Blockchain-Based Distributed Information Hiding Framework for Data Privacy Preserving in Medical Supply Chain Systems
Abstract
:1. Introduction
- We deploy an improved version of steganography techniques to encrypt the desired communicated messages and information into another auxiliary message to enhance the privacy and security of the communicated medical supply chain information against any possible cyber-attack.
- We deploy Blockchain technology to create a secure and private cluster of pre-authenticated healthcare providers. Only nodes included in the cluster may participate in the communication, view the received messages, and decrypt the desired block while ignoring the auxiliary blocks.
- Finally, the smart contract is implemented in our proposed framework to automatically generate one-time secret keys and distribute them between the concerned parties securely. The secret key changes with every new communication initialization, eliminating the risk of cyber-attacker having the key to decrypt the information, thus enhancing the security and privacy of critical systems, such as smart healthcare.
2. Related Works
2.1. Background
2.1.1. Blockchain
2.1.2. Critical IoT Systems
2.1.3. Information Hiding Techniques
2.2. Existed Solutions for IoT and Medical Supply Chain Security
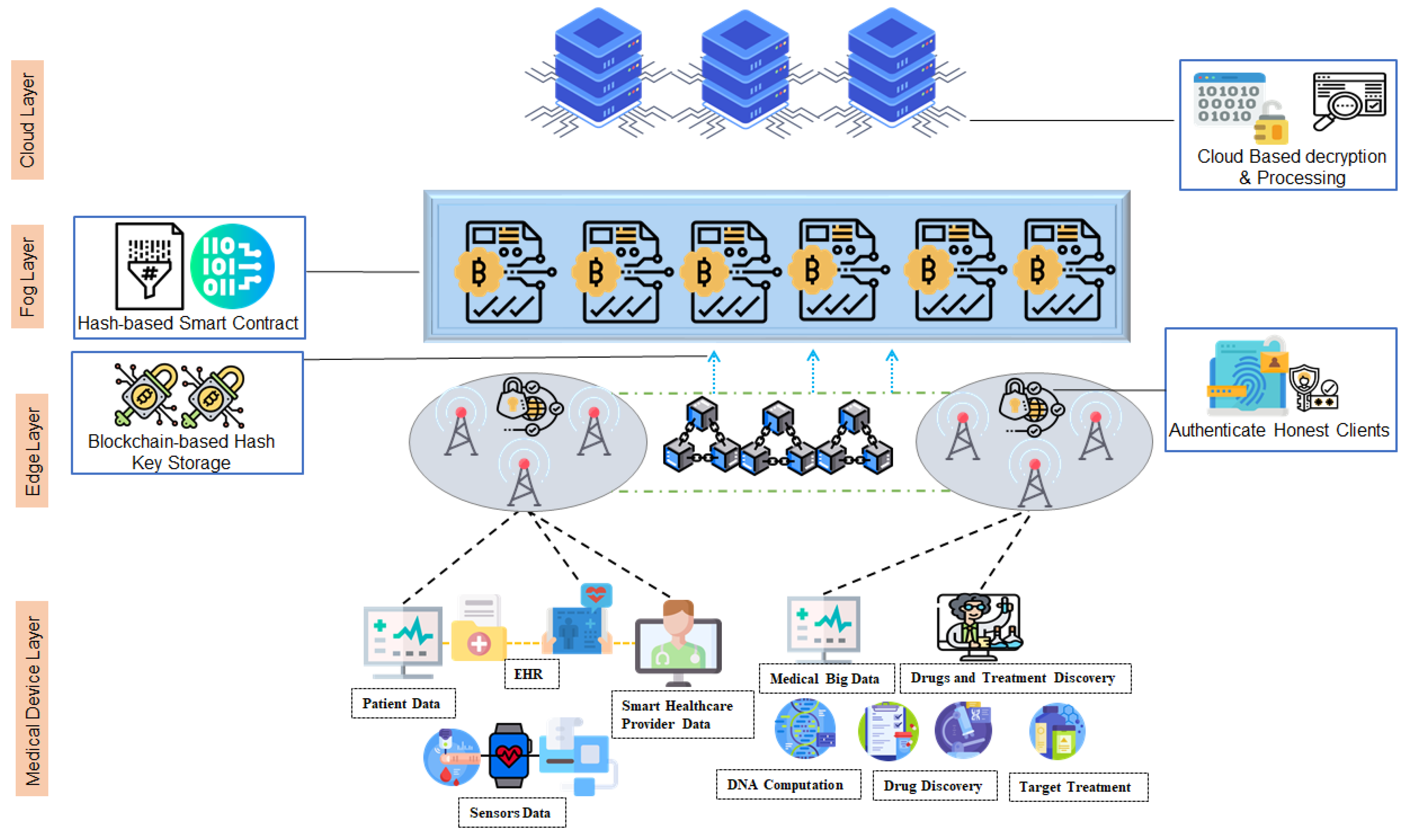
3. Proposed Blockchain-Based IHT for Critical IoT Security Framework
3.1. Proposed System Overview
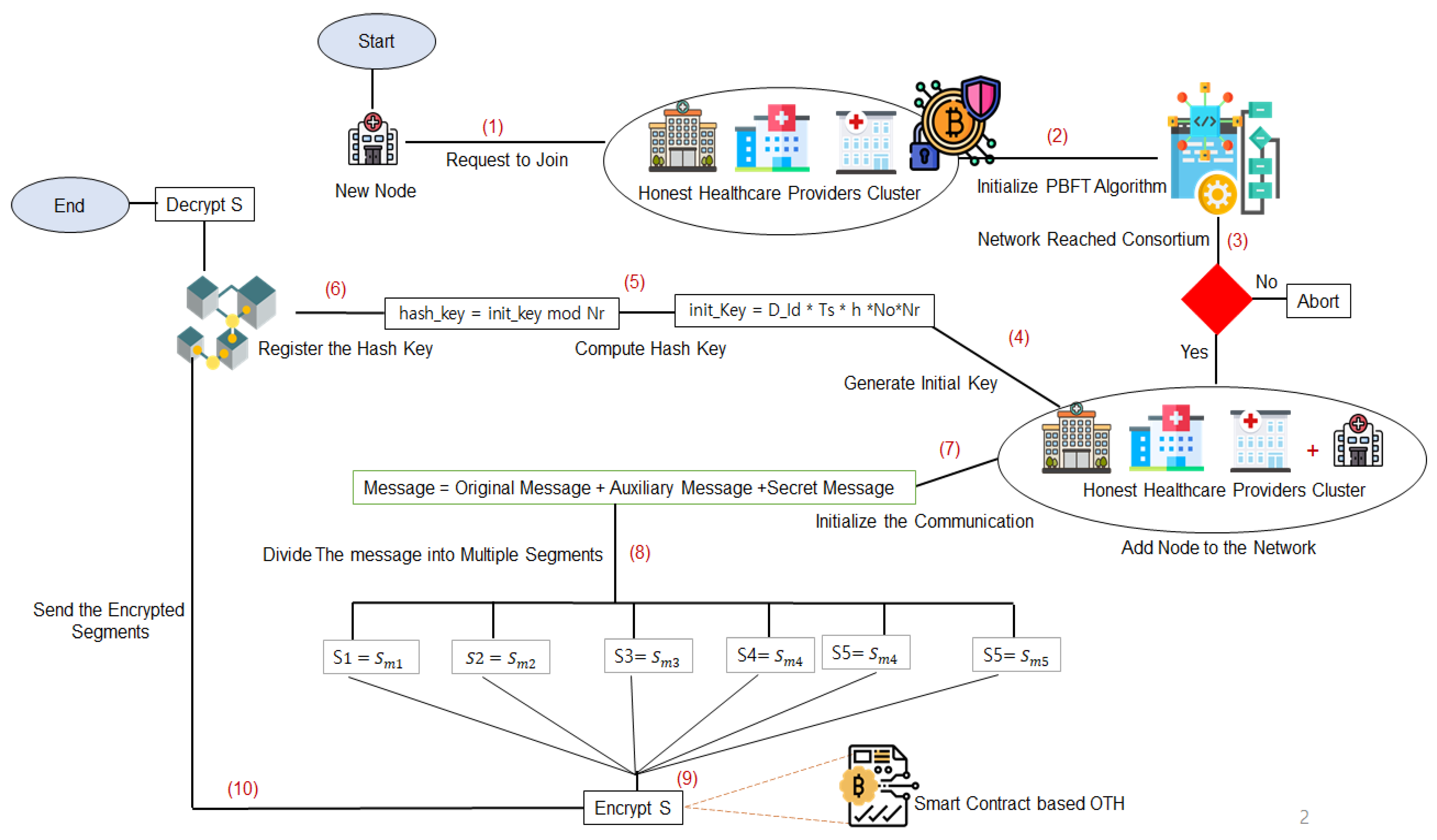
3.2. Methodology of the Proposed System
3.2.1. Cluster Pre-Selection Phase
| Algorithm 1. Cluster pre-selection (message Broadcast). |
| 1: Input: Healthcare provider identification and request |
| 2: Output: Final consensus decision (Authenticated or rejected) |
| 3: Process: |
| 4: .Send(<, Request, Ts>, VC); |
| 5: VC. Check (<, Hi, Request, Ts>, ); |
| 6: .Prepare(<w, Hi, Di>, Request); |
| 7: .Communicate (<w, Hi, Di>, ); |
| 8: for i = 1 to n |
| { |
| 9: .Get(<w, Hi, Di>); |
| 10: .Check(<w, Hi, Di>, f, n); |
| 11: .Prepare(<w, Hi, Di>); |
| 12: . Communicate (<w, Hi, Di>, ); |
| 13: .count(<f: fault>, count C); |
