Abstract
Unmanned Aerial Vehicles (UAVs) have been regarded as a promising means to reshape future wireless communication systems. In this paper, we consider how to plan the trajectory of a solar-powered UAV under a cloudy condition to secure the communication between the UAV and a target ground node against multiple eavesdroppers. We propose a new 3D UAV trajectory optimization model by taking into account the UAV energy consumption, solar power harvesting, eavesdropping and no-fly zone avoidance. A Rapidly-exploring Random Tree (RRT) method is developed to construct the UAV trajectory. Computer simulations and comparisons with a baseline method demonstrate that the proposed method is able to produce trajectories to ensure the valid wireless communication link with the ground node and prevent eavesdropping.
1. Introduction
With rapidly growing demand for energy and decreasing fossil fuel reserves, renewable energy has attracted great of attention worldwide in the last few decades. Solar power is an important source of renewable energy, and various solar-powered products have become part of our daily-life, such as solar-powered cars [1] and solar-powered Unmanned Aerial Vehicles (UAVs) [2]. Powering UAVs by solar energy is a promising solution to overcome the bottleneck of the limited flight time of UAVs powered by onboard battery. Harvesting solar energy while flying allows UAVs to fly longer in the sky, which enables the UAVs to provide uninterrupted service in different applications such as monitoring and surveillance [3,4], disaster management [5], infrastructure inspection [6,7], parcel delivery [8] and wireless communications [9].
The application of UAVs in wireless communications is a hot topic. Compared to conventional wireless communication systems based on stationary infrastructures, UAV-based communication systems can provide timely and economical services in temporary hotspots, disaster areas, and complex terrains [9,10], thanks to their maneuverability. Many research articles relevant to UAV-enabled wireless communication systems have been published, and the UAVs assist existing communication systems by offloading the traffic demand of the stationary access points [9,11,12] and acting as relays to connect remote users to network [13].
UAVs have also been used to protect wireless communications. Wang et al. [14] maximized the non-zero secrecy capacity of a UAV-node link in the presence of an eavesdropper by optimally deploying the UAV. Wang et al. [15] considered a four-entity system with a transmitter, a receiver, an eavesdropper and a UAV relay. They optimized the transmit power of the transmitter and the UAV to maximize the secrecy rate of the system. Li et al. [16] used a UAV as a jammer that interferes with eavesdroppers. They focused on optimizing the trajectory and the jamming power of the UAV and the transmit power of the transmitter to maximize the average achievable secrecy rate. Cai et al. [17] studied a protection scheme using two UAVs: one transmits information, and the other interferes with eavesdroppers. The method jointly optimizes the UAVs’ trajectories and the user transmission schedule. Li et al. [18] investigated a scenario where two UAVs transmit confidential messages to specified ground nodes using the same spectrum in the presence of an eavesdropper. Although the mutual co-channel interferences arising from spectrum sharing may lower the spectral efficiency, the eavesdropping effect can be reduced as the two UAVs act in essence as cooperative jammers for each other. The authors of [19,20] secured the wireless data communication between a ground transmitter and a UAV by jointly optimizing the trajectory of the UAV and the transmit power of the ground transmitter to maximize the average secrecy rate over a given period of time. One common setting in [14,15,16,17,18,19,20] is that the UAV is powered by an onboard capacity-limited battery. Therefore, these designs may not ensure a sustainable defence against eavesdropping.
This paper considers using a solar-powered UAV to secure wireless communications with a ground node in the presence of collaborative eavesdroppers. By securing wireless communication, we mean that the ground node can recover the data sent by the UAV and the eavesdroppers cannot do this at any time. This is a new scenario which has not been considered comprehensively in the literature. Firstly, in light of the method in [21], we consider a solar-powered UAV which is possible to operate for a longer time than the onboard battery-powered UAVs. Secondly, unlike the methods in [16,18,19,20], which optimize the integrated jamming or eavesdropping performance, we target on the instantaneous communication protection. Thirdly, in light of the method in [22], the eavesdroppers can collaborate by combining the collected signals to get a better understanding of the information sent by the UAV. Obviously, this can make it more difficult for the UAV to optimize its trajectory. Moreover, different from most existing publications, which assume that the UAV flies in free space, we consider no-fly zones. The no-fly zones may be tall buildings or areas with high risks of being targeted by ground-to-air missiles [23,24,25]. These different considerations make the problem considered in this paper more general, challenging and practical.
In this paper, we focus on a new trajectory optimization problem for a UAV by taking into account solar power harvesting, instantaneous communication protection, collaborative eavesdropping and no-fly zones. We propose a new optimization model to minimize the energy expenditure of a UAV with a solar-powered rechargeable battery, while securing communications between the UAV and a ground node, avoiding no-fly zones, satisfying the aeronautic maneuverability and preventing depletion of the battery. This is a realistic problem but needs a nonconvex optimization technique, as the solar power is non-smooth and the UAV dynamic model is non-linear. We propose a scheme to plan the UAV trajectory based on Rapidly-exploring Random Tree (RRT). In the proposed method, an RRT can be constructed to capture the non-linear UAV motion model and the secure communication requirements. From the RRT, we can randomly select a set of possible trajectories which end in a pre-defined destination set. (The final position of the UAV is in the destination set.) We verify the energy storage along each possible trajectory and choose the one with the minimum energy expenditure while satisfying all the constraints. Our key contributions include the new problem formulation and the new RRT-based trajectory planning method, which is computational efficient and can quickly explore the flight space to construct UAV trajectory. Computer simulations demonstrate the effectiveness of the proposed approach. By comparing to a baseline method which is unaware of eavesdropping, the proposed method is shown to guarantee the valid wireless communication link with the ground node and prevent eavesdropping. Although a static environment setting is demonstrated in the paper, the proposed RRT-based method can be potentially applied to dynamic environments thanks to its computational efficiency.
