A Novel Feature-Selection Algorithm in IoT Networks for Intrusion Detection
Abstract
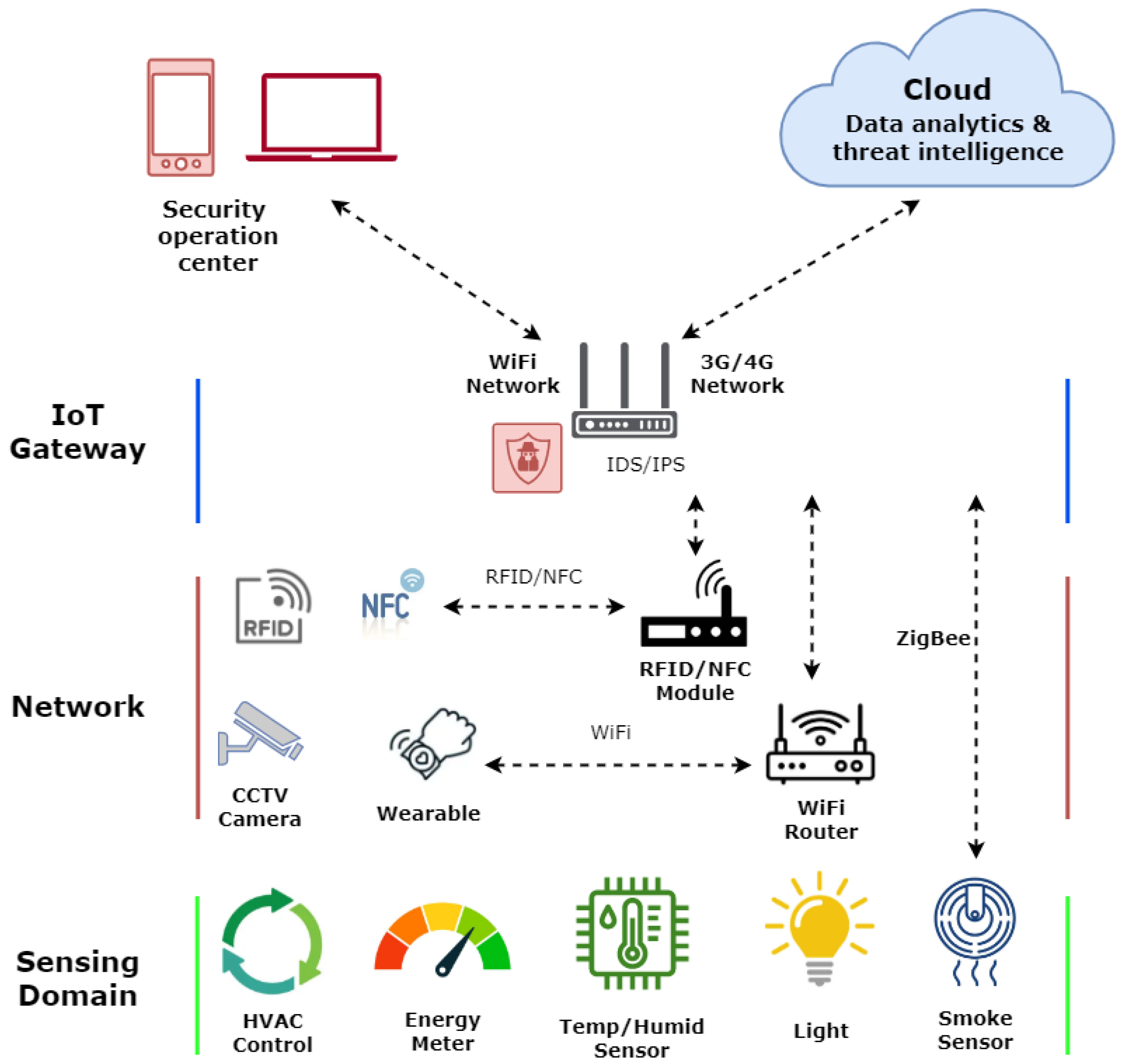
:1. Introduction
- IoT systems are relatively easy to attack compared to normal networks because IoT vendors focus more on device cost, usability, dimensions, etc., as compared to the security [6].
- A large number of IoT devices are exposed to medium- to high-risk vulnerabilities [9].
- Common Vulnerabilities and Exposure (CVE) [9] data for IoT devices showed that several devices, such as endoscopic cameras and blood pressure monitoring devices, use vulnerable operating systems or software packages, leaving the whole infrastructure vulnerable.
- IoT networks generally use lightweight communication protocols and weak security standards/techniques; therefore, they are easily exploitable [10].
