Real-Time Anomaly Detection for an ADMM-Based Optimal Transmission Frequency Management System for IoT Devices
Abstract
:1. Introduction
- 1.
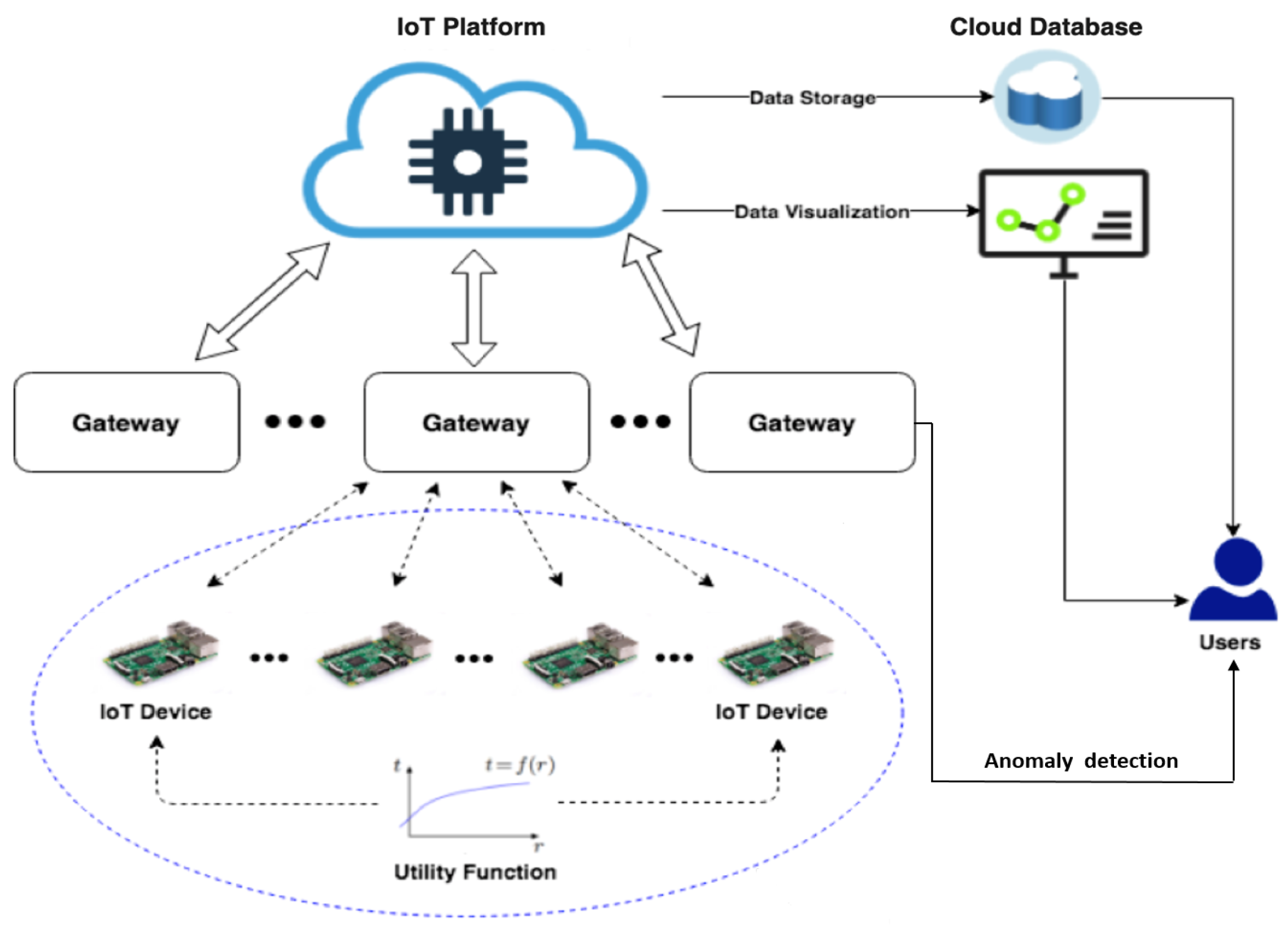
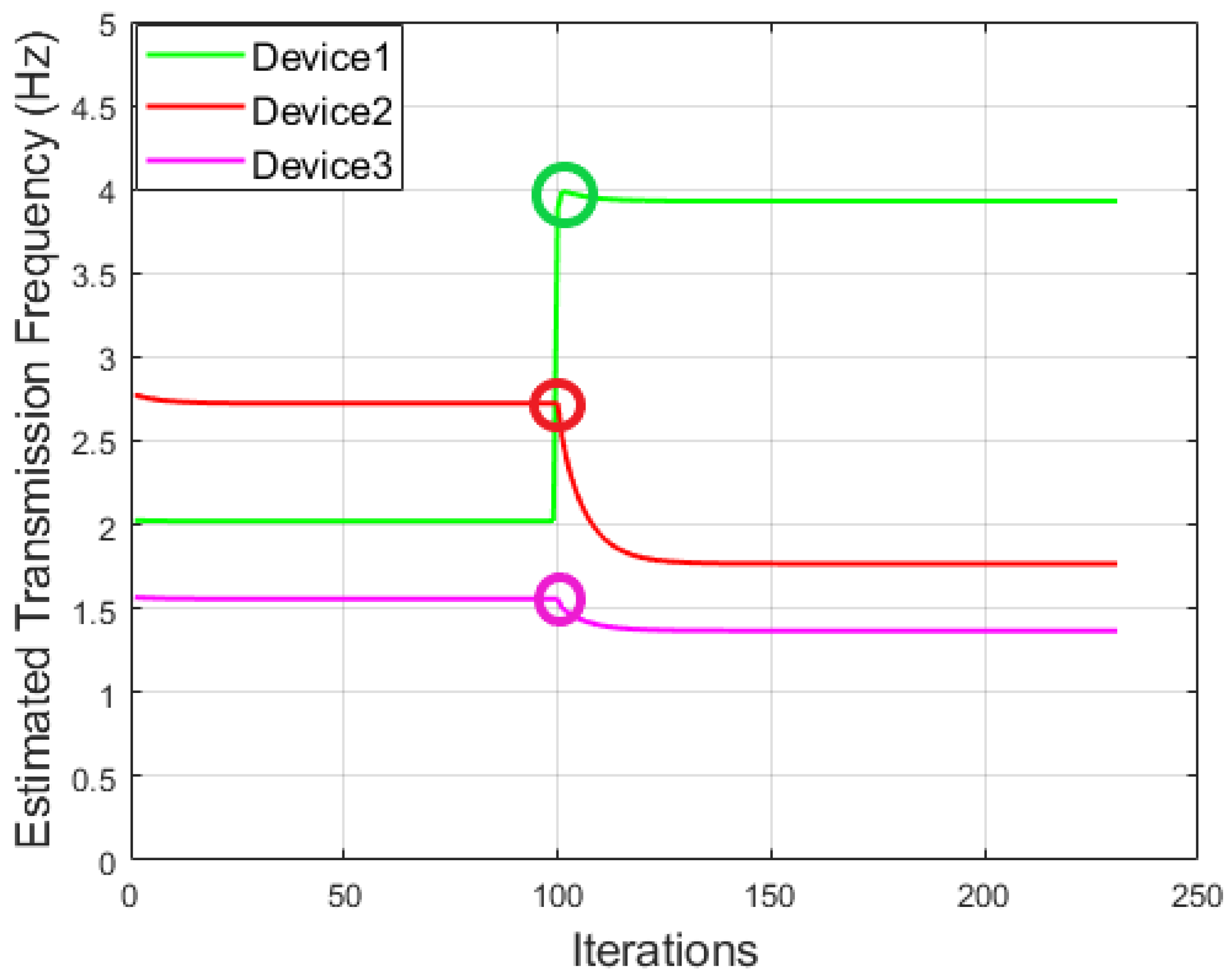
- The key focus of our previous work [10] was to propose an optimisation framework for an IoT network so that the transmission frequency of the connected IoT devices can be dynamically adjusted to their optimal values through an ADMM-based iterative optimisation method. In this work, we focus on the design of an anomaly detector on top of the system we proposed in [10], which is able to infer anomalies that may occur in the underlying IoT transmission management system in real time. Thus, the scope of work is significantly extended in comparison to [10].