| } |
| Algorithm 2. Cluster pre-selection (message count and execute). |
| 1: while count: C > (f + 1) then |
| 2: .Stamp(<w, in: Di, out: Di, Ts, Stamp: k>); |
| 3: .Commit(<w, Hi, Di, Ts>, Result: k, ); |
| 4: Get(<w, Hi, Di, Ts>, Request: x, count C); |
| 5: while count: C>(2f+1) then |
| 6: Compute(<w, Hi, Di>, Request: x, = 0.Mark = x); |
| 7: for k = 1 to n |
| 8: . Check(VC .Stamp = x); |
| 9: if . Stamp == .Mark then |
| 10: addToBlockhain (BC, , 0, ); |
| 11: else |
| 12: skip ; |
| End |
3.2.2. Hash Key Registration Phase
| Algorithm 3: Hash key registration. |
| 1: Input: IoT devices, Cloud server |
| 2: Output: Secure shared hash key |
| 3: Process: |
| 4: Start: //Initialization |
| 5: M_IoT. Send (<D_Id, Ts, Msg, h, No>, CS); // with D_Id is the IoT device identification, |
| 6: Ts is the timestamp, No is the nonce, h is the height of the message |
| 7: CS is the cloud server |
| 8: CS. Receive(<D_Id, Ts, Msg, h, No>); |
| 9: CS. Check (<D_Id, Ts, Msg, h, No>); |
| 10: if Device. Existe == true |
| { |
| 11: CS. Generate (<init_Key <= (D_Id * Ts * h *No*Nr)) //with is the number of communication round |
| 12: CS. Send (<init_Key>, M_IoT) |
| 13: M_IoT.Compute (<hash_key>, init_key mod Nr) |
| 14: CS.Generate(<New Block>) |
| 15: if CS.hash_key == M_IoT.hash_key |
| { |
| 16: CS.Add (hash_key, M_IoT>, New Block) |
| 17: else |
| 18: CS. Abort (Communication); |
| } |
| } |
| 19: end; |
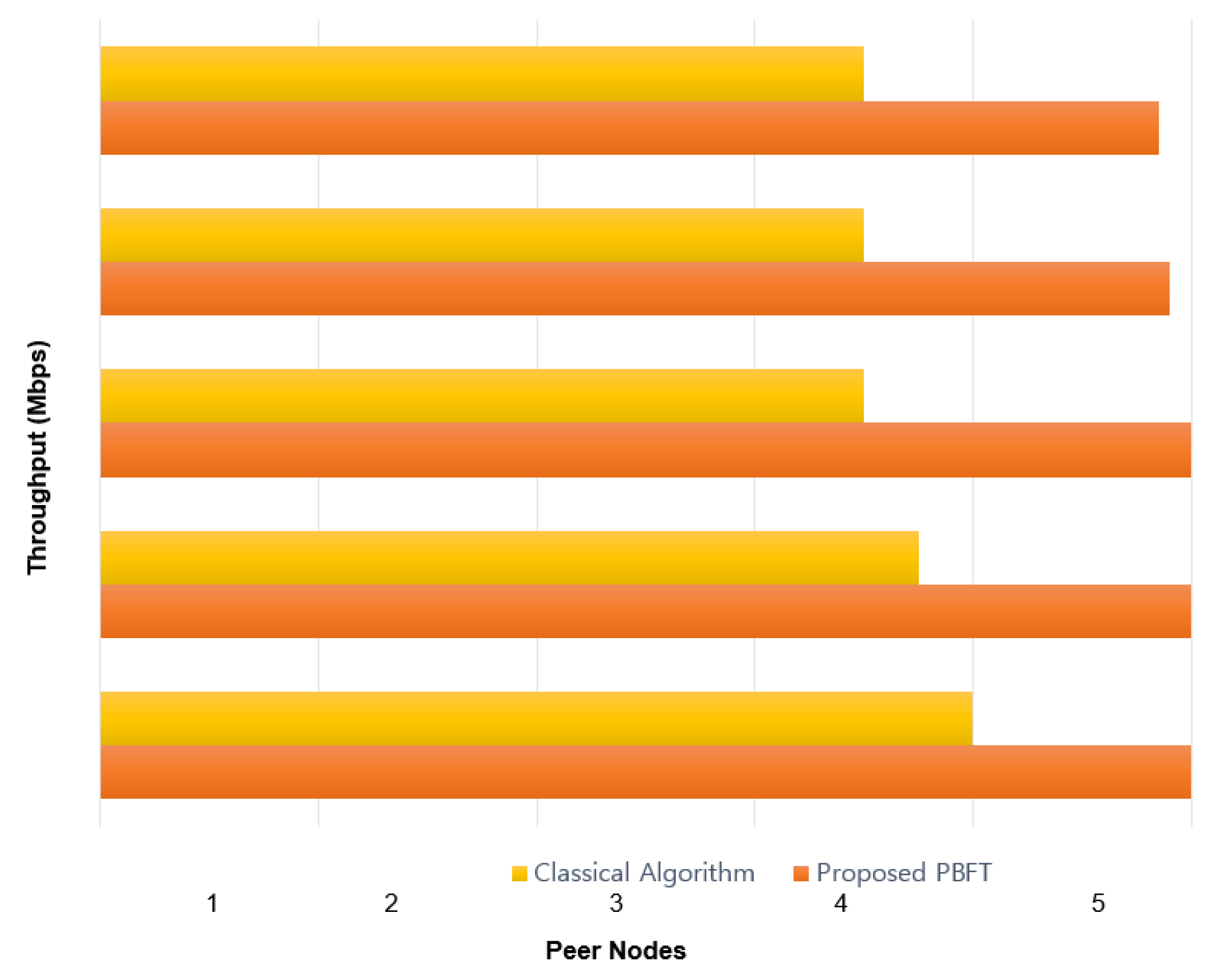
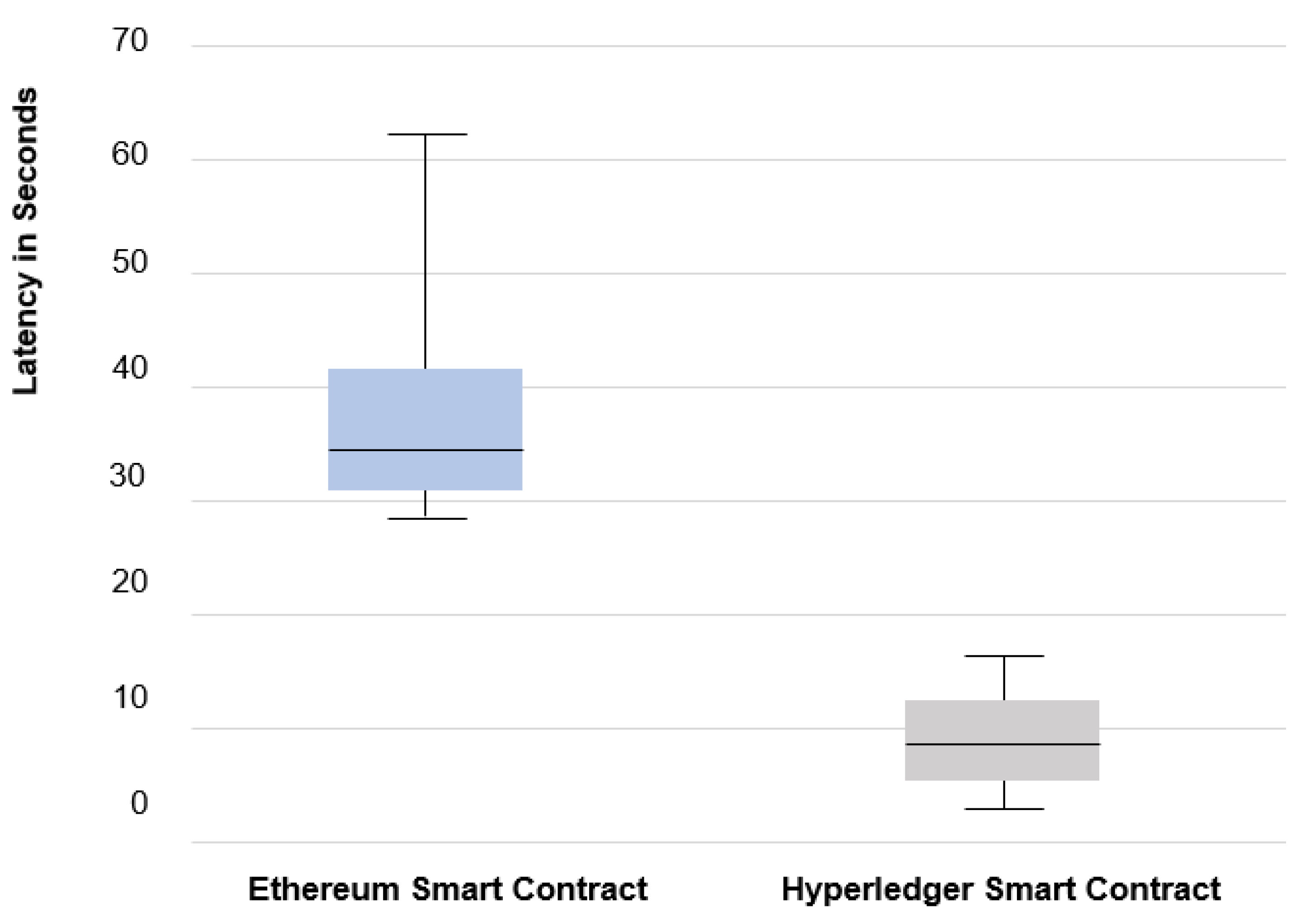
4. Analysis and Discussion
4.1. Analysis
4.2. Discussion and Open Research Challenges
5. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
References
- HealthIT Gov. Official Website of the Office of the National Coordinator for Health Information Technology (ONC). Available online: https://www.healthit.gov/topic/health-it-and-health-information-exchange-basics/getting-started-hie (accessed on 12 November 2021).
- Mariani, D.M.R.; Mohammed, S.; Mohammed, S. Cybersecurity challenges and compliance issues within the us healthcare sector. Int. J. Bus. Soc. Res. 2015, 5, 55–56. [Google Scholar]
