1. Introduction
Dynamic environments are characterized by changes in their architecture, data flows, and operational processes. Such changes can appear periodically, continuously, or be event triggered. The Internet of Things (IoT) is a typical example of such an environment, with instantiations across various ecosystems such as smart homes, eHealth, vehicular networks, cloud computing and mobile communications. This dynamicity, along with the increased interconnectivity and enhanced operational features increase the attack surface of such ecosystems [
1].
Smart homes is a typical instantiation of a dynamic ecosystem where the ICT penetration is significant since several types of connected devices and locally or remotely deployed services leverage ICT. Many works in the literature have introduced definitions for the “smart home” [
2,
3,
4]. Smart homes can be defined by taking a social perspective or a technical viewpoint. The former describes the influence of the smart home to human and social needs, whilst the latter describes the systems, processes, services, and smart devices which are connected so as to facilitate control over the home’s ecosystem. A smart home is able to support diversified components and entities, such as utility suppliers, infrastructure providers and third party software or hardware vendors [
5]. Due to this diversity, the attack surface of the smart home is increasing rapidly, since more security vulnerabilities are introduced, paving the way to an unreliable and insecure ecosystem. To this end, the European Union Agency for Cybersecurity (ENISA) [
6] identified potential threats and proposed good practices for their mitigation.
Existing risk assessment methods are mostly suitable for static environments and systems. Dynamic environments such as those described above, require risk assessment methods able to cope with frequent changes in the environment. The scope of this work is to carry out a threat analysis for the smart home ecosystem, as the first step towards a comprehensive dynamic risk assessment method, by leveraging an existing smart home reference architecture.
Furthermore, by considering the technical viewpoint that defines the smart home environment, we design a smart home network topology generator, based on the existing reference architecture. Subsequently, to provide knowledge about the effects of the dynamic dependencies of the network on the propagation of a malware infection, we use the outputs provided by the topology generator to create a graph-based attack model. Our attack model is based on the initial hypothesis that at any given time
t each node can be observed at a discrete state and. subsequently, after homogeneous intervals of time
t, it can either transit to another state or remain at the current state. The model assumes types of malware that use either random or localized scanning techniques. A malware that employs random scanning selects target IP addresses at random [
7]. Localized scanning malware preferentially scans for hosts in the “local” address space, instead of selecting targets randomly [
7].
The contributions of this paper can be summarized as follows: (i) a review of dynamic risk assessment methodologies appropriate for identifying and assessing risks within the smart home ecosystem; (ii) a threat analysis on an existing smart home reference architecture focusing on the data flows and cloud services; (iii) an algorithm for modeling and visualizing the dynamic changes in a smart home topology; and (iv) a study of the propagation of a malware infection in such networks, with the use of connected graphs.
The remainder of this paper is structured as follows:
Section 2 reviews related work. In
Section 3, we describe the reference architecture of the smart home. In
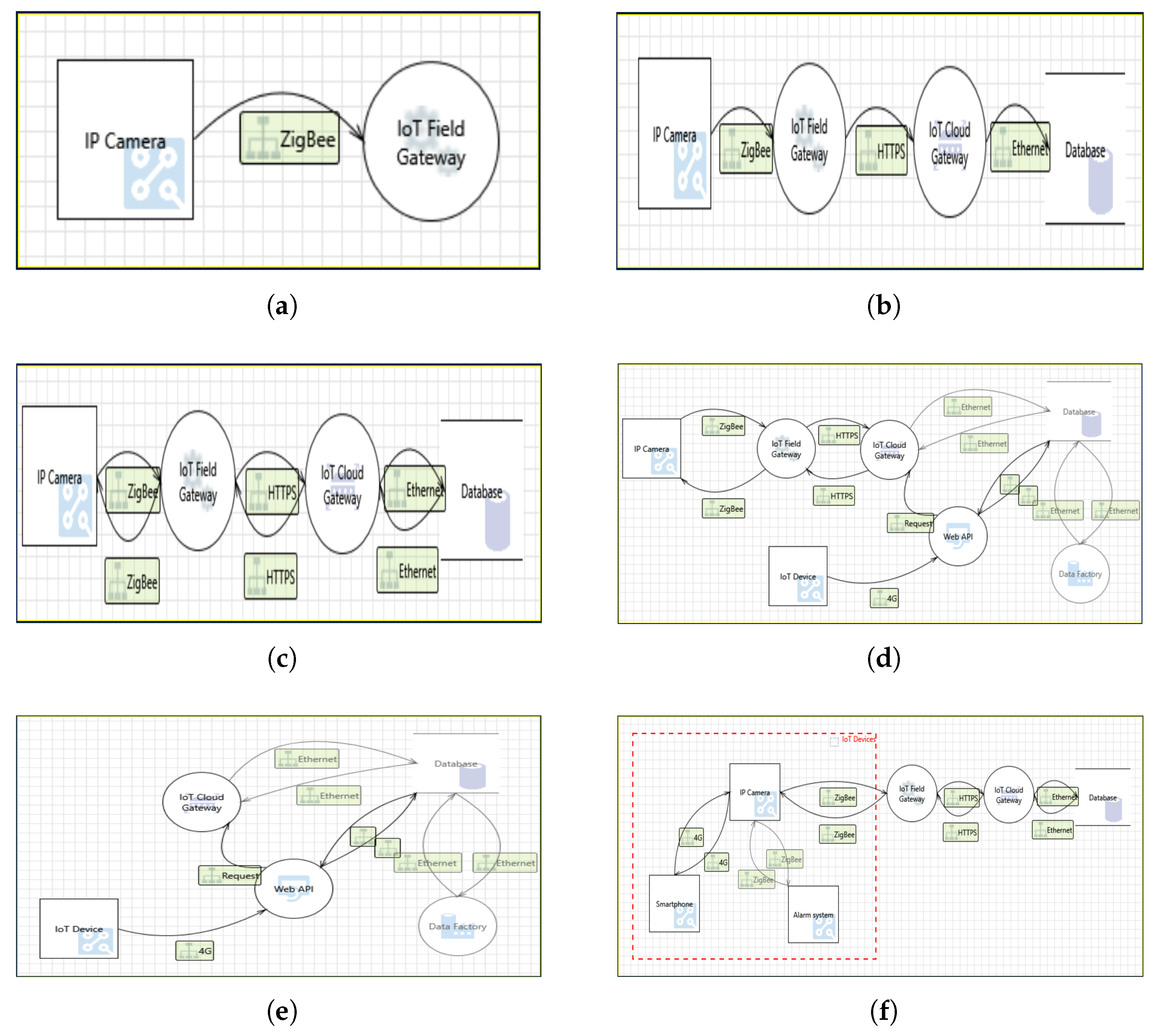
Section 4, we briefly discuss the STRIDE (Spoofing, Tampering, Repudiation, Information Disclosure, Denial of Service, and Elevation of Privileges) method and Microsoft’s threat analysis tool, and we apply them in smart home scenarios of various complexity, to identify threats and to establish the attack surface variability in dynamic environments. In
Section 5, we present the methodology used for developing a network topology generator, and, in
Section 6, we present the attack model. In
Section 7, we validate the outputs of the models previously designed by creating a network simulator. Finally, in
Section 8, we summarize our conclusions and we propose directions for future work.
This paper is an extended version of the paper entitled “Threat analysis in dynamic environments: The case of the smart home” by Georgios Kavallieratos, Vasileios Gkioulos and Sokratis Katsikas that was published in the Proceedings of the 1st International Workshop on Security and Reliability of IoT Systems (SecRIoT 2019), held in conjunction with the 15th International Conference on Distributed Computing in Sensor Systems (DCOSS), Santorini Island, Greece, 2019, pp. 234–240 © 2019 IEEE [
8]. Portions of the work in [
8] are reused in the present paper. In particular,
Section 1,
Section 2,
Section 3 and
Section 4 and
Section 8 follow closely [
8], with some changes of an editorial nature. The additional contribution of this work over [
8] is described in
Section 5,
Section 6 and
Section 7.