- 2.
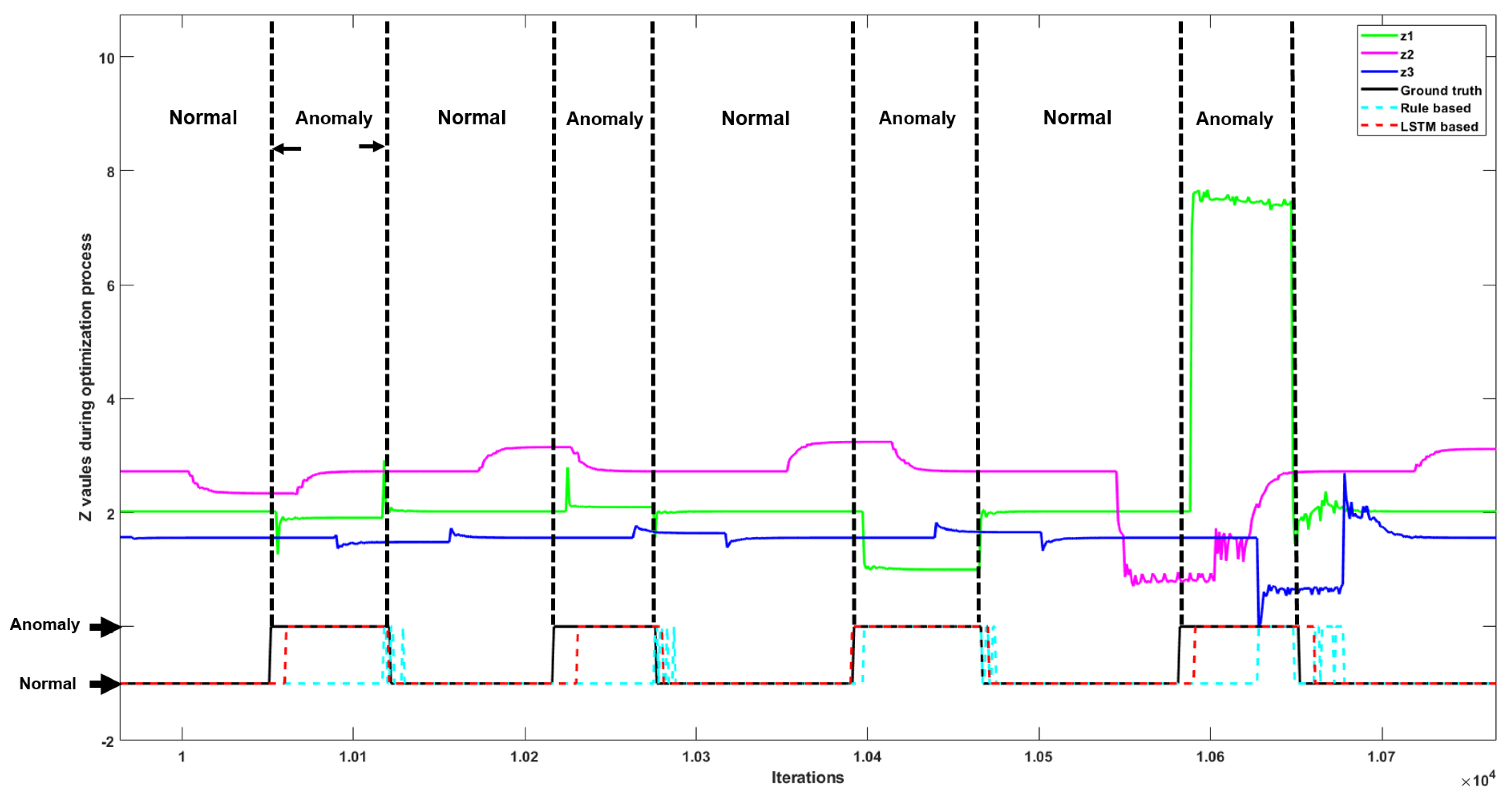
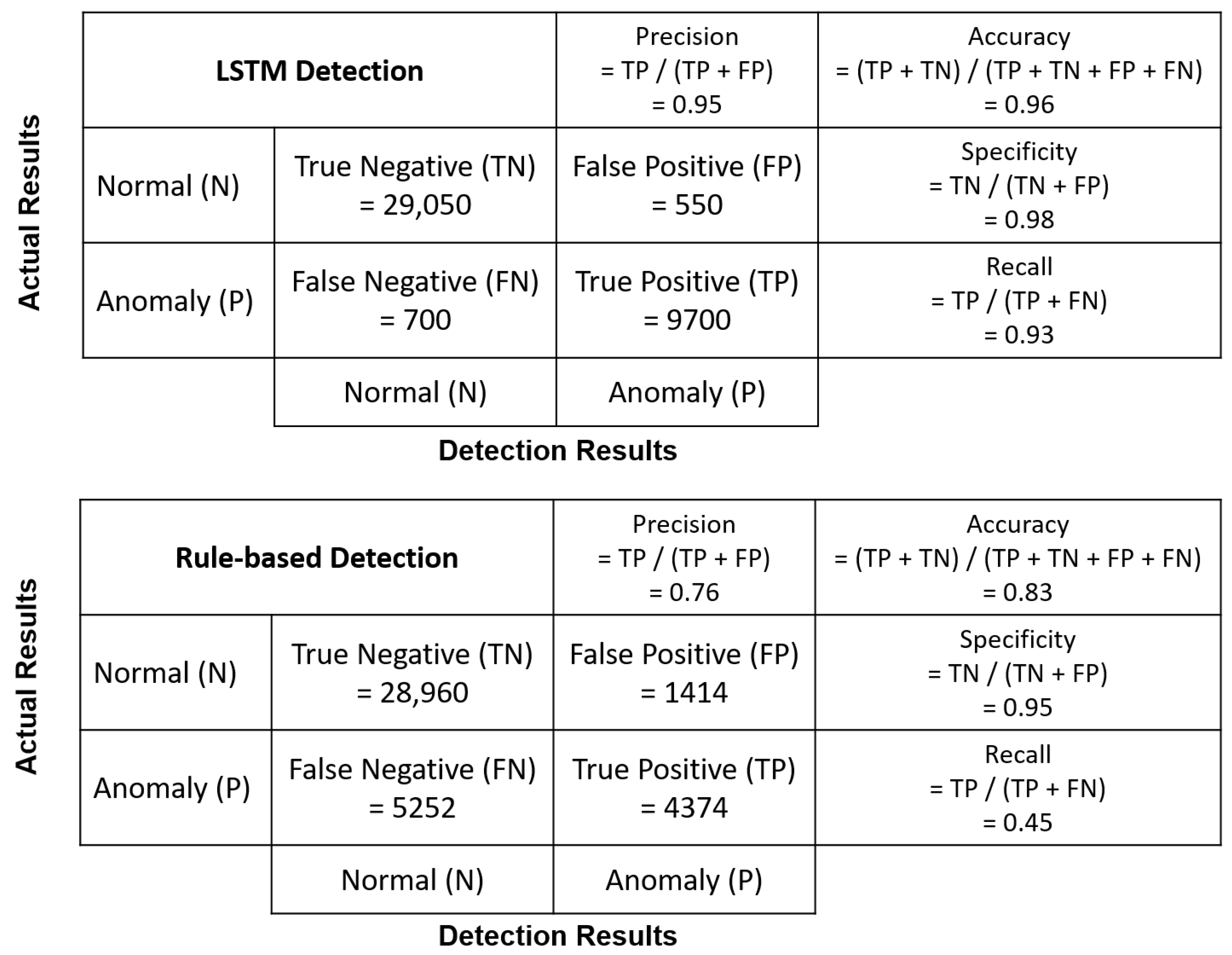
- We propose both mathematical-rule-based and deep-learning-based approaches for detecting anomalies in the IoT transmission frequency management system. In particular, the rule-based approach is designed to reveal anomalies of the system based on fundamental optimisation theory, and the deep learning approach aims to establish a prediction model based on sequential data analysis in system implementations.
