Mist and Edge Computing Cyber-Physical Human-Centered Systems for Industry 5.0: A Cost-Effective IoT Thermal Imaging Safety System
Abstract
1. Introduction
- The essential concepts for the development of CPHS systems are detailed.
- Some of the most relevant works on CPHSs have been analyzed. Their main design requirements and key implementation components have been identified.
- The major challenges for the development of Industry 5.0 CPHSs are outlined.
- An Industry 5.0 CPHS use case designed to increase industrial operator safety in human-machine collaborative environments is described in detail and its performance is evaluated. The use case makes use of a hybrid edge computing architecture and low-cost thermal imaging sensors to provide an adequate trade-off between cost, accuracy, resiliency and computational efficiency. To the best of our knowledge, no similar CPHS has been previously described in the literature.
- Key findings, challenges and relevant guidelines are outlined in order to help future Industry 5.0 researchers and engineers.
2. Related Works
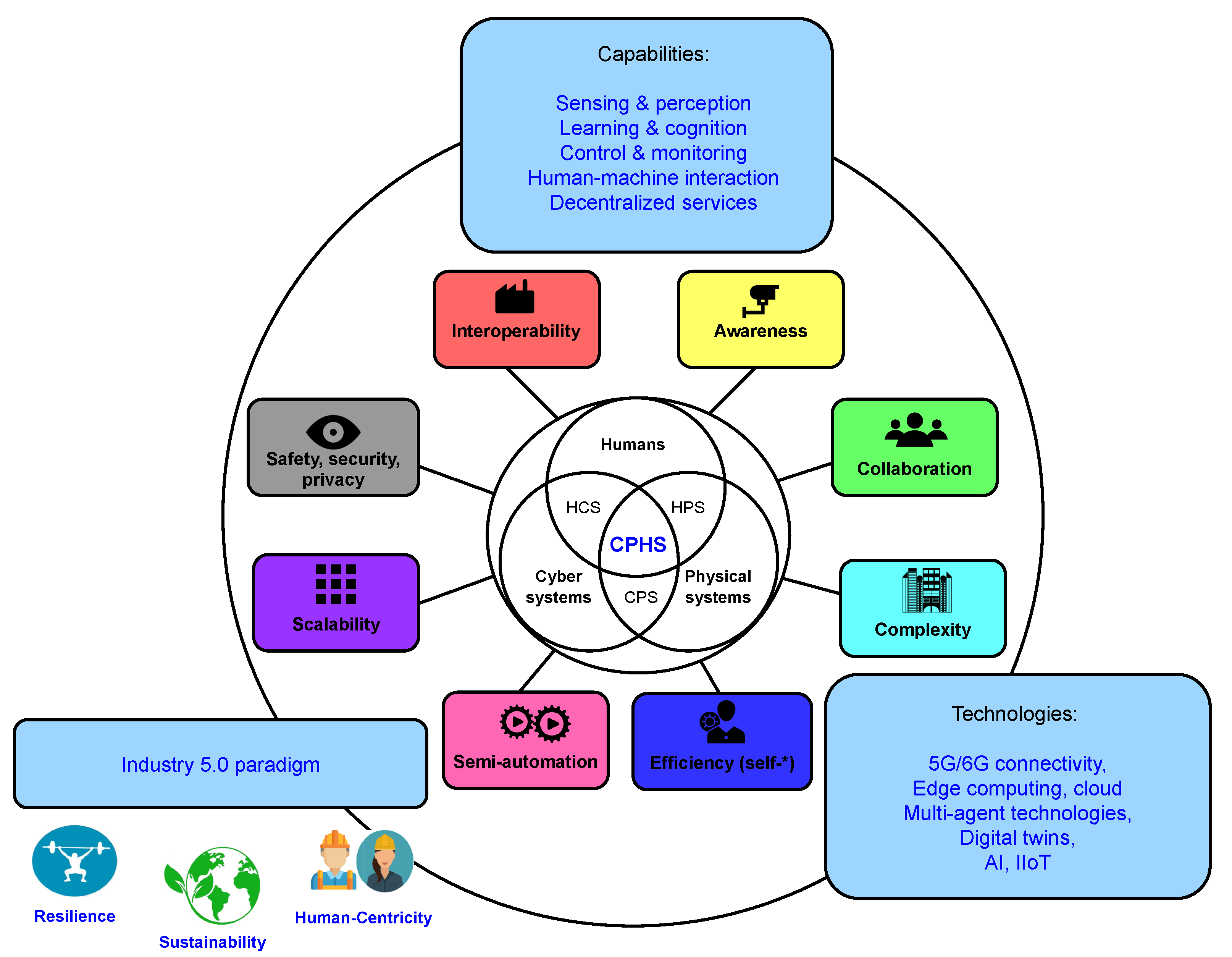
2.1. Towards Industry 5.0 Cyber-Physical Systems
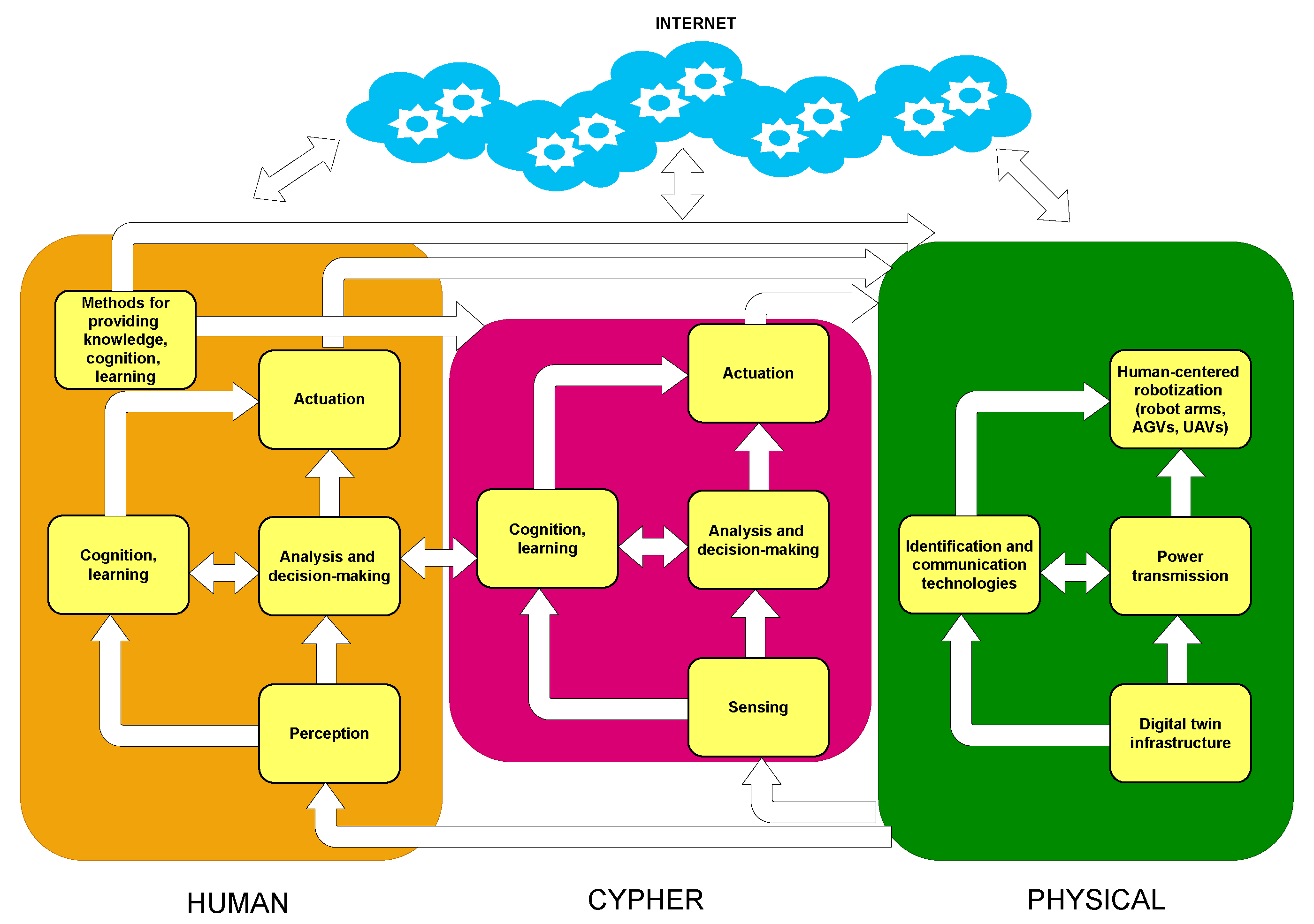
2.2. Cyber-Physical Human Systems
- Knowledge: Human performance and behavior is affected by factors like available information and training, but also by different factors like stress, mood, fatigue, or motivation.
- Perception: The process of data collection can be performed by hardware sensors and/or humans (i.e., social sensors).
- Cognition: Regarding situational or context awareness, people observe and process information differently than computers.
- Learning: Humans do not perform the same task in exactly the same way every time, therefore, there are different levels of predictability. In addition, humans have high adaptability, so they can easily adapt to changing environments.
- Actuation: Remote monitoring and control to provide safer and human-friendly human–machine interactions.
2.3. New Communications Architectures for CPHSs and CPSs
2.4. Human Detection and Safety in Industrial Scenarios
2.5. Analysis of the State of the Art
2.6. Contributions and Novelty of the Proposed System
- Human-centricity: The whole system has been specifically designed for preserving industrial operator safety in human–machine collaborative scenarios. Thus, specific human-detection algorithms have been developed to determine when dangerous situations may happen in industrial environments in order to control certain IIoT devices (e.g., cobots in operation).
- Sustainability: The devised system was conceived to be implemented by using low-cost and low-power devices. In addition, the proposed solution is based on a hybrid edge/mist communications architecture that seeks to minimize data exchanges with the remote cloud servers, thus decreasing their energy consumption and the power dedicated to communications. Furthermore, since the developed human-detection algorithms do not make use of machine learning or other Artificial Intelligence techniques, the usually energy-consuming training stage and the required hardware (e.g., computers with power-hungry GPUs) are not necessary.
- Resilience: The previously mentioned edge/mist computing architecture provides IIoT node redundancy, and it allows for distributing the computational load, thus decreasing the potential saturation of the cloud. In addition, the architecture avoids unnecessary data exchanges with the cloud, so it prevents attacks on the system communications (e.g., man-in-the-middle attacks). Furthermore, since the proposed solution uses thermal imaging sensors instead of regular webcams, it deals with potential privacy issues, which have been a traditional cybersecurity concern for many industrial surveillance systems.
