Cybersecurity Enterprises Policies: A Comparative Study
Abstract
:1. Introduction
- RQ1: What are the aspects of cybersecurity that different enterprises have in common?
- RQ2: How are the cybersecurity aspects used among different enterprises?
2. Background and Related Work
2.1. Research Context
2.2. Literature Review
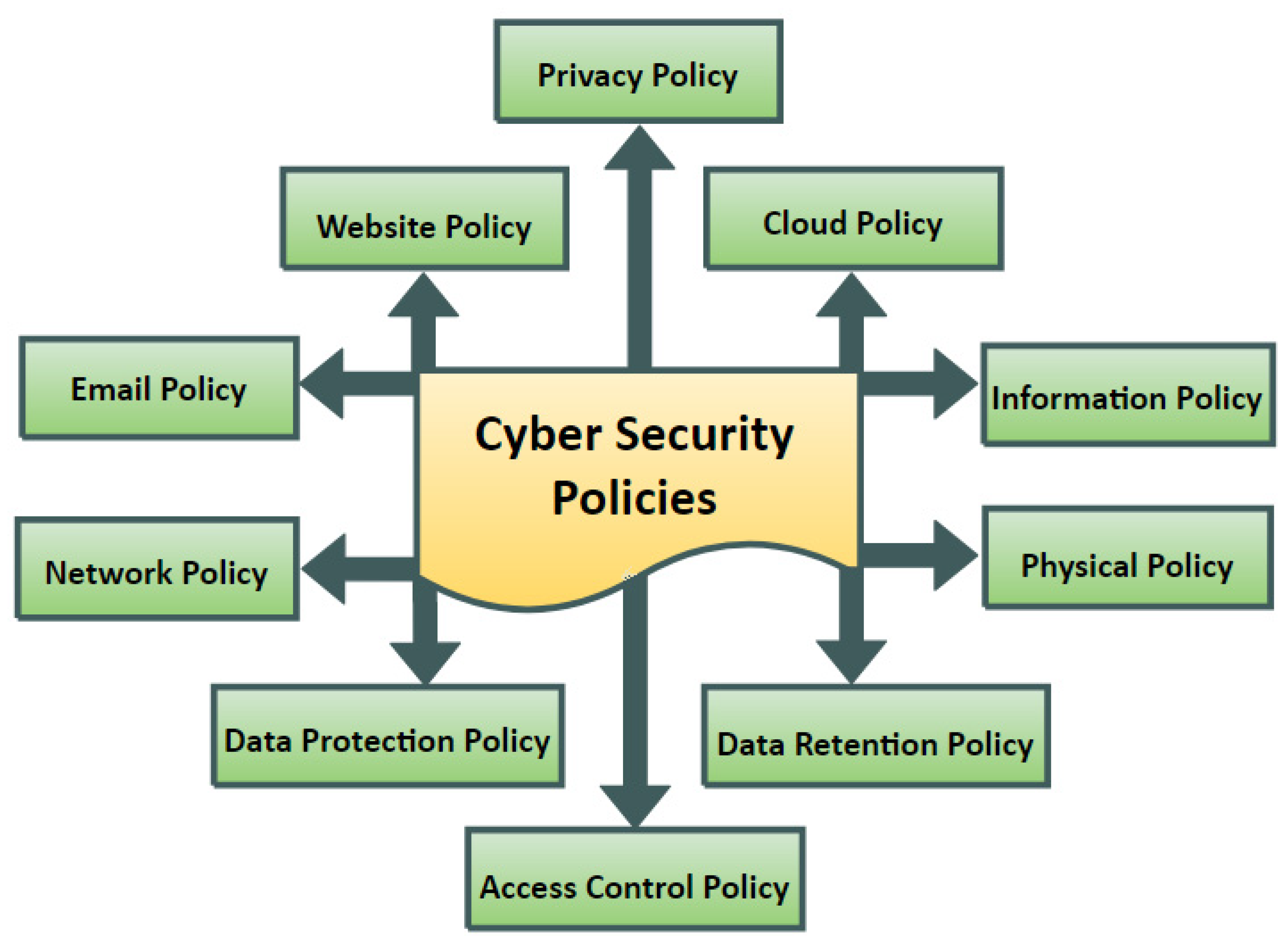
2.2.1. Cybersecurity Policies
2.2.2. Information Security Policies
3. Results
3.1. RQ1: Cybersecurity Policies Taxonomy
- Viruses: Viruses are computer programs or files that may move from one computer to another, infecting the target computers and allowing the infection to propagate further through the Internet;
- Worms: Worms, by design, are comparable to viruses and are classified as a viral subclass. The worm travels from computer to computer, but unlike viruses, it may travel without the need for human intervention;
- Trojan Horse: A Trojan is a software that looks to perform a helpful purpose but actually performs a secret function that poses a security risk;
- Spyware: Spyware is a type of harmful software that infiltrates computer systems to collect personal information from users. It usually comes through compromised computers or websites;
- Impersonation: In an impersonation attack, the attacker poses as a real user or server and provides false or harmful services to genuine users;
- Man-in-the-Middle: The attacker in a Man-in-the-Middle attack surreptitiously transmits and maybe changes messages between communicators without disclosing them to legitimate users;
- Denial of Service Attack (DoS): A DoS, also known as a distributed DoS (DDoS) attack, is a type of website assault in which an attacker floods victim’s computer with a huge amount of data packets. A DDoS occurs when attackers obtain unauthorized access to a large number of computers on the Internet, including the target systems.
3.1.1. Privacy Policy
3.1.2. Website Security Policy
3.1.3. Cloud Computing Security Policy
3.1.4. Email Security Policy
3.1.5. Physical Security Policy
3.1.6. Network Security Policy
3.1.7. Information Security Policy
3.1.8. Access Control Policy
3.1.9. Data-Retention Policy
3.1.10. Data-Protection Policy
3.2. RQ2: Comparison of Cybersecurity Policies among Selected Enterprises
3.2.1. Privacy Policy
3.2.2. Website Security Policy
3.2.3. Cloud Computing Security Policy
3.2.4. Email Security Policy
3.2.5. Physical Security Policy
3.2.6. Network Security Policy
3.2.7. Information Security Policy
3.2.8. Access Control Policy
3.2.9. Data-Retention Policy
3.2.10. Data-Protection Policy
4. Discussion
4.1. Implications
- It should incorporate CS policies appropriate to the industry. Each company should set up a CS office to oversee the security of their information and communication infrastructure, with primary responsibility for implementing CS policies in both technical and administrative elements of their operations, such as using IDs, firewalls, and cryptography;
- To track and oversee the execution of these security rules in each sector, all companies’ information and communication infrastructures require leadership and follow-up processes;
- The policies should be understood and approved by all workers. Each security strategy should be tailored to a specific group of people. A team should be formed within the organization to train employees on the company’s CS policies, with a focus on how to protect against spam and phishing emails;
- It should be written in accordance with the company’s culture, such as its educational, financial, and medical policies. Furthermore, CS rules should be adjusted in response to changes in the severity of threats over time;
- Network-related policies, data-protection-related policies, Cloud policies, and other policies will be used to create security policies;
- Effective, useful, consistent, relevant, useable, intelligible, legible, easy, and memorable CS policies are essential;
- Each security policy must meet a distinct requirement and must thus be maintained individually.