- Chen, W.; Chen, Z.; Cui, F. Collaborative and secure transmission of medical data applied to mobile healthcare. Biomed. Eng. Online 2019, 18, 60. [Google Scholar] [CrossRef] [PubMed] [Green Version]
- Ogundokun, R.O.; Abikoye, O.C. A Safe and Secured Medical Textual Information Using an Improved LSB Image Steganography. Int. J. Digit. Multimed. Broadcast. 2021, 2021, 1–8. [Google Scholar] [CrossRef]
- Yang, C.-H. Inverted pattern approach to improve image quality of information hiding by LSB substitution. Pattern Recognit. 2008, 41, 2674–2683. [Google Scholar] [CrossRef]
- Monrat, A.A.; Schelen, O.; Andersson, K. A Survey of Blockchain From the Perspectives of Applications, Challenges, and Opportunities. IEEE Access 2019, 7, 117134–117151. [Google Scholar] [CrossRef]
- Lu, Y. The blockchain: State-of-the-art and research challenges. J. Ind. Inf. Integr. 2019, 15, 80–90. [Google Scholar] [CrossRef]
- Almaiah, M.A. A New Scheme for Detecting Malicious Attacks in Wireless Sensor Networks Based on Blockchain Technology. In Studies in Big Data; Springer Science and Business Media LLC.: Berlin, Germany, 2021; pp. 217–234. [Google Scholar]
- Dai, H.-N.; Zheng, Z.; Zhang, Y. Blockchain for Internet of Things: A Survey. IEEE Internet Things J. 2019, 6, 8076–8094. [Google Scholar] [CrossRef] [Green Version]
- Li, X.; Jiang, P.; Chen, T.; Luo, X.; Wen, Q. A survey on the security of blockchain systems. Future Gener. Comput. Syst. 2020, 107, 841–853. [Google Scholar] [CrossRef] [Green Version]
- Thampi, S.M. Information hiding techniques: A tutorial review. arXiv 2008, arXiv:0802.3746. [Google Scholar]
- Ahvanooey, M.T.; Li, Q.; Shim, H.J.; Huang, Y. A Comparative Analysis of Information Hiding Techniques for Copyright Protection of Text Documents. Secur. Commun. Netw. 2018, 2018, 1–22. [Google Scholar] [CrossRef]
- Eze, P.; Parampalli, U.; Evans, R.; Liu, D. A New Evaluation Method for Medical Image Information Hiding Techniques. In Proceedings of the 2020 42nd Annual International Conference of the IEEE Engineering in Medicine & Biology Society (EMBC), Montréal, QC, Canada, 20–24 July 2020; Institute of Electrical and Electronics Engineers (IEEE): Piscataway, NJ, USA, 2020; pp. 6119–6122. [Google Scholar]
