Melding Fog Computing and IoT for Deploying Secure, Response-Capable Healthcare Services in 5G and Beyond
Abstract
1. Introduction
2. Technical Enablers for Contemporary Health-Monitoring Services
2.1. IoT and Fog Computing
2.2. 5G
2.2.1. SDN/NFV
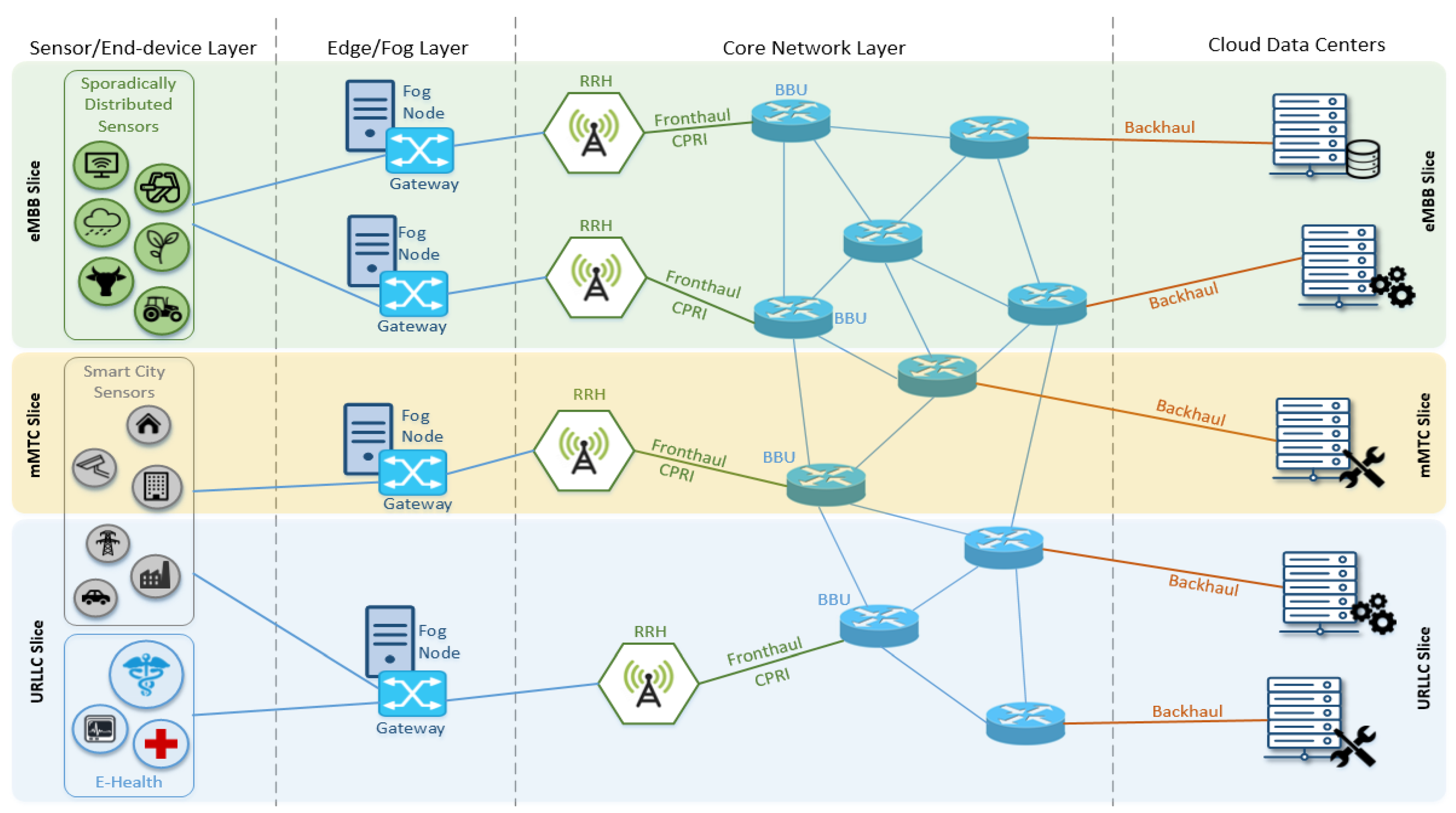
2.2.2. Network Slicing
3. Designing Response-Capable Healthcare Application Frameworks
3.1. Next-Generation Emergency Services
3.2. Experimental Evaluation Based on Next-Generation Emergency Services
3.3. Dominant Healthcare Application Framework Use Cases
- Patient self-monitoring, involving end-users willing to monitor their own medical condition, for instance when recuperating from an incident or simply as part of a preventive health monitoring routine with inherent support for early identification of potentially alarming metrics.