- 3.
- We conduct a comprehensive comparative study using both anomaly detector strategies and demonstrate the strengths and weaknesses for the two approaches in both simulated and practical working environments.
2. Related Works
2.1. Transmission Frequency Management System
| Algorithm 1 Decentralised ADMM algorithm. |
|
2.2. Related Solution for Anomaly Detection
- Point: Anomalies happen randomly without clear reason and always with irregularity. For instance, network sensors can catch a sudden fluctuation in video signals [20] due to abnormal noises.
- Contextual: Anomalies happen given the specific context, including the spatial and temporal cues. For example, in [21], the pattern related to traffic accident varies between long-term and short-term prediction (e.g., day-level and hour-level prediction) in different areas.
- Collective: Anomalies happen when the central node and edge devices work incongruously or the observation in a group has unusual patterns with other groups. For instance, in [22], anomalies can be defined as cascading delays in railway traffic, and these delays are common in traffic data across different weeks.
3. Problem Statement
- 1.
- Manipulation on utility function input only: The independent variable of the utility function is manipulated by adding an input factor with a small given range, .
- 2.
- Manipulation on utility function type and input: The utility function can be totally changed to anther type of concave function specified by the utility function set of the system, i.e., . Note that this setting maps to the “multiple user-defined utility functions” example in Section 2.1.