- Sengupta, J.; Ruj, S.; Das Bit, S. A Comprehensive Survey on Attacks, Security Issues and Blockchain Solutions for IoT and IIoT. J. Netw. Comput. Appl. 2020, 149, 102481. [Google Scholar] [CrossRef]
- Wen, Q.; Gao, Y.; Chen, Z.; Wu, D. A Blockchain-based Data Sharing Scheme in The Supply Chain by IIoT. In Proceedings of the 2019 IEEE International Conference on Industrial Cyber Physical Systems (ICPS), Taipei, Taiwan, 6–9 May 2019; IEEE: Piscataway, NJ, USA, 2019; pp. 695–700. [Google Scholar]
- Iqbal, A.; Amir, M.; Kumar, V.; Alam, A.; Umair, M. Integration of next generation IIoT with Blockchain for the development of smart industries. Emerg. Sci. J. 2020, 4, 1–17. [Google Scholar] [CrossRef]
- Zhao, S.; Li, S.; Yao, Y. Blockchain Enabled Industrial Internet of Things Technology. IEEE Trans. Comput. Soc. Syst. 2019, 6, 1442–1453. [Google Scholar] [CrossRef]
- Yu, K.-P.; Tan, L.; Aloqaily, M.; Yang, H.; Jararweh, Y. Blockchain-Enhanced Data Sharing With Traceable and Direct Revocation in IIoT. IEEE Trans. Ind. Inform. 2021, 17, 7669–7678. [Google Scholar] [CrossRef]
- Wu, Y.; Dai, H.-N.; Wang, H. Convergence of Blockchain and Edge Computing for Secure and Scalable IIoT Critical Infrastructures in Industry 4.0. IEEE Internet Things J. 2021, 8, 2300–2317. [Google Scholar] [CrossRef]
- Liu, M.; Yu, F.R.; Teng, Y.; Leung, V.C.M.; Song, M. Performance Optimization for Blockchain-Enabled Industrial Internet of Things (IIoT) Systems: A Deep Reinforcement Learning Approach. IEEE Trans. Ind. Informa. 2019, 15, 3559–3570. [Google Scholar] [CrossRef]
- Guan, Z.; Lu, X. Towards secure and efficient energy trading in IIoT-enabled energy internet: A blockchain approach. Future Gener. Comput. Syst. 2020, 110, 686–695. [Google Scholar] [CrossRef]
- Panchal, A.C.; Khadse, V.M.; Mahalle, P.N. Security Issues in IIoT: A Comprehensive Survey of Attacks on IIoT and Its Countermeasures. In Proceedings of the 2018 IEEE Global Conference on Wireless Computing and Networking (GCWCN), Lonavala, India, 23–24 November 2018; IEEE: Piscataway, NJ, USA, 2018; pp. 124–130. [Google Scholar]
