A Survey of Intellectual Property Rights Protection in Big Data Applications §
Abstract
1. Introduction
- This paper will take a closer look at the unclear boundaries of intellectual property rights in Big Data applications and present different viewpoints on copyright in cross-data platforms.
- This paper addresses real-world case studies of the underlying technology of cross-data analytics with a security policy framework to protect intellectual property rights.
- This paper highlights the main technical solutions for intellectual property protection, including the latest copyright algorithms for multimedia data.
- This paper discusses some important aspects of copyright protection and identifies the main problems and difficulties.
2. Related Work
2.1. Copyright
2.2. Patent
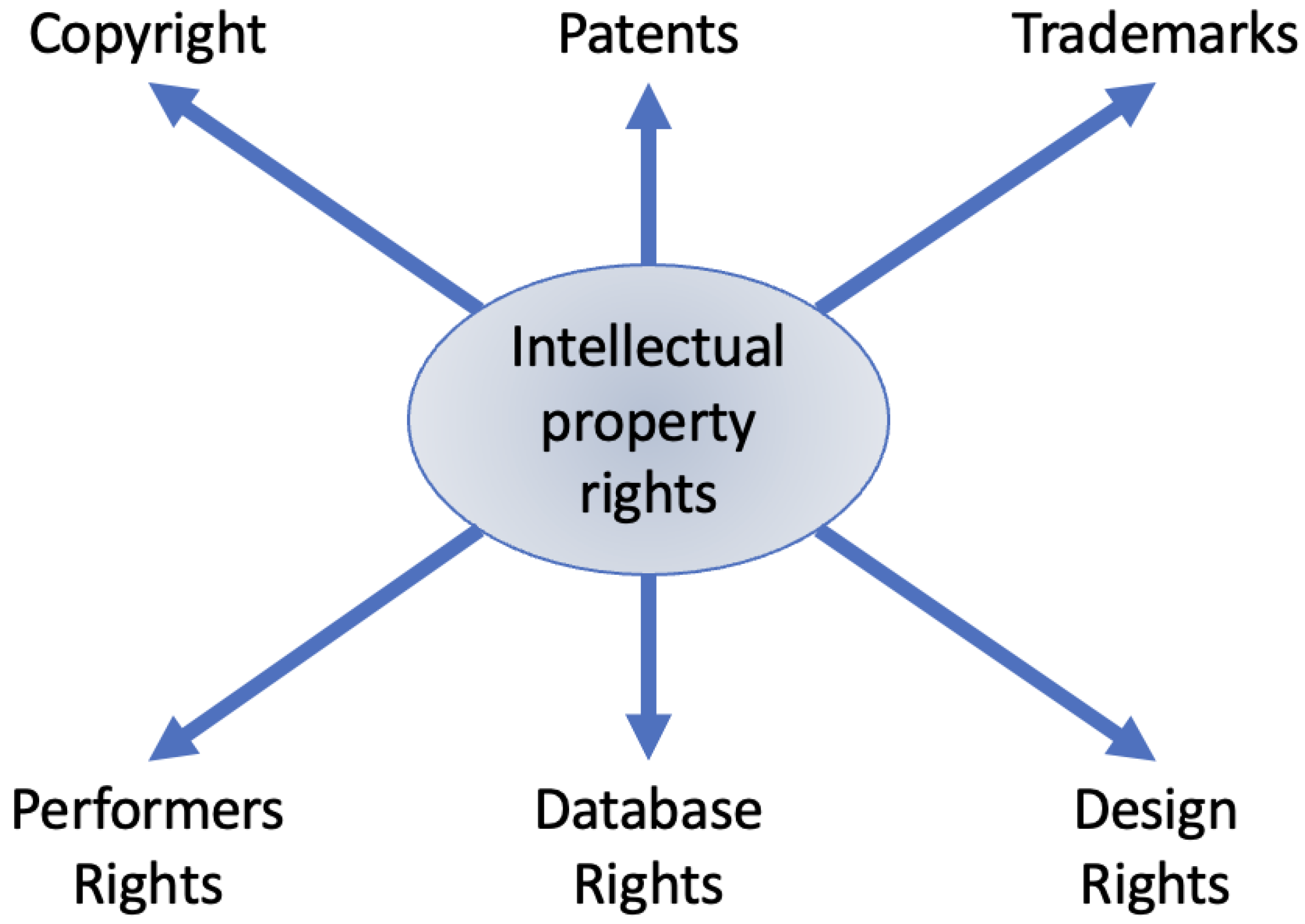
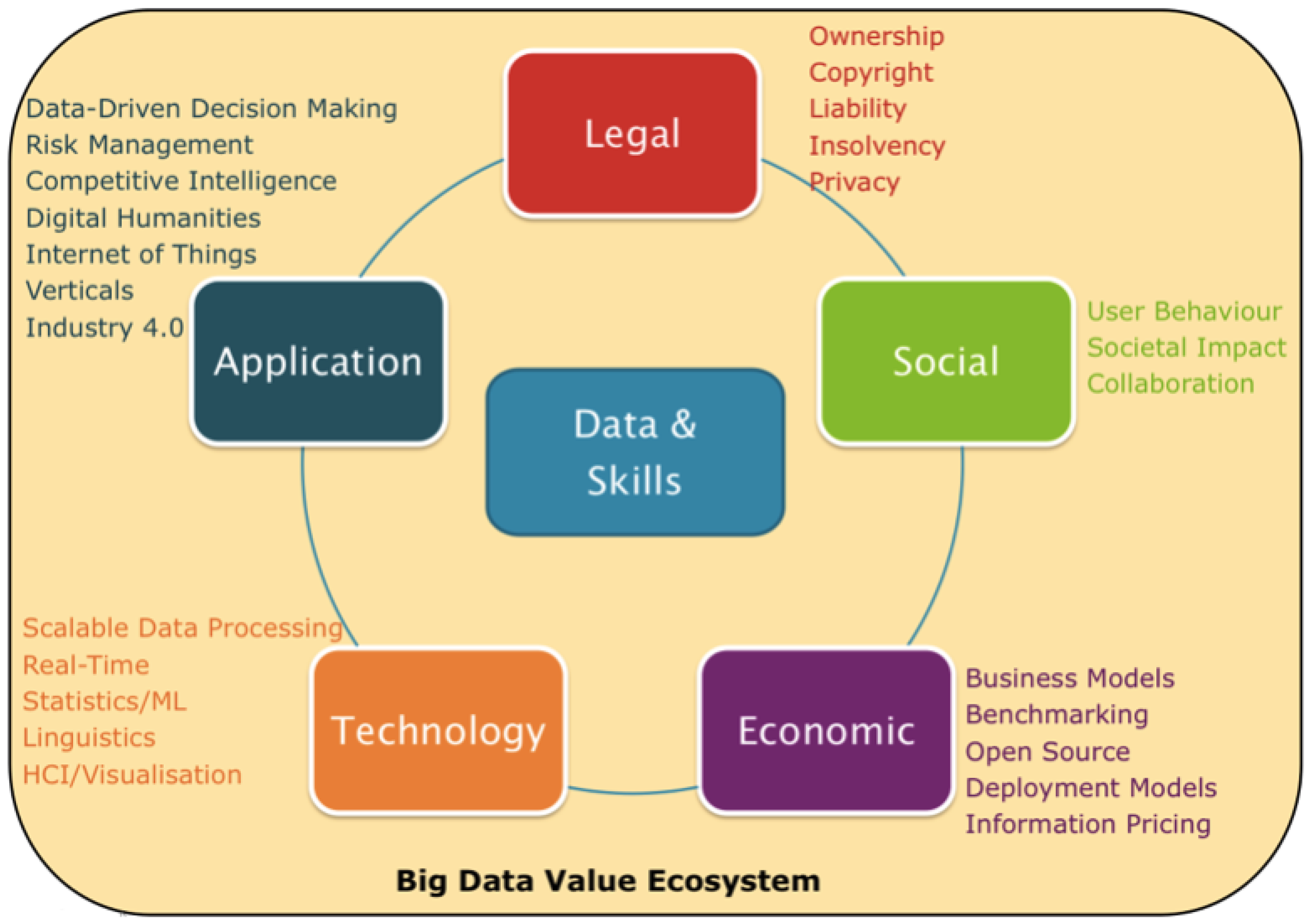
3. Non-Technical Solutions for Protecting Intellectual Property Rights
3.1. Legal Compliance
3.2. The Intellectual Property Rights of the Various Information Assets
3.3. Limitations
4. Technical Solutions for Protecting Intellectual Property Rights
4.1. Fingerprinting Algorithms
4.2. Watermarking Algorithms
4.3. Non-Watermarking Algorithms
5. Discussion
6. Conclusions
Author Contributions
Funding
Data Availability Statement
Conflicts of Interest
References
- Hamza, R.; Dao, M.S. Privacy-preserving deep learning techniques for wearable sensor-based Big Data applications. Virtual Real. Intell. Hardw. 2022, 4, 210–222. [Google Scholar] [CrossRef]
- Aquilani, B.; Piccarozzi, M.; Abbate, T.; Codini, A. The role of open innovation and value co-creation in the challenging transition from industry 4.0 to society 5.0: Toward a theoretical framework. Sustainability 2020, 12, 8943. [Google Scholar] [CrossRef]
- Fukuda, K. Science, technology and innovation ecosystem transformation toward society 5.0. Int. J. Prod. Econ. 2020, 220, 107460. [Google Scholar] [CrossRef]
- Holroyd, C. Technological innovation and building a ‘super smart’society: Japan’s vision of society 5.0. J. Asian Public Policy 2022, 15, 18–31. [Google Scholar] [CrossRef]
- Miragliotta, G.; Sianesi, A.; Convertini, E.; Distante, R. Data driven management in Industry 4.0: A method to measure Data Productivity. IFAC-PapersOnLine 2018, 51, 19–24. [Google Scholar] [CrossRef]
- Taeihagh, A.; Lim, H.S.M. Governing autonomous vehicles: Emerging responses for safety, liability, privacy, cybersecurity, and industry risks. Transp. Rev. 2019, 39, 103–128. [Google Scholar] [CrossRef]
- Nair, M.M.; Tyagi, A.K.; Sreenath, N. The future with industry 4.0 at the core of society 5.0: Open issues, future opportunities and challenges. In Proceedings of the 2021 International Conference on Computer Communication and Informatics (ICCCI), Coimbatore, India, 27–29 January 2021; pp. 1–7. [Google Scholar]