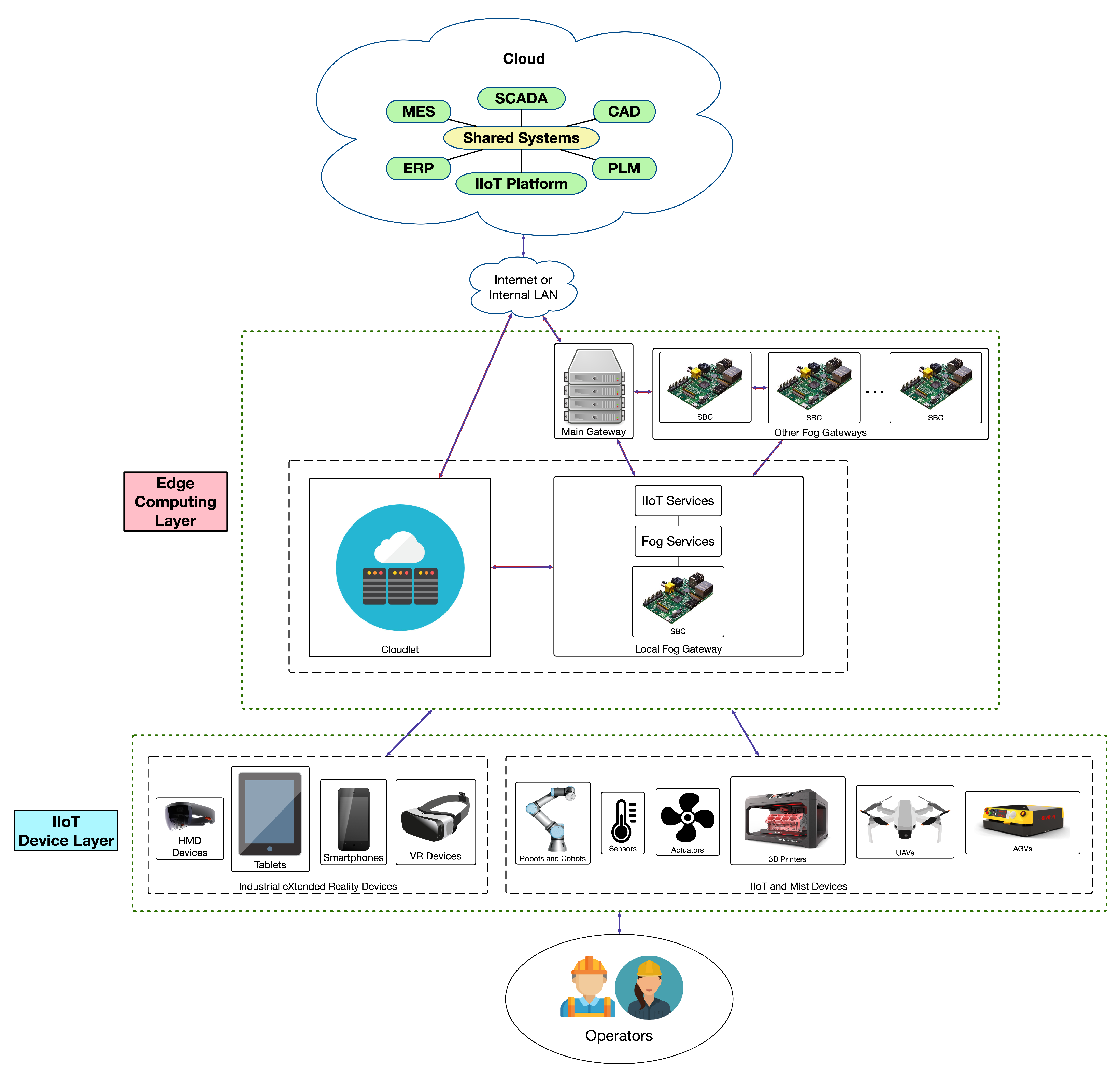
3. CPHS Communications Architecture
3.1. Essential Components
3.2. IIoT Device Layer
3.3. Edge Computing Layer
3.4. Cloud
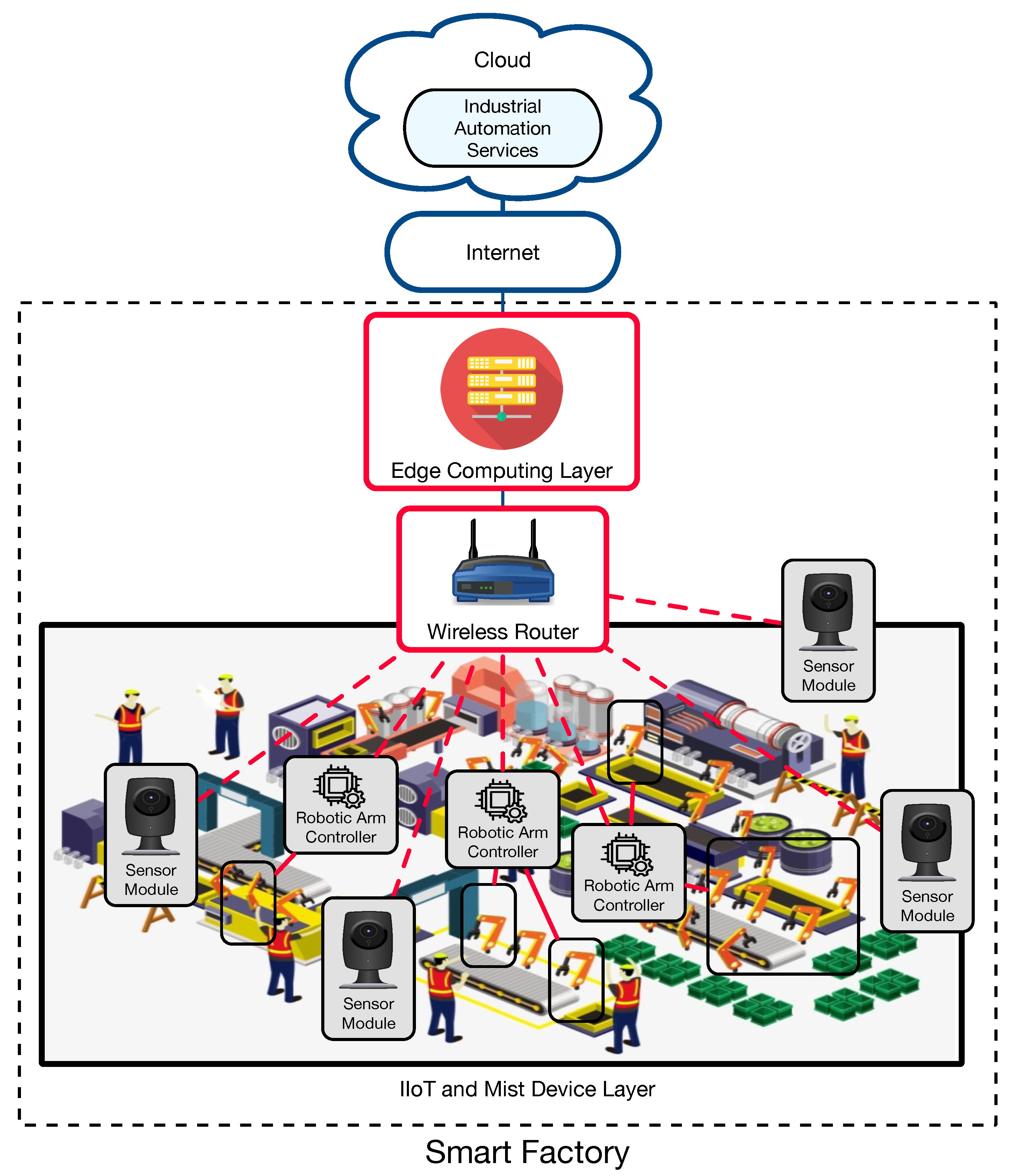
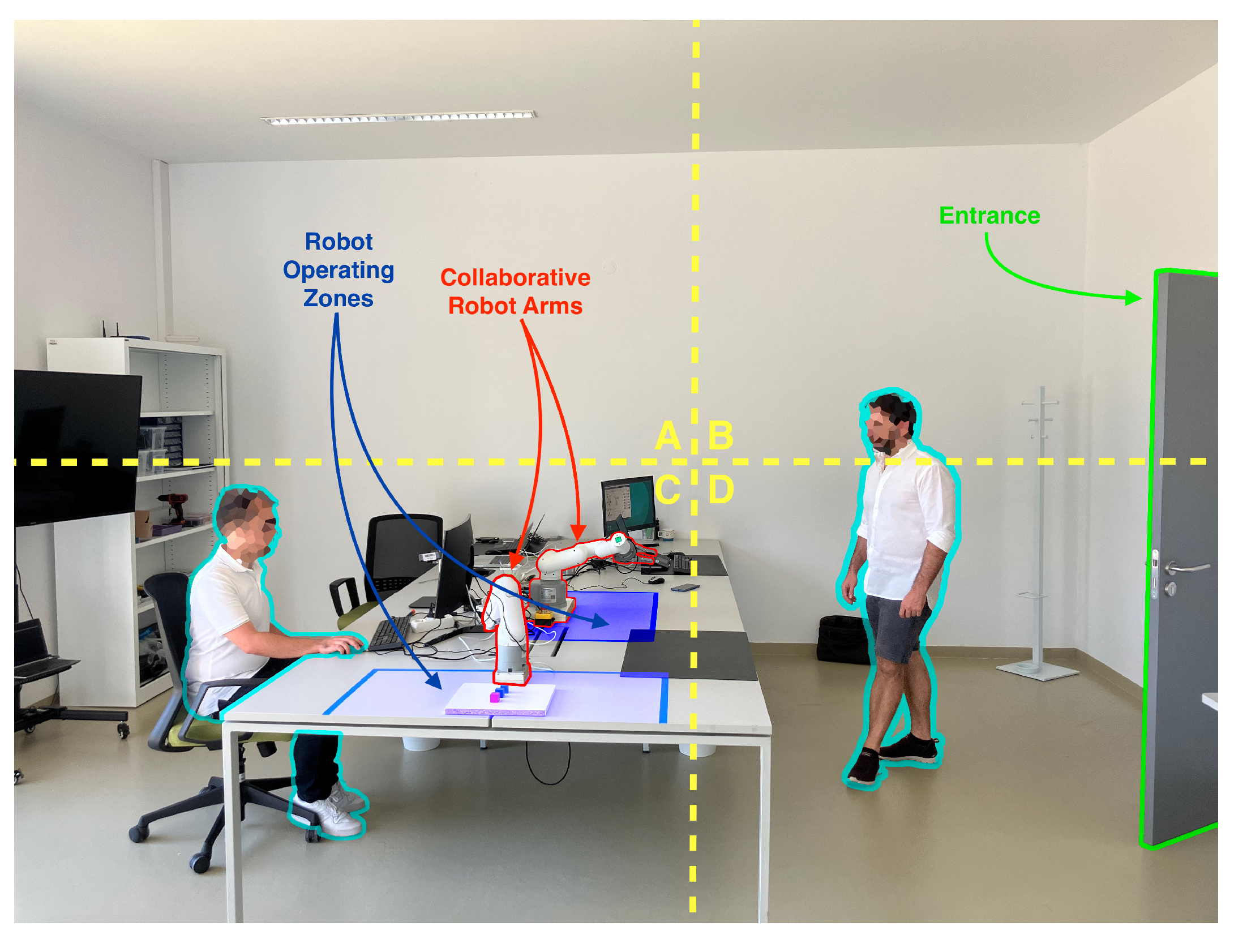
4. Application Case: CPHS-Based Thermal Imaging Sensors for a Smart Workshop
4.1. General Overview of the Proposed System
4.2. Implemented Communications Architecture
- IIoT Device Layer: It is composed of IIoT sensor modules and robotic arms controllers, which act as mist computing devices that collaborate to prevent industrial operators from being exposed to dangerous situations when working next to robotic arms. These mist computing devices can avoid exchanging image data over the network with edge computing devices or with the cloud, thus benefiting from:
- -
- Low latency: Since most of the processing is performed locally, a mist computing device can respond faster.