- 3.
- Manipulation on transmission data size: The data size required for the j’th device per writing request is manipulated by adding a size factor with a small given range, .
- 1.
- We assume that at every given time only one edge device is manipulated, which is the fundamental basis for detecting an anomaly when multiple devices are manipulated in our system.
- 2.
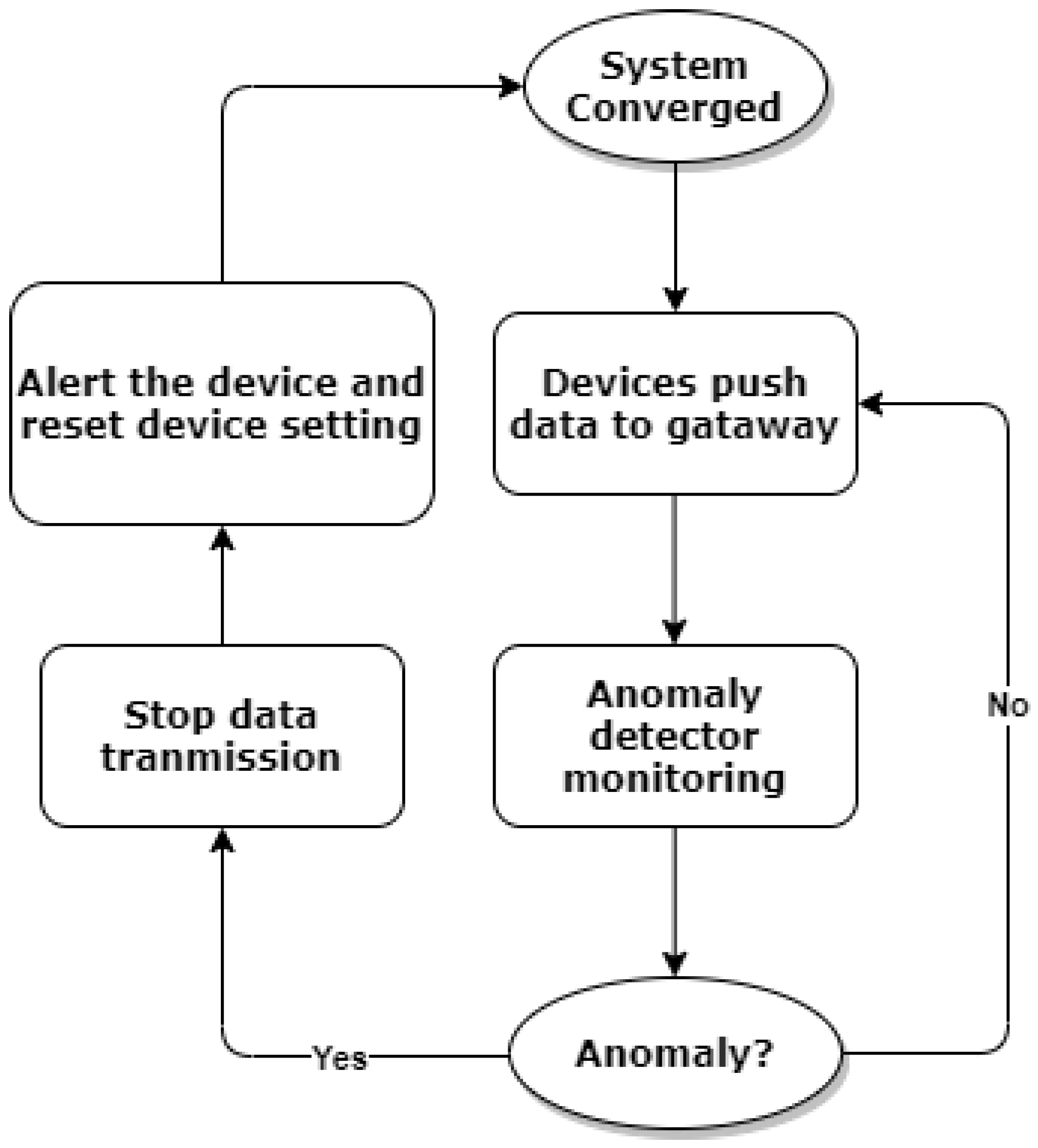
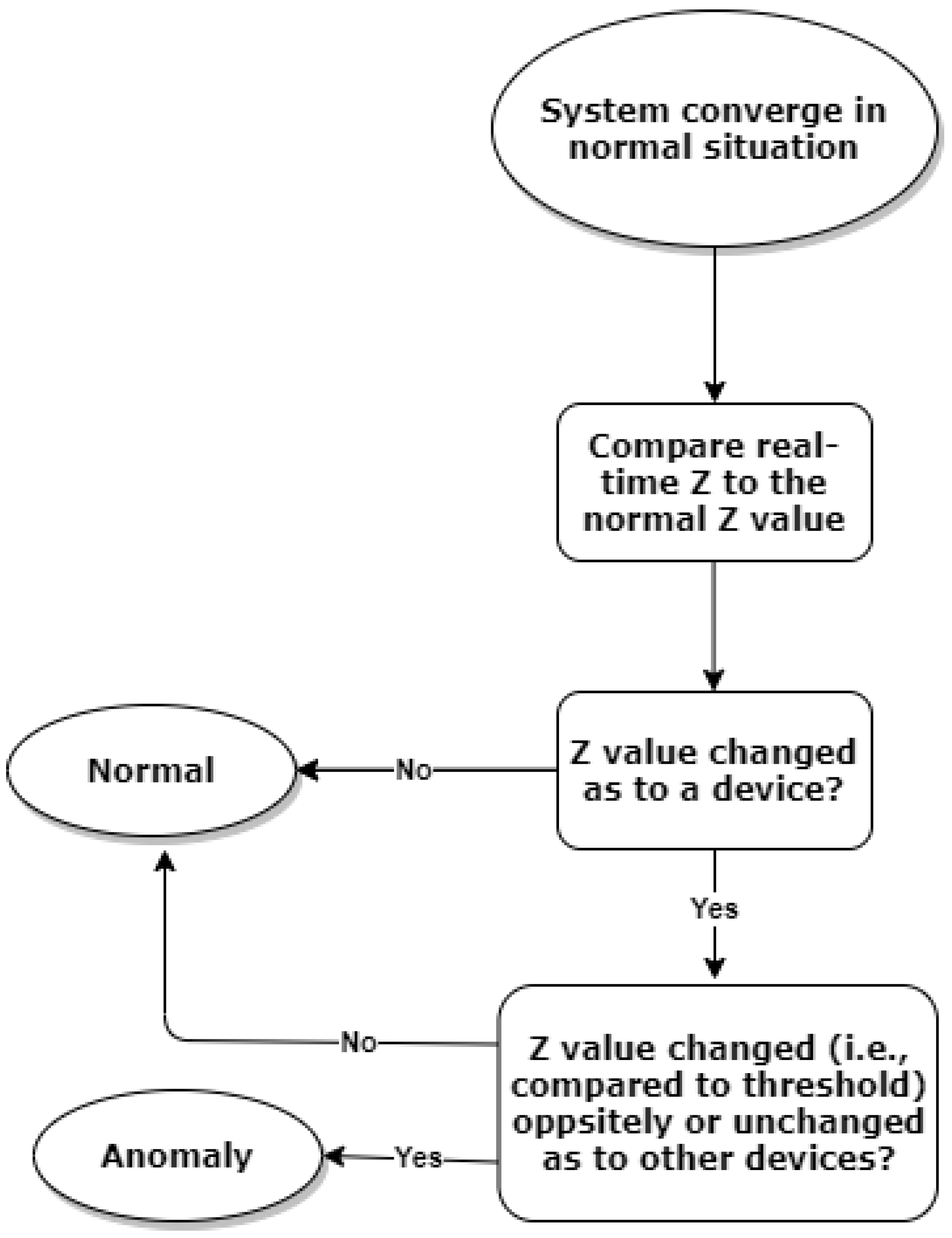
- We assume that the anomaly detector is a separate process running on the gateway, and it can only access limited information on the gateway but not all. More specifically, we assume that the anomaly detector can only access the value of and the sum of and , denoted by , from the ADMM iterative process at the gateway. It will never access the exact transmission frequency directly from the local devices and other resources/parameters shared between devices and the gateway.
- 3.
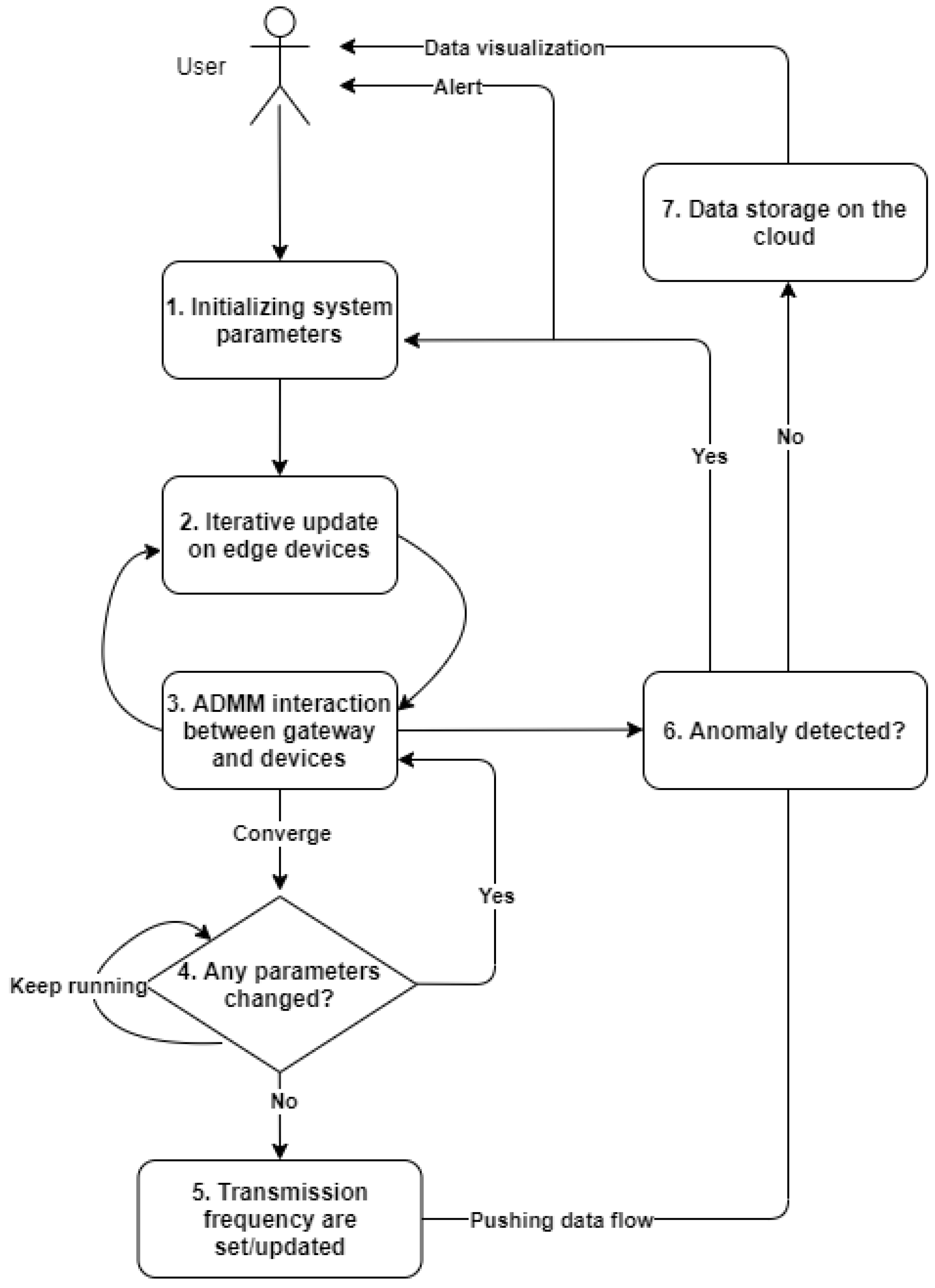
- We assume that the anomaly detector starts to monitor anomalies in real time once the ADMM algorithm converges and local devices start pushing data to the gateway. The device setting will be reset when any anomalies are detected, and the optimisation process will be reactivated to reset the optimal solutions for fair resource allocation as per the normal situation. To further illustrate this point, the process of anomaly detection is shown in Figure 3.