RRT falls into the category of sampling-based path planning algorithms. A similar algorithm is the Probabilistic Roadmap (PRM). It first builds up a dense enough roadmap (graph) and finds a path from the start to the destination by a graph search algorithm [26]. By contrast, the RRT method achieves the best feasible path to the goal all by its own processing procedure, which is more suitable for dynamic cases. Another category of path planning methods is the node-based algorithms such as Dijkstra’s algorithm [27]. They grid the solution space and need a specific metric to characterize the cost of moving from one grid to another. These algorithms cannot handle the mobility constraints of UAVs, such as the non-holonomic constraints, as they generally regard the robot as a point in the graph [27]. However, the RRT-based method can account for the mobility constraint in the process of constructing the tree. Furthermore, as shown below, it is not straightforward to define the cost of moving from one grid to another needed for the node-based algorithms. From these discussions, the RRT-based method well suits the considered problem.
The remainder of the paper is organized as follows. In Section 2, we present the system models and state the problem under investigation. In Section 3, we present the proposed 3D trajectory optimization method to minimize the energy consumption subject to the constraints of the UAV maneuverability, communication security, battery lifetime and no-fly zones. Computer simulations are presented in Section 4 to show the performance of the proposed navigation algorithm. Finally, a conclusion is given in Section 5.
2. Problem Statement
In this section, we first present the system model and then formulate the problem of interest.
2.1. UAV Dynamics
We consider a UAV flying in a 3D space. Let be the coordinates of the UAV at time t, where and are the coordinates on the horizontal plane parallel to the ground and is the altitude of the UAV. We consider the following well-known model of the UAV’s motion, (This 3D UAV motion model is extended from a 2D model [28] where a forward speed and an angular speed are the control inputs. Beyond these two control inputs, we consider the vertical speed such that the UAV can adjust its altitude.)
where is the heading of the UAV with respect to the x-axis; , and are its linear horizontal, angular and vertical speeds, respectively; and and are given positive constants indicating the maximum linear, angular and vertical speeds, respectively. The linear horizontal speed , angular speed and vertical speed are considered as the control inputs of the model in Equation (1). The UAV altitude should satisfy the constraints:
where is the lower bound of the UAV altitude and is the upper bound. Furthermore, the horizontal position of the UAV must be outside no-fly zones :
We assume that the set of no-fly zones consists of r no-fly zones where are bounded and connected planar sets. These no-fly zones may be urban areas where flights of UAVs are prohibited, or, in military applications, they may represent areas with high risks of being targeted by ground-to-air missiles [23,24,25].
2.2. Harvesting Solar Energy
The UAV can harvest solar energy, and the harvesting rate depends on the cloud condition if there is any. We consider a cloudy weather, and there is a cloud layer with the altitude ranging from to . The output power of the solar panel () can be modeled by a function of the altitude () [29]:
where is a constant representing the energy transfer efficiency of solar energy harvesting, S is the area of the solar panels, G is the average solar radiation intensity on the earth and is the absorption coefficient of the solar panels. From Equation (4), we see that, when the UAV is above the cloud, the solar energy harvesting power is the largest; when it is below the cloud, is the lowest; and when it is inside the cloud, increases exponentially with the altitude. Equation (4) is a piecewise function of . The non-smoothness makes the problem under consideration complex to solve.
2.3. UAV Energy Consumption
The energy consumption of the UAV depends on the velocity vector [21] and can can be modeled as the summation of the induced power for level flight, the power for vertical flight and the profile power related the blade drag.
The induced power for level flight is modeled as:
where W is the UAV weight, is the air density, A is the total area of the UAV rotor disks, and .
The power for vertical flight is modeled as:
The profile power related to the blade drag is modeled as:
where is the profile drag coefficient depending on the geometry of the rotor blades.
Thus, at any time t, the power consumption of the for movement is:
Moreover, let be the static power consumed for maintaining the operation of the UAV and be the constant transmit power. Let denote the energy stored in the on-board battery. Then, the dynamics of the stored energy of the battery is characterized by:
Let denote the battery capacity. Then, the following constraint should be satisfied:
2.4. Securing Communication
We consider that the UAV communicates with a stationary ground node . Let be the position of the node. Moreover, there are M stationary eavesdroppers on the ground, which attempt to eavesdrop on the communication between the UAV and the node . Let be the position of an eavesdropper i, .
Let denote the Euclidean distance between the UAV and the node at time t, and be the Euclidean distance between the UAV and the eavesdropper i at time t:
We introduce a function which measures the communication/eavesdropping performance from the distance d. Clearly, is a decreasing function of d. For example, in the well-known Friis formula [30], when the transmitter and receiver are d apart with dominating line-of-sight, the received signal-to-noise ratio (SNR) is , where is a given parameter depending on the transmit power, the gains of the transmitter and receiver and the noise power.
To guarantee secure communication between the UAV and the ground node, a set of constraints are considered below. The first requirement is that the received power at the ground node needs to be no lower than a threshold :
This is to ensure that the node can successfully recover the received data. Secondly, the received power at each eavesdropper needs to be no larger than a threshold :
for all . This is to ensure that any eavesdropper i cannot recover the captured data. Lastly, the following constraint is satisfied to avoid eavesdropping when the eavesdroppers collaborate:
where . The constraint in Equation (13) ensures that, when the eavesdroppers collaborate, they cannot recover the combined data. When they carry out maximal ratio combining (MRC) [30], Equation (13) can take the equality. General speaking, the constraints in Equations (12) and (13) require the UAV to be far enough from the eavesdroppers, whereas Equation (11) expects the UAV to be close to the node . We note that constraints in Equations (11)–(13) specify stringent instantaneous security rate requirement. We also note that in cases where several eavesdroppers are located closely, they may block the path for the UAV, and there may not exist a feasible trajectory satisfying Equations (11)–(13). To avoid being eavesdropped, we assume that the UAV stops transmitting in these cases.