2. Related Work
Several risk assessment methodologies for dynamic environments have appeared in the literature. Merrick et al. [
9] proposed a risk modeling method for maritime transport. The authors considered simulations, expert judgment and available data, and proposed a method which handles multiple scenarios reflecting past, present and future operating procedures of the vessel’s ICT systems. Poolsappasit et al. [
10] developed a framework for dynamic risk management that uses Bayesian attack graphs to address security issues in a network system. Puppala et al. [
11] proposed a dynamic risk assessment system using an improved attack graph to assess dynamic risks in cloud computing, and proposed appropriate mitigation techniques. The authors used the Common Vulnerability Scoring system to initiate each node’s score in the attack graph. The Dynamical Risk Assessment Method for IoT inspired by AIS (DRAMIA) dynamic risk assessment method for the IoT was proposed by Kiu et al. [
12]. DRAMIA consists of attack detection agents and sub-systems of dynamic risk assessment, which adopt immune system principles in order to dynamically change the attack detectors and estimate the risk according to the detection results of all attack detection agents. Naumov et al. [
13] introduced a dynamic framework to assess cyber risks in continuously changing environments. However, this work is in a preliminary stage. The National technical authority for information assurance in the UK proposed a technical risk assessment and risk treatment standard [
14] that is able to assess risks in dynamic systems or services where components are being regularly upgraded or replaced. A risk assessment engine for assessing cyber risks in real-time was also proposed by the WISER-Wide-Impact cyber Security framework project [
15]. Specifically, machine-reliable risk assessment algorithms have been developed in order to facilitate the risk identification in dynamic environments. These algorithms take as inputs the business configuration, the vulnerability assessment, the network constraints and the application layer of the environment, to estimate the cyber risk. The aforementioned risk engines could in principle be used to assess risks in the smart home ecosystem.
Dynamic risk assessment tailored specifically to smart home environments has been addressed within the EU project GHOST-Safe—Guarding Home IoT Environments with Personalized Real-time Risk Control [
16]. The project has proposed a dynamic risk assessment model for real-time security and risk assessment on the ongoing activities over the network of a smart home, which may be implemented by means of a real time risk engine. Consequently, the risk assessment’s results remain valid since the engine is able to dynamically identify changes in the environment and to re-assess the risk taking into consideration these changes [
17].
The security of the smart home ecosystem has been studied in several works that seek to identify potential vulnerabilities, threats and risks in this dynamic environment. Schiefer [
18] demonstrated the challenges that risk analysis poses in a smart home installation, due to the heterogeneous nature of the IoT devices. Jacobsson et al. [
19] applied an information security risk assessment approach in the development phase of smart home automation systems. The authors identified nine low and four high level risks, and concluded that humans represent the highest risk exposure in smart home automation systems. Further, a risk framework for the smart home was proposed by Denning et al. [
5]. This framework focuses on the feasibility of an attack on the system, the attractiveness of the system as a compromised platform, and the damage caused by performing a successful attack. Its drawback is that it examines particular devices of the smart home and does not consider the data flows or the cloud services that are also crucial parts of the smart home’s ecosystem. The security of the information flow in the Home Area Network (HAN) of a smart grid was examined by Tong et al. [
20]. They identified the security levels of HAN devices and data packets, and proposed a security model which aims to protect such data flows over the HAN network. Ali et al. [
4] proposed the use of the Operationally Critical Threat, Asset, and Vulnerability Evaluation (OCTAVE) Alegro risk assessment method to identify potential risks in the smart home environment. They focused on the cyber and the physical layer of the smart home’s architecture, and they identified ten critical cyber and physical assets. Although they carried out a comprehensive risk assessment, they did not take into consideration the complexity of the smart services and devices. Additionally, Beckers et al. [
21] proposed a structured threat analysis method for smart home scenarios by leveraging Microsoft’s Security Development Lifecycle (SDL). In particular, they used a model-based method for the SDL’s threat analysis and they presented an attack path Data Flow Diagram (DFD) pattern in order to explain potential intrusions in the smart home environment.
A great deal of research has been conducted to analyze and validate network topology generators currently available. Haddadi et al. [
22] discussed techniques for inference, modeling, and generation of the Internet topology at both the router and administrative levels. They concluded that providing a realistic mapping of the Internet network is challenging, highlighting the importance of defining the physical interconnection of the nodes for routing and resilience purposes. Tangmunarunkit et al. [
23] compared structural topology generators to degree-based generators. They concluded that degree-based algorithms produce more accurate results that match the metrics used with higher fidelity than structural models. Nevertheless, they noted that choosing smaller topologies on which to run network simulations would likely provide a drastically different result. Tangmunarunkit et al. [
23] noted that a power-law distribution is almost meaningless if the number of nodes is small because, with only a few nodes, it is unlikely that the degree distribution will be able to create the implicit hierarchy necessary for modeling networks.
Attack modeling techniques and analysis have also been the focus of a large number of research works on cyber threat analysis [
24]. Cheng and Ji [
7] compared the performance of different malware propagation models through a spatial-temporal random process based on local interactions of nodes in networks. They concluded that a Markov model that incorporates both detailed topology information and simple spatial dependence achieves better overall results than the other models analyzed. One limitation of the model proposed by Cheng and Ji is that it does not specifically consider the states at which the nodes could be observed. Wang et al. [
25] proposed a discrete-state Markov model that assumes a network node to be observable in one of the five following states: vulnerable, infected, quarantined, healthy and disseminator.
5. Smart Home Topology Modeling
To effectively analyze the dependencies between the dynamic properties of a smart home network and security threats identified previously, we developed a smart home network topology modeling algorithm. To develop a generator that could provide knowledge and belief about the dynamic states of a smart home topology, in the form of annotated graphs, we first determined a layer-based reference architecture mapping based on the viewpoints discussed in
Section 3: functional, physical and communication. The proposed taxonomy is divided in five Layers:
The pseudocode in Algorithm 1 describes the procedural approach used to implement the graph generation algorithm and the condition needed to be satisfied in order to produce the output graph. The steps taken by the algorithm are further detailed in
Section 5.2 and
Section 5.3.
| Algorithm 1 Graph generation algorithm pseudocode. |
ifthen else while do end while end if ifthen for do end for end if ifthen else end if ifthen end if
|
IoT devices are represented in the graph as homogeneous components, as their typical network behavior—with a few exceptions—depends on the adopted communication protocol more than it does on their specific properties. The first step for the algorithm is to generate a vector of
n names
Nameip(Name1,…,Namen) for each input parameter
ip, where
n is equal to the input value associated with the input parameters described in
Table 3.
5.1. Node Generation
Afterwards, all the nodes corresponding to the IoT appliances at Layer 3 of the taxonomy are generated. For each hub NameH and gateway NameG, a normally distributed number of IoT devices nIoTH and nIoTG is generated. The values for the mean of the normal distribution have been set between 10 and 25 and for the standard deviation to 2, based on the usage share of the different protocols and the average number of devices that support these protocols. Name vectors IoTNi(IoTn1,…,IoTnm) and weight vectors IoTWi(IoTw1,…,IoTwm) associated to all m IoT vectors nIoTH and nIoTG are also generated. The weight vector corresponds to the physical distance between the IoT device IoTnamea and its associated hub NameH. The algorithm has now generated all the nodes that compose Layers 0–4 of the taxonomy.
5.2. Edge Generation
Next, the algorithm generates the edges between the nodes. Network generators come in two families, namely structure-based that attempt to create a hierarchical structure and degree-based that focus solely on the degree distribution [
23]. A degree-based approach was discarded in favor of a structural approach that took into consideration topological information of different communication protocols. All clouds
NameC, hubs
NameH, smartphones
NameS and PCs
NamePC are connected to exactly one gateway
NameG. The scalability of the dependencies for the connections between all IoT appliances
IoTnamea and their hubs
NameH has been reduced to ensure clarity and comprehensibility of the final graph. For this reason, we opted to adopt partial mesh topology networks as the standard arrangement for the nodes in a sub-network formed by each hub
NameH and its associated appliances
IoTnamea. The weight vectors
IoTWi(IoTw1,…,IoTwm) previously generated are now used to determine whether an IoT device IoTname
a is connected directly to a hub
NameH or to a router node
IoTnb. If the weight value
IoTw(c) is lower than the maximum range
RH supported by the hub’s protocol, then the device is connected directly to
NameH. If
IoTw(c) is greater than
RH, then the device is connected to a router node
IoTnb, which itself is directly connected to
NameH.