- Hamza, R.; Zettsu, K. Investigation on Privacy-Preserving Techniques For Personal Data. In Proceedings of the 2021 Workshop on Intelligent Cross-Data Analysis and Retrieval, Taipei, Taiwan, 21 August 2021; pp. 62–66. [Google Scholar]
- Liang, G.; Weller, S.R.; Luo, F.; Zhao, J.; Dong, Z.Y. Distributed blockchain-based data protection framework for modern power systems against cyber attacks. IEEE Trans. Smart Grid 2018, 10, 3162–3173. [Google Scholar] [CrossRef]
- Kuzminykh, I.; Carlsson, A.; Yevdokymenko, M.; Sokolov, V. Investigation of the IoT device lifetime with secure data transmission. In Internet of Things, Smart Spaces, and Next Generation Networks and Systems; Springer: Berlin/Heidelberg, Germany, 2019; pp. 16–27. [Google Scholar]
- Hamza, R.; Dao, M.S.; Ito, S.; Koji, Z. Towards Intellectual Property Rights Protection in Big Data. In Proceedings of the 3rd ACM Workshop on Intelligent Cross-Data Analysis and Retrieval, Newark, NJ, USA, 27–30 June 2022; pp. 50–57. [Google Scholar]
- Lu, Y.; Zhu, M. Privacy preserving distributed optimization using homomorphic encryption. Automatica 2018, 96, 314–325. [Google Scholar] [CrossRef]
- Pulido-Gaytan, B.; Tchernykh, A.; Cortés-Mendoza, J.M.; Babenko, M.; Radchenko, G.; Avetisyan, A.; Drozdov, A.Y. Privacy-preserving neural networks with Homomorphic encryption: Challenges and opportunities. Peer-to-Peer Netw. Appl. 2021, 14, 1666–1691. [Google Scholar] [CrossRef]
- Murali, P.; Sankaradass, V. An efficient ROI based copyright protection scheme for digital images with SVD and orthogonal polynomials transformation. Optik 2018, 170, 242–264. [Google Scholar] [CrossRef]
- Devi, B.P.; Singh, K.M.; Roy, S. A copyright protection scheme for digital images based on shuffled singular value decomposition and visual cryptography. SpringerPlus 2016, 5, 1091. [Google Scholar] [CrossRef] [PubMed][Green Version]
- Contreras, G.K.; Nahiyan, A.; Bhunia, S.; Forte, D.; Tehranipoor, M. Security vulnerability analysis of design-for-test exploits for asset protection in SoCs. In Proceedings of the 2017 22nd Asia and South Pacific Design Automation Conference (ASP-DAC), Chiba, Japan, 16–19 January 2017; pp. 617–622. [Google Scholar]
- Zhang, D.Y.; Li, Q.; Tong, H.; Badilla, J.; Zhang, Y.; Wang, D. Crowdsourcing-based copyright infringement detection in live video streams. In Proceedings of the 2018 IEEE/ACM International Conference on Advances in Social Networks Analysis and Mining (ASONAM), Barcelona, Spain, 28–31 August 2018; pp. 367–374. [Google Scholar]