2.5. Problem Statement
Let be the time the UAV can use to fly to a destination set . We assume that the destination set is a bounded and connected planar set which does not overlap with the set of no-fly zones . During the period , the UAV keeps transmitting confidential data to the stationary ground node. The problem of interest is formulated as follows:
subject to
subject to Equations (2), (3), (11), (12) and (13).
4. Simulation Results
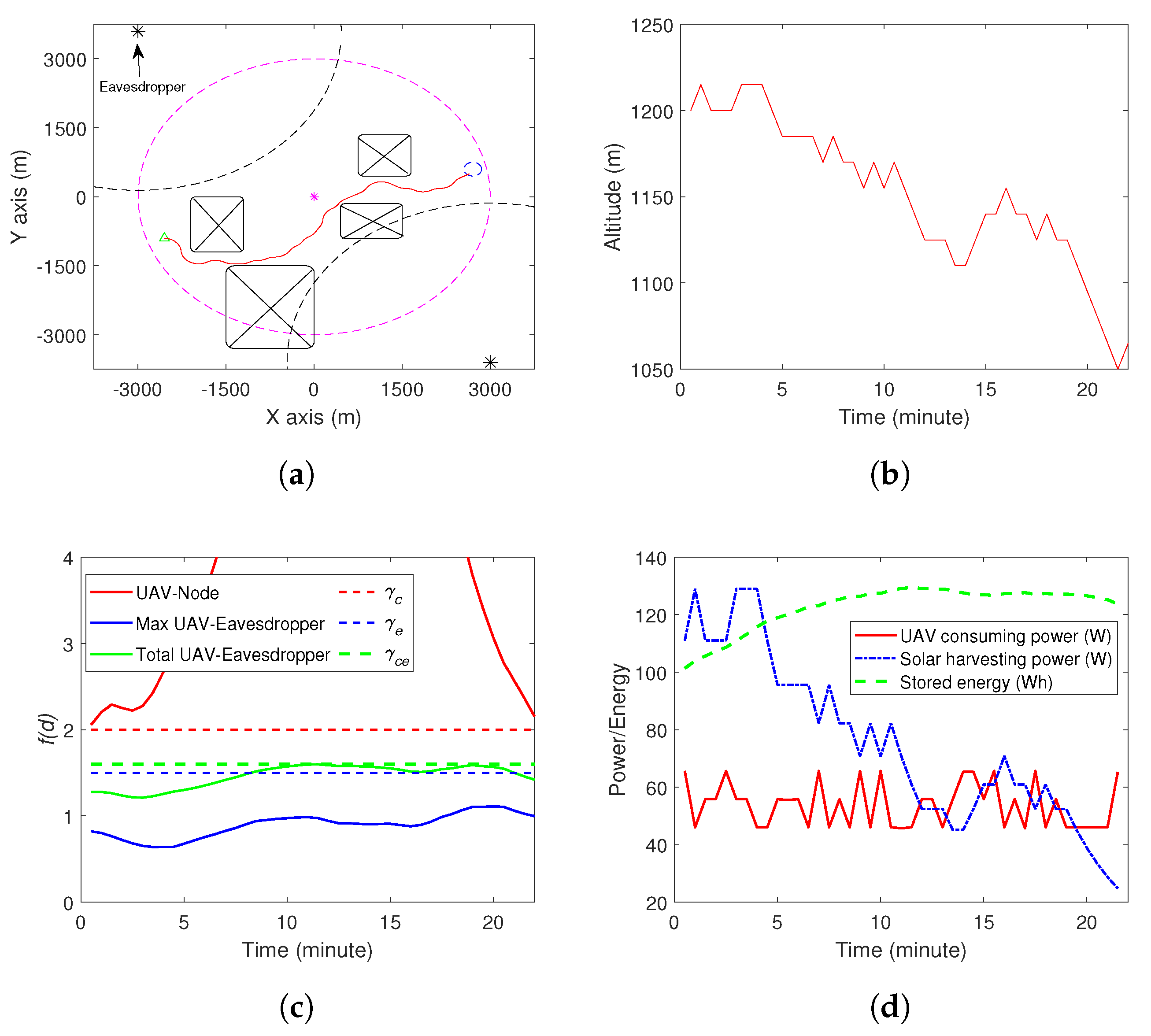
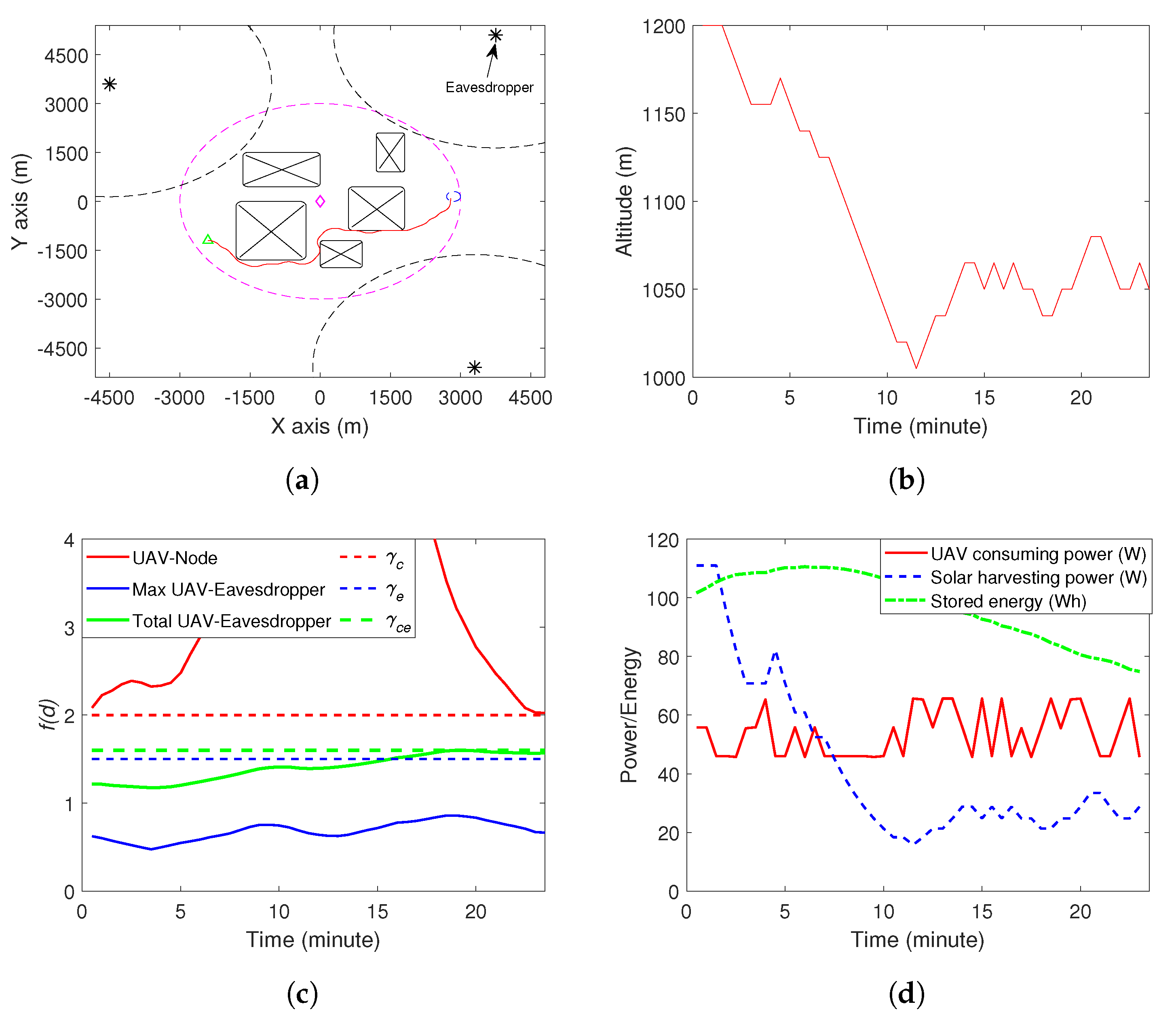
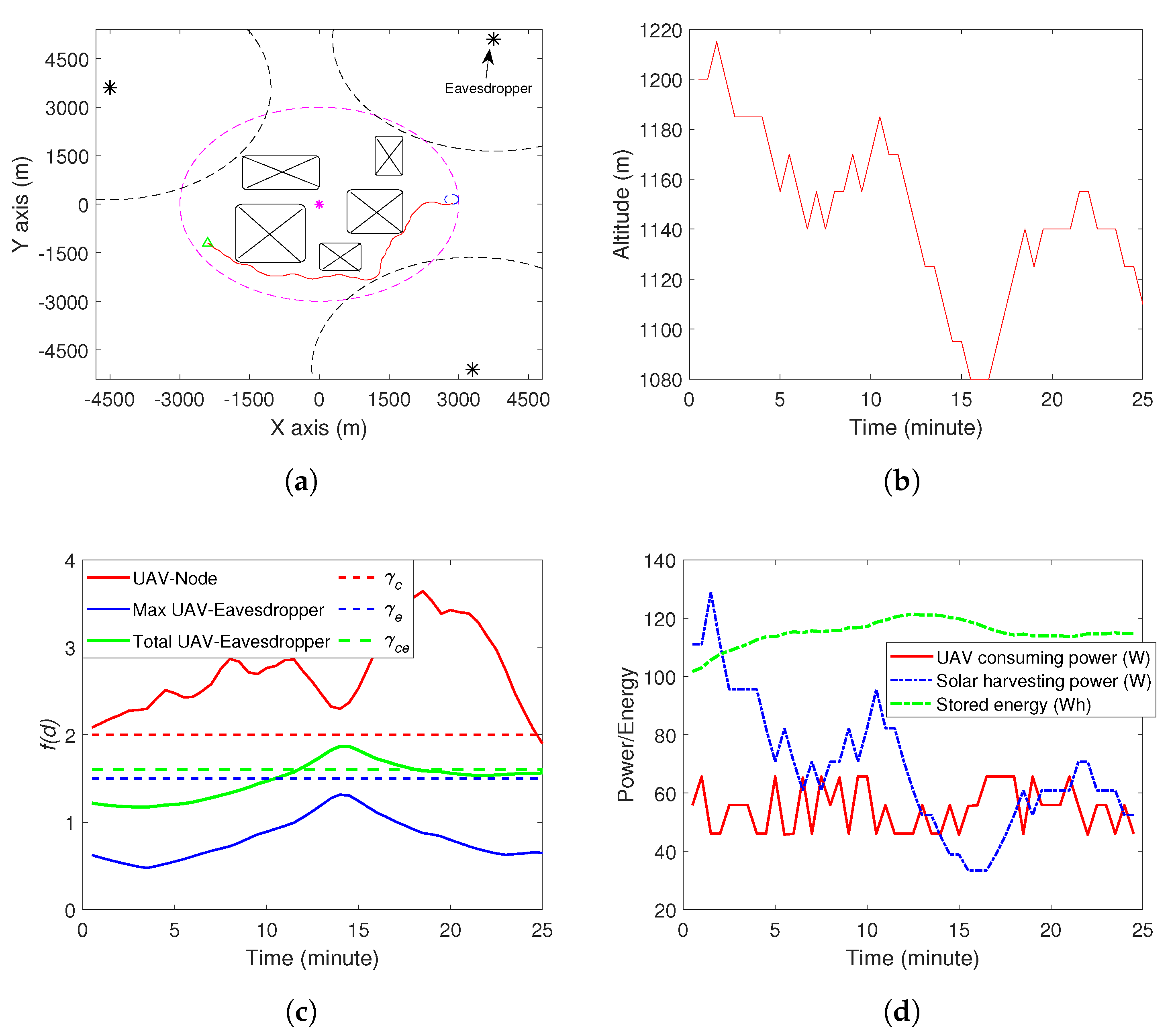
In this section, we demonstrate the effectiveness of the proposed method via computer simulations. The parameters used are summarized in Table 2. We considered two simulation environments, as shown in Figure 1 and Figure 2. In Figure 1, there are two eavesdroppers and four no-fly zones, while, in Figure 2, there are three eavesdroppers and five zo-fly zones. The ground node locates at (0,0). The UAV starts from the initial position, which is shown by the green triangle in Figure 1a and Figure 2a. The destination set is shown by a blue circle on the right side of Figure 1a and Figure 2a. In