The Fast Detection and Identification Algorithm of Optical Fiber Intrusion Signals
Abstract
1. Introduction
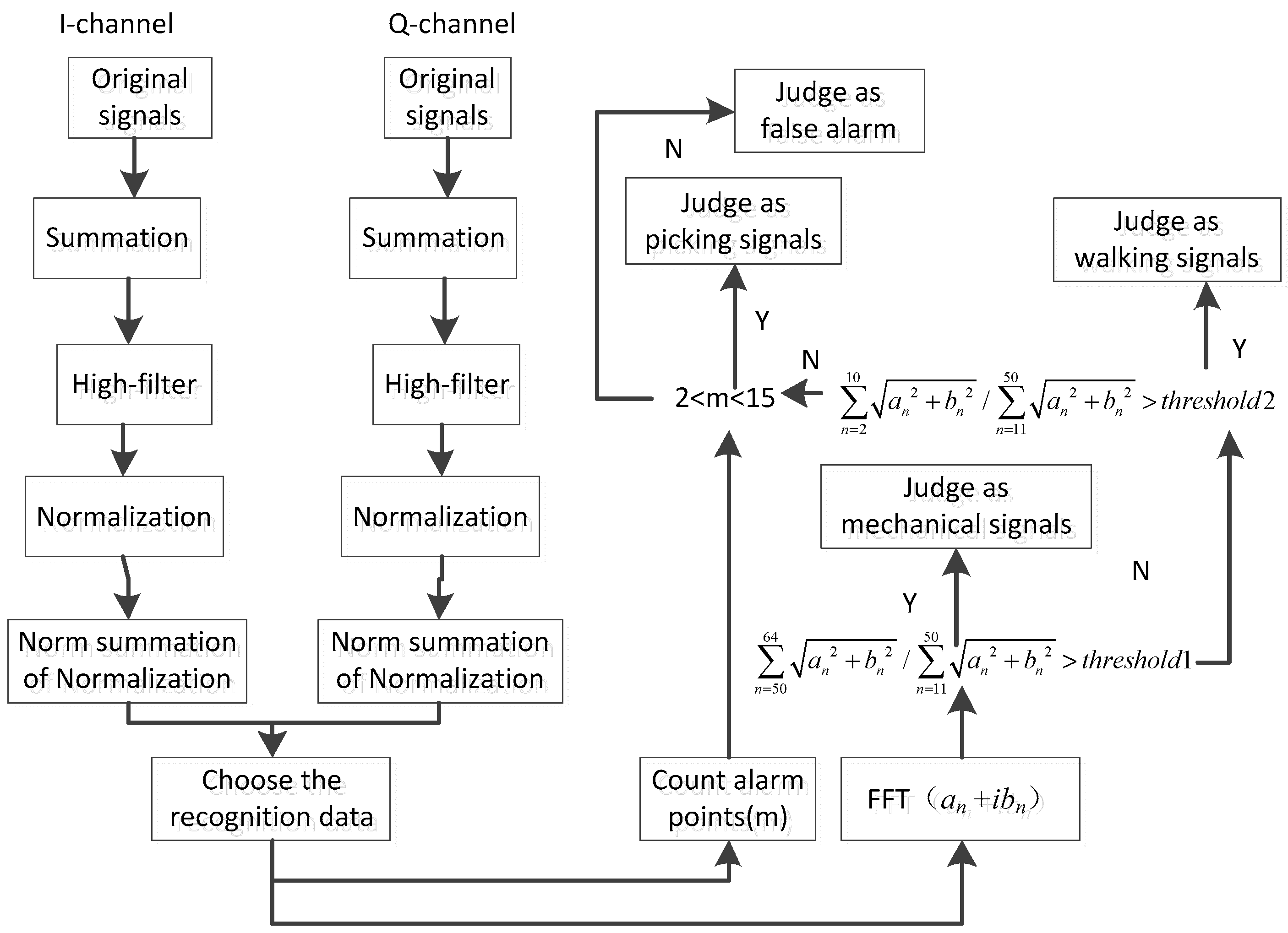
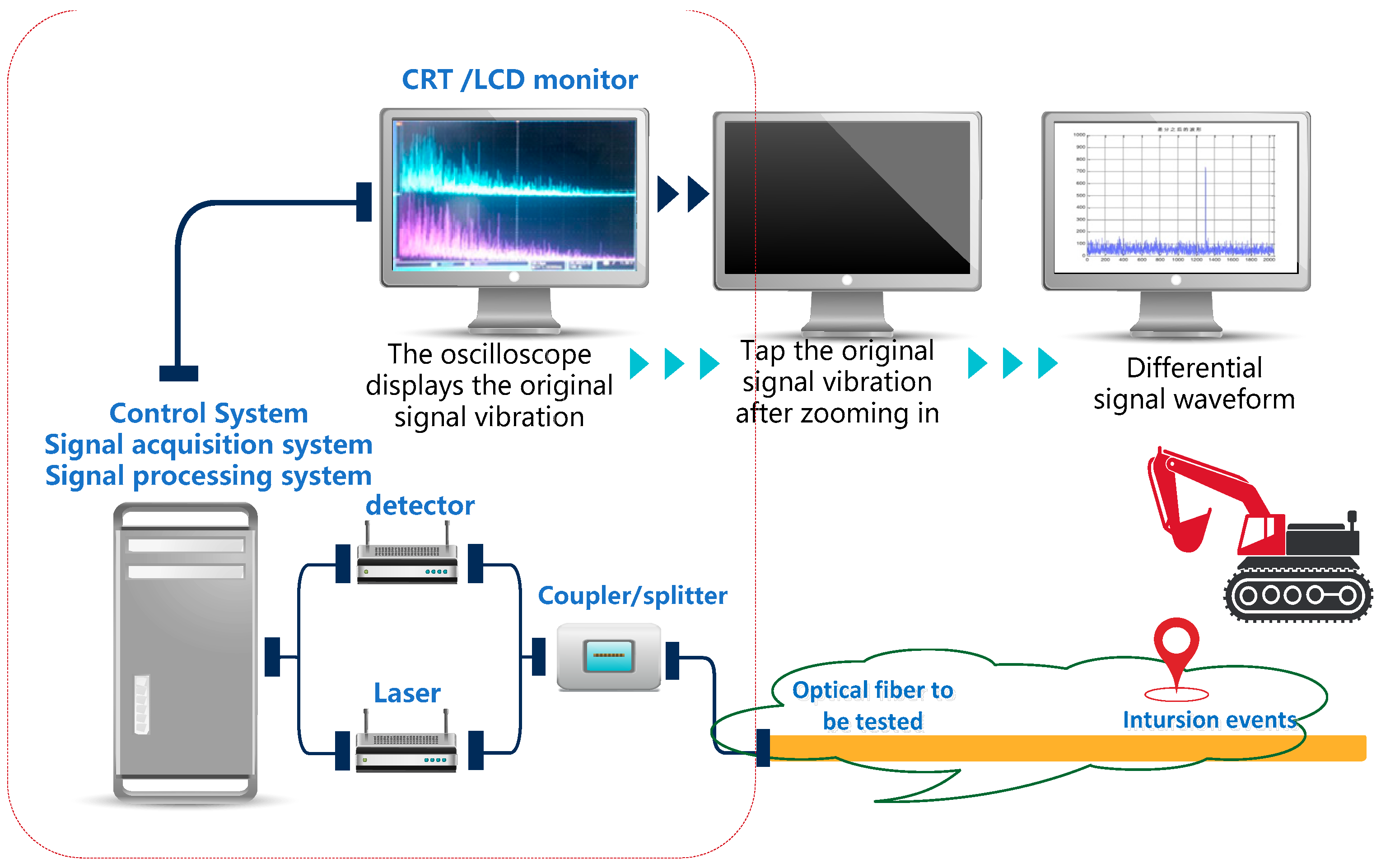
2. Design of Fast Detection and Identification Algorithm for Optical Fiber Intrusion Signals
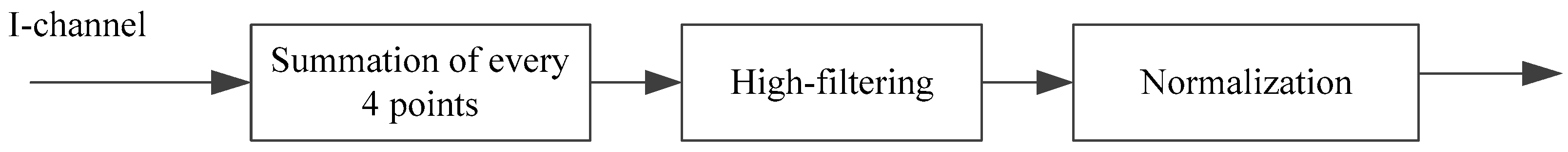
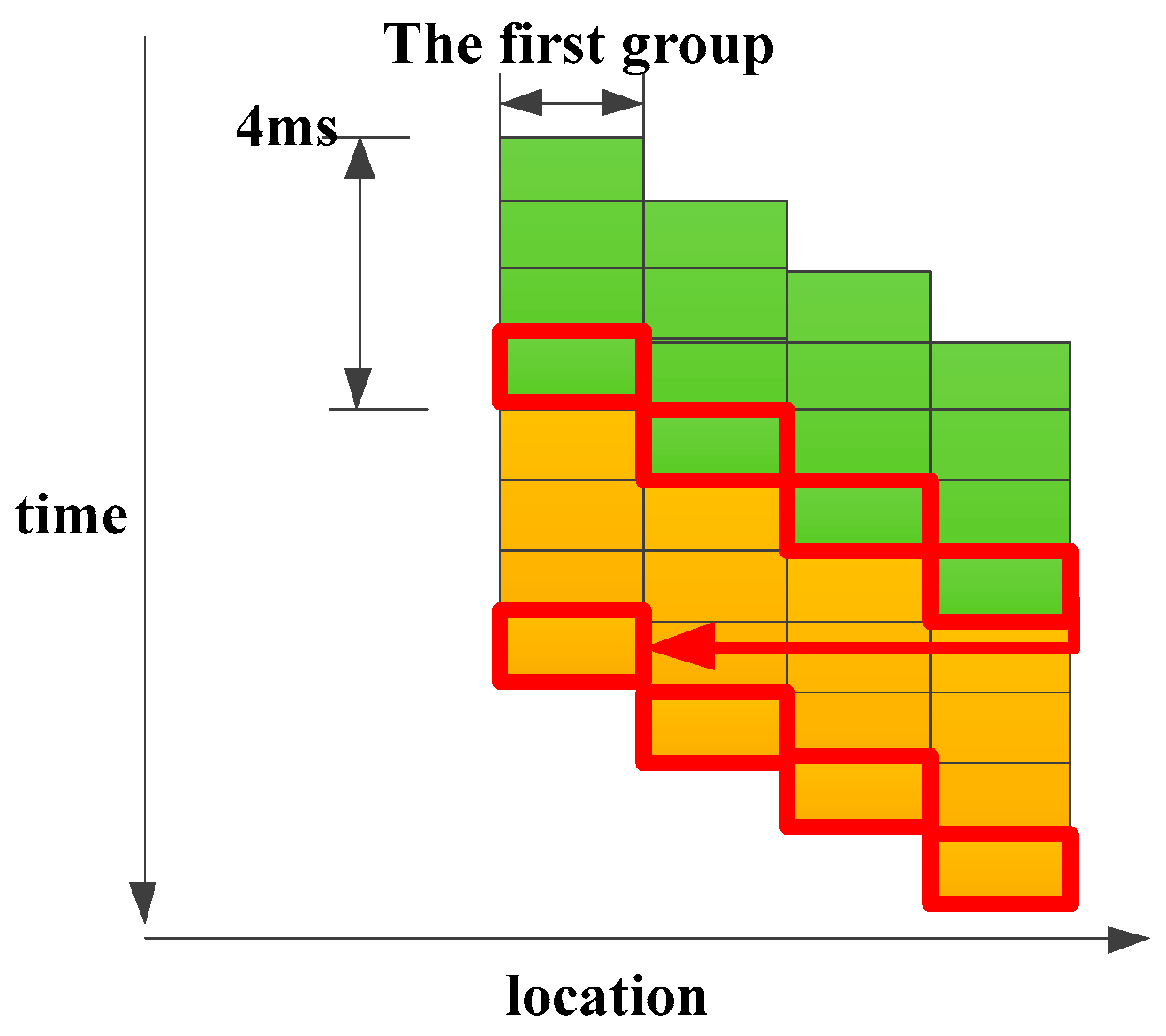
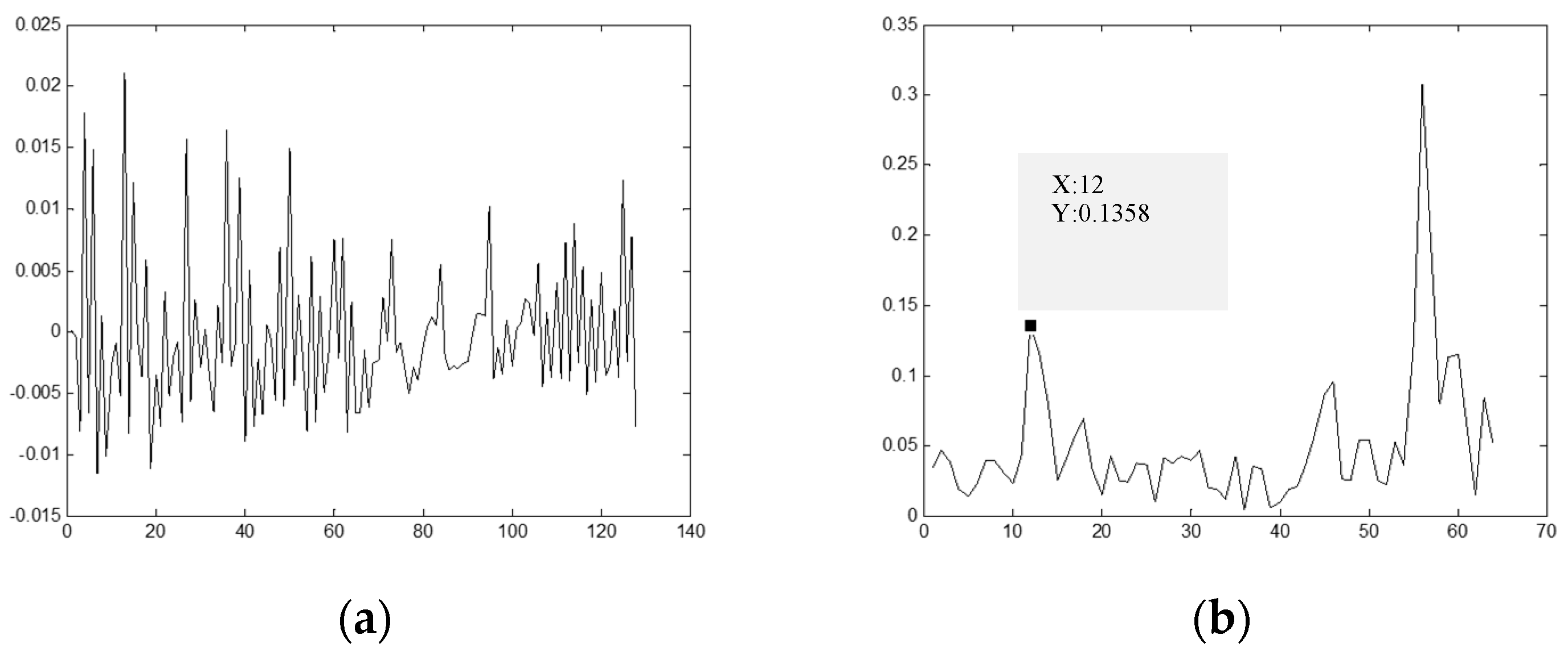
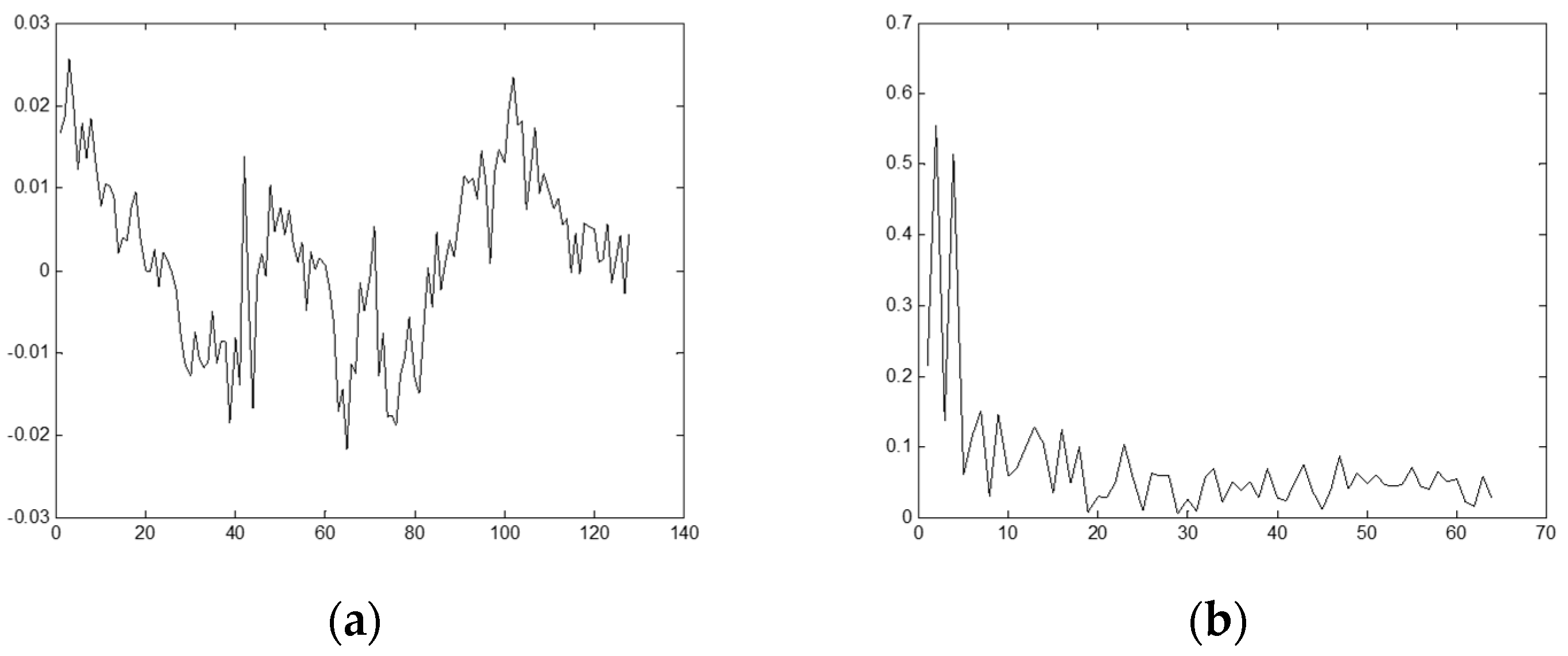
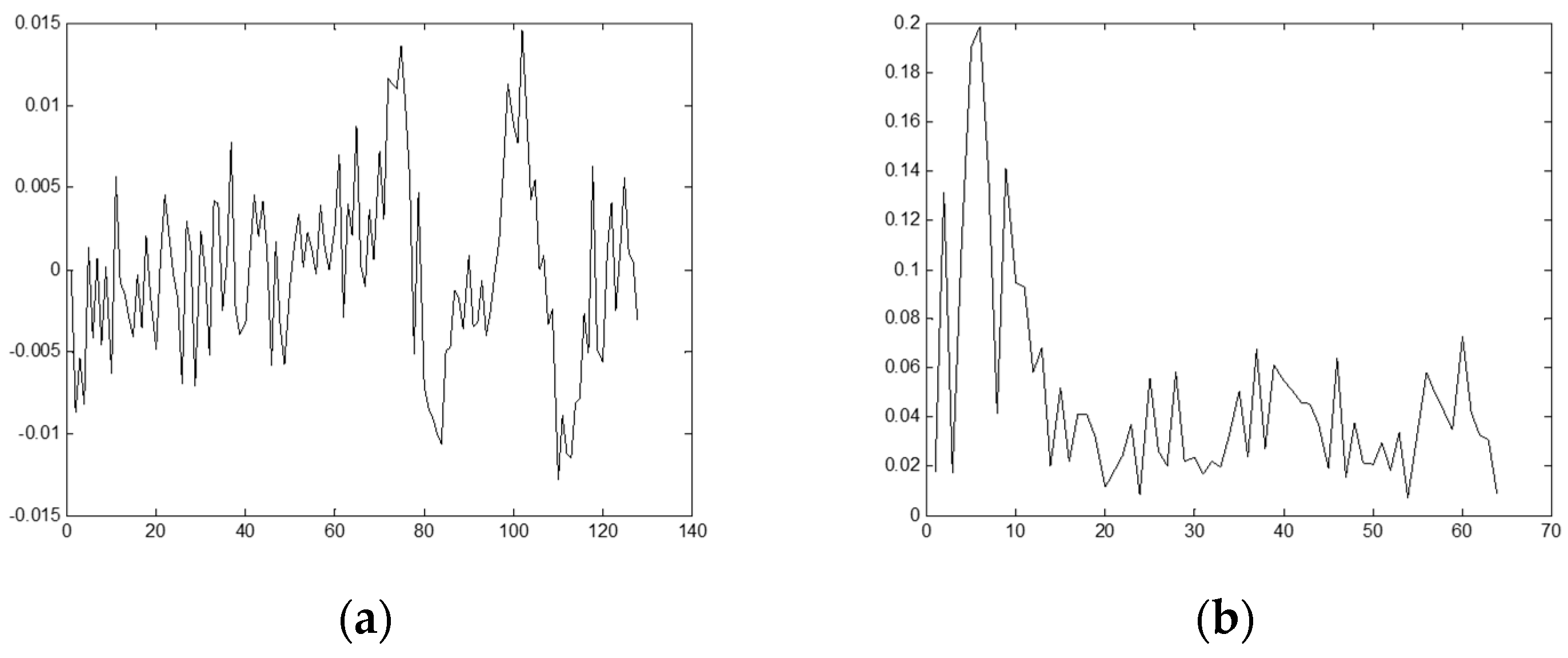
2.1. Single-Channel Detection Algorithm
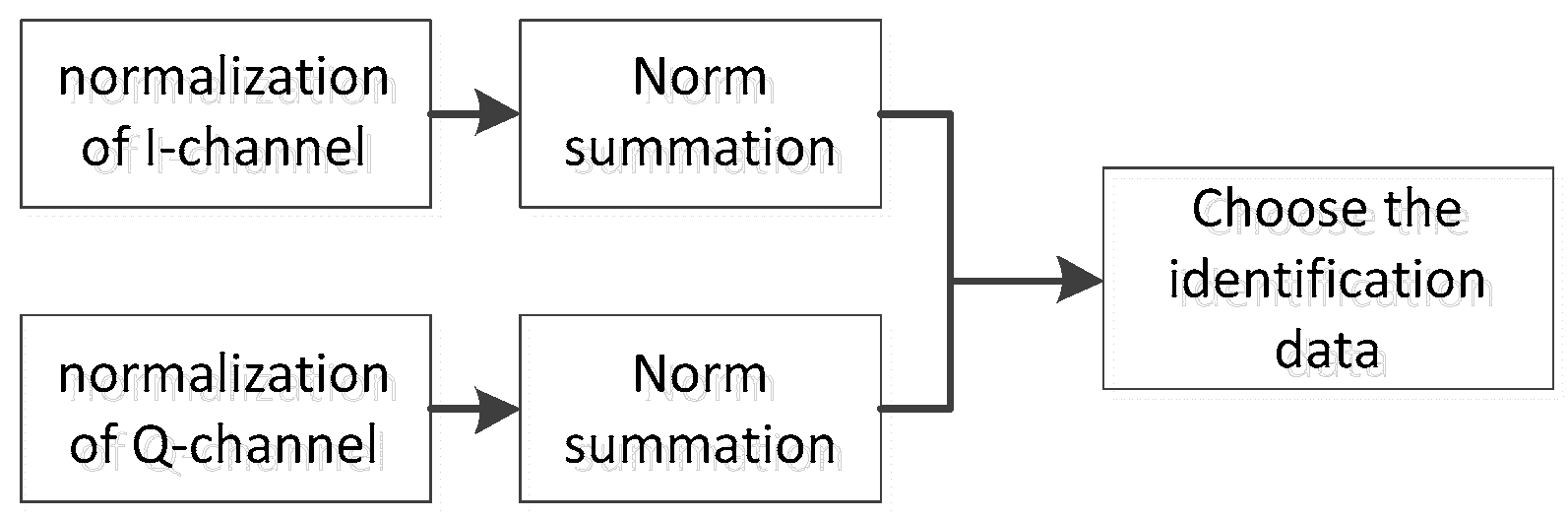
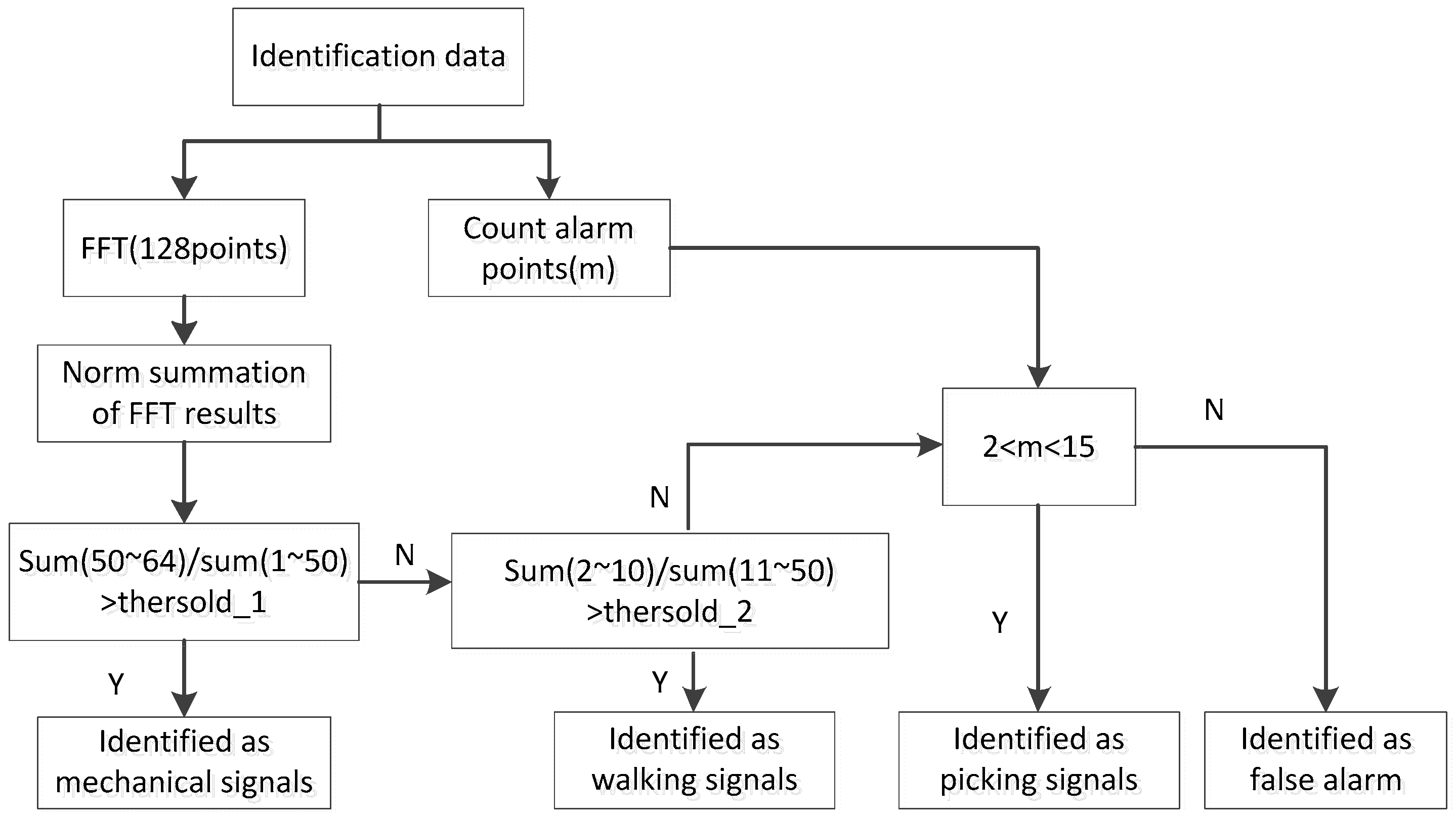
2.2. Feature Extraction and Identification
3. The Implementation of Recognition Algorithm and the Experimental Analysis
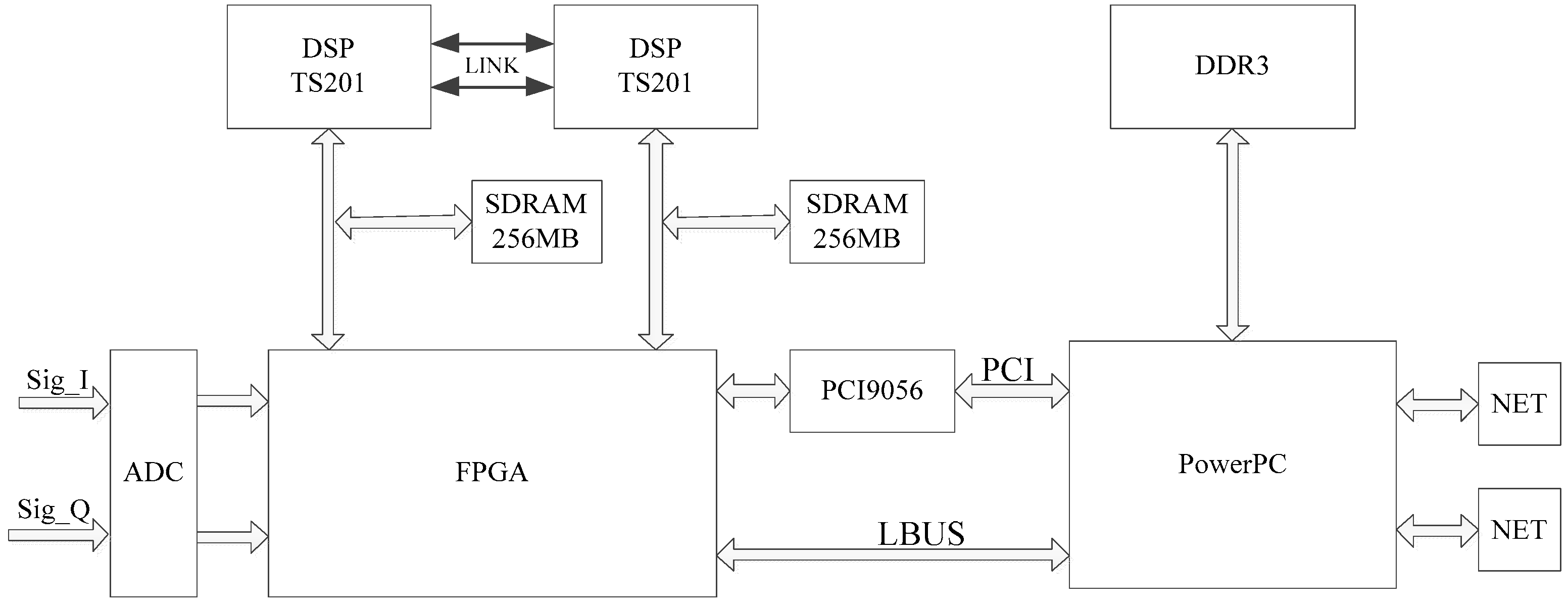
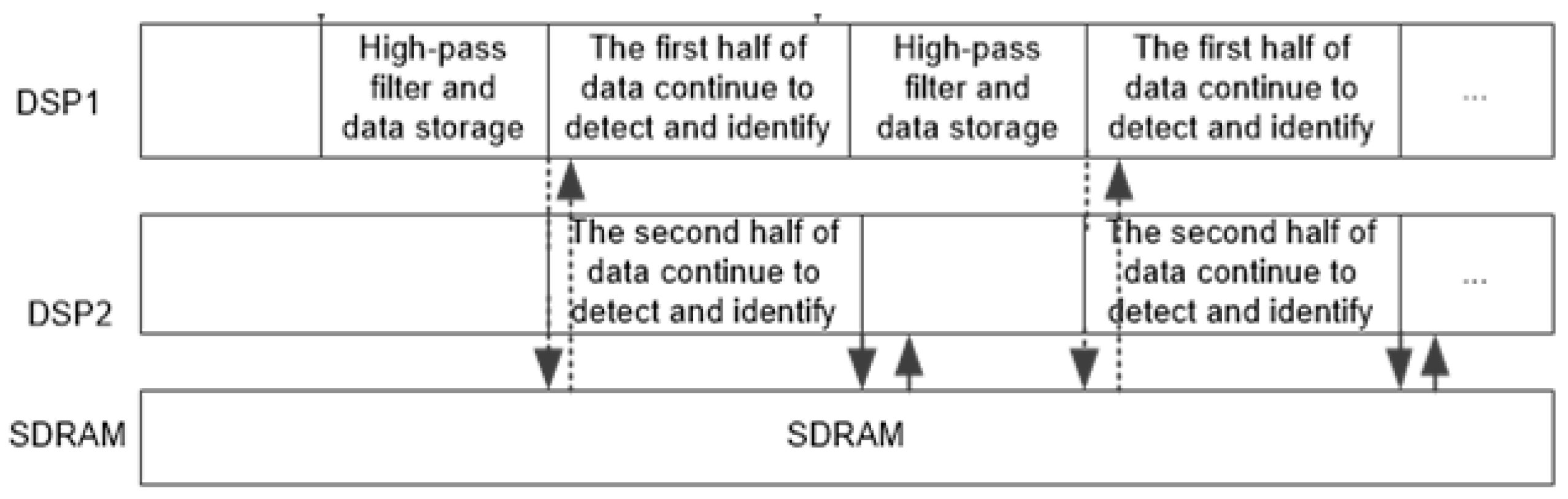
