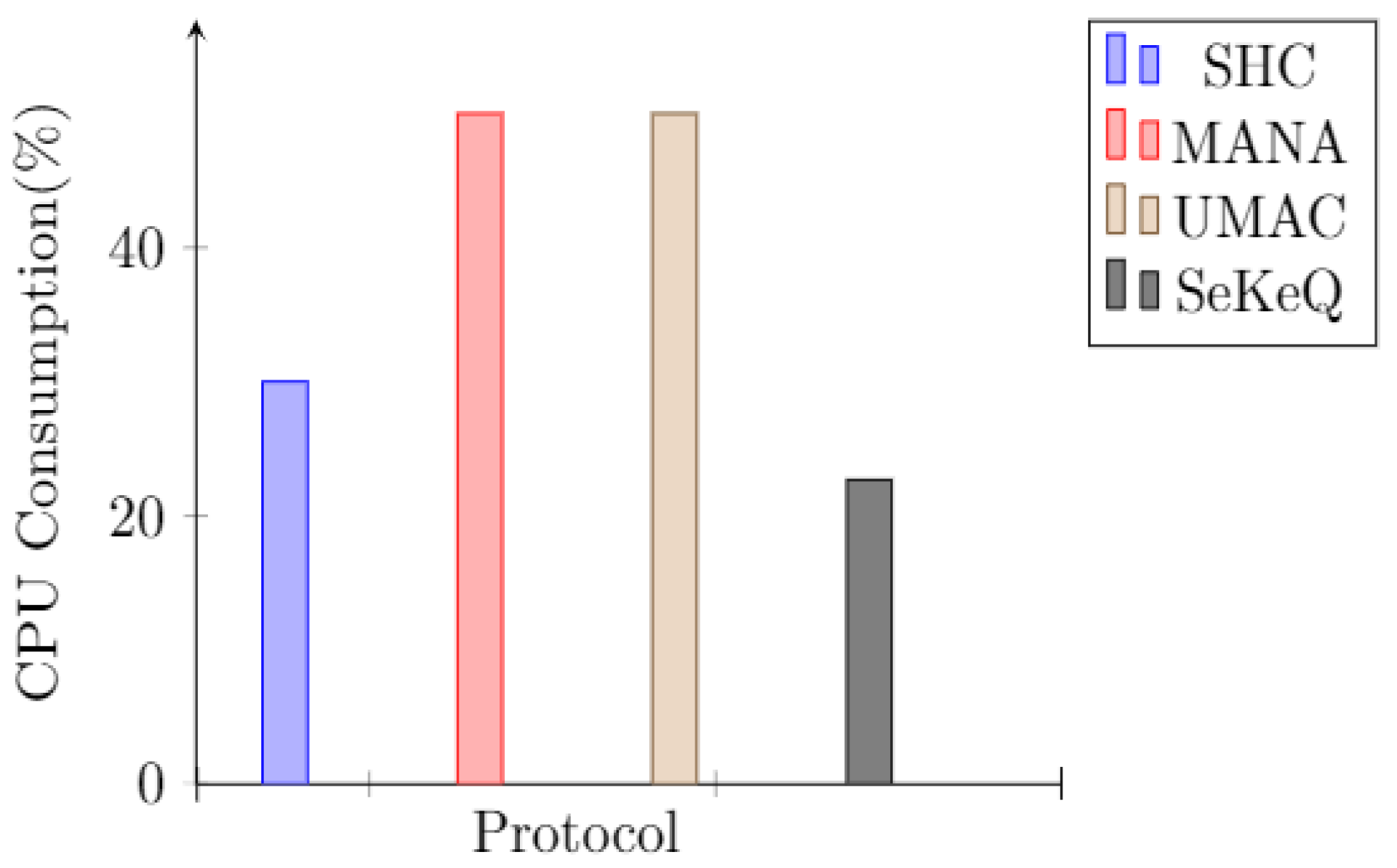
The results of CPU consumption are presented in
Figure 6. We can notice that the consumption of our scheme represented by 22.7% is less than CPU usage of SHC how stands with 30%, MANA and UMAC with the large 50% usage. Accordingly, these outperformed results of Time generation, Memory consumption and CPU usage, prove that the key exchange can be performed efficiently on mobile devices.