Figure 1a and Figure 2a, we also demonstrate some dash lines on the plane of , i.e., the ground. The purple one indicates the area within which the ground node can effectively recover the sent data by the UAV. The black dash lines represent the area within which the eavesdroppers (marked by the black squares) can recover the captured data. Starting from the initial position, the UAV moves along the red trajectory and reaches the destination set in 22 min in environment 1 and 23.5 min in environment 2, which are before the due time. The altitude of the UAV during the movement is shown in Figure 1b and Figure 2b. The communication between the UAV and the ground node is good, as shown in Figure 1c and Figure 2c, and this trajectory avoids the individual and collaborative eavesdropping (see Figure 1c and Figure 2c). Finally, the energy consumption of the UAV, the solar energy harvesting and the stored amount of energy are shown in Figure 1d and Figure 2d. Note that the simulations were conducted on a normal PC with Inter(R) Core(TM) i7-8565U CPU @ 1.8GHz, 1.99GHz and 8G RAM. The average time to find the trajectory was about 3–5 s. Specifically, for the simulation in Environment 1, the algorithm generated about 800–1000 samples. The number of samples generated changed in each simulation as the RRT-based algorithm is a random method. For Environment 2, the algorithm generated more samples, i.e, 10,000–13,000. The reason is that Environment 2 (three eavesdroppers and five no-fly zones) is more complex than Environment 1 (two eavesdroppers and four no-fly zones). Thus, there were more infeasible samples generated in Environment 2.

Table 2.
Parameters and values.
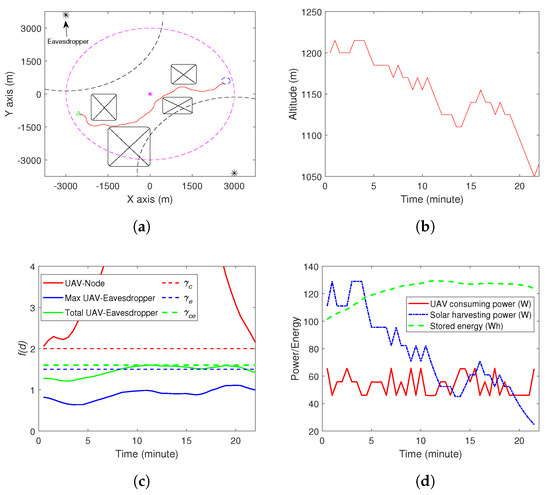
Figure 1.
Simulation results in Environment 1 by the proposed method. (a) The UAV movement on x-y plane. A video is available: https://youtu.be/7EpmQZuOwao. (b) The UAV altitude. (c) The communication and eavesdropping performance. (d) Energy consumption and solar energy harvesting.
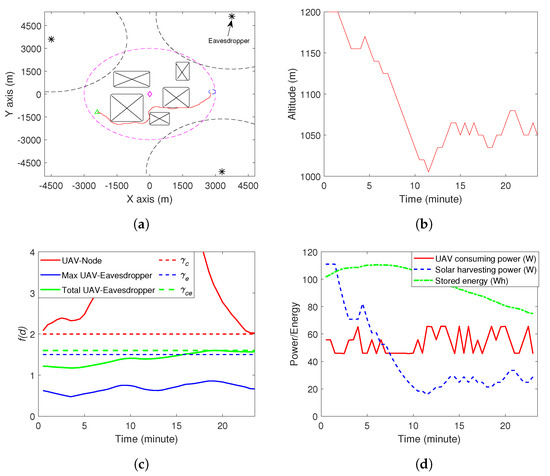
Figure 2.
Simulation results in Environment 2 by the proposed method. (a) The UAV movement on x-y plane. A video is available: https://youtu.be/BiNL8gA0n-w. (b) The UAV altitude. (c) The communication and eavesdropping performance. (d) Energy consumption and solar energy harvesting.
