Towards Enhancing the Robustness of Scale-Free IoT Networks by an Intelligent Rewiring Mechanism
Abstract
1. Introduction
- Closeness Centrality (CC) measure is utilized to determine the central nodes in the network using minimum computational time.
- An Intelligent Rewiring (INTR) mechanism is proposed to make an optimized SFN using the intelligent selection of nodes.
- Using the global information of nodes, the network is optimized against CC based node removal.
- The Recalculated High Degree based Link Attack (RHDLA) and the High Degree based Link Attack (HDLA) are proposed to affect the network connectivity effectively using the local information of nodes.
2. Related Work
3. Initialization of Scale-Free Network and Robustness Measure
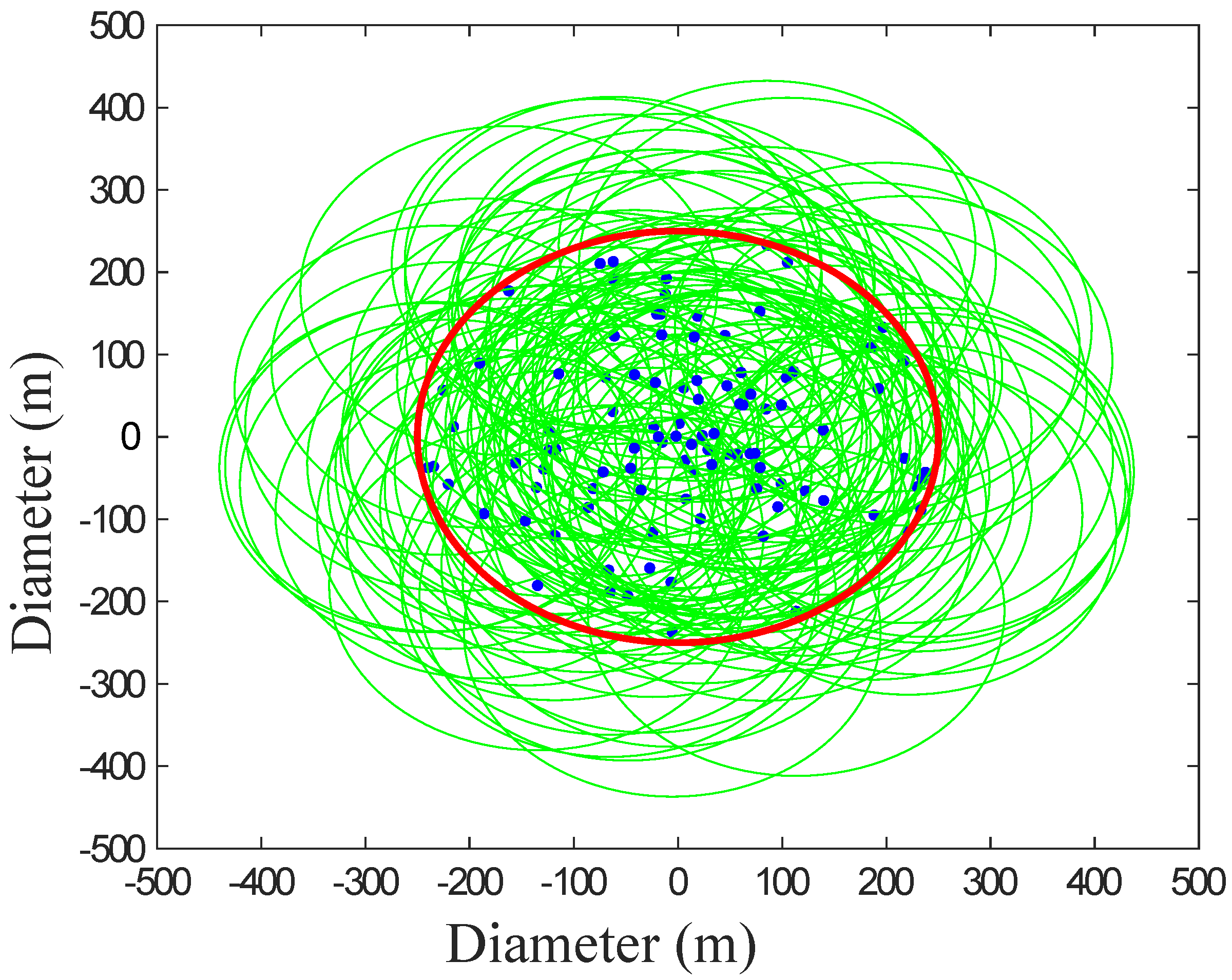
3.1. Initial Scale-Free Network Construction
| Algorithm 1: Construction of an Initial SFN |
Input: A, N, m Output: 1: Procedure BA model (A) 2: Random deployment of nodes 3: for all do 4: broadcast the packet 5: 6: If then 7: Make edge with the node that replies first 8: else 9: for all do 10: Calculate connection probability 11: Roulette wheel based node selection 12: end for 13: end if 14: end for 15: end procedure 16: Update: |
3.2. Robustness Metric
3.3. Closeness Centrality Based Malicious Attacks
| Algorithm 2: Evaluate R Against Closeness Centrality Measure |
Input: G, N Output: MCS, G2, R 1: Procedure Centrality Measure (G) 2: for all do 3: Find CC of all nodes using Equation (2) 4: Select node having maximum value of CC in G 5: Remove the node and update G to G2 6: Calculate R using Equation (1) 7: end for 8: end procedure |
