A HMM-R Approach to Detect L-DDoS Attack Adaptively on SDN Controller
Abstract
1. Introduction
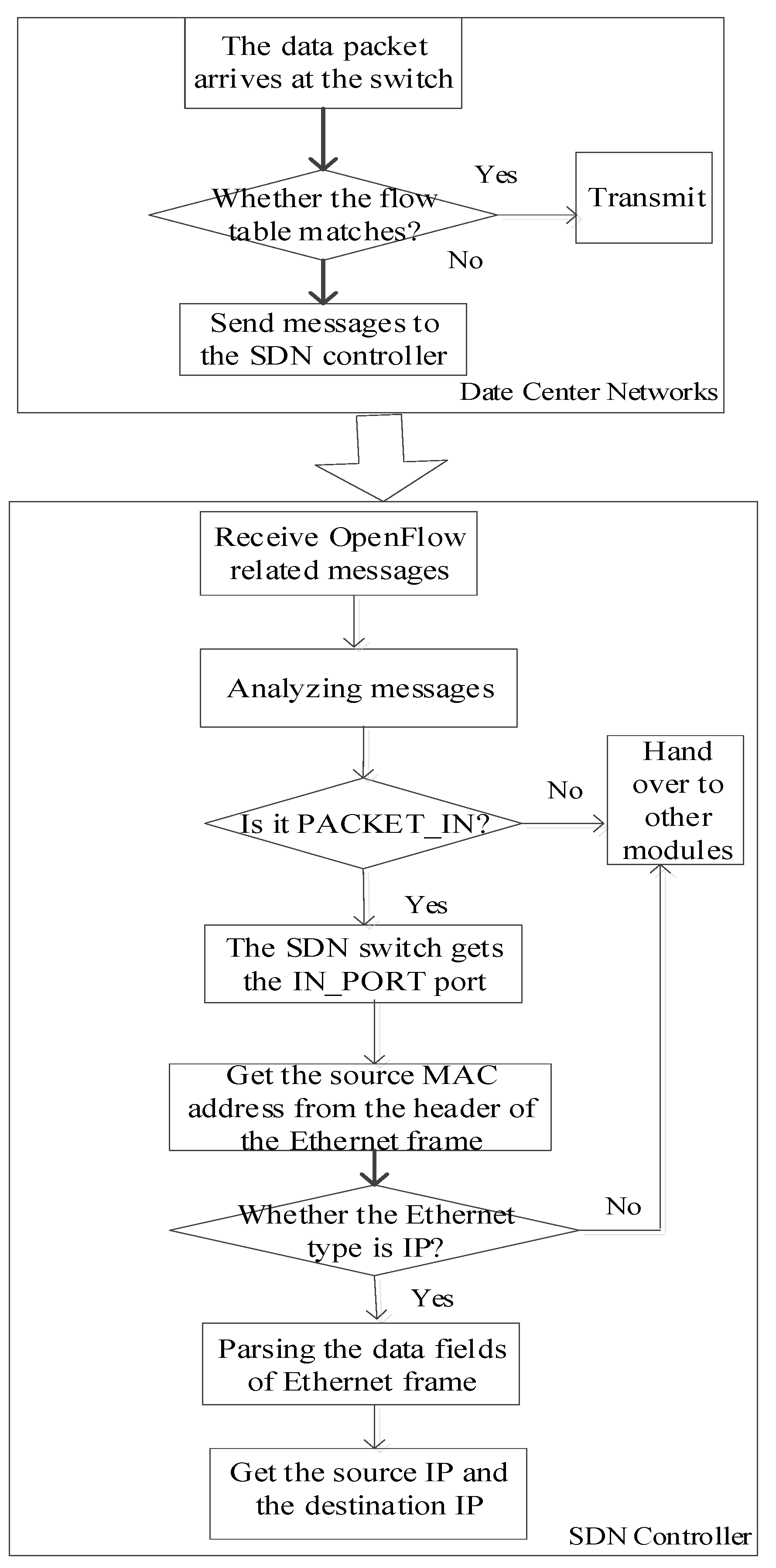
- We combine software defined network (SDN) to achieve complete control of network traffic that improves the detection of single link or single host of traditional data center network and utilize OpenFlow’s massage mechanism to increase the flexibility of the detection period.