- Hou, K.; Zhang, M. Discussion on legal model of intellectual property of computer software. Proc. J. Phys. Conf. Ser. 2021, 1883, 012011. [Google Scholar] [CrossRef]
- Gürkaynak, G.; Yılmaz, I.; Yeşilaltay, B.; Bengi, B. Intellectual property law and practice in the blockchain realm. Comput. Law Secur. Rev. 2018, 34, 847–862. [Google Scholar] [CrossRef]
- Cai, Z. Usage of deep learning and blockchain in compilation and copyright protection of digital music. IEEE Access 2020, 8, 164144–164154. [Google Scholar] [CrossRef]
- Karjala, D.S. Intellectual Property Rights in Japan and the Protection of Computer Software. In Intellectual Property Rights in Science, Technology, and Economic Performance; Routledge: London, UK, 2019; pp. 277–289. [Google Scholar]
- Melero, E.; Palomeras, N.; Wehrheim, D. The effect of patent protection on inventor mobility. Manag. Sci. 2020, 66, 5485–5504. [Google Scholar] [CrossRef]
- Mansfield, E. Intellectual property, technology and economic growth. In Intellectual Property Rights in Science, Technology, and Economic Performance; Routledge: London, UK, 2019; pp. 17–30. [Google Scholar]
- Fang, L.H.; Lerner, J.; Wu, C. Intellectual property rights protection, ownership, and innovation: Evidence from China. Rev. Financ. Stud. 2017, 30, 2446–2477. [Google Scholar] [CrossRef]
- Lundqvist, B. Big data, open data, privacy regulations, intellectual property and competition law in an internet-of-things world: The issue of accessing data. In Personal Data in Competition, Consumer Protection and Intellectual Property Law; Springer: Berlin/Heidelberg, Germany, 2018; pp. 191–214. [Google Scholar]
- Gervais, D. Exploring the interfaces between Big Data and intellectual property law. J. Intellect. Prop. Inf. Technol. Electron. Commer. Law 2019, 10, 3. [Google Scholar] [CrossRef]
- Liu, C.y.; Hou, C.C. Challenges of Credit Reference Based on Big Data Technology in China. Mob. Netw. Appl. 2022, 27, 47–57. [Google Scholar] [CrossRef]
- Liu, Z.; Shestak, V. Issues of crowdsourcing and mobile app development through the intellectual property protection of third parties. Peer-to-Peer Netw. Appl. 2021, 14, 2618–2625. [Google Scholar] [CrossRef]
- Wang, S. The Solution of Network Intellectual Property Infringement under the Background of Big Data. Proc. J. Phys. Conf. Ser. 2020, 1533, 042048. [Google Scholar] [CrossRef]
- Hoeren, T. Big data and the ownership in data: Recent developments in Europe. Eur. Intellect. Prop. Rev. 2014, 36, 751–754. [Google Scholar]
- Goddard, M. The EU General Data Protection Regulation (GDPR): European regulation that has a global impact. Int. J. Mark. Res. 2017, 59, 703–705. [Google Scholar] [CrossRef]