3.4. HDLA and RHDLA Based Link Attacks
| Algorithm 3: HDLA and RHDLA |
Input: A, E, N Output: 1: Procedure High Degree Link Attacks (A) 2: for all do 3: Calculate the edge’s degree of whole network as Ed 4: Sort Ed 5: Remove max(Ed) 6: Calculate connectivity of the network 7: end for 8: end procedure |
3.5. Optimization of Network Using Independent Edges
3.6. INTR Mechanism
| Algorithm 4: INTR Mechanism |
Input: N, E, G Output: R, A 1: Procedure INTR Based Edge Rewire (A) 2: for all do 3: Find the highest degree node and mark it as i 4: Find the lowest degree neighbor node j based on i 5: Find the second highest degree node and marked k 6: Find the lowest degree neighbor node l based on k 7: Mark edges ij and kl 8: if both edges are independent from E 9: Rewire edge (i,k) and edge (j,l) 10: Calculate R 11: Update A and G 12: end if 13: end for 14: end procedure |
4. Simulation Results and Discussion
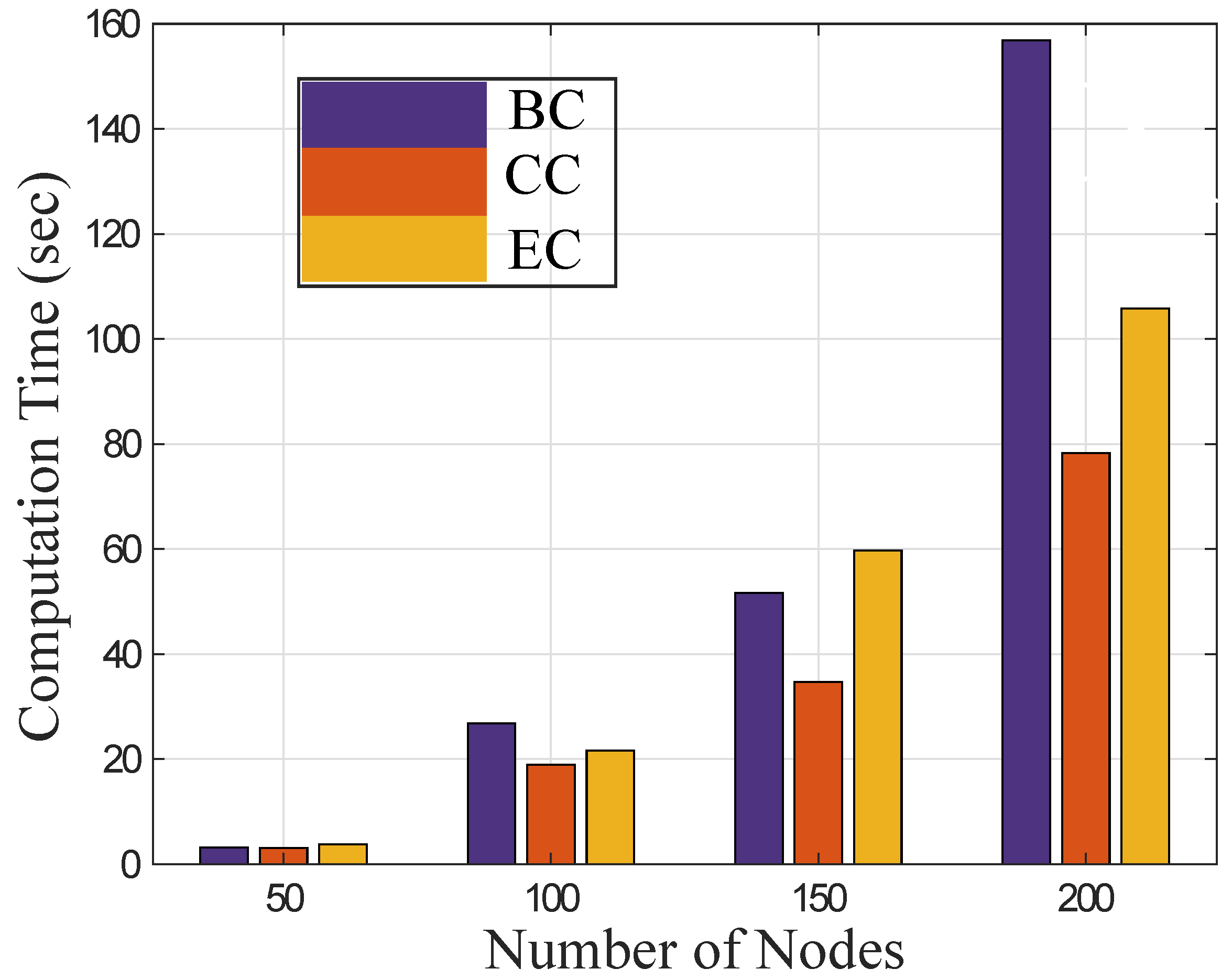
4.1. Evaluation of Centrality Measures with Computational Time
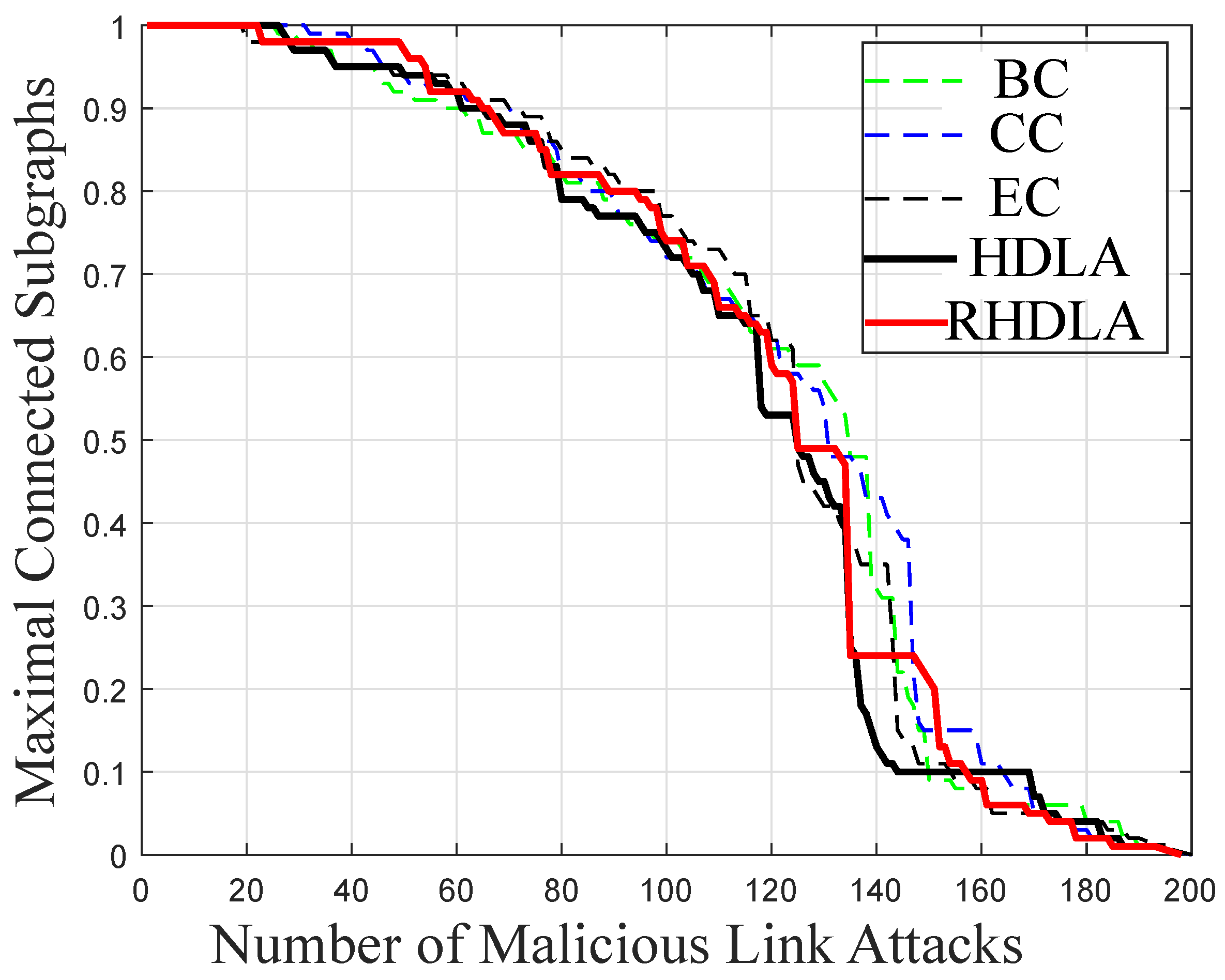
4.2. Network Connectivity against Link Attacks
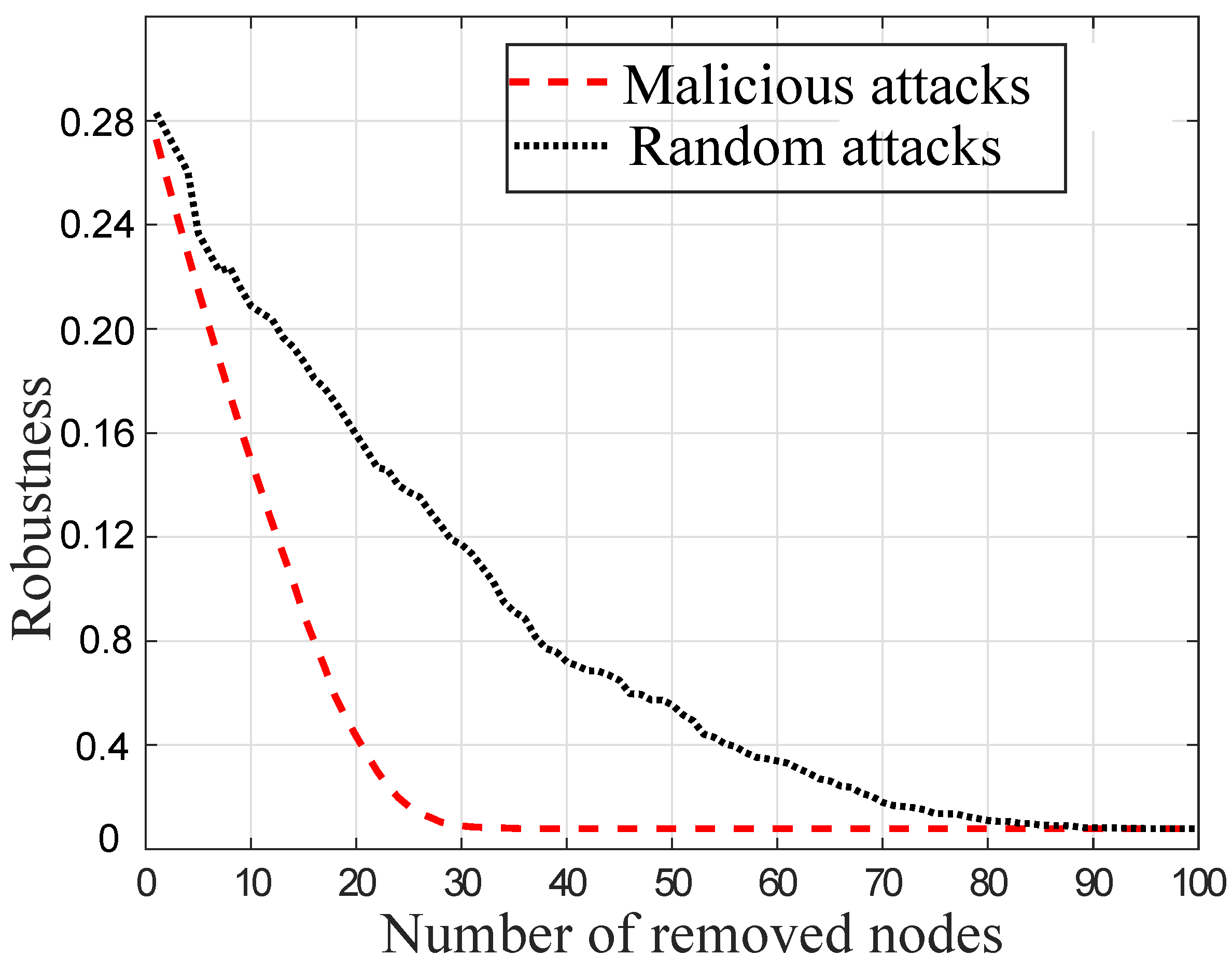
4.3. Robustness against Random and Malicious Attacks
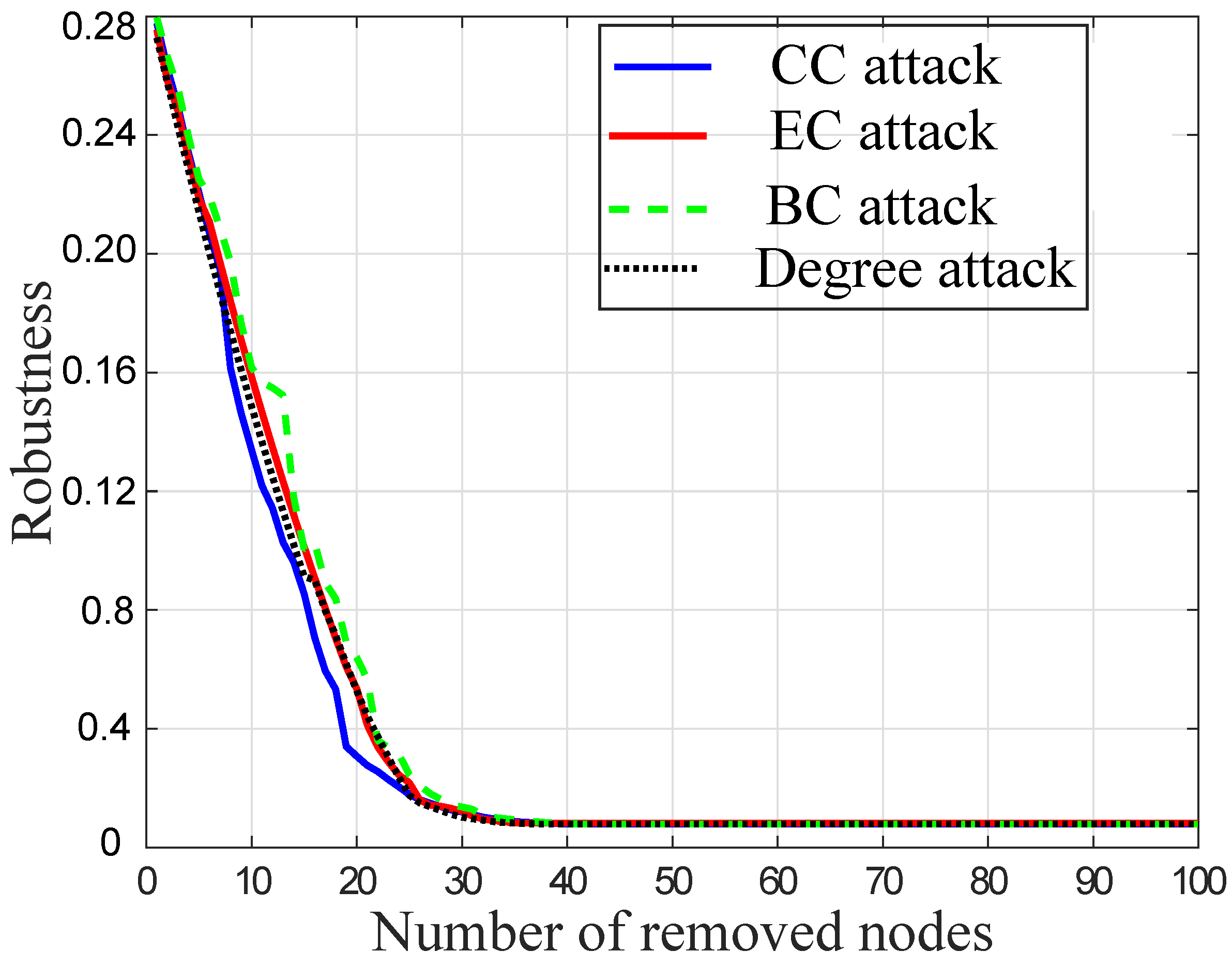
4.4. Centrality Based Node Attacks
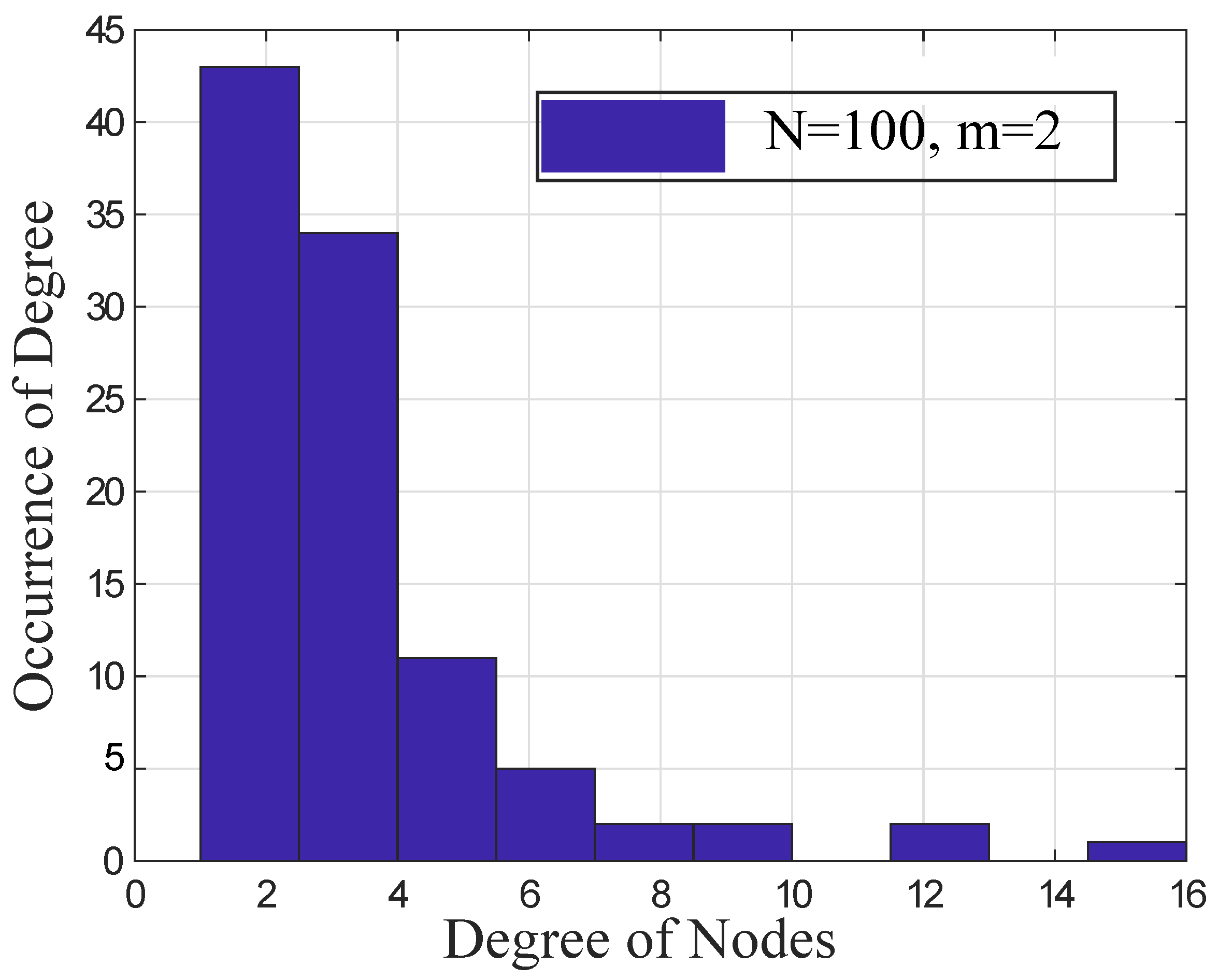
4.5. Evaluate the Power-Law Distribution
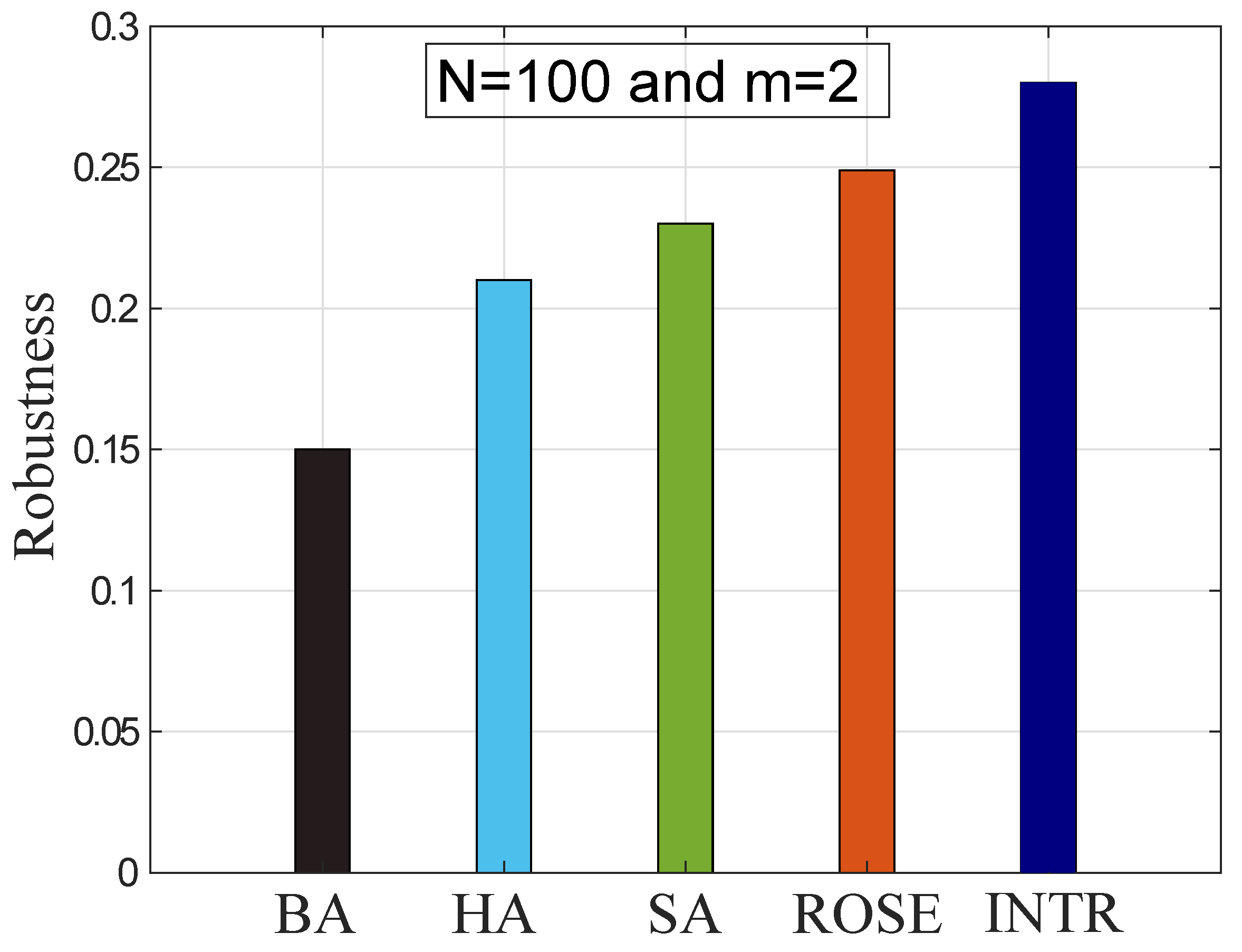
4.6. Comparison with Existing Algorithms
5. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Acknowledgments
Conflicts of Interest
Abbreviations
| Abbreviations and Acronyms | Description |
| BA | Barabasi Albert |
| BC | Betweenness Centrality |
| CC | Closeness Centrality |