- We use the PACKET_IN message of OpenFlow mechanism to set up a trigger detection period.
- We propose a Renyi entropy to add the entropy difference between the normal traffic and L-DDoS to reduce the false positive in attribute statistics.
- We propose a probabilistic model of combining Renyi entropy and hidden Markov model (HMM-R) to define a variety of states with double stochastic processes of hidden states and observed states to improve the true positive and reduce the false positive and increase the flexibility.
2. Related Work
2.1. Non-Machine Learning Algorithms
2.2. Machine Learning Algorithms
3. Background
3.1. L-DDoS Attacks
3.2. Software Defined Network
3.3. Renyi Entropy
- Maximum entropy: when or , a maximum entropy is obtained. The maximum entropy model is to use the weakest randomness of maximum entropy to obtain the model parameters at the highest time. Then the model parameters are obtained at the highest uncertain time.
- Minimum entropy: when , converges to the minimum entropy. When the possible number of all events is b, the probability of all events is shown to be in the minimum entropy. Minimum entropy is the smallest of the entropy family and is the most lightweight method to measure unpredictability, it pays an important role in theoretical computer science.
- Shannon entropy: when , converges to Shannon entropy., so:
3.4. Hidden Markov Model
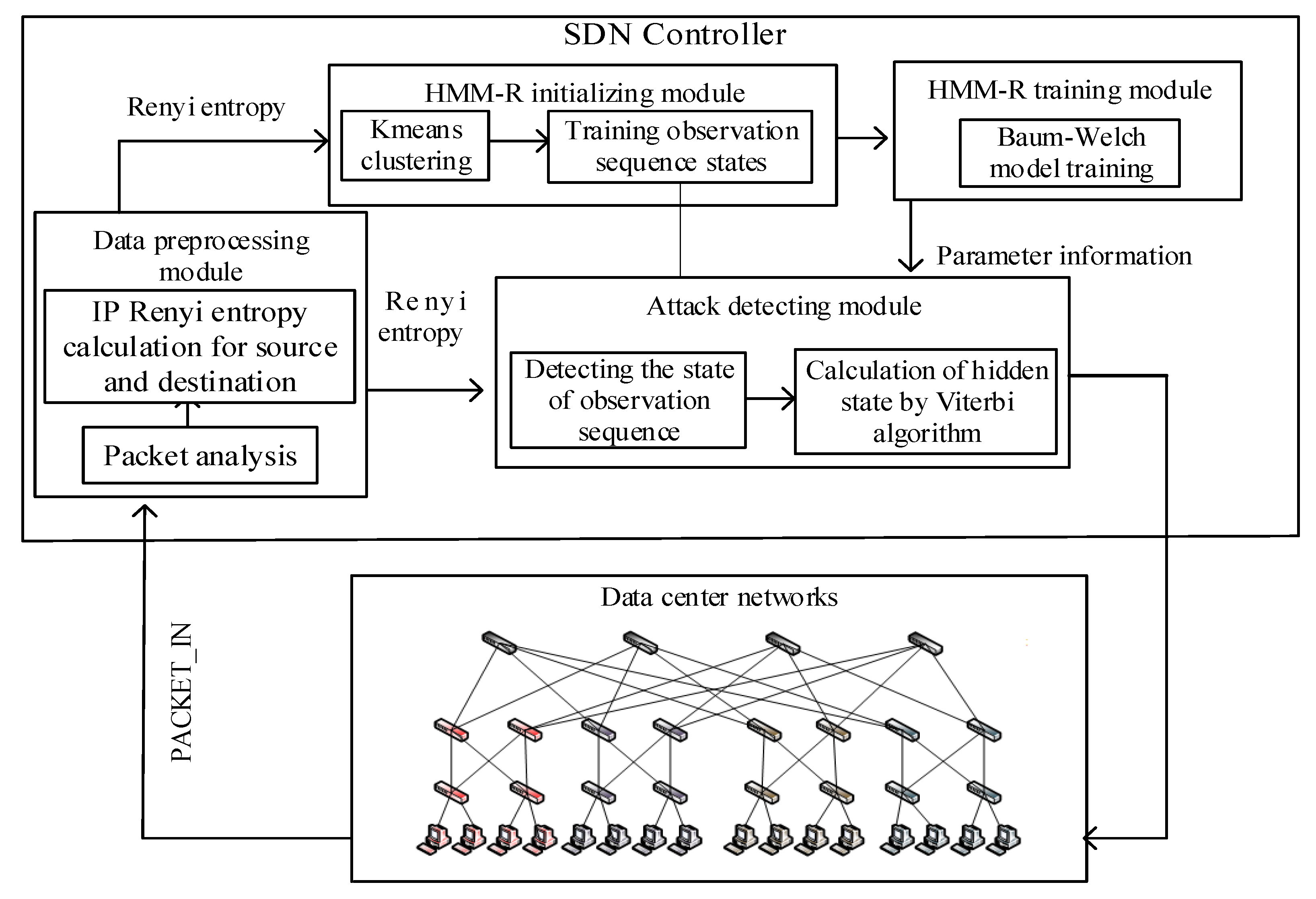
4. HMM-R Detection Scheme
4.1. Overall Architecture
4.2. Detection Features and Performance Indices
4.2.1. Detection Features
4.2.2. Performance Indices
4.3. Data Preprocessing
4.4. Model Initializing
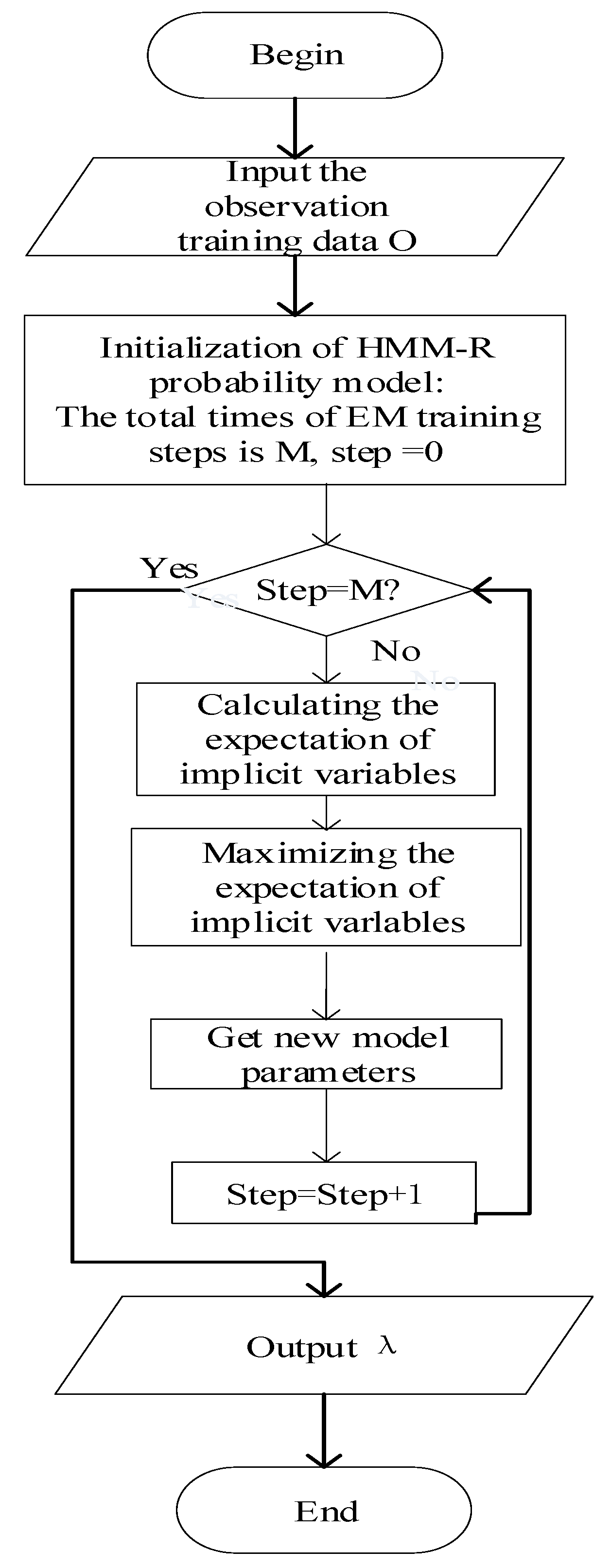
4.5. Model Training
4.6. Model Detecting
| Algorithm 1 HMM-R detection algorithm |