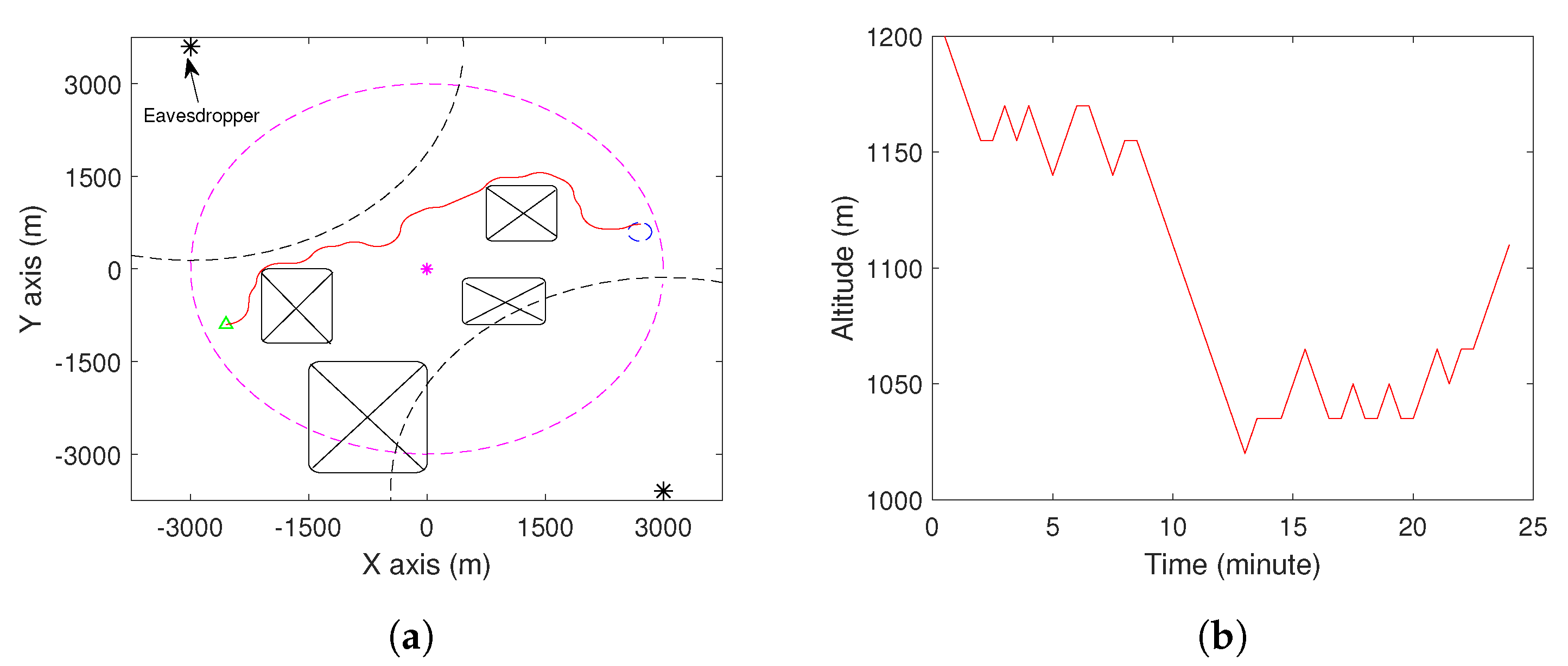
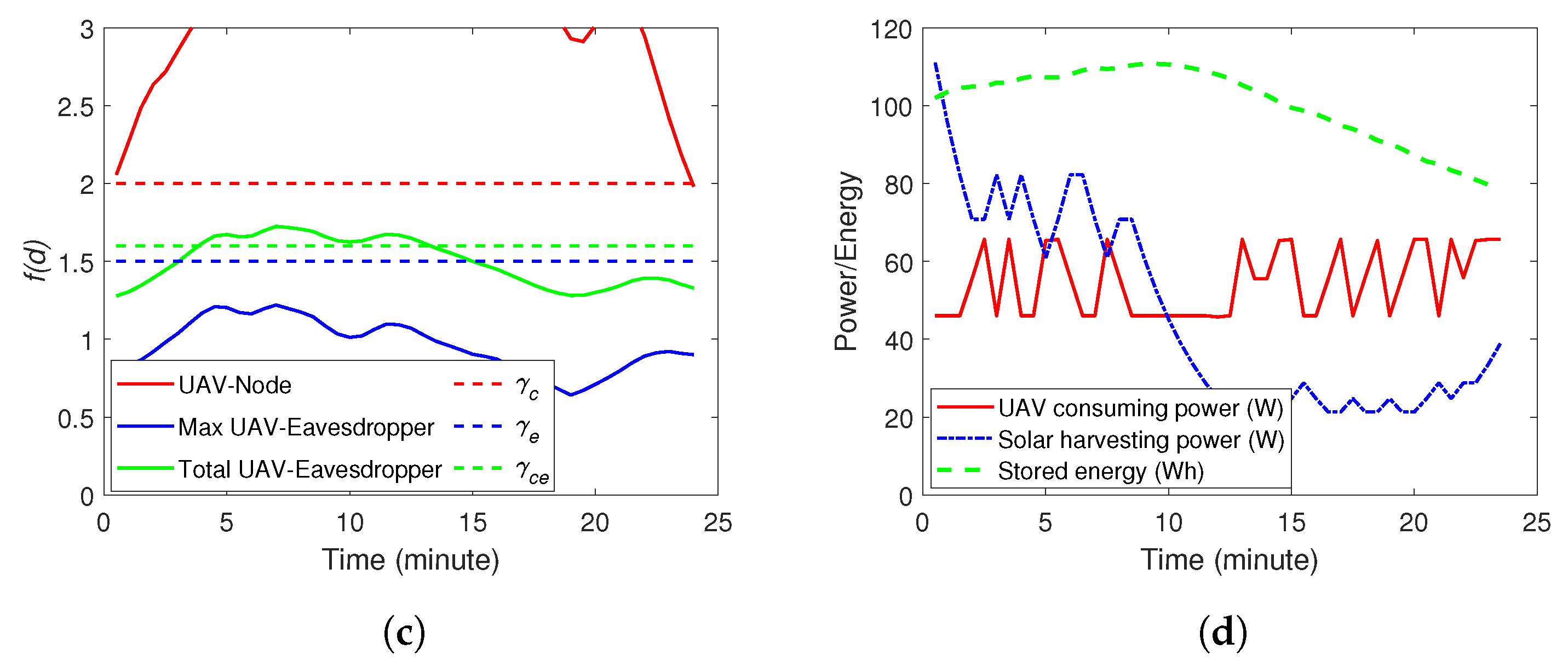
For comparison, we applied a baseline method to the considered case. This baseline method only considers effectively transmitting data to the ground node while ignoring the eavesdroppers. All the parameters were the same as above. The simulation results are shown in Figure 3 and Figure 4. The trajectories of the UAV are shown in Figure 3a and Figure 4b. Comparing Figure 3a and Figure 1a (Figure 4a and Figure 2a), we see that this trajectory is closer to the eavesdropping boundary of one of the eavesdroppers. Although this does not lead to the successful individual eavesdropping by the top eavesdroppers, the two eavesdroppers can recover the captured data by analyzing the combined data. This is shown in Figure 3c. Between 5 and 13 min, the eavesdropping performance is above the threshold . A similar finding can be observed in Figure 4c. From this comparison, we can see that the proposed method can construct a safe trajectory, which ensures the communication with the ground node, avoids eavesdropping and avoids collision with no-fly zones.