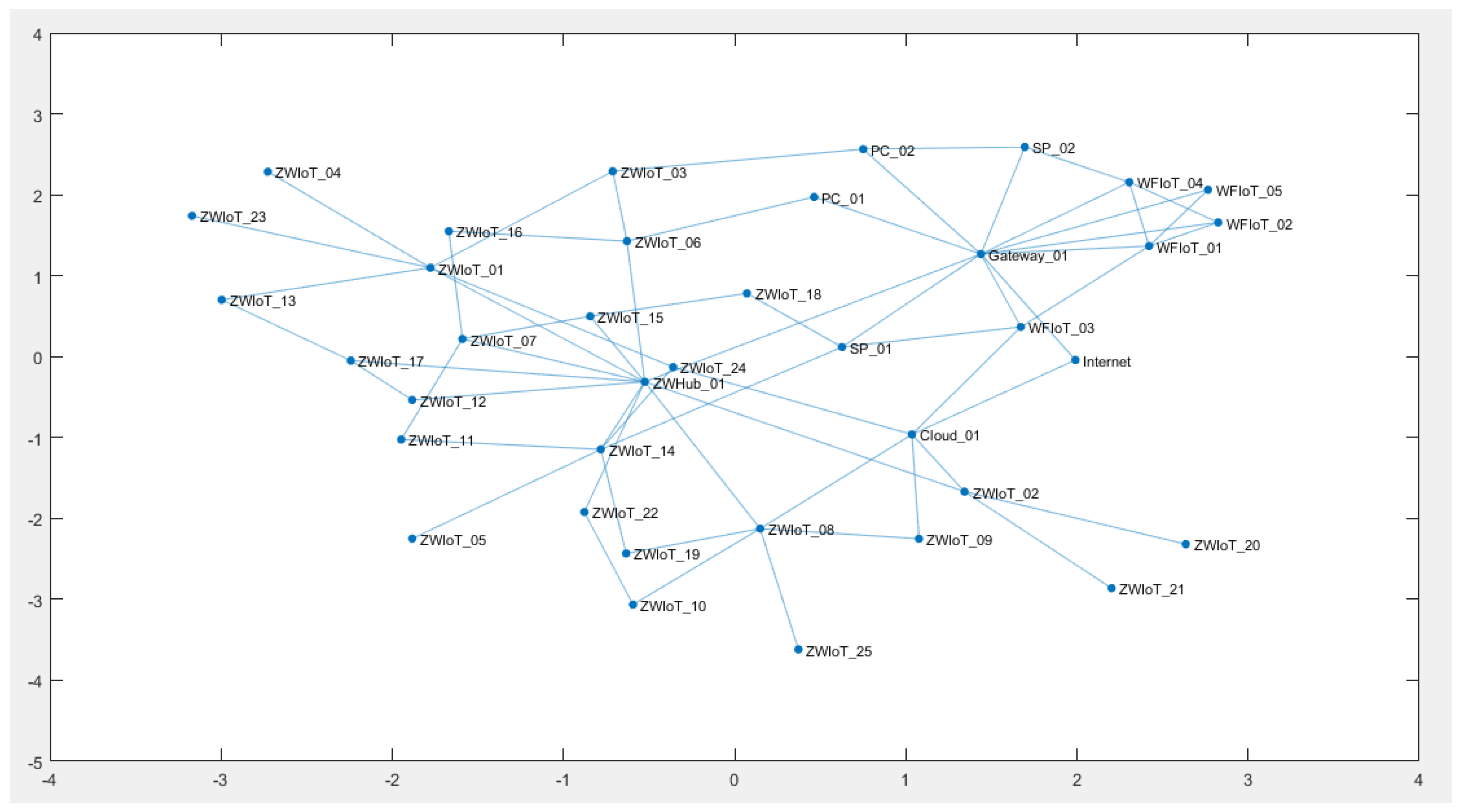
5.3. Plot Generation
The final step of the algorithm consists in visualizing the plot of the generated network topology. The generated plot should correspond to an observable static state of a smart home network. In addition, the algorithm generates two additional plots. These graphs represent two possible dynamic changes in the network. There are different dynamic changes that a smart home network topology could go through over time. One of these changes is the removal of one of its network nodes. The first additional generated plot shows the change of the network topology after the removal of one of its nodes. This could happen due to different causes, e.g., the malfunctioning or intermittent availability of one of the appliances.
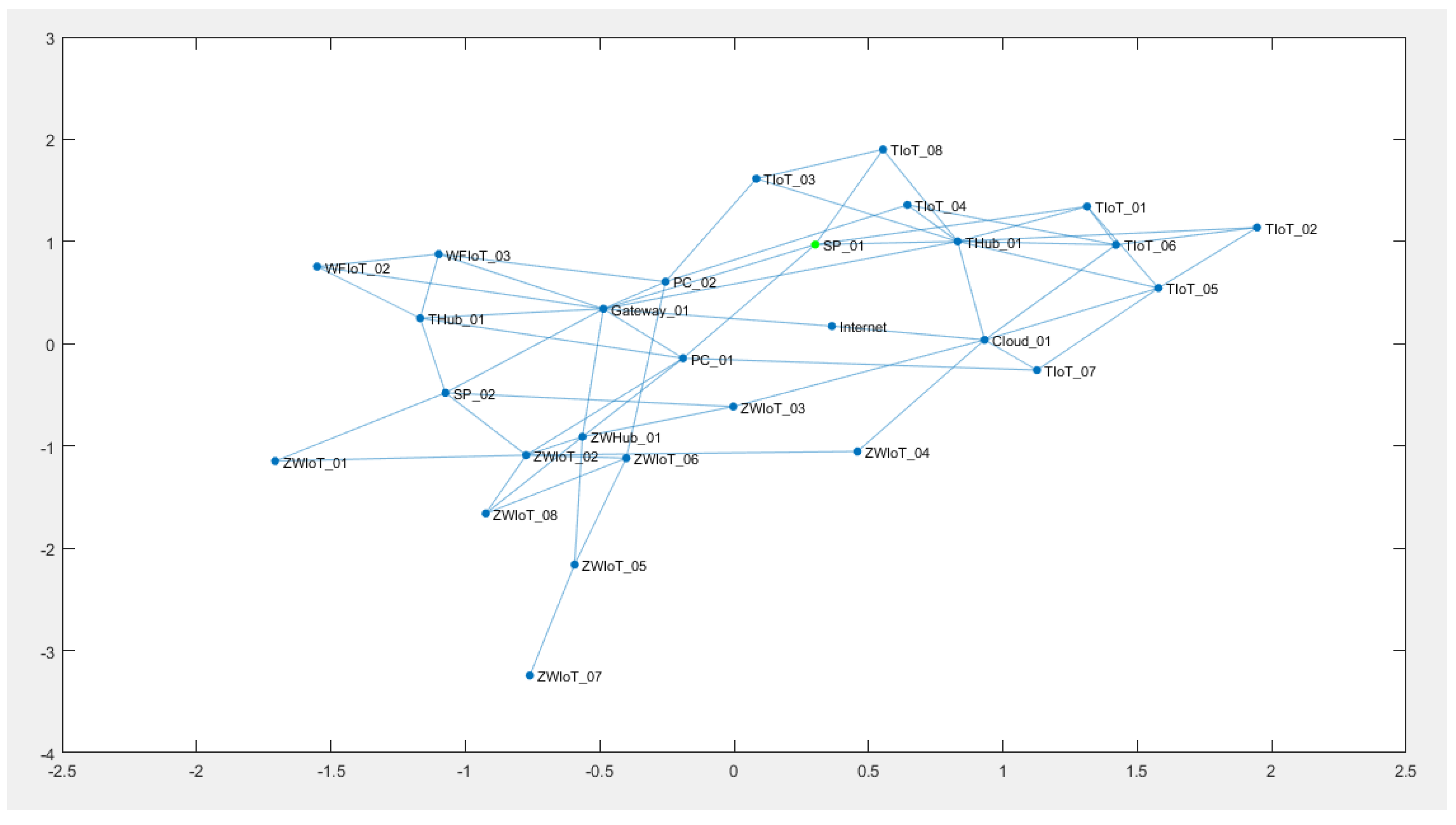
Figure 2 shows the plot generated with the following input parameters:
.