- Physician off-line monitoring, targeting doctors using fog-enabled medical grade wearables to monitor their patients. The patients must carry the wearable device at home and then, after a predefined period, return the device to their physician, allowing the physician to acquire the traces and conduct the diagnosis.
- Physician on-line monitoring, which extends the previous use case and grants to the physician the ability of remotely monitoring all accumulated vital traces through secure and highly available cloud services
- Patient monitoring within healthcare infrastructure, in which the wearable devices are operated by a personal health assistant or professional caregiver, inside an ambulance, hospital or adult daycare center to instantly acquire patient vitals and carry out real-time situation evaluation before storing the data to the cloud services for future reference and analysis.
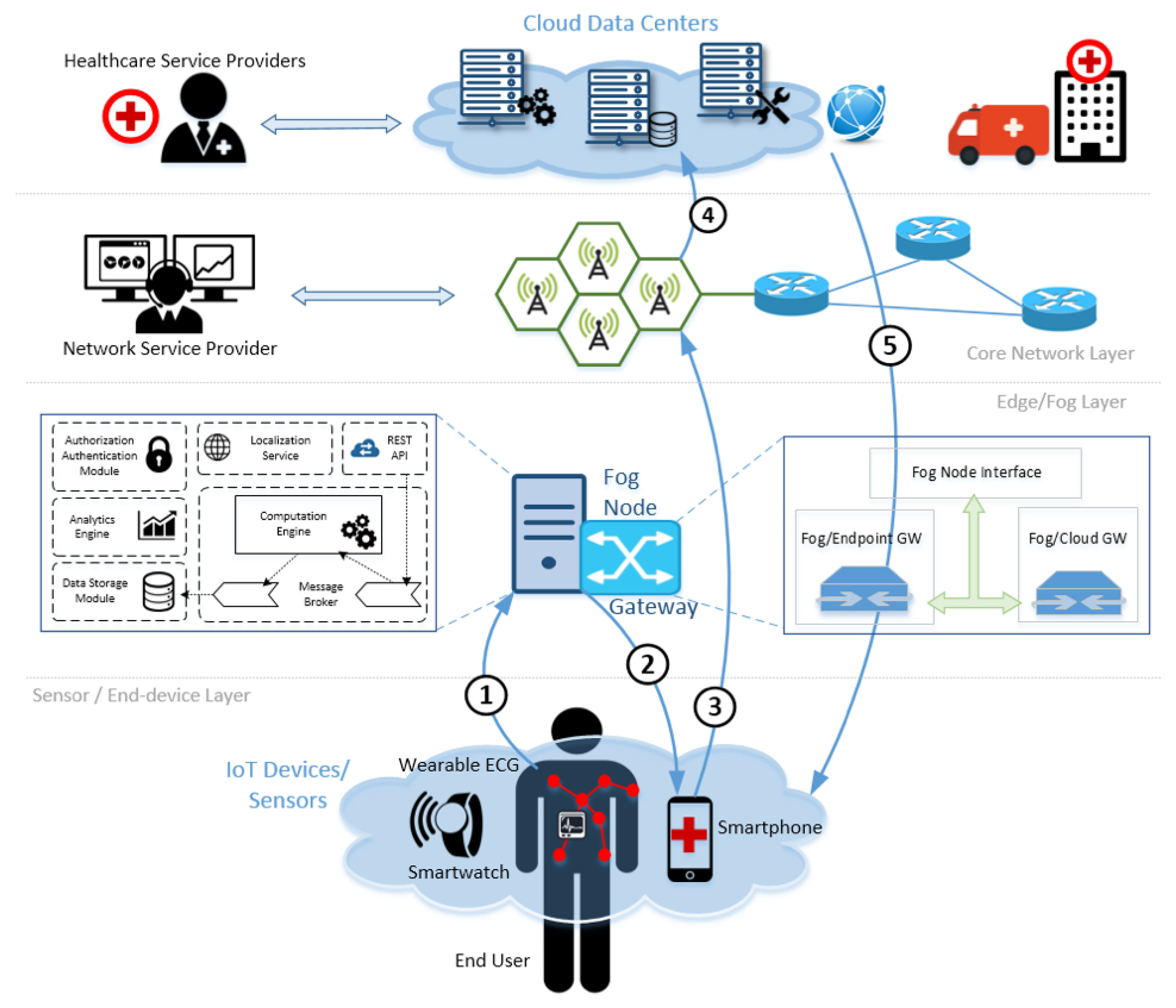
4. Proposed Architecture
4.1. Fog Node
4.2. Gateway
4.3. Delivering Response-Capable Emergency Healthcare Services over 5G Infrastructure
5. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
References
- European Commission. The European Emergency Number 112. Available online: https://bit.ly/2UnEbyz (accessed on 9 March 2022).
- Tselios, C.; Tsolis, G. On QoE-awareness through virtualized probes in 5G networks. In Proceedings of the 2016 IEEE 21st International Workshop on Computer Aided Modelling and Design of Communication Links and Networks (CAMAD), Toronto, ON, Canada, 23–25 October 2016; pp. 159–164. [Google Scholar] [CrossRef]
- Politis, I.; Lykourgiotis, A.; Tselios, C.; Orfanoudakis, T. On Measuring the Efficiency of Next Generation Emergency Communications: The EMYNOS Paradigm. In Proceedings of the 2018 IEEE International Conference on Communications (ICC), Kansas City, MO, USA, 20–24 May 2018; pp. 1–6. [Google Scholar] [CrossRef]