2. Literature Review
2.1. Intrusion Datasets for IoT Networks
2.2. Dimension-Reduction Techniques for Network Intrusion-Detection Systems (NIDSs)
2.2.1. Filter Approach
2.2.2. Wrapper Approach
2.2.3. Embedded Approach
2.3. Machine Learning-Based IDS Techniques for IoT Networks
3. Hybrid Metahueristics-Based Feature Selection Method
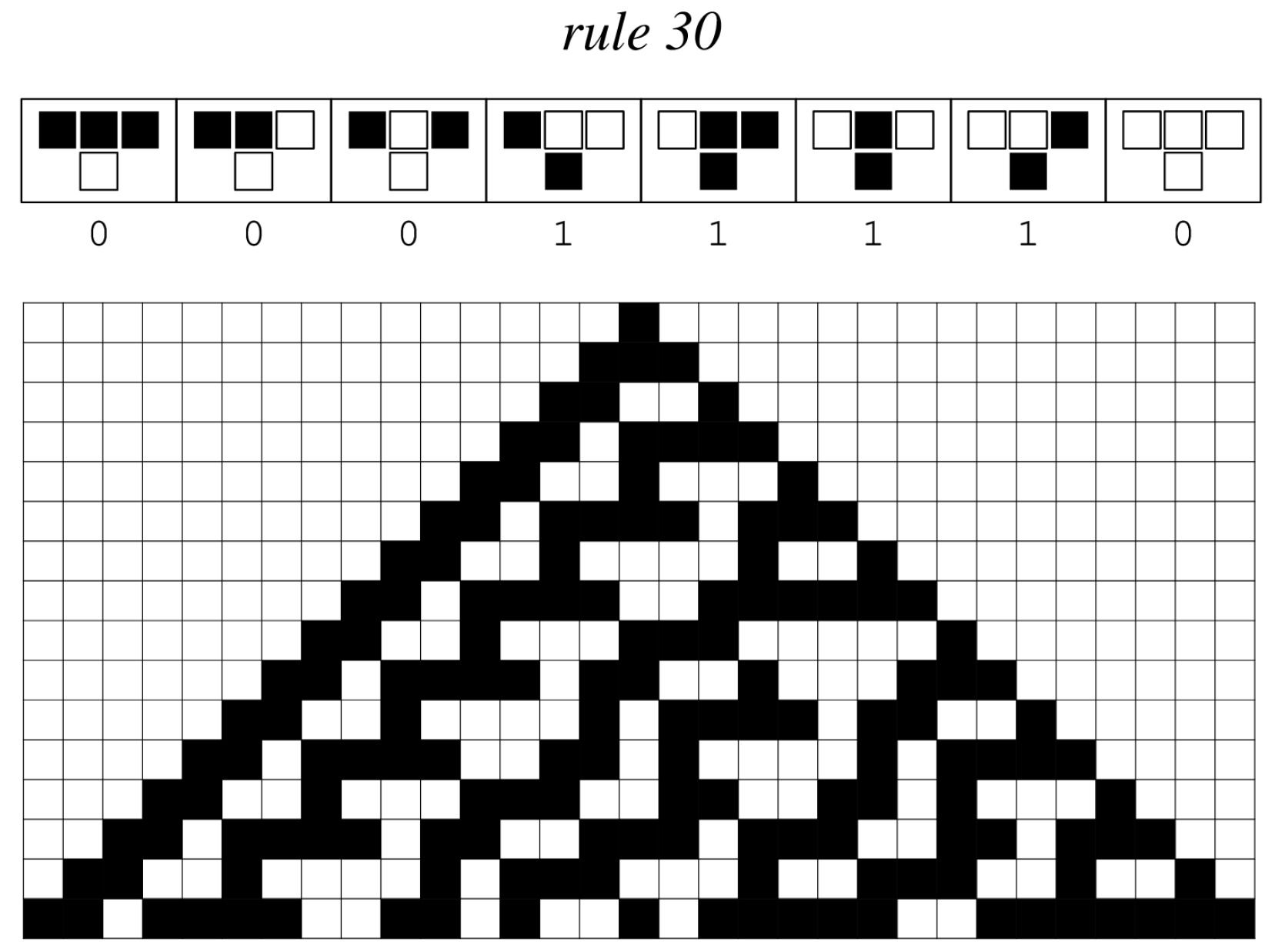
3.1. Cellular Automata (CA)—Basics
3.2. Tabu Search (TS)
3.3. Random Forest (RF)
3.4. Fitness Function
3.5. Cellular Automata (CA)-Based Tabu Search (TS) Feature-Selection Algorithm (CAT-S)
3.5.1. Data Preprocessing
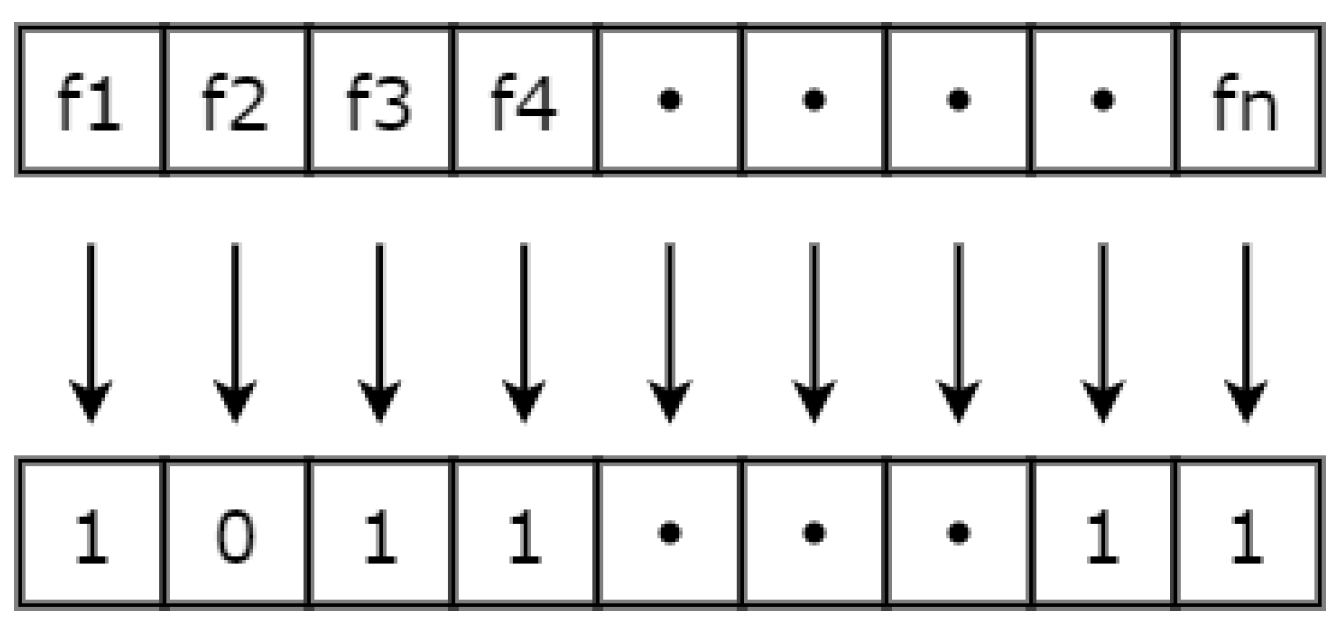
3.5.2. Generating an Initial Solution and Calculating the Fitness
- The Random Forest classifier is used to find the accuracy, detection error , and false positive rate .