- -
- Improved local communications with other IIoT nodes: Mist devices can implement additional logic to communicate directly and autonomously with other IIoT devices and machines. Since there is no need for intermediary devices (e.g., servers or the cloud), responses and data exchanges are faster and less traffic is generated to the higher layers.
- -
- Fewer communication problems: Less interference in complex industrial environments, given that local processing prevents continuous and persistent communications with local edge devices, or remote clouds [88].
- -
- Fewer privacy issues: There is no need to send camera images to devices over the network, so possible attacks on those devices or man-in-the-middle attacks can be avoided and thus prevent other image leaks.
- Edge Computing Layer: it is able to provide fast-response services to the IIoT/mist devices. Nonetheless, since the development presented in this article is focused on analyzing the performance of the created mist computing devices, no specific data processing services were deployed in this layer.
- Cloud: It behaves as in traditional edge computing-based architectures, thus handling requests that cannot be dealt with locally.
4.3. Implementation
4.3.1. Mist Node Hardware
- Processing Subsystem: An Espressif ESP32 microcontroller was selected since it provides a good tradeoff among embedded computing power, low cost and energy efficiency [89], as well as abundant General Purpose Inputs Outputs (GPIOs), built-in Wi-Fi and Bluetooth communications, and an I2C interface for communicating with the sensor interface.
- Thermal Imaging Sensor: A FLIR Lepton 3.5 was selected. It is a small (11.8 × 12.7 × 7.2 mm) but very capable sensor, which provides a very good trade-off between performance and price. Specifically, the sensor uses an Uncooled VOx microbolometer for thermal imaging detection, and is capable of outputting 160 × 120 pixels resolution images with a 57° horizontal FOV, it has a thermal sensitivity of less than 50 mK (0.050 °C) and features a power dissipation of 150 mW while operating (650 mW during shutter events and 5 mW in standby).
- Sensor Interfacing: Allows for integrating the processing subsystem with the selected sensor. For such a purpose, a PureThermal2 was selected, which is a hackable Smart I/O Module. It has a built-in Micro-USB port and supports communications via I2C, UART and JTAG. It also includes a STM32F412 microprocessor that allows for executing on-board image processing. All this is provided in a compact form factor of only 30 × 18 mm.
4.3.2. Implemented Software
- 1.
- Thermal Images Dataset: To evaluate and validate the developed human-detection methods, a new thermal image dataset was obtained. For such a purpose, a Raspberry Pi 3B was used together with the PureThermal2 and the FLIR Lepton 3.5. A script was created to capture an image once every minute. During the acquisition phase, 1114 images were captured and added to the dataset.
- 2.
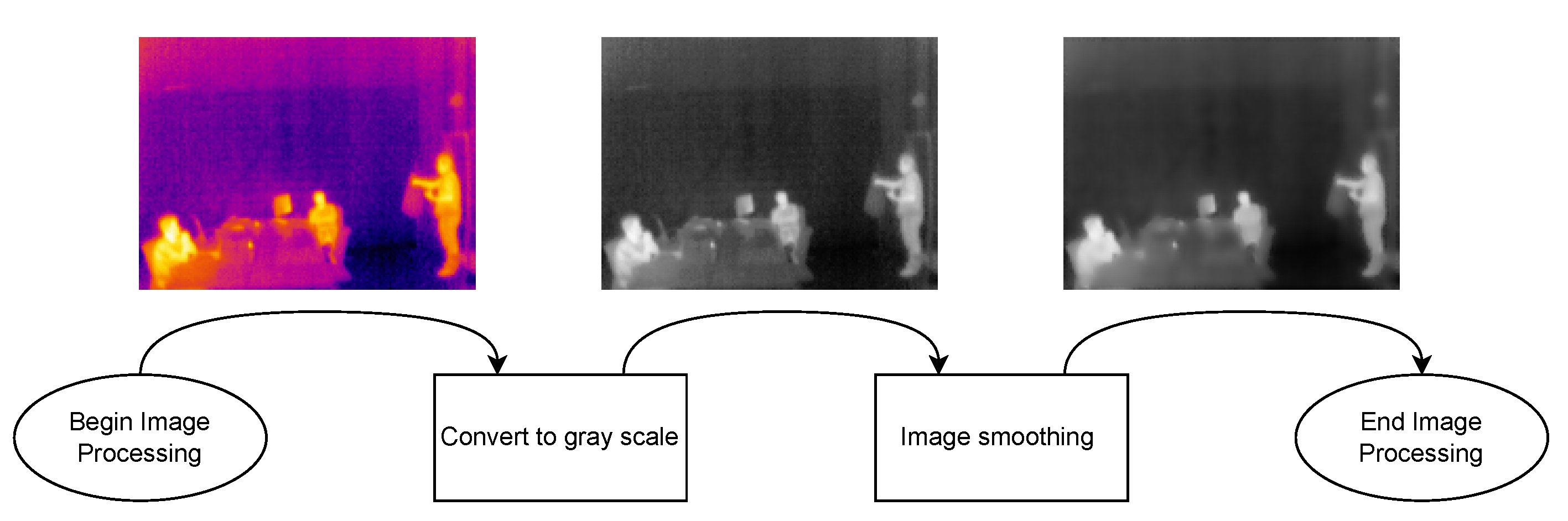
- Image Processing Module: Every image frame needs to be processed before applying the developed human-detection methods in order to uniformize the dataset. Specifically, every captured frame results in a 3D matrix of 160 × 120 × 3, corresponding to width, height, and color space (RGB), respectively. Such a matrix is first processed to convert it to gray scale, removing the third dimension of the matrix, thus resulting in a 160 × 120 pixels images, where every pixel corresponds to its intensity. Then, with the frame in gray scale, the image is smoothened by applying an isotropic Gaussian smoothing. Previous steps are illustrated in Figure 6.
- 3.
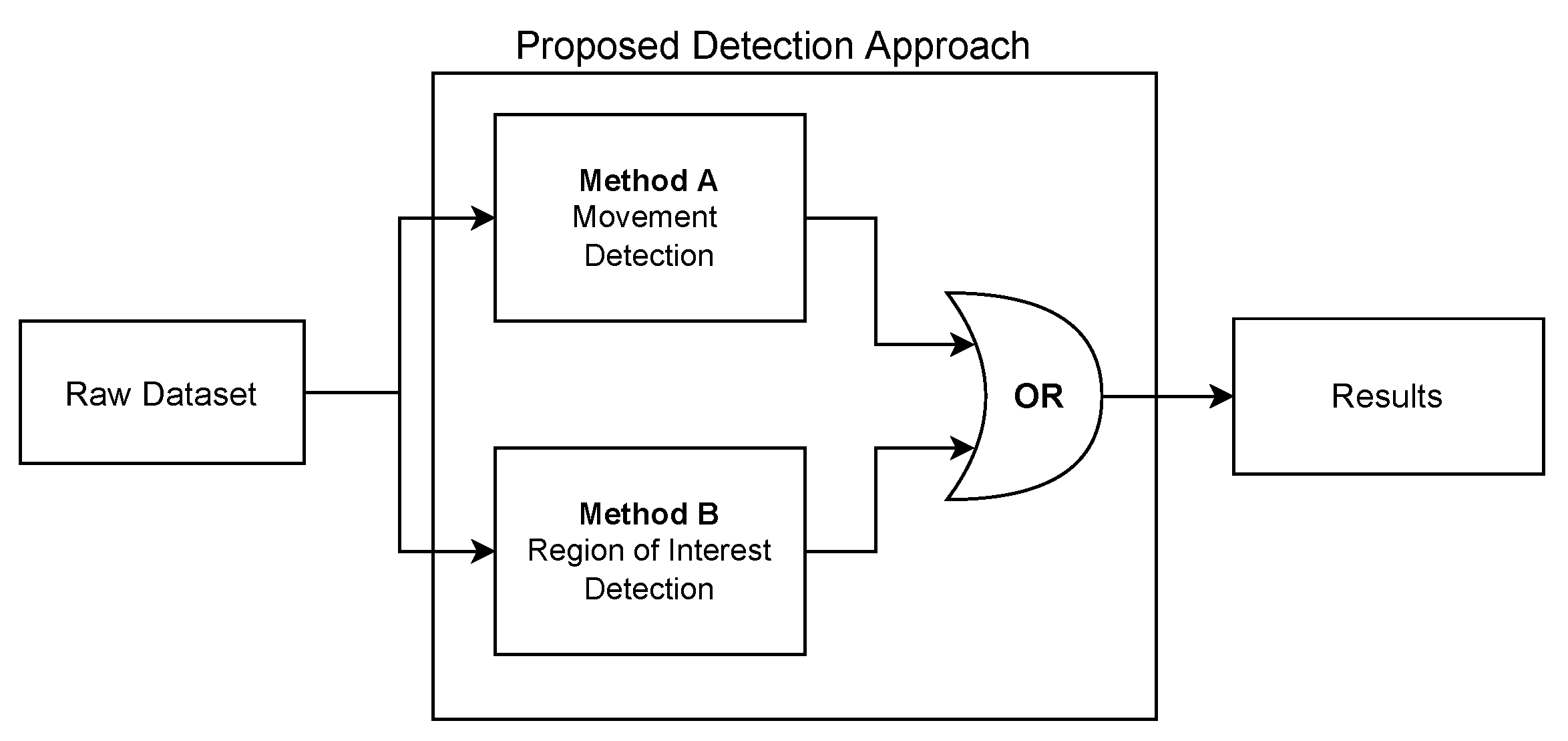
- Human-detection Methods: This is arguably the most critical part of the developed software, since it is responsible for accurately detecting the presence of humans within a given frame. For this software development, a hybrid detection approach was devised around one simple principle: every human is considered a body of heat, so, any body of heat with a shape resembling a human should be considered as one. This principle is only valid when using thermal imaging cameras, since traditional RGB cameras are not capable of detecting sources of heat. The devised hybrid detection mechanism consists of two methods: one capable of detecting movement and a second capable of detecting regions of interest within a frame. Both methods run in parallel, so, if one of them determines that there is a human present, the result is predicted as a positive detection. Therefore, a negative detection will only occur if both methods determine that there is no human present. Figure 7 depicts the proposed detection approach, using the terms “Method A” and “Method B” for the two developed approaches.