- Bonomi, F.; Milito, R.; Zhu, J.; Addepalli, S. Fog computing and its role in the internet of things. In Proceedings of the First Edition of the MCC Workshop on Mobile Cloud Computing (MCC’12), Helsinki, Finland, 17 August 2012; Association for Computing Machinery: New York, NY, USA, 2012; pp. 13–16. [Google Scholar] [CrossRef]
- Porambage, P.; Okwuibe, J.; Liyanage, M.; Ylianttila, M.; Taleb, T. Survey on Multi-Access Edge Computing for Internet of Things Realization. IEEE Commun. Surv. Tutor. 2018, 20, 2961–2991. [Google Scholar] [CrossRef]
- Chiang, M.; Zhang, T. Fog and IoT: An Overview of Research Opportunities. IEEE Internet Things J. 2016, 3, 854–864. [Google Scholar] [CrossRef]
- Jia, B.; Hu, H.; Zeng, Y.; Xu, T.; Yang, Y. Double-matching resource allocation strategy in fog computing networks based on cost efficiency. J. Commun. Netw. 2018, 20, 237–246. [Google Scholar] [CrossRef]
- Liu, Z.; Yang, Y.; Chen, Y.; Li, K.; Li, Z.; Luo, X. A Multi-tier Cost Model for Effective User Scheduling in Fog Computing Networks. In Proceedings of the IEEE INFOCOM 2019—IEEE Conference on Computer Communications Workshops (INFOCOM WKSHPS), Paris, France, 29 April–2 May 2019; pp. 1–6. [Google Scholar] [CrossRef]
- Dang, T.D.; Hoang, D. A data protection model for fog computing. In Proceedings of the 2017 Second International Conference on Fog and Mobile Edge Computing (FMEC), Valencia, Spain, 8–11 May 2017; pp. 32–38. [Google Scholar] [CrossRef]
- Bousselham, M.; Benamar, N.; Addaim, A. A new Security Mechanism for Vehicular Cloud Computing Using Fog Computing System. In Proceedings of the 2019 International Conference on Wireless Technologies, Embedded and Intelligent Systems (WITS), Fez, Morocco, 3–4 April 2019; pp. 1–4. [Google Scholar] [CrossRef]