- Error , number of features in the feature vector, and are input into Equation (3) to calculate the fitness.
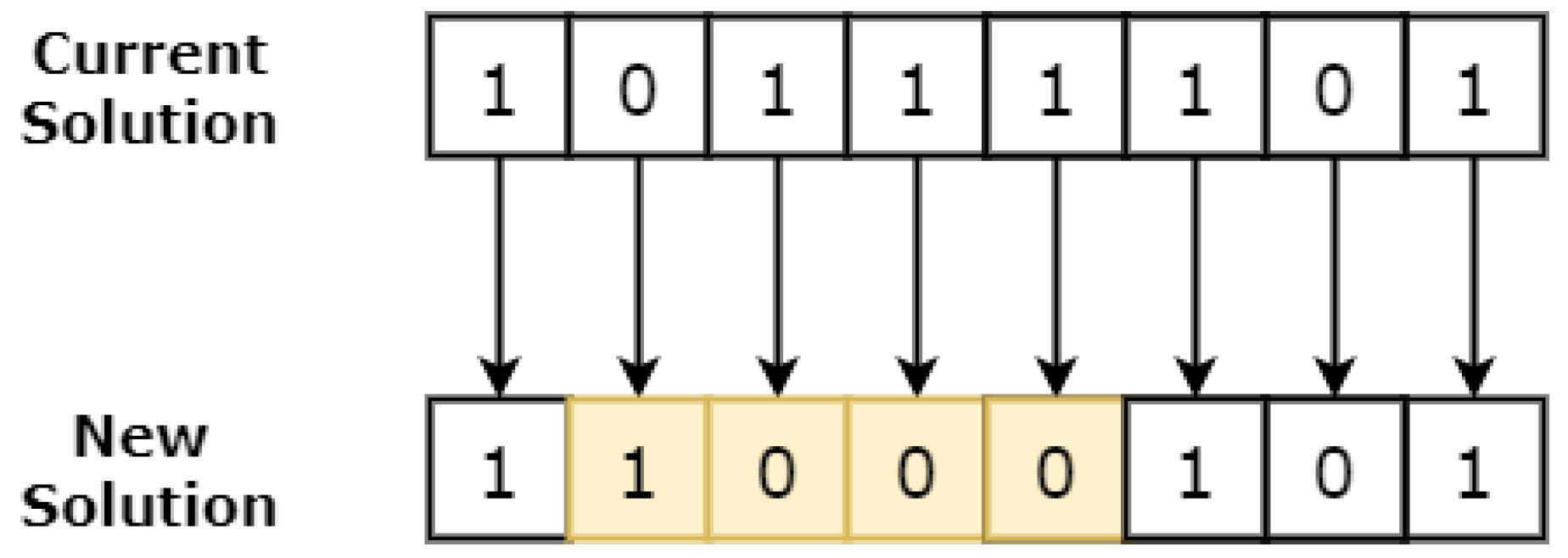
3.5.3. CA Engine—Generate Neighbour Solutions
3.5.4. Calculating the Fitness of Each Neighbour Solution
3.5.5. Tabu List Lookup
3.5.6. Aspiration Level Checking
3.5.7. Accepting the Best Neighbour
3.5.8. Stopping Criteria
4. Dataset Details (TON_IoT)
- Scanning attack: This attack is alternatively known as a reconnaissance or probing attack, and it represents the initial phase in the cyber kill chain model or penetration testing. The primary objective of this attack is to gather information about the target systems, which involves identifying active IP addresses and open ports within the testbed network.
- Denial of Service (DoS) attack: DoS refers to the act of flooding a network or IoT/IIoT services with fake requests in an attempt to disrupt or corrupt their resources.
- Distributed Denial of Service (DDoS) attack: A DDoS is a sophisticated cyber attack that overwhelms a target with an enormous volume of fake requests from multiple sources simultaneously. The goal of DDoS attacks is to render a website or online service inaccessible to legitimate users, causing disruption and downtime. Perpetrators use networks of compromised devices (botnets) to orchestrate DDoS attacks, making them difficult to mitigate.
- Ransomware attack: A ransomware attack is a type of malicious cyber attack where hackers encrypt the victim’s data and demand a ransom in exchange for the decryption key. Once infected, users are denied access to their files until the ransom is paid, posing significant risks to data privacy and business operations. Ransomware attacks are typically delivered through phishing emails, malicious downloads, or exploiting software vulnerabilities.
- Backdoor attack: A backdoor attack is a stealthy and unauthorised method used by hackers to gain access to a computer system or network. It involves exploiting vulnerabilities to create hidden entry points, allowing attackers to bypass normal authentication measures. Backdoor attacks can result in unauthorised access, data breaches, and compromised system security.
- Injection attack: An injection attack is a form of cyber attack where malicious code or commands are inserted into an application or system. These attacks exploit vulnerabilities, such as SQL injection, to manipulate the behaviour of the target and potentially gain unauthorised access or compromise data. Injection attacks pose significant risks to web applications, databases, and other software systems susceptible to user input manipulation.
- Cross-site Scripting (XSS) attack: Cross-site scripting (XSS) is a type of cyber attack that allows attackers to inject malicious scripts into web pages viewed by other users. These scripts can then be executed in the context of the victim’s browser, stealing sensitive information or performing unauthorised actions on behalf of the user. XSS attacks pose a serious threat to web applications and can lead to the theft of user credentials, session hijacking, and other security breaches.