- Daigle, B.; Khan, M. The EU General Data Protection Regulation: An Analysis of Enforcement Trends by EU Data Protection Authorities. Available online: https://www.usitc.gov/publications/332/journals/jice_gdpr_enforcement.pdf (accessed on 20 September 2022).
- ITGP Team. Eu General Data Protection Regulation (GDPR)—An Implementation and Compliance Guide; IT Governance Ltd.: Ely, UK, 2020. [Google Scholar]
- Abouelmehdi, K.; Beni-Hessane, A.; Khaloufi, H. Big healthcare data: Preserving security and privacy. J. Big Data 2018, 5, 1. [Google Scholar] [CrossRef]
- Hon, W.K. Data Localization Laws and Policy: The EU Data Protection International Transfers Restriction through a Cloud Computing Lens; Edward Elgar Publishing: Cheltenham, UK, 2017. [Google Scholar]
- Cavanillas, J.M.; Curry, E.; Wahlster, W. The Big Data value opportunity. In New Horizons for a Data-Driven Economy; Springer: Berlin/Heidelberg, Germany, 2016; pp. 3–11. [Google Scholar]
- Yoon, C. Theory of planned behavior and ethics theory in digital piracy: An integrated model. J. Bus. Ethics 2011, 100, 405–417. [Google Scholar] [CrossRef]
- Gagliani, G. Cybersecurity, Technological Neutrality, and International Trade Law. J. Int. Econ. Law 2020, 23, 723–745. [Google Scholar] [CrossRef]
- Dornis, T.W. Artificial Intelligence and Innovation: The End of Patent Law As We Know It. Yale J. Law Technol. 2020, 23, 97. [Google Scholar] [CrossRef]
- Shuaib, M.; Daud, S.M.; Alam, S.; Khan, W.Z. Blockchain-based framework for secure and reliable land registry system. Telkomnika 2020, 18, 2560–2571. [Google Scholar] [CrossRef]
- Kim, S.K.; Huh, J.H. Neuron Blockchain Algorithm for Legal Problems in Inheritance of Legacy. Electronics 2020, 9, 1595. [Google Scholar] [CrossRef]
- Rahman, R.; Liu, K.; Kagal, L. From legal agreements to blockchain smart contracts. In Proceedings of the 2020 IEEE International Conference on Blockchain and Cryptocurrency (ICBC), Toronto, ON, Canada, 2–6 May 2020; pp. 1–5. [Google Scholar]
- Mushtaq, S.; Mehraj, S.; Parah, S.A.; Giri, K.J.; Sheikh, J.A. Cultural Heritage Copyright Protection: A blind and robust watermarking technique for heritage images. In Proceedings of the 2022 IEEE 7th International Conference for Convergence in Technology (I2CT), Pune, India, 7–9 April 2022; pp. 1–6. [Google Scholar]
- Parah, S.A.; Sheikh, J.A.; Loan, N.A.; Bhat, G.M. Robust and blind watermarking technique in DCT domain using inter-block coefficient differencing. Digit. Signal Process. 2016, 53, 11–24. [Google Scholar] [CrossRef]
- Ghouti, L. A new perceptual video fingerprinting system. Multimed. Tools Appl. 2018, 77, 6713–6751. [Google Scholar] [CrossRef]