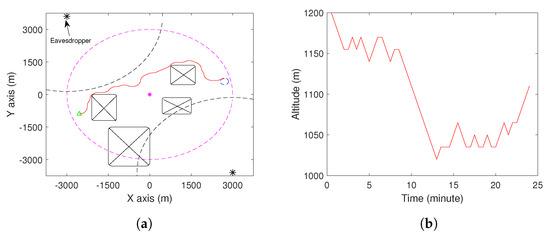
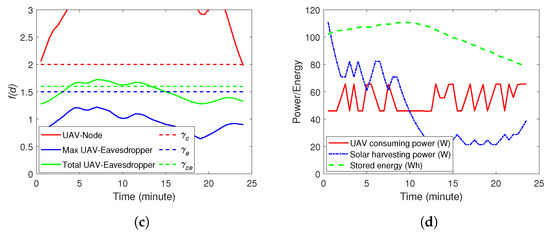
Figure 3.
Simulation results in Environment 1 by the benchmark method. (a) The UAV movement on x-y plane. A video is available: https://youtu.be/kGFlpWV-SkQ. (b) The UAV altitude. (c) The communication and eavesdropping performance. (d) Energy consumption and solar energy harvesting.
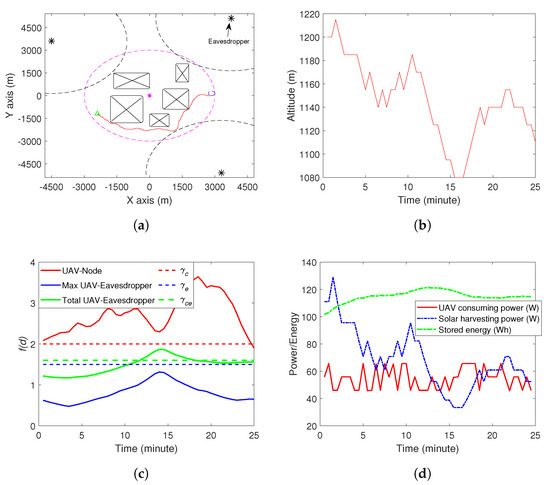
Figure 4.
Simulation results in Environment 2 by the benchmark method. (a) The UAV movement on x-y plane. A video is available: https://youtu.be/FzNNrJzABzQ. (b) The UAV altitude. (c) The communication and eavesdropping performance. (d) Energy consumption and solar energy harvesting.
5. Conclusions
In this paper, we consider a problem of securing wireless communication between a solar-powered UAV and a stationary ground node in the presence of stationary eavesdroppers that can carry out the eavesdropping task independently and collaboratively. We developed a 3D UAV trajectory optimization model which minimizes the UAV flight energy expenditure, subject to that the communication between the UAV and the ground node is reliable and secure, and the UAV does deplete battery during the flight. An RRT trajectory planning scheme was developed. Computer simulations showed that the proposed method guarantees the valid wireless communication link with the ground node, prevents eavesdropping and avoids no-fly zones.
Author Contributions
Conceptualization, A.V.S.; Formal analysis, H.H.; Funding acquisition, A.V.S.; Investigation, H.H. and W.N.; Methodology, H.H. and A.V.S.; Validation, W.N.; Writing–review and editing, W.N. All authors have read and agreed to the published version of the manuscript.
Funding
This work was supported by the Australian Research Council. In addition, this work received funding from the Australian Government, via grant AUSMURIB000001 associated with ONR MURI grant N00014-19-1-2571.
Conflicts of Interest
The authors declare no conflict of interest.