- Password cracking attack: A password cracking attack is a cybersecurity technique aimed at gaining unauthorised access to user accounts by systematically guessing or decrypting passwords. Attackers use various methods such as brute force, dictionary attacks, or rainbow tables to crack weak or poorly protected passwords. Once successful, password cracking allows attackers to impersonate users, potentially leading to data breaches and compromising sensitive information.
- Man-In-The-Middle (MITM) attack: A Man-in-the-Middle (MITM) attack is a cyber attack where an unauthorised actor intercepts and relays communications between two parties without their knowledge. During the attack, the attacker can eavesdrop, modify, or inject malicious content into the communication, potentially stealing sensitive information or gaining unauthorised access. MITM attacks pose significant risks to data privacy, online transactions, and the integrity of communication channels.
5. CAT-S Working Example
5.1. Binary Encoding and Initial Solution
5.2. Calculate Cost of Initial Solution
5.3. Generate Neighbour Solutions
5.4. Calculating the Fitness of Each Neighbour Solution
5.5. Tabu List Lookup
5.6. Aspiration Level Checking
6. Testing Configuration
7. Experiments and Results
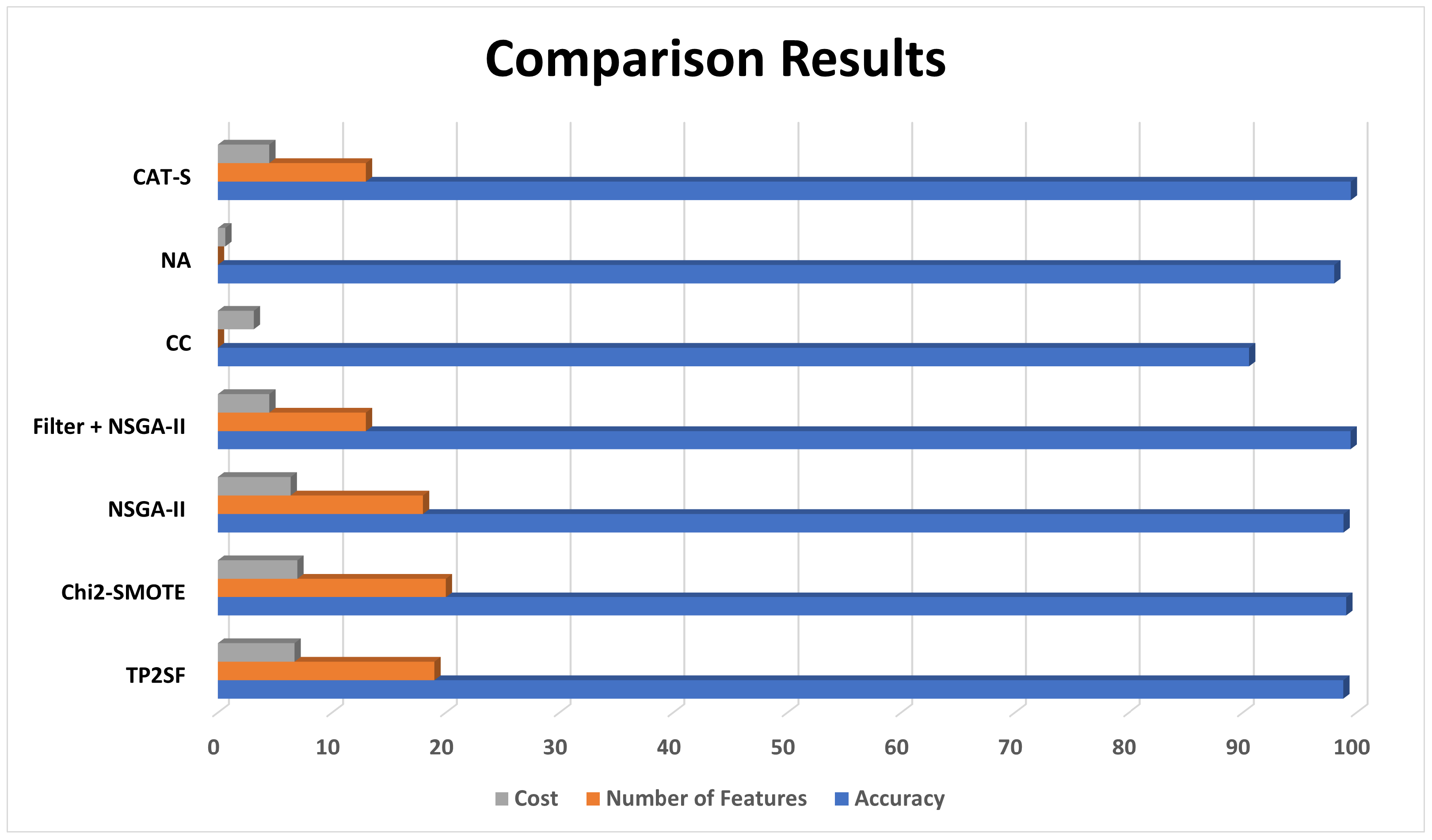
Critical Discussion
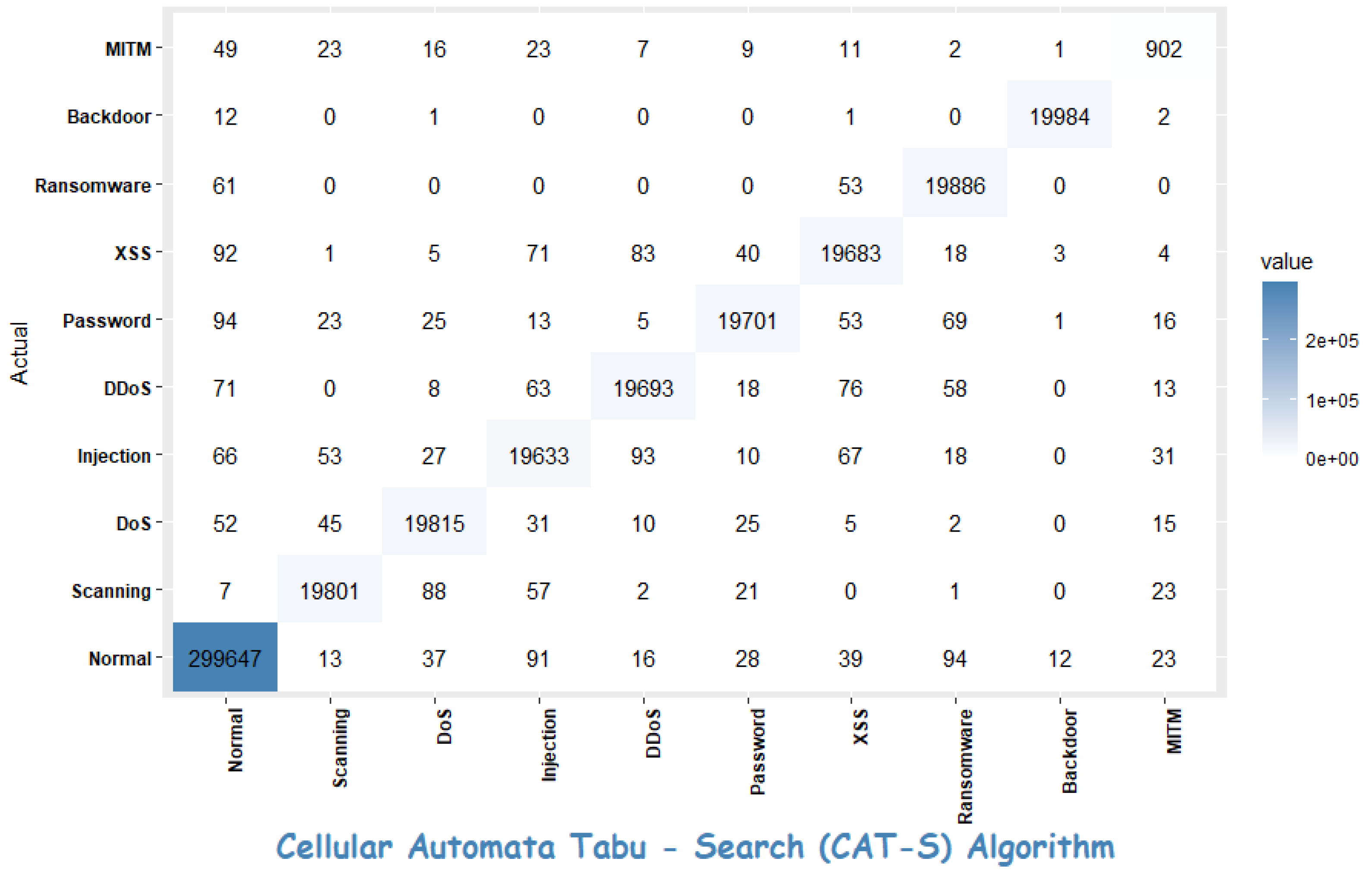
- The normal class has the number of highest true positives; however, it also has a significant number of false positives for some other classes (e.g., “Injection”, “DDoS”). The high false positives suggest that the classifier occasionally misclassifies instances as “Normal” when they belong to other classes.
- The scanning and DoS classes have a relatively high number of true positives and fewer false positives compared to some other classes. It indicates that the model performs relatively well in identifying instances of these classes.
- The injection class also has a reasonably high number of true positives but has a moderate number of false positives, particularly for the “Normal” class. This suggests that the model sometimes misclassifies “Injection” instances as “Normal”.
- The DDoS class has a high number of true positives and a relatively low number of false positives, indicating that the model performs well in identifying instances of this class.