| DE | Differential Evolution |
| EHO | Elephant Herding Optimization |
| GA | Genetic Algorithm |
| GM | Greedy Model |
| HA | Hill Climbing |
| HDLA | High Degree based Link Attacks |
| INTR | Intelligent Rewiring |
| IoT | Internet of Things |
| MAs | Malicious Attacks |
| MCS | Maximum Connected Subgraphs |
| MPGA | Multiple Population Genetic Algorithm |
| NCM | Natural Connectivity Model |
| RAs | Random Attacks |
| R | Robustness |
| RHDLA | Recalculated High Degree based Link Attacks |
| SA | Simulated Annealing |
| SFNs | Scale-Free Networks |
| SWNs | Small World Networks |
| WSNs | Wireless Sensor Networks |
| A | Adjacency matrix of network |
| Closeness of a node x | |
| Shortest distance between y and x | |
| E | Number of edges in graph |
| G | Current graph |
| Updated graph | |
| m | Edge density |
| N | Total number of nodes |
References
- Elfouly, F.H.; Ramadan, R.A.; Khedr, A.Y.; Yadav, K.; Azar, A.T.; Abdelhamed, M.A. Efficient Node Deployment of Large-Scale Heterogeneous Wireless Sensor Networks. Appl. Sci. 2021, 11, 10924. [Google Scholar] [CrossRef]
- Kumar, D.S.; Nagarajan, N.; Azar, A.T. An Improved Key Management Scheme with High Security in Wireless Sensor Networks. In Bio-Inspiring Cyber Security and Cloud Services: Trends and Innovations, Intelligent Systems Reference Library; Springer: Berlin/Heidelberg, Germany, 2014; pp. 249–264. [Google Scholar]
- Abdelgawad, A. and Yelamarthi, K. Internet of Things (IoT) platform for structure health monitoring. Wirel. Commun. Mob. Comput. 2017, 2017, 6560797. [Google Scholar] [CrossRef]
