A Distributed Approach to the Evasion Problem
Abstract
1. Introduction
- We adapt the algorithm from [2] to a distributed computing setting, where each mobile sensor only needs to track their neighbors.
- We propose an algorithm for enumerating possible evasion paths up to homotopy.
2. Materials and Methods
2.1. Previous Algorithm for the Evasion Problem
2.1.1. Network Assumptions and Problem Formulation
2.1.2. Adams’ Algorithm
| Algorithm 1 Adams’ Evasion Detection algorithm. This algorithm was described in [2]. |
Input: A collection N of coordinates of sensing nodes with coverage radius r. Output: True if evasion is possible, False otherwise.
|
2.2. Distributing the Algorithm
| Algorithm 2 Distributed Evasion Detection. |
|
2.2.1. Tracked Information
- Its own location
- Locations of its neighbors and the neighbors’ neighbors
- A Voronoi diagram of these locations
- A Delaunay complex of these locations
- An -complex generated by the Delaunay complex and the sensing range
- For each region in the (planar) -complex graph,
- -
- Whether that region is labelled False or True
- -
- What the nodes along the boundary of that region are
- A list of neighbors in the Delaunay graph
- A list of neighbors in the -complex
- A list of two-hop neighbors in the -complex
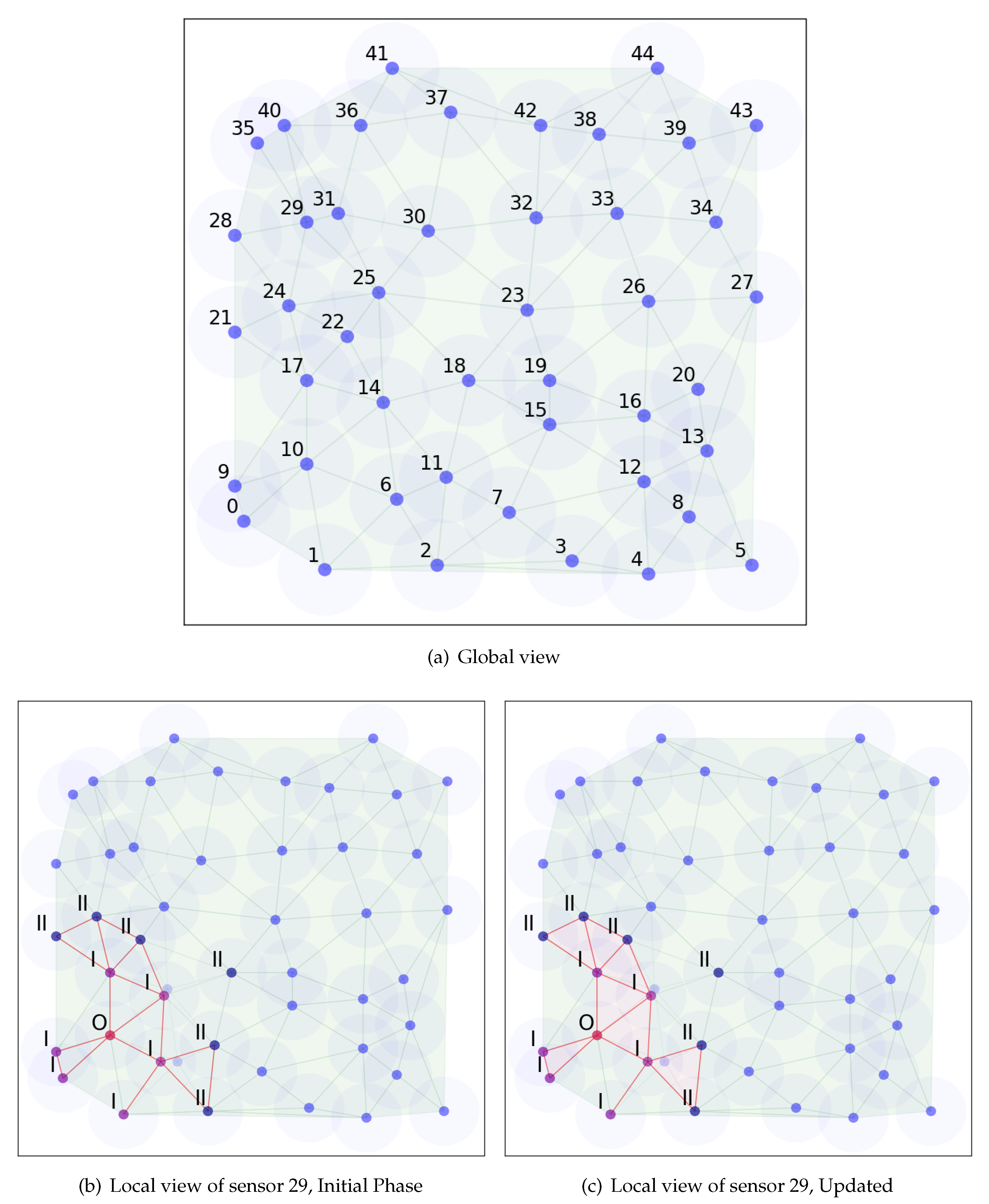
2.2.2. Initial Phase
2.2.3. Location Update
2.2.4. Event-Driven Messages
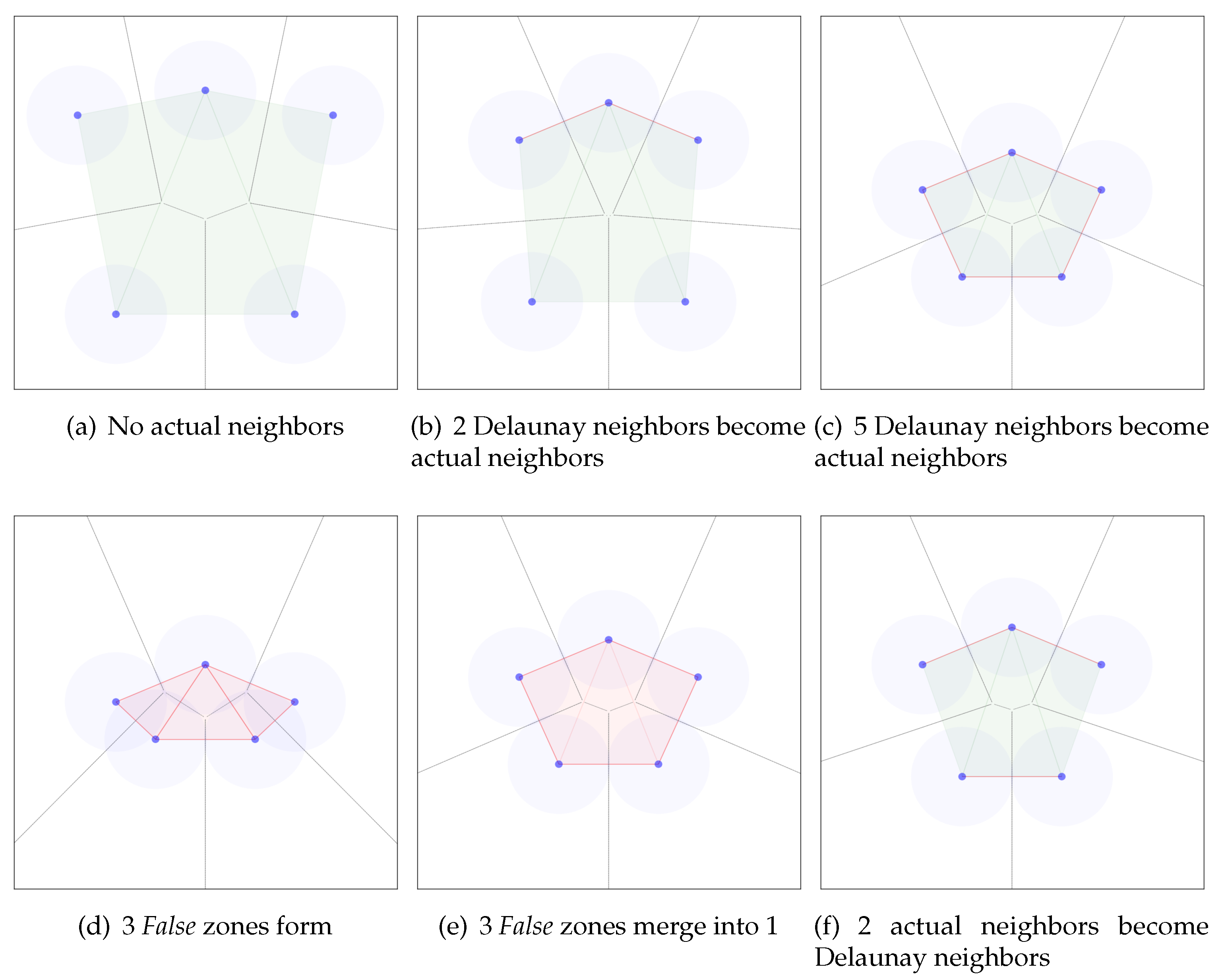
2.2.5. Neighbor Changes
2.2.6. Edge Changes
2.2.7. Region Changes
2.2.8. Routing Protocol
2.2.9. Examples
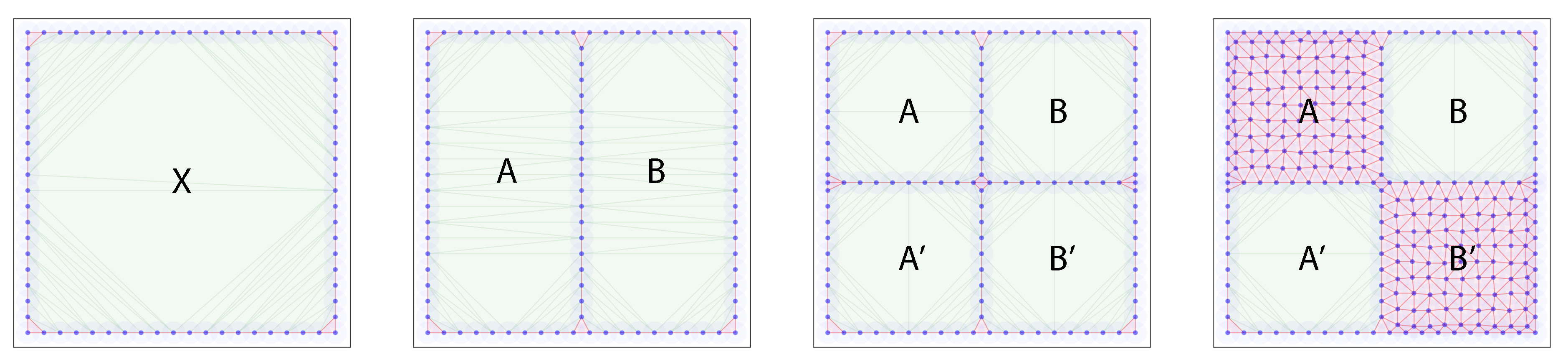
2.3. Two Hop Neighbors Suffice
2.4. Enumerating Evasion Paths
2.4.1. Backwards Propagation
| Algorithm 3 Evasion paths enumeration through backward propagation. |
Given: A full history of an Evasion Detection using either Algorithm 1 or Algorithm 2.