References
- Ota, Y.; Masuda, T.; Araki, K.; Yamaguchi, M. A mobile multipyranometer array for the assessment of solar irradiance incident on a photovoltaic-powered vehicle. Sol. Energy 2019, 184, 84–90. [Google Scholar] [CrossRef]
- Zhang, J.; Lou, M.; Xiang, L.; Hu, L. Power cognition: Enabling intelligent energy harvesting and resource allocation for solar-powered UAVs. Future Gener. Comput. Syst. 2019. [Google Scholar] [CrossRef]
- Jung, S.; Jo, Y.; Kim, Y.J. Aerial Surveillance with Low-Altitude Long-Endurance Tethered Multirotor UAVs Using Photovoltaic Power Management System. Energies 2019, 12, 1323. [Google Scholar] [CrossRef]
- Savkin, A.V.; Huang, H. A Method for Optimized Deployment of a Network of Surveillance Aerial Drones. IEEE Syst. J. 2019, 13, 4474–4477. [Google Scholar] [CrossRef]
- Ejaz, W.; Azam, M.A.; Saadat, S.; Iqbal, F.; Hanan, A. Unmanned aerial vehicles enabled IoT platform for disaster management. Energies 2019, 12, 2706. [Google Scholar] [CrossRef]
- Lee, D.H.; Park, J.H. Developing Inspection Methodology of Solar Energy Plants by Thermal Infrared Sensor on Board Unmanned Aerial Vehicles. Energies 2019, 12, 2928. [Google Scholar] [CrossRef]
- Wang, J.; Wang, G.; Hu, X.; Luo, H.; Xu, H. Cooperative Transmission Tower Inspection with a Vehicle and a UAV in Urban Areas. Energies 2020, 13, 326. [Google Scholar] [CrossRef]
- Mohiuddin, A.; Taha, T.; Zweiri, Y.; Gan, D. UAV payload transportation via RTDP based optimized velocity profiles. Energies 2019, 12, 3049. [Google Scholar] [CrossRef]
- Huang, H.; Savkin, A.V. A Method for Optimized Deployment of Unmanned Aerial Vehicles for Maximum Coverage and Minimum Interference in Cellular Networks. IEEE Trans. Ind. Inform. 2019, 15, 2638–2647. [Google Scholar] [CrossRef]
- Savkin, A.V.; Huang, H. Range-Based Reactive Deployment of Autonomous Drones for Optimal Coverage in Disaster Areas. IEEE Trans. Syst. Man Cybern. Syst. 2019, 1–5. [Google Scholar] [CrossRef]
- Huang, H.; Savkin, A.V. An Algorithm of Efficient Proactive Placement of Autonomous Drones for Maximum Coverage in Cellular Networks. IEEE Wirel. Commun. Lett. 2018, 7, 994–997. [Google Scholar] [CrossRef]
- Lyu, J.; Zeng, Y.; Zhang, R.; Lim, T.J. Placement Optimization of UAV-Mounted Mobile Base Stations. IEEE Commun. Lett. 2017, 21, 604–607. [Google Scholar] [CrossRef]
- Chen, Y.; Feng, W.; Zheng, G. Optimum Placement of UAV as Relays. IEEE Commun. Lett. 2018, 22, 248–251. [Google Scholar] [CrossRef]
- Wang, D.; Bai, B.; Zhang, G.; Han, Z. Optimal Placement of Low-Altitude Aerial Base Station for Securing Communications. IEEE Wirel. Commun. Lett. 2019, 8, 869–872. [Google Scholar] [CrossRef]
- Wang, Q.; Chen, Z.; Mei, W.; Fang, J. Improving Physical Layer Security Using UAV-Enabled Mobile Relaying. IEEE Wirel. Commun. Lett. 2017, 6, 310–313. [Google Scholar] [CrossRef]
- Li, A.; Wu, Q.; Zhang, R. UAV-enabled cooperative jamming for improving secrecy of ground wiretap channel. IEEE Wirel. Commun. Lett. 2019, 8, 181–184. [Google Scholar] [CrossRef]
- Cai, Y.; Cui, F.; Shi, Q.; Zhao, M.; Li, G.Y. Dual-UAV-Enabled Secure Communications: Joint Trajectory Design and User Scheduling. IEEE J. Sel. Areas Commun. 2018, 36, 1972–1985. [Google Scholar] [CrossRef]
- Li, Y.; Zhang, R.; Zhang, J.; Yang, L. Cooperative Jamming via Spectrum Sharing for Secure UAV Communications. IEEE Wireless Commun. Lett. 2019. [Google Scholar] [CrossRef]
- Cui, M.; Zhang, G.; Wu, Q.; Ng, D.W.K. Robust Trajectory and Transmit Power Design for Secure UAV Communications. IEEE Trans. Veh. Technol. 2018, 67, 9042–9046. [Google Scholar] [CrossRef]
- Zhang, G.; Wu, Q.; Cui, M.; Zhang, R. Securing UAV Communications via Joint Trajectory and Power Control. IEEE Trans. Wirel. Commun. 2019, 18, 1376–1389. [Google Scholar] [CrossRef]
- Sun, Y.; Xu, D.; Ng, D.W.K.; Dai, L.; Schober, R. Optimal 3D-Trajectory Design and Resource Allocation for Solar-Powered UAV Communication Systems. IEEE Trans. Commun. 2019, 67, 4281–4298. [Google Scholar] [CrossRef]
- Yuan, X.; Feng, Z.; Ni, W.; Liu, R.P.; Zhang, J.A.; Xu, W. Secrecy Performance of Terrestrial Radio Links under Collaborative Aerial Eavesdropping. IEEE Trans. Inf. Forensics Secur. 2020, 15, 604–619. [Google Scholar] [CrossRef]
- Savkin, A.V.; Huang, H. Optimal Aircraft Planar Navigation in Static Threat Environments. IEEE Trans. Aerosp. Electron. Syst. 2017, 53, 2413–2426. [Google Scholar] [CrossRef]
- Inanc, T.; Muezzinoglu, M.K.; Misovec, K.; Murray, R.M. Framework for low-observable trajectory generation in presence of multiple radars. J. Guid. Control. Dyn. 2008, 31, 1740–1749. [Google Scholar] [CrossRef]
- Zabarankin, M.; Uryasev, S.; Murphey, R. Aircraft routing under the risk of detection. Nav. Res. Logist. (NRL) 2006, 53, 728–747. [Google Scholar] [CrossRef]
- Kavraki, L.E.; Svestka, P.; Latombe, J.C.; Overmars, M.H. Probabilistic roadmaps for path planning in high-dimensional configuration spaces. IEEE Trans. Robot. Autom. 1996, 12, 566–580. [Google Scholar] [CrossRef]
- Dijkstra, E.W. A note on two problems in connexion with graphs. Numer. Math. 1959, 1, 269–271. [Google Scholar] [CrossRef]
- Kang, Y.; Hedrick, J.K. Linear tracking for a fixed-wing UAV using nonlinear model predictive control. IEEE Trans. Control Syst. Technol. 2009, 17, 1202–1210. [Google Scholar] [CrossRef]
- Duffie, J.A.; Beckman, W.A. Solar Engineering of Thermal Processes; John Wiley & Sons: Hoboken, NJ, USA, 2013. [Google Scholar]
- Friis, H.T. A note on a simple transmission formula. Proc. IRE 1946, 34, 254–256. [Google Scholar] [CrossRef]
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).