| Input: , , |
| Output: |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
5. Implementation and Evaluation
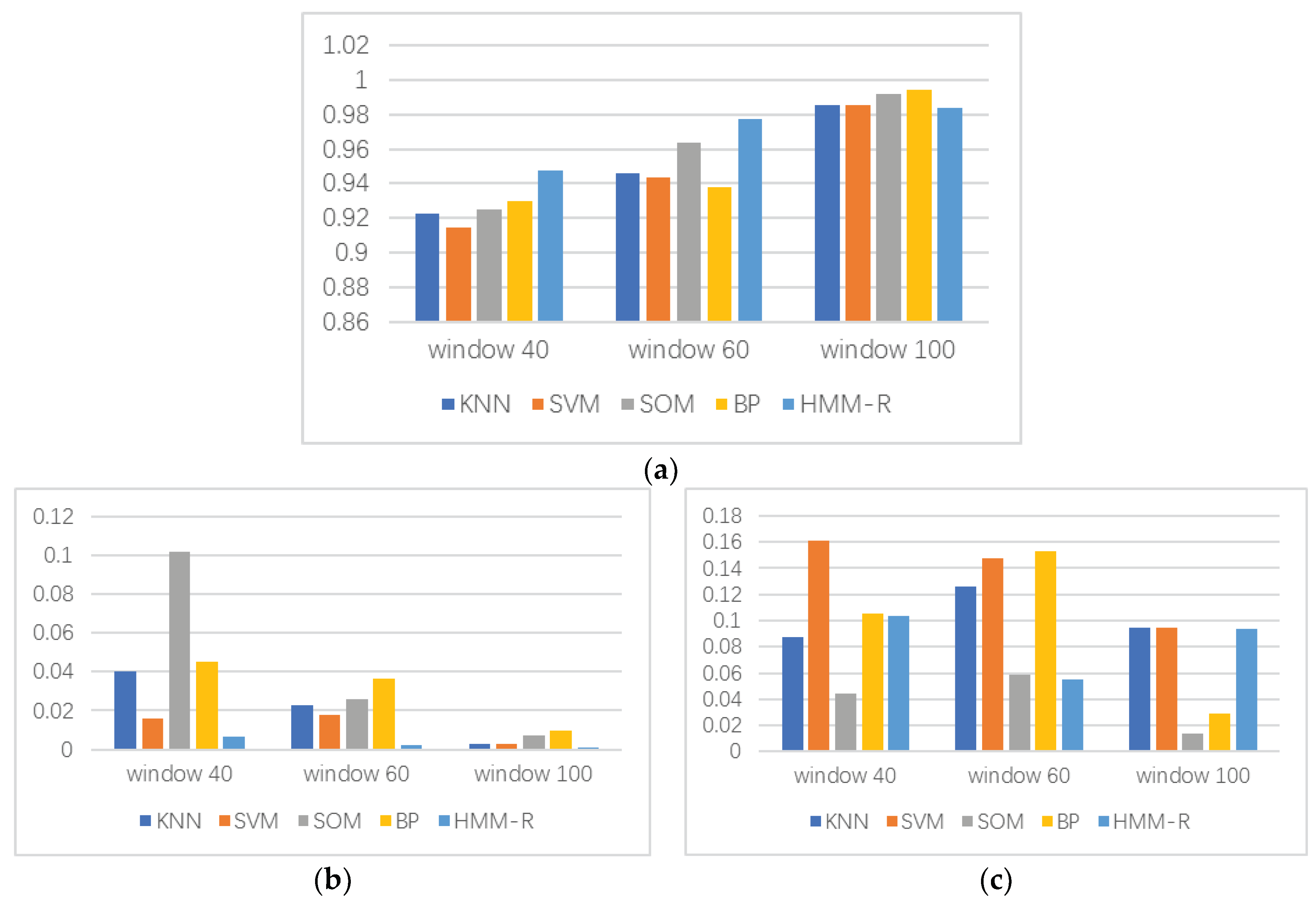
5.1. Model Detection Performance
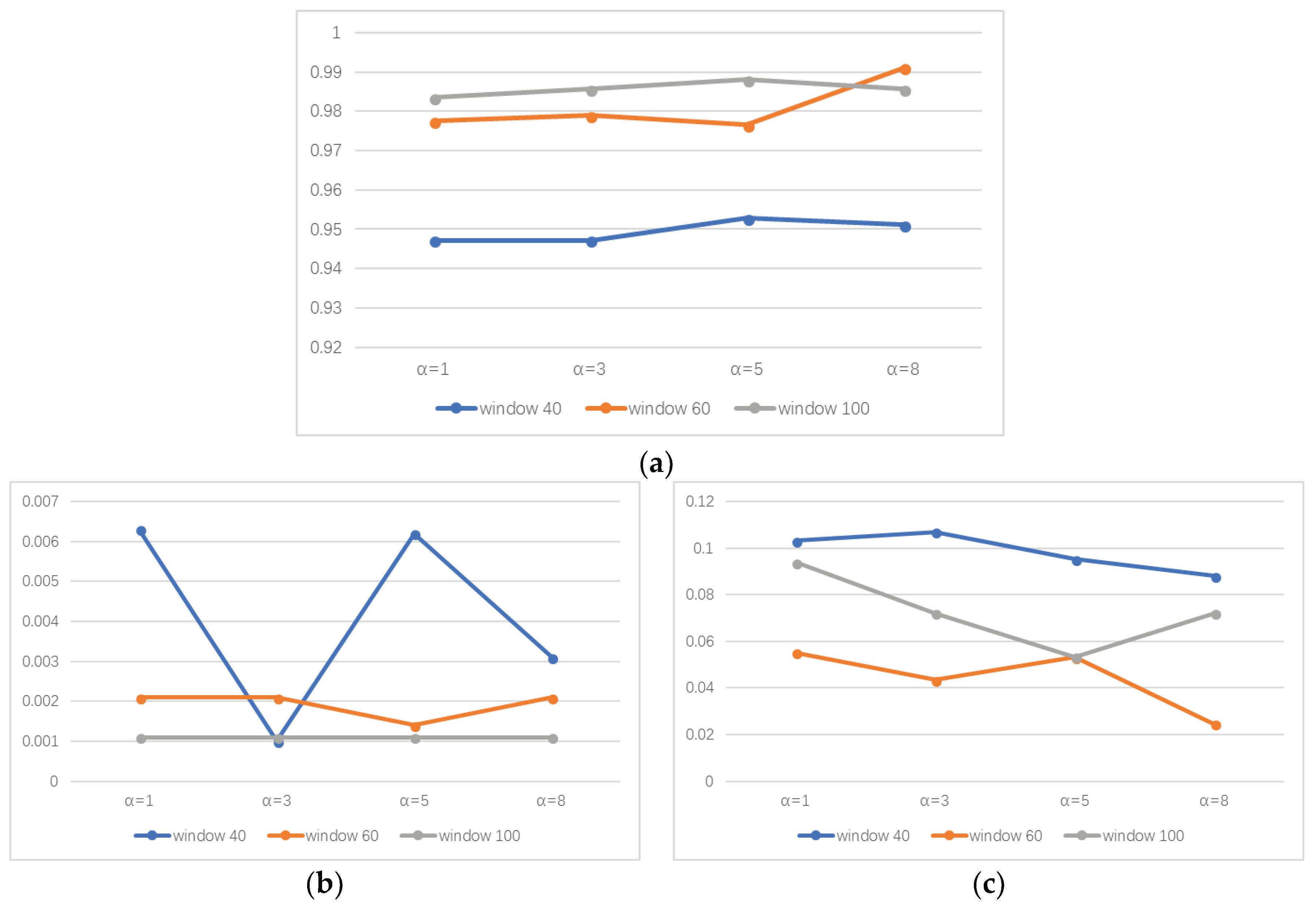
5.2. Sliding Window
5.3. Robustness
5.4. Time Performance
6. Conclusions
Author Contributions
Funding
Conflicts of Interest
References
- Gang, D.; Gong, Z.; Hong, W. Characteristics research on modern data center network. J. Comput. Res. Dev. 2014, 51, 395–407. Available online: http://crad.ict.ac.cn/EN/Y2014/V51/I2/395 (accessed on 18 July 2018).