- Mabkhot, M.M.; Al-Ahmari, A.M.; Salah, B.; Alkhalefah, H. Requirements of the Smart Factory System: A Survey and Perspective. Machines 2018, 6, 23. [Google Scholar] [CrossRef] [Green Version]
- Ghadge, A.; Weiß, M.; Caldwell, N.; Wilding, R. Managing cyber risk in supply chains: A review and research agenda. Supply Chain Manag. Int. J. 2019, 25, 223–240. [Google Scholar] [CrossRef]
- Helo, P.; Hao, Y. Blockchains in operations and supply chains: A model and reference implementation. Comput. Ind. Eng. 2019, 136, 242–251. [Google Scholar] [CrossRef]
- Bhaskar, S.; Tan, J.; Bogers, M.L.A.M.; Minssen, T.; Badaruddin, H.; Israeli-Korn, S.; Chesbrough, H. At the Epicenter of COVID-19–the Tragic Failure of the Global Supply Chain for Medical Supplies. Front. Public Health 2020, 8, 562882. [Google Scholar] [CrossRef] [PubMed]
- Musamih, A.; Salah, K.; Jayaraman, R.; Arshad, J.; Debe, M.; Al-Hammadi, Y.; Ellahham, S. A Blockchain-Based Approach for Drug Traceability in Healthcare Supply Chain. IEEE Access 2021, 9, 9728–9743. [Google Scholar] [CrossRef]
- Carmody, S.; Coravos, A.; Fahs, G.; Hatch, A.; Medina, J.; Woods, B.; Corman, J. Building resilient medical technology supply chains with a software bill of materials. NPJ Digit. Med. 2021, 4, 1–6. [Google Scholar] [CrossRef]
- García-Villarreal, E.; Bhamra, R.; Schoenheit, M. Critical success factors of medical technology supply chains. Prod. Plan. Control 2019, 30, 716–735. [Google Scholar] [CrossRef] [Green Version]
- Pandey, S.; Singh, R.; Gunasekaran, A.; Kaushik, A. Cyber security risks in globalized supply chains: Conceptual framework. J. Glob. Oper. Strateg. Sourc. 2020, 13, 103–128. [Google Scholar] [CrossRef]
- Nour, B.; Ksentini, A.; Herbaut, N.; Frangoudis, P.A.; Moungla, H. A Blockchain-Based Network Slice Broker for 5G Services. IEEE Netw. Lett. 2019, 1, 99–102. [Google Scholar] [CrossRef] [Green Version]