4.2. Limitations and Future Work
5. Conclusions
Author Contributions
Funding
Acknowledgments
Conflicts of Interest
Appendix A
| Reference | Significance | Security Policy |
|---|---|---|
| [70] | An overview of the issues and necessity for critical infrastructure protection, as well as the worldwide hazards that are associated with it | Privacy policy |
| [71] | Outline the current situation of privacy law in the USA and how it differs from other nations in terms of substantive safeguards | |
| [72] | Examining how the legislative systems in Europe and the USA aid in the protection of sensitive customer data on the Cloud | |
| [88] | Privacy and data-protection regulations | |
| [89] | End-to-end privacy and security control for collaborative access to healthcare | |
| [90] | Coordination between IT, business, and information security initiatives is addressed by an integrated framework | |
| [91] | The European Union (EU) General Data Privacy Regulation (GDPR) to address difficulties linked to personal data protection and to unify data protection across the EU | |
| [92] | Family Educational Rights and Private Act (FERPA) in the USA to protect students’ personal privacy while also making their educational data available to them | |
| [93] | Balance student’s privacy, anonymity, and big data in the social sciences | |
| [94] | Personalization of web pages for online users | |
| [96] | Law enforcement and trusted traveler programs are blurring the lines between privacy and security | |
| [38] | A conceptual model that blends the Unified Theory of Acceptance and Use of Technology (UTAUT) with risk perception to analyze online banking behavior intention and utilization | Website policy |
| [73] | Multidomain research of phishing-website detection technologies to calibrate the trust of automated security IT artifacts | |
| [75] | A model to enhance social media access control systems | |
| [99] | Explore the methods of security used by websites—how should we safeguard our data, and what is the best course of action? | |
| [100] | Delivers up-to-date research on customer sentiments, beliefs, thoughts, intentions, and attitudes toward effective customer interaction management | |
| [1] | A theoretical framework for cybersecurity management in Cloud computing based on a semantic review of the literature | Cloud policy |
| [76] | A model for dealing with the issues of data-intensive applications on mobile Cloud platforms | |
| [77] | Addresses data security problems and solutions in Cloud computing paradigms including delivery of services and deployment strategies | |
| [83] | A study model that merged aspects of information systems security policy | |
| [105] | Discuss why banks need to implement additional security measures in addition to the protection supplied by the cloud vendors | |
| [106] | Discussion of the use of cloud computing in different aviation and aerospace businesses, as well as the growing technology concerns | |
| [107] | Using a digital signature with the RSA encryption method to improve the data security of cloud computing | |
| [108] | A model to integrate Cloud computing and e-commerce as a service | |
| [103] | Examine the privacy and security concerns created by the usage of the Cloud in e-health | |
| [46] | Invention applications and the USA patent and trademark office’s success | Email policy |
| [78] | An overview of the law at USA schools and security challenges | |
| [79] | Using email user insights to guide organizational email management policies | |
| [110] | Evaluation of employee sensitivity to phishing attacks in US healthcare facilities | |
| [111] | Discussion of the best standard for email encryption for Health Information Technology for Economic and Clinical Health (HITECH) Act compliance to secure Protected Health Information (PHI) | |
| [112] | Study on the role of Russian “patriotic hackers” in the cyberattacks on Estonia and Georgia in 2007 and 2008, and how the expertise of surviving this attack aided | |
| [113] | A new approach for detecting fake customer reviews | |
| [114] | A machine-learning-based approach for detecting spam with high accuracy | |
| [5] | Comparison between the United Kingdom and France in terms of safeguarding key infrastructure from cyberattacks | Physical policy |
| [12] | An explanation of the distinctions between information security and cybersecurity | |
| [17] | Guidelines for information security standards, procedures, and policies | |
| [59] | Examining information security policies and objectives and offering insights on them through a rigorous theoretical perspective | |
| [80] | Explanation of physical security and information security, and why treating these two distinct forms of security in a unified manner is vital in today’s shifting security scenario | |
| [98] | A theoretical model that studies the link between security, perceived risks, and privacy, and how they relate to customers’ confidence in e-commerce | |
| [116] | Providing baseline information on the Data Protection Officer (DPO) in order to ensure data security and compliance | |
| [24] | A survey on privacy protection and data security for Cloud storage | Network policy |
| [51] | An overview of cybersecurity and networks that emphasizes their linkages and the complexity of current network design challenges | |
| [81] | An examination of the smart grid’s IoT-based security issues and potential remedies | |
| [120] | A review of security vulnerabilities in wireless medical sensor network-enabled healthcare applications | |
| [121] | Review of the Directive 2011/24/EU on patients’ rights in cross-border healthcare | |
| [122] | Discussion of the concept and development of The Interface to Network Security Functions (I2NSF) architecture, providing ways to improve its efficiency through integration with SDN | |
| [123] | Network security concepts and guidelines | |
| [124] | Review of risks and remedies in e-learning systems | |
| [125] | Outlines the primary variables that underlie the United States’ attempts to improve their cybercapacity | |
| [126] | Exploring an innovative approach to privacy protection and providing a persuasive collection of prospective legislative suggestions and practical answers | |
| [20] | A comprehensive framework that covers all areas of online learning design, creation, and planning | Information policy |
| [28] | A bibliometric investigation of the structure, quality, and quantity of e-commerce usage in emerging economies’ small- and medium-sized businesses | |
| [53] | Analysis of security flaws in the Automatic Dependent Surveillance-Broadcast (ADS-B) system and suggestions to improve security | |
| [57] | An overview of current and future challenges facing behavioral information security | |