- Wen, K.; Yang, J.H.; Zhang, B. Survey on research and progress of low-rate denial of service attacks. J. Softw. 2014, 533, 37. [Google Scholar] [CrossRef]
- Min, S.K.; Lee, S.B.; Gligor, V.D. The crossfire attack. In Proceedings of the IEEE Symposium on Security & Privacy, Berkeley, CA, USA, 19–22 May 2013; pp. 127–141. [Google Scholar] [CrossRef]
- Xiang, Y.; Li, K.; Zhou, W. Low-rate DDoS attacks detection and traceback by using new information metrics. IEEE Trans. Inf. Forensics Secur. 2011, 6, 426–437. [Google Scholar] [CrossRef]
- Chaovalit, P.; Gangopadhyay, A.; Karabatis, G.; Chen, Z. Discrete wavelet transform-based time series analysis and mining. ACM Comput. Surv. 2011, 43, 6. [Google Scholar] [CrossRef]
- Oshima, S.; Nakashima, T.; Sueyoshi, T. Early DoS/DDoS Detection Method using Short-term Statistics. In Proceedings of the International Conference on Complex, Intelligent and Software Intensive Systems, Krakow, Poland, 15–18 February 2010; pp. 168–173. [Google Scholar] [CrossRef]
- Bhuyan, M.H.; Bhattacharyya, D.K.; Kalita, J.K. An empirical evaluation of information metrics for low-rate and high-rate DDoS attack detection. Pattern Recognit. Lett. 2015, 51, 1–7. [Google Scholar] [CrossRef]
- Bhuyan, M.H.; Bhattacharyya, D.K.; Kalita, J.K. Information metrics for low-rate DDoS attack detection: A comparative evaluation. In Proceedings of the International Conference on Contemporary Computing, Noida, India, 7–9 August 2014; pp. 80–84. [Google Scholar] [CrossRef]
- Mousavi, S.M.; Sthilaire, M. Early detection of DDoS attacks against SDN controllers. In Proceedings of the International Conference on Computing, NETWORKING and Communications, Garden Grove, CA, USA, 16–19 February 2015; Volume 17, pp. 77–81. [Google Scholar] [CrossRef]
- Jadhav, P.N.; Patil, B.M. Low-rate DDoS attack detection using optimal objective entropy method. Int. J. Comput. Appl. 2014, 78, 33–38. [Google Scholar] [CrossRef]
- Xiao, P.; Qu, W.; Qi, H.; Li, Z. Detecting DDoS attacks against data center with correlation analysis. Comput. Commun. 2015, 67, 66–74. [Google Scholar] [CrossRef]
- Ain, A.; Bhuyan, M.H.; Bhattacharyya, D.K.; Kalita, J.K. Rank correlation for low-rate DDoS attack detection: An empirical evaluation. Int. J. Netw. Secur. 2016, 18, 474–480. [Google Scholar] [CrossRef]
- Bhuyan, M.H.; Kalwar, A.; Goswami, A.; Bhattacharyya, D.K.; Kalita, J.K. Low-Rate and High-Rate Distributed DoS Attack Detection Using Partial Rank Correlation. In Proceedings of the IEEE Fifth International Conference on Communication Systems and Network Technologies, Gwalior, India, 4–6 April 2015; pp. 706–710. [Google Scholar] [CrossRef]
- Wei, W.; Chen, F.; Xia, Y.; Jin, G. A rank correlation based detection against distributed reflection dos attacks. IEEE Commun. Lett. 2013, 17, 173–175. [Google Scholar] [CrossRef]