- Liu, Y.; Weng, X.; Wan, J.; Yue, X.; Song, H.; Vasilakos, A.V. Exploring data validity in transportation systems for smart cities. IEEE Commun. Mag. 2017, 55, 26–33. [Google Scholar] [CrossRef]
- Lou, Y.; Zhang, L. Defending transportation networks against random and targeted attacks. Transp. Res. Rec. 2011, 2234, 31–40. [Google Scholar] [CrossRef]
- Aslam, S.; Michaelides, M.P.; Herodotou, H. Internet of ships: A survey on architectures, emerging applications, and challenges. IEEE Internet Things J. 2020, 7, 9714–9727. [Google Scholar] [CrossRef]
- Javaid, N. Integration of Context Awareness in Internet of Agricultural Things. ICT Express, 2021; in press. [Google Scholar] [CrossRef]
- Li, S.; Da Xu, L.; Zhao, S. 5g internet of things: A survey. J. Ind. Inf. Integr. 2018, 10, 1–9. [Google Scholar] [CrossRef]
- Javaid, N.; Sher, A.; Nasir, H.; Guizani, N. Intelligence in IoT-based 5G networks: Opportunities and challenges. IEEE Commun. Mag. 2018, 56, 94–100. [Google Scholar] [CrossRef]
- Javaid, N. A Secure and Efficient Trust Model for Wireless Sensor IoTs using Blockchain. IEEE Access 2022, 10, 4568–4579. [Google Scholar] [CrossRef]
- Chen, Q.; Yin, X.; You, D.; Hou, H.; Tong, G.; Wang, B.; Liu, H. Review on blackout process in China Southern area main power grid in 2008 snow disaster. In Proceedings of the IEEE Power and Energy Society General Meeting, Calgary, AB, Canada, 26–30 July 2009; pp. 1–8. [Google Scholar]
- Jaffee, D.M. The US subprime mortgage crisis: Issues raised and lessons learned. In Urbanization and Growth; World Bank Publications: Washington, DC, USA, 2008; p. 197. [Google Scholar]
- Watts, D.J.; Strogatz, S.H. Collective dynamics of ‘small-world’networks. Nature 1998, 393, 440–442. [Google Scholar] [CrossRef]