- Li, Y.; Wang, D.; Tang, L. Robust and secure image fingerprinting learned by neural network. IEEE Trans. Circuits Syst. Video Technol. 2019, 30, 362–375. [Google Scholar] [CrossRef]
- Chen, J.; Wang, J.; Peng, T.; Sun, Y.; Cheng, P.; Ji, S.; Ma, X.; Li, B.; Song, D. Copy, right? A testing framework for copyright protection of deep learning models. In Proceedings of the 2022 IEEE Symposium on Security and Privacy (SP), San Francisco, CA, USA, 22–26 May 2022; pp. 824–841. [Google Scholar]
- Saadatpanah, P.; Shafahi, A.; Goldstein, T. Adversarial attacks on copyright detection systems. In Proceedings of the International Conference on Machine Learning. PMLR, Virtual Event, 13–18 July 2020; pp. 8307–8315. [Google Scholar]
- Fatima, M.; Nisar, M.W.; Rashid, J.; Kim, J.; Kamran, M.; Hussain, A. A novel fingerprinting techniqufe for data storing and sharing through clouds. Sensors 2021, 21, 7647. [Google Scholar] [CrossRef] [PubMed]
- Monga, V.; Evans, B.L. Perceptual image hashing via feature points: Performance evaluation and tradeoffs. IEEE Trans. Image Process. 2006, 15, 3452–3465. [Google Scholar] [CrossRef]
- Wei, S.; Zhao, Y.; Zhu, C.; Xu, C.; Zhu, Z. Frame fusion for video copy detection. IEEE Trans. Circuits Syst. Video Technol. 2011, 21, 15–28. [Google Scholar] [CrossRef]
- Mohsenfar, S.; Mosleh, M.; Barati, A. Audio watermarking method using QR decomposition and genetic algorithm. Multimed. Tools Appl. 2013, 74, 759–779. [Google Scholar] [CrossRef]
- Lerch, A. Zplane Development, EAQUAL Evaluate Audio QUALity, Version: 0.1.3. 2012. Available online: http://www.mp3-tech.org/programmer/misc.html (accessed on 20 September 2022).
- Yuan, Z.; Su, Q.; Liu, D.; Zhang, X. A blind image watermarking scheme combining spatial domain and frequency domain. Vis. Comput. 2021, 37, 1867–1881. [Google Scholar] [CrossRef]
- Liu, D.; Su, Q.; Yuan, Z.; Zhang, X. A color watermarking scheme in frequency domain based on quaternary coding. Vis. Comput. 2021, 37, 2355–2368. [Google Scholar] [CrossRef]
- Shen, Y.; Tang, C.; Xu, M.; Chen, M.; Lei, Z. A DWT-SVD based adaptive color multi-watermarking scheme for copyright protection using AMEF and PSO-GWO. Expert Syst. Appl. 2021, 168, 114414. [Google Scholar] [CrossRef]
- Liu, D.; Su, Q.; Yuan, Z.; Zhang, X. A fusion-domain color image watermarking based on Haar transform and image correction. Expert Syst. Appl. 2021, 170, 114540. [Google Scholar] [CrossRef]
- Chen, Y.; Jia, Z.G.; Peng, Y.; Peng, Y.X.; Zhang, D. A new structure-preserving quaternion QR decomposition method for color image blind watermarking. Signal Process. 2021, 185, 108088. [Google Scholar] [CrossRef]
- Mosleh, M.; Setayeshi, S.; Barekatain, B.; Mosleh, M. A Novel Audio Watermarking Scheme Based on Fuzzy Inference System in DCT Domain. Multimed. Tools Appl. 2021, 80, 20423–20447. [Google Scholar] [CrossRef]