|
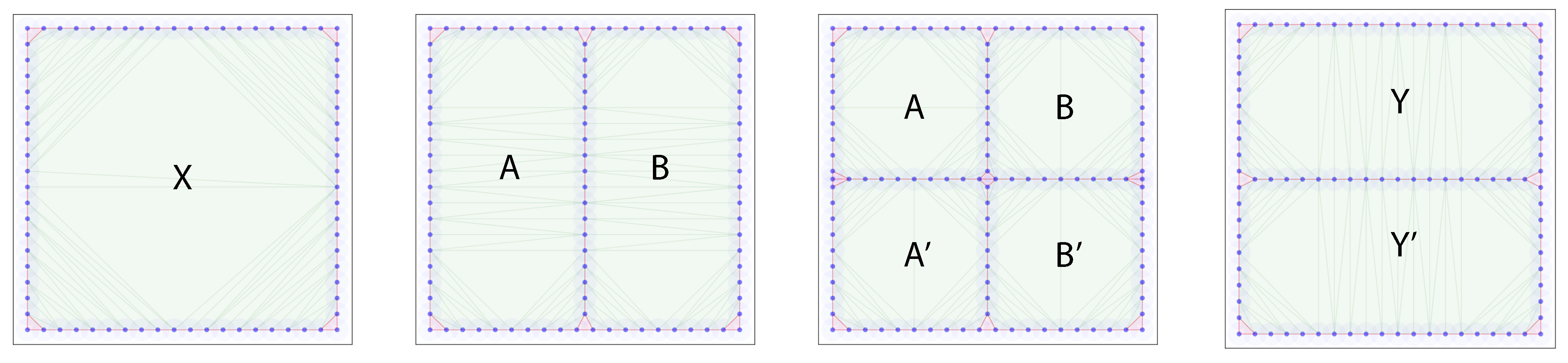
2.4.2. Forwards Propagation
| Algorithm 4 Evasion paths enumeration through forward propagation. |
|
2.4.3. Examples
| Time step | Evasion path list |
| 1 | |
| 2 | , |
| 3 | , , , |
| 4 | , |
| Time step | Evasion path list |
| 4 | , |
| 3 | , , , |
| 2 | , , , |
| 1 | , , , |
3. Discussion
Author Contributions
Funding
Conflicts of Interest
References
- De Silva, V.; Ghrist, R. Coordinate-Free Coverage in Sensor Networks with Controlled Boundaries via Homology. Int. J. Robot. Res. 2006, 25, 1205–1222. [Google Scholar] [CrossRef]
- Adams, H.; Carlsson, G. Evasion paths in mobile sensor networks. Int. J. Robot. Res. 2015, 34, 90–104. [Google Scholar] [CrossRef]
- Ghrist, R.; Krishnan, S. Positive Alexander Duality for Pursuit and Evasion. SIAM J. Appl. Algebra Geom. 2017, 1, 308–327. [Google Scholar] [CrossRef]
- Zhu, C.; Zheng, C.; Shu, L.; Han, G. A survey on coverage and connectivity issues in wireless sensor networks. J. Netw. Comput. Appl. 2012, 35, 619–632. [Google Scholar] [CrossRef]
- Mohamed, S.M.; Hamza, H.S.; Saroit, I.A. Coverage in Mobile Wireless Sensor Networks (M-WSN). Comput. Commun. 2017, 110, 133–150. [Google Scholar] [CrossRef]
- Zhang, H.; Hou, J.C. Maintaining sensing coverage and connectivity in large sensor networks. Ad Hoc Sens. Wirel. Netw. 2005, 1, 89–124. [Google Scholar]
- Huang, C.F.; Tseng, Y.C. The Coverage Problem in a Wireless Sensor Network. Mob. Netw. Appl. 2005, 10, 519–528. [Google Scholar] [CrossRef]
- Wang, X.; Xing, G.; Zhang, Y.; Lu, C.; Pless, R.; Gill, C. Integrated coverage and connectivity configuration in wireless sensor networks. In Proceedings of the 1st International Conference on Embedded Networked Sensor Systems, Los Angeles, CA, USA, 5–7 November 2003; pp. 28–39. [Google Scholar]
- Chaudhary, M.; Pujari, A.K. Q-Coverage Problem in Wireless Sensor Networks. In Distributed Computing and Networking; Garg, V., Wattenhofer, R., Kothapalli, K., Eds.; Springer: Berlin, Germany, 2009; pp. 325–330. [Google Scholar]
- Tao, D.; Wu, T.Y. A Survey on Barrier Coverage Problem in Directional Sensor Networks. IEEE Sens. J. 2015, 15, 876–885. [Google Scholar]
- Li, M.; Cheng, W.; Liu, K.; He, Y.; Li, X.; Liao, X. Sweep Coverage with Mobile Sensors. IEEE Trans. Mob. Comput. 2011, 10, 1534–1545. [Google Scholar]
- De Silva, V.; Ghrist, R. Coverage in Sensor Networks via Persistent Homology. Algebr. Geomet. Topol. 2007, 7, 339–358. [Google Scholar] [CrossRef]
- De Silva, V.; Ghrist, R. Homological Sensor Networks. Not. Am. Math. Soc. 2007, 54, 10–17. [Google Scholar]