| [82] | An overview of information security policy violations by employees in corporate contexts | |
| [128] | A model, using a Chaotic Map-Based Three-Factor Authenticated Key Agreement Scheme to Secure Telecare Medical Information Systems | |
| [129] | An overview of the electronic banking service, stressing several security concerns and proposing potential solutions | |
| [130] | An overview of remote working software professionals’ perceptions on the Information Security Policy (ISP) and the factors that should be considered in order to keep remote employees in the software sector productive | |
| [131] | Discussion about Saudi Arabia’s e-government vulnerabilities and the necessity for a defined information security system | |
| [43] | Evaluation of the Cloud security by defining specific security needs and solutions that overcome possible threats | Access control policy |
| [58] | A framework that enables academics to improve their efforts in the field of insider attacks | |
| [133] | A model to enhance privacy and access control in electronic health-record systems | |
| [134] | A strategy for obtaining safe banking services on multimedia large data in Cloud computing | |
| [135] | An overview of online banking communication and authentication security issues | |
| [136] | Elucidate the main security concerns that must be addressed while creating while using an e-learning system | |
| [47] | An overview of essential challenges of big data, such as technological difficulties, a lack of expertise, and epistemological and ontological disparities | Data-retention policy |
| [84] | An overview of privacy rights and regulation of personal data retention and erasure in European Union (EU) | |
| [85] | A book of the illegal and legal considerations of information security | |
| [137] | Two models for standardizing audit query meaning | |
| [138] | A model of HIPAA compliance regulations for clinician texting | |
| [139] | A policy framework to create an environment that allows for ethical data collection and use, and to address concerns of susceptibility | |
| [140] | An overview of European security laws in European passenger name recording system | |
| [141] | Discussion of the European proposal to share the personal information of all passengers | |
| [142] | An assessment of the transnational problems faced by government monitoring and business interference on the right to privacy | |
| [62] | A book on information technology crimes and regulations | Data-protection policy |
| [67] | An overview of the privacy problems of wearable personal health-monitoring equipment | |
| [86] | A book on e-commerce, IT, and data protection in Europe | |
| [145] | E-health, privacy, IoT, design, and corporate compliance framework | |
| [147] | An examination of the primary data-sharing tools utilized by police agencies and intelligence agencies in the EU and the US was conducted between 2001 to 2015 | |
| [148] | A review of the privacy of personal data in the Malaysian setting | |
| [4] | A review of the evolution of information security policy | Website and information policies |
| [10] | Evaluation of Cloud security concerns and designing preventions or remedies, depending on the source or cause of a security issue | Cloud and data-protection policies |
| [15] | A book on the development of information security in healthcare | Privacy, network, information, access control, data protection, and data-protection policies |
| [22] | A review of cybersecurity metrics and their applications in e-learning systems | Information and access control policies |
| [25] | An investigation into the ethical concerns surrounding the aviation industry in Indonesia | Physical and access control policies |
| [37] | Evaluation of the access controls applied on IoT, including the adoption of access controls and the challenges of access control techniques | Network and access control policies |
| [42] | An assessment of Cloud computing security and privacy, as well as a proposal for a framework of possible solutions | |
| [45] | An overview of the European Union’s General Data Protection Regulation (GDPR) | Privacy, website, and data-protection policies |
| [74] | Evaluation of security design methods and their qualities, we used a hybrid technique called Fuzzy AHP-TOPSIS (Analytic Hierarchy Process-Technique for Order Preference by Similarity Ideal Solution) | Website and network policies |
| [95] | Examining the background and future possibilities of body scanners vs. data protection and privacy via the lenses of challenges, legal tools, and potential remedies | Privacy and data-protection policies |
| [158] | A review of how small- and medium-sized businesses manage cybersecurity risks | Website, email, access control, data-retention policies |
| [102] | A review of e-commerce security challenges and solutions | Cloud, network, information, access control, physical, and data-retention policies |
| [104] | A book of CompTIA Advanced Security Practitioner (CASP) certificate guidelines | Cloud and email policies |
| [115] | Analysis of e-commerce and mobile commerce (M-Commerce) security issues and solutions | Email and physical policies |
| [117] | A book on public aviation law that covers international safety requirements, safety rules, and security regulations, among other aviation topics | Physical and information policies |
References
- Tissir, N.; El Kafhali, S.; Aboutabit, N. Cybersecurity management in cloud computing: Semantic literature review and conceptual framework proposal. J. Reliab. Intell. Environ. 2021, 7, 69–84. [Google Scholar] [CrossRef]
- Senol, M.; Karacuha, E. Creating and Implementing an Effective and Deterrent National Cyber Security Strategy. J. Eng. 2020, 2020, 5267564. [Google Scholar] [CrossRef]
- Haddad, C.; Binder, C. Governing through cybersecurity: National policy strategies, globalized (in-) security and sociotechnical visions of the digital society. Osterr. Z. Für Soziol. 2019, 44, 115–134. [Google Scholar] [CrossRef] [Green Version]
- Paananen, H.; Lapke, M.; Siponen, M. State of the art in information security policy development. Comput. Secur. 2020, 88, 101608. [Google Scholar] [CrossRef]
- Weiss, M.; Biermann, F. Cyberspace and the protection of critical national infrastructure. J. Econ. Policy Reform 2021, 1–18. [Google Scholar] [CrossRef]
- Hatcher, W.; Meares, W.L.; Heslen, J. The cybersecurity of municipalities in the United States: An exploratory survey of policies and practices. J. Cyber Policy 2020, 5, 302–325. [Google Scholar] [CrossRef]
- Alzoubi, Y.I.; Al-Ahmad, A.; Jaradat, A. Fog computing security and privacy issues, open challenges, and blockchain solution: An overview. Int. J. Electr. Comput. Eng. 2021, 11, 5081–5088. [Google Scholar] [CrossRef]