- Song, C.; Zhang, M.; Zhan, Y.; Wang, D.; Guan, L.; Liu, W.; Zhang, L.; Xu, S. Hierarchical edge cloud enabling network slicing for 5G optical fronthaul. J. Opt. Commun. Netw. 2019, 11, B60–B70. [Google Scholar] [CrossRef]
- Liu, G.; Wu, J.; Wang, T. Blockchain-enabled fog resource access and granting. Intell. Converg. Netw. 2021, 2, 108–114. [Google Scholar] [CrossRef]
- Al-Khafajiy, M.; Baker, T.; Waraich, A.; Alfandi, O.; Hussien, A. Enabling High Performance Fog Computing through Fog-2-Fog Coordination Model. In Proceedings of the 2019 IEEE/ACS 16th International Conference on Computer Systems and Applications (AICCSA), Abu Dhabi, United Arab Emirates, 3–7 November 2019; pp. 1–6. [Google Scholar] [CrossRef]
- Akrivopoulos, O.; Chatzigiannakis, I.; Tselios, C.; Antoniou, A. On the Deployment of Healthcare Applications over Fog Computing Infrastructure. In Proceedings of the 2017 IEEE 41st Annual Computer Software and Applications Conference (COMPSAC), Turin, Italy, 4–8 July 2017; pp. 288–293. [Google Scholar] [CrossRef]
- Sangaiah, A.K.; Medhane, D.V.; Han, T.; Hossain, M.S.; Muhammad, G. Enforcing position-based confidentiality with machine learning paradigm through mobile edge computing in real-time industrial informatics. IEEE Trans. Ind. Inform. 2019, 15, 4189–4196. [Google Scholar] [CrossRef]
- Bolivar, L.T.; Tselios, C.; Area, D.M.; Tsolis, G. On the Deployment of an Open-Source, 5G-Aware Evaluation Testbed. In Proceedings of the 2018 6th IEEE International Conference on Mobile Cloud Computing, Services, and Engineering (MobileCloud), Bamberg, Germany, 26–29 March 2018; pp. 51–58. [Google Scholar] [CrossRef]
- ETSI, GS NFV 002, Network Functions Virtualisation (NFV): Architectural Framework, V.1.2.1. December 2014. Available online: https://bit.ly/2ZYlrrI (accessed on 9 March 2022).