- For other classes like Password, XSS, etc., they have varying numbers of true positives and false positives. The model’s performance in these classes may require further investigation and potentially fine-tuning.
- The precision values for the majority of the classes, such as “Normal”, “Scanning”, “DoS”, and “Password”, are very high, exceeding 0.98. This suggests that the model performs exceptionally well in correctly identifying instances of these classes and minimising false positives.
- The MITM class has moderately low precision as compared to other classes. This may be due to the smaller number of samples for the MITM class.
8. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
References
- Sengupta, J.; Ruj, S.; Bit, S.D. A comprehensive survey on attacks, security issues and blockchain solutions for IoT and IIoT. J. Netw. Comput. Appl. 2020, 149, 102481. [Google Scholar] [CrossRef]
- Lee, I. Internet of Things (IoT) cybersecurity: Literature review and IoT cyber risk management. Future Internet 2020, 12, 157. [Google Scholar] [CrossRef]
- Hung, M. Leading the IoT, gartner insights on how to lead in a connected world. Gart. Res. 2017, 1, 1–5. [Google Scholar]
- Symantec. Internet Security Threat Report; Technical Report; Symentec Corporaton: Tempe, AZ, USA, 2019; Volume 24. [Google Scholar]
- Louvieris, P.; Clewley, N.; Liu, X. Effects-based feature identification for network intrusion detection. Neurocomputing 2013, 121, 265–273. [Google Scholar] [CrossRef]
- Rathore, S.; Park, J.H. Semi-supervised learning based distributed attack detection framework for IoT. Appl. Soft Comput. 2018, 72, 79–89. [Google Scholar] [CrossRef]
- Capellupo, M.; Liranzo, J.; Bhuiyan, M.Z.A.; Hayajneh, T.; Wang, G. Security and Attack Vector Analysis of IoT Devices. In Security, Privacy, and Anonymity in Computation, Communication, and Storage; Wang, G., Atiquzzaman, M., Yan, Z., Choo, K.K.R., Eds.; Springer: Cham, Switzerland, 2017; pp. 593–606. [Google Scholar]
- Networks, P.A. 2020 Unit 42 IoT Threat Report; Technical Report; Palo Alto: Santa Clara, CA, USA, 2020. [Google Scholar]
- CVE: Common Vulnerabilities and Exposures (CVE). Available online: https://cve.mitre.org/ (accessed on 16 July 2022).