4. Proposed Approach
4.1. Rule-Based Anomaly Detection
4.1.1. Situation ,
4.1.2. Situation ,
4.1.3. Situation ,
4.2. Limitations on the Rule-Based Anomaly Detection
- A.
- The rule-based approach mainly relies on the optimality criteria without fully leveraging information from the iterative process, and as a result it cannot further distinguish different types of anomalies when a manipulation happens on the edge device.
- B.
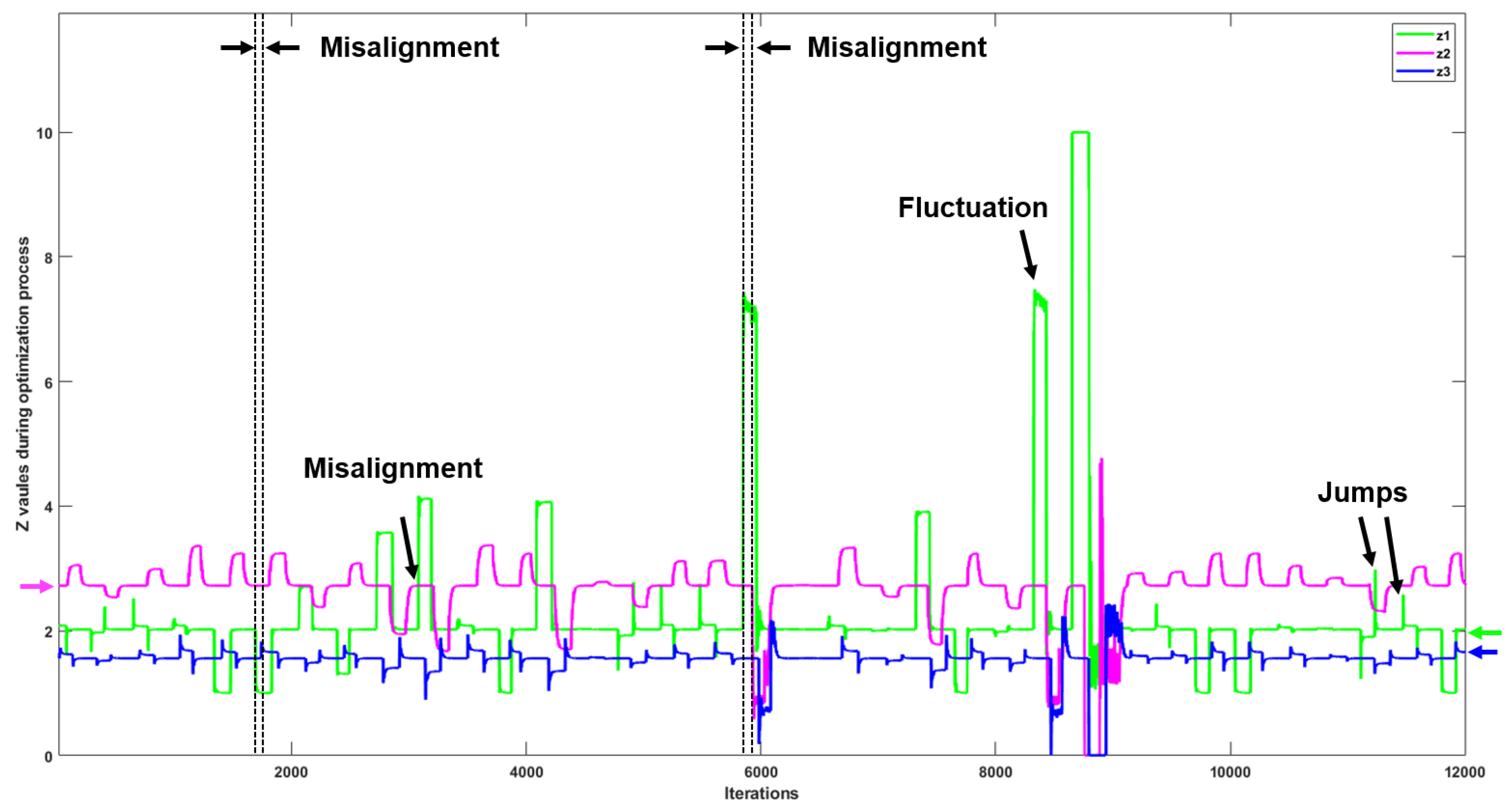
- As we shall see, system parameters, i.e., , may fluctuate during the optimisation process, and this can easily result in misjudgements when using the rule-based approach.
- C.
- Furthermore, when there are network delays in the IoT network, transmission frequencies of the devices may not change simultaneously, which can also lead to misjudgements when using the rule-based approach.
4.3. IoT Anomaly Detection with LSTM-Based Approaches
5. Experimental Setup
5.1. Setup for Manipulations
- Manipulation on utility function type and input: The utility function is changed from to (i.e., see Table 2) with input factor, resulting in manipulation input factor), labelled as type 1.
- Manipulation on transmission data size: The data size factor is set as a random value from the set of and the is manipulated as size factor, labelled as type 2.
- Manipulation on utility function input only: In this case, the is set as a random value from the set of for the manipulation input factor), which is labelled as type 3.