- Alotaibi, M.; Furnell, S.; Clarke, N. Information security policies: A review of challenges and influencing factors. In Proceedings of the 11th International Conference for Internet Technology and Secured Transactions (ICITST), Barcelona, Spain, 5–7 December 2016; pp. 352–358. [Google Scholar]
- Knapp, K.J.; Morris, R.F., Jr.; Marshall, T.E.; Byrd, T.A. Information security policy: An organizational-level process model. Comput. Secur. 2009, 28, 493–508. [Google Scholar] [CrossRef]
- Mthunzi, S.N.; Benkhelifa, E.; Bosakowski, T.; Guegan, C.G.; Barhamgi, M. Cloud computing security taxonomy: From an atomistic to a holistic view. Future Gener. Comput. Syst. 2020, 107, 620–644. [Google Scholar] [CrossRef]
- Tchernykh, A.; Schwiegelsohn, U.; Talbi, E.-G.; Babenko, M. Towards understanding uncertainty in cloud computing with risks of confidentiality, integrity, and availability. J. Comput. Sci. 2019, 36, 100581. [Google Scholar] [CrossRef]
- Von Solms, R.; Van Niekerk, J. From information security to cyber security. Comput. Secur. 2013, 38, 97–102. [Google Scholar] [CrossRef]
- Barr, J.R.; D’Auria, D.; Persia, F. Telemedicine, Homecare in the Era of COVID-19 & Beyond. In Proceedings of the Third International Conference on Artificial Intelligence for Industries (AI4I), Irvine, CA, USA, 21–23 September 2020; pp. 48–51. [Google Scholar]
- Granja, C.; Janssen, W.; Johansen, M.A. Factors determining the success and failure of eHealth interventions: Systematic review of the literature. J. Med. Internet Res. 2018, 20, e10235. [Google Scholar] [CrossRef] [Green Version]
- Herzig, T.; Walsh, T. Implementing Information Security in Healthcare: Building a Security Program; CRC Press: Boca Raton, FL, USA, 2020. [Google Scholar]
- Alzoubi, Y.I.; Osmanaj, V.H.; Jaradat, A.; Al-Ahmad, A. Fog computing security and privacy for the Internet of Thing applications: State-of-the-art. Secur. Priv. 2021, 4, e145. [Google Scholar] [CrossRef]
- Peltier, T.R. Information Security Policies, Procedures, and Standards: Guidelines for Effective Information Security Management; CRC Press: Boca Raton, FL, USA, 2016. [Google Scholar]
- AlJaafreh, A.; Al-Adaileh, R.; Gill, A.; Al-Ani, A.; Alzoubi, Y. A review of literature of initial trust in e-services: The case of internet banking services in Jordanian context. J. Electron. Bank. Syst. 2014, 2014, 690673. [Google Scholar]
- Auta, E.M. E-banking in developing economy: Empirical evidence from Nigeria. J. Appl. Quant. Methods 2010, 5, 212–222. [Google Scholar]
- Crane, B.E. Online Teaching and Learning: A Practical Guide for Librarians; Rowman & Littlefield: Lanham, MD, USA, 2016; Volume 29. [Google Scholar]
- Herrera, A.V.; Ron, M.; Rabadão, C. National cyber-security policies oriented to BYOD (bring your own device): Systematic review. In Proceedings of the 2017 12th Iberian Conference on Information Systems and Technologies (CISTI), Lisbon, Portugal, 21–24 June 2017; pp. 644–648. [Google Scholar]
- Bandara, I.; Ioras, F.; Maher, K. Cyber security concerns in e-learning education. In Proceedings of the ICERI2014 Conference, IATED, Seville, Spain, 17–19 November 2014; pp. 728–734. [Google Scholar]
- Buja, A.G. Cyber Security Featuresfor National E-Learning Policy. Turk. J. Comput. Math. Educ. (TURCOMAT) 2021, 12, 1729–1735. [Google Scholar] [CrossRef]
- Yang, P.; Xiong, N.; Ren, J. Data security and privacy protection for cloud storage: A survey. IEEE Access 2020, 8, 131723–131740. [Google Scholar] [CrossRef]
- Kania, D.D. The Ethical Issues of Aviation Business in Indonesia. J. Manaj. Transp. Logist. 2018, 5, 1–10. [Google Scholar]
- Wang, H.; He, W. A reservation-based smart parking system. In Proceedings of the 2011 IEEE Conference on Computer Communications Workshops (INFOCOM WKSHPS), Shanghai, China, 10–15 April 2011; pp. 690–695. [Google Scholar]
- Chukwu, M.A.; Idoko, E.C. Inhibitors of Electronic Banking Platforms’ Usage Intention in Deposit Money Banks: Perspectives of Elderly Customers in Developing Economy. Sch. Bull. 2021, 7, 134–145. [Google Scholar]
- Villa, E.; Ruiz, L.; Valencia, A.; Picón, E. Electronic commerce: Factors involved in its adoption from a bibliometric analysis. J. Theor. Appl. Electron. Commer. Res. 2018, 13, 39–70. [Google Scholar] [CrossRef] [Green Version]
- CPA Practice Advisor. Digital Payments to Hit $6.6 Trillion in 2021, a 40% Jump in Two Years|CPA Practice Advisor. 2021. Available online: https://www.cpapracticeadvisor.com/accounting-audit/news/21208440/digital-payments-to-hit-66-trillion-in-2021-a-40-jump-in-two-years (accessed on 20 October 2021).
- Walton, S.; Wheeler, P.R.; Zhang, Y.; Zhao, X. An Integrative Review and Analysis of Cybersecurity Research: Current State and Future Directions. J. Inf. Syst. 2021, 35, 155–186. [Google Scholar] [CrossRef]
- London, R.W. Comparative Data Protection and Security: A Critical Evaluation Of legal Standards. Doctoral Dissertation, University of South Africa, Pretoria, South Africa, 2014. [Google Scholar]
- Yoo, R. An Expected Harm Approach to Compensating Consumers for Unauthorized Information Disclosures. Richmond J. Law Technol. 2012, 19, 1. [Google Scholar]
- Liu, J.; Xiao, Y.; Chen, C.P. Authentication and access control in the internet of things. In Proceedings of the 32nd International Conference on Distributed Computing Systems Workshops, Macau, China, 18–21 June 2012; pp. 588–592. [Google Scholar]
- Persadha, P.; Waskita, A.; Yazid, S. Comparative study of cyber security policies among malaysia, australia, indonesia: A responsibility perspective. In Proceedings of the Fourth International Conference on Cyber Security, Cyber Warfare, and Digital Forensic (CyberSec), Jakarta, Indonesia, 29–31 October 2015; pp. 146–150. [Google Scholar]
- Saiedian, H.; Broyle, D. Security vulnerabilities in the same-origin policy: Implications and alternatives. Computer 2011, 44, 29–36. [Google Scholar] [CrossRef]
- Patil, K.; Vyas, T.; Braun, F.; Goodwin, M.; Liang, Z. Poster: UserCSP-user specified content security policies. In Proceedings of the Symposium on Usable Privacy and Security, Newcastle, UK, 24–26 July 2013; pp. 1–2. [Google Scholar]
- Qiu, J.; Tian, Z.; Du, C.; Zuo, Q.; Su, S.; Fang, B. A survey on access control in the age of internet of things. IEEE Internet Things J. 2020, 7, 4682–4696. [Google Scholar] [CrossRef]
- Martins, C.; Oliveira, T.; Popovič, A. Understanding the Internet banking adoption: A unified theory of acceptance and use of technology and perceived risk application. Int. J. Inf. Manag. 2014, 34, 1–13. [Google Scholar] [CrossRef]