- Albert, R.; Jeong, H.; Barabási, A.L. Error and attack tolerance of complex networks. Nature 2000, 406, 378–382. [Google Scholar] [CrossRef] [PubMed]
- Herrmann, H.J.; Schneider, C.M.; Moreira, A.A.; Andrade, J.S.; Havlin, S. Onion-like network topology enhances robustness against malicious attacks. J. Stat. Mech. Theory Exp. 2011, 2011, P01027. [Google Scholar] [CrossRef]
- Schneider, C.M.; Moreira, A.A.; Andrade, J.S.; Havlin, S.; Herrmann, H.J. Mitigation of malicious attacks on networks. Proc. Natl. Acad. Sci. USA 2011, 108, 3838–3841. [Google Scholar] [CrossRef] [PubMed]
- Zhou, M.; Liu, J. A two-phase multiobjective evolutionary algorithm for enhancing the robustness of scale-free networks against multiple malicious attacks. IEEE Trans. Cybern. 2016, 4, 539–552. [Google Scholar] [CrossRef] [PubMed]
- Zhou, M.; Liu, J. A memetic algorithm for enhancing the robustness of scale-free networks against malicious attacks. Phys. A Stat. Mech. Its Appl. 2014, 410, 131–143. [Google Scholar] [CrossRef]
- Qiu, T.; Liu, J.; Si, W.; Wu, D.O. Robustness optimization scheme with multi-population co-evolution for scale-free wireless sensor networks. IEEE/ACM Trans. Netw. 2019, 2, 1028–1042. [Google Scholar] [CrossRef]
- Qiu, T.; Luo, D.; Xia, F.; Deonauth, N.; Si, W.; Tolba, A. A greedy model with small world for improving the robustness of heterogeneous internet of things. Comput. Netw. 2016, 101, 127–143. [Google Scholar] [CrossRef]
- Qureshi, T.N.; Javaid, N.; Almogren, A.; Abubaker, Z.; Almajed, H.; Mohiuddin, I. Attack resistance based topology robustness of scale-free internet of things for smart cities. Int. J. Web Grid Serv. 2021, 17, 343–370. [Google Scholar] [CrossRef]