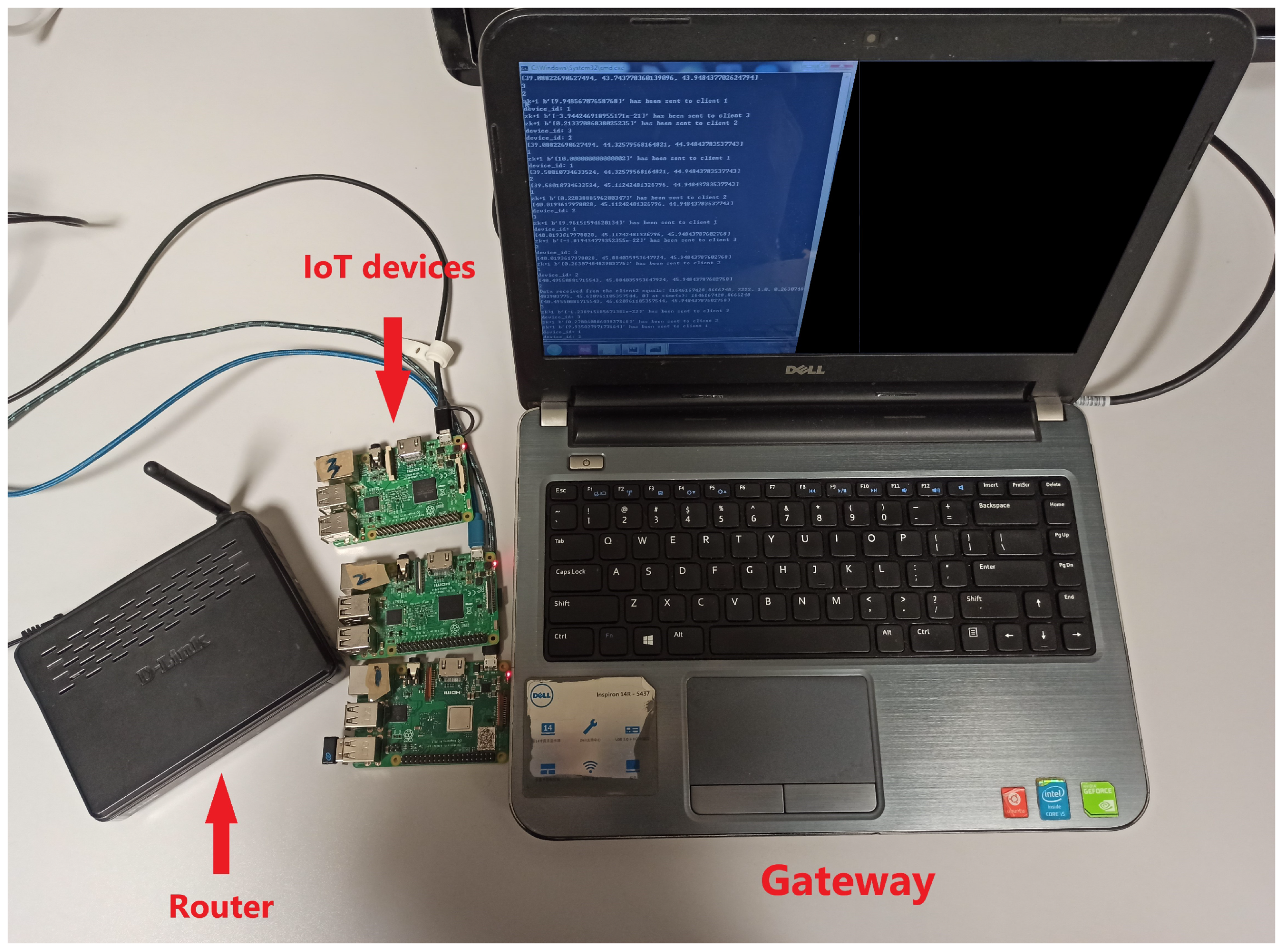
5.2. System Setup
5.3. Data Generation
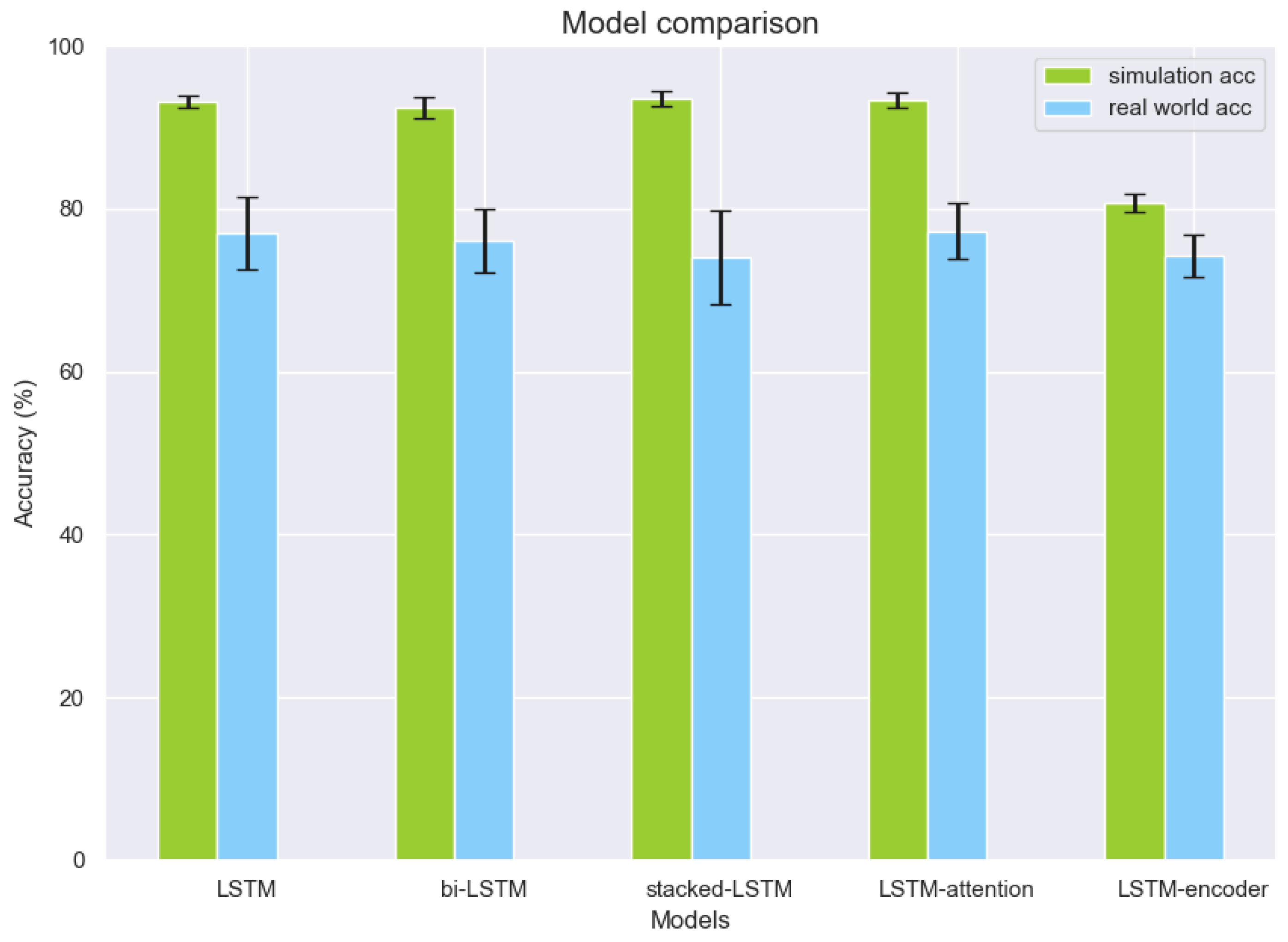
5.4. Setup for LSTM-Based Networks
6. Experimental Results
6.1. Anomaly Detection on SS
6.2. Anomaly Detection on RS
7. Discussion
8. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
Abbreviations
| MWF | Maximum writing frequency |
| DFWF | Data flow writing frequency |
| SS | Simulation system |
| RS | Real-world system |
References
- Madakam, S.; Lake, V.; Lake, V.; Lake, V. Internet of Things (IoT): A literature review. J. Comput. Commun. 2015, 3, 164. [Google Scholar] [CrossRef] [Green Version]
- Hao, C.; Jia, X.; Li, H. A brief introduction to IoT gateway. In Proceedings of the International Conference on Communications Technology & Applications, Beijing, China, 14–16 October 2011; pp. 610–613. [Google Scholar]
- Singh, C.S.; Pilli, E.S.; Joshi, R.C.; Girdhari, S.; Govil, M.C. Brokering in interconnected cloud computing environments: A survey. J. Parallel Distrib. Comput. 2018, 133, 193–209. [Google Scholar]
- Nir, M.; Matrawy, A.; St-Hilaire, M. Economic and Energy Considerations for Resource Augmentation in Mobile Cloud Computing. IEEE Trans. Cloud Comput. 2015, 6, 99–113. [Google Scholar] [CrossRef]
- Aazam, M.; Huh, E.N.; St-Hilaire, M.; Lung, C.H.; Lambadaris, I. Cloud Customer’s Historical Record Based Resource Pricing. IEEE Trans. Parallel Distrib. Syst. A Publ. IEEE Comput. Soc. 2016, 27, 1929–1940. [Google Scholar] [CrossRef]
- Ni, J.; Zhang, K.; Vasilakos, A.V. Security and Privacy for Mobile Edge Caching: Challenges and Solutions. IEEE Wirel. Commun. 2020, 28, 77–83. [Google Scholar] [CrossRef]
- Alwarafy, A.; Al-Thelaya, K.A.; Abdallah, M.; Schneider, J.; Hamdi, M. A Survey on Security and Privacy Issues in Edge Computing-Assisted Internet of Things. IEEE Internet Things J. 2020, 8, 4004–4022. [Google Scholar] [CrossRef]
- Atlam, H.F.; Wills, G.B. IoT security, privacy, safety and ethics. In Digital twin Technologies and Smart Cities; Springer: Berlin/Heidelberg, Germany, 2020; pp. 123–149. [Google Scholar]
- Zhou, W.; Piramuthu, S. Security/privacy of wearable fitness tracking IoT devices. In Proceedings of the 2014 9th Iberian Conference on Information Systems and Technologies (CISTI), Barcelona, Spain, 18–21 June 2014; pp. 1–5. [Google Scholar]
- Wu, H.; O’Connor, N.E.; Bruton, J.; Liu, M. An ADMM-based Optimal Transmission Frequency Management System for IoT Edge Intelligence. In Proceedings of the 2021 IEEE 7th World Forum on Internet of Things (WF-IoT), New Orleans, LA, USA, 26–31 July 2021; pp. 217–222. [Google Scholar] [CrossRef]
- Miller, B.N. Detection of Malicious Content in JSON Structured Data Using Multiple Concurrent Anomaly Detection Methods; Eastern Michigan University: Ypsilanti, MI, USA, 2016. [Google Scholar]
- Khan, M.A.; Toseef, U. User utility function as quality of experience (qoe). In Proceedings of the ICN, Citeseer, Toronto, ON, Canada, 19 August 2011; Volume 11, pp. 99–104. [Google Scholar]
- Abdeljaouad, I.; Karmouch, A. Monitoring IPTV quality of experience in overlay networks using utility functions. J. Netw. Comput. Appl. 2015, 54, 1–10. [Google Scholar] [CrossRef]
- Zhang, R.; Wu, K.; Li, M.; Wang, J. Online Resource Scheduling Under Concave Pricing for Cloud Computing. IEEE Trans. Parallel Distrib. Syst. 2016, 27, 1131–1145. [Google Scholar] [CrossRef]
- Bian, B.; Chen, X.; Xu, Z.Q. Utility Maximization Under Trading Constraints with Discontinuous Utility. SIAM J. Financ. Math. 2019, 10, 243–260. [Google Scholar] [CrossRef]
- Lv, Z.; Chen, D.; Lou, R.; Wang, Q. Intelligent edge computing based on machine learning for smart city. Future Gener. Comput. Syst. 2021, 115, 90–99. [Google Scholar] [CrossRef]