3.1. The Implementation of Fast Identification Algorithm
3.2. Experiment Analysis of Actual Data
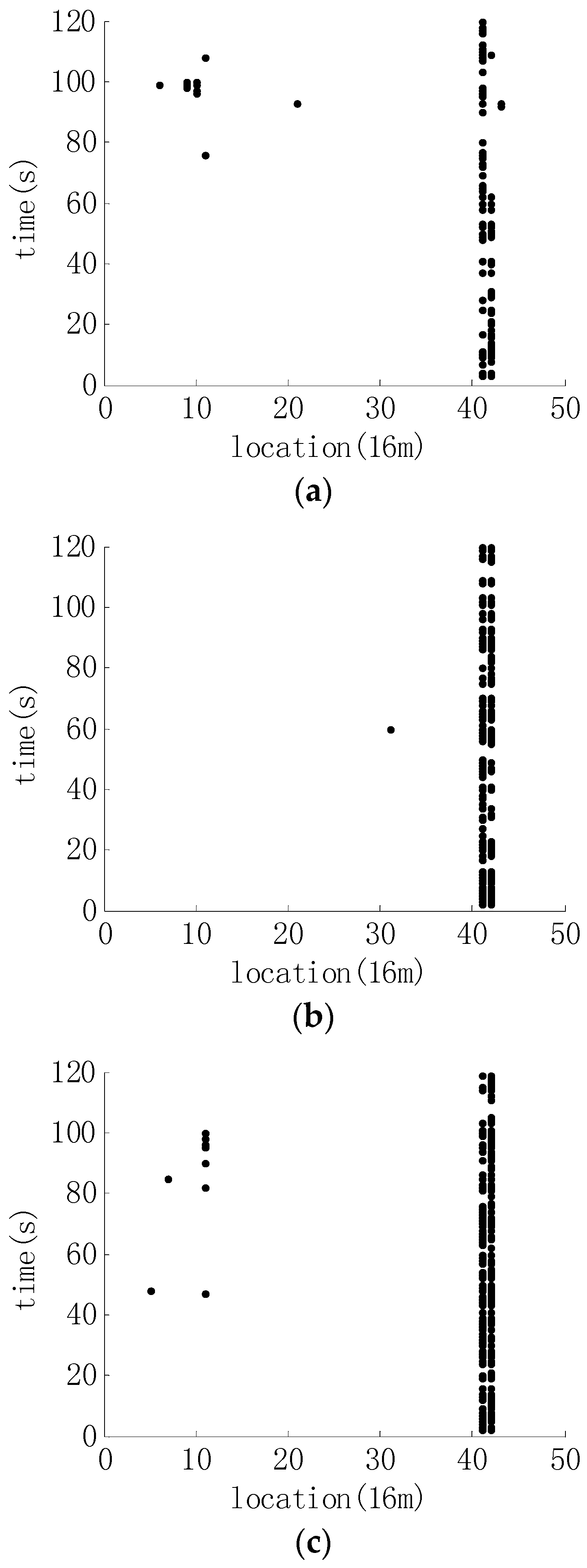
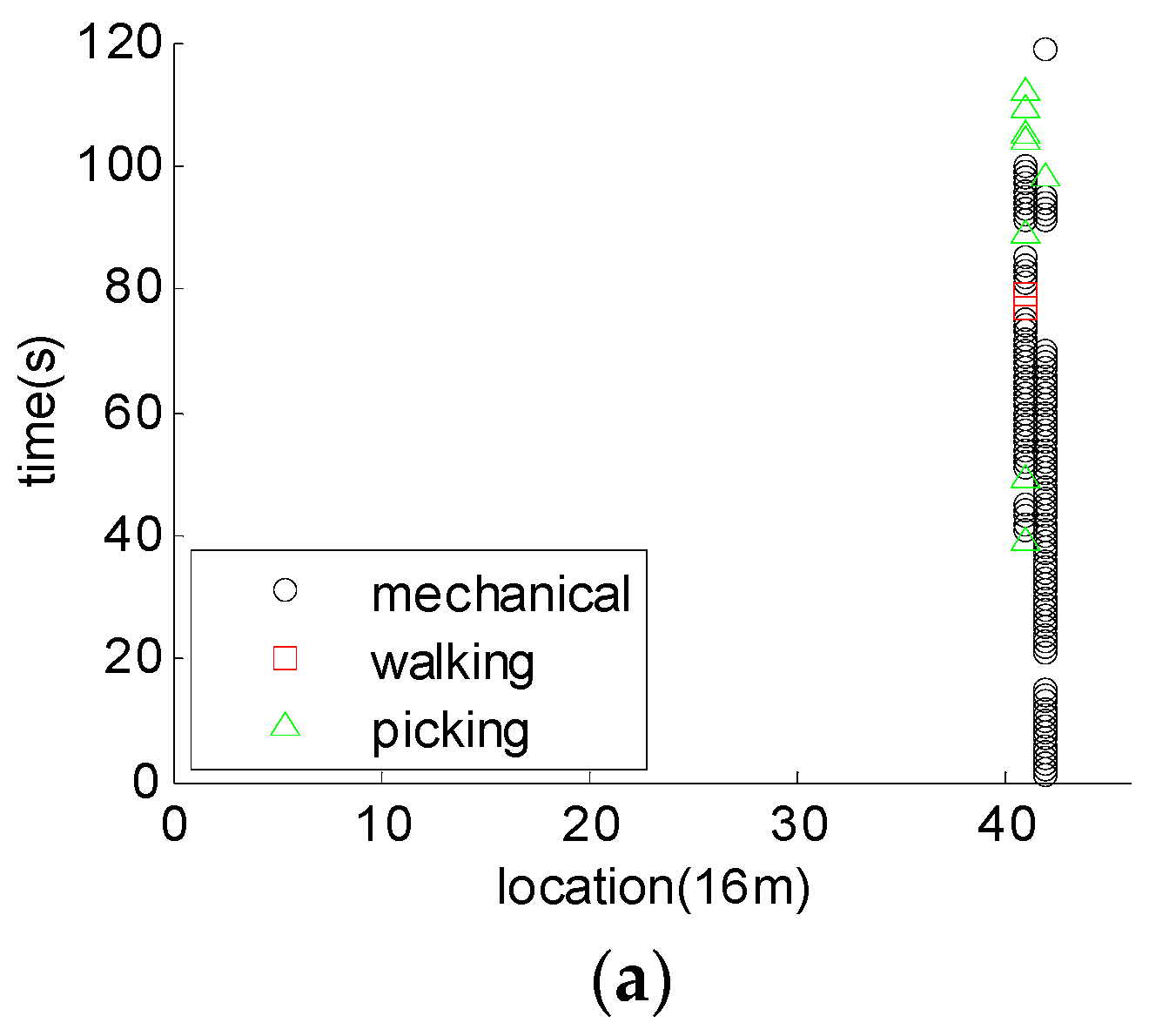
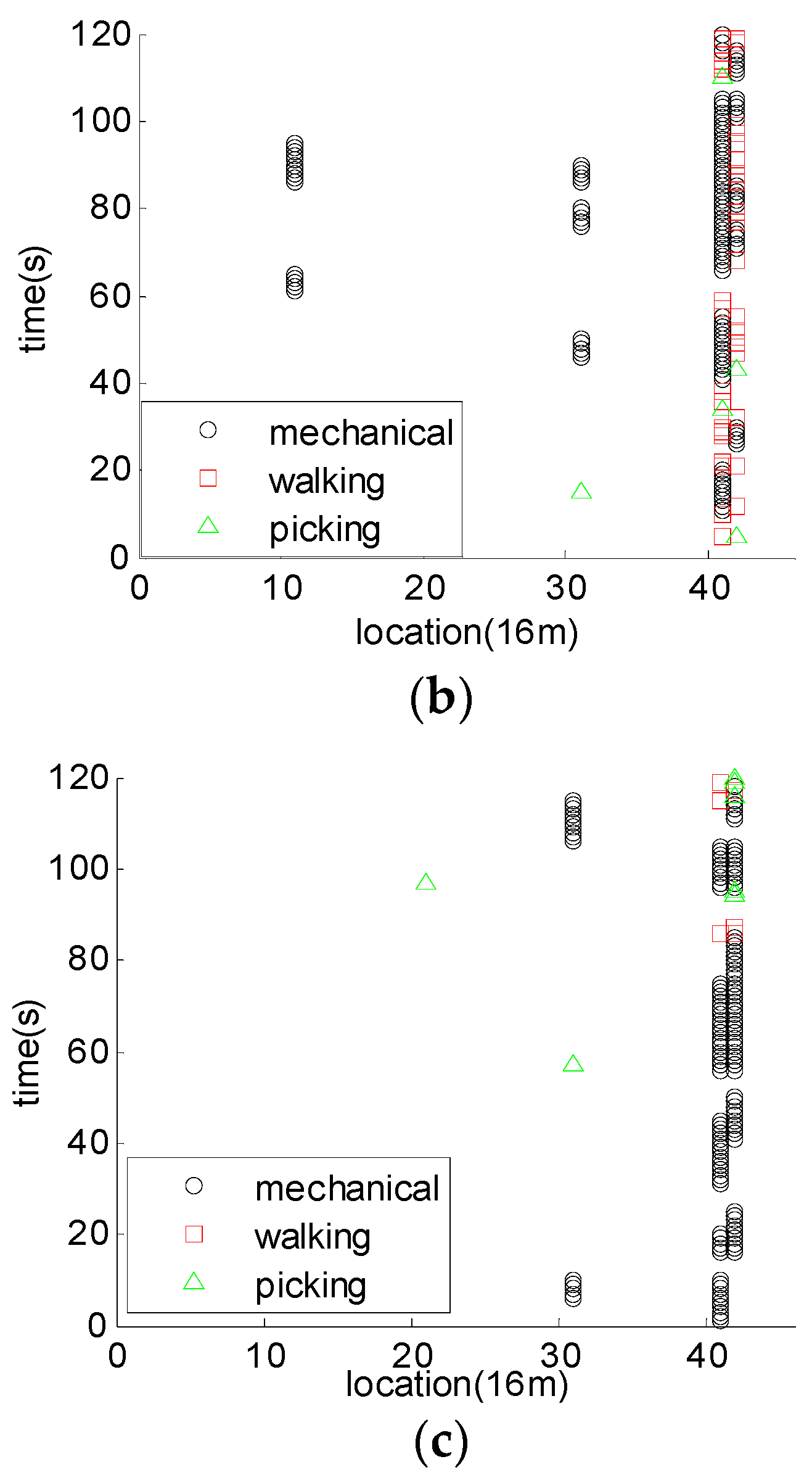
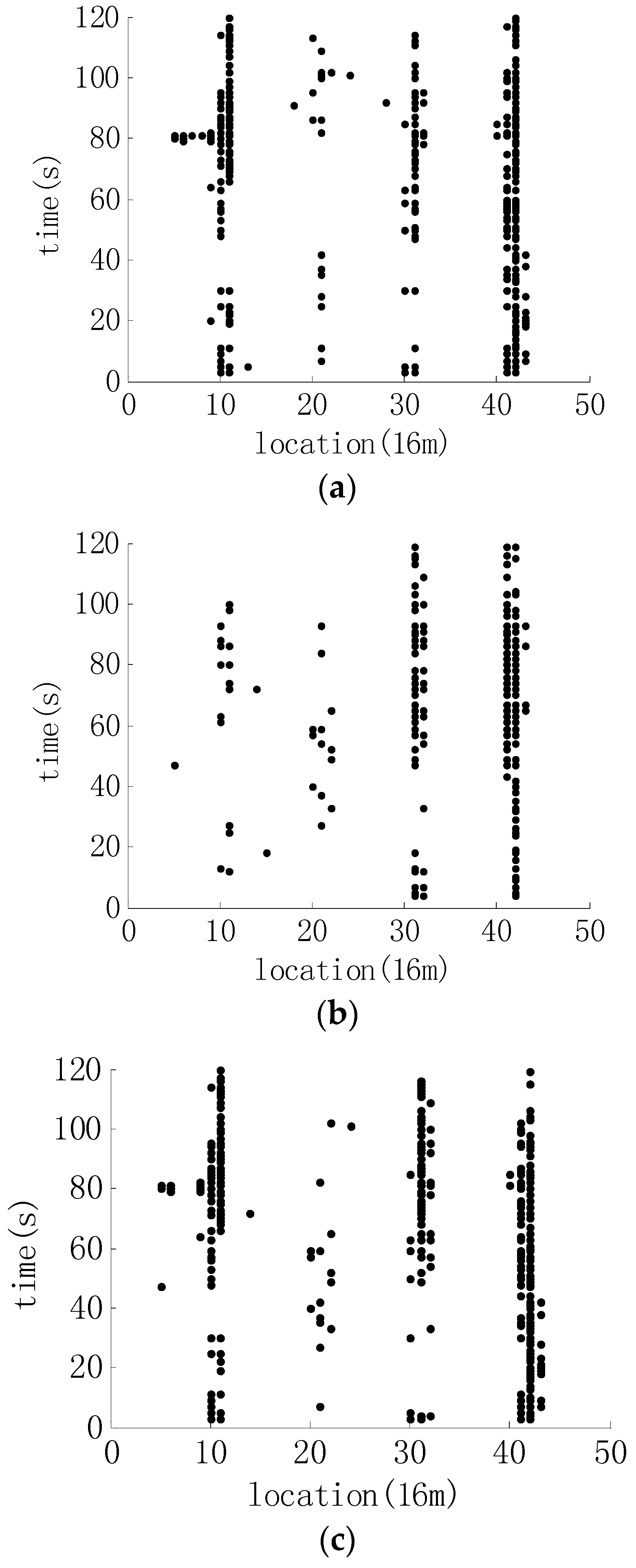
3.2.1. The Detection and Identification Results of Mechanical Signals
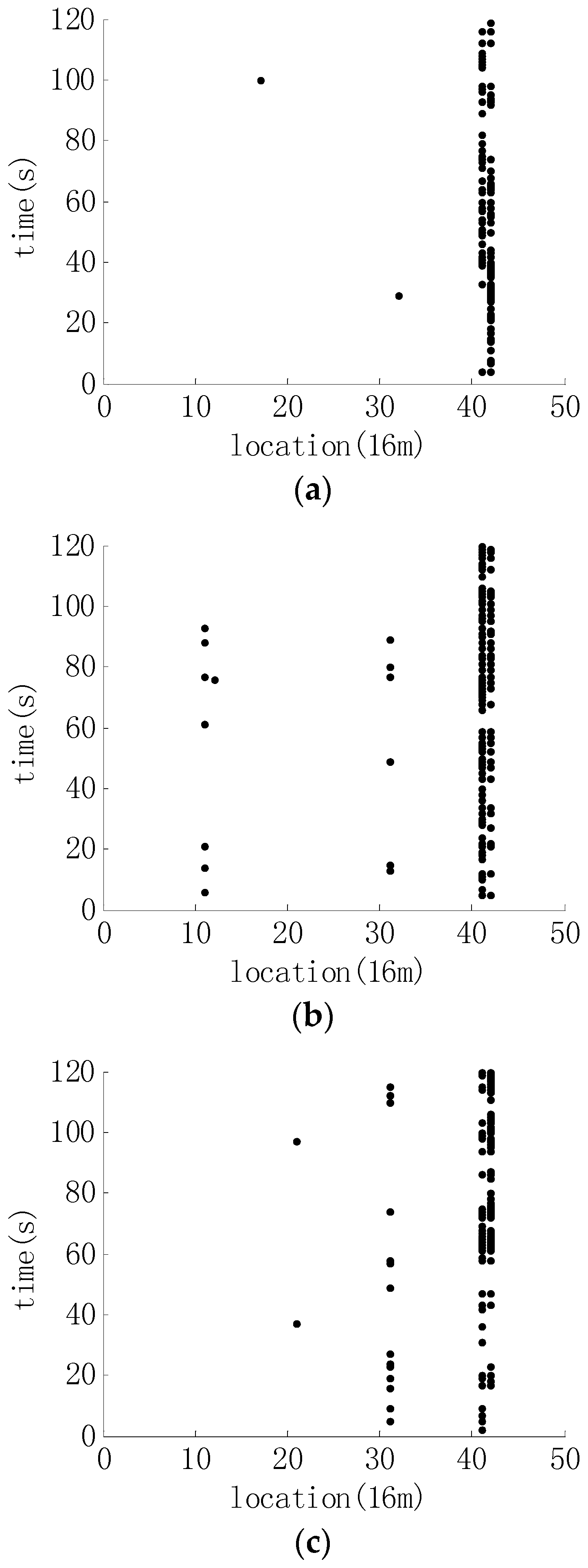
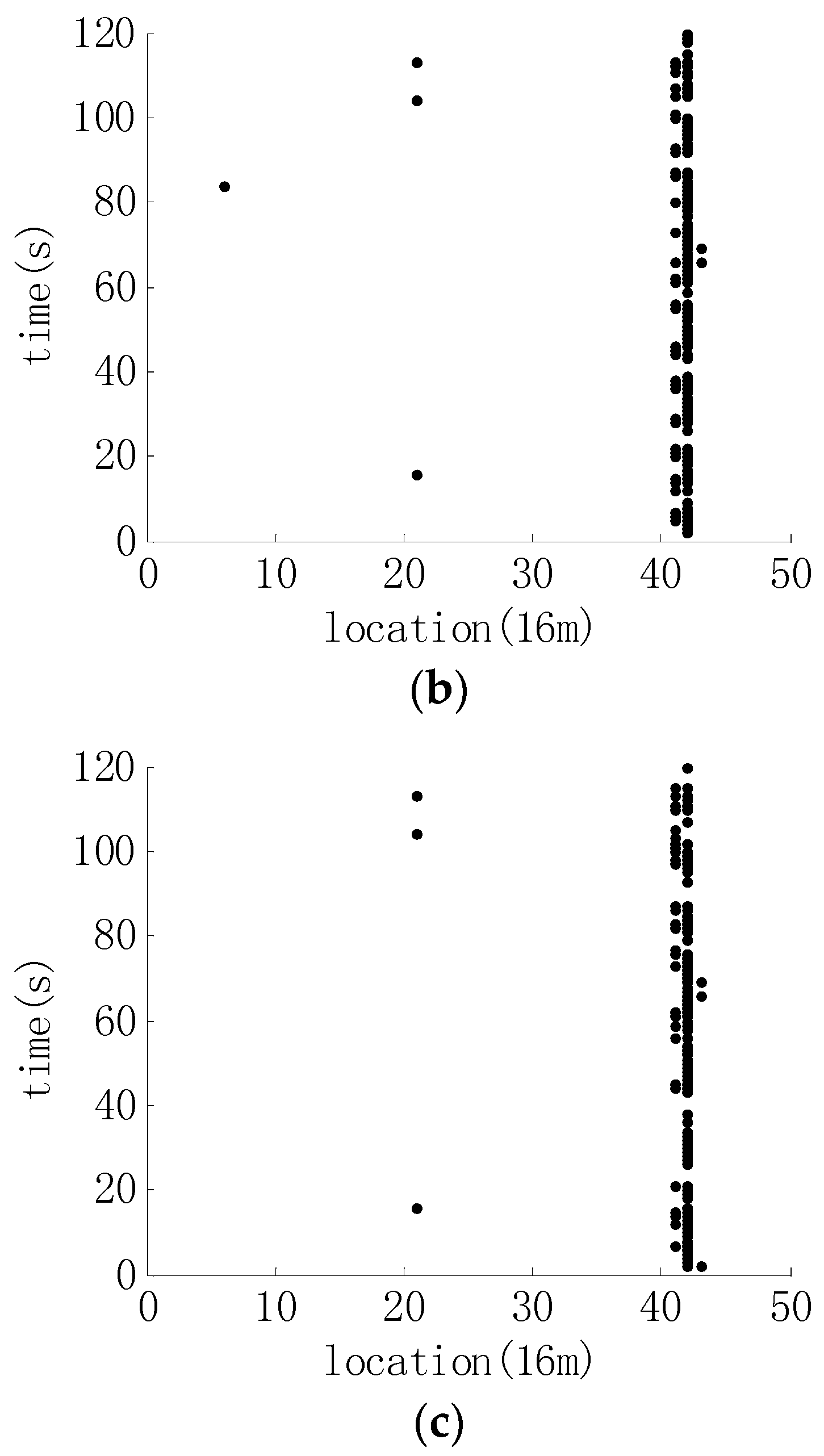
3.2.2. The Detection and Identification Results of Walking Signals
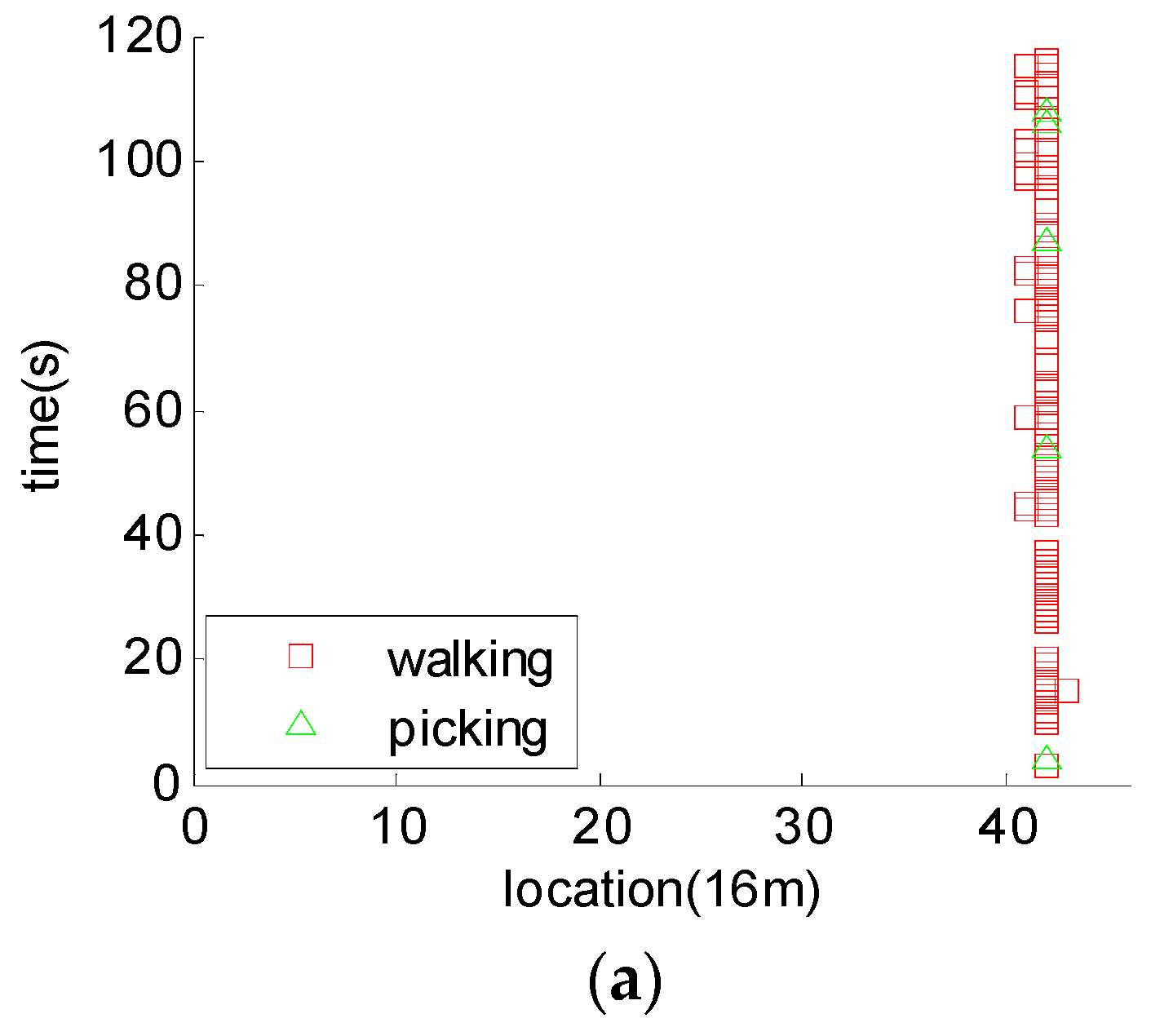
3.2.3. The Identification Results of Picking Signals
3.2.4. The Performance Comparison of Fast Algorithm with Other Methods
4. Conclusions
Author Contributions
Funding
Acknowledgments
Conflicts of Interest
References