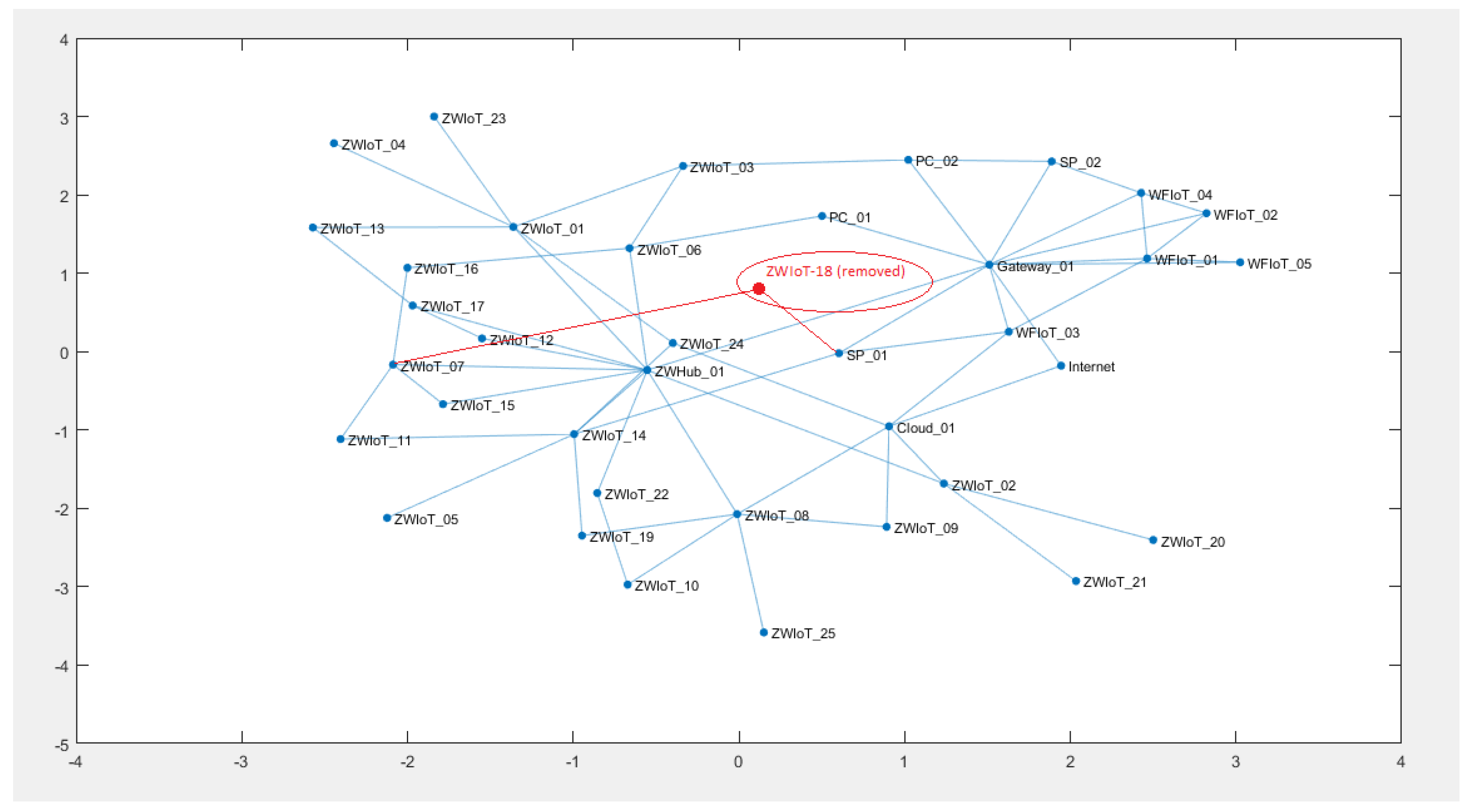
Figure 3 shows the change in the topology after the removal of one node from the network of devices.
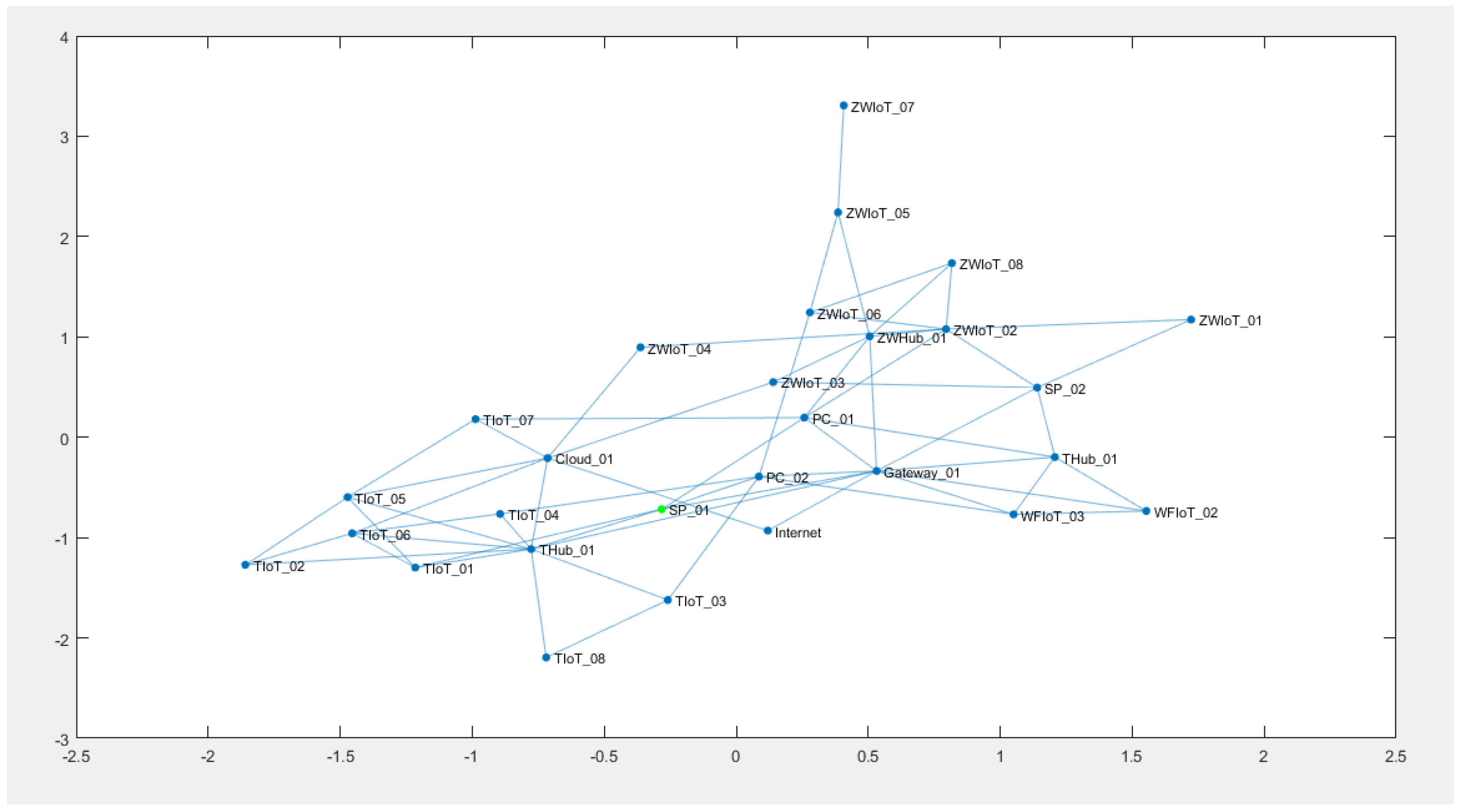
The output of the second plot varies greatly depending on which node is removed from the graph. If a node with high nodal degree is removed, the impact it would have on the network would be greater than if it had a lower nodal degree. On the contrary, if a node only has a peer-to-peer connection to another node, its removal would not impact the network as a whole. The third plot generated by the algorithm highlights the nodal mobility property that characterizes certain devices in smart home networks. Since the mobility property is very typical of smartphone devices, it was implemented exclusively for this category of appliances.