- Ibrahim, H.; Karabatak, S.; Abdullahi, A.A. A Study on Cybersecurity Challenges in E-learning and Database Management System. In Proceedings of the 2020 8th International Symposium on Digital Forensics and Security (ISDFS), Beirut, Lebanon, 1–2 June 2020; pp. 1–5. [Google Scholar]
- Abomhara, M.; Køien, G.M. Cyber security and the internet of things: Vulnerabilities, threats, intruders and attacks. J. Cyber Secur. Mobil. 2015, 4, 65–88. [Google Scholar] [CrossRef]
- Lee, I. Internet of Things (IoT) cybersecurity: Literature review and IoT cyber risk management. Future Internet 2020, 12, 157. [Google Scholar] [CrossRef]
- Sun, P. Security and privacy protection in cloud computing: Discussions and challenges. J. Netw. Comput. Appl. 2020, 160, 102642. [Google Scholar] [CrossRef]
- Zissis, D.; Lekkas, D. Addressing cloud computing security issues. Future Gener. Comput. Syst. 2012, 28, 583–592. [Google Scholar] [CrossRef]
- Subashini, S.; Kavitha, V. A survey on security issues in service delivery models of cloud computing. J. Netw. Comput. Appl. 2011, 34, 1–11. [Google Scholar] [CrossRef]
- Laurer, M.; Seidl, T. Regulating the European Data-Driven Economy: A Case Study on the General Data Protection Regulation. Policy Internet 2021, 13, 257–277. [Google Scholar] [CrossRef]
- Cotropia, C.A.; Quillen, C.D., Jr.; Webster, O.H. Patent applications and the performance of the US Patent and Trademark Office. Fed. Circuit Bar J. 2013, 23, 179. [Google Scholar]
- Daniel, B.K. Big Data and data science: A critical review of issues for educational research. Br. J. Educ. Technol. 2019, 50, 101–113. [Google Scholar] [CrossRef] [Green Version]
- Kalpana, P.; Singaraju, S. Data security in cloud computing using RSA algorithm. Int. J. Res. Comput. Commun. Technol. 2012, 1, 2278–5841. [Google Scholar]
- Goyal, V.; Pandey, U.; Batra, S. Mobile banking in India: Practices, challenges and security issues. Int. J. Adv. Trends Comput. Sci. Eng. 2012, 1, 56–66. [Google Scholar]
- Yildirim, E.Y.; Akalp, G.; Aytac, S.; Bayram, N. Factors influencing information security management in small-and medium-sized enterprises: A case study from Turkey. Int. J. Inf. Manag. 2011, 31, 360–365. [Google Scholar] [CrossRef]
- Wu, C.-H.J.; Irwin, J.D. Introduction to Computer Networks and Cybersecurity; CRC Press: Boca Raton, FL, USA, 2016. [Google Scholar]
- Rajaretnam, T. A review of data governance regulation, practices and cyber security strategies for businesses: An Australian perspective. Int. J. Technol. Manag. Inf. Syst. 2020, 2, 1–17. [Google Scholar]
- McCallie, D.; Butts, J.; Mills, R. Security analysis of the ADS-B implementation in the next generation air transportation system. Int. J. Crit. Infrastruct. Prot. 2011, 4, 78–87. [Google Scholar] [CrossRef]
- Sampigethaya, K.; Poovendran, R.; Shetty, S.; Davis, T.; Royalty, C. Future e-enabled aircraft communications and security: The next 20 years and beyond. Proc. IEEE 2011, 99, 2040–2055. [Google Scholar] [CrossRef]
- Panda, M. Security in wireless sensor networks using cryptographic techniques. Am. J. Eng. Res. 2014, 3, 50–56. [Google Scholar]
- Subramanian, D.V.; Kumar, K.P. Fuzzy based modeling for an effective it security policy management. In Proceedings of the 2016 SAI Computing Conference (SAI), London, UK, 13–15 July 2016; pp. 173–181. [Google Scholar]
- Crossler, R.E.; Johnston, A.C.; Lowry, P.B.; Hu, Q.; Warkentin, M.; Baskerville, R. Future directions for behavioral information security research. Comput. Secur. 2013, 32, 90–101. [Google Scholar] [CrossRef]
- Alsowail, R.A.; Al-Shehari, T. Empirical detection techniques of insider threat incidents. IEEE Access 2020, 8, 78385–78402. [Google Scholar] [CrossRef]
- Stahl, B.C.; Doherty, N.F.; Shaw, M. Information security policies in the UK healthcare sector: A critical evaluation. Inf. Syst. J. 2012, 22, 77–94. [Google Scholar] [CrossRef]
- Susanto, H.; Almunawar, M. Information Security Awareness: A Marketing Tools for Corporate’s Business Processes. Comput. Sci. J. 2012, 12. [Google Scholar]
- Bilbao-Osorio, B.; Dutta, S.; Lanvin, B. The Global Information Technology Report 2014: Rewards and Risks of Big Data; Johnson Cornell University: Geneva, Switzerland, 2014. [Google Scholar]
- Lloyd, I. Information Technology Law; Oxford University Press: Oxford, UK, 2020. [Google Scholar]
- Rani, R.; Kumar, N.; Khurana, M.; Kumar, A.; Barnawi, A. Storage as a service in fog computing: A systematic review. J. Syst. Archit. 2021, 116, 102033. [Google Scholar] [CrossRef]
- AlAhmad, A.S.; Kahtan, H.; Alzoubi, Y.I.; Ali, O.; Jaradat, A. Mobile cloud computing models security issues: A systematic review. J. Netw. Comput. Appl. 2021, 190, 103152. [Google Scholar] [CrossRef]
- Alzoubi, Y.I.; Al-Ahmad, A.; Jaradat, A.; Osmanaj, V.H. Fog computing architecture, benefits, security, and privacy, for the internet of thing applications: An overview. J. Theor. Appl. Inf. Technol. 2021, 99, 436–451. [Google Scholar]
- Li, R.; Zhao, Z.; Sun, Q.; Chih-Lin, I.; Yang, C.; Chen, X.; Zhao, M.; Zhang, H. Deep reinforcement learning for resource management in network slicing. IEEE Access 2018, 6, 74429–74441. [Google Scholar] [CrossRef]
- Paul, G.; Irvine, J. Privacy implications of wearable health devices. In Proceedings of the 7th International Conference on Security of Information and Networks, Glasgow UK, 9–11 September 2014; pp. 117–121. [Google Scholar]
- Warkentin, M.; Johnston, A.C.; Shropshire, J. The influence of the informal social learning environment on information privacy policy compliance efficacy and intention. Eur. J. Inf. Syst. 2011, 20, 267–284. [Google Scholar] [CrossRef]
- Pearson, S. Privacy, security and trust in cloud computing. In Privacy and Security for Cloud Computing. Computer Communications and Networks; Pearson, S., Yee, G., Eds.; Springer: London, UK, 2013; pp. 3–42. [Google Scholar] [CrossRef]
- Roshanaei, M. Resilience at the Core: Critical Infrastructure Protection Challenges, Priorities and Cybersecurity Assessment Strategies. J. Comput. Commun. 2021, 9, 80–102. [Google Scholar] [CrossRef]
- Brookman, J. Protecting privacy in an era of weakening regulation. Harv. Law Policy Rev. 2015, 9, 355. [Google Scholar]
- King, N.J.; Raja, V. Protecting the privacy and security of sensitive customer data in the cloud. Comput. Law Secur. Rev. 2012, 28, 308–319. [Google Scholar] [CrossRef]
- Chen, Y.; Zahedi, F.M.; Abbasi, A.; Dobolyi, D. Trust calibration of automated security IT artifacts: A multi-domain study of phishing-website detection tools. Inf. Manag. 2021, 58, 103394. [Google Scholar] [CrossRef]
- Alenezi, M.; Agrawal, A.; Kumar, R.; Khan, R.A. Evaluating performance of Web application security through a fuzzy based hybrid multi-criteria decision-making approach: Design tactics perspective. IEEE Access 2020, 8, 25543–25556. [Google Scholar] [CrossRef]