- Liu, D.; Su, Q.; Yuan, Z.; Zhang, X. A blind color digital image watermarking method based on image correction and eigenvalue decomposition. Signal Process. Image Commun. 2021, 95, 116292. [Google Scholar] [CrossRef]
- Jing, N.; Liu, Q.; Sugumaran, V. A blockchain-based code copyright management system. Inf. Process. Manag. 2021, 58, 102518. [Google Scholar] [CrossRef]
- Sun, X.C.; Lu, Z.M.; Wang, Z.; Liu, Y.L. A geometrically robust multi-bit video watermarking algorithm based on 2-D DFT. Multimed. Tools Appl. 2021, 80, 13491–13511. [Google Scholar] [CrossRef]
- Wang, B.; Jiawei, S.; Wang, W.; Zhao, P. Image Copyright Protection Based on Blockchain and Zero-Watermark. IEEE Trans. Netw. Sci. Eng. 2022, 9, 2188–2199. [Google Scholar] [CrossRef]
- Halgamuge, M.; Guruge, D. Fair Rewarding Mechanism in Music Industry using Smart Contracts on Public-Permissionless Blockchain. Multimed. Tools Appl. 2022, 81, 1523–1544. [Google Scholar] [CrossRef]
- Wu, X.; Ma, P.; Jin, Z.; Wu, Y.; Ou, W.; Han, W. A Novel Zero-Watermarking Scheme Based on NSCT-SVD and Blockchain for Video Copyright. EURASIP J. Wirel. Commun. Netw. 2022, 20. [Google Scholar] [CrossRef]
- Tien, N.H.; Ngoc, N.M. Comparative Analysis of Advantages and Disadvantages of the Modes of Entrying the International Market. Int. J. Adv. Res. Eng. Manag. 2019, 5, 29–36. [Google Scholar]
- Chandra, G.R.; Liaqat, I.A. Commercialization of intellectual property; an insight for technocrats. In Proceedings of the 2019 International Conference on Automation, Computational and Technology Management (ICACTM), London, UK, 24–26 April 2019; pp. 373–378. [Google Scholar]
- Drahos, P. A Philosophy of Intellectual Property; Routledge: London, UK, 2016. [Google Scholar]
- Drahos, P.; Braithwaite, J. Information Feudalism: Who Owns the Knowledge Economy? Routledge: London, UK, 2017. [Google Scholar]

| Information Assets | Description |
|---|---|
| Contents | Audio, image and visual inputs information (copyright, relevant information, and confidential information when using economic material), consumer history. |
| User information | Private information about the customer (identification, zip code, contact details, date and place of birth, account number, etc.), digital information about the customer, previous transactions, etc. |
| Equipment information | Communication device information (manufacturer, identification, unique driver’s license, etc.), device account credentials, and so on. Operating system monitoring (operating statistics, connection usage status, etc.) specific to each system. |