- Liu, K.; Chai, T.J.; Liu, T.G.; Jiang, J.F.; Chen, Q.N.; Pan, L. Multi-area optical perimeter security system with quick invasion judgement algorithm. J. Optoelectron. Laser 2015, 26, 288–294. (In Chinese) [Google Scholar]
- Jing, K.; Zhi-Hong, Z. Time prediction model for pipeline leakage based on grey relational analysis. Phys. Procedia 2010, 25, 2019–2024. [Google Scholar] [CrossRef]
- Liang, W.; Lu, L.; Zhang, L. Coupling relations and early-warning for ‘equipment chain’ in long-distance pipeling. Mech. Syst. Signal Process. 2013, 41, 335–347. [Google Scholar] [CrossRef]
- Liang, W.; Zhang, L.; Xu, Q.; Yan, C. Gas pipeline leakage detection based on acoustic technology. Eng. Fail. Anal. 2013, 31, 1–7. [Google Scholar] [CrossRef]
- Zhang, T.; Tan, Y.; Yang, H.; Zhao, J.; Zhang, X. Locating gas pipeline leakage based on stimulus-response method. Energy Procedia 2014, 61, 207–210. [Google Scholar] [CrossRef]
- Zhu, C.H.; Qu, Y.Z.; Wang, J.P. The vibration signal recognition of optical fiber perimeter based on time-frequency features. Opto-Electron. Eng. 2014, 41, 16–22. [Google Scholar]
- Qu, H.; Zheng, T.; Pang, L.; Li, X. A new detection and recognition method for optical fiber pre-warning system. Optik 2017, 137, 209–219. [Google Scholar] [CrossRef]
- Zhang, R.; Sheng, W.; Ma, X. Improved switching CFAR detector for non-homogeneous environments. Signal Process. 2013, 93, 35–48. [Google Scholar] [CrossRef]
- Weinberg, G.V. Management of interference in Pareto CFAR processes using adaptive test cell analysis. Signal Process. 2014, 104, 264–273. [Google Scholar] [CrossRef]
- Shi, B.; Hao, C.; Hou, C.; Ma, X.; Peng, C. Parametric Rao test for multichannel adaptive detection of range-spread target in partially homogeneous environments. Signal Process. 2015, 108, 421–429. [Google Scholar] [CrossRef]