Figure 4 and
Figure 5 highlight the change in position of the smartphone node SP01, which causes the node to lose the connection it had to some of its previous neighbors, but also forms new connections to other nodes in the graph.
6. Attack Model Graph Representation
The threat analysis presented in
Section 4.2 identified different threats that can arise as a result of malware infection of the smart home’s network. To delve deeper into the study of such threats, we first developed the smart home network topology modeling algorithm described in
Section 5, and then studied the malware propagation in the Smart Home infrastructure. To correctly study and visualize the effects that dynamic changes on a network have on specific security threats, we developed an attack model designed on the smart home networks generated by the topology generator. The attack model focuses on representing malware propagation. The model developed in this work is based on the discrete state Markov model presented by Wang et al. [
25] with additional considerations about spatial-temporal dependencies.
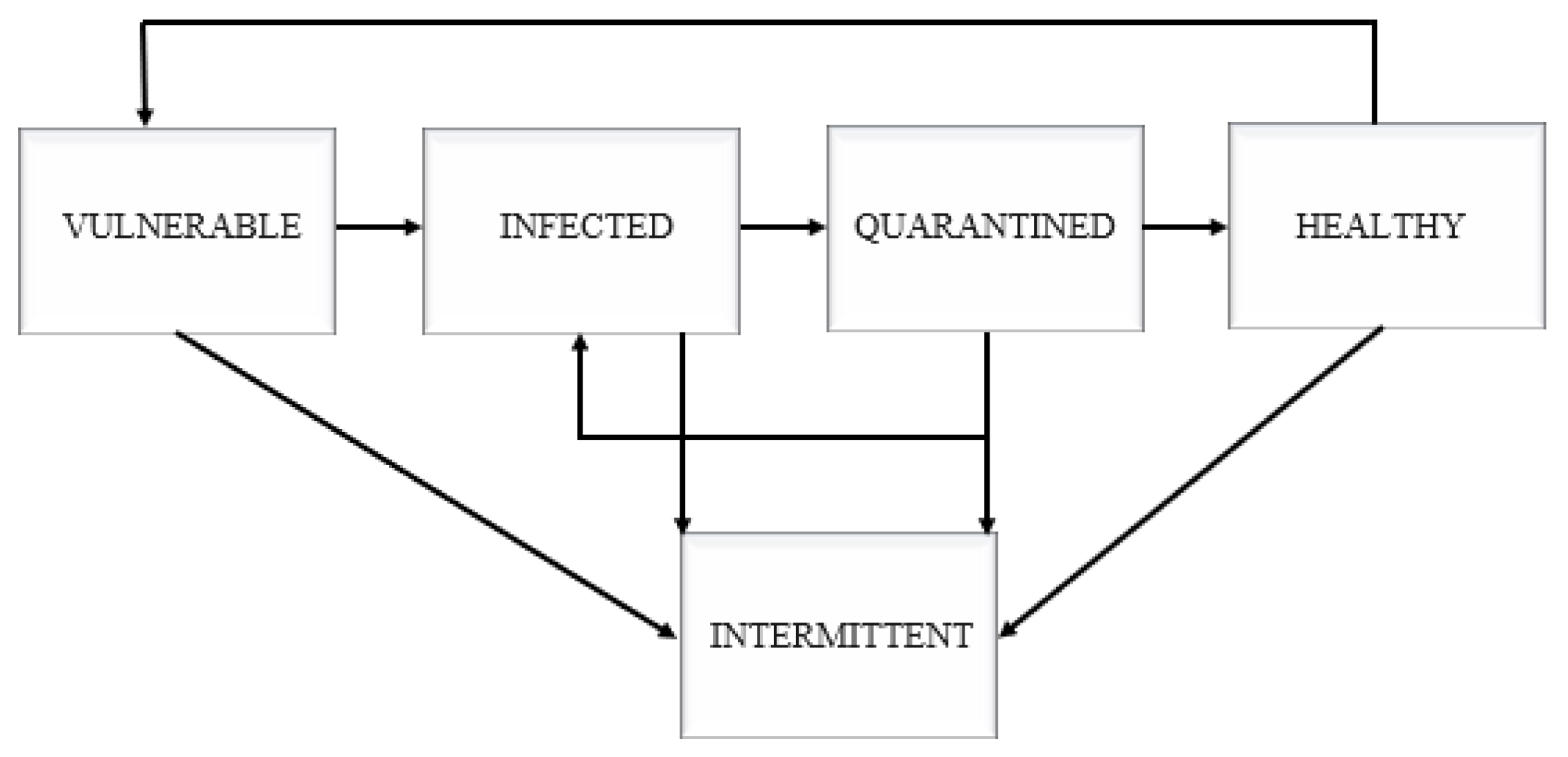
Figure 6 describes the state-change process of our model.
Our model assumes that a recovered node can either remain healthy or become vulnerable again after a certain time interval. In addition, our model considers the existence of a fifth state, namely the intermittent state. If a node is in the intermittent state at time
t, after an interval of time
t, it may either remain in the intermittent state or transit back to the state it was at
. The rate for the state-transitions are determined by a set of parameters.
Table 4 describes these parameters and their constraints.
The rates are used to determine the set of conditional probability functions of Equation (
1), where each state is associated with a state (
v = vulnerable,
i = infected,
q = quarantined,
h = healthy, and
i = intermittent).
In addition to the intermittent property, the property of spatial dynamicity has also been added to specific nodes. These nodes have been assigned a
dynamic attribute that allows them to move from their current location to a different location after an interval of time
t. At every iteration, the algorithm selects whether a dynamic node will be moved from its current position to a new position.