| Software settings | Configuration information (procedure setting, connection setting, authorization setting, version) and other information specific to each program; computer operating system, middleware, etc. |
| Design data and internal logic | In the planning/design processes, design information of the requirements/design documentation is developed. |
| Management | Security, practices, policy, Process standards: example information security management ISO 27001 |
| Regulation | Non-industry relevant: data protection, competition rules Industry-relevant: commercial, professional services, etc. |
| Contracting for datasets | Contract is priority Effective but restricted (contractual parties only) |
| Intellectual property rights in Big Data | Copyright, database right, confidentiality, patents, trademarks Weak but extensive, intellectual property rights in data uncertain |
| Ref ID | Applications | Goals | Approaches | Evaluation Metric | Limitations |
|---|---|---|---|---|---|
| [54] | Images | To design a color image watermarking algorithm which has high performance and can be applied into different watermarking schemes. | Discrete cosine transform (DCT) and discrete hartley transform (DHT) | PSNR, SSIM, and NC | The effectiveness of proposed method is low when the loss of pixel value after the zoom-out attack. |
| [55] | Images | To design a color image watermarking algorithm which has strong robustness, large watermark capacity, and high security. | Schur decomposition | NC | The proposed system has low accuracy on salt-and-pepper noise attack. |
| [56] | Images | To find the optimal embedding region solutions with multiple different embedding in application to a color multi-watermarking. | Adaptive multiple embedding factors (AMEF), particle swarm optimization and gray wolf optimizer (PSO-GWO), discrete wavelet transform (DWT), singular value decomposition (SVD) | PSNR and CC | The total of the sizes of all the watermarks should be lower than the size of the selected regions in the image. |
| [57] | Images | To focus on simple geometric attacks: cropping, translation, rotation and distortion. | A fusion-domain color watermarking based on Haar transform and image correction | PSNR, SSIM, and NC | the size of both input image and watermark image still needs to be the same. |
| [58] | Images | To integrate RGB channels to obtain the effective way for watermark extraction for increasing computing performance. | quaternion QR decomposition (QQRD) | PSNR, BER, and NC | The resistance of proposed method is limited up to 50% by Gaussian noise and scaling correction. |