- Ordonez-Lucena, J.; Adamuz-Hinojosa, O.; Ameigeiras, P.; Muñoz, P.; Ramos-Muñoz, J.J.; Chavarria, J.F.; Lopez, D. The Creation Phase in Network Slicing: From a Service Order to an Operative Network Slice. In Proceedings of the 2018 European Conference on Networks and Communications (EuCNC), Ljubljana, Slovenia, 18–21 June 2018; pp. 1–36. [Google Scholar] [CrossRef]
- Infiesta, J.T.; Guimarães, C.; Contreras, L.M.; de la Oliva, A. GANSO: Automate Network Slicing at the Transport Network Interconnecting the Edge. In Proceedings of the 2020 IEEE Conference on Network Function Virtualization and Software Defined Networks (NFV-SDN), Leganes, Spain, 10–12 November 2020; pp. 161–166. [Google Scholar] [CrossRef]
- Afolabi, I.; Taleb, T.; Samdanis, K.; Ksentini, A.; Flinck, H. Network Slicing and Softwarization: A Survey on Principles, Enabling Technologies, and Solutions. IEEE Commun. Surv. Tutor. 2018, 20, 2429–2453. [Google Scholar] [CrossRef]
- Chafika, B.; Taleb, T.; Phan, C.-T.; Tselios, C.; Tsolis, G. Distributed AI-based Security for Massive Numbers of Network Slices in 5G & Beyond Mobile Systems. In Proceedings of the 2021 Joint European Conference on Networks and Communications & 6G Summit (EuCNC/6G Summit), Porto, Portugal, 8–11 June 2021; pp. 401–406. [Google Scholar] [CrossRef]
- Guan, W.; Wen, X.; Wang, L.; Lu, Z.; Shen, Y. A Service-Oriented Deployment Policy of End-to-End Network Slicing Based on Complex Network Theory. IEEE Access 2018, 6, 19691–19701. [Google Scholar] [CrossRef]
- Ai, Y.; Qiu, G.; Liu, C.; Sun, Y. Joint resource allocation and admission control in sliced fog radio access networks. China Commun. 2020, 17, 14–30. [Google Scholar] [CrossRef]
- Karras, K.; Pallis, E.; Mastorakis, G.; Nikoloudakis, Y.; Batalla, J.M.; Mavromoustakis, C.X.; Markakis, E. A hardware acceleration platform for AI-based inference at the edge. Circuits Syst. Signal Process. 2020, 39, 1059–1070. [Google Scholar] [CrossRef]
- Kukliński, S.; Kołakowski, R.; Tomaszewski, L.; Sanabria-Russo, L.; Verikoukis, C.; Phan, C.T.; Zanzi, L.; Devoti, F.; Ksentini, A.; Tselios, C.; et al. MonB5G: AI/ML-Capable Distributed Orchestration and Management Framework for Network Slices. In Proceedings of the 2021 IEEE International Mediterranean Conference on Communications and Networking (MeditCom), Athens, Greece, 7–10 September 2021; pp. 29–34. [Google Scholar] [CrossRef]
- Ulema, M.; Zuckerman, D.; Chatzimisios, P.; Granelli, F.; Mangra, N.; Markakis, E.; Namuduri, K.; Nikoloudakis, Y.; Rawat, P.; Shakir, M.Z.; et al. Public Safety Technology Gaps and Opportunities. Available online: https://bit.ly/3KyotXH (accessed on 9 March 2022).
- Markakis, E.K.; Politis, I.; Lykourgiotis, A.; Rebahi, Y.; Mastorakis, G.; Mavromoustakis, C.X.; Pallis, E. Efficient Next Generation Emergency Communications over Multi-Access Edge Computing. IEEE Commun. Mag. 2017, 55, 92–97. [Google Scholar] [CrossRef]
- Markakis, E.; Nikoloudakis, Y.; Mastorakis, G.; Mavromoustakis, C.X.; Pallis, E.; Sideris, A.; Zotos, N.; Antic, J.; Cernivec, A.; Fejzic, D.; et al. Acceleration at the Edge for Supporting SMEs Security: The FORTIKA Paradigm. IEEE Commun. Mag. 2019, 57, 41–47. [Google Scholar] [CrossRef]
- Markakis, E.; Nikoloudakis, Y.; Pallis, E.; Manso, M. Security Assessment as a Service Cross-Layered System for the Adoption of Digital, Personalised and Trusted Healthcare. In Proceedings of the 2019 IEEE 5th World Forum on Internet of Things (WF-IoT), Limerick, Ireland, 15–18 April 2019; pp. 91–94. [Google Scholar] [CrossRef]