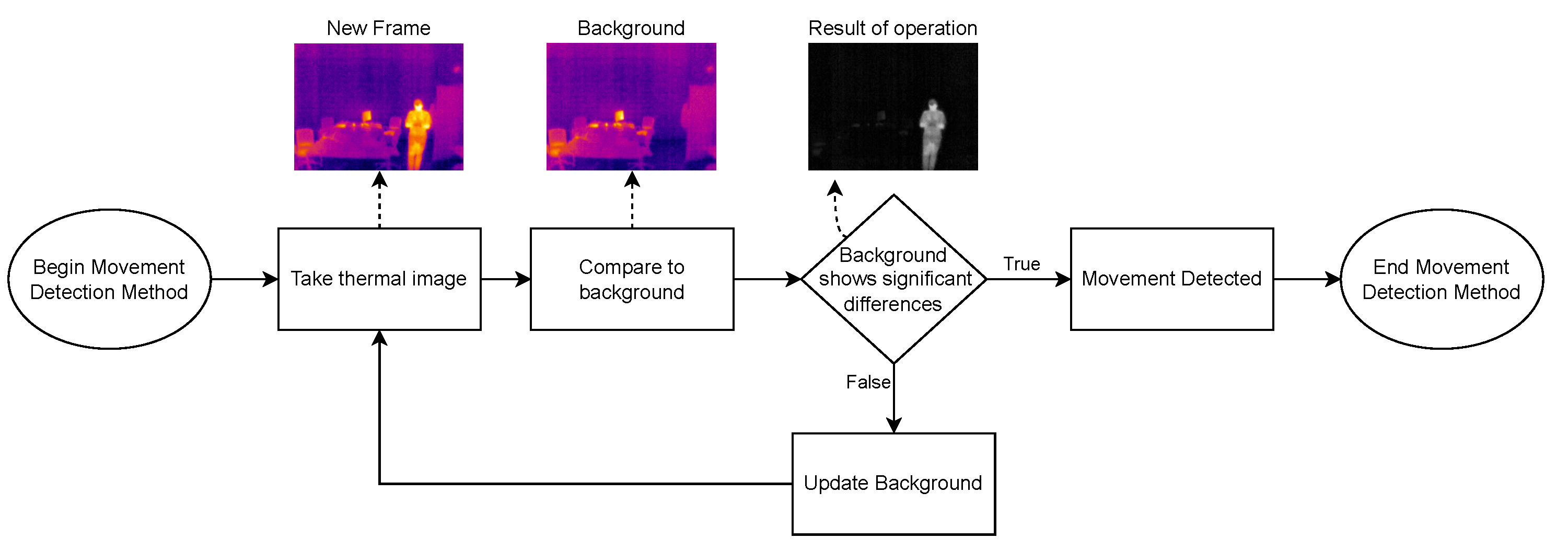
- Method A focuses on movement detection and follows the flowchart shown in Figure 8. As can be observed, it makes use of two frames: one that will serve as a starting point for the comparison, and another one that is compared to the previous. Thus, this method uses direct subtraction of image matrices to generate a new frame. This operation can yield two possible outcomes:
- (a)
- The result of absolute difference results in a new frame with pixel values averaging zero or near zero. This means that the new frame has no new significant updates; therefore, it can be concluded that no significant movement was detected. If this happens, the new frame will serve as the new background frame for the next comparison. This assures that the next comparison will always be performed with the most recent reference frames, so more accurate comparisons can be performed, and environmental factors can be compensated, such as temperature increases during the day and other external factors.
- (b)
- The absolute difference results in one or more group of pixels (also called active pixels) that have values near reference values. This means that there was a major update in the frame, so the likelihood of existing movement is very high. To achieve higher confidence when detecting movement, the obtained result is compared with a threshold. Such a threshold was calculated by considering the number of pixels in the image. For a frame of 19,200 pixels (i.e., image resolution of 160 × 120 pixels), if at least 5% (i.e., 960 pixels) of those pixels are considered as active pixels, then it can be determined with certainty that there was a significant amount of movement.
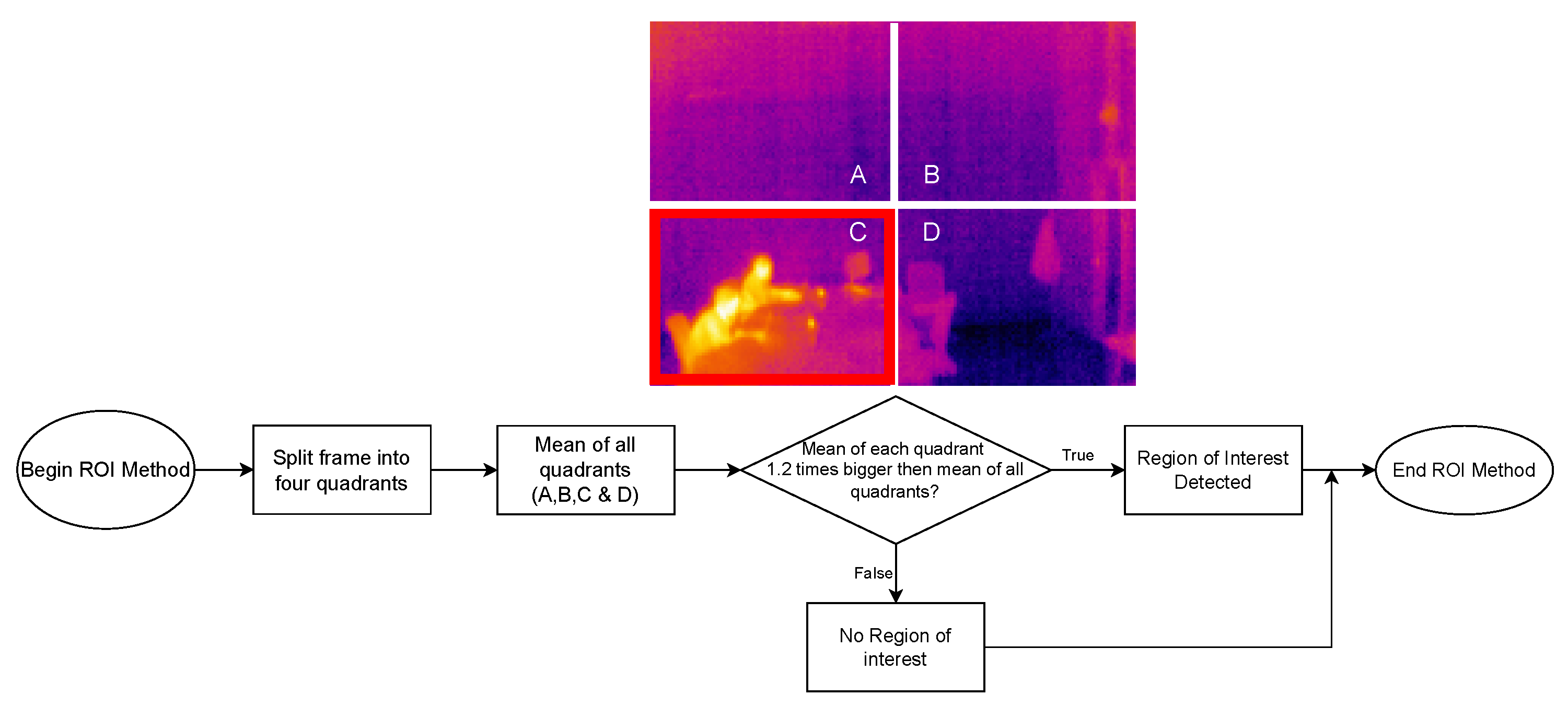
- Method B, whose flowchart is depicted in Figure 9, uses a Region of Interest Approach that consists in using a single 160 × 120 area that is then divided into four 80 × 60 pixel quadrants. An example of these quadrants is shown in Figure 10. Such four quadrants, on their own, do not contain much information, but when compared with the complete frame, they can help to determine whether those quadrants have any significant value. This comparison is made by using the mean value of all the pixels in the total frame with each image quadrant, so, if the original frame (i.e., 19,200 pixels) has a mean value of X, a quadrant (i.e., 4800 pixels) will be considered of interest when its mean is at least 20% greater than X. This method is fast and simple, and presented good results, as will be shown later in Section 4.4. Moreover, it is worth pointing out that Method B shows increased accuracy in detecting static persons in different parts of the frame. However, its performance decreases when the body of heat is in the center of the frame, which results in dividing it into four different quadrants. Nonetheless, this method is easy to implement and customize, as its deployment can be targeted into resource-constrained devices. For instance, a single quadrant could be monitored or, considering the room layout shown in Figure 10, only two specific quadrants could be monitored.
4.4. Experiments
4.4.1. Experimental Testbed
4.4.2. Performed Tests
4.4.3. Results
4.4.4. Result Analysis
5. Discussion
5.1. Key Findings
- After an analysis of the state-of-the art of the recent CPS and CPHS available in literature, surprisingly, it was found that most of current works only comply with one or two of the Industry 5.0 principles (human-centricity, sustainability, and resilience). In addition, most of the current CPHSs are mainly used in healthcare. Furthermore, there are not many cost-effective systems with low computational complexity to detect human presence.
- In addition, it is worth noting that the proposed novel hybrid mist and edge communications architecture, the Industry 4.0/5.0 enabling technologies discussed throughout this article were considered having a hostile industrial scenario in mind with real-time or near real-time and intensive computing requirements.
- Managing Quality of Service (QoS) in CPHSs communications is an important issue, since the implementation of CPHSs usually depends on state-of-the-art communications like 5G. QoS analysis is an important topic, since CPHSs are frequently used in industrial applications where latency requirements are strict. For example, 5G technologies present built-in mechanisms for defining, implementing, controlling, policing, and monitoring QoS.