| [59] | Audios | To create a compromise method by following robustness, transparency, and capacity. | Fuzzy inference system, singular value decomposition (SVD), and discrete cosine transform (DCT). | SNR and ODG | Proposed scheme is weak againts Addbrumm_2100 attack type. |
| Ref ID | Applications | Goals | Approaches | Evaluation Metric | Limitations |
|---|---|---|---|---|---|
| [61] | Multimedia | To solve the problem of copyright confirmation and protection. | Full nodes and lightweight nodes | Precision and recall | Optimizing the process during extracting eigenvalues to decrease computation time. |
| [62] | Videos | To create a simplification algorithm by direct extraction without performing synchronization for simple geometric attacks. | 2-D DFT (two-dimensional discrete Fourier transform) | PSNR and SSIM | The effectiveness of proposed method is low against frame dropping attacks. |
| [63] | Images | To create the features of de-trusted third parties with combining the fairness and process automation of smart contracts to make up for the shortcomings of the zero-watermarking algorithm. | Blockchain and Zero-Watermark | NC | Due to cost constraints, it is almost impossible to make the absolute credibility of the third party in the digital watermarking technology. |
| [64] | Musics | To address the problem of illegal distribution of copyright-protected music files without the consent of the owners, which has negative consequences in the music industry. | A public-permission-less blockchain | File size vs uploading cost | Smart contracts cannot be able to pull data from off-chain resources; instead, that data should be “pushed” to the smart contract. |
| [65] | Videos | To address poor robustness, weak imperceptibility and difficulty in traceability of the current protection schemes for video copyright | blockchain with two layers: “on-chain” and “off-chain” | NC and Precision ratio | The proposed system has low accuracy on noise attack. |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2022 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Hamza, R.; Pradana, H. A Survey of Intellectual Property Rights Protection in Big Data Applications. Algorithms 2022, 15, 418. https://doi.org/10.3390/a15110418
Hamza R, Pradana H. A Survey of Intellectual Property Rights Protection in Big Data Applications. Algorithms. 2022; 15(11):418. https://doi.org/10.3390/a15110418
Chicago/Turabian StyleHamza, Rafik, and Hilmil Pradana. 2022. "A Survey of Intellectual Property Rights Protection in Big Data Applications" Algorithms 15, no. 11: 418. https://doi.org/10.3390/a15110418
APA StyleHamza, R., & Pradana, H. (2022). A Survey of Intellectual Property Rights Protection in Big Data Applications. Algorithms, 15(11), 418. https://doi.org/10.3390/a15110418