- Hoque, N.; Bhattacharyya, D.K.; Kalita, J.K. A novel measure for low-rate and high-rate DDoS attack detection using multivariate data analysis. In Proceedings of the IEEE International Conference on Communication Systems and Networks, Bangalore, India, 5–10 January 2016; pp. 1–2. [Google Scholar] [CrossRef]
- Zhang, C.; Cai, Z.; Chen, W.; Luo, X.; Yin, J. Flow level detection and filtering of low-rate DDoS. Comput. Netw. Int. J. Comput. Telecommun. Netw. 2012, 56, 3417–3431. [Google Scholar] [CrossRef]
- Suresh, M.; Anitha, R. Evaluating machine learning algorithms for detecting DDoS attacks. In Proceedings of the Advances in Network Security and Applications: 4th International Conference, CNSA 2011, Chennai, India, 15–17 July 2011; pp. 441–452. [Google Scholar] [CrossRef]
- Yusof, A.R.; Udzir, N.I.; Selamat, A. An evaluation on KNN-SVM algorithm for detection and prediction of DDoS attack. Parasitology 2011, 138, 578–582. [Google Scholar] [CrossRef]
- Priyanka, P.S.; Gowrishankar, A.; Priyanka, P.S.; Gowrishankar, A. Detection of Low and High Rate DDoS Attack Using Metrics with SVM in FireCol Distributed Network. Available online: https://www.ijcaonline.org/proceedings/icaccthpa2014/.../19445-6027 (accessed on 18 July 2018).
- Yan, Q.; Gong, Q.; Deng, F.A. Detection of DDoS attacks against wireless sdn controllers based on the fuzzy synthetic evaluation decision-making model. Ad Hoc Sens. Wirel. Netw. 2016, 33, 275–299. Available online: http://ahswn-volume-33-number-1-4-2016/ahswn-33-1-4-p-275-299/ (accessed on 18 July 2018).
- Braga, R.; Mota, E.; Passito, A. Lightweight DDoS flooding attack detection using NOX/OpenFlow. In Proceedings of the IEEE Conference on Local Computer Networks, Denver, CO, USA, 10–14 October 2010; Volume 8, pp. 408–415. [Google Scholar] [CrossRef]
- Giotis, K.; Argyropoulos, C.; Androulidakis, G.; Kalogeras, D.; Maglaris, V. Combining OpenFlow and sFlow for an effective and scalable anomaly detection and mitigation mechanism on SDN environments. Comput. Netw. 2014, 62, 122–136. [Google Scholar] [CrossRef]
- Cui, Y.; Yan, L.; Li, S.; Xing, H.; Pan, W.; Zhu, J.; Zheng, X. SD-anti-DDoS: Fast and efficient DDoS defense in software-defined networks. J. Netw. Comput. Appl. 2016, 68, 65–79. [Google Scholar] [CrossRef]
- Farhady, H.; Lee, H.Y.; Nakao, A. Software-defined networking: A survey. Comput. Netw. 2015, 81, 79–95. [Google Scholar] [CrossRef]
- Zhang, C.K.; Cui, Y.; Tang, H.Y.; Wu, J.P. State-of-the-art survey on software-defined networking (SDN). J. Softw. 2015, 26, 62–81. [Google Scholar] [CrossRef]
- Terrence, L. Foundations of Probability. In Advanced Real Analysis. Cornerstones; Birkhäuser: Boston, MA, USA, 2005; ISBN 978-0-8176-4382-9. [Google Scholar] [CrossRef]
- Lantz, B.; Heller, B.; Mckeown, N. A network in a laptop: Rapid prototyping for software-defined networks. In Proceedings of the ACM Workshop on Hot Topics in Networks, HOTNETS 2010, Monterey, CA, USA, 20–21 October 2010; pp. 1–6. [Google Scholar]
- POX Controller. Available online: https://github.com/pkpk8/pox (accessed on 18 July 2018).