- Salim, M.M.; Shanmuganathan, V.; Loia, V.; Park, J.H. Deep Learning Enabled Secure IoT Handover Authentication for BlockchainNetworks. Hum. Cent. Comput. Inf. Sci. 2021, 11, 21. [Google Scholar]
- Kim, M.; Kim, K.; Kim, J.H. Cost Modeling for Analyzing Network Performance of IoT Protocols in Blockchain-Based IoT. Hum. Cent. Comput. Inf. Sci. 2021, 11, 7. [Google Scholar]
- Kim, Y.; Park, J. Hybrid decentralized PBFT Blockchain Framework for OpenStack message queue. Hum. Cent. Comput. Inf. Sci. 2020, 10, 1–12. [Google Scholar] [CrossRef]
- Kim, H.-W.; Jeong, Y.-S. Secure Authentication-Management human-centric Scheme for trusting personal resource information on mobile cloud computing with blockchain. Hum. Cent. Comput. Inf. Sci. 2018, 8, 11. [Google Scholar] [CrossRef] [Green Version]
- Wang, Y.; Kim, D.K.; Jeong, D. A Survey of the Application of Blockchain in Multiple Fields of Financial Services. J. Inf. Processing Syst. 2020, 16, 935–958. [Google Scholar] [CrossRef]
- Yu, S.; Yeom, C.; Won, Y. Implementation of Search Engine to Minimize Traffic Using Blockchain-Based Web Usage History Management System. J. Inf. Process Syst. 2021, 17, 989–1003. [Google Scholar] [CrossRef]
- Niu, B.; Chen, Y.; Wang, Z.; Li, F.; Wang, B.; Li, H. Eclipse: Preserving Differential Location Privacy Against Long-Term Observation Attacks. IEEE Trans. Mob. Comput. 2020, 21, 125–138. [Google Scholar] [CrossRef]
- Jin, H.; Su, L.; Xiao, H.; Nahrstedt, K. Incentive Mechanism for Privacy-Aware Data Aggregation in Mobile Crowd Sensing Systems. IEEE/ACM Trans. Netw. 2018, 26, 2019–2032. [Google Scholar] [CrossRef]
- Jia, M.; He, K.; Chen, J.; Du, R.; Chen, W.; Tian, Z.; Ji, S. PROCESS: Privacy-Preserving On-Chain Certificate Status Service. In Proceedings of the IEEE INFOCOM 2021-IEEE Conference on Computer Communications, Vancouver, BC, Canada, 10–13 May 2021; pp. 1–10. [Google Scholar]
| Research Work | Year | Technologies | Key Contribution | Limitation |
|---|---|---|---|---|
| Sengupta et al. [14] | 2020 | Blockchain Smart Contract Classification | Summarize security issues of blockchain-based IoT and IIoT | No case study was proposed |