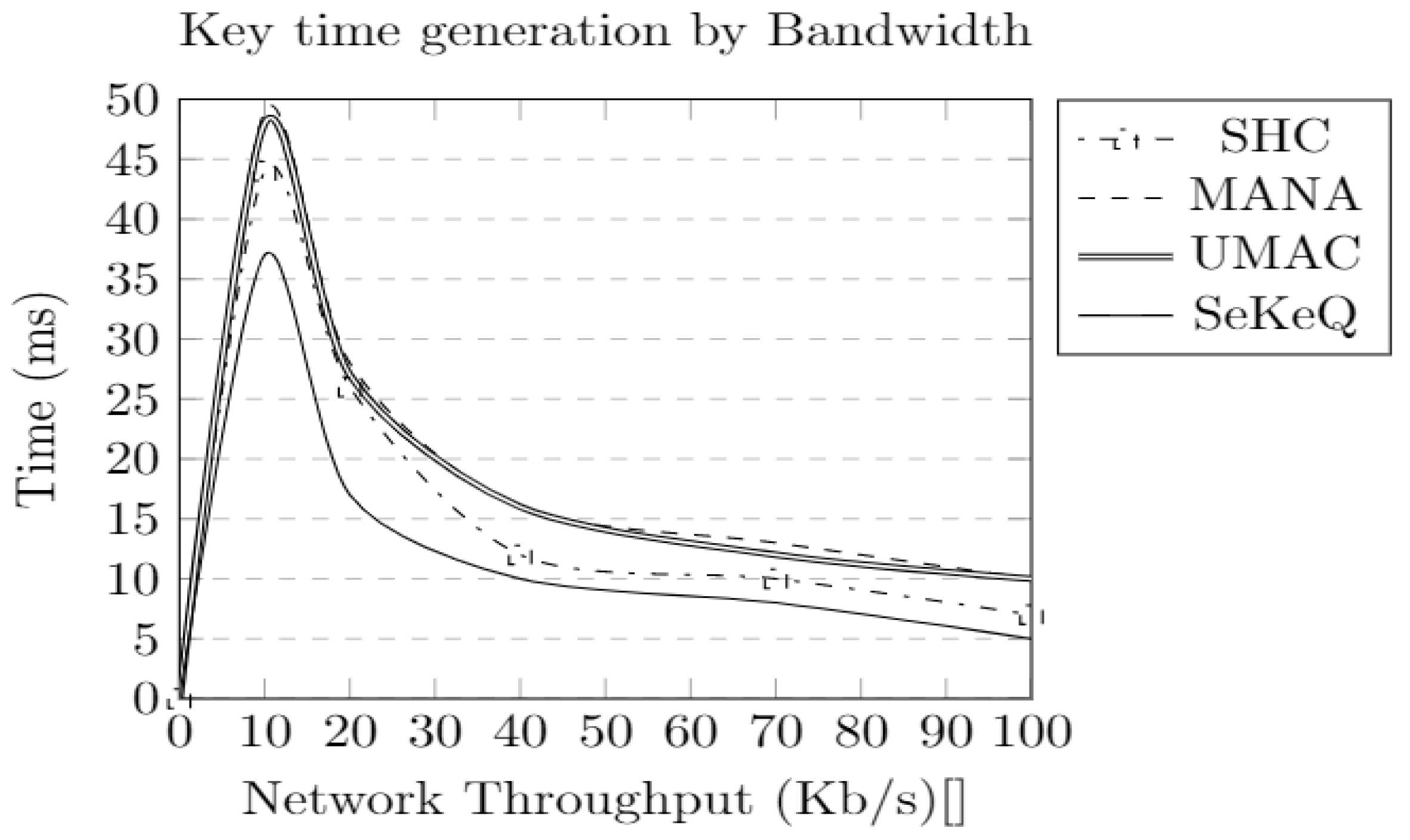
When fixing the bandwidth from low to high throughput in order to test the proposals in different situations, e.g., in environments with lower bandwidth.
Figure 8 shows that the generation time increases when the bandwidth decreases since the data transmission time increases rapidly when network throughput decreases for all protocols. However, the amount of time taken by our proposed SeKeQ protocol in different throughput degrees stays more stable compared to the others and can enhance largely the achievable data rate on each device. At the initial time, and with lowest throughput 10 Kb/s, all protocols have nearly the same key generation time. However, MANA and UMAC remains slower than the others for key generation even when network throughput increases. SHC results a medium duration of key generation on highest bandwidth.
We extend the comparison for a group with 3 users. First, all 3 users are from the same group. For that, the standard group formation is performed. The device elected as the GO acquits the other 2 clients with IP addresses from the same range. Thereafter, the GO have to establish a shared secret key with each of 2 other clients. In addition, the clients establish a shared secret for a secure direct communication between them. The number of needed keys depends on the following formula:
where
N is the number of group users and NK is the total number of keys for this group. In this case, 3 shared secret keys are needed regarding the 3 group users.
Figure 7 shows the amount of time elapsed for performing different keys generation. Our protocol SeKeQ surpass SHC, MANA and UMAC. The other protocols still take more time for establishing the shared secret. Due to the large size of hash in UMAC and its 2-key components. MANA also requires high time during generation regarding its inefficiency on wireless channel. Finally, SHC maintains good results with a small key size.
We can notice that the metrics for our protocol compared SekeQ with SHC are nearly equal. However, the research study in [
21] proved that an MD5 hash can be broken within seconds. For success, it requires an attacker to use significant resources, i.e., to perform one billion trials in less than 1 s. The time out of mobile users is assumed to be 10 s, which makes it easy for the attacker to, by a performing man in the middle with brute-force attack, prevent the 32 hexadecimal digits as a hash of MD5.
A comparison summary of different protocols is presented in
Table 2. Our results show clearly that our protocol SeKeQ outperforms SHC, MANA, and UMAC in terms of time generation of the shared secret maintaining less memory allocation and perfect time generation on different network throughput values. While SHC also has less memory allocation for key generation, it is limited to the brute-force attack, in which an attacker can predict the value of the short hash. MANA is also vulnerable to the man in the middle attack and provides long key generation time. UMAC shows a strong key size but with more key components due to its HMAC digital signature first, followed by SHA in a second step for providing a shared secret key.
This discussion forces us to go back to the cyber attacks. Our proposal avoids the man in the middle and eavesdropping attacks due to its efficiency ensuring secure key establishment among devices offering digital signature without giving strange users the ability to access D2D communication. In addition, DDoS and Jamming are settled by allowing only authorized users to use D2D services over wireless channel.
Besides the achieved performance, our proposal can be further improved through the use of a more lightweight hash function. We also plan to make the proposal flexible for large scale networks through the incorporation of Blockchain technology [
30].