- Peng, G.S.; Wu, J. Optimal network topology for structural robustness based on natural connectivity. Phys. A Stat. Mech. Its Appl. 2016, 443, 212–220. [Google Scholar] [CrossRef]
- Strumberger, I.; Beko, M.; Tuba, M.; Minovic, M.; Bacanin, N. Elephant herding optimization algorithm for wireless sensor network localization problem. In Proceedings of the Doctoral Conference on Computing, Electrical and Industrial Systems, Costa de Caparica, Portugal, 8–10 May 2018; Springer: Cham, Switzerland, 2018; pp. 175–184. [Google Scholar]
- Buesser, P.; Daolio, F.; Tomassini, M. Optimizing the robustness of scale-free networks with simulated annealing. In Proceedings of the International Conference on Adaptive and Natural Computing Algorithms, Ljubljana, Slovenia, 14–16 April 2011; Springer: Berlin/Heidelberg, Germany, 2011; pp. 167–176. [Google Scholar]
- Qiu, T.; Zhao, A.; Xia, F.; Si, W.; Wu, D.O. Rose: Robustness strategy for scale-free wireless sensor networks. IEEE/ACM Trans. Netw. 2017, 25, 2944–2959. [Google Scholar] [CrossRef]
- Abbas, S.M.; Javaid, N.; Usman, M.; Baig, S.M.; Malik, A.; Rehman, A.U. An efficient approach to enhance the robustness of scale-free networks. In Proceedings of the International Conference on Innovative Mobile and Internet Services in Ubiquitous Computing, Asan, Korea, 1–3 July 2021; Springer: Cham, Switzerland, 2021; pp. 76–86. [Google Scholar]
- Xiao, S.; Xiao, G.; Cheng, T.H.; Ma, S.; Fu, X.; Soh, H. Robustness of scale-free networks under rewiring operations. EPL Europhys. Lett. 2010, 89, 380021–380026. [Google Scholar] [CrossRef][Green Version]