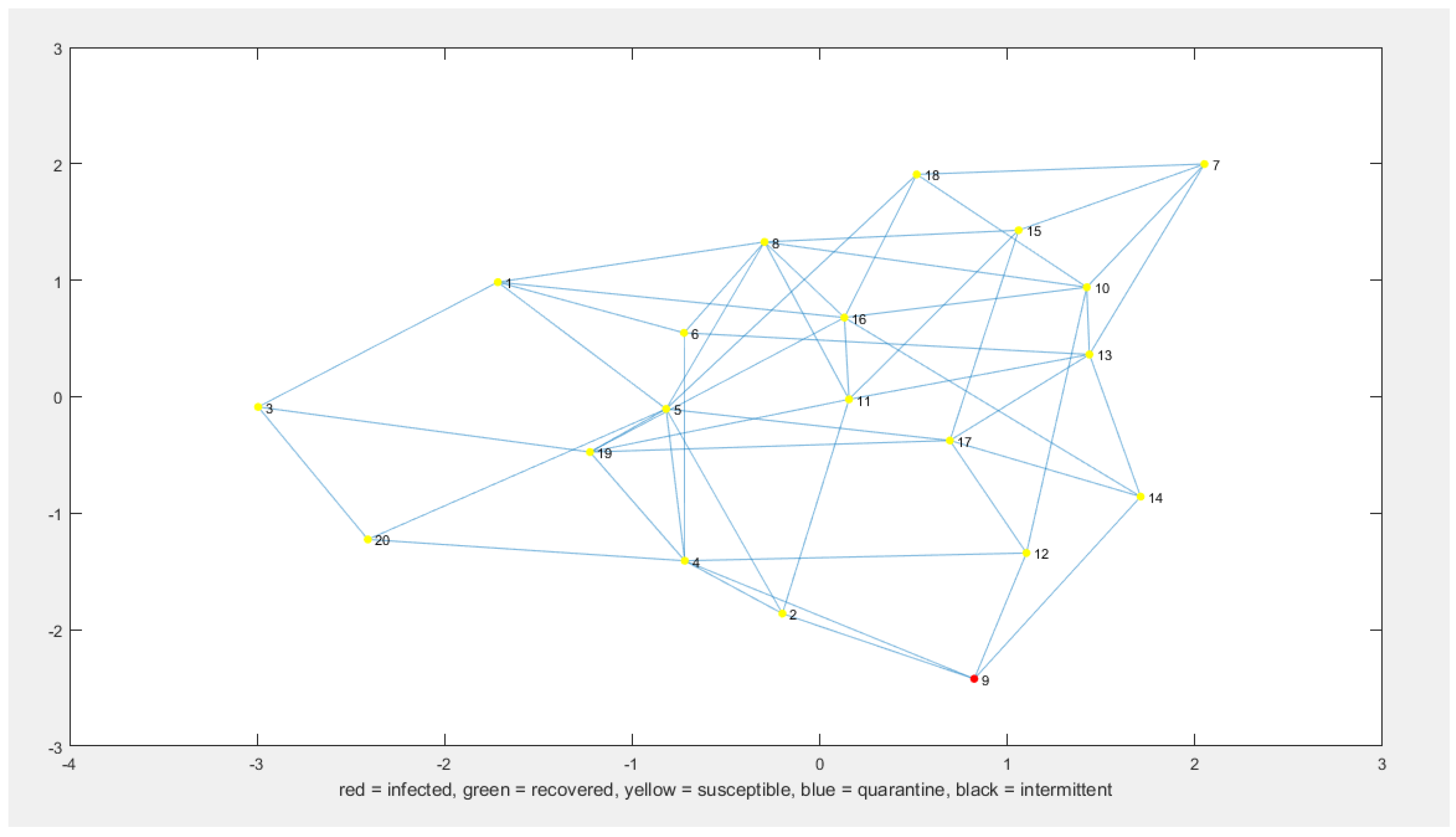
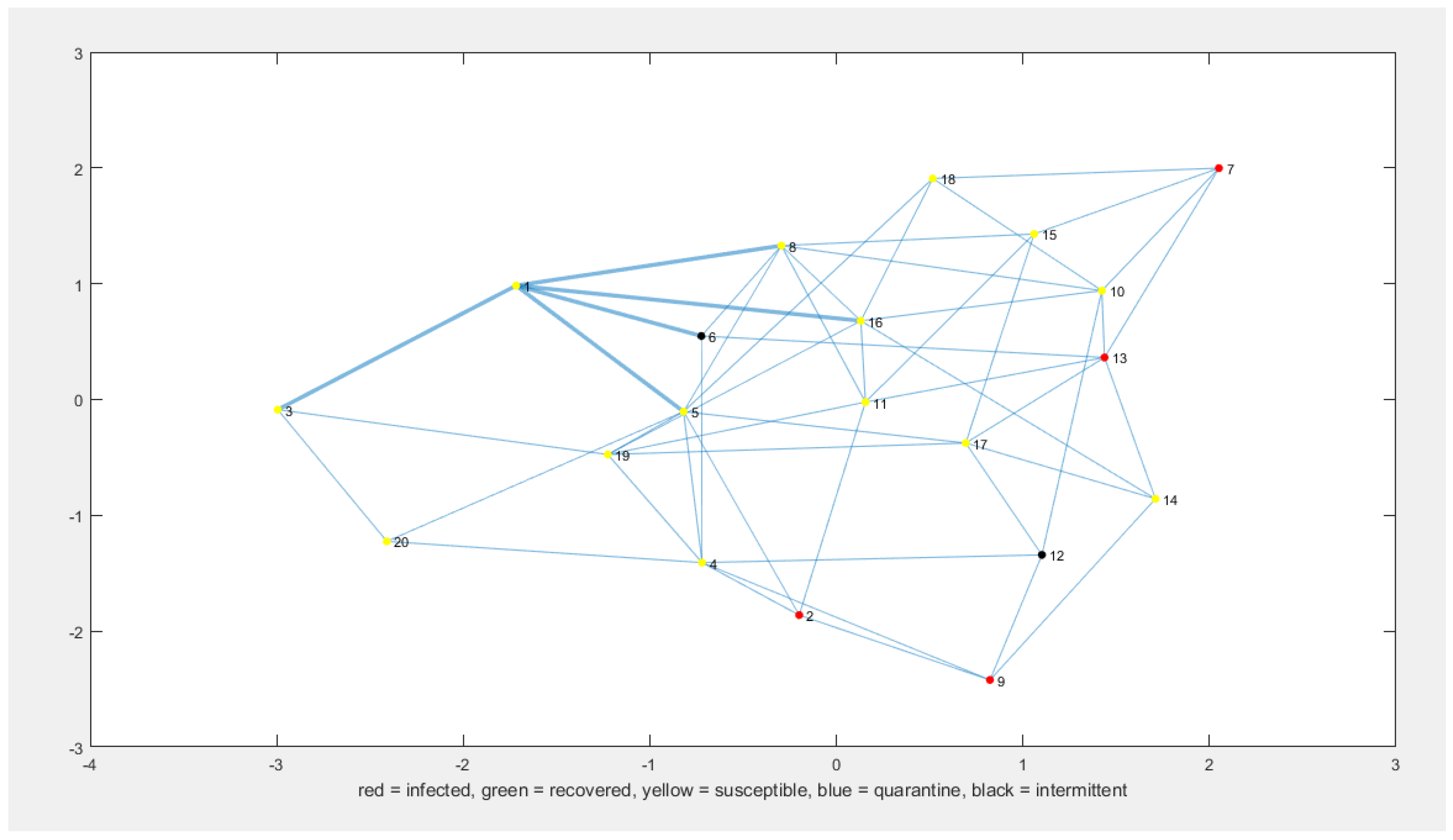
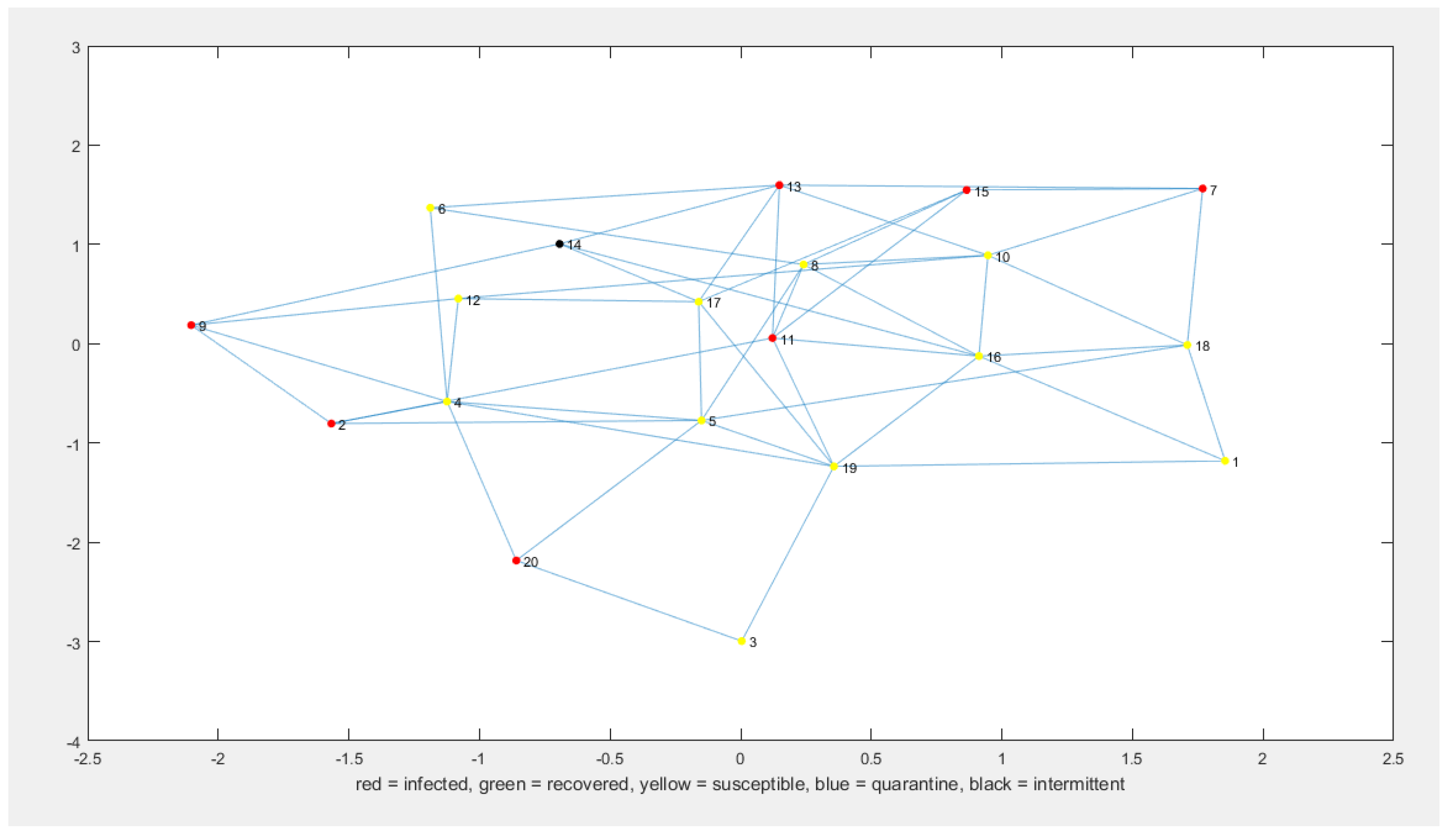
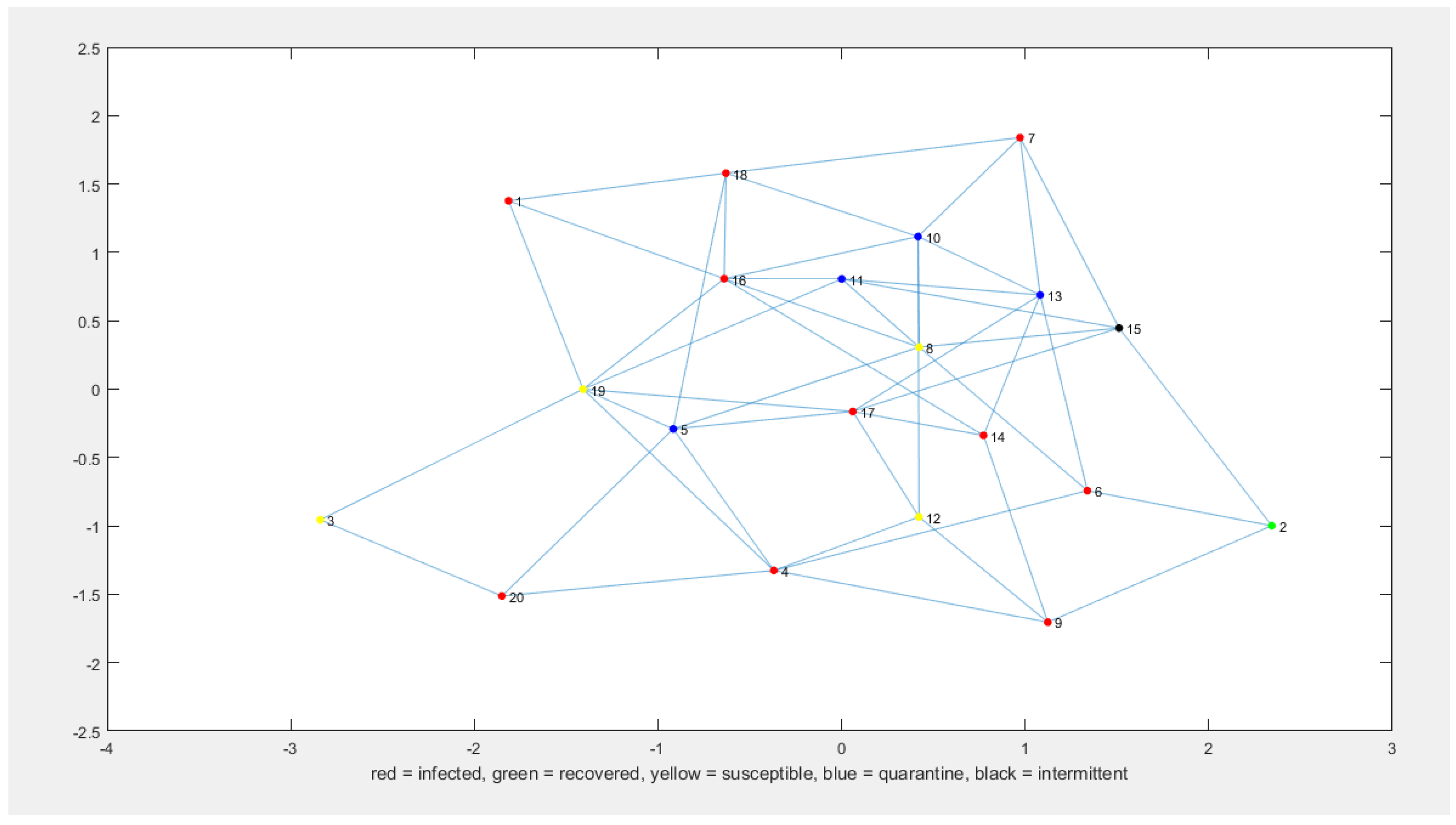
Figure 7,
Figure 8,
Figure 9 and
Figure 10 show sample outputs of the final algorithm.
To analyze the effects of the two properties implemented-intermittency and spatial dynamicity of nodes-both algorithms were run 50 times with the following inputs:
= 0.2,
= 0.1,
= 0.2, and
= 0.2. The number of nodes of the network was set to
N = 20 and the nodal degree to
d = 3. These values were selected in order to represent a small connected network, with medium infection and recovery speed.
Table 5 depicts the average number of nodes in each state, after 10 time intervals, for both models.
Table 5 shows that the most significant effect of the presence of intermittent and mobile nodes in the network is the decrease in the number of nodes infected after an equal interval of time. This can be interpreted as a slower propagation of the infection. Two factors that may have influenced the propagation of the malware are:
decreased neighborhood of nodes visible to the malware scanning and consequently the malware spreading; and
increased average time for the defense mechanisms to quarantine an infected node before it can propagate the infection to its neighborhood.
Further testing of the algorithm has shown that increasing the number of intermittent nodes in the network, or the rate of intermittency, has an inversely proportional effect on the propagation of the infection, in agreement with the previous hypotheses.