- Asharf, J.; Moustafa, N.; Khurshid, H.; Debie, E.; Haider, W.; Wahab, A. A review of intrusion-detection systems using machine and deep learning in internet of things: Challenges, solutions and future directions. Electronics 2020, 9, 1177. [Google Scholar] [CrossRef]
- Kaspersky: Antivirus Fundamentals: Viruses, Signatures, Disinfection. Available online: https://www.kaspersky.com/blog/signature-virus-disinfection/13233/ (accessed on 16 May 2018).
- Forouzan, B.A. TCP/IP Protocol Suite, 2nd ed.; McGraw-Hill Higher Education: New York, NY, USA, 2002. [Google Scholar]
- Dharmapurikar, S.; Krishnamurthy, P.; Sproull, T.; Lockwood, J. Deep packet inspection using parallel bloom filters. In Proceedings of the 11th Symposium on High Performance Interconnects, 2003. Proceedings, Stanford, CA, USA, 20–22 August 2003; pp. 44–51. [Google Scholar]
- Thomason, S. Improving network security: Next generation firewalls and advanced packet inspection devices. Glob. J. Comput. Sci. Technol. 2012, 12, 47–50. [Google Scholar]
- Gan, X.S.; Duanmu, J.S.; Wang, J.F.; Cong, W. Anomaly intrusion detection based on PLS feature extraction and core vector machine. Knowl. Based Syst. 2013, 40, 1–6. [Google Scholar] [CrossRef]
- Karami, A.; Guerrero-Zapata, M. A fuzzy anomaly detection system based on hybrid PSO-Kmeans algorithm in content-centric networks. Neurocomputing 2015, 149, 1253–1269. [Google Scholar] [CrossRef]
- Ripley, B.D. Pattern Recognition and Neural Networks; Cambridge University Press: Cambridge, UK, 2007. [Google Scholar]
- Kourou, K.; Exarchos, T.P.; Exarchos, K.P.; Karamouzis, M.V.; Fotiadis, D.I. Machine learning applications in cancer prognosis and prediction. Comput. Struct. Biotechnol. J. 2015, 13, 8–17. [Google Scholar] [CrossRef]
- Libbrecht, M.W.; Noble, W.S. Machine learning applications in genetics and genomics. Nat. Rev. Genet. 2015, 16, 321. [Google Scholar] [CrossRef] [PubMed]
- Tong, S.; Koller, D. Support vector machine active learning with applications to text classification. J. Mach. Learn. Res. 2001, 2, 45–66. [Google Scholar]
- Chopra, S.; Hadsell, R.; LeCun, Y. Learning a similarity metric discriminatively, with application to face verification. In Proceedings of the CVPR (1), San Diego, CA, USA, 20–25 June 2005; pp. 539–546. [Google Scholar]
- Khan, R.A.; Crenn, A.; Meyer, A.; Bouakaz, S. A novel database of children’s spontaneous facial expressions (LIRIS-CSE). Image Vis. Comput. 2019, 83, 61–69. [Google Scholar] [CrossRef]
- Khan, R.A.; Meyer, A.; Konik, H.; Bouakaz, S. Human vision inspired framework for facial expressions recognition. In Proceedings of the 2012 19th IEEE International Conference on Image Processing, Orlando, FL, USA, 30 September–3 October 2012; pp. 2593–2596. [Google Scholar] [CrossRef]
- Khan, R.A.; Meyer, A.; Konik, H.; Bouakaz, S. Saliency-based framework for facial expression recognition. Front. Comput. Sci. 2019, 13, 183–198. [Google Scholar] [CrossRef]
- Liu, H.; Motoda, H. Computational Methods of Feature Selection; CRC Press: Boca Raton, FL, USA, 2007. [Google Scholar]
- Kasongo, S.M.; Sun, Y. A deep learning method with wrapper based feature extraction for wireless intrusion-detection system. Comput. Secur. 2020, 92, 101752. [Google Scholar] [CrossRef]
- Panthong, R.; Srivihok, A. Wrapper feature subset selection for dimension reduction based on ensemble learning algorithm. Procedia Comput. Sci. 2015, 72, 162–169. [Google Scholar] [CrossRef]
- Lal, T.N.; Chapelle, O.; Weston, J.; Elisseeff, A. Embedded methods. In Feature Extraction; Springer: Berlin/Heidelberg, Germany, 2006; pp. 137–165. [Google Scholar]
- Nazir, A.; Khan, R.A. A novel combinatorial optimization based feature selection method for network intrusion detection. Comput. Secur. 2021, 102, 102164. [Google Scholar] [CrossRef]
- Nazir, A.; Khan, R.A. Network Intrusion Detection: Taxonomy and Machine Learning Applications. In Machine Intelligence and Big Data Analytics for Cybersecurity Applications; Maleh, Y., Shojafar, M., Alazab, M., Baddi, Y., Eds.; Springer International Publishing: Cham, Switzerland, 2021; pp. 3–28. [Google Scholar] [CrossRef]
- Diro, A.A.; Chilamkurti, N. Distributed attack detection scheme using deep learning approach for Internet of Things. Future Gener. Comput. Syst. 2018, 82, 761–768. [Google Scholar] [CrossRef]
- Alrawais, A.; Alhothaily, A.; Hu, C.; Cheng, X. Fog computing for the internet of things: Security and privacy issues. IEEE Internet Comput. 2017, 21, 34–42. [Google Scholar] [CrossRef]
- Masaeli, M.; Fung, G.; Dy, J.G. From transformation-based dimensionality reduction to feature selection. In Proceedings of the ICML, Haifa, Israel, 21–24 June 2010. [Google Scholar]