- Tao, P.; Yan, F.; Liu, P.; Peng, W.; Li, Q.; Feng, T. Fiber-optic intrusion recognition system based on Mach-Zehnder interferometer. Chin. J. Quantum Electron. 2011, 28, 183–190. [Google Scholar]
- Wang, S. M-Z interferometer Optical Fiber Sensing System of distributed disturbance pattern recognition method. Infrared Laser Eng. 2014, 43, 613–618. [Google Scholar]
- Qu, H.; Ren, X.; Li, G.; Li, Y.; Zhang, C. Study on the algorithm of vibration source identification based on the optical fiber vibration pre-warning system. Photonic Sens. 2015, 5, 180–188. [Google Scholar] [CrossRef]
- Qu, H.; Liu, S.; Wang, Y.; Li, G. Approach to identifying raindrop vibration signal detected by optical fiber. Sens. Transducers 2013, 160, 85–92. [Google Scholar]
- Qin, Z.; Chen, L.; Bao, X. Continuous wavelet transform for non-stationary vibration detection with phase-OTDR. Opt. Express 2012, 20, 20459–20465. [Google Scholar] [CrossRef] [PubMed]
- Hui, X.; Zheng, S.; Zhou, J.; Chi, H.; Jin, X.; Zhang, X. Hilbert-Huang Transform Time-Frequency Analysis in phi-OTDR Distributed Sensor. IEEE Photonics Technol. Lett. 2014, 26, 2403–2406. [Google Scholar] [CrossRef]
- Zhu, C.; Zhao, Y.; Wang, J.; Li, W.; Zhang, Q. Ensemble Recognition of Fiber Intrusion Behavior Based on Blending Features. Opto-Electron. Eng. 2016, 43, 6–12. [Google Scholar]







| Picking | Mechanical | Walking | |
|---|---|---|---|
| Mechanical drilling1 | 14 | 93 | 8 |
| Mechanical drilling2 | 30 | 107 | 10 |
| Mechanical drilling3 | 0 | 210 | 10 |
| Picking | Mechanical | Walking | |