- Netsniff-ng Toolkit. Available online: http://www.netsniff-ng.org/ (accessed on 18 July 2018).

| Variable Name | Meanings |
|---|---|
| Parameter of HMM-R model | |
| Length of observation sequence | |
| Threshold of window size | |
| Statistics of window size | |
| Hidden state space | |
| Source IP address | |
| Destination IP address | |
| Renyi entropy of source IP | |
| Renyi entropy of destination IP | |
| Observation sequence |
| Detection Algorithm | RP | FA | DR |
|---|---|---|---|
| KNN | 0.8990 | 0.2530 | 0.0 |
| SVM | 0.8990 | 0.2409 | 0.007 |
| SOM | 0.9250 | 0.0636 | 0.0834 |
| BP | 0.9230 | 0.1315 | 0.0 |
| HMM-R | 0.9461 | 0.01 | 0.08 |
| Order of Renyi Entropy | K | L |
|---|---|---|
| 10 | 13 | |
| 11 | 13 | |
| 10 | 13 | |
| 11 | 13 |
| Attack Ratio | RP | FA | DR |
|---|---|---|---|
| 0.01 | 0.9461 | 0.0181 | 0.0800 |
| 0.02 | 0.9692 | 0.0 | 0.0533 |
| 1 | 0.9711 | 0.0 | 0.0500 |
| Detection Algorithm | RP | FA | DR |
|---|---|---|---|
| KNN | 0.9833 | 0.0147 | 0.0247 |
| 0.9960 | 0.0025 | 0.0088 | |
| SVM | 0.9814 | 0.0147 | 0.0247 |
| 0.9960 | 0.0025 | 0.0088 | |
| SOM | 0.9814 | 0.0147 | 0.0247 |
| 0.9911 | 0.0041 | 0.0237 | |
| BP | 0.9792 | 0.0181 | 0.0454 |
| 0.9903 | 0.0307 | 0.0153 | |
| HMM-R | 0.9847 | 0.0072 | 0.0197 |
| 0.9950 | 0.0049 | 0.0052 |
| Detection Algorithm | Time (s) |
|---|---|
| KNN | 0.0009 |
| SVM | 0.0246 |
| SOM | 0.5576 |
| BP | 119.7 |
| HMM-R | 0.2227 |
| Window | Time (s) |
|---|---|
| 40 | 0.1642 |
| 60 | 0.1700 |
| 100 | 0.2316 |
| Attack Ratio | Time (s) |
|---|---|
| 0.025 | 0.1642 |
| 0.25 | 0.2227 |
| 2.5 | 0.2831 |
© 2018 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Wang, W.; Ke, X.; Wang, L. A HMM-R Approach to Detect L-DDoS Attack Adaptively on SDN Controller. Future Internet 2018, 10, 83. https://doi.org/10.3390/fi10090083
Wang W, Ke X, Wang L. A HMM-R Approach to Detect L-DDoS Attack Adaptively on SDN Controller. Future Internet. 2018; 10(9):83. https://doi.org/10.3390/fi10090083
Chicago/Turabian StyleWang, Wentao, Xuan Ke, and Lingxia Wang. 2018. "A HMM-R Approach to Detect L-DDoS Attack Adaptively on SDN Controller" Future Internet 10, no. 9: 83. https://doi.org/10.3390/fi10090083
APA StyleWang, W., Ke, X., & Wang, L. (2018). A HMM-R Approach to Detect L-DDoS Attack Adaptively on SDN Controller. Future Internet, 10(9), 83. https://doi.org/10.3390/fi10090083