- The proposed IoT Thermal Imaging Safety System is a cost-effective solution designed to trigger different safety states in manufacturing processes that rely on collaborative robotics. It enables the protection against possible incidents or accidents or the optimization of the energy efficiency of the deployed industrial devices and machinery. However, the proposed system should be used, in parallel, with a secondary safety redundant system, because although the system performance is high, detection accuracy is still not 100%.
- The system does not use centralized ML or AI algorithms that require prior training. It demands low-energy consumption, low footprint, low complexity, being a cost-effective solution that can be easily deployed into IoT architectures, with minimal intervention and tuning requirements, thus being able to operate in different environmental conditions.
- The adoption of Safety by Design (SbD) practices in CPHSs has a relevant impact in reducing accidents, by predicting, recognizing, and avoiding hazards, rather than retrofitting CPHSs after an accident has occurred. In this case, user safety is prioritized during the design and development of CPHSs.
- The design and development of CPHSs rely on distributed autonomous computing devices that require Distributed Real-Time Operative Systems (DRTOS) capabilities to perform inter-dependent critical tasks, such as motion control, computer vision, and machinery actuation, which demand deterministic execution and low-latency networks.
5.2. Challenges
5.3. Relevant Guidelines for Future Researchers
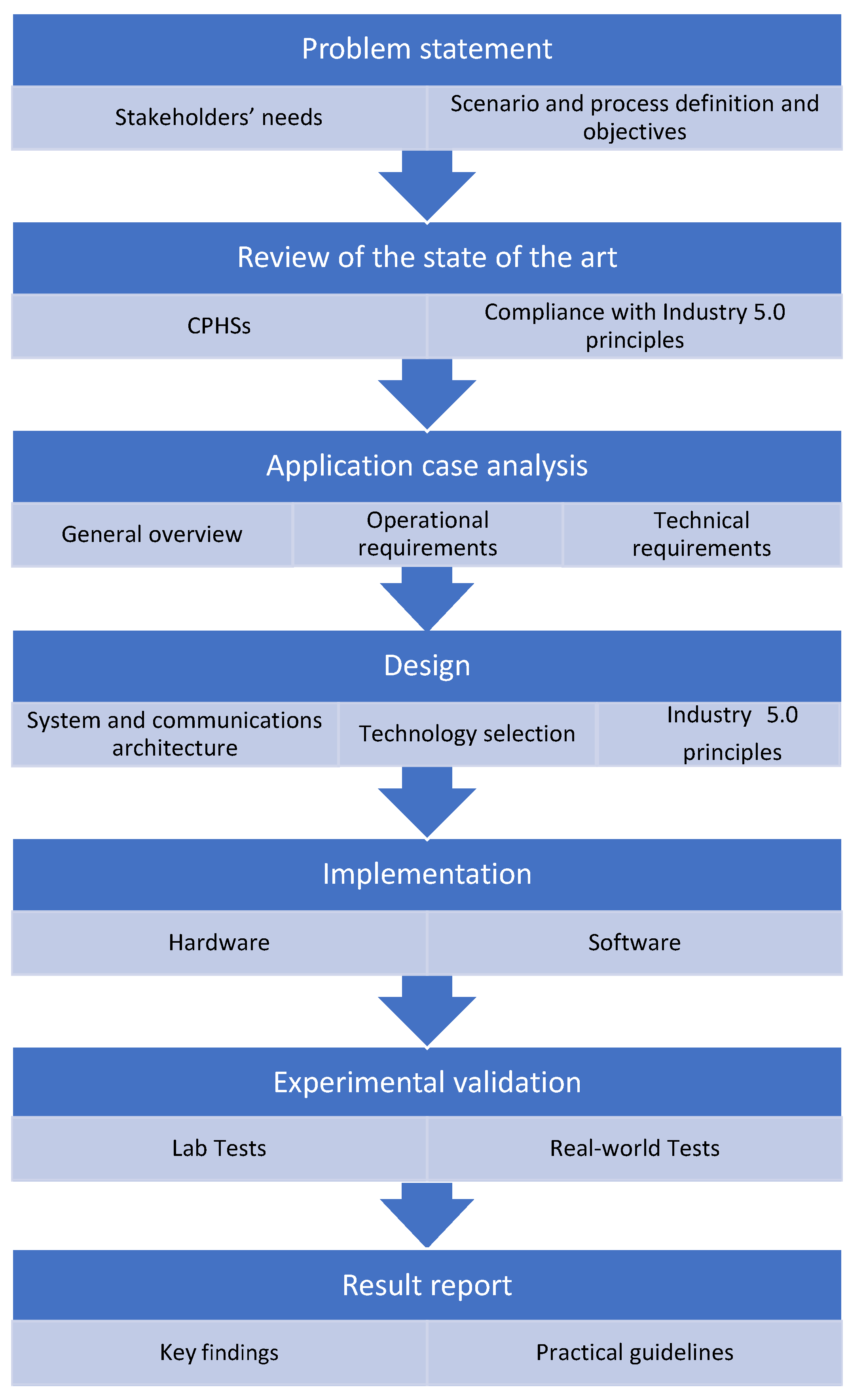
- 1.
- Problem statement. it is first necessary to analyze the stakeholders’ needs, to define the application scenario and to determine the involved processes.
- 2.
- Review of the state of the art. Relevant works on CPHSs have to be analyzed in terms of compliance with the principles of Industry 5.0. In addition, a detailed analysis of available technologies and communication architectures must be performed.
- 3.
- Application case analysis. The first step is to describe the selected use case in general terms, with emphasis on its main objectives. Specific operational and technical requirements must be detailed and analyzed along with the application scenario itself.
- 4.
- Design. Industry 5.0 principles (human-centricity, sustainability, and resilience) have to be taken into account throughout all the design process. An adequate trade-off must be obtained between the following aspects:
- Human-centricity: The system must be designed with the human needs in mind (e.g., human–machine collaborative scenarios) in a context of no full automation. Aspects like upskilling and reskilling of operators or technical assistance have to be carefully considered, adapting the production process to the needs of the worker and using technology to guide and/or train humans.
- Sustainability: The system must be designed with operational and resource efficiency at the core. In terms of hardware, low-cost and low power hardware must be considered. The communication architecture must be designed to minimize energy consumption. In terms of software, service-orientation and personalization have to be considered. In addition, accountability and transparency, data sharing (e.g., vertically or horizontally communications (in real-time when needed)) must be included [31]. The designed and developed services must be environmentally friendly across their lifetime and function within a circular economy framework.
- Resiliency: Real-time or near real-time communications must be provided together with resilience to cyberattacks (e.g., redundancy) and privacy measures.
- 5.
- Implementation. The designed CPHS will be implemented using the selected hardware and software.
- 6.
- Experimental validation. The developed system needs to be tested in the laboratory. After an analysis of the obtained results, the system must be evaluated in terms of performance with state-of-the-art systems.
- 7.
- Results report. The key findings based on practical experience may be reported to guide future researchers and developers.
6. Conclusions
Author Contributions
Funding
Acknowledgments
Conflicts of Interest
References
- Announcement of the Industrie 4.0 Project in the 2011 Hannover Fair. Available online: https://www.vdi-nachrichten.com/Technik-Gesellschaft/Industrie-40-Mit-Internet-Dinge-Weg-4-industriellen-Revolution (accessed on 1 September 2022).
- Council for Science, Technology and Innovation, Government of Japan, Report on The 5th Science and Technology Basic Plan. 18 December 2015. Available online: https://www8.cao.go.jp/cstp/kihonkeikaku/5basicplan_en.pdf (accessed on 28 July 2021).
- Nahavandi, S. Industry 5.0—A Human-Centric Solution. Sustainability 2019, 11, 16. [Google Scholar] [CrossRef]
- Paschek, D.; Mocan, A.; Draghici, A. Industry 5.0—The expected impact of next industrial revolution. In Proceedings of the MakeLearn & TIIM Conference, Piran, Slovenia, 15–17 May 2019; pp. 1–8. [Google Scholar]
- Maddikunta, P.K.R.; Pham, Q.V.; Prabadevi, B.; Deepa, N.; Dev, K.; Gadekallu, T.R.; Ruby, R.; Liyanage, M. Industry 5.0: A survey on enabling technologies and potential applications. J. Ind. Inf. Integr. 2022, 26, 100257. [Google Scholar] [CrossRef]
- Longo, F.; Padovano, A.; Umbrello, S. Value-oriented and ethical technology engineering in industry 5.0: A human-centric perspective for the design of the factory of the future. Appl. Sci. 2020, 10, 4182. [Google Scholar] [CrossRef]
- Lu, Y.; Xu, X.; Wang, L. Smart manufacturing process and system automation—A critical review of the standards and envisioned scenarios. J. Manuf. Syst. 2020, 56, 312–325. [Google Scholar] [CrossRef]
- European Commission, Industry 5.0: Towards a Sustainable, Human-Centric and Resilient European Industry. January 2021. Available online: https://ec.europa.eu/info/news/industry-50-towards-more-sustainable-resilient-and-human-centric-industry-2021-jan-07_en (accessed on 28 October 2022).