|---|---|---|---|
| Mechanical drilling1 | 12.1% | 80.9% | 7.0% |
| Mechanical drilling2 | 20.4% | 72.8% | 6.8% |
| Mechanical drilling3 | 0 | 95.5% | 4.5% |
| Mechanical picking1 | 6.3% | 92.1% | 1.6% |
| Mechanical picking2 | 10.4% | 86.5% | 3.1% |
| Mechanical picking3 | 4.5% | 91.6% | 3.9% |
| Mechanical | Walking | Picking | |
|---|---|---|---|
| walking 1 | 5.6% | 94.4% | 0 |
| walking 2 | 1.6% | 98.4% | 0 |
| walking 3 | 2.7% | 97.3% | 0 |
| Picking | Mechanical | Walking | |
|---|---|---|---|
| Picking 1 | 96.2% | 3.8% | 0 |
| Picking 2 | 100% | 0 | 0 |
| Picking 3 | 95.6% | 4.4% | 0 |
| Method | False Alarm Rate | Realization Method |
|---|---|---|
| single-channel detection algorithm | 5.2% | Embedded platform |
| CA-CFAR | 7.8% | Embedded platform |
© 2018 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Sheng, Z.; Qu, D.; Zhang, Y.; Yang, D. The Fast Detection and Identification Algorithm of Optical Fiber Intrusion Signals. Algorithms 2018, 11, 129. https://doi.org/10.3390/a11090129
Sheng Z, Qu D, Zhang Y, Yang D. The Fast Detection and Identification Algorithm of Optical Fiber Intrusion Signals. Algorithms. 2018; 11(9):129. https://doi.org/10.3390/a11090129
Chicago/Turabian StyleSheng, Zhiyong, Dandan Qu, Yuan Zhang, and Dan Yang. 2018. "The Fast Detection and Identification Algorithm of Optical Fiber Intrusion Signals" Algorithms 11, no. 9: 129. https://doi.org/10.3390/a11090129
APA StyleSheng, Z., Qu, D., Zhang, Y., & Yang, D. (2018). The Fast Detection and Identification Algorithm of Optical Fiber Intrusion Signals. Algorithms, 11(9), 129. https://doi.org/10.3390/a11090129