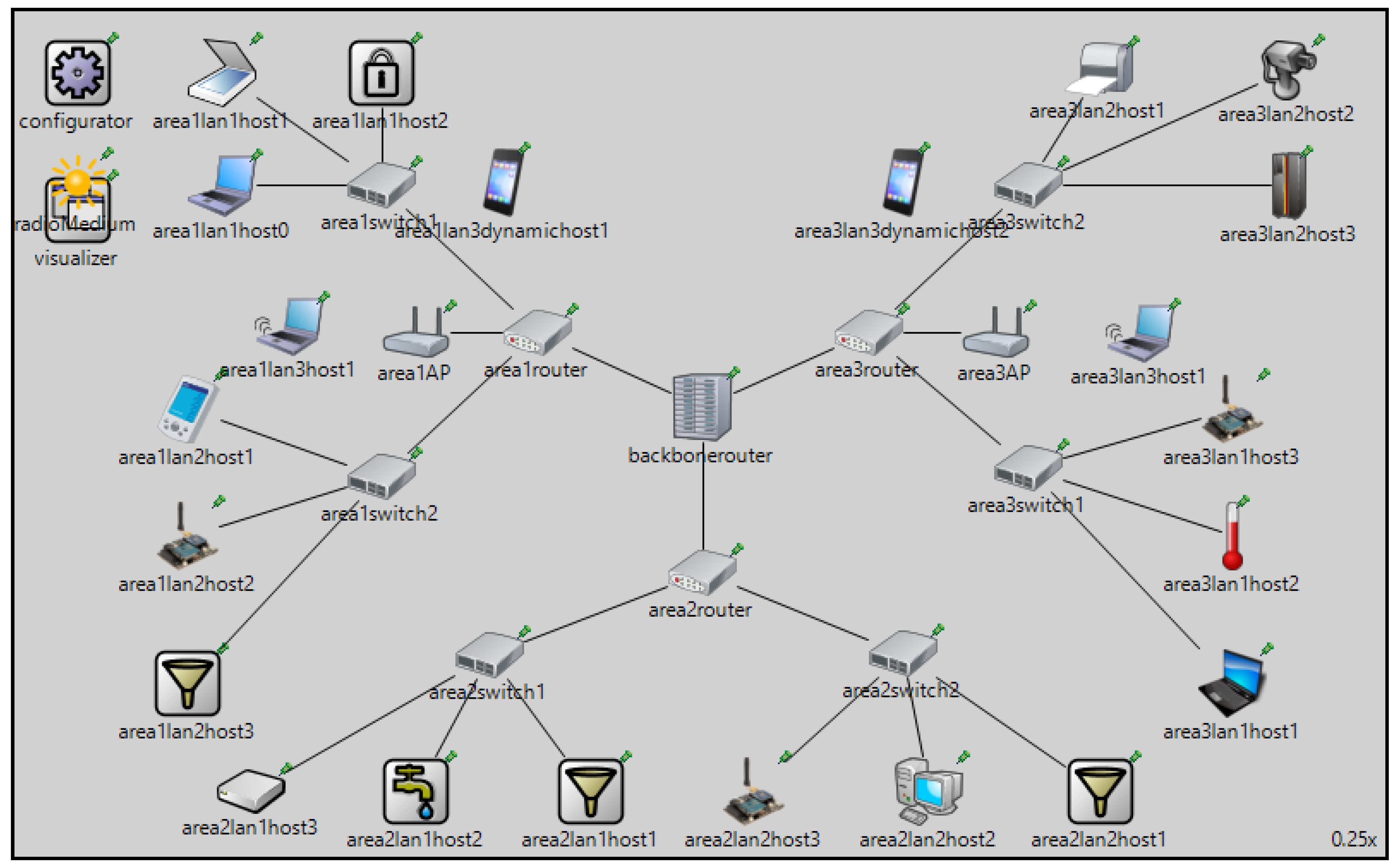
7. Network Topology Simulation
To validate the outputs of the network topology algorithm and the attack model graph representation developed and described in
Section 5 and
Section 6, we developed a network simulation of a smart home system. The simulation was implemented with the INET framework version 4.1.0 of OMNeT++ version 5.4.1 [
39]. The simulation, based on a pre-existing configuration provided by the INET framework, consists of a hierarchical mixed wireless/wired network. Two different network configurations are used to highlight the effect of dynamic and intermittent nodes on malware propagation in a network. The first network is comprised of three areas, each containing two local area networks (LANs). Each LAN contains three heterogeneous hosts. The hosts in the LAN connect to an area router through switches. The three area routers connect to a central backbone router. The network contains three hierarchical levels, which correspond to the hosts in the LANs, the area routers, and the backbone router. In addition, two wireless access points are added to the network. The access points are connected to
area1router and
area3router, respectively. These access points allow for wireless hosts to be connected to the network. Two wireless hosts are connected to each access point. Different Service Set Identifiers (SSIDs) are configured for the members of the two wireless LANs, so they do not communicate directly with each other. To assign IP addresses hierarchically, starting from the central router to the single hosts, the following strategy was adopted: the first octet of the address for all nodes is 10; the second octet denotes the area; the third octet denotes the LAN within the area; and the fourth octet is the host identifier within a LAN. For example, a host
host1 found in area 3 in lan 1 would have the IP address 10.3.1.1.
Figure 11 shows the configuration for the first network simulation.
To visualize malware scanning and malware propagation, localized routing tables for ping communication are made. These tables determine the routes that packets have to follow when trying to reach a certain host. Packet reception is interpreted as successful malware scanning. A state variable is added to all hosts. Whenever the malware scans a certain host, the state variable is updated following the conditional probability functions of Equation (
1). Whenever a host transits between two states, a message stating which state-transition the host has gone through is printed. The second network configuration modifies the behavior of certain devices in the network, to account for intermittent availability and mobility of nodes. First, shut down and startup scenarios have been scripted for certain nodes in the network.This addition allows the implementation of intermittent availability to nodes. In particular,
area2lan1host3,
area2lan2host1 and
area3switch2 are scripted to shut down and start up sequentially after specific time intervals. Nodal mobility is also added to the previously static
area1lan3dynamichost1 and
area3lan3dynamichost2. A rectangular moving pattern, with constant speed and acceleration is added to these two hosts, taking them out of the range of their initial access points and into the range of another access point during the course of their movement pattern. The results of running the second configuration of the network simulation confirm that intermittent availability of nodes affects malware propagation in a way that is inversely proportional; the more intermittent nodes in a network and the longer these nodes are “hidden” to the malware scanning, the slower the propagation of the malware. The detection and recovery rate of the network nodes are comparable in both models, although the slower propagation of the malware allows for the detection system to offset a rapid expansion. One behavior that is highlighted in the simulation, but is not taken into account in the network topology generator and the attack model, is the somewhat deterministic patterns followed by dynamic nodes. This means that the neighborhood of these nodes after short subsequent instants of time is not random, but usually correspond to adjacent nodes to the current neighborhood. Consequently, the short-term effect of dynamic mobility of nodes is not as significant as suggested by the attack model, but its long-term effects may still affect the malware propagation in a meaningful way.
8. Conclusions
To facilitate threat analysis for dynamic environments, it is necessary to be able to continuously identify and analyze different components, systems and communication protocols. In this work, we conducted a threat analysis for the smart home ecosystem, utilizing the smart home reference architecture of Ghirardello et al. [
31], the STRIDE threat analysis method and Microsoft’s threat modeling tool, with an eye towards identifying and analyzing potential threats which target both physical components of a smart home environment and data flows among them. The analysis considered six smart home instances of varying complexity. We later developed a smart home network topology generator and a malware propagation graph-based model to effectively evaluate the effects of the dynamic properties of the environment in specific security threats.
Even though the proposed approach has been demonstrated to allow the capture of dynamic changes of devices and/or back-end services in a smart home environment, it does not come without limitations. These are mostly related to the threat analysis tool, which has not managed to identify denial of service threats and cannot handle physical threats that might affect the physical infrastructure. Furthermore, the existing DFD template does not support all the communication protocols that may be used in a smart home; hence, our analysis was limited only to the ZigBee, HTTPS and 4G protocols. Moreover, the analysis of existing communication protocols considered only spoofing, tampering and elevation of privileges threats, as repudiation and information disclosure threats are not fully supported. What is more, the currently available template does not allow the examination of transitive attacks over the network. Specifically, the specific template analyzes each component of the DFD separately and cannot consider malicious actions which, for example, could occur by a stealthy malware. Despite these limitations, the approach can be used to provide input to one of the dynamic risk assessment methods to identify potential risks to the physical and communication viewpoint.
Results from the attack model algorithm show that the presence of dynamic nodes can change the propagation pattern and rate of a malware, with effects directly proportional to the initial and final neighborhood size of the mobile nodes. The presence of intermittently available nodes also has an impact on the network. With a higher number of intermittent nodes in a network, the final rate of propagation of a malware in otherwise identical conditions is reported to be slower and with a smaller expansion. A network simulation, to showcase real-time malware propagation in a smart home network, was conducted to validate the outputs of the models developed. The results of the simulation confirm that intermittent availability of nodes impact malware propagation. The simulation also highlights that mobility patterns of dynamic nodes should be taken into consideration when developing network topology generators and attack models, as they would allow for more realistic prediction of the neighborhood size and topological position of infected nodes.
As future work, we intend to develop a more flexible template to reflect the smart home ecosystem in higher fidelity, and use this to carry out a refined threat analysis, to be used as input to the dynamic risk assessment approach taken in the GHOST project [
16]. To this end, we will analyze the security of the communication protocols and data packets in more detail in order to contribute to the most crucial part of the Risk Engine, namely risk analysis. The more rigorous threat analysis results will be used for Contextual Profiling (CP) as described in the GHOST architecture. In particular, the development of the classification templates and profiles of the typical Smart Home devices will be enhanced, by leveraging the results herein in the training process.
We also intend to adjust the topology generator algorithm in accordance to the results obtained by the network simulation, in particular to characterize the behavior of mobile nodes in the generated networks with more deterministic mobility patterns, based on the structural properties of the topologies. The results of this study and future studies will be utilized during the training process in order to improve the accuracy of the results.