- Boyd, S.; Parikh, N.; Chu, E. Distributed Optimization and Statistical Learning via the Alternating Direction Method of Multipliers; Now Publishers Inc.: Delft, The Netherlands, 2011. [Google Scholar]
- Chalapathy, R.; Chawla, S. Deep Learning for Anomaly Detection: A Survey. arXiv 2019, arXiv:1901.03407. [Google Scholar]
- Cook, A.A.; Mısırlı, G.; Fan, Z. Anomaly Detection for IoT Time-Series Data: A Survey. IEEE Internet Things J. 2020, 7, 6481–6494. [Google Scholar] [CrossRef]
- Zhong, J.X.; Li, N.; Kong, W.; Liu, S.; Li, T.H.; Li, G. Graph convolutional label noise cleaner: Train a plug-and-play action classifier for anomaly detection. In Proceedings of the IEEE/CVF Conference on Computer Vision and Pattern Recognition, Long Beach, CA, USA, 15–20 June 2019; pp. 1237–1246. [Google Scholar]
- Zhou, Z.; Wang, Y.; Xie, X.; Chen, L.; Liu, H. RiskOracle: A Minute-Level Citywide Traffic Accident Forecasting Framework. In Proceedings of the AAAI Conference on Artificial Intelligence, New York, NY, USA, 7–12 February 2020; Volume 34, pp. 1258–1265. [Google Scholar]
- Heglund, J.S.; Taleongpong, P.; Hu, S.; Tran, H.T. Railway delay prediction with spatial-temporal graph convolutional networks. In Proceedings of the 2020 IEEE 23rd International Conference on Intelligent Transportation Systems (ITSC), Rhodes, Greece, 20–23 September 2020; pp. 1–6. [Google Scholar]
- Liu, X.; Liu, Y.; Liu, A.; Yang, L.T. Defending ON–OFF Attacks Using Light Probing Messages in Smart Sensors for Industrial Communication Systems. IEEE Trans. Ind. Inform. 2018, 14, 3801–3811. [Google Scholar] [CrossRef]
- Anthi, E.; Williams, L.; Burnap, P. Pulse: An adaptive intrusion detection for the Internet of Things. In Proceedings of the Living in the Internet of Things: Cybersecurity of the IoT-2018, London, UK, 28–29 March 2018; pp. 1–4. [Google Scholar] [CrossRef]
- Ukil, A.; Bandyoapdhyay, S.; Puri, C.; Pal, A. IoT Healthcare Analytics: The Importance of Anomaly Detection. In Proceedings of the 2016 IEEE 30th International Conference on Advanced Information Networking and Applications (AINA), Crans-Montana, Switzerland, 23–25 March 2016; pp. 994–997. [Google Scholar] [CrossRef]
- Hu, Y.; Qu, A.; Work, D. Graph Convolutional Networks for traffic anomaly. arXiv 2020, arXiv:2012.13637. [Google Scholar]
- Strom, B.E.; Applebaum, A.; Miller, D.P.; Nickels, K.C.; Pennington, A.G.; Thomas, C.B. Mitre Att&ck: Design and Philosophy; Technical Report; The MITRE Corporation: McLean, VI, USA, 2018. [Google Scholar]
- Gordon, G.; Tibshirani, R. Karush-kuhn-tucker conditions. Optimization 2012, 10, 725. [Google Scholar]
- Schmidhuber, J.; Hochreiter, S. Long short-term memory. Neural Comput. 1997, 9, 1735–1780. [Google Scholar]
- Ergen, T.; Kozat, S.S. Unsupervised anomaly detection with LSTM neural networks. IEEE Trans. Neural Netw. Learn. Syst. 2019, 31, 3127–3141. [Google Scholar] [CrossRef] [Green Version]
- Lindemann, B.; Maschler, B.; Sahlab, N.; Weyrich, M. A survey on anomaly detection for technical systems using LSTM networks. Comput. Ind. 2021, 131, 103498. [Google Scholar] [CrossRef]
- Aljbali, S.; Roy, K. Anomaly detection using bidirectional LSTM. In Proceedings of the SAI Intelligent Systems Conference, London, UK, 16–17 July 2020; pp. 612–619. [Google Scholar]
- Thill, M.; Däubener, S.; Konen, W.; Bäck, T.; Barancikova, P.; Holena, M.; Horvat, T.; Pleva, M.; Rosa, R. Anomaly detection in electrocardiogram readings with stacked LSTM networks. In Proceedings of the 19th Conference Information Technologies-Applications and Theory (ITAT 2019), CEUR-WS, Donovaly, Slovakia, 20–24 September 2019; pp. 17–25. [Google Scholar]
- Xia, L.; Li, Z. A new method of abnormal behavior detection using LSTM network with temporal attention mechanism. J. Supercomput. 2021, 77, 3223–3241. [Google Scholar] [CrossRef]