- Fraga-Lamas, P.; Fernández-Caramés, T.M. Leveraging blockchain for sustainability and open innovation: A cyber-resilient approach toward EU Green Deal and UN Sustainable Development Goals. In Computer Security Threats; IntechOpen: London, UK, 2020. [Google Scholar]
- Verma, A.; Bhattacharya, P.; Madhani, N.; Trivedi, C.; Bhushan, B.; Tanwar, S.; Sharma, G.; Bokoro, P.N.; Sharma, R. Blockchain for Industry 5.0: Vision, Opportunities, Key Enablers, and Future Directions. IEEE Access 2022, 10, 69160–69199. [Google Scholar] [CrossRef]
- Wang, F.Y.; Zhang, J.J. Transportation 5.0 in CPSS: Towards ACP-based society-centered intelligent transportation. In Proceedings of the 2017 IEEE 20th International Conference on Intelligent Transportation Systems (ITSC), Yokohama, Japan, 16–19 October 2017; pp. 762–767. [Google Scholar]
- Shahzadi, S.; Iqbal, M.; Chaudhry, N.R. 6G Vision: Toward Future Collaborative Cognitive Communication (3C) Systems. IEEE Commun. Stand. Mag. 2021, 5, 60–67. [Google Scholar] [CrossRef]
- Fraga-Lamas, P.; Ramos, L.; Mondéjar-Guerra, V.; Fernández-Caramés, T.M. A Review on IoT Deep Learning UAV Systems for Autonomous Obstacle Detection and Collision Avoidance. Remote Sens. 2019, 11, 2144. [Google Scholar] [CrossRef]
- Jain, D.K.; Li, Y.; Er, M.J.; Xin, Q.; Gupta, D.; Shankar, K. Enabling Unmanned Aerial Vehicle Borne Secure Communication With Classification Framework for Industry 5.0. IEEE Trans. Ind. Inform. 2022, 18, 5477–5484. [Google Scholar] [CrossRef]
- Galambos, P. Cloud, fog, and mist computing: Advanced robot applications. IEEE Syst. Man Cybern. Mag. 2020, 6, 41–45. [Google Scholar] [CrossRef]
- Fernández-Caramés, T.M.; Fraga-Lamas, P. Design of a Fog Computing, Blockchain and IoT-Based Continuous Glucose Monitoring System for Crowdsourcing mHealth. Proceedings 2019, 4, 37. [Google Scholar] [CrossRef]
- Tanganelli, G.; Cassano, L.; Miele, A.; Vallati, C. A methodology for the design and deployment of distributed cyber–physical systems for smart environments. Future Gener. Comput. Syst. 2020, 109, 420–430. [Google Scholar] [CrossRef]
- Jagatheesaperumal, S.K.; Rahouti, M.; Ahmad, K.; Al-Fuqaha, A.; Guizani, M. The Duo of Artificial Intelligence and Big Data for Industry 4.0: Applications, Techniques, Challenges, and Future Research Directions. IEEE Internet Things J. 2022, 9, 12861–12885. [Google Scholar] [CrossRef]
- Shi, Y.; Yang, K.; Jiang, T.; Zhang, J.; Letaief, K.B. Communication-Efficient Edge AI: Algorithms and Systems. IEEE Commun. Surv. Tutorials 2020, 22, 2167–2191. [Google Scholar] [CrossRef]
- Blanco-Novoa, Ó.; Fraga-Lamas, P.; Vilar-Montesinos, M.A.; Fernández-Caramés, T.M. Creating the Internet of Augmented Things: An Open-Source Framework to Make IoT Devices and Augmented and Mixed Reality Systems Talk to Each Other. Sensors 2020, 20, 3328. [Google Scholar] [CrossRef]
- Zhang, Y.; Guo, Z.; Lv, J.; Liu, Y. A framework for smart production-logistics systems based on CPS and industrial IoT. IEEE Trans. Ind. Inform. 2018, 14, 4019–4032. [Google Scholar] [CrossRef]
- Hernández-Rojas, D.L.; Fernández-Caramés, T.M.; Fraga-Lamas, P.; Escudero, C.J. A Plug-and-Play Human-Centered Virtual TEDS Architecture for the Web of Things. Sensors 2018, 18, 2052. [Google Scholar] [CrossRef]
- Arshad, R.; Zahoor, S.; Shah, M.A.; Wahid, A.; Yu, H. Green IoT: An Investigation on Energy Saving Practices for 2020 and Beyond. IEEE Access 2017, 5, 15667–15681. [Google Scholar] [CrossRef]
- Albreem, M.A.; Sheikh, A.M.; Alsharif, M.H.; Jusoh, M.; Mohd Yasin, M.N. Green Internet of Things (GIoT): Applications, Practices, Awareness, and Challenges. IEEE Access 2021, 9, 38833–38858. [Google Scholar] [CrossRef]
- Zhu, C.; Leung, V.C.M.; Shu, L.; Ngai, E.C.-H. Green Internet of Things for Smart World. IEEE Access 2015, 3, 2151–2162. [Google Scholar] [CrossRef]
- Fraga-Lamas, P.; Lopes, S.I.; Fernández-Caramés, T.M. Green IoT and edge AI as key technological enablers for a sustainable digital transition towards a smart circular economy: An industry 5.0 use case. Sensors 2021, 21, 5745. [Google Scholar] [CrossRef]
- Mylonas, G.; Kalogeras, A.; Kalogeras, G.; Anagnostopoulos, C.; Alexakos, C.; Muñoz, L. Digital Twins From Smart Manufacturing to Smart Cities: A Survey. IEEE Access 2021, 9, 143222–143249. [Google Scholar] [CrossRef]
- Qi, Q.; Tao, F. Digital Twin and Big Data Towards Smart Manufac- turing and Industry 4.0: 360 Degree Comparison. IEEE Access 2018, 6, 3585–3593. [Google Scholar] [CrossRef]
- Wang, B.; Zhou, H.; Yang, G.; Li, X.; Yang, H. Human Digital Twin (HDT) Driven Human-Cyber-Physical Systems: Key Technologies and Applications. Chin. J. Mech. Eng. 2022, 35, 1. [Google Scholar] [CrossRef]
- Fraga-Lamas, P.; Varela-Barbeito, J.; Fernández-Caramés, T.M. Next Generation Auto-Identification and Traceability Technologies for Industry 5.0: A Methodology and Practical Use Case for the Shipbuilding Industry. IEEE Access 2021, 9, 140700–140730. [Google Scholar] [CrossRef]
- Ghobakhloo, M.; Iranmanesh, M.; Mubarak, M.F.; Mubarik, M.; Rejeb, A.; Nilashi, M. Identifying industry 5.0 contributions to sustainable development: A strategy roadmap for delivering sustainability values. Sustain. Prod. Consum. 2022, 33, 716–737. [Google Scholar] [CrossRef]
- Mehdiabadi, A.; Shahabi, V.; Shamsinejad, S.; Amiri, M.; Spulbar, C.; Birau, R. Investigating Industry 5.0 and Its Impact on the Banking Industry: Requirements, Approaches and Communications. Appl. Sci. 2022, 12, 5126. [Google Scholar] [CrossRef]
- Qiu, T.; Chi, J.; Zhou, X.; Ning, Z.; Atiquzzaman, M.; Wu, D.O. Edge Computing in Industrial Internet of Things: Architecture, Advances and Challenges. IEEE Commun. Surv. Tutor. 2020, 22, 2462–2488. [Google Scholar] [CrossRef]
- Assaderaghi, F.; Chindalore, G.; Ibrahim, B.; de Jong, H.; Joye, M.; Nassar, S.; Steinbauer, W.; Wagner, M.; Wille, T. Privacy and security: Key requirements for sustainable IoT growth. In Proceedings of the 2017 Symposium on VLSI Technology, Kyoto, Japan, 5–8 June 2017. [Google Scholar]
- Zhang, Y.; Qiu, M.; Tsai, C.-W.; Hassan, M.M.; Alamri, A. Health-CPS: Healthcare cyber-physical system assisted by cloud and big data. IEEE Syst. J. 2015, 11, 88–95. [Google Scholar] [CrossRef]
- Leitão, P.; Colombo, A.W.; Karnouskos, S. Industrial automation based on cyber-physical systems technologies: Prototype implementations and challenges. Comput. Ind. 2016, 81, 11–25. [Google Scholar] [CrossRef]
- Gil, M.; Albert, M.; Fons, J.; Pelechano, V. Engineering human-in-the-loop interactions in cyber-physical systems. Inf. Softw. Technol. 2020, 126, 106349. [Google Scholar] [CrossRef]
- Krugh, M.; Mears, L. A complementary cyber-human systems framework for Industry 4.0 cyber-physical systems. Manuf. Lett. 2018, 15, 89–92. [Google Scholar] [CrossRef]
- Schirner, G.; Erdogmus, D.; Chowdhury, K.; Padir, T. The Future of Human-in-the-Loop Cyber- Physical Systems. Computer 2013, 46, 36–45. [Google Scholar] [CrossRef]
- Nunes, D.; Silva, J.S.; Boavida, F. A Practical Introduction to Human-in-the-Loop Cyber–Physical Systems; John Wiley & Sons: Hoboken, NJ, USA, 2018. [Google Scholar]
- Lopes, S.I.; Cruz, A.; Moreira, P.M.; Abreu, C.; Silva, J.P.; Lopes, N.; Vieira, J.; Curado, A. On the design of a Human-in-the-Loop Cyber-Physical System for online monitoring and active mitigation of indoor Radon gas concentration. In Proceedings of the 2018 IEEE International Smart Cities Conference (ISC2), Kansas City, MO, USA, 16–19 September 2018; pp. 1–8. [Google Scholar]
- Zhou, J.; Zhou, Y.; Wang, B.; Zang, J. Human–Cyber–Physical Systems (HCPSs) in the Context of New-Generation Intelligent Manufacturing. Engineering 2019, 5, 624. [Google Scholar] [CrossRef]
- Wang, B.; Zheng, P.; Yin, Y.; Shih, A.; Wang, L. Toward human-centric smart manufacturing: A human-cyber-physical systems (HCPS) perspective. J. Manuf. Syst. 2022, 63, 471. [Google Scholar] [CrossRef]
- Sowe, S.K.; Simmon, E.; Zettsu, K.; de Vaulx, F.; Bojanova, I. Cyber-Physical-Human Systems: Putting People in the Loop. IT Prof. 2016, 18, 10–13. [Google Scholar] [CrossRef]
- Jiao, J.; Zhou, F.; Gebraeel, N.Z.; Duffy, V. Towards augmenting cyber-physical-human collaborative cognition for human-automation in- teraction in complex manufacturing and operational environments. Int. J. Prod. Res. 2020, 58, 5089–5111. [Google Scholar] [CrossRef]
- Yilma, B.A.; Panetto, H.; Naudet, Y. Systemic formalisation of Cyber-Physical-Social System (CPSS): A systematic literature review. Comput. Ind. 2021, 129, 103458. [Google Scholar] [CrossRef]
- De, S.; Zhou, Y.; Abad, I.L.; Moessner, K. Cyber–Physical–Social Frameworks for Urban Big Data Systems: A Survey. Appl. Sci. 2017, 7, 1017. [Google Scholar] [CrossRef]
- Zhou, Y.; Yu, F.R.; Chen, J.; Kuo, Y. Cyber-physical-social systems: A state-of-the-art survey, challenges and opportunities. IEEE Commun. Surv. Tutor. 2020, 22, 389–425. [Google Scholar] [CrossRef]
- Wang, S.; Zhou, A.; Yang, M.; Sun, L.; Hsu, C.; Yang, F. Service composition in cyber-physical-social systems. IEEE Trans. Emerg. Top. Comput. 2020, 8, 82–91. [Google Scholar] [CrossRef]
- Thakur, P.; Sehgal, V.K. Emerging architecture for heterogeneous smart cyber-physical systems for industry 5.0. Comput. Ind. Eng. 2021, 162, 107750. [Google Scholar] [CrossRef]