- Dash, M.; Choi, K.; Scheuermann, P.; Liu, H. Feature selection for clustering-a filter solution. In Proceedings of the 2002 IEEE International Conference on Data Mining, 2002. Proceedings, Maebashi City, Japan, 9–12 December 2002; pp. 115–122. [Google Scholar]
- He, X.; Cai, D.; Niyogi, P. Laplacian score for feature selection. In Proceedings of the Advances in Neural Information Processing Systems, Vancouver, BC, Canada, 5 December 2005; pp. 507–514. [Google Scholar]
- Moustafa, N.; Turnbull, B.; Choo, K.K.R. An Ensemble Intrusion Detection Technique Based on Proposed Statistical Flow Features for Protecting Network Traffic of Internet of Things. IEEE Internet Things J. 2019, 6, 4815–4830. [Google Scholar] [CrossRef]
- Anthi, E.; Williams, L.; Słowińska, M.; Theodorakopoulos, G.; Burnap, P. A supervised intrusion-detection system for smart home IoT devices. IEEE Internet Things J. 2019, 6, 9042–9053. [Google Scholar] [CrossRef]
- Zolanvari, M.; Teixeira, M.A.; Gupta, L.; Khan, K.M.; Jain, R. Machine learning-based network vulnerability analysis of industrial Internet of Things. IEEE Internet Things J. 2019, 6, 6822–6834. [Google Scholar] [CrossRef]
- Manimurugan, S.; Al-Mutairi, S.; Aborokbah, M.M.; Chilamkurti, N.; Ganesan, S.; Patan, R. Effective attack detection in internet of medical things smart environment using a deep belief neural network. IEEE Access 2020, 8, 77396–77404. [Google Scholar] [CrossRef]
- Eskandari, M.; Janjua, Z.H.; Vecchio, M.; Antonelli, F. Passban IDS: An intelligent anomaly-based intrusion-detection system for IoT edge devices. IEEE Internet Things J. 2020, 7, 6882–6897. [Google Scholar] [CrossRef]
- Ullah, I.; Mahmoud, Q.H. Design and Development of a Deep Learning-Based Model for Anomaly Detection in IoT Networks. IEEE Access 2021, 9, 103906–103926. [Google Scholar] [CrossRef]
- Alkahtani, H.; Aldhyani, T.H. Intrusion-detection system to advance internet of things infrastructure-based deep learning algorithms. Complexity 2021, 2021, 5579851. [Google Scholar] [CrossRef]
- Bays, C. Introduction to cellular automata and Conway’s Game of Life. In Game of Life Cellular Automata; Springer: Berlin/Heidelberg, Germany, 2010; pp. 1–7. [Google Scholar]
- Gallego, R.A.; Romero, R.; Monticelli, A.J. Tabu search algorithm for network synthesis. IEEE Trans. Power Syst. 2000, 15, 490–495. [Google Scholar] [CrossRef]
- Banfield, R.E.; Hall, L.O.; Bowyer, K.W.; Kegelmeyer, W.P. A comparison of decision tree ensemble creation techniques. IEEE Trans. Pattern Anal. Mach. Intell. 2006, 29, 173–180. [Google Scholar] [CrossRef]
- Khan, R.A.; Meyer, A.; Konik, H.; Bouakaz, S. Framework for reliable, real-time facial expression recognition for low resolution images. Pattern Recognit. Lett. 2013, 34, 1159–1168. [Google Scholar] [CrossRef]
- Ranger: A Fast Implementation of Random Forests in C++. Available online: https://github.com/imbs-hl/ranger (accessed on 20 June 2022).
- Kumar, P.; Gupta, G.P.; Tripathi, R. TP2SF: A Trustworthy Privacy-Preserving Secured Framework for sustainable smart cities by leveraging blockchain and machine learning. J. Syst. Archit. 2021, 115, 101954. [Google Scholar] [CrossRef]
- Gad, A.R.; Nashat, A.A.; Barkat, T.M. Intrusion-detection system using machine learning for vehicular ad hoc networks based on ToN-IoT dataset. IEEE Access 2021, 9, 142206–142217. [Google Scholar] [CrossRef]
- Dey, A.K.; Gupta, G.P.; Sahu, S.P. Hybrid Meta-Heuristic based Feature Selection Mechanism for Cyber-Attack Detection in IoT-enabled Networks. Procedia Comput. Sci. 2023, 218, 318–327. [Google Scholar] [CrossRef]
- Oseni, A.; Moustafa, N.; Creech, G.; Sohrabi, N.; Strelzoff, A.; Tari, Z.; Linkov, I. An explainable deep learning framework for resilient intrusion detection in IoT-enabled transportation networks. IEEE Trans. Intell. Transp. Syst. 2022, 24, 1000–1014. [Google Scholar] [CrossRef]
- Sarhan, M.; Layeghy, S.; Portmann, M. Towards a standard feature set for network intrusion-detection system datasets. Mob. Netw. Appl. 2022, 27, 357–370. [Google Scholar] [CrossRef]

| Year | Dataset | Attacks |
|---|---|---|
| 2018 | N-BaIot | Botnet (Mirai and BASHLITE) |
| 2019 | Bot-IoT | DoS/DDoS, Botnet, Information theft (data exfiltration, |
| keylogging), Reconnaissance (OS fingerprint, service scan) | ||
| 2019 | UNSW-IoT | DDos, MITM |
| 2019 | IoT Network Intrusion Dataset | DDoS, Botnet, MITM, Scanning |
| 2020 | TON IoT | DDoS, Ransomware, Backdoor, Data Injection |
| XSS, Password Cracking attack, MITM | ||
| 2020 | IoTID20 | DDoS, Botnet, MITM, Scanning |
| Year | Ref. | Dataset | Classifiers /Technique | FeatureSelection | Critical Comments |
|---|---|---|---|---|---|