- Khan, M.A.; Javaid, N. Computationally efficient topology optimization of scale-free IoT networks. Comput. Commun. 2021, 185, 1–12. [Google Scholar] [CrossRef]
- Hu, S.; Li, G. Tmse: A topology modification strategy to enhance the robustness of scale-free wireless sensor networks. Comput. Commun. 2020, 157, 53–63. [Google Scholar] [CrossRef]
- Qureshi, T.N.; Javaid, N.; Almogren, A.; Khan, A.U.; Almajed, H.; Mohiuddin, I. An adaptive enhanced differential evolution strategies for topology robustness in internet of things. Int. J. Web Grid Serv. 2021, 18, 343–370. [Google Scholar] [CrossRef]
- Sabidussi, G. The centrality index of a graph. Psychometrika 1966, 31, 581–603. [Google Scholar] [CrossRef]
- Qiu, T.; Lu, Z.; Li, K.; Xue, G.; Wu, D.O. An adaptive robustness evolution algorithm with self-competition for scale-free internet of things. In Proceedings of the IEEE INFOCOM 2020-IEEE Conference on Computer Communications, Toronto, ON, Canada, 6–9 July 2020; pp. 2106–2115. [Google Scholar]
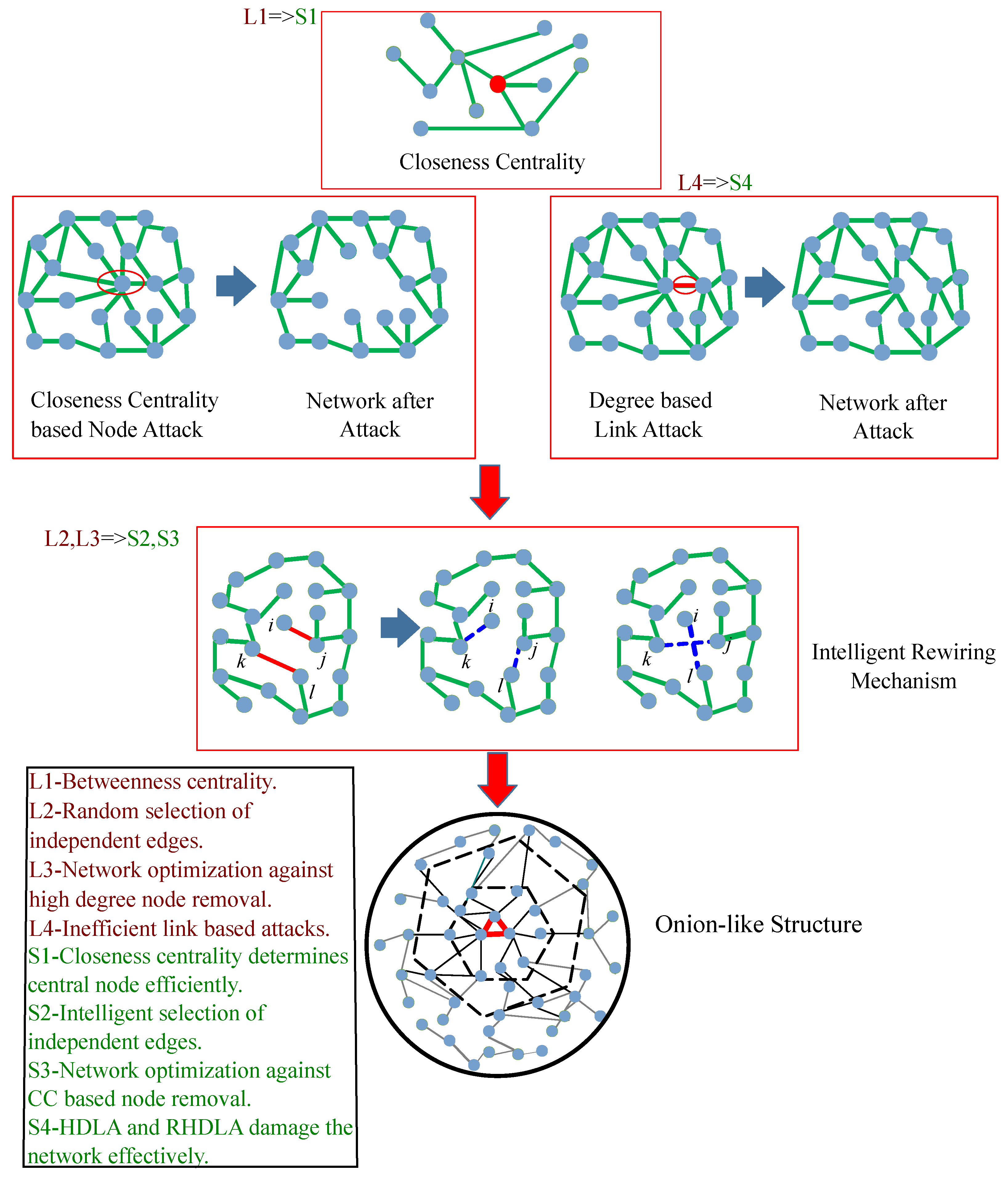
| Limitations | Solutions | Validations |
|---|---|---|
| L1: The BC measure determines the central node in the network inefficiently [17]. | S1: The CC measure determines the network’s central node in less computational time. | V1: The computational time of different centrality measures is evaluated in Figure 3. |
| L2: No specific criteria for selection of independent edges [24]. | S2: INTR is proposed to select the independent edges between high and low degree nodes for optimizing the network R. | V2: The R value evaluates the overall performance of network in Figure 8. |