- Patil, R.V.; Ambritta, N.P.; Mahalle, P.N.; Dey, N. Medical Cyber-Physical System s in Society 5.0: Are We Ready? IEEE Trans. Technol. Soc. 2022, 3, 189–198. [Google Scholar] [CrossRef]
- Lee, J.; Bagheri, B.; Kao, H. A Cyber-Physical Systems architecture for Industry 4.0-based manufacturing systems. Manuf. Lett. 2015, 3, 18–23. [Google Scholar] [CrossRef]
- Noguchi, H.; Sugano, S. Ephemeral-Cyber-Physical System: A Cloud-Like CPS Using Shared Devices in Open IoT. IEEE Syst. J. 2020, 14, 5176–5186. [Google Scholar] [CrossRef]
- Song, K.; Anderson, K.; Lee, S. An energy-cyber-physical system for personalized normative messaging interventions: Identification and classification of behavioral reference groups. Appl. Energy 2020, 260, 114237. [Google Scholar] [CrossRef]
- Broo, D.G. Transdisciplinarity and three mindsets for sustainability in the age of cyber-physical systems. J. Ind. Inf. Integr. 2022, 27, 100290. [Google Scholar] [CrossRef]
- Monostori, L. Cyber-physical production systems: Roots, expectations and R&D challenges. Procedia CIRP 2014, 17, 9–13. [Google Scholar]
- Liu, H.; Wang, L. Remote human–robot collaboration: A cyber–physical system application for hazard manufacturing environment. J. Manuf. Syst. 2020, 54, 24–34. [Google Scholar] [CrossRef]
- Zografopoulos, I.; Ospina, J.; Liu, X.; Konstantinou, C. Cyber-Physical Energy Systems Security: Threat Modeling, Risk Assessment, Resources, Metrics, and Case Studies. IEEE Access 2021, 9, 29775–29818. [Google Scholar] [CrossRef]
- Cao, K.; Hu, S.; Shi, Y.; Colombo, A.W.; Karnouskos, S.; Li, X. A Survey on Edge and Edge-Cloud Computing Assisted Cyber-Physical Systems. IEEE Trans. Ind. Inform. 2021, 17, 7806–7819. [Google Scholar] [CrossRef]
- Zhang, C.; Tang, P.; Cooke, N.; Buchanan, V.; Yilmaz, A.; Germain, S.W.S.; Boring, R.L.; Akca-Hobbins, S.; Gupta, A. Human-centered automation for resilient nuclear power plant outage control. Autom. Constr. 2017, 82, 179–192. [Google Scholar] [CrossRef]
- Gao, X.; Su, X.; Qian, H.; Pan, X. Dependence assessment in human reliability analysis under uncertain and dynamic situations. Nucl. Eng. Technol. 2022, 54, 948–958. [Google Scholar] [CrossRef]
- Jirgl, M.; Bradac, Z.; Fiedler, P. Human-in-the-loop issue in context of the cyber-physical systems. IFAC-PapersOnLine 2018, 51, 225–230. [Google Scholar] [CrossRef]
- Madni, A.; Sievers, M.; Madni, C. Adaptive cyber-physical-human systems: Exploiting cognitive modeling and machine learning in the control loop. Insight 2018, 21, 87–93. [Google Scholar] [CrossRef]
- Ignatius, H.T.N.; Bahsoon, R. A Conceptual Reference Model for Human as a Service Provider in Cyber Physical Systems. In Proceedings of the 2021 International Symposium on Software Engineering for Adaptive and Self-Managing Systems (SEAMS), Madrid, Spain, 18–24 May 2021; pp. 1–10. [Google Scholar] [CrossRef]
- Razaque, A.; Amsaad, F.; Abdulgader, M.; Alotaibi, B.; Alsolami, F.; Gulsezimhas, D.; Mohanty, S.; Hariri, S. A Mobility-aware Human-centric Cyber-physical System for Efficient and Secure Smart Healthcare. IEEE Internet Things J. 2022. [Google Scholar] [CrossRef]
- Ma, M.; Lin, W.; Pan, D.; Lin, Y.; Wang, P.; Zhou, Y.; Liang, X. Data and decision intelligence for human-in-the-loop cyber-physical systems: Reference model, recent progresses and challenges. J. Signal Process. Syst. 2018, 90, 1167–1178. [Google Scholar] [CrossRef]
- Broo, D.G.; Schooling, J. A framework for using data as an engineering tool for sustainable cyber-physical systems. IEEE Access 2021, 9, 22876–22882. [Google Scholar] [CrossRef]
- Zhang, Y.; Qian, C.; Lv, J.; Liu, Y. Agent and cyber-physical system based self-organizing and self-adaptive intelligent shopfloor. IEEE Trans. Ind. 2017, 13, 737–747. [Google Scholar] [CrossRef]
- Wang, B.; Li, X.; Freiheit, T.; Epureanu, B.I. Learning and Intelligence in Human-Cyber-Physical Systems: Framework and Perspective. In Proceedings of the 2020 Second International Conference on Transdisciplinary AI (TransAI), Irvine, CA, USA, 21–23 September 2020; pp. 142–145. [Google Scholar]
- Ren, Y.; Li, G.-P. An Interactive and Adaptive Learning Cyber Physical Human System for Manufacturing With a Case Study in Worker Machine Interactions. IEEE Trans. Ind. Inform. 2022, 18, 6723–6732. [Google Scholar] [CrossRef]
- Broo, D.G.; Bravo-Haro, M.; Schooling, J. Design and implementation of a smart infrastructure digital twin. Autom. Constr. 2022, 136, 104171. [Google Scholar] [CrossRef]
- Bonomi, F.; Milito, R.; Zhu, J.; Addepalli, S. Fog Computing and its Role in the Internet of Things. In Proceedings of the First Edition of the MCC Workshop on Mobile Cloud Computing, Helsinki, Finlad, 17 August 2012; pp. 13–16. [Google Scholar]
- Dolui, K.; Datta, S.K. Comparison of edge computing implementations: Fog computing, cloudlet and mobile edge computing. In Proceedings of the Global Internet of Things Summit (GIoTS), Geneva, Switzerland, 6–9 June 2017. [Google Scholar]
- Preden, J.S.; Tammemäe, K.; Jantsch, A.; Leier, M.; Riid, A.; Calis, E. The Benefits of Self-Awareness and Attention in Fog and Mist Computing. Computer 2015, 48, 37–45. [Google Scholar] [CrossRef]
- Song, J.C.; Demir, M.A.; Prevost, J.J.; Rad, P. Blockchain Design for Trusted Decentralized IoT Networks. In Proceedings of the 2018 13th Annual Conference on System of Systems Engineering (SoSE), Paris, France, 19–22 June 2018; pp. 169–174. [Google Scholar]
- Sun, M.; Tay, W.P. On the Relationship Between Inference and Data Privacy in Decentralized IoT Networks. IEEE Trans. Inf. Forensics Secur. 2020, 15, 852–866. [Google Scholar] [CrossRef]
- Santamaria, A.F.; Raimondo, P.; Tropea, M.; De Rango, F.; Aiello, C. An IoT Surveillance System Based on a Decentralised Architecture. Sensors 2019, 19, 1469. [Google Scholar] [CrossRef]
- Zlatanski, M.; Sommer, P.; Zurfluh, F.; Madonna, G.L. Radar Sensor for Fenceless Machine Guarding and Collaborative Robotics. In Proceedings of the 2018 IEEE International Conference on Intelligence and Safety for Robotics (ISR), Shenyang, China, 24–27 August 2018; pp. 19–25. [Google Scholar] [CrossRef]
- Proia, S.; Carli, R.; Cavone, G.; Dotoli, M. Control Techniques for Safe, Ergonomic, and Efficient Human-Robot Collaboration in the Digital Industry: A Survey. IEEE Trans. Autom. Sci. Eng. 2022, 19, 1798–1819. [Google Scholar] [CrossRef]
- Gradolewski, D.; Maslowski, D.; Dziak, D.; Jachimczyk, B.; Mundlamuri, S.T.; Prakash, C.G.; Kulesza, W.J. A Distributed Computing Real-Time Safety System of Collaborative Robot. Elektron. Elektrotechnika 2020, 26, 4–14. [Google Scholar] [CrossRef]
- Altaf, M.A.; Ahn, J.; Khan, D.; Kim, M.Y. Usage of IR Sensors in the HVAC Systems, Vehicle and Manufacturing Industries: A Review. IEEE Sens. J. 2022, 22, 9164–9176. [Google Scholar] [CrossRef]
- Chidurala, V.; Li, X. Occupancy Estimation Using Thermal Imaging Sensors and Machine Learning Algorithms. IEEE Sens. J. 2021, 21, 8627–8638. [Google Scholar] [CrossRef]
- Braga, B.; Queirós, G.; Abreu, C.; Lopes, S.I. Assessment of Low-Cost Infrared Thermography Systems for Medical Screening in Nursing Homes. In Proceedings of the 2021 17th International Conference on Wireless and Mobile Computing, Networking and Communications (WiMob), Bologna, Italy, 11–13 October 2021; pp. 157–162. [Google Scholar]
- Abah, C.; Orekhov, A.L.; Johnston, G.L.H.; Yin, P.; Choset, H.; Simaan, N. A Multi-modal Sensor Array for Safe Human-Robot Interaction and Mapping. In Proceedings of the 2019 International Conference on Robotics and Automation (ICRA), Montreal, QC, Canada, 20–24 May 2019; pp. 3768–3774. [Google Scholar] [CrossRef]
- Swamy, S.N.; Kota, S.R. An Empirical Study on System Level Aspects of Internet of Things (IoT). IEEE Access 2020, 8, 188082–188134. [Google Scholar] [CrossRef]
- Sánchez, J.M.G.; Jörgensen, N.; Törngren, M.; Inam, R.; Berezovskyi, A.; Feng, L.; Fersman, E.; Ramli, M.R.; Tan, K. Edge Computing for Cyber-physical Systems: A Systematic Mapping Study Emphasizing Trustworthiness. Acm Trans. Cyber-Phys. Syst. 2022, 6, 1–28. [Google Scholar] [CrossRef]
- Rocha, D.; Rocha, P.; Ribeiro, J.; Lopes, S.I. Identification and Classification of Human Body Parts for Contactless Screening Systems: An Edge-AI Approach. In Science and Technologies for Smart Cities; SmartCity 360 2021. Lecture Notes of the Institute for Computer Sciences, Social Informatics and Telecommunications Engineering; Springer: Cham, Switzerland, 2022; Volume 442. [Google Scholar]
- Fraga-Lamas, P.; Fernández-Caramés, T.M.; Noceda-Davila, D.; Vilar-Montesinos, M. RSS stabilization techniques for a real-time passive UHF RFID pipe monitoring system for smart shipyards. In Proceedings of the 2017 IEEE International Conference on RFID (RFID), Phoenix, AZ, USA, 9–11 May 2017; pp. 161–166. [Google Scholar]
- Gatial, E.; Balogh, Z.; Hluchý, L. Concept of Energy Efficient ESP32 Chip for Industrial Wireless Sensor Network. In Proceedings of the 2020 IEEE 24th International Conference on Intelligent Engineering Systems (INES), Reykjavík, Iceland, 8–10 July 2020; pp. 179–184. [Google Scholar] [CrossRef]
- Real-Time Human Detection with OpenCV. (n.d.). Available online: https://thedatafrog.com/en/articles/human-detection-video (accessed on 18 August 2022).