| Wen et al. [15] | 2019 | BSCS ABE | Solve supply chain resource interaction security issues | Lack of comparative results |
| Iqbal et al. [16] | 2020 | Blockchain DEMATEL | A detailed study to evaluate IIoT performance and reduce the cost of infrastructure deployment | Propose only a study of existing solutions |
| Zhao et al. [17] | 2019 | Blockchain Smart Contract Identification technology | A comprehensive survey on Blockchain scalability and data capacity of IIoT | Propose only a study of existing solutions |
| Yu et al. [18] | 2021 | Blockchain | Enhanced secure storage and sharing of smart factory data in the cloud | The time cost of the encryption phase is slightly higher than other works |
| Wu et al. [19] | 2020 | Blockchain Edge Computing | Solve the scalability and data security problems of the Industrial Internet of Things | Lack of comparative results |
| Liu et al. [20] | 2019 | Blockchain DRL | Optimize IIoT scalability/throughput. | Lack of comparative results |
| Guan et al. [21] | 2020 | BC-ETS | Balance power supply and demand while protecting the privacy | System communication overhead is slightly higher than related work |
| Panchal et al. [22] | 2018 | IoT, IIoT, Security, CPS | A comprehensive survey on the security threats on IIoT and various attacks on the layered IIoT architectures | Propose only a study of recent states-of-art |
| Mabkhot et al. [23] | 2018 | Big Data, Cloud, Manufacturing, IoT, CPS, Smart Factory | Analyze and identify perspectives of the smart factory. | Propose only a study of recent states-of-art |
| Ghadge et al. [24] | 2019 | Data mining | Defines the traditional supply chain risk and summarizes how the organization manages the network risk in the supply chain. | No case study was proposed |
| Helo et al. [25] | 2019 | Blockchain, BLMS | Study of a blockchain-based logistics monitoring system (BLMS). | Lack of comparative results |
| Bhaskar et al. [26] | 2021 | Blockchain | Discuss the core development and innovation needs of the medical supply chain | Lack of simulation results |