| 2018 | [31] | NSL-KDD | Proposed a distributed Deep Learning (DL) model. | None | The authors claimed that the performance of the proposed distributed DL model is better than traditional machine learning systems; however, the comparison results are not presented. The authors used the NSL-KDD dataset, which was published in the year 2000 and was not designed to represent network traffic and attack vectors of current IoT systems. |
| 2019 | [36] | UNSW-NB15, NIMS botnet dataset with simulated sensors’ data | Proposed AdaBoost-based ensemble learning | Coefficient Correlation | Proposed the AdaBoost ensemble learning method by using three ML techniques. Decision Tree (DT), Naive Bayes (NB) and Artificial Neural Networks (ANNs). Comparison is performed on DNS and HTTP traffic. Comparison results showed that the proposed ensemble technique performed better than DT, NB, and ANN. |
| 2019 | [37] | Designed and deployed IoT testbed for data collection | They used nine different classifiers for testing. NB, BN, J48, Zero R, OneR, Simple Logistic, SVM, MLP, RF | Gain ratio, coefficient correlation | Proposed model comprised three-layer design to detect intrusion, i.e., (i) classifies the type of attack and profiles the normal behaviour of IoT appliances, (ii) identifies malicious packets, and (iii) classifies the type of the attack. The study is carried out in a custom design testbed built for evaluation. |
| 2019 | [38] | Collected traffic from the testbed | They studied seven different techniques SVM, KNN, NB, RF, DT, LR and ANN | Yes, chose features whose values change during attack phases compared to normal operation phases. Feature Ranking | The authors built a real-world testbed to conduct attacks and design an IDS. They performed backdoor, command injection and SQLi attacks. Results shows that Random Forest’s accuracy is highest among all classifiers. |
| 2020 | [39] | CICIDS 2017 | Proposed DL-based technique Deep Belief Network (DBN) and compared with SVMIDS, RNNIDS, SNNIDS, FNNIDS | None | The authors compared DBN with other mentioned techniques. Simulation results show that DBN performed better than the other studied techniques. |
| 2020 | [40] | Built their own dataset by collecting logs from in house testbed | Passban—IDS | None | The authors designed and built an anomaly-based IDS for attack detection. They launched port scanning, http and ssh brute force, and syn flooding attacks The results are not compared with other approaches. |
| 2021 | [41] | BoT-IoT, IoT Network Intrusion, MQTT- IoT-IDS2020, and IoT-23 | Proposed a novel intrusion detection model based on CNN by using transfer learning. | Recursive Feature Elimination (RFE) | Proposed CNN-based model for IDS. Transfer learning is used to implement binary and multiclass classification. |
| 2021 | [42] | IoTID20 | CNN, LSTM and hybrid CNN-LSTM model | PSO | Comparison with state-of-the-art techniques proved that it has good performance |
| Parameter | Value |
|---|---|
| Tabu List size | 7 |
| No. of neighbours in each iteration | 5 |
| Aspiration level | 0.02 |
| Stopping criteria | Max. number of iterations (set to 100) |
| Reference | Classifier | Feature-Selection Technique | Accuracy | FPR | Number of Features | Cost |
|---|---|---|---|---|---|---|
| Kumar et al. [48] | XG-Boost | TP2SF | 98.84 | NA | 19 | 6.713 + fpr |
| Gad et al. [49] | XG-Boost | Chi2-SMOTE | 99.10 | NA | 20 | 6.959 + fpr |
| Dey et al. [50] | SVM | NSGA-II | 98.86 | NA | 18 | 6.373 + fpr |
| Dey et al. [50] | SVM | Filter + NSGA-II | 99.48 | NA | 13 | 4.502 + fpr |
| Oseni et al. [51] | CNN | CC | 90.55 | NA | NA | 3.146 + n + fpr |
| M Sarhan et al. [52] | Extra Trees | NA | 98.05 | NA | NA | 0.649 + n + fpr |
| CAT-S | RF | CAT-S | 99.50 | 0.004 | 13 | 4.496 |
| Type | Precision |
|---|---|
| Normal | 0.998320845 |
| Scanning | 0.992083772 |
| DoS | 0.989661372 |
| Injection | 0.982534281 |
| DDoS | 0.989150635 |
| Password | 0.992393713 |
| XSS | 0.984740845 |
| Ransomware | 0.986996228 |
| Backdoor | 0.999150042 |
| MITM | 0.876579203 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2023 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Nazir, A.; Memon, Z.; Sadiq, T.; Rahman, H.; Khan, I.U. A Novel Feature-Selection Algorithm in IoT Networks for Intrusion Detection. Sensors 2023, 23, 8153. https://doi.org/10.3390/s23198153
Nazir A, Memon Z, Sadiq T, Rahman H, Khan IU. A Novel Feature-Selection Algorithm in IoT Networks for Intrusion Detection. Sensors. 2023; 23(19):8153. https://doi.org/10.3390/s23198153
Chicago/Turabian StyleNazir, Anjum, Zulfiqar Memon, Touseef Sadiq, Hameedur Rahman, and Inam Ullah Khan. 2023. "A Novel Feature-Selection Algorithm in IoT Networks for Intrusion Detection" Sensors 23, no. 19: 8153. https://doi.org/10.3390/s23198153
APA StyleNazir, A., Memon, Z., Sadiq, T., Rahman, H., & Khan, I. U. (2023). A Novel Feature-Selection Algorithm in IoT Networks for Intrusion Detection. Sensors, 23(19), 8153. https://doi.org/10.3390/s23198153