- Dłotko, P.; Ghrist, R.; Juda, M.; Mrozek, M. Distributed computation of coverage in sensor networks by homological methods. Appl. Algebra Eng. Commun. Comput. 2012, 23, 29–58. [Google Scholar] [CrossRef]
- Gamble, J.; Chintakunta, H.; Krim, H. Applied Topology in Static and Dynamic Sensor Networks. In Proceedings of the International Conference on Signal Processing and Communications (SPCOM), Bangalore, India, 22–25 July 2012; pp. 1–5. [Google Scholar]
- Senouci, M.R.; Mellouk, A.; Asnoune, K.; Bouhidel, F.Y. Movement-Assisted Sensor Deployment Algorithms: A Survey and Taxonomy. IEEE Commun. Surv. Tutor. 2015, 17, 2493–2510. [Google Scholar] [CrossRef]
- Senouci, M.R.; Mellouk, A.; Assnoune, K. Localized Movement-Assisted SensorDeployment Algorithm for HoleDetection and Healing. IEEE Trans. Parallel. Distr. Syst. 2014, 25, 1267–1277. [Google Scholar] [CrossRef]
- Alsalih, W.; Islam, K.; Núñez Rodríguez, Y.; Xiao, H. Distributed Voronoi Diagram Computation in Wireless Sensor Networks. In Proceedings of the Twentieth Annual Symposium on Parallelism in Algorithms and Architectures, New York, NY, USA, 14–16 June 2008; p. 364. [Google Scholar]
- Karp, B.; Kung, H.T. GPSR: Greedy perimeter stateless routing for wireless networks. In Proceedings of the 6th annual international conference on Mobile computing and networking, Boston, MA, USA, 1 August 2000; pp. 243–254. [Google Scholar]
- Lingas, A. A linear-time construction of the relative neighborhood graph from the Delaunay triangulation. Comput. Geom. 1994, 4, 199–208. [Google Scholar] [CrossRef]
- Edelsbrunner, H. Geometry and Topology for Mesh Generation; Cambridge University Press: Cambridge, UK, 2001. [Google Scholar]
| Symbols | Events |
|---|---|
| Del- | a Delaunay-edge becomes an -edge. |
| -Del | an -edge becomes a Delaunay-edge. |
| + | a triangle is added (Voronoi vertex is within of all vertices). |
| - | a triangle disappears. |
| Nbr+ | a new Delaunay neighbor appears. |
| Nbr- | a Delaunay neighbor disappears. |
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Khryashchev, D.; Chu, J.; Vejdemo-Johansson, M.; Ji, P. A Distributed Approach to the Evasion Problem. Algorithms 2020, 13, 149. https://doi.org/10.3390/a13060149
Khryashchev D, Chu J, Vejdemo-Johansson M, Ji P. A Distributed Approach to the Evasion Problem. Algorithms. 2020; 13(6):149. https://doi.org/10.3390/a13060149
Chicago/Turabian StyleKhryashchev, Denis, Jie Chu, Mikael Vejdemo-Johansson, and Ping Ji. 2020. "A Distributed Approach to the Evasion Problem" Algorithms 13, no. 6: 149. https://doi.org/10.3390/a13060149
APA StyleKhryashchev, D., Chu, J., Vejdemo-Johansson, M., & Ji, P. (2020). A Distributed Approach to the Evasion Problem. Algorithms, 13(6), 149. https://doi.org/10.3390/a13060149