| Musamih et al. [27] | 2020 | Blockchain | Developed and evaluated a solution for decentralized tracking of drugs in a blockchain-based platform pharmaceutical supply chain | Latency and throughput of the proposed solution are not considered in the simulation |
| Carmody et al. [28] | 2021 | Software Bill of Materials | Addresses vulnerabilities exploited in individual software components of healthcare technology | Lack of security analysis |
| Garcia-Villarreal et al. [29] | 2019 | Big data | Discuss outstanding factors of supply chain management success that have not been fully recognized by previous studies | No case study was proposed |
| Pandey et al. [30] | 2020 | Big data, deep learning | A comprehensive study on network security risk of global supply chain | No solution was proposed |
| Our Work | 2021 | Blockchain, One-time hash-based smart contract | Privacy-preserving in the medical supply chain using Blockchain and smart contract | Only tested on medical supply chain-based scenario |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2022 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
EL Azzaoui, A.; Chen, H.; Kim, S.H.; Pan, Y.; Park, J.H. Blockchain-Based Distributed Information Hiding Framework for Data Privacy Preserving in Medical Supply Chain Systems. Sensors 2022, 22, 1371. https://doi.org/10.3390/s22041371
EL Azzaoui A, Chen H, Kim SH, Pan Y, Park JH. Blockchain-Based Distributed Information Hiding Framework for Data Privacy Preserving in Medical Supply Chain Systems. Sensors. 2022; 22(4):1371. https://doi.org/10.3390/s22041371
Chicago/Turabian StyleEL Azzaoui, Abir, Haotian Chen, So Hyeon Kim, Yi Pan, and Jong Hyuk Park. 2022. "Blockchain-Based Distributed Information Hiding Framework for Data Privacy Preserving in Medical Supply Chain Systems" Sensors 22, no. 4: 1371. https://doi.org/10.3390/s22041371
APA StyleEL Azzaoui, A., Chen, H., Kim, S. H., Pan, Y., & Park, J. H. (2022). Blockchain-Based Distributed Information Hiding Framework for Data Privacy Preserving in Medical Supply Chain Systems. Sensors, 22(4), 1371. https://doi.org/10.3390/s22041371





_Park.png)