- Carminati, B.; Ferrari, E.; Heatherly, R.; Kantarcioglu, M.; Thuraisingham, B. Semantic web-based social network access control. Comput. Secur. 2011, 30, 108–115. [Google Scholar] [CrossRef]
- Alkhalaileh, M.; Calheiros, R.N.; Nguyen, Q.V.; Javadi, B. Data-intensive application scheduling on mobile edge cloud computing. J. Netw. Comput. Appl. 2020, 167, 102735. [Google Scholar] [CrossRef]
- Kumar, P.R.; Raj, P.H.; Jelciana, P. Exploring data security issues and solutions in cloud computing. Procedia Comput. Sci. 2018, 125, 691–697. [Google Scholar] [CrossRef]
- Alexander, K.; Alexander, M.D.; Alexander, M.D. American Public School Law; West/Thomson Learning: Belmont, CA, USA, 2001. [Google Scholar]
- Ramsay, J.; Renaud, K. Using insights from email users to inform organisational email management policy. Behav. Inf. Technol. 2012, 31, 587–603. [Google Scholar] [CrossRef]
- Crowell, W.P.; Contos, B.T.; DeRodeff, C.; Dunkel, D. Physical and Logical Security Convergence: Powered by Enterprise Security Management; Syngress: Burlington, NJ, USA, 2011. [Google Scholar]
- Gunduz, M.Z.; Das, R. Cyber-security on smart grid: Threats and potential solutions. Comput. Netw. 2020, 169, 107094. [Google Scholar] [CrossRef]
- Hu, Q.; Xu, Z.; Dinev, T.; Ling, H. Does deterrence work in reducing information security policy abuse by employees? Commun. ACM 2011, 54, 54–60. [Google Scholar] [CrossRef] [Green Version]
- Ifinedo, P. Understanding information systems security policy compliance: An integration of the theory of planned behavior and the protection motivation theory. Comput. Secur. 2012, 31, 83–95. [Google Scholar] [CrossRef]
- Tsesis, A. Data Subjects’ Privacy Rights: Regulation of Personal Data Retention and Erasure. Univ. Colo. Law Rev. 2019, 90, 593–629. [Google Scholar] [CrossRef] [Green Version]
- Grama, J.L. Legal Issues in Information Security: Print Bundle; Jones & Bartlett Publishers: Burlington, MA, USA, 2014. [Google Scholar]
- Gijrath, S.; van der Hof, S.; Lodder, A.R.; Zwenne, G.-J. Concise European Data Protection, E-Commerce and IT Law; Kluwer Law International BV: Alphen aan den Rijn, The Netherlands, 2018. [Google Scholar]
- Zhang, K.; Shao, S.; Fan, S. Market integration and environmental quality: Evidence from the Yangtze river delta region of China. J. Environ. Manag. 2020, 261, 110208. [Google Scholar] [CrossRef]
- Jay, R.P. Data Protection & Privacy; Law Business Research Ltd.: London, UK, 2015. [Google Scholar]
- Gerdes, M.; Fensli, R. End-to-end security and privacy protection for co-operative access to health and care data in a telehealth trial system for remote supervision of COPD-Patients. In Proceedings of the 13th Scandinavien Conference on Health Informatics, Tromsø, Norway, 15–17 June 2015; pp. 25–32. [Google Scholar]
- Goldman, J.E.; Ahuja, S. Integration of COBIT, balanced scorecard and SSE-CMM as an organizational & strategic information security management (ISM) framework. In ICT Ethics and Security in the 21st Century: New Developments and Applications; IGI Global: Hershey, PA, USA, 2011; pp. 277–309. [Google Scholar]
- Tikkinen-Piri, C.; Rohunen, A.; Markkula, J. EU General Data Protection Regulation: Changes and implications for personal data collecting companies. Comput. Law Secur. Rev. 2018, 34, 134–153. [Google Scholar] [CrossRef] [Green Version]
- Elliott, T.L.; Fatemi, D.; Wasan, S. Student privacy rights—History, Owasso, and FERPA. J. High. Educ. Theory Pract. 2014, 14, 34–47. [Google Scholar]
- Daries, J.P.; Reich, J.; Waldo, J.; Young, E.M.; Whittinghill, J.; Ho, A.D.; Seaton, D.T.; Chuang, I. Privacy, anonymity, and big data in the social sciences. Commun. ACM 2014, 57, 56–63. [Google Scholar] [CrossRef] [Green Version]
- Kobsa, A. Privacy-enhanced personalization. Commun. ACM 2007, 50, 24–33. [Google Scholar] [CrossRef]
- Mironenko, O. Body scanners versus privacy and data protection. Comput. Law Secur. Rev. 2011, 27, 232–244. [Google Scholar] [CrossRef]
- Leese, M. Blurring the dimensions of privacy? Law enforcement and trusted traveler programs. Comput. Law Secur. Rev. 2013, 29, 480–490. [Google Scholar] [CrossRef]
- Ike, M.; Sarac, K. PPEP: A deployable privacy preserving E-commerce protocol for electronic goods. In Proceedings of the 6th International Conference on Communication and Network Security, Singapore, 26–29 November 2016; pp. 104–112. [Google Scholar]
- Neama, G.; Alaskar, R.; Alkandari, M. Privacy, security, risk, and trust concerns in e-commerce. In Proceedings of the 17th International Conference on Distributed Computing and Networking, Singapore, 4–7 January 2016; pp. 1–6. [Google Scholar]
- Muhammad, N.B.; Kandil, A. Information protection of end users on the web: Privacy issues and measures. Int. J. Inf. Comput. Secur. 2021, 15, 357–372. [Google Scholar] [CrossRef]
- Suki, N.M. Handbook of Research on Leveraging Consumer Psychology for Effective Customer Engagement; IGI Global: Hershey, PA, USA, 2016. [Google Scholar]
- Alshammari, S.T.; Albeshri, A.; Alsubhi, K. Integrating a High-Reliability Multicriteria Trust Evaluation Model with Task Role-Based Access Control for Cloud Services. Symmetry 2021, 13, 492. [Google Scholar] [CrossRef]
- Badotra, S.; Sundas, A. A systematic review on security of E-commerce systems. Int. J. Appl. Sci. Eng. 2021, 18, 1–19. [Google Scholar]
- Lynda, K.; Saliha, O.-K.; Nadjia, B. Data security and privacy in e-health cloud: Comparative study. In Proceedings of the International Conference on Intelligent Information Processing, Security and Advanced Communication, Batna, Algeria, 23–25 November 2015; pp. 1–6. [Google Scholar]
- Abernathy, R.; McMillan, T. CompTIA Advanced Security Practitioner (CASP) CAS-003 Cert Guide: CompTIA Advanced Secur_o2; Pearson IT Certification: Indianapolis, IN, USA, 2018. [Google Scholar]
- Auxilia, M.; Raja, K. Knowledge Based Security Model for Banking in Cloud. In Proceedings of the International Conference on Informatics and Analytics, Pondicherry, India, 25–26 August 2016; pp. 1–6. [Google Scholar]
- Vagdevi, P.; Guruprasad, H. A study on cloud computing in aviation and aerospace. Int. J. Comput. Sci. Eng. Technol. 2015, 6, 94–98. [Google Scholar]
- Somani, U.; Lakhani, K.; Mundra, M. Implementing digital signature with RSA encryption algorithm to enhance the Data Security of cloud in Cloud Computing. In Proceedings of the 1st International Conference on Parallel, Distributed and Grid Computing (PDGC), Solan, India, 28–30 October 2010; pp. 211–216. [Google Scholar]
- Talib, A.M.; Alomary, F.O. Cloud computing based E-Commerce as a service model: Impacts and recommendations. In Proceedings of the International Conference on Internet of things and Cloud Computing, Cambridge, UK, 22 March 2016; pp. 1–7. [Google Scholar]