| L3: Network is optimized only against high degree node removal [21,25,32]. | S3: Network is optimized against high CC based node removal. | V3: The network performance is evaluated with R values in Figures 5, 7 and 8. |
| L4: The network connectivity is affected by link attacks using high computational resources [17]. | S4: Two attacks HDLA and RHDLA are introduced that damage the network effectively. | V4: The network connectivity is validated by performing different centrality based link attacks in Figure 4. |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2022 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Abbas, S.M.; Javaid, N.; Azar, A.T.; Qasim, U.; Khan, Z.A.; Aslam, S. Towards Enhancing the Robustness of Scale-Free IoT Networks by an Intelligent Rewiring Mechanism. Sensors 2022, 22, 2658. https://doi.org/10.3390/s22072658
Abbas SM, Javaid N, Azar AT, Qasim U, Khan ZA, Aslam S. Towards Enhancing the Robustness of Scale-Free IoT Networks by an Intelligent Rewiring Mechanism. Sensors. 2022; 22(7):2658. https://doi.org/10.3390/s22072658
Chicago/Turabian StyleAbbas, Syed Minhal, Nadeem Javaid, Ahmad Taher Azar, Umar Qasim, Zahoor Ali Khan, and Sheraz Aslam. 2022. "Towards Enhancing the Robustness of Scale-Free IoT Networks by an Intelligent Rewiring Mechanism" Sensors 22, no. 7: 2658. https://doi.org/10.3390/s22072658
APA StyleAbbas, S. M., Javaid, N., Azar, A. T., Qasim, U., Khan, Z. A., & Aslam, S. (2022). Towards Enhancing the Robustness of Scale-Free IoT Networks by an Intelligent Rewiring Mechanism. Sensors, 22(7), 2658. https://doi.org/10.3390/s22072658