- Nguyen, H.; Tran, K.P.; Thomassey, S.; Hamad, M. Forecasting and Anomaly Detection approaches using LSTM and LSTM Autoencoder techniques with the applications in supply chain management. Int. J. Inf. Manag. 2021, 57, 102282. [Google Scholar] [CrossRef]
- Fan, Z. Distributed demand response and user adaptation in smart grids. In Proceedings of the 12th IFIP/IEEE International Symposium on Integrated Network Management (IM 2011) and Workshops, Dublin, Ireland, 23–27 May 2011; pp. 726–729. [Google Scholar] [CrossRef] [Green Version]
- Chen, Z.; Chen, D.; Zhang, X.; Yuan, Z.; Cheng, X. Learning graph structures with transformer for multivariate time series anomaly detection in iot. IEEE Internet Things J. 2021, 9, 9179–9189. [Google Scholar] [CrossRef]
- Deng, A.; Hooi, B. Graph neural network-based anomaly detection in multivariate time series. In Proceedings of the AAAI Conference on Artificial Intelligence, Vancouver, BC, Canada, 2–9 February 2021; Volume 35, pp. 4027–4035. [Google Scholar]
- Zhao, H.; Wang, Y.; Duan, J.; Huang, C.; Cao, D.; Tong, Y.; Xu, B.; Bai, J.; Tong, J.; Zhang, Q. Multivariate time-series anomaly detection via graph attention network. In Proceedings of the 2020 IEEE International Conference on Data Mining (ICDM), Sorrento, Italy, 17–20 November 2020; pp. 841–850. [Google Scholar]
- Jun, M.; Woo, D.; Chung, E.Y. Partial connection-aware topology synthesis for on-chip cascaded crossbar network. IEEE Trans. Comput. 2010, 61, 73–86. [Google Scholar] [CrossRef]

| Index | Utility Functions |
|---|---|
| 1 | |
| 2 | |
| 3 |
| Utility Functions |
|---|
| Anomaly Types | Simulation | Real-World System |
|---|---|---|
| Function input only | 98.14% ± 0.52% | 82.84% ± 3.81% |
| Function type and input | 99.82% ± 0.01% | 93.90% ± 1.52% |
| Data size | 93.91% ± 1.00% | 92.65% ± 0.85% |
| General (two-class) | 98.81% ± 0.38% | 96.28% ± 0.89% |
| General (four-class) | 92.35% ± 0.84% | 78.88% ± 3.80% |
| Anomaly Types | Simulation | Real-World System |
|---|---|---|
| Function input only | 97.48% | 86.53% |
| Function type and input | 99.65% | 80.21% |
| Data size | 65.26% | 66.59% |
| General (two-class) | 91.78% | 83.34% |
| Complexity | LSTM | bi-LSTM | Stacked-LSTM | LSTM-att. | LSTM-en. |
|---|---|---|---|---|---|
| Num. of model parameters | 43,204 | 86,404 | 123,604 | 73,204 | 124,210 |
| Simulation inference (s) | 0.66 | 1.05 | 0.93 | 0.56 | 0.36 |
| Real-world inference (s) | 0.60 | 1.13 | 0.93 | 0.52 | 0.33 |
| Thresholds | Real-World System |
|---|---|
| 1% optimal frequency | 86.53% |
| 5% optimal frequency | 87.90% |
| 10% optimal frequency | 87.02% |
| 15% optimal frequency | 86.62% |
| 30% optimal frequency | 83.23% |
| 50% optimal frequency | 77.10% |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2022 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Wu, H.; O’Connor, N.E.; Bruton, J.; Hall, A.; Liu, M. Real-Time Anomaly Detection for an ADMM-Based Optimal Transmission Frequency Management System for IoT Devices. Sensors 2022, 22, 5945. https://doi.org/10.3390/s22165945
Wu H, O’Connor NE, Bruton J, Hall A, Liu M. Real-Time Anomaly Detection for an ADMM-Based Optimal Transmission Frequency Management System for IoT Devices. Sensors. 2022; 22(16):5945. https://doi.org/10.3390/s22165945
Chicago/Turabian StyleWu, Hongde, Noel E. O’Connor, Jennifer Bruton, Amy Hall, and Mingming Liu. 2022. "Real-Time Anomaly Detection for an ADMM-Based Optimal Transmission Frequency Management System for IoT Devices" Sensors 22, no. 16: 5945. https://doi.org/10.3390/s22165945
APA StyleWu, H., O’Connor, N. E., Bruton, J., Hall, A., & Liu, M. (2022). Real-Time Anomaly Detection for an ADMM-Based Optimal Transmission Frequency Management System for IoT Devices. Sensors, 22(16), 5945. https://doi.org/10.3390/s22165945