- Süzen, A.A. A Risk-Assessment of Cyber Attacks and Defense Strategies in Industry 4.0 Ecosystem. Int. J. Comput. Netw. Inf. Secur. 2020, 12, 1–12. [Google Scholar] [CrossRef]
- Gordon, W.J.; Wright, A.; Aiyagari, R.; Corbo, L.; Glynn, R.J.; Kadakia, J.; Kufahl, J.; Mazzone, C.; Noga, J.; Parkulo, M. Assessment of employee susceptibility to phishing attacks at US health care institutions. JAMA Netw. Open 2019, 2, e190393. [Google Scholar] [CrossRef]
- Gardazi, S.U.; Shahid, A.A. Email system architecture for HITECH compliance. In Proceedings of the 2nd International Conference on Software Engineering and Data Mining, Chengdu, China, 23–25 June 2010; pp. 561–570. [Google Scholar]
- Lysenko, V.; Endicott-Popovsky, B. Hackers at the state service: Cyberwars against Estonia and Georgia. In Proceedings of the 7th International Conference on Information Warfare and Security (ICIW), Seattle, WA, USA, 22–23 March 2011; p. 404. [Google Scholar]
- Bajaj, S.; Garg, N.; Singh, S.K. A novel user-based spam review detection. Procedia Comput. Sci. 2017, 122, 1009–1015. [Google Scholar] [CrossRef]
- GuangJun, L.; Nazir, S.; Khan, H.U.; Haq, A.U. Spam detection approach for secure mobile message communication using machine learning algorithms. Secur. Commun. Netw. 2020, 2020, 8873639. [Google Scholar] [CrossRef]
- Niranjanamurthy, M.; Kavyashree, N.; Jagannath, S.; Chahar, D. Analysis of e-commerce and m-commerce: Advantages, limitations and security issues. Int. J. Adv. Res. Comput. Commun. Eng. 2013, 2, 2360–2370. [Google Scholar]
- Recio, M. Data protection officer: The key figure to ensure data protection and accountability. Eur. Data Prot. Law Rev. 2017, 3, 114. [Google Scholar] [CrossRef]
- Dempsey, P.S.; Jakhu, R.S. Routledge Handbook of Public Aviation Law; Routledge: London, UK, 2016. [Google Scholar]
- Ter, K.L. Singapor’s cybersecurity strategy. Comput. Law Secur. Rev. 2018, 34, 924–927. [Google Scholar] [CrossRef]
- Montasari, R.; Hosseinian-Far, A.; Hill, R. Policies, innovative self-adaptive techniques and understanding psychology of cybersecurity to counter adversarial attacks in network and cyber environments. In Cyber Criminology. Advanced Sciences and Technologies for Security Applications; Jahankhani, H., Ed.; Springer: Cham, Switzerland, 2018; pp. 71–93. [Google Scholar] [CrossRef]
- Kumar, P.; Lee, H.-J. Security issues in healthcare applications using wireless medical sensor networks: A survey. Sensors 2012, 12, 55–91. [Google Scholar] [CrossRef] [PubMed] [Green Version]
- Kierkegaard, P. Electronic health record: Wiring Europe’s healthcare. Comput. Law Secur. Rev. 2011, 27, 503–515. [Google Scholar] [CrossRef]
- Hyun, S.; Kim, J.; Kim, H.; Jeong, J.; Hares, S.; Dunbar, L.; Farrel, A. Interface to network security functions for cloud-based security services. IEEE Commun. Mag. 2018, 56, 171–178. [Google Scholar] [CrossRef]
- Cobb, C. Network Security for Dummies; John Wiley & Sons: Hoboken, NJ, USA, 2011. [Google Scholar]
- Barik, N.; Karforma, S. Risks and remedies in e-learning system. Int. J. Netw. Secur. Its Appl. 2012, 4, 51–59. [Google Scholar] [CrossRef]
- Calderaro, A.; Craig, A.J. Transnational governance of cybersecurity: Policy challenges and global inequalities in cyber capacity building. Third World Q. 2020, 41, 917–938. [Google Scholar] [CrossRef]
- Klitou, D. Privacy-invading technologies and privacy by design. Inf. Technol. Law Ser. 2014, 25, 27–45. [Google Scholar]
- Wood, S.; Raj, R. The impact of security scanners at airports and ethnic minority travellers’ experience. Secur. J. 2021, 34, 278–298. [Google Scholar] [CrossRef]
- Zhang, L.; Zhu, S.; Tang, S. Privacy protection for telecare medicine information systems using a chaotic map-based three-factor authenticated key agreement scheme. IEEE J. Biomed. Health Inform. 2016, 21, 465–475. [Google Scholar] [CrossRef] [PubMed]
- Chaimaa, B.; Najib, E.; Rachid, H. E-banking Overview: Concepts, Challenges and Solutions. Wirel. Pers. Commun. 2021, 117, 1059–1078. [Google Scholar] [CrossRef]
- Sandamali, A.A.D. Effective Information Security Policies for Efficient Remote Working. Master Dissertation, University of Moratuwa, Moratuwa, Sri Lanka, 2019. [Google Scholar]
- Thakur, K.; Ali, M.L.; Gai, K.; Qiu, M. Information security policy for e-commerce in Saudi Arabia. In Proceedings of the 2nd International Conference on Big Data Security on Cloud (BigDataSecurity), IEEE International Conference on High Performance and Smart Computing (HPSC), and IEEE International Conference on Intelligent Data and Security (IDS), New York, NY, USA, 9–10 April 2016; pp. 187–190. [Google Scholar]
- Ulven, J.B.; Wangen, G. A Systematic Review of Cybersecurity Risks in Higher Education. Future Internet 2021, 13, 39. [Google Scholar] [CrossRef]
- Zhou, X.; Liu, J.; Liu, W.; Wu, Q. Anonymous role-based access control on e-health records. In Proceedings of the 11th ACM on Asia Conference on Computer and Communications Security, Xi’an, China, 30 May–3 June 2016; pp. 559–570. [Google Scholar]
- Li, Y.; Gai, K.; Ming, Z.; Zhao, H.; Qiu, M. Intercrossed access controls for secure financial services on multimedia big data in cloud systems. ACM Trans. Multimed. Comput. Commun. Appl. (TOMM) 2016, 12, 1–18. [Google Scholar] [CrossRef]
- Kiljan, S.; Simoens, K.; Cock, D.D.; Eekelen, M.V.; Vranken, H. A survey of authentication and communications security in online banking. ACM Comput. Surv. (CSUR) 2016, 49, 1–35. [Google Scholar] [CrossRef]
- Luminita, D.C. Information security in E-learning Platforms. Procedia-Soc. Behav. Sci. 2011, 15, 2689–2693. [Google Scholar] [CrossRef] [Green Version]
- Lu, W.; Miklau, G.; Immerman, N. Auditing a database under retention policies. VLDB J. 2013, 22, 203–228. [Google Scholar] [CrossRef]
- Greene, A.H. HIPAA compliance for clinician texting. J. AHIMA 2012, 83, 34–36. [Google Scholar] [PubMed]
- Prinsloo, P.; Slade, S. An evaluation of policy frameworks for addressing ethical considerations in learning analytics. In Proceedings of the Third International Conference on Learning Analytics and Knowledge, Leuven, Belgium, 8–13 April 2013; pp. 240–244. [Google Scholar]
- Bellanova, R.; Duez, D. A different view on the ‘making’of European security: The EU passenger name record system as a socio-technical assemblage. Eur. Foreign Aff. Rev. 2012, 17, 109–124. [Google Scholar]
- Brouwer, E. Ignoring Dissent and Legality. The EU’s Proposal to Share the Personal Information of All Passengers; CEPS Centre for European Policy Studies: Brussels, Belgium, 2011. [Google Scholar]
- Cole, D.; Fabbrini, F.; Schulhofer, S. Surveillance, Privacy and Trans-Atlantic Relations; Bloomsbury Publishing: London, UK, 2017. [Google Scholar]