- Naik, U.P.; Rajesh, V.; Kumar, R.R.; Mohana. Implementation of YOLOv4 Algorithm for Multiple Object Detection in Image and Video Dataset using Deep Learning and Artificial Intelligence for Urban Traffic Video Surveillance Application. In Proceedings of the 2021 Fourth International Conference on Electrical, Computer and Communication Technologies (ICECCT), Erode, India, 15–17 September 2021; pp. 1–6. [Google Scholar] [CrossRef]
- Saponara, S.; Elhanashi, A.; Gagliardi, A. Implementing a real-time, AI-based, people detection and social distancing measuring system for Covid-19. J. Real-Time Image Proc. 2021, 18, 1937–1947. [Google Scholar] [CrossRef]


| Reference | Type of System | Application Field | Human-Centricity | Sustainability | Resilience | Other Relevant Features |
|---|---|---|---|---|---|---|
| [50] | CPS | Design automation, System synchronization, Dynamic Voltage and Frequency Scaling (DVFS) control, Voltage Frequency Islands (VFI) partition | × | ✓ | ✓ | Discussion on the design of a smart mission-critical CPS. |
| [51] | CPS | Healthcare | × | × | ✓ | Framework with a Security Layer with Open Authorization (OAuth), User-Managed Access (UMA), and Self-Sovereign Identity (SSI). |
| [52] | CPS | Manufacturing, Prognostics and health management | × | × | ✓ | Description of the flow of information on a 5-layer CPS architecture. |
| [36] | CPS | Manufacturing, Electronics assembly, Continuous processing, Energy management | Partially (theoretical) | × | ✓ | Overview of key aspects of ICPSs, future research, as well as implementation challenges based on the experience of four European innovation projects. |
| [53] | CPS | Experiments with IoT devices: two lighting devices and a web camera. | × | ✓ | ✓ | CPS for Open IoT. It includes a method of actuator control optimization based on service satisfaction and system operation cost. It allows for automatically constructing the CPS by using non-configured IoT devices or robots connected to the network. |
| [54] | CPS | Smart grid infrastructure, Household energy consumption, Behavior change | ✓ | ✓ | × | CPS developed with data mining techniques to provide households with feedback messages about energy use. Evaluation of performance of dynamic behavioral reference group classification. |
| [55] | CPS | Digital twin in smart infrastructure (E-type steel half-through railway bridge) | Partially (information collected is presented in a human-centered way, metrics) | × | ✓ | Literature review of digital twin architectures. |
| [56] | CPS | Manufacturing | × | × | × | Challenges of CPSs in manufacturing |
| [57] | CPHS | Hazard Manufacturing | Yes (human-robot collaboration) | × | × | Design and testing of a remote robot control system (i.e., from robot to robot) and a model-driven display system (i.e., to ease the understanding of the production context by the operator) that can work in several modes. |
| [58] | CPS | Critical infrastructure, energy systems | Partially (HMI) | × | ✓ | Framework for security evaluation (model, simulate, assess and mitigate) illustrated by four attack case studies. Risk assessment analysis. |
| [59] | CPS | - | × | Partially (energy consumption minimization) | ✓ | Edge and edge-cloud computing CPS. Survey of the state of the art and analysis of challenges in service latency reduction, Quality of Service (QoS) optimization, energy consumption minimization, trade-off service latency and energy consumption, security and privacy enhancement, and reliability augmentation. Description of future research directions. |
| [60] | CPHS | Critical infrastructure, nuclear power plant | ✓ | × | ✓ | Identification of domain requirements (e.g., data collection, data processing, computational modeling, simulation), challenges, and potential solutions to create a human-centered automation system that supports resilient nuclear power plant outage control. Enhanced performance of handoff monitoring and control between tasks and to respond to contingencies in workflows during the outage. Research roadmap for human-centered automation in construction. |
| [44] | CPHS | - | ✓ | × | × | Human service capability description model to help in the integration of people in CPHSs. The model focuses on the structure of data representing a person’s capability. |
| [62] | CPHS | - | ✓ | × | ✓ | Measurements and modeling of human behavior, prediction of human response and his/her dynamic properties. |
| [63] | Adaptive CPHS | - | ✓ | × | × | Three types of adaptive CPHS: human controls CPS, CPS monitors human and act when needed, and human monitoring of the CPS that acts as controller. Discussion of key learning and adaptation techniques. Current challenges of adaptive CPHS (e.g., cognitive modeling and machine learning in the control loop). Functional reference architecture to guide the developers of adaptive CPH systems. |
| [64] | CPHS | Healthcare | ✓ | × | × | SOA ontology model for CPHS: human characteristics and their dynamics, as a service provider or collaborator with the machine (e.g., sensing, processing, actuating, and promote adaptation for other nodes). Ontology evaluation. |
| [65] | CPHS | Healthcare | ✓ | ✓ | ✓ | Prototype for a privacy-aware secure human-centric mobility-aware (SHM) model to analyze physical and human domains in IoT-based wireless sensor networks (WSNs). |
| [66] | CPHS | Smart space, transportation and grid | ✓ | × | × | Reference model and key challenges (semantic, interactive, iterative). Analysis of different aspects of data characteristics. |
| [67] | CPS | Smart infrastructure (bridges, railways and transport systems) | ✓ | ✓ | × | Systems architecture to integrate different digital twins. |
| [68] | CPS | Manufacturing, smart shopfloor | × | ✓ | ✓ | CPS for intelligent shopfloor with high autonomy, adaptability, and efficiency. Manufacturing machines are modeled as smart agents. Self-organizing capabilities to maximize resource efficiency. Self-adaptive mechanism when exceptions occur. |
| [69] | CPHS | - | Partially | × | × | Review-based and interaction-based learning and intelligence in CPHS. |
| [70] | CPHS | Manufacturing, worker-machine interaction | ✓ | × | ✓ | Adaptive ML based smart manufacturing interactive CPHS. The ML model self-evolves during deployment with the streaming data in a self-labeling manner. Enhanced accuracy for human machine interaction detection by up to 12.5%. |
| This work | CPHS | Industrial operator safety | ✓ | ✓ | ✓ | Use of a novel edge/mist computing and efficient human-presence detection algorithms that can be executed in low-power IoT nodes. |
| Ground Truth (Manually Analyzed) | ||||
|---|---|---|---|---|
| 1069 | 44 | |||
| Positive | Negative | |||
| Predicted (Method A) | 1101 | Positive | 1057 TP (94.97%) | 44 FP (3.95%) |
| 12 | Negative | 12 FN (1.08 %) | 0 TN (0 %) | |
| Ground Truth (Manually Analyzed) | ||||
|---|---|---|---|---|
| 1055 | 59 | |||
| Positive | Negative | |||
| Predicted (Method B) | 1038 | Positive | 1027 TP (92.19%) | 11 FP (0.99%) |
| 76 | Negative | 28 FN (2.51%) | 48 TN (4.31%) | |
| Ground Truth (Manually Analyzed) | ||||
|---|---|---|---|---|
| 1057 | 57 | |||
| Positive | Negative | |||
| Predicted (Both Methods) | 1056 | Positive | 1040 TP (93.35%) | 16 FP (1.44%) |
| 58 | Negative | 17 FN (1.53%) | 41 TN (3.68%) | |
| Reference | Type of System | Architecture | Main Hardware | Detection Algorithm | Accuracy | Maximum Detection Latency | Cost |
|---|---|---|---|---|---|---|---|
| [80] | CPHS for preserving safety when working with cobots | Cloud Computing | Each IoT node has an 8 Megapixel camera and several, an ultrasound sensor, a stepper motor and a Raspberry Pi. Images are preprocessed on the Raspberry Pi and sent to a remote Linux server that carries out detection through its GPU. | HoG Viola Jones YOLO v3 | 70% 77% 99% | 201 ms 191 ms 151 ms | Medium (IoT nodes cost less than 100€, but a powerful server is required) |
| [90] | Algorithm implementation | n/a | Powerful GPU (e.g., GeForce GTX 1080 Ti) and a webcam. | YOLO v3 | 99% | 200 ms | Medium (IoT nodes cost less than 50€, but a powerful server is required) |
| [91] | Algorithm implementation | n/a | Webcam and PC with at least 8 GB of RAM, 500 GB of disk drive, 64-bit CPU and a dedicated GPU. | YOLO v4 | 99.28% | n/a | Medium |
| [92] | CPHS for measuring social distancing | Cloud Computing | 8 Megapixel webcam and an NVIDIA Jetson Nano (ARM57, 1.43 GHz, 64-bit CPU, 4 GB of RAM, 128-core GPU). | Based on YOLO v2 | 95.60% | 37 ms | Low (less than 200€ per IoT node) |
| This Work | CPHS for avoiding industrial operator exposition to dangerous situations | Edge/Mist Computing | Low cost SBC (Raspberry Pi 3B), thermal imaging sensor, PureThermal2 adapter. | Method A Method B Hybrid Method | 94.97% 96.50% 97.04% | 7 ms 6 ms 10 ms | Low (roughly 200€ per IoT node) |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2022 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Fraga-Lamas, P.; Barros, D.; Lopes, S.I.; Fernández-Caramés, T.M. Mist and Edge Computing Cyber-Physical Human-Centered Systems for Industry 5.0: A Cost-Effective IoT Thermal Imaging Safety System. Sensors 2022, 22, 8500. https://doi.org/10.3390/s22218500
Fraga-Lamas P, Barros D, Lopes SI, Fernández-Caramés TM. Mist and Edge Computing Cyber-Physical Human-Centered Systems for Industry 5.0: A Cost-Effective IoT Thermal Imaging Safety System. Sensors. 2022; 22(21):8500. https://doi.org/10.3390/s22218500
Chicago/Turabian StyleFraga-Lamas, Paula, Daniel Barros, Sérgio Ivan Lopes, and Tiago M. Fernández-Caramés. 2022. "Mist and Edge Computing Cyber-Physical Human-Centered Systems for Industry 5.0: A Cost-Effective IoT Thermal Imaging Safety System" Sensors 22, no. 21: 8500. https://doi.org/10.3390/s22218500
APA StyleFraga-Lamas, P., Barros, D., Lopes, S. I., & Fernández-Caramés, T. M. (2022). Mist and Edge Computing Cyber-Physical Human-Centered Systems for Industry 5.0: A Cost-Effective IoT Thermal Imaging Safety System. Sensors, 22(21), 8500. https://doi.org/10.3390/s22218500