- Markakis, E.K.; Lykourgiotis, A.; Politis, I.; Dagiuklas, A.; Rebahi, Y.; Pallis, E. EMYNOS: Next Generation Emergency Communication. IEEE Commun. Mag. 2017, 55, 139–145. [Google Scholar] [CrossRef][Green Version]
- Sendra, S.; Parra, L.; Lloret, J.; Tomás, J. Smart system for children’s chronic illness monitoring. Inf. Fusion 2018, 40, 76–86. [Google Scholar] [CrossRef]
- Lloret, J.; Parra, L.; Taha, M.; Tomás, J. An architecture and protocol for smart continuous eHealth monitoring using 5G. Comput. Netw. 2017, 129, 340–351. [Google Scholar] [CrossRef]
- Akrivopoulos, O.; Zhu, N.; Amaxilatis, D.; Tselios, C.; Anagnostopoulos, A.; Chatzigiannakis, I. A Fog Computing-Oriented, Highly Scalable IoT Framework for Monitoring Public Educational Buildings. In Proceedings of the 2018 IEEE International Conference on Communications (ICC), City, MO, USA, 20–24 May 2018; pp. 1–6. [Google Scholar] [CrossRef]

| SIP MSG. Rate (Messages/s) | Transmitted | Successful | Unacknowledged | Re-Transmitted |
|---|---|---|---|---|
| 30 | 1000 | 943 | 57 | 1539 |
| 40 | 1000 | 763 | 237 | 2152 |
| 50 | 1000 | 664 | 336 | 2305 |
| 60 | 1000 | 548 | 452 | 2424 |
| Rate (Messages/s) | Transmitted | Successful | Unacknowledged | Re-Transmitted |
|---|---|---|---|---|
| 30 | 1000 | 975 | 25 | 998 |
| 35 | 1000 | 762 | 238 | 1867 |
| 40 | 1000 | 763 | 237 | 2058 |
| 45 | 1000 | 616 | 384 | 2239 |
| 50 | 1000 | 666 | 334 | 2204 |
| 55 | 1000 | 511 | 489 | 2375 |
| 60 | 1000 | 539 | 461 | 2353 |
| 30 | 2000 | 1677 | 373 | 3615 |
| 35 | 2000 | 1417 | 583 | 4305 |
| 40 | 2000 | 1483 | 517 | 4375 |
| 45 | 2000 | 1173 | 827 | 4686 |
| 50 | 2000 | 1226 | 774 | 4649 |
| 55 | 2000 | 1005 | 995 | 4886 |
| 60 | 2000 | 1061 | 939 | 4834 |
| Packet Loss (%) | Transmitted | Successful | Unacknowledged | Re-Transmitted |
|---|---|---|---|---|
| 2 | 1000 | 986 | 14 | 2712 |
| 5 | 1000 | 985 | 15 | 2828 |
| 7 | 1000 | 984 | 16 | 3094 |
| 10 | 1000 | 970 | 30 | 4599 |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2022 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Tselios, C.; Politis, I.; Amaxilatis, D.; Akrivopoulos, O.; Chatzigiannakis, I.; Panagiotakis, S.; Markakis, E.K. Melding Fog Computing and IoT for Deploying Secure, Response-Capable Healthcare Services in 5G and Beyond. Sensors 2022, 22, 3375. https://doi.org/10.3390/s22093375
Tselios C, Politis I, Amaxilatis D, Akrivopoulos O, Chatzigiannakis I, Panagiotakis S, Markakis EK. Melding Fog Computing and IoT for Deploying Secure, Response-Capable Healthcare Services in 5G and Beyond. Sensors. 2022; 22(9):3375. https://doi.org/10.3390/s22093375
Chicago/Turabian StyleTselios, Christos, Ilias Politis, Dimitrios Amaxilatis, Orestis Akrivopoulos, Ioannis Chatzigiannakis, Spyros Panagiotakis, and Evangelos K. Markakis. 2022. "Melding Fog Computing and IoT for Deploying Secure, Response-Capable Healthcare Services in 5G and Beyond" Sensors 22, no. 9: 3375. https://doi.org/10.3390/s22093375
APA StyleTselios, C., Politis, I., Amaxilatis, D., Akrivopoulos, O., Chatzigiannakis, I., Panagiotakis, S., & Markakis, E. K. (2022). Melding Fog Computing and IoT for Deploying Secure, Response-Capable Healthcare Services in 5G and Beyond. Sensors, 22(9), 3375. https://doi.org/10.3390/s22093375