- Szádeczky, T. Cybersecurity authorities and related policies in the EU and Hungary. Cent. East. Eur. Edem Egov Days 2018, 331, 287–299. [Google Scholar] [CrossRef]
- Goddard, M. The EU General Data Protection Regulation (GDPR): European regulation that has a global impact. Int. J. Mark. Res. 2017, 59, 703–705. [Google Scholar] [CrossRef]
- Malgieri, G. Data Protection and Privacy: (In) Visibilities and Infrastructures. Eur. Data Prot. Law Rev. 2017, 3, 426. [Google Scholar]
- Tamburri, D.A. Design principles for the General Data Protection Regulation (GDPR): A formal concept analysis and its evaluation. Inf. Syst. 2020, 91, 101469. [Google Scholar] [CrossRef]
- Casagran, C.B. Global Data Protection in the Field of Law Enforcement: An EU Perspective; Routledge: London, UK, 2016. [Google Scholar]
- Hamzah, M.A.; Ahmad, A.R.; Hussin, N.; Ibrahim, Z. Personal Data Privacy Protection: A Review on Malaysia‘s Cyber Security Policies. Int. J. Acad. Res. Bus. Soc. Sci. 2018, 8, 1475–1483. [Google Scholar] [CrossRef] [Green Version]
- Schwartz, P.M.; Solove, D.J. The PII problem: Privacy and a new concept of personally identifiable information. N. Y. Univ. Law Rev. 2011, 86, 1814–1894. [Google Scholar]
- Kaya, T.; Kahraman, C. A fuzzy approach to e-banking website quality assessment based on an integrated AHP-ELECTRE method. Technol. Econ. Dev. Econ. 2011, 17, 313–334. [Google Scholar] [CrossRef]
- Hartono, E.; Holsapple, C.W.; Kim, K.-Y.; Na, K.-S.; Simpson, J.T. Measuring perceived security in B2C electronic commerce website usage: A respecification and validation. Decis. Support Syst. 2014, 62, 11–21. [Google Scholar] [CrossRef]
- Baykara, M.; Gürel, Z.Z. Detection of phishing attacks. In Proceedings of the 6th International Symposium on Digital Forensic and Security (ISDFS), Antalya, Turkey, 22–25 March 2018; pp. 1–5. [Google Scholar]
- Blesi, M. Medical Assisting: Administrative and Clinical Competencies; Cengage Learning: Boston, MA, USA, 2016. [Google Scholar]
- Kigerl, A.C. Evaluation of the CAN SPAM ACT: Testing deterrence and other influences of e-mail spammer legal compliance over time. Soc. Sci. Comput. Rev. 2015, 33, 440–458. [Google Scholar] [CrossRef]
- Yusta, J.M.; Correa, G.J.; Lacal-Arántegui, R. Methodologies and applications for critical infrastructure protection: State-of-the-art. Energy Policy 2011, 39, 6100–6119. [Google Scholar] [CrossRef]
- Demchenko, Y.; Grosso, P.; De Laat, C.; Membrey, P. Addressing big data issues in scientific data infrastructure. In Proceedings of the 2013 International conference on collaboration technologies and systems (CTS), San Diego, CA, USA, 20–24 May 2013; pp. 48–55. [Google Scholar]
- Hasan, R.; Winslett, M. Efficient audit-based compliance for relational data retention. In Proceedings of the 6th ACM Symposium on Information, Computer and Communications Security, Hong Kong, China, 22–24 March 2011; pp. 238–248. [Google Scholar]
- Alahmari, A.; Duncan, B. Cybersecurity risk management in small and medium-sized enterprises: A systematic review of recent evidence. In Proceedings of the 2020 International Conference on Cyber Situational Awareness, Data Analytics and Assessment (CyberSA), Dublin, Ireland, 15–19 June 2020; pp. 1–5. [Google Scholar]
- Mohan, A.M.; Meskin, N.; Mehrjerdi, H. A comprehensive review of the cyber-attacks and cyber-security on load frequency control of power systems. Energies 2020, 13, 3860. [Google Scholar] [CrossRef]
- Ahmad, A.; Desouza, K.; Naseer, H.; Baskerville, R.L. How integration of security management and incident response enables organizational learning. J. Assoc. Inf. Sci. Technol. 2020, 71, 939–953. [Google Scholar] [CrossRef]
| Common Attribute | Healthcare | Finance | Education | Aviation | E-Commerce |
|---|---|---|---|---|---|
| Privacy policy | |||||
| Website policy | |||||
| Cloud computing policy | |||||
| Email policy | |||||
| Physical policy | |||||
| Network policy | |||||
| Information policy | |||||
| Access control policy | |||||
| Retention policy | |||||
| Data protection policy |
| Sector | Privacy Policy |
|---|---|
| Healthcare [15,71,88,89] |
|
| Finance [71,90,91] |
|
| Education [47,92,93] |
|
| Aviation [25,94,95,96] |
|
| E-commerce [28,86,88,97,98] |
|
| Sector | Website Security Policy |
|---|---|
| Healthcare [4,15] |
|
| Finance [42,99] |
|
| Education [47,74] |
|
| Aviation [74,100] |
|
| E-commerce [73,101] |
|
| Sector | Cloud Computing Security Policy |
|---|---|
| Healthcare [1,103] |
|
| Finance [1,104,105] |
|
| Education [10,83] |
|
| Aviation [106,107] |
|
| E-commerce [102,108] |
|
| Sector | Email Security Policy |
|---|---|
| Healthcare [110,111] |
|
| Finance [101,104,112] |
|
| Education [79,113] |
|
| Aviation [25,113,114] |
|
| E-commerce [102,115] |
|
| Sector | Physical Security Policy |
|---|---|
| Healthcare [59,116] |
|
| Finance [17,80] |
|
| Education [80,92] |
|
| Aviation [5,25,117] |
|
| E-commerce [52,98,115] |
|
| Sector | Network Security Policy |
|---|---|
| Healthcare [120,121] |
|
| Finance [74,122,123] |
|
| Education [15,124] |
|
| Aviation [37,125,126] |
|
| E-commerce [102,120] |
|
| Sector | Information Security Policy |
|---|---|
| Healthcare [15,128] |
|
| Finance [4,129,130] |
|
| Education [20,22] |
|
| Aviation [53,117] |
|
| E-commerce [28,102,131] |
|
| Sector | Access Control Policy |
|---|---|
| Healthcare [15,110,133] |
|
| Finance [37,42,134,135] |
|
| Education [22,37,136] |
|
| Aviation [25,58] |
|
| E-commerce [37,101,102] |
|
| Sector | Data-Retention Policy |
|---|---|
| Healthcare [15,137,138] |
|
| Finance [47,137] |
|
| Education [84,137,139] |
|
| Aviation [112,127,140,141,142] |
|
| E-commerce [84,101,102,137] |
|
| Sector | Data Protection Policy |
|---|---|
| Healthcare [15,121,145] |
|
| Finance [45,146] |
|
| Education [10,45,62] |
|
| Aviation [95,147] |
|
| E-commerce [52,86,148] |
|
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2022 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Mishra, A.; Alzoubi, Y.I.; Gill, A.Q.; Anwar, M.J. Cybersecurity Enterprises Policies: A Comparative Study. Sensors 2022, 22, 538. https://doi.org/10.3390/s22020538
Mishra A, Alzoubi YI, Gill AQ, Anwar MJ. Cybersecurity Enterprises Policies: A Comparative Study. Sensors. 2022; 22(2):538. https://doi.org/10.3390/s22020538
Chicago/Turabian StyleMishra, Alok, Yehia Ibrahim Alzoubi, Asif Qumer Gill, and Memoona Javeria Anwar. 2022. "Cybersecurity Enterprises Policies: A Comparative Study" Sensors 22, no. 2: 538. https://doi.org/10.3390/s22020538
APA StyleMishra, A., Alzoubi, Y. I., Gill, A. Q., & Anwar, M. J. (2022). Cybersecurity Enterprises Policies: A Comparative Study. Sensors, 22(2), 538. https://doi.org/10.3390/s22